Abstract
Keywords
Introduction
Electronic Health Records (EHRs) contain and enable the distribution medical information relevant to the delivery of care of an individual, along with relevant ancillary information, such as their demographic characteristics and insurance or financial data related to their care provision.1,2 Following rapid developments in this area since 2000, the use of EHRs is now integral to healthcare provision in most developed healthcare systems in high or middle-income countries. 3
Successful implementation of the EHRs can bring about substantial benefits for patients, HCPs, and the health organizations such as better care, more efficiency, improved data accuracy, and minimal errors. Indeed, successful implementation of EHR is often viewed as a key quality improvement indicator within these organizations.2,4
However, for the full benefits of EHRs to be realized, the information they contain must be as freely available as necessary to relevant healthcare professionals, but the widespread and easy access to EHRs within healthcare can also pose a potential threat to patients’ data privacy. This can arise from unauthorized access of, or use of this information,5–7 or through security breaches enabled through poor system security measures or practice. 8 The likelihood of the latter is raised exponentially in relation to the level of access permitted. 9 The potential for risk in this area is also exacerbated by the recognized deficit in digital skills and competencies found within the HCP workforce globally, 10 meaning that inadvertent misuse, or ill-considered uses of data or systems, such as password sharing is more likely.11,12 Indeed, the most reported privacy violations do seem to be traceable to poor practice by HCPs who have valid access to the EHR system 5 ; something that numerous healthcare facilities worldwide have struggled to deal with. 13 A recent study in the US reported 3912 verified healthcare data breach incidents between 2005 and 2019. This level of incident reporting is about 43% higher in the healthcare sector compared with other industries. As a result, the average cost incurred due to these issues is estimated to be approximately $15 million. 14
Whilst there has been an increased awareness of the need to tackle data security issues within healthcare settings in recent years, rather than reducing, there is evidence that incidents of unauthorized access, where an individual HCP does not have a valid reason to access the data, or where they fail to secure the data they are accessing, are actually becoming more frequent. This increase does not appear to be confined to one healthcare context, but has been observed globally in countries including the UK 15 and Saudi Arabia. 16 Therefore, it is not surprising that concerns around EHR data privacy have escalated in recent years and are being voiced by many stakeholders, including patients and practitioners. 17
Healthcare organizations themselves often face severe financial or reputational penalties when EHR data breaches occur,14,18,19 perhaps partly underlying the increased concern they too are showing.20,21 There is an increase realization that managing and storing patients’ data is complex and open to multiple threats 22 and that many healthcare systems simply do not have the experience, expertise or processes to deal with this adequately. 23 At the same time, national and pan-national legislation, such as the EU’s General Data Protection Regulations (GDPR), are requiring greater and greater stringency, governance, risk management and accountability. 24 Therefore, data privacy has become a fundamental element within health organizations’ strategic plans,25,26 with many implementing official data policies 27 that require HCPs to follow strict and comprehensive protocols for using digital technology and managing data security. 5
Given that the behavior of HCPs concerning data privacy plays such a pivotal role in the effectiveness (or otherwise) of data security, it is vital to comprehend the factors that may influence behavior in this area. In particular, it is imperative to understand what drives or impedes compliance with data privacy policies. Moreover, while it is broadly accepted that attitudes to technology acceptance will play a big part in this, many other factors may likely act as barriers or drivers to compliance behavior. 28 Furthermore, some of these factors will be common, and others related to more specific sociocultural, national, or clinical contexts. 5 Therefore, a broad investigation is required to uncover these factors within the literature.5,29
Given the diverse nature of the likely influences on behavior, it is also expected that studies that have factors to investigate these will utilize a range of research methodologies. Therefore, a scoping review was adopted, as this approach is exploratory in nature. It does not exhibit bias towards or seek to assimilate similar types of studies or methodologies. Instead, this approach relies on more narrative synthesis and allows the inclusion of literature from a broad range of sources. In addition, it does not seek to exclude evidence based on an assessment of its quality. The present scoping review has been undertaken with the following question: “What does the literature reveal about the factors that influence HCPs’ intention to comply with the local data privacy policies aimed at protecting information within the EHR?” It aims to comprehensively understand the existing evidence base in this area. By comprehending the factors that influence the HCPs’ intention with the EHR privacy policy, we hope to understand current behavioral practices and develop better strategies to support compliance in the future. 30
Materials and methods
Joanna Briggs Institute scoping review framework
This scoping review was conducted according to Joanna Briggs Institute’s scoping review guidelines. 31 A scoping review allows researchers to explore the breadth of the literature and identify available materials in a particular field of investigation. 32 It is particularly suitable for an exploratory investigation of the literature into an area that is not highly focused, researched or clearly defined, and where several disparate elements may be expected to be contribute to the scope of the subject under investigation. Given its nature as an investigation into the boundaries of a field of study, the methodology does not rely on a systematized evaluation of the quality of the evidence-based discovered as part of the inclusion process, rather leaving it to the researcher to comment on and evaluate the significance of this. It is also suitable where the researcher expects to acquire information gained from a range of different study designs and research paradigms in order to cover the breadth of investigation required. It enables the researcher to call on both published and unpublished, peer reviewed and non-peer reviewed information. 32 A scoping review was, therefore, highly suitable for this investigation of the, as yet poorly defined and potentially disparate factors that influence HCPs’ intentions to comply with data privacy.
The list of steps undertaken when conducting a scoping review in line with enhanced JBI Scoping Review Framework, as followed in this study.
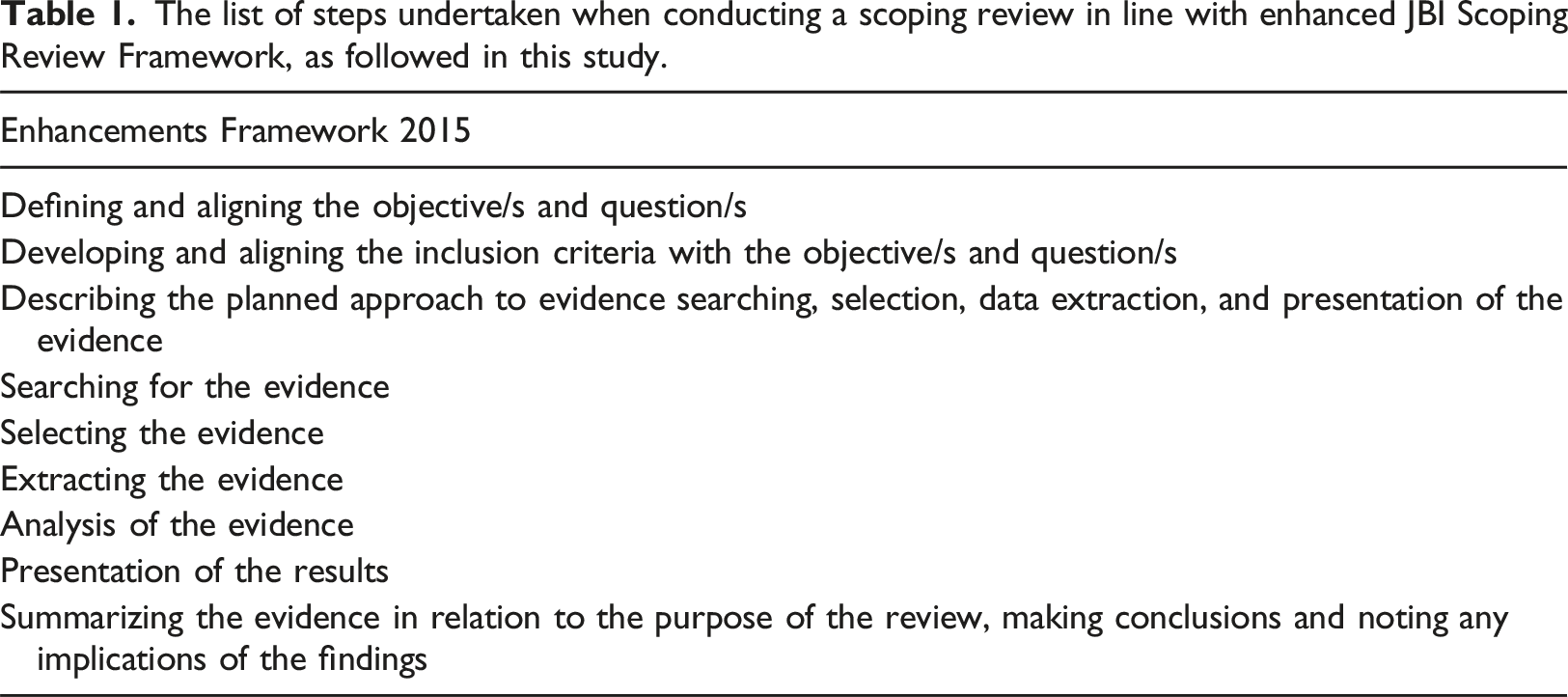
Defining and aligning the objectives and question
Scoping review question
The following question was defined by the researchers, in consultation with other experts in the field:
“What does the literature reveal about the factors that influence HCPs’ intention to comply with the local data privacy policies that are aimed at protecting information within the EHR?”
Scoping review objectives
In order to address the research question outlined above, the following review objectives were outlined: i. To identify what is already known about the barriers and drivers that influence HCPs’ compliance or intention to comply with their local data privacy policies, as these relate to the EHR. ii. To identify the theoretical frameworks that have been applied to this area of study and how these relate to different fields of study. iii. To synthesize the information gained regarding barriers and drivers that influence HCPs’ compliance or intention to comply with their local data privacy policies into one holistic framework.
Developing and aligning the inclusion criteria with the objective/s and questions
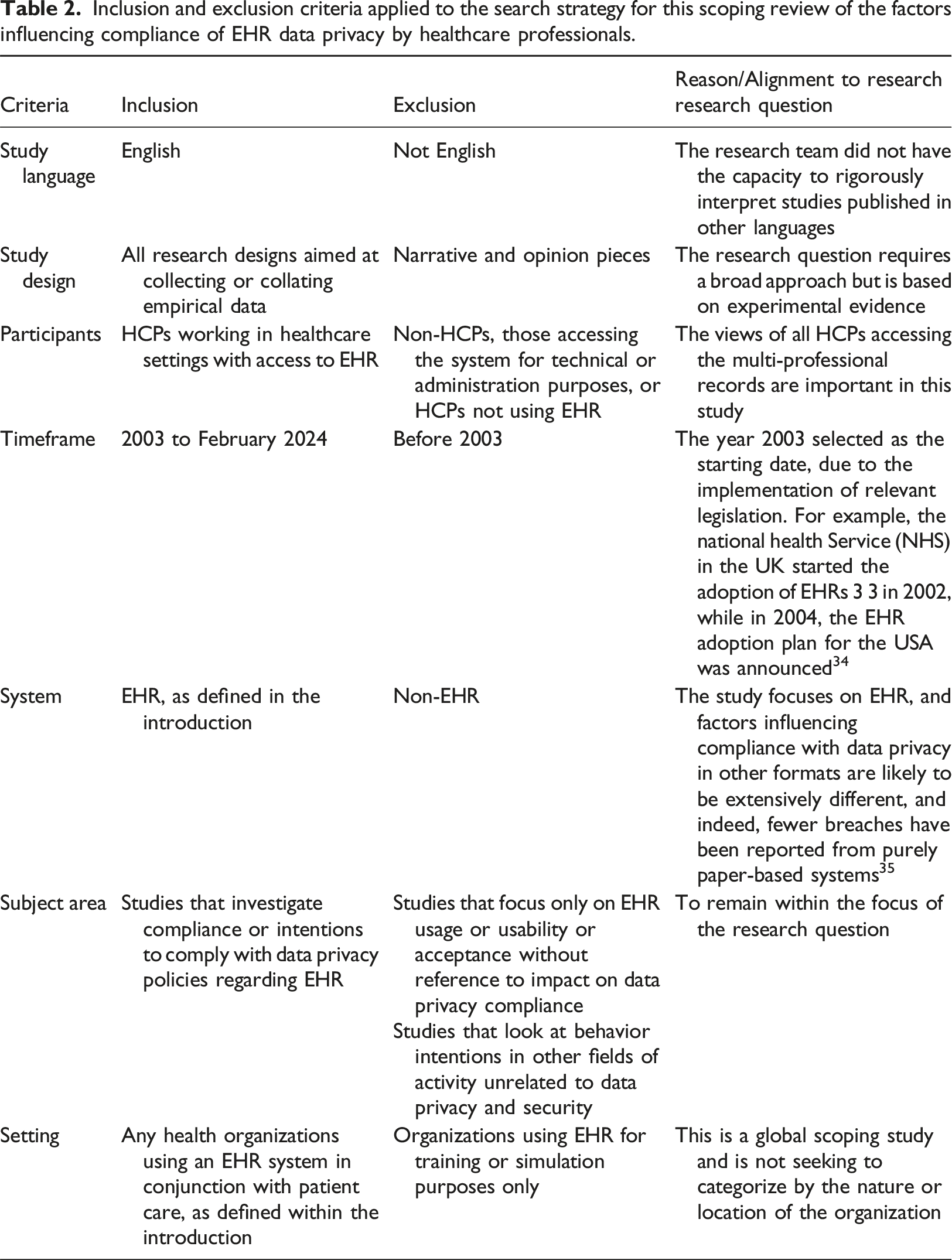
Inclusion and exclusion criteria applied to the search strategy for this scoping review of the factors influencing compliance of EHR data privacy by healthcare professionals.
Describing the planned approach to evidence searching, selection, data extraction, and presentation of the evidence
Participants
The search covered all HCPs using EHR systems as end-users, that is, inputting or accessing the data for clinical purposes.
Concept
The review focused on the HCPs’ compliance or intentions to comply with EHR data privacy, as presented in Table 2.
Context
This review includes any health organization with an EHR implemented for clinical purposes, as shown in Table 2. As the investigation is global, the review was not limited to a specific country, region, or demographic group.
Outcome
The outcomes considered within this review were wide in nature and included any measures or records of compliance or stated intentions in relation to compliance, and the factors that were recorded or articulated as impacting on this compliance or intention to comply. HCPs’ perceptions, attitudes, beliefs, social influences, perceived control, and behavioral intentions regarding compliance were the main concern of this review.
Searching, selecting, and extracting evidence
Following exploratory searches using the OVID (MEDLINE) database and consultation with expert search librarians regarding the search approach and search objectives, the main search for this study was carried out using seven scientific publications’ databases, as between them, these were known to cover the key literature in this area. These were; Cochrane library, OVID (MEDLINE, AMED, PsycINFO, and EMBASE), SCOPUS, and Web of Science.
The search terms used, and the relationships between them, as employed to interrogate the databases used to identify articles relating to the barriers and drivers influencing behavioral intentions to comply with data privacy policies in relation to EHR use.
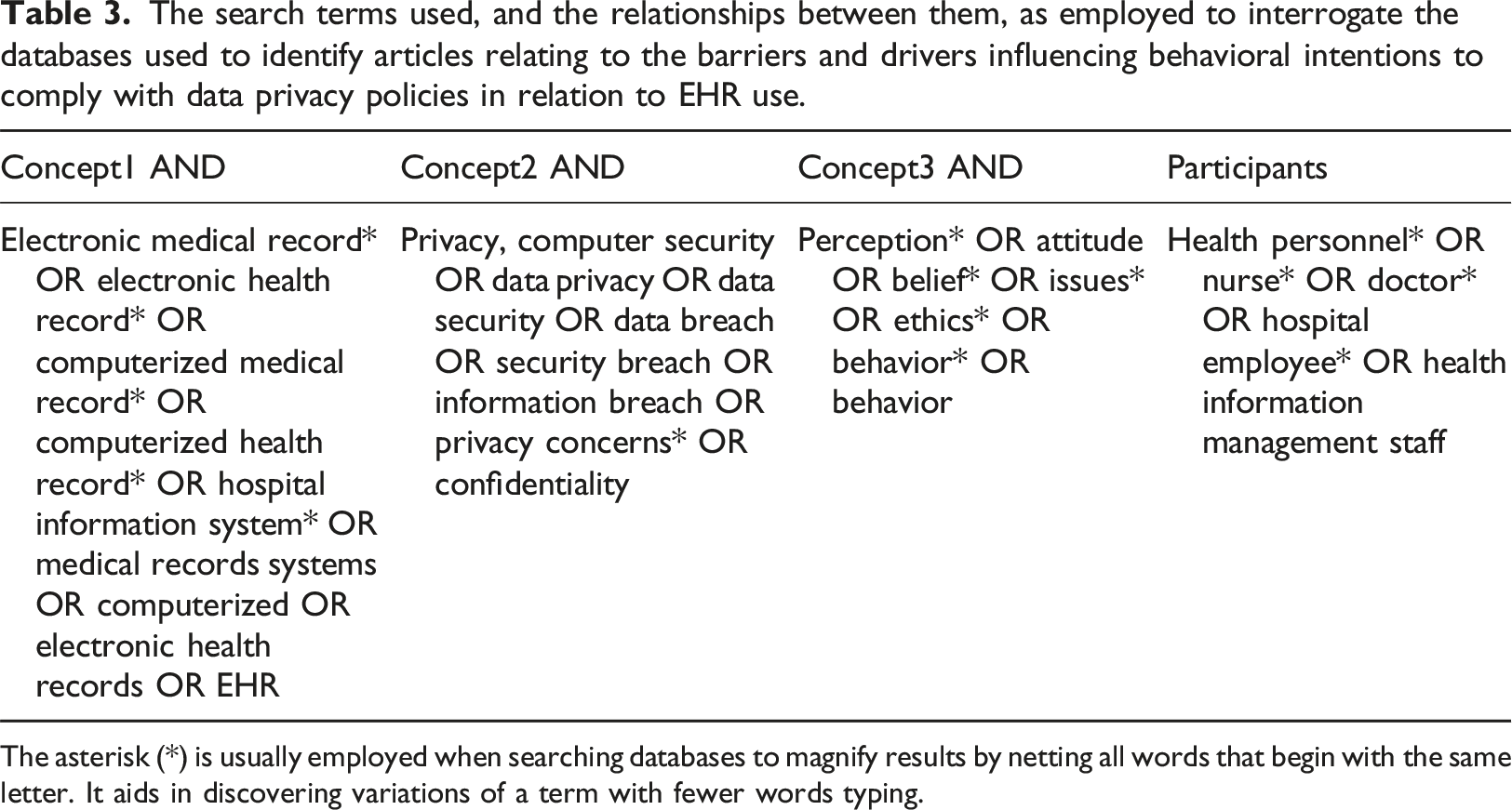
The asterisk (*) is usually employed when searching databases to magnify results by netting all words that begin with the same letter. It aids in discovering variations of a term with fewer words typing.
“Hand searching”, that is searching outside of the recognized scientific databases of published work, was also carried out using the Google Scholar search engine to identify any additional information fitting within the inclusion criteria. The reference lists of relevant articles found through the search process were also hand searched for relevant article that could be included.
Selecting the evidence
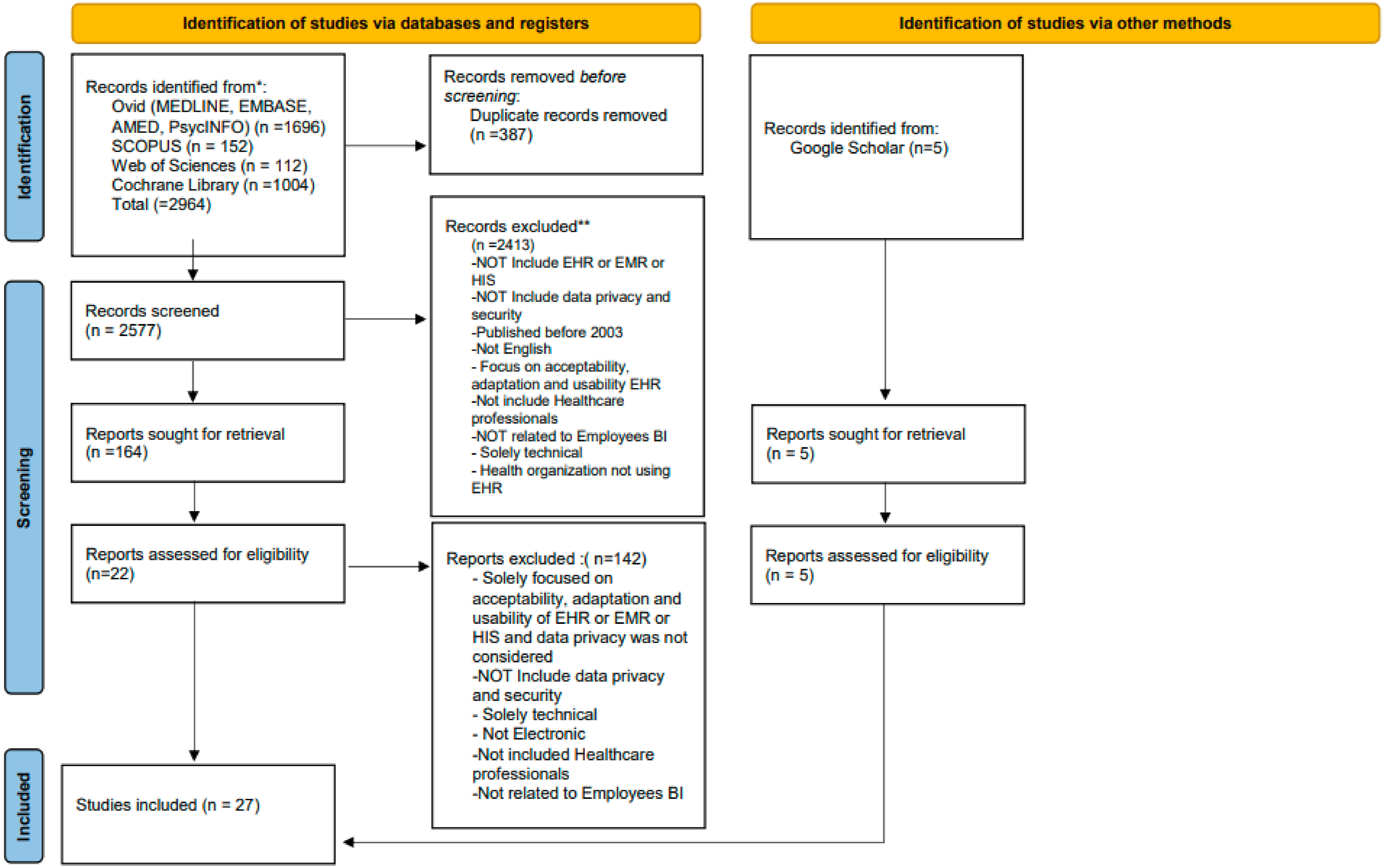
Based on the approach outlined above, the search was performed in February 2024 on the seven databases noted. This resulted in 2964 articles. An additional five articles were found by hand-searching.
In order to find the articles that were relevant to the research question posed, the articles identified from the search process were then screened using the Preferred Reporting Items for Systematic reviews and Meta-Analyses (PRISMA) process.
36
This is illustrated in Figure 1. Initially, 387 duplicate articles were removed using bibliographic software. Following this process, an initial screening of the titles of the papers resulted in a further 2577 being rejected. Therefore, 164 articles were then retrieved for further screening. Screening of the abstracts and then full text of these articles led to the exclusion of a further 142, leaving 22 articles that satisfied the inclusion criteria for the study. The five hand-sought articles were added to these to make a total of 27 articles that were accepted into the analysis phase of the review. The detailed reasons for excluding the articles from the study are outlined in Figure 1. Moreover, the Scoping Reviews (PRISMA-ScR) Checklist was used to help in checking and identifying the content of the review
37
(see Table 10 in the supplementary file). The PRISMA flow diagram outlining the steps taken to collect and review articles for inclusion in the scoping review.
36
Extracting the evidence
The 27 articles identified as being relevant to the review were read in detail several times and all information contained within them that was relevant to the search question was extracted. The information was coded and stored for thematic analysis, using EndNote Version 20.
Analysis of the evidence
As outlined above, each article included in the review was subjected to thematic analysis. A narrative synthesis was used to combine the findings from the different papers together. This included an iterative combining of the more granular themes identified from individual papers into more robust, general categories. This process of coalescing the themes continued until these could not be justifiably combined further.
Presentation and summarization of the data
The data will be presented and discussed in the remainder of this article in textual form. Conclusions and implications of the findings will be presented in a similar manner.
Results
Summary of the studies
All of the 27 studies included in this review focused on the factors that influence HCPs’ intention to comply with data privacy in relation to EHR use and were conducted in healthcare organizations that have electronic systems. The majority of the studies used descriptive, quantitative approaches with questionnaires being the most commonly used data collection tool. Two studies did employ qualitative methods28,38 and one study was a systematic review 58 (see Table 6 in the supplementary information).
There has been a surge of research interest on the factors that influence HCPs’ compliance with EHRs data privacy globally in recent years with the results indicating that 88% of the studies captured in this scoping review were published between 2015 and 2023, (see Table 7, supplementary information). Studies were published in a range of different countries from America, Europe, Asia and the Middle East, representing high or middle-income countries, as might be expected in relation to the prevalence of EHR implementation. Whilst six studies focused on nurses, most studies included participants from a range of healthcare professions.
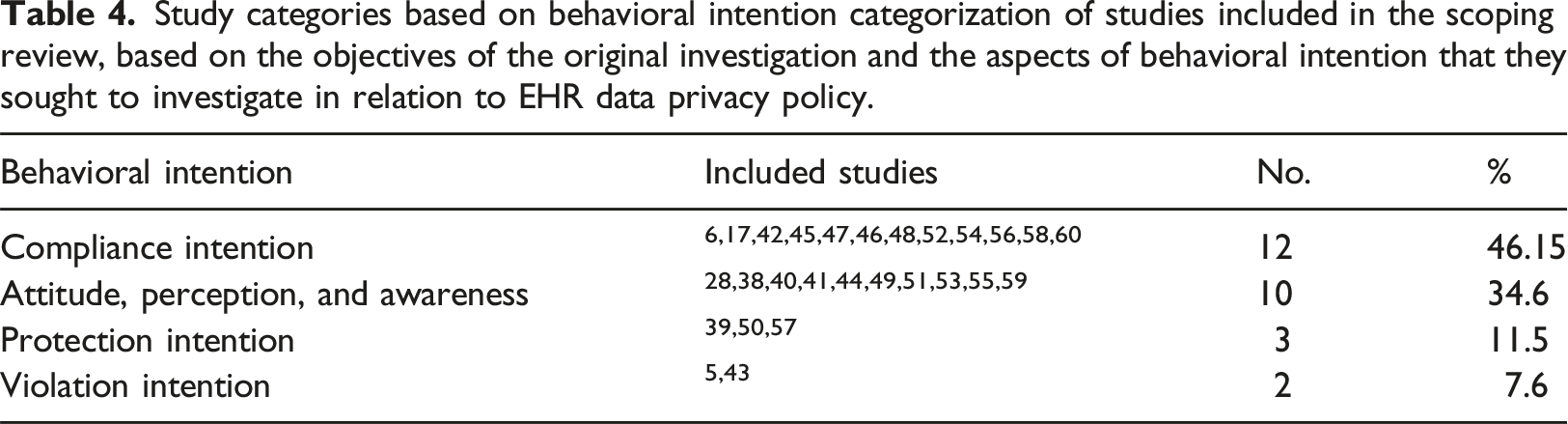
Study categorization
Study categories based on behavioral intention categorization of studies included in the scoping review, based on the objectives of the original investigation and the aspects of behavioral intention that they sought to investigate in relation to EHR data privacy policy.
Factors identified as impacting HCP’s intentions to comply with data privacy in relation in EHR
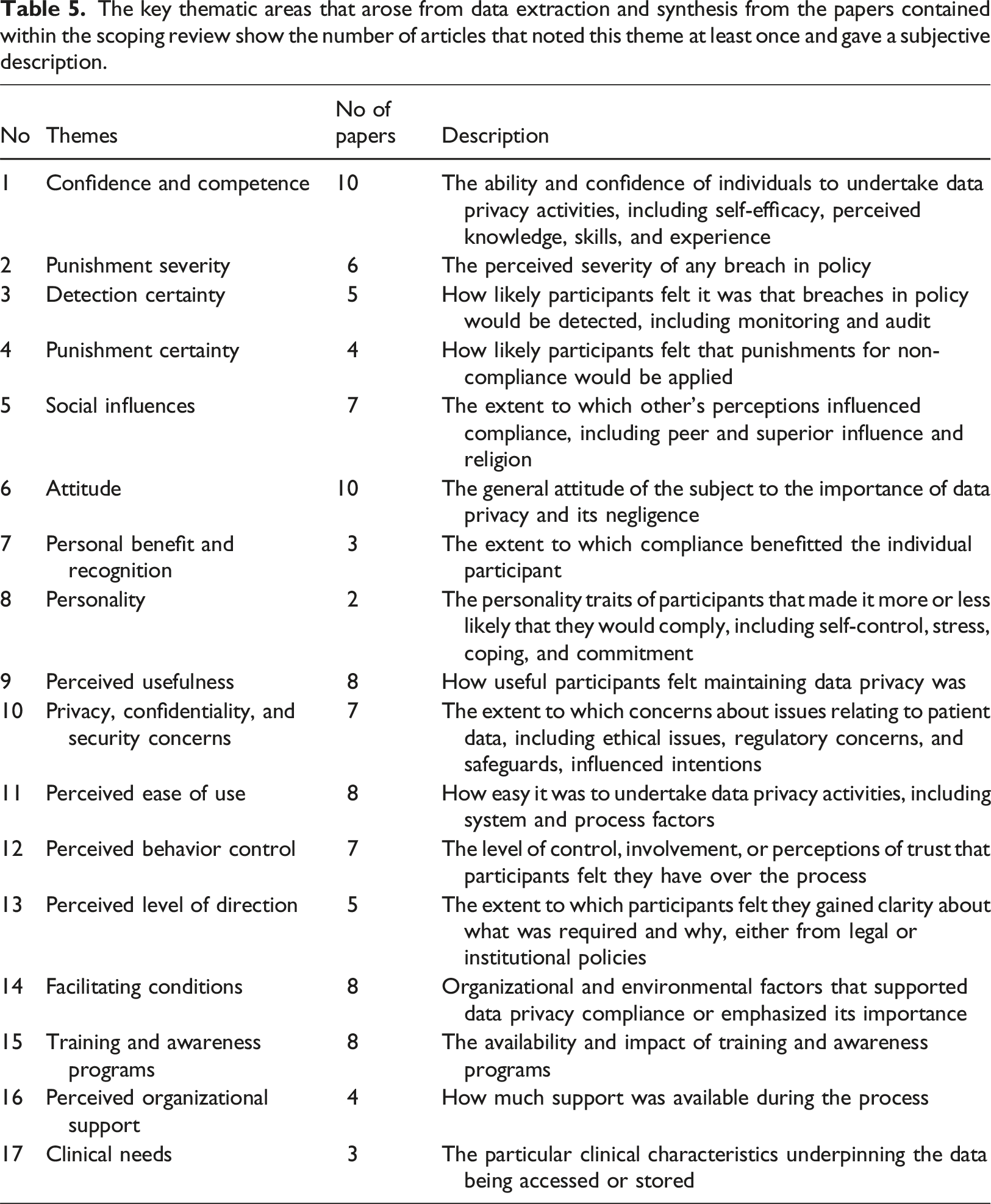
The key thematic areas that arose from data extraction and synthesis from the papers contained within the scoping review show the number of articles that noted this theme at least once and gave a subjective description.
Extracted theories and theoretical framework
In total, 18 different theoretical frameworks were adopted by 21 out of 27 studies to help interpret HCPs’ compliance with the EHR policy, with eight adopting multiple frameworks5,6,40–42,45,53,54 (see Table 9 in supplementary file). These theories range from pure behavioral theories, the most commonly used being the Theory of Planned Behavior (TPB),,5,42,45,52,59,60 which argues that action is determined by beliefs or the perceived beliefs of others, about a behavioral course of action. Others, such as Deterrence Theory (DT),5,17,47,56 and Protection Motivation Theory (PMT),6,57 are concerned with responses to threats. Moreover, some studies adopted theories that related more specifically to technology adoption behaviors, including the Technology Acceptance Model (TAM),42,45 or the Unified Theory of the Acceptance and Use of Technology (UTAUT),.38,42
Discussion
Scope and focus of observations
The data from the papers included in the scoping review show there were many different factors that arose as influencing HCPs intentions to comply with data privacy policy and procedure in relation the EHR. Many of these were internal factors, such as attitude, confidence or concern about the implications for non-compliance (see Table 5). This is perhaps not surprising as the vast majority of the studies started with a purpose to explore person-centered behavioral objectives, such as intentions to comply, or inherent attitudes, as outlined in Table 4. However, between them the studies also uncovered a whole range of structural factors such as organizational culture that also influenced behavior.
The broad scope that must be considered when looking at factors influencing intentions to comply with data privacy policy, as outlined in the results of the review is also evident from the range of theoretical positions and perspectives that were applied in attempts to understand the observations made. It is pleasing to see that nearly all of the studies relied on at least one theoretical framework in order to interpret their results. In total, 18 different theoretical frameworks have been employed in this way. These theories and theoretical framework were adopted from different fields, such as psychology, criminology and technology disciplines. Several of the theoretical frameworks were used to determine the actual behavior or behavioral intentions of HCPs. 58 The diversity of theoretical frameworks in the reviewed studies indicate that there is no single theory or theoretical framework that alone can adequately explain HCPs’ compliance or behavioral intention concerning EHR privacy and security policies. Nevertheless, it is notable that the most frequently used theoretical frameworks were the TPB, the DT, and the PMT. 58 The TPB argues that our externalized behaviors are driven largely by our beliefs and attitudes towards the behavior and its outcome, as well as our own beliefs about how others perceive our potential behavior in this area. Therefore, internal, person-centered factors become the overarching barriers and drivers to behavior despite the facilitatory or inhibitory conditions that surround the action, suggesting the primacy of these internal factors. The DT and PMT theoretical frameworks are concerned with perceptions about avoidance of negative consequences as a result of decisions taken in relation to behavioral actions, and so again, deal very largely with internalized factors.
Of course, it does not follow that the most used theories are the best fit to study the HCPs’ compliance behavior, and we also have to be careful of an ”“echo chamber effect” where application of the theoretical model can lead to observations to support that positioning. However, it is notable that theoretical models that dealt more with the technological aspects of the EHR and data privacy did not feature highly in the investigations, suggesting that this was not seen as a primarily a technological issue. In the longer term, other frameworks such as Decomposed Theory Planned Behavior (DTPB), which is an extended theory from the TPB, 61 should be also considered, as they offer a broader number of constructs and may be able to holistically capture and categorize many of the factors more fully.
The broad scope of the observations does also illustrate and confirm the decision to undertake this review as a scoping review, which enables a much more exploratory investigation of the literature without the constraints of a systematic review and enables a wider range of literature to be considered in order to probe the parameters of the field under investigation.31,32
Confidence and competence
Whilst this review is primarily a qualitative synthesis, confidence and competence were the elements most commonly reported as having an influence on compliance, despite the focus of the investigation undertaken.
A lack of computer skills, such as logging in and off from the system, and changing passwords, can hinder HCPs from running the electronic health system properly.6,39 There is a well-recorded deficit in digital competencies across HCPs internationally,6,39,42,46 and it is vital that this is addressed, if higher levels of compliance with data privacy procedures are to be effectively implemented. Some studies have suggested that hospitals should equip HIM staff with suitable and sufficient skills to operate software and hardware in a way that ensures data privacy is protected. 6 Nurses’ self-efficacy, that is their personal belief that they are capable to execute the course of action required, is important with regard to their technical abilities to maintain EHR data privacy. 39 Indeed, when hospital staff are made aware that the management trust and rely upon their skills to protect data, their intentions to comply with data regulations has been seen to increase commensurately. 50
Negative consequences from non-compliance
Concerns over detection of non-compliance, the level of any ensuing punishment or negative personal consequences as well as the certainty with which HCPs perceived such a punishment would be applied were clearly factors that influenced HCPs intentions to comply with EHR data privacy policy. Monitoring was considered to be a driver for the HCPs’ compliance.17,58,56 It has been reported that HCPs are deterred from violating EHR privacy policy if the policy itself states and communicates to them that the system is actively monitored, and that any unethical or illegal activities and non-compliance will be detectable. 17 Nurses’ intentions to violate privacy policy can be deterred if their organizations audit and inspect employee use of the EHR, as this makes employees feel more accountable for their actions. 47 Moreover, the severity and certainty of sanctions have been reported to be effective in reducing non-compliance behavior towards data privacy policy among HCPs and others who work within healthcare organizations.6,17,58,47 Thus, the more HCPs and other professionals are worried about the consequences of violating EHR and other data policy, the more likely they are to follow it.
In contrast, some studies argued that sanction and punishments cannot solely prevent the HCPs from violating data privacy policy. 43 Furthermore, if health organizations monitor HCPs’ activities via the computerized system, this can reduce inappropriate system usage behavior, but might also impact their performance negatively, due to feelings of suspicion, which are known to have detrimental impacts on moral and productivity. 17
Social influence
Social influence is the change in behavior that one person causes in another, intentionally or unintentionally. It happens as a result of the way the influencee person perceives themselves in relationship to the influencer, other people and society in general. 62
Peer social influence is an important factor that influences HCPs’ intentions towards data privacy policy and regulations.5,6,39,45,47 Previous studies have reported that nurses are more likely to influence other nurses to desist from non-compliance if they themselves are skilled and familiar with the EHR data privacy process,39,47 and peer influence between IT staff in hospitals has been found to be effective to the management and valuing the privacy environment in the hospital. 6 However, the actual strength of this influence is disputed. Foth 5 for example argues that from their observations, peer influence between HCPs is low regarding adherence to data protection rules. Therefore, we need to understand more about the nature and effectiveness of positive peer influences.
Many scholars agree that a positive influence of supervisors and managers has an important driving effect on the intention of HCPs to accept the data privacy policy and regulation.6,39,45,47 However, this can also have negative influence if the culture inside the hospital prioritizes HCPs’ task-based productivity over their compliance with EHR privacy and security measures.53,58
Attitudes, personality and personal gain
Attitudes towards compliance5,41,45,48,39,55,58,60 and conceptions of negligence51,53,58 were seen to play a mediating role in the intentions of individual HCPs to comply with data privacy. Likewise, personality traits, including self-control, 58 stress and coping strategies 58 were also seen to mediate compliance. However, it must be recognized that these are intermediary, potentially dynamic constructs, as much influenced by other personal and organizational factors as they in turn influence them.
The prospect of personal benefit and recognition was one of the drivers seen have a positive impact on compliance intention towards data protection regulations.5,46,52,50 HCPs were more likely to comply where they felt it led to intrinsic personal benefit, 57 or if they felt their efforts were noticed and appreciated. 48 This suggests that healthcare organizations need to create a reward environment, to encourage the system’s end users to follow the rules. Moreover, there is evidence that suitable rewards systems can have a positive impact on reinforcing compliance into more habitual behavior 46 with a potentially greater and more sustained impact on data protection.
Perceived usefulness and perceived ease of use
Perceived Usefulness is the extent to which the employee believes that using a specific application will increase their job performance, 63 and Perceived Ease of Use, is the extent to which task-effort is minimized. 63 These are both key constructs in many technology acceptance models, and they did indeed feature in the review here. There was generally a sense that compliance with data privacy policy was useful for HCPs as individuals49,59,54 and also for patient care. 49
Many factors were listed as negatively impacting on ease of use of the systems or processes. Impact on workload was an important example of this. Workload is a key barrier to HPCs’ compliance with EHR policy, 58 and compliance itself can sometimes exert an invisible additional pressure on clinical staff. 46 HCPs can find themselves facing dilemmas between the impetus to comply with privacy and security regulations and the expectations placed upon them to provide clinical care in practice. 38 Other studies have indicated major concerns about HCPs’ compliance with data protection within health organizations due to the added a workload and changed clinical workflow.5,45 Some researchers asserted that HCPs can be preoccupied with privacy issues to the extent that this obstructs their work routine, which can ultimately cripple the system usage itself in addition to potentially reducing quality of care and undermining patient satisfaction and safety. 40 Some studies reported that suboptimal workflows caused HCPs to adopt negative behaviors such as failing to log out at the end of session or copying patient information, even though they were aware of the pertinent privacy regulations and understood the legal consequences.28,58,54,53 Some adopted beliefs that stringent information privacy protection regulations were negatively impacting on patient care.28,38,51
Perceived behavior control
A sense of ownership, involvement and control in the process of data privacy also appeared to be an important factor in some of the studies identified in this review, and it is known that these factors can play an important role in behavioral intention and technology acceptance.5,39,58,40,41 However, this appears to be a fine balance as HCPs were also concerned about receiving an appropriate and helpful level of direction for the use of the process from both organizational58,38 and legislative frameworks. 40
Facilitating conditions and training
Although person-centered factors were clearly important in relation to intentions to comply with EHR data privacy, a number of structural components were identified that could influence this intention. Many of these related to the organizations in which the HCPs worked and related to issues such as their organizational management, 58 the culture within the organization, 58 the size and status of the organizations concerned, 40 their maturity in terms of information security, 44 the clarity of the communication 39 and the integration of the processes into already established everyday working practices. 58 It is clear then that organizations wanted to undertake successful implementation or improve the compliance with data privacy must address institutional culture and may need to invest specifically into change management processes.
Resource availability is another factor that facilitates a higher level of compliance with data protection regulations.5,46,54 The availability of compatible software and hardware affiliated with the hospital EHR system was found to enable privacy protection behavior among nurses in Taiwan. 39 Moreover, training and availability of information have been shown to be essential for a high level of adherence to data protection regulations among HCPs.56,5,51,52,58 Training can empower and equip the HCPs with the knowledge and skills they need when they notice privacy or security threats, empowering them to adhere with best practices.50–52,58 It can positively impact the HCPs’ awareness and their compliance with the EHR privacy policy. 52 Conversely, a lack of training and insufficient knowledge can lead to inadvertent data breaches.43,51
Limitations
Whilst scoping reviews do not require critical appraisal of the materials accessed, some limitations need to be noted regarding studies that were included in. Firstly, this method may lead to the inclusion of low-quality data. The reviewed studies primarily relied on one source of information, and most often on self-reporting, rather than observation or more objective measures. This could lead to bias in the results analyzed. Moreover, several studies analyzed multiple HCP groups and so it was not possible to draw conclusions between them.5,38,42
With regard to the conduct of the scoping review itself, again, some limitations need to be acknowledged. Even though this review was performed on seven major databases, inclusion of other databases may have uncovered other, more specialized articles and hence other factors to be considered. 64
Conclusions
This review set out to explore the factors that influence HCPs intentions to comply with EHR privacy policy and showed that in recent years a range of studies had sought to capture this information in a range of countries. The review identified many individual and organizational factors that have the potential to either encourage or hinder associated behavior. These observations were under pinned by a series of diverse theoretical frameworks, highlighting the multifactorial nature of these influential factors.
The review shows that in order for an organization to develop approaches that improve compliance, they must take a multifaceted approach working to improve training, capability and training of their workforce and also ensuring that the organizational culture is one that is mature in its management of change, has sufficient structural resources and clearly values individuals for their work in this area. Clearly articulating the potential consequences of lack of compliance is also important.
As the current research is primarily quantitative in nature, there may be scope to conduct qualitative or mixed methods research in order to gain deeper an in-depth insight into the behavioral intentions of HCPs toward data privacy compliance.
Supplemental Material
Supplemental Material - A scoping review of the drivers and barriers influencing healthcare professionals’ behavioral intentions to comply with electronic health record data privacy policy
Supplemental Material for A scoping review of the drivers and barriers influencing healthcare professionals’ behavioral intentions to comply with electronic health record data privacy policy by Nabil D Alhassani, Richard Windle, and Stathis Th Konstantinidis in Health Informatics Journal
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Correction footnote:
Updated Correspondence address: Nabil D Alhassani, Department of Health Services Management, College of Public Health and Health Informatics, Umm Al-Qura University, P.O. Box 715, Makkah 21955, Saudi Arabia. Email:
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Ethical statement
Supplemental Material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
