Abstract
The purpose of the healthcare Information System (HIS) is to replace the conventional method of data gathering and organization in hospitals into a modern method of systematic data collection, maintenance and dissemination. There has been an unprecedented rise in the malware and cyber-attacks on HIS recently. Cyber-attacks have become a major crisis for the healthcare industry. To address this scenario, the present paper conducts a study on the security factors integral to the healthcare information system and conducts the performance analysis of these factors. For this intent, the study has employed the Fuzzy Analytic Hierarchy Process (F.AHP) integrated with Technique Order Preference by Similarity to Ideal Solution (TOPSIS) integrated framework for evaluating the performance of each factor. Thereafter, the factors that play a vital role in healthcare data security breaches have been prioritized as per their security weights. Furthermore, the validity of the results obtained by the stated methodology has been established by conducting the sensitivity analysis and comparison of results with the other methods by using the same data set. Based on results thus obtained, the access control and software security have been identified as the most promising security factors.
Keywords
Introduction
Nowadays, healthcare is generating a large amount of data, and this necessitates the use of robust information systems that can cater to both the hospitals’ as well as the patients’ needs efficiently and securely. 1 Healthcare information system (HIS) is used for managing information, people and processes. Healthcare information system is like a system, which takes data as inputs, processes on the data, stores, and transmits the information. 2 Adopting the HIS improves the efficiency and effectiveness of the hospital’s work. HIS replaces the paperwork of hospitals by digitalization; digitalization of the hospitals facilitates in the easy access of the patient’s history in the system.3,4 However, the increased dependency on digitalization has led to several security issues in the digital world.
Security is an essential part of analyzing the medical data.5,6 Healthcare information system shares the data of the patients over the system; thus, reducing overcrowding at the hospitals. It is easy for the patients to communicate with the doctors remotely. Moreover, the doctors can also connect frequently with patients and diagnose the patients’ ailments at an early stage. 7 In the present era, the security of the Information system is a vital issue. The high costs of the medical data on the dark web and several vulnerabilities in the information systems make healthcare sector the most targeted industry of the cyber invasions. 8 In the electronic health system, assurance of the data security, and availability of the information between the doctor and patient is both a sensitive and a critical concern.
Many researchers are already working on the MCDM approach with different aims in this league. 9 Rajeev et al. (2020) applied fuzzy-based AHP-TOPSIS procedure for evaluating the impact of harmful factors of HIS. In this study, the authors prioritized the harmful factors which affect the data layers used in HIS. The authors focused basically on the data layers affected by harmful factors of HIS. 10
Zarour et al. (2021) have used the Fuzzy AHP approach for ensuring data integrity of healthcare information in digital health. The authors have prioritized the data integrity techniques that are used for maintaining the integrity of healthcare data. 11 M.H. Behzadi (2015) did a comparative study on Fuzzy AHP and Fuzzy TOSIS approaches in math teachers’ selection and found that both the fuzzy based techniques obtained better results than the traditional approaches. 12
In the case of inventory, Kabir and Hasin (2011) illustrated the benefits of capturing the fuzziness of human thought and assisting in the solution of the research issue through a systematic and straight forward approach. They identified the flexibility of manipulating criteria for a specific implementation, different classification analyses for different inventory records, application specific variable sets and crisp comparison values can be substituted for fuzzy comparison values for optimization if fuzzy comparisons aren’t available in case. 13
However, according to Mishra and Thakar (2012), the main advantage of Fuzzy AHP approaches is that they can be utilized for both qualitative and quantitative criteria, as well as convincingly resolve the conflicting assessments made by several decision-makers methodically . 14 In addition, a fuzzy AHP can fix and assist spatial cognition issues in several of circumstances, including: hospital site selection (Chi and Kue, 2001), screening potential landfill sites (Charnpratheep et al., 1997), teacher selection (M.H. Behzadi 2015). 12
Motivated by quality results obtained by using the fuzzy AHP and Fuzzy TOPSIS, the authors applied the fuzzy.AHP.TOPSIS approach for the scientific analysis of the security factors. 15 This study commenced by reviewing the research articles that specify the possible factors that are affecting the security of the healthcare information system security. 16 HIS also needs sustainable security features that can ensure confidentiality, integrity and Access control. However, identifying the factors in the healthcare infrastructure is a complex task; this is one of the key reasons for data breaches on the healthcare systems. 17 To increase the security and quality of healthcare information system services, full understanding of the notion of the security and variables that influence healthcare information system security becomes as important research query.
Furthermore, the contributions of the study are as: Section 2nd presents the Literature Review related to security factors in the HIS. The 3rd section discusses the HIS and factors for securing the HIS. Section 4th contains the methodology and sensitivity analysis. Section 5 and 6 present the discussion and conclusion, respectively.
Literature study
Though we reviewed several studies for our reference, the present section specifically mentions the studies related to approaches for securing the HIS. Managing security of HIS is the most critical aspect because attackers frequently and easily prey on the medical data.
Rajeev et al., (2020) applied fuzzy-based AHP-TOPSIS procedure for evaluating the impact of harmful factors of HIS. In this study, the authors prioritized the harmful factors which affect the data layers used in HIS. The authors focused basically on the data layers affected by harmful factors of HIS. 10
Although most of the authors have worked on the security of the information system, only a select few have done work on the healthcare information system security. Authors have opted CIA factors and sub factors which directly affects the HIS security. Multi-Criteria Decision Making (MCDM) technique is rarely used in the healthcare information system. However, we have observed that the accuracy of the MCMD technique is high, and hence, appropriate for reliable results. We have used the integrated technique of Fuzzy-AHP.TOPSIS for accurate assessment.
Materials and methods
Healthcare information system security
The use of Information System (IS)
25
in healthcare is in the digitalization of healthcare. Healthcare industry is adopting IS to replace the manual processing. Since the patient’s information contains personal information, information security becomes a critical issue because the data is daily uploaded and retrieved online.
26
HIS’s architecture is depicted in Figure 1. HIS can be divided into two parts: first, is the patients’ management system, and, the other is the managerial information system. PMS contains all the activities related to patients and MIS contains all the l managerial activities performed by the hospital staff. Collection of all information related to the patients is known as the Electronic Health Record (EHR). Healthcare information system architecture.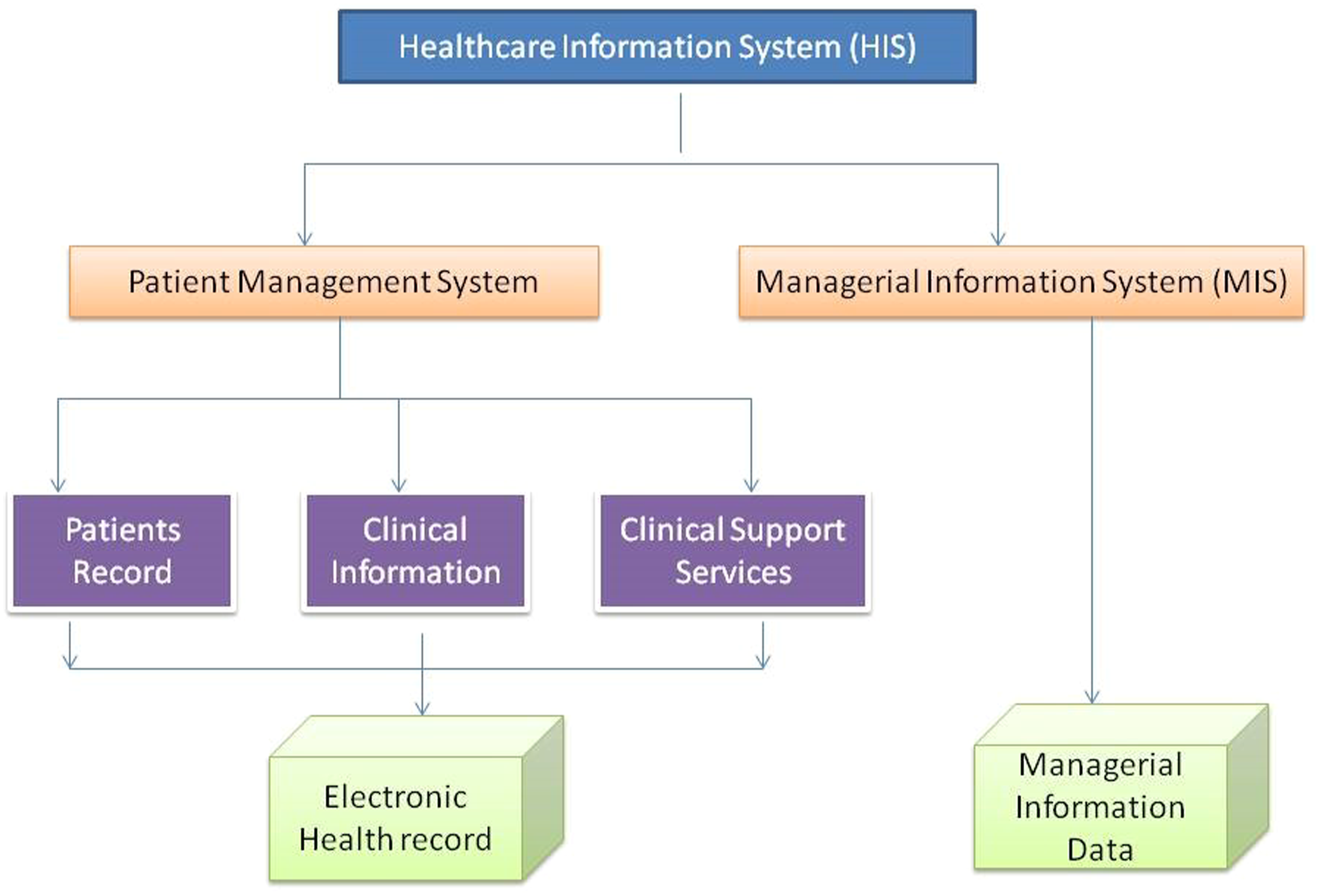
Electronic Health Records (EHR) stores the personal details and the present and past history of the patient’s diseases and many more test results. EHRs records can be shared easily. Without the security framework, the patients’ information can be used in an illegal way and be sold on the black web. Healthcare data are highly lucrative and hence frequently targeted by the attackers. Thus, healthcare sector must develop its own cybersecurity plan and operations addressing these three key issues:
Factors for securing HIS
A lot of factors have been identified for securing the HIS. However, for effective security management of HIS, the focus should be on the main important factor, that is the HI system that helps in protecting the vulnerabilities in healthcare information is several ways. Factors that may affect the security of the HIS are shown in Figure 2. We have addressed three main factors that affect the security and other sub-factors related to the main factors are shown in the figure. Security factors hierarchy.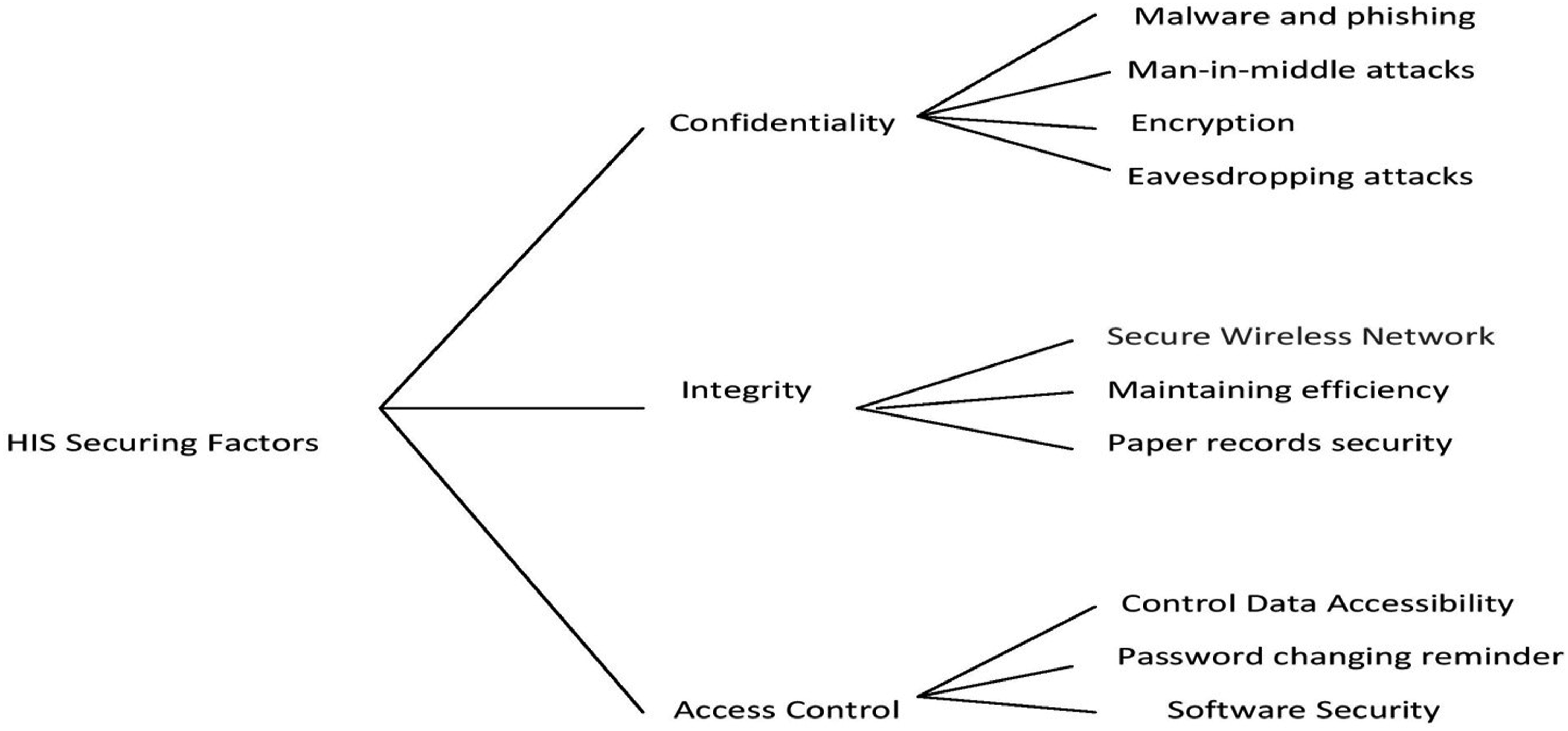
Confidentiality
In the context of healthcare, confidentiality is the obligation of the professionals to save the patients’ information that is confidential. Sensitive information of patients’ needs special confidentiality, and must be preserved by the health information management professionals.
a. Malware and phishing
Malware and phishing attacks invade the systems with the malicious code that compromises the security. Most of the malware and phishing attempts are engineered through emails.
b. Man-in-middle attacks
Man-in-middle attacks are also known as the brute force attacks. In this attack, the attackers trespass the data when the communication happens between the doctors and patients or data is sent for processing over the network.
c. Encryption
If the information is encrypted, then the data cannot be trespassed when data is transmitted to the system or the authorised users.
d. Eavesdropping attacks
These attacks are also known as the sniffing or snooping attacks. In such attacks, the attackers steal the data when the information is transmitted over the network. Such attacks cannot be detected easily because no anomaly is observed in the network.
Integrity
Data should not be altered without proper verification of the users. Data integrity maintains the accuracy of the patient’s records, health summary, test results and other information of the patient’s over the lift-cycle of it. Healthcare information should be error-free and accurate and follow the latest security policies and procedure of the industry.
a. Secure wireless network
In the present context, almost all the healthcare organizations are providing free Wi-Fi to the patients and visitors. Since the network is always turned on and open to all, the HIS become even more vulnerable.
b. Paper record security
In the HIS, ignoring the security of paper records can result in easy access of data and its theft. Paper record security requires proper training of auditing staff; lack of training of staff is the main reason for the breaches and alteration of data.
Access control
Access control over the system is very important by the separate and frequently updated login information, identity verification and auto logs off after a period of time.
a. Software security
Software security also plays role in access control. Through the software vulnerabilities, attackers can enter the system and get control of the whole HIS. HIS software should be up to date with current patches. If the software is not updated timely, then the system runs with a high risk.
b. Hardware security
When hard disk of the system is changed, then the disk should be properly disposed of. If the hard disk is not properly disposed of, then the data can be easily recovered. The company should implement proper hardware protection devices - and these include the hardware protection such as HP, IBM, etc.
c. Password changing reminder
To protect the system from the unauthorized access, one should set a reminder for changing the password of the system. The alarm setting is done on the software, which creates a sound or sends a message to the authority to change the password after a time limit.
Methodology
This section deals with evaluating and prioritising the performance of various factors for Securing Healthcare Information System. Prioritizing the securing factors provides a systematic way to the security experts of the hospital management to design a secure healthcare information system. Authors’ contribution to this study is the quantitative analysis of factors’ performance in securing the healthcare information system with the help of MCDM. MCDM is used to calculate the results with validation and accuracy.
Fuzzy AHP TOPSIS
AHP is the most widely used MCDM technique for assessing the weights of factors. Fuzzy-AHP uses triangular fuzzy numbers instead of crisp values for calculating the weights of factors. The authors used here F.AHP.TOPSIS integrated technique for ranking the factors as discussed in Figure 2.10,11 The authors have designed a hierarchy by the help of experts and applied the F.AHP.TOPSIS on it.
The fuzzy AHP.TOPSIS technique is particularly well suited to solving group decision-making problems in fuzzy environments.
27
Fuzzy AHP.TOPSIS techniques were used to estimate the feasibility of the whole weight collection process. The sequential procedure of the fuzzy AHP.TOPSIS methodology depicts on Figure 3. Working of Proposed framework for HIS security.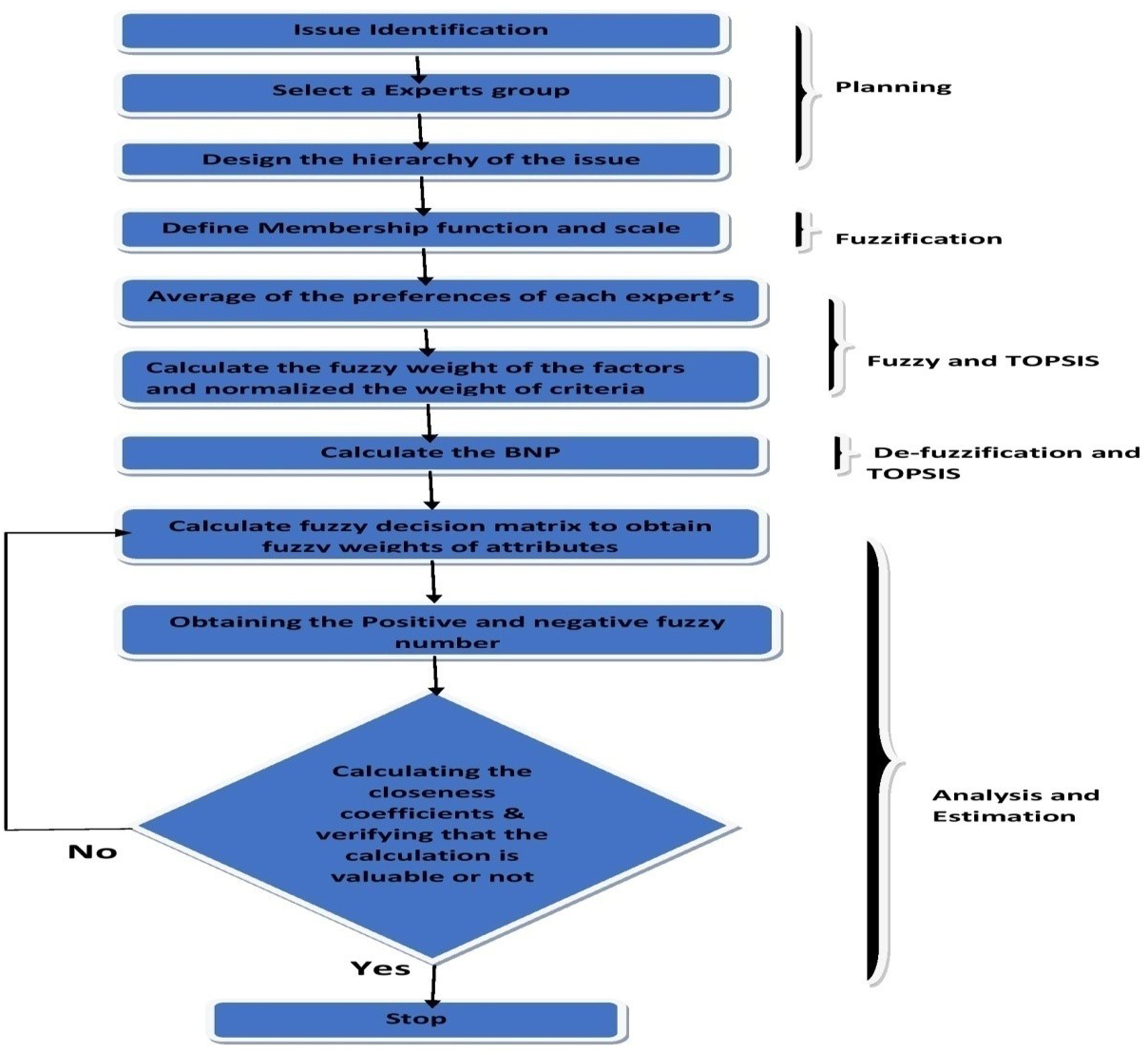

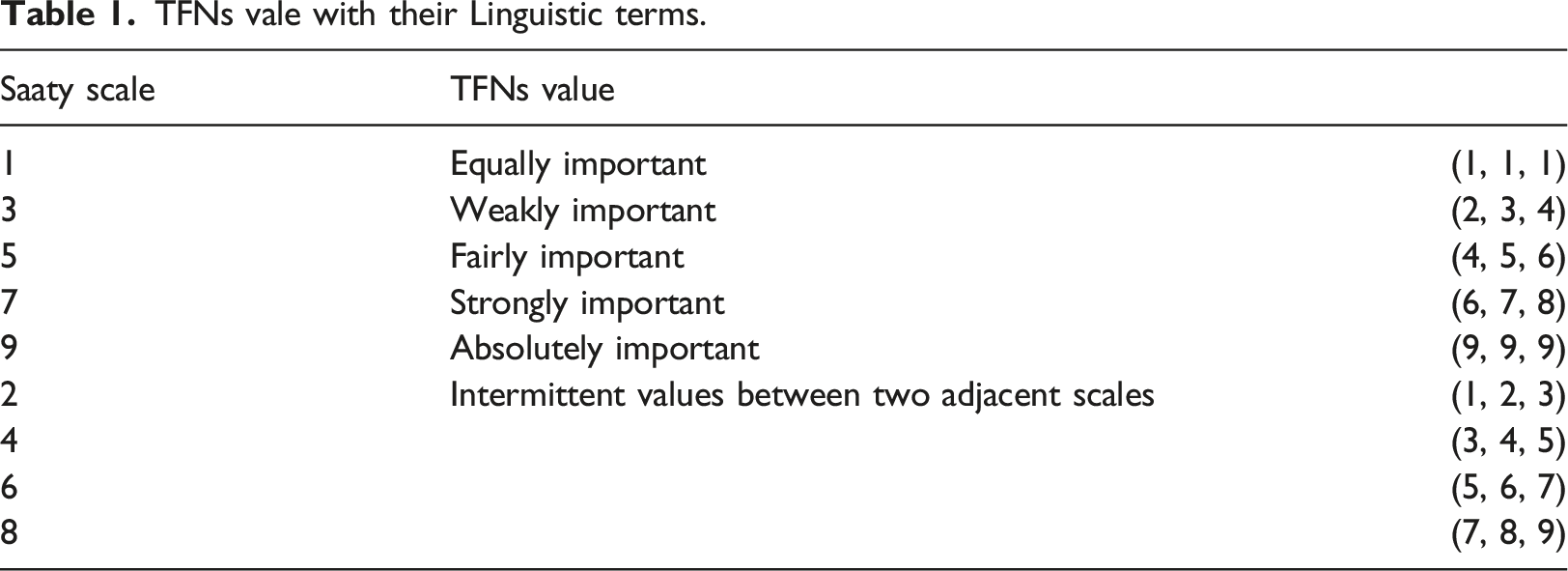
TFNs vale with their Linguistic terms.
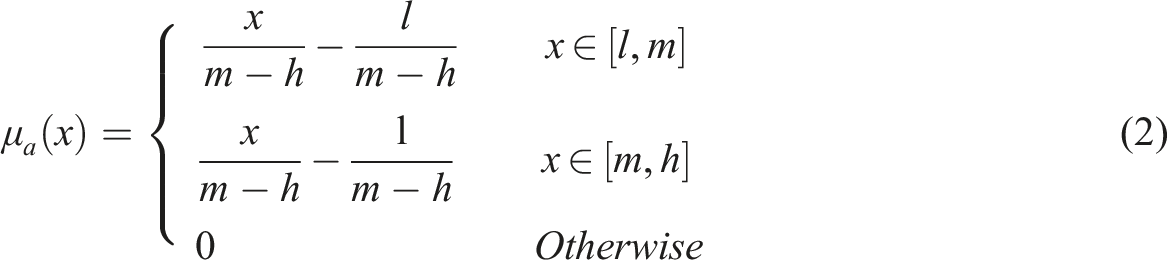
In Figure 4, Triangular fuzzy number.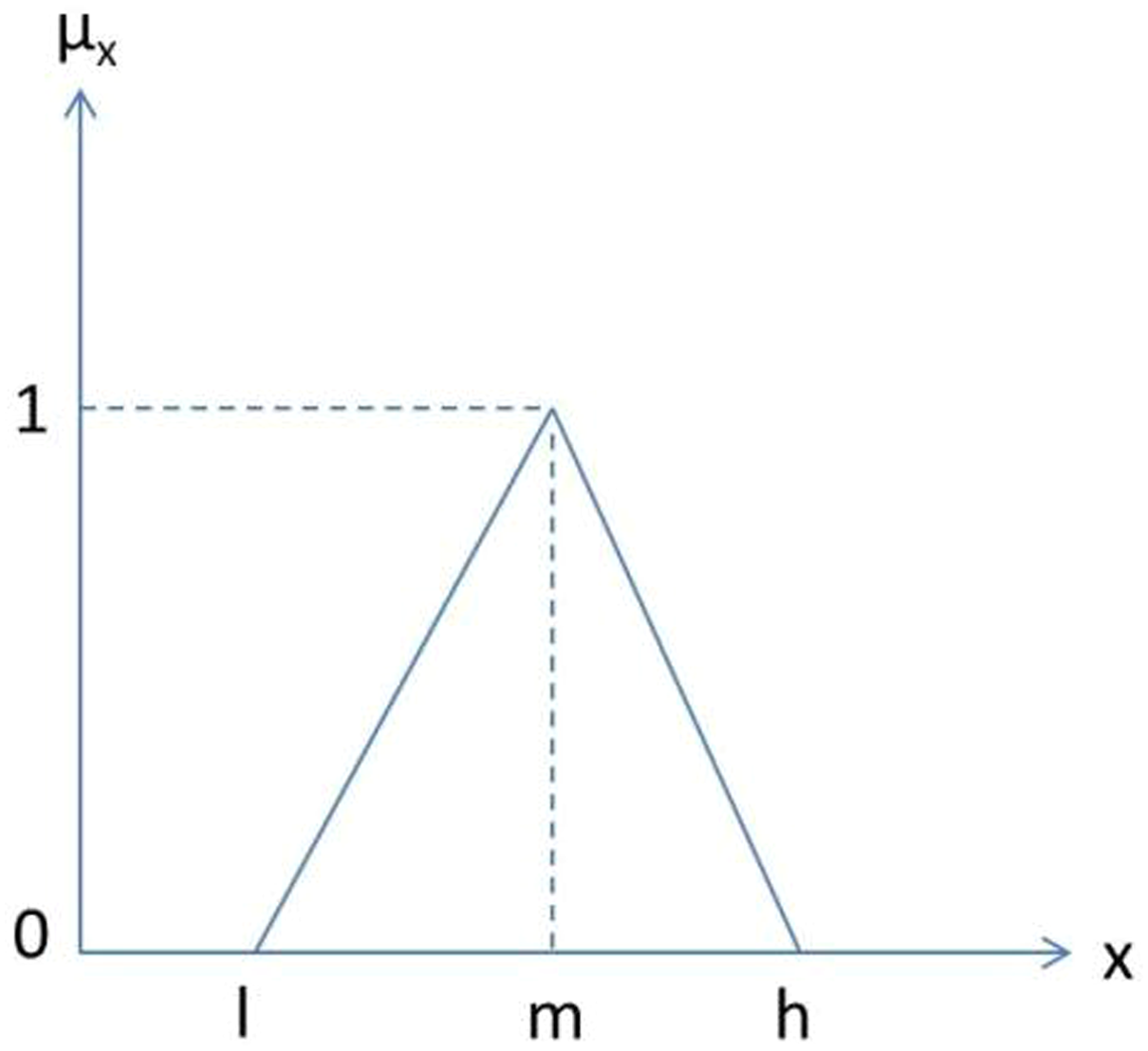
With the help of equations (3)–(6), the linguistic terms are converted into precise Triangular Fuzzy Number (TFNs).
where 


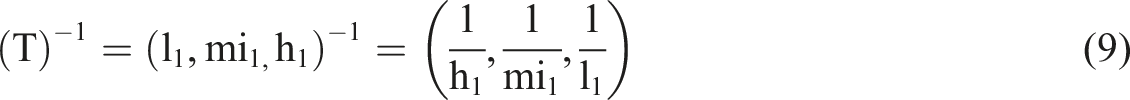
By the above situation, assume that there are two TFNs- T1 and T2, T1 = (l1, m1, h1) and T2 = (l2, m2, h2). Further, equations (7)–(9) help to aggregate TFN values.

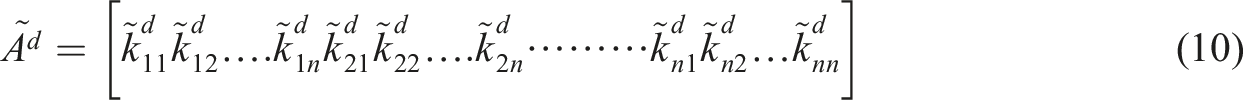
The average of the preferences of each expert is evaluated by
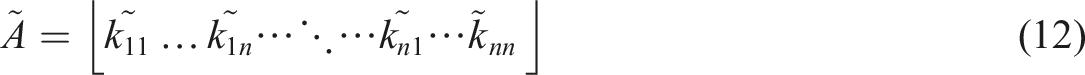
We obtained the geometrical mean and fuzzy weights of all factors that were achieved by as follows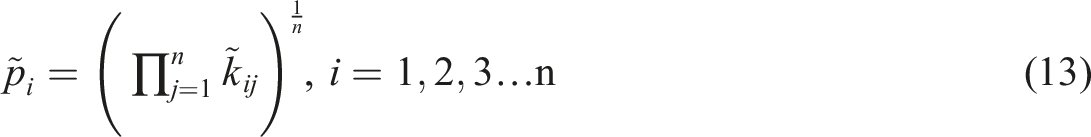
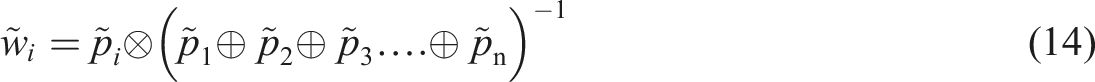
After that, average weights were calculated and normalized weight of criteria was achieved by as follows




Distance from 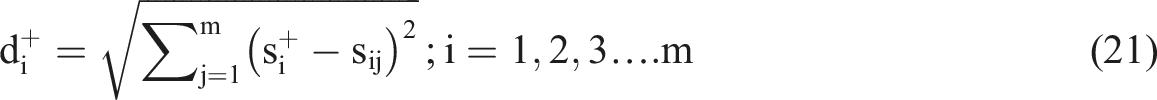
Distance from 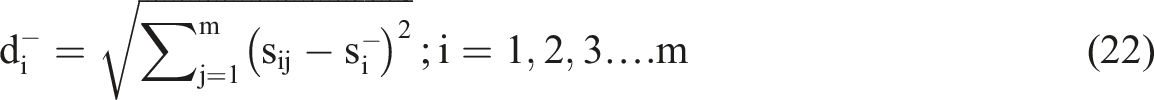
By the help of the above steps, the authors evaluated the performance of factors for securing the HIS by using F.AHP.TOPSIS approach. We have evaluated the performance of the factors for securing the HIS in the next section.
Results and outcome
Performance evaluation of various factors for securing healthcare information system (HIS) quantitatively is very hard for the experts. For any calculation factors, identification is a vital task. If the factors are identified properly, then the calculation for the statement will be effective for any system. We used the F.AHP.TOPSIS integrated technique for ranking the selected factors and evaluated the performance of the factors for securing the HIS. F.AHP.TOPSIS is the best MCDM technique. 27
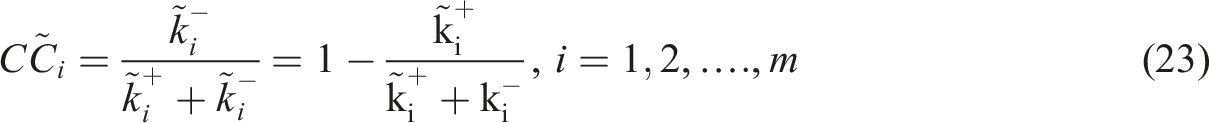
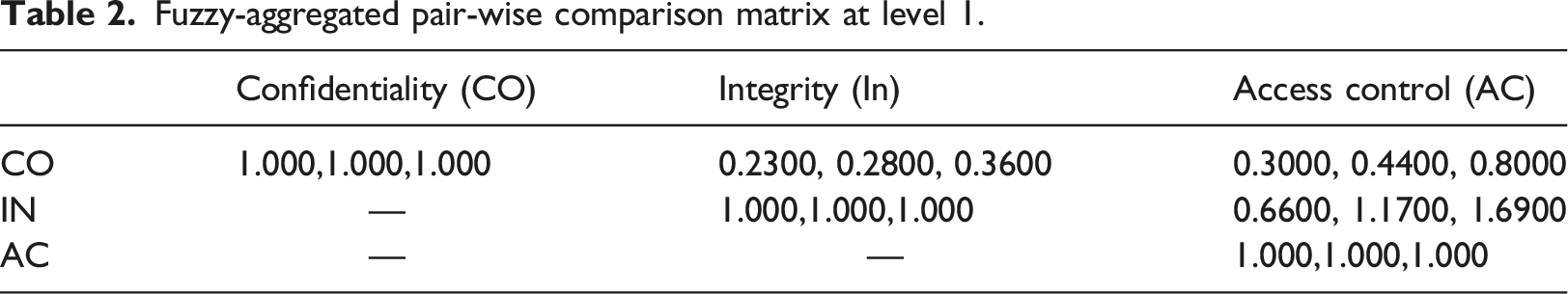
Fuzzy-aggregated pair-wise comparison matrix at level 1.
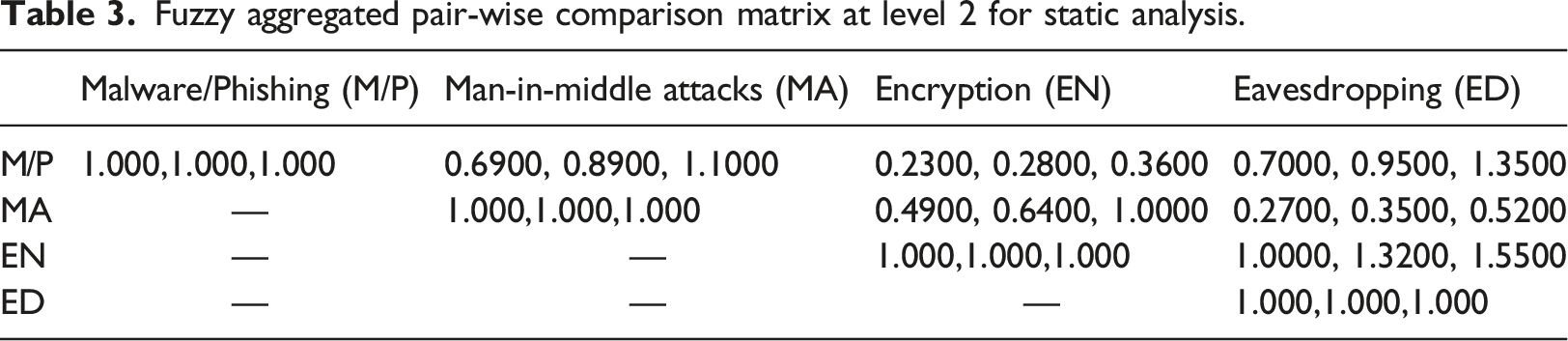
Fuzzy aggregated pair-wise comparison matrix at level 2 for static analysis.
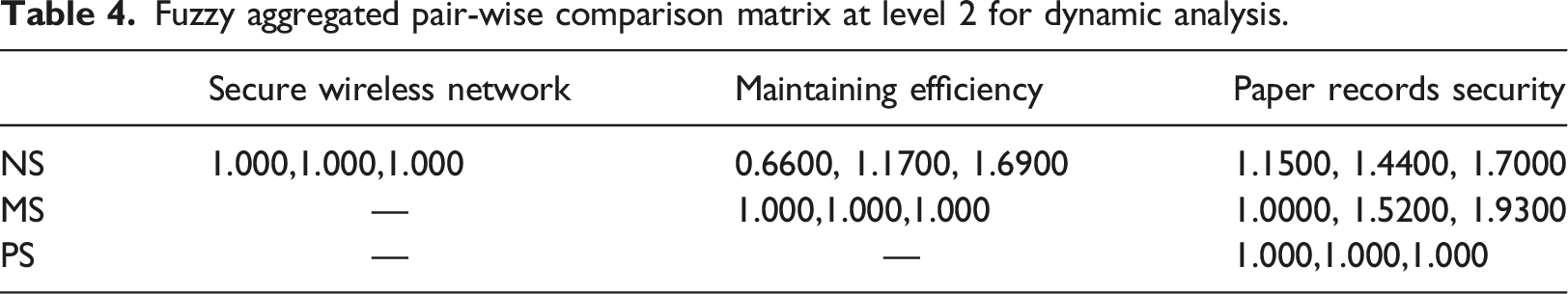
Fuzzy aggregated pair-wise comparison matrix at level 2 for dynamic analysis.
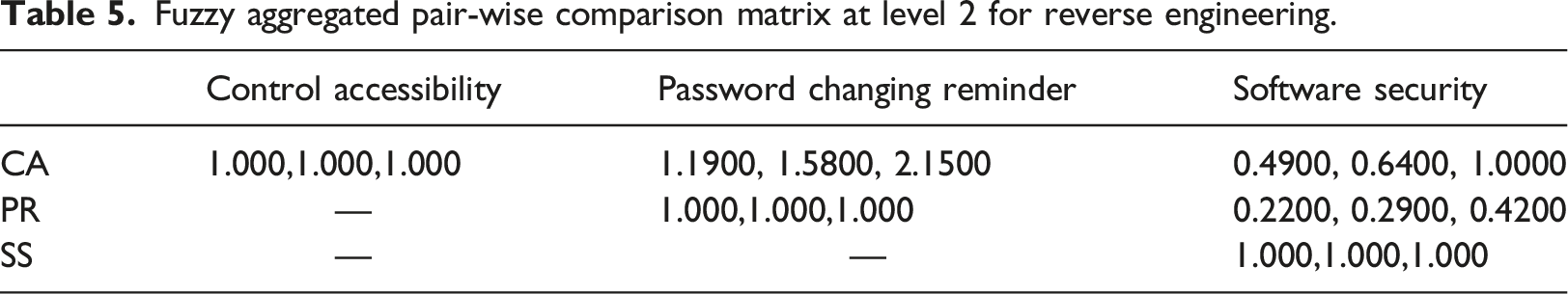
Fuzzy aggregated pair-wise comparison matrix at level 2 for reverse engineering.
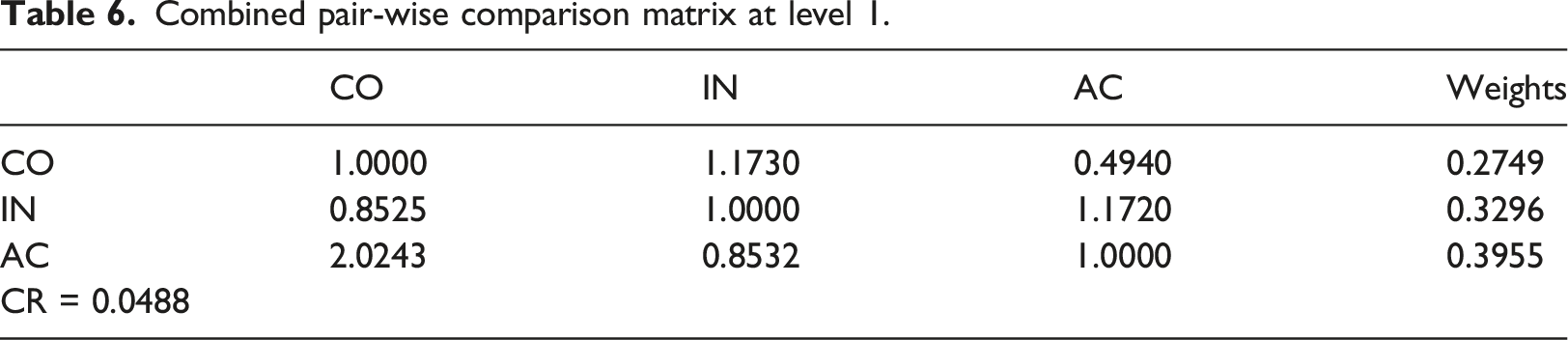
Combined pair-wise comparison matrix at level 1.
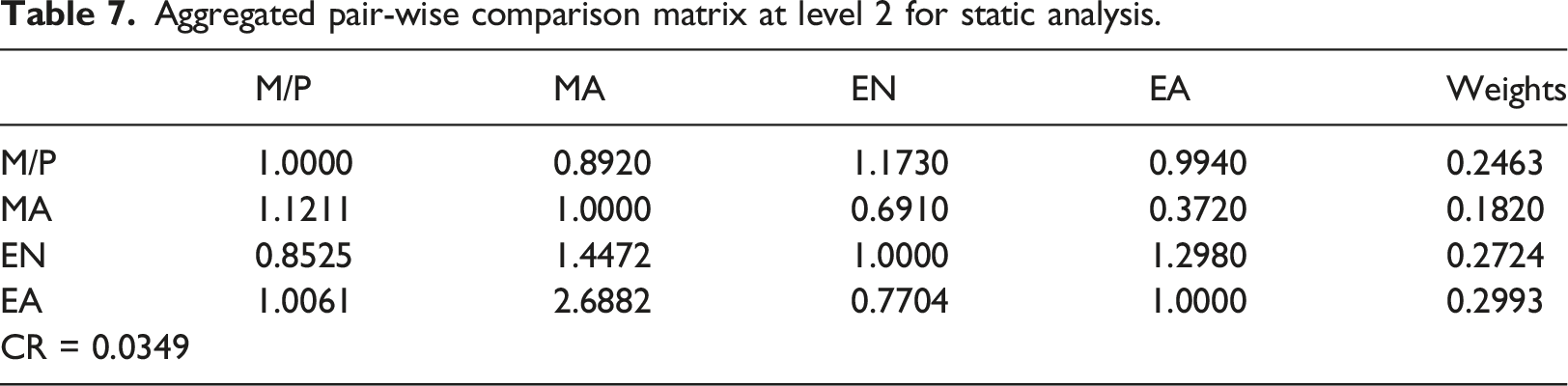
Aggregated pair-wise comparison matrix at level 2 for static analysis.
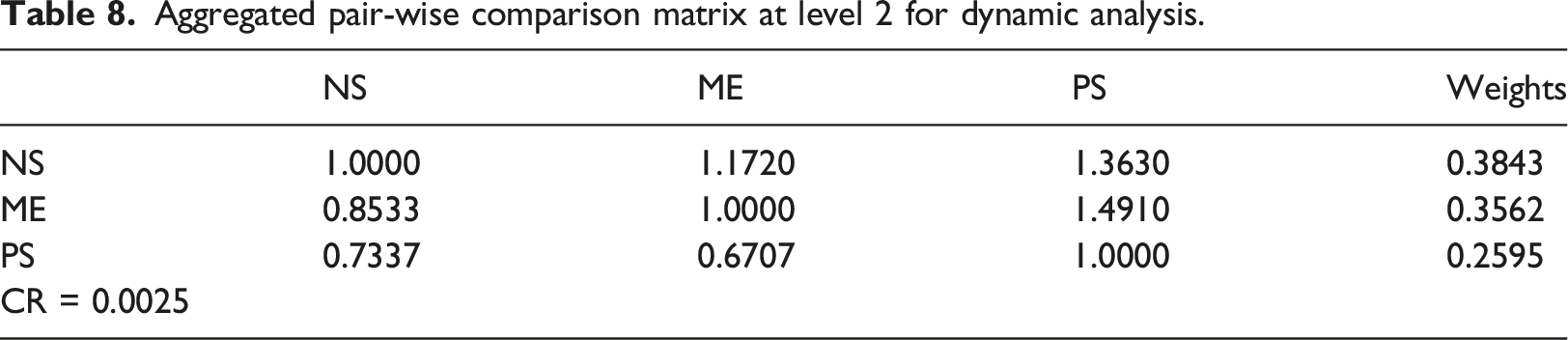
Aggregated pair-wise comparison matrix at level 2 for dynamic analysis.
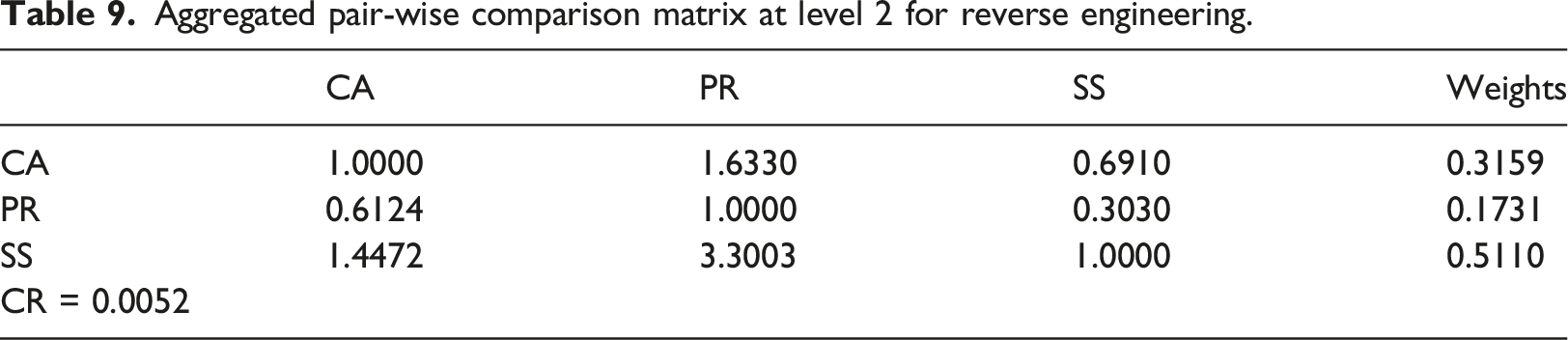
Aggregated pair-wise comparison matrix at level 2 for reverse engineering.
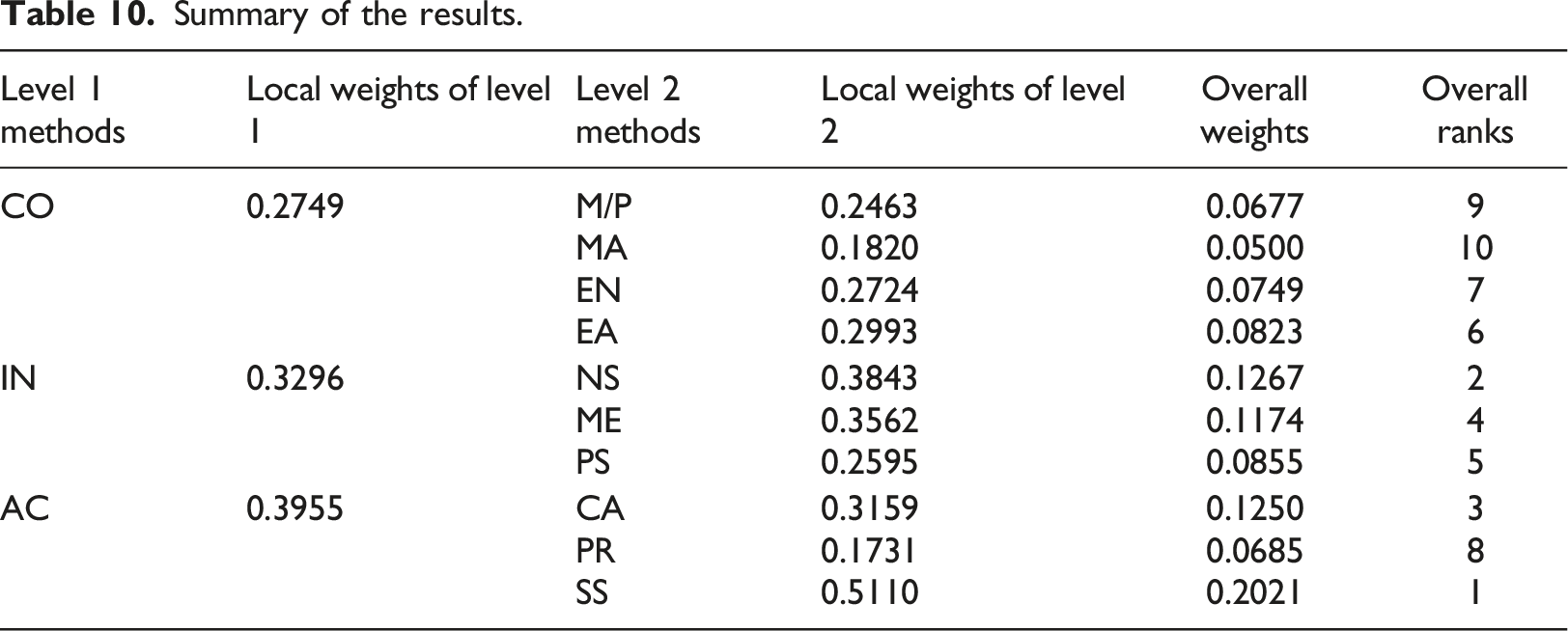
Summary of the results.
Subjective cognition matrix.
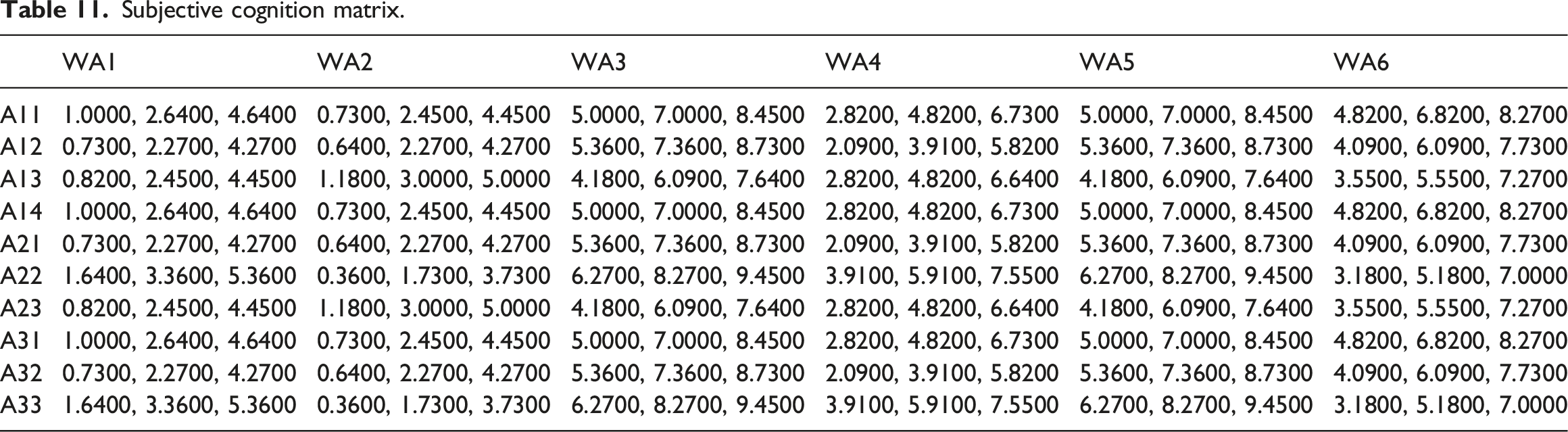
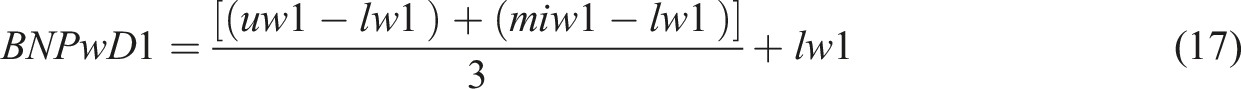
Weights of all the factors at different level are calculated and displayed in the Tables 6–9. 29 The weights show the performance of factors for securing the HIS. With the help of step 4 and equations (14)–(16), the study obtained the Table 10 displays the aggregated weights of factors for securing the HIS. Based on the obtained aggregated weight, the authors assigned the ranks of each security factor. The highest weight of the factors obtains the 1st ranks and rest all. In Table 10 various security sub factors obtain the ranks based on the security level. In Table 10, Access control obtains the highest weight (0.3955) in level 1 and sub-factor of access control software security obtained (0.2.21) the highest weight, based on the obtained weight assigned the 1st rank to software security. Same integrity obtained 2nd highest weight (0.3296) for level 1 and sub-factor of integrity, network security also obtained the second highest weights (0.1267), so we assigned the 2nd rank, control accessibility based on weight (0.1250) obtained 3rd rank, maintain efficiency obtains 4th rank based on weight (0.1174), paper security obtain 5th rank based on obtained weight (0.0855), eavesdropping obtain 6th rank based on weight (0.0823), encryption obtain 7th rank based on weight (0.0749), password changing remainder obtain8th rank based on weight (0.0685), Man in middle attacks and malware/phishing obtain 9th and 10th rank based on weight (0.0500) (0.0677), respectively. The authors have evaluated the performance of factors for securing the HIS with the help of criteria. We opted for six-hospital information systems of the hospitals in Varanasi to evaluate the factors’ performance for securing the HIS. Here WA1 to WA6 are alternatives that represent the HIS of different hospitals. Table 11 is constructed again with the help of equations (4)–(9). By using the equation (15), we calculated the normalized weights of the matrix.
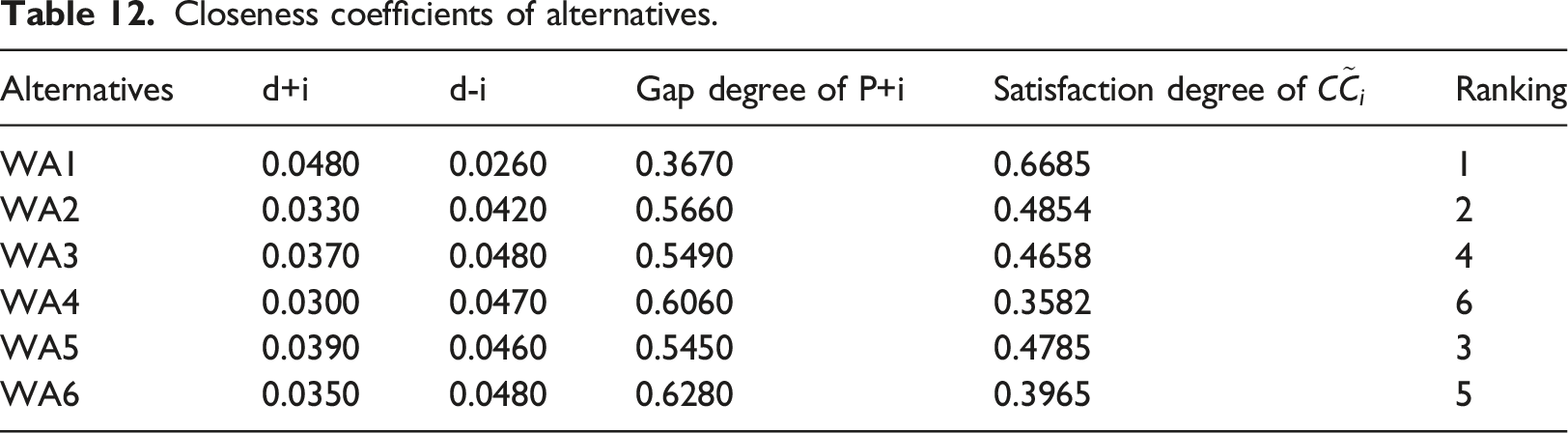
Closeness coefficients of alternatives.
Sensitivity analysis
For the checking the accuracy and validation of the results, sensitivity analysis is the most essential procedure. In the sensitivity analysis, we checked their results by changing the variable used in the analysis.
10
We have used here 10 experiments for sensitivity analysis; we opted for 10 experiments because 10 factors were selected at the last level. In our observation, each factor’s sensitivity weight is different, other factors’ weights; closeness coefficients are same at experiment time. The calculated sensitivity results analyses are displayed in Figure 5. Sensitivity analysis.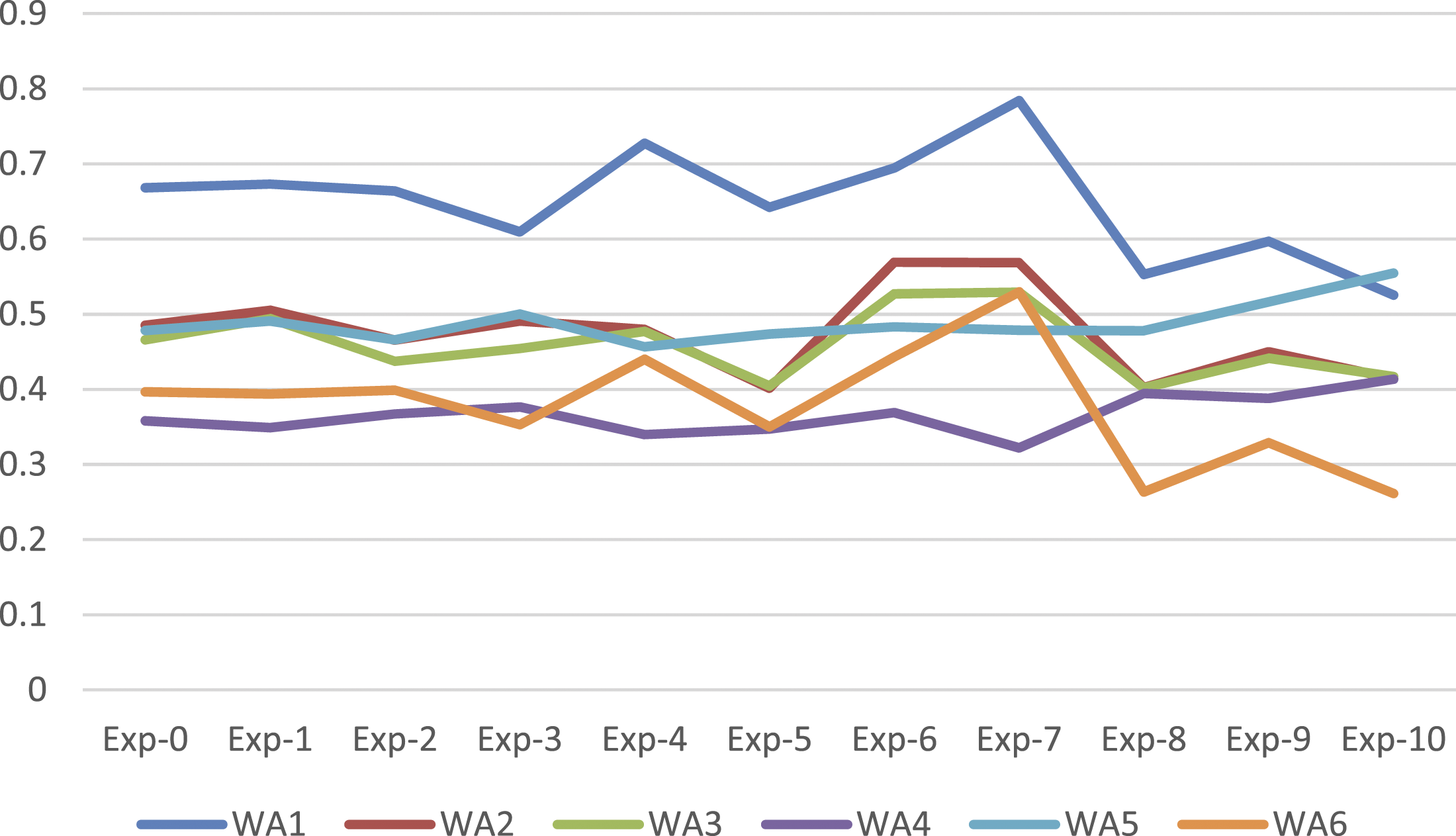
As per the closeness coefficient in Table 12, Alternative −1 obtained the highest weight. Furthermore, as per the sensitivity analysis in Figure 5, we found that WA1 obtained the highest satisfaction degree in all the 10 experiments.
Comparison with the classical AHP-TOPSIS and fuzzy weighted average method
Some authors have performed the comparative study with traditional and classical AHP, TOPSIS approach with Fuzzy AHP, TOPSIS approaches and find that Fuzzy base MCDM and TOPSIS approach obtains better results. 31 The authors have cited some references in this section. Akin and Guzin (2007), state that the Fuzzy Analytical Hierarchy Process (FAHP) is a synthetic extension of the classical AHP method when the fuzziness of the decision-makers is considered. 32 M.H. Behzadi (2015), has performed a comparison study of fuzzy AHP and fuzzy TOSIS approaches in math teacher’s selection. 12 Rajeev et al., (2020), applied fuzzy-based AHP-TOPSIS procedure for evaluating the impact of harmful factors of HIS and comparing their results with other prioritized methods. The authors found that the fuzzy AHP-TOPSIS provides better results than the ones obtained by using traditional techniques. 10 Similarly, we have also compared our experiments’ results with the other methods discussed here.
We compared the results that were obtained by using the Fuzzy Weighted Average method with the Classical-AHP_TOPSIS method. To the results verification, the same data set was used by the authors in the traditional AHP TOPSIS and Fuzzy weighted average method. And evaluate the results of both methods and compare them with Fuzzy AHP.TOPSIS method.10–14 They compared the results of the methods depicted in Figure 6. From the comparison, we observed that F.AHP.TOPSIS generated better results than the Fuzzy Weighted Average and Classical AHP.TOPSIS method. Comparative analysis.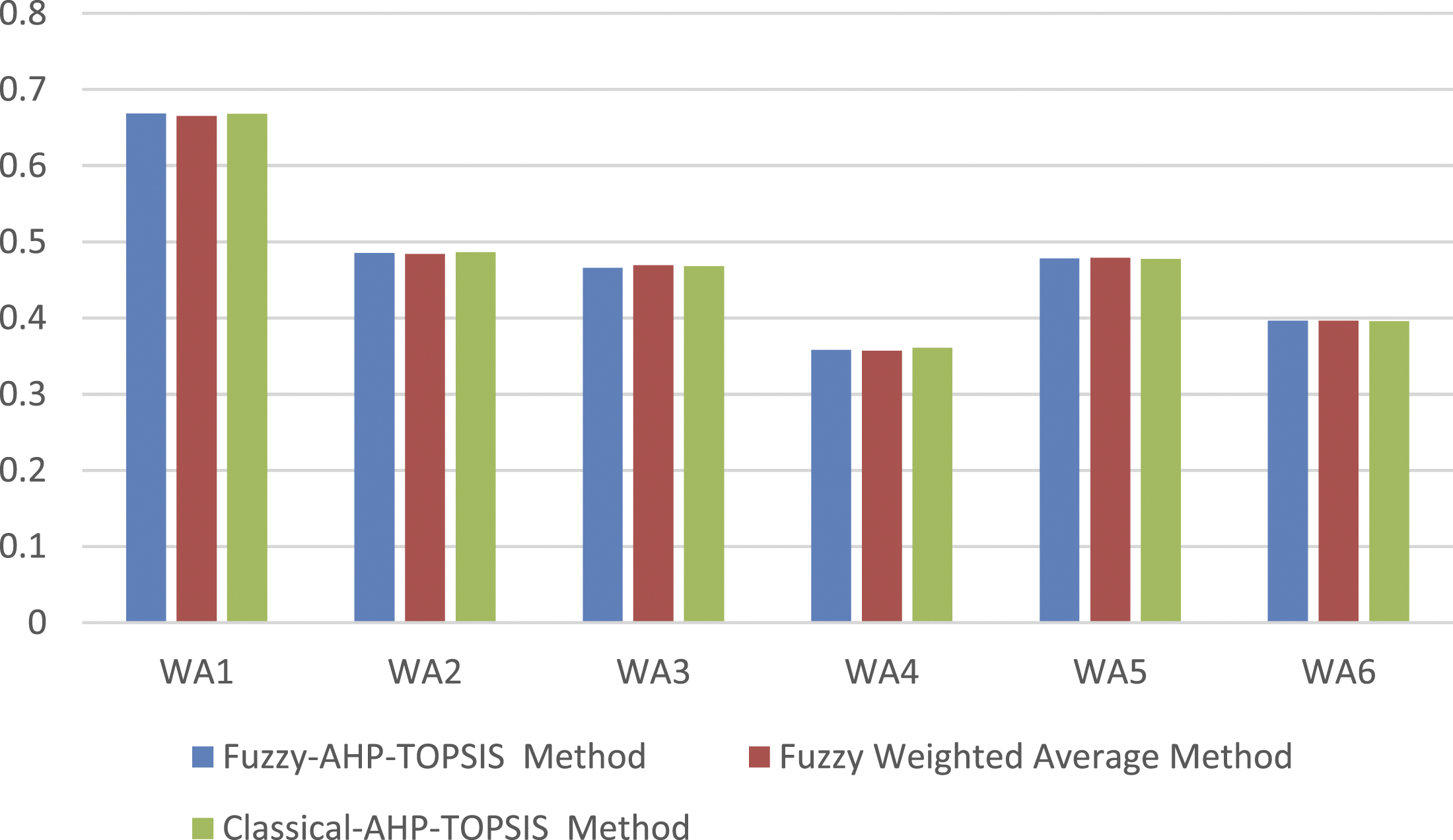
The authors employed fuzzy AHP-TOPSIS commonly for selecting the most appropriate security factors. The authors discovered that all these methods are stochastic processes to deal with some uncertainty, but the major advantage of fuzzy AHP-TOPSIS is that it performs an optimization with the Max-Min function to maximise the desired results and minimize potential threats, whereas traditional and classical AHP-TOPSIS and Fuzzy average weighted only determines a deterministic result.
Conclusion
In this article, we have discussed the various factors that are crucial for securing the HIS. We have found three main factors that significantly affect the security of HIS. These factors show that healthcare information system security is under risk. In Figure 2, the authors have constructed the hierarchy of the factors and sub-factors in different levels. These factors and sub-factors affect each other and depend on each other, as discussed in the result analysis. Given the rapid pace of digitalisation in the Healthcare sector, the HIS-staff information, patients’ information, report results, and many more essential and sensitive information will be stored and transmitted by the hospitals for processing in the near future. When healthcare sends or stores the data over the network, then the attackers trespass on the data and access or alter the sensitive information. The ranking order of performance of factors for securing the HIS obtained by our analysis is
To achieve the intended goal, we identified and classified the various factors and sub-factors, which create the loopholes in the HIS. Thereafter, we applied the F.AHP.TOPSIS technique for assigning the ranking order. Then, we validated the accuracy of the proposed technique. Results of the F.AHP.TOPSIS technique will help the security experts to develop more secure HIS. The Findings of the proposed study can be summarized as: • By using our study’s results, the security experts can design and find their ways to make more secure HIS. • According to our analysis, Access control and software security are the most prioritized factors. Hence, the security experts and researchers need to focus more on these factors for future research. • We have opted for three main factors which affect the security of HIS at every level. By using our methodology, the developers can evaluate the performance of factors for securing any HIS.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: We deeply acknowledge Taif University for Supporting This research through Taif University Researchers Supporting Project number (TURSP-2020/231), Taif University, Taif, Saudi Arabia.
