Abstract
Social media has enabled information-sharing across massively large networks of people without spending much financial resources and time that are otherwise required in the print and electronic media. Mobile-based social media applications have overwhelmingly changed the information-sharing perspective. However, with the advent of such applications at an unprecedented scale, the privacy of the information is compromised to a larger extent if breach mitigation is not adequate. Since healthcare applications are also being developed for mobile devices so that they also benefit from the power of social media, cybersecurity privacy concerns for such sensitive applications have become critical. This article discusses the architecture of a typical mobile healthcare application, in which customized privacy levels are defined for the individuals participating in the system. It then elaborates on how the communication across a social network in a multi-cloud environment can be made more secure and private, especially for healthcare applications.
Introduction
Social network analysis (SNA) aims at understanding the underlying social structure in a social network by description, visualization, and statistical modeling. Social network data consist of various elements which can help to explore and visualize patterns found within collections of linked entities that also include people. SNA is now becoming a very active area of research, and many individuals and organizations are putting their efforts in this area. Many researchers1–4 have defined SNA as the methodology for examining the structure among actors, groups, and organizations in order to explain the variations in beliefs, behaviors, and outcomes. Hatala 1 also highlighted that the process to conduct a SNA mainly involves eight steps which include the following: determining the type of analysis, defining the relationships in the network using a theoretically relevant measure, collecting the network data, measuring the relations, determining whether to include actor attribute information, analyzing the network data, creating descriptive indices, and presenting the network data. Kietzmann et al. 5 describe the essential components of social media structuring, namely, presence, sharing, relationship, identity, conversation, group, and reputation. It has been observed that the description of the user identity can often be investigated by the thoughts, feelings, likes, and other subjective information if they are not disclosed directly. Tong et al. 6 have identified that a friend’s profile on facebook.com is a major source of personality evaluation for any given individual. An effective semantic analysis can provide an exploratory analysis about an individual by examining the profiles of his or her friends, his or her likes and posts, and so on.7,8
The use of social media is naturally diverse.9–13 For instance, many people use social networks to exchange information on healthcare issues. This is a significant use of social media platforms, which in turn asserts their growing presence in the healthcare domain. The utility of the use of social media is outstanding and so is the outcome when the procedures to use the social media for healthcare are in place. Griffiths et al. 14 have elaborated that in such systems, individuals take the responsibility to provide up-to-date information about their health either by the use of some system or by interventions such as cognitive therapy, and some other researchers have also argued the same.15–18 Self-reporting systems can be applied where it is observed that the patient is not in a stable state, for example, those patients observing the bipolar disorder or the like. Healthcare data are kept confidential and people are informed as to where and how to upload data. Over the years, many large data sets have been collected which can be used for experimental purposes in subsequent research.
Healthcare is a two-sided process between patients and medical professionals. As far as the platform used is concerned, it supports the interaction among the patient, doctors, or community health services. In the two-sided healthcare system, a network of components is associated with a number of platforms. Roughan et al. 19 and Papadimitriou et al. 20 have addressed those significant issues such as inter-clinic communication, data privacy, and information synchronization. In the current trends, many public and private organizations deal with cloud-based healthcare systems and social networking is changing people’s perspective toward health-related issues. Social networks have emerged over time as a great platform for sharing medical opinions, and it has been noted that online communities can develop quasi-professional knowledge about the health status of the communities in general and about the individuals in particular. The topic of preparing effective communication guidelines for online communities and distance learning education have been addressed in several studies,21–23 where a number of improvization methods are identified to make the communication more effective in an environment where the meaningful information can be extracted from the communication.
The orientation and application of a broad range of new e-Health applications help improve the exchange of health information between consumers and providers for the purpose of promoting healthy behaviors. Kreps and Neuhauser 24 have argued that the new and exciting health information technology (HIT) gave responsibility to the designers of e-Health systems to design such tools that are capable of providing the right information irrespective of the time and location. The role of communication is vital in the improvization of public health, and it is important to appreciate that understanding human communication requires the strategic design, monitoring, and responsiveness of an e-healthcare application. Higgins et al. 25 have specified certain behavioral factors that contribute in problematic lifestyles including alcohol. Ylimäki et al. 26 have identified that the adaptation of e-healthcare systems to improve the lifestyle in order to decrease health-related problems has been very slow. e-Health communication has made it attractive by providing databases to compare data by other providers, and it was identified that the number of individuals using healthcare systems is increasing but the increase is not very robust. According to a recent study, 24 it has been observed that Americans go to the Internet first, rather than to a provider, for health information. The authors have further claimed that HITs should have an interactive feedback system and must be designed to work effectively and efficiently.
The advent of wearable devices has enabled a wireless access to the healthcare data to help the medical professionals to save time and overcome data latency issues, but there is a tendency to wait for these technologies to become mature before they are used. Sensor networks are being used to monitor human activities, which can be broadly divided into the areas that relate to medical and non-medical applications. Wearable devices have been used to check a patient’s temperature, blood pressure, and so on, and implanted devices are used to check cardiac arrhythmia, brain liquid pressure, and so on. Applications of wireless sensor networks in the medical domain primarily address the monitoring of a patient’s health condition. Wireless sensor networks are becoming popular, and they are being adapted rapidly. For example, they are being used to capture the data of elder patients for long-term treatments. Such devices and wireless sensor networks have certain cybersecurity vulnerabilities which can be categorized as follows: privacy, security, buffer overflow, exposure of sensitive data, broken session management and authentication, injection vulnerabilities, security misconfiguration, and legal issues.27,28 Research in the healthcare application of wireless technologies has been performed worldwide in many domains and also in many dimensions.
To that effect, Sezgin et al. 29 have studied the possibility of using mobile healthcare applications and the user perception about these applications. Li et al. 30 have studied the adaptation patterns of wearable devices for the healthcare. It has been observed that the risk to adopt a new wearable device is higher in the beginning but with the passage of time, the trust on the device improves and further grows when the associated risks are deemed to be less than the associated advantages. Guo et al. 31 have reported that the privacy deficit is a major factor in determining the goodness of a healthcare system and recommend that healthcare devices should be secure enough to provide only a restricted access to the defined individuals. The authors also hail the concept of considering the geographical diversities of human behavior before recommending suitable devices. Nurses can use radio frequency identification (RFID) to identify patients in intensive care units (ICUs). Wireless devices are being used for real-time monitoring of patients’ electrocardiography (ECG) signals, and the doctors have access to the latest and always up-to-date records of patients using multimedia messages. Furthermore, the adoption of mobile healthcare is attractive considering such factors as patient behavior, subjective norm, personal innovativeness, perceived behavioral control, and behavioral intention.23,32
As is the case for wireless sensor networks, healthcare applications are also vulnerable to active and passive attacks. The attackers can cause much harm to the process by malicious attempts such as data modification, impersonation, eavesdropping, and replaying. The primary purpose of these attacks is to steal the patient’s data, which are not only valuable but also private and sensitive. In some cases, implanted medical devices are used to administer drugs (such as insulin), and attacks could lead to serious outcomes for the patient if the administration of drugs is compromised. If the security issues with the healthcare applications are not resolved in a timely fashion, the impact may be catastrophic and may also cause the rise of socio-technical problems. So, while designing socio-technical integration of mobile and other electronic devices with healthcare applications for the purposes of sharing patients’ data, information, and messaging, it is vital to incorporate system security, administrative- and physical-level security, and information security into such applications.
In this section, an introduction of the healthcare systems and its integration with social media platforms is presented. Possible challenges in such integration have also been elaborated on. Section “Related work” discusses some related works which have taken place in this domain. Section “Architecture of a healthcare model based on social networks” discusses the privacy concerns of healthcare models based on social networks, while section “Privacy concerns” elaborates on social media models. Section “Privacy and security” discusses the security issues while highlighting the mitigation-related work. Section “Conclusion” concludes the article with a summary of our findings.
Related work
In healthcare applications, SNA has been used to understand communication patterns between and collaboration of healthcare providers. Bae et al. 33 have identified that healthcare providers’ interactions contribute to the culture and knowledge of healthcare organizations. Without any interaction between professionals and patients, it is obviously not possible to share information between them. SNA can be used to study the interactions, as well as the performance of teams and organizations. Many researchers have used SNA in healthcare, especially in the context of hospitals, nursing homes, and clinics.34,35 To improve communication among healthcare providers, it is critical to find the optimal structure of communication under a certain healthcare setting. It has been observed that the operating rooms, the type of surgical specialty team, and facility layouts were critical factors contributing to the characteristics of inter-professional social networks.
In a study conducted in the United States, Hendryx et al. 36 studied the variability of access to healthcare across 22 major cities in the United States and observed that the access pattern to healthcare instruments and institutions is not similar in all the states. It was hypothesized that reported access to care is positively associated with the community social capital. Four different informatory resources were used for this purpose which include the following: Counseling and Testing System (CTS), National Institute for Health Care Management (NIHCM), National Profile of Local Health Departments (NPLHD), and a multicity media marketing database. The results can be seen to put forward the hypothesis that the social capital has a relation to the improvement in access to healthcare. The result of this study also supports the work done by other researchers. The study, however, could not identify how and why the social capital may help in improving access. The study argues that the social capital has a vital role to play if compared with the structural healthcare variables. Berkman 37 has elaborated that in the social network model, we have a personal cell which then extends step by step to different zones. Social networks may impact health by cultural differences, economic factors, and social changes. For example, it has been observed that people with no social support have the highest blood pressure. 38
Boukerche and Yen 39 and Hwang et al. 40 have argued that mobile healthcare is becoming popular and security and privacy are the critical issues. Security is one of the most important issues in mobile healthcare, and devices like bi-directional telephones are tested to overcome the issue of health parameters. Mobile healthcare has such features as the use of wearable devices (such as sensors and implantable devices), the mobility of users, data transmission, and remote medical control. There are many types of devices being developed to secure the data and maintain the privacy of patients. In a mobile healthcare system, a trust relationship can be defined between two nodes, that is, the sender and the receiver. In a simple trust model, if one node routes a packet of data over another node by choosing it among many others, then we can say that it has the highest level of trust placed on it by the sender. By routing data again and again over the same chosen node, the value of trust placed on that node is increased. It can then be argued with confidence that a trust-based multicast strategy can be a means of ensuring reliable communication and pervasive healthcare networks.
Developers in medical and computer networks have been working to develop some innovative ideas like the adoption of wireless sensor networks, which generally consist of body area networks (BAN) and personal data networks (PAN). Alemdar and Ersoy 41 have identified that the gateway subsystem has the responsibility of establishing a connection among the BAN and PAN subsystems and connecting them to a wide area network (WAN). As the magnitude of communication grows with the healthcare data, satellite communication may further help ease the communication load. By the virtue of cognitive disabilities that emerge fast in the elderly and chronically ill people, medical noncompliance has also been observed. The need to give high-quality medical care to new-born babies is also a matter of utmost importance. In order to address such issues, medical monitoring systems are needed, and more sensitive sensors can report in such cases more effectively. It is essential that the communication is noise free, which can be ensured by low transmission power and small-size antennas of wireless sensor devices; furthermore, the interoperability problem is observed when multiple sensing devices operate at different frequencies.
There are a number of security requirements to which a healthcare system must adhere. These requirements include privacy, data integrity, accountability, readiness, and access control, all of which have been advocated by several researchers.42–44 The security and privacy requirements of healthcare applications based on the social media are discussed in the following sections. In a recent work, Li et al. 45 have found that the leakage of information from the social network can still happen even when the user has adequate knowledge of the privacy controls with which he or she can effectively configure the privacy settings. Külcü and Henkoğlu 46 have argued that there should be more social awareness in ensuring privacy and that the non-existence of strict cybercrime laws is also a factor in reducing the resistance against the privacy concerns. It can be observed that mobile-based healthcare solutions are needed by the society, especially for the elderly patients who strive for movement in case of emergency. There is a significant improvement in this area, and the application of mobile devices, sensors, wearables, and cloud computing is being witnessed which has really assisted with patients’ healthcare needs. Along with the improvements in the clinical part of healthcare, the security and privacy issues of the data have increased and are of intense interest in recent research. Since privacy factors are of significance for the healthcare data, access control is required to be prominent and effective as well. The architecture and privacy controls are discussed next to overcome the research gap in this area.
Architecture of a healthcare model based on social networks
A healthcare model based on social networks includes the actors of the system, the system itself, the environment, and the communication between the actors and the system using the environment to perform a meaningful communication. The system is designed for the patient who is in continuous need of monitoring, where the off-hospital view and review of the patient are deemed necessary for the safety, and the recovery of the health, of the patient. The proposed model relies on the basic assumption that all the components are well integrated to react on a call and that the connections for communication are available. The physical infrastructure is readily available to respond when there is an emergency call. This article does not discuss the physical infrastructure of the system, and the communication aspects of the system are also beyond the scope of this research. In this article, we present a scenario where we identify how a patient will be treated in case of an emergency. The primary focus of this article is to discuss the privacy and security challenges and their possible mitigation framework in the healthcare system. There are several roles involved in such systems including the patient, the patient’s family, the system administrator, doctors, ambulance drivers, and paramedical staff. The communication among different actors is essential while the system is in execution. A flow graph of the activities and communication among the actors is presented in Figure 1. An overview of the system is presented in Figure 2 which illustrates the overall composition of the system by describing the possible ways of interaction among the entities of the system.
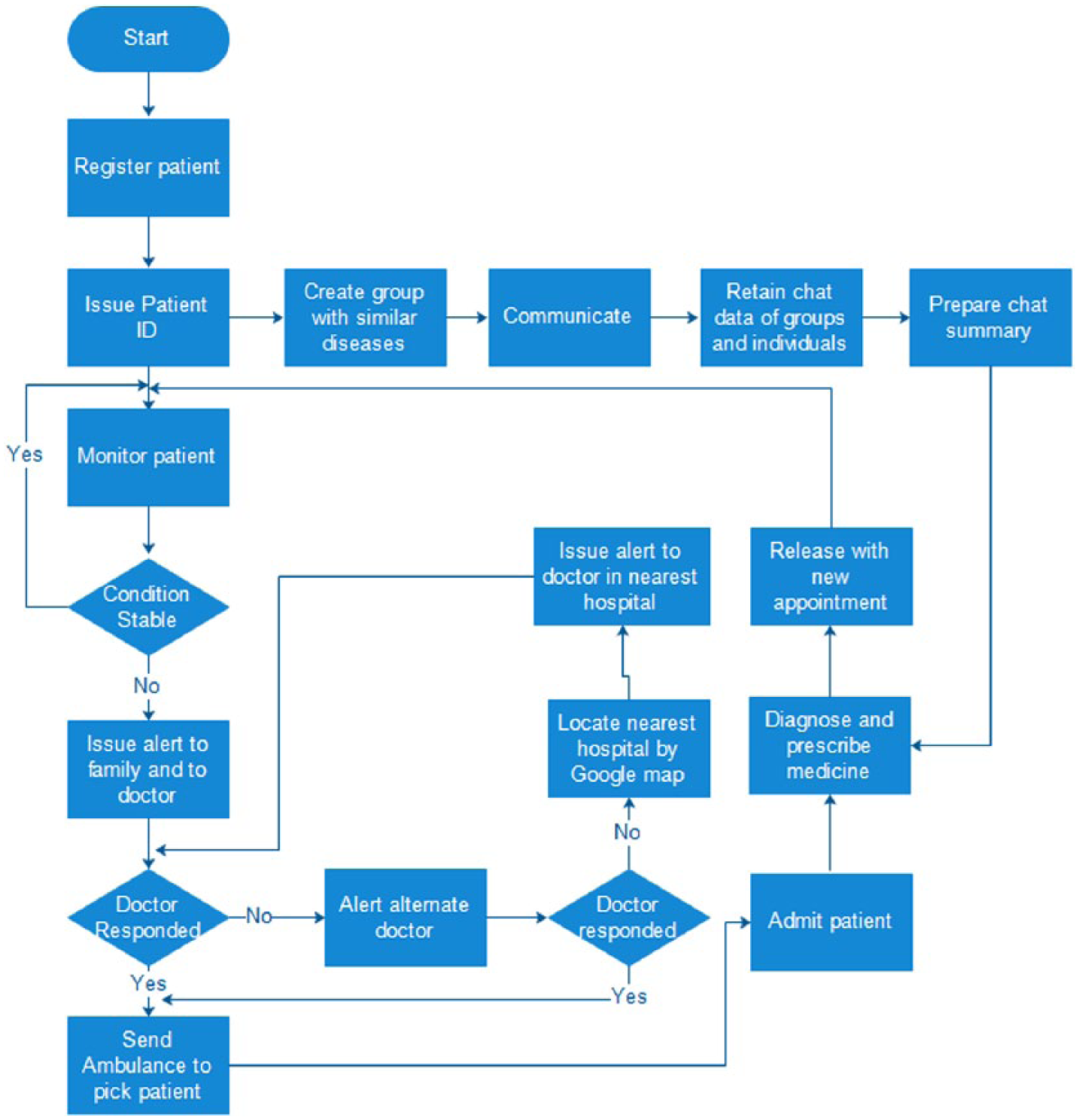
Flow of events for monitoring, registration, and medication of a patient.
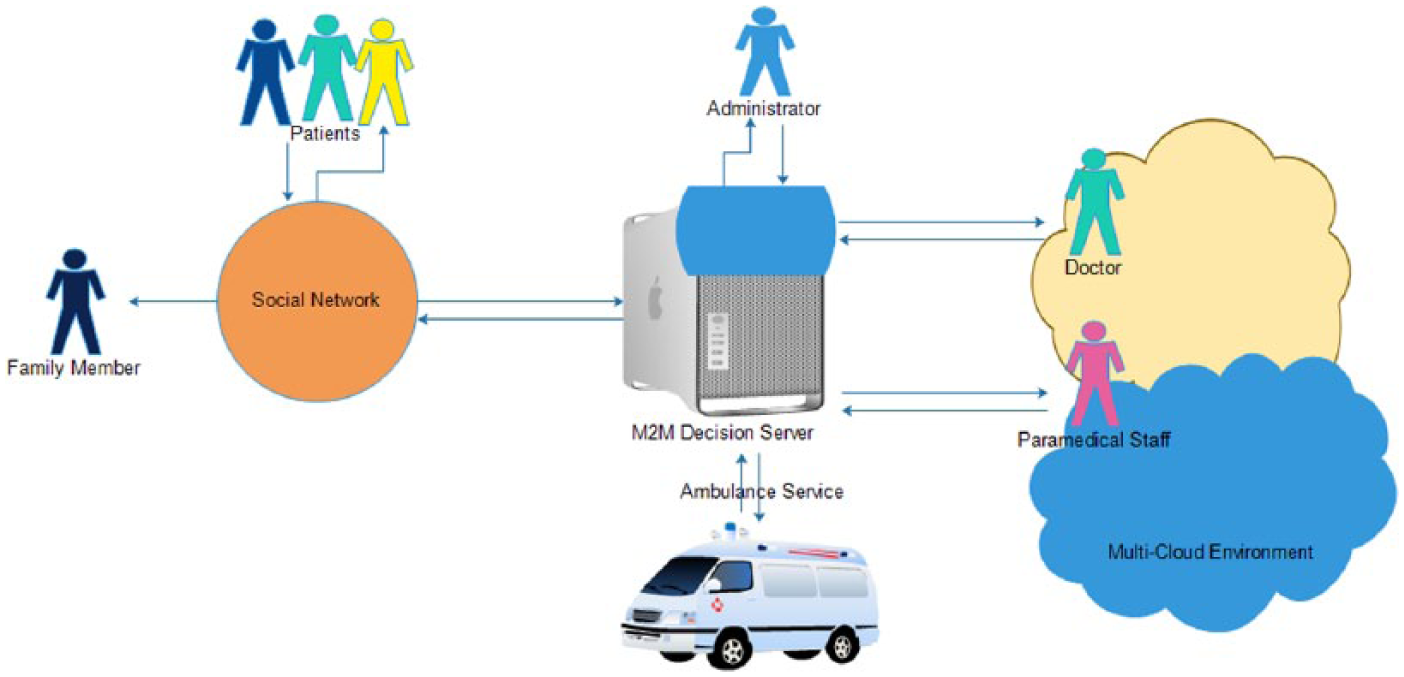
Overview of a healthcare system.
In a normal scenario, a patient is registered with the system through the social network application when brought to the hospital. The registration takes place in a specific group where the patient can communicate with other patients of the same illness and symptoms. The communication is logged for providing an input in the reports of the patient. Summaries of such communications are prepared by applying data mining techniques to extract meaningful facts from the communication. The patients are kept in a stage of continuous monitoring by applying bio-medical sensors and any irregularity in the healthcare data readings is immediately forwarded to the family and to the system. While the family member prepares the patient for transportation to the hospital, the system generates an emergency alarm to the designated doctor. As an immediate response is needed, the system generates an alarm to an alternate doctor in case the primary doctor does not respond within designated time. Even if the alternate doctor does not respond, the system is capable of locating other nearby hospitals using the Google Maps application. Once the doctor is located, the ambulance picks up the patient and transports him or her to the hospital where he or she is admitted and diagnosed in light of his or her medical history, test reports, and the summarized chats. The multi-cloud setup integrates/communicates within itself for data transmission from one cloud segment to another. The doctor may decide to keep the patient admitted or may decide to release him or her if the patient’s situation is found stable. However, regardless of whether the patient resides in or outside of the hospital, his or her continuous monitoring is done by the system. Several studies reported in the literature47–49 have implemented such an idea without the utilization of a multi-cloud environment by overcoming the risks in such a system.50–52
While it is well understood that the security concerns in a mobile-based solution is a major concern, the privacy issues are also vital to be addressed especially when it comes to healthcare applications. This paper focuses on the description of the privacy and security of the data when the healthcare applications are integrated with social networks in a multi-cloud environment to communicate and disseminate the information among specific groups on the networks. The information access control and privacy schemes for the social-media-based healthcare applications are discussed in the next section.
Privacy concerns
The utility of data is increased when the relevant persons in the domain use it. Some data or data sets are publicly available, while many other types of data have different levels of privacy. Medical data are considered among the most private types of data and access to this data is highly sensitive and can only be authorized to be accessed by designated professionals. Since, in this article, we address the healthcare data, we identify the possible security and privacy breaches and propose ways in which they can be mitigated against. In the context of social-media-based application data, the data can be classified into different categories, as shown in Figure 3.
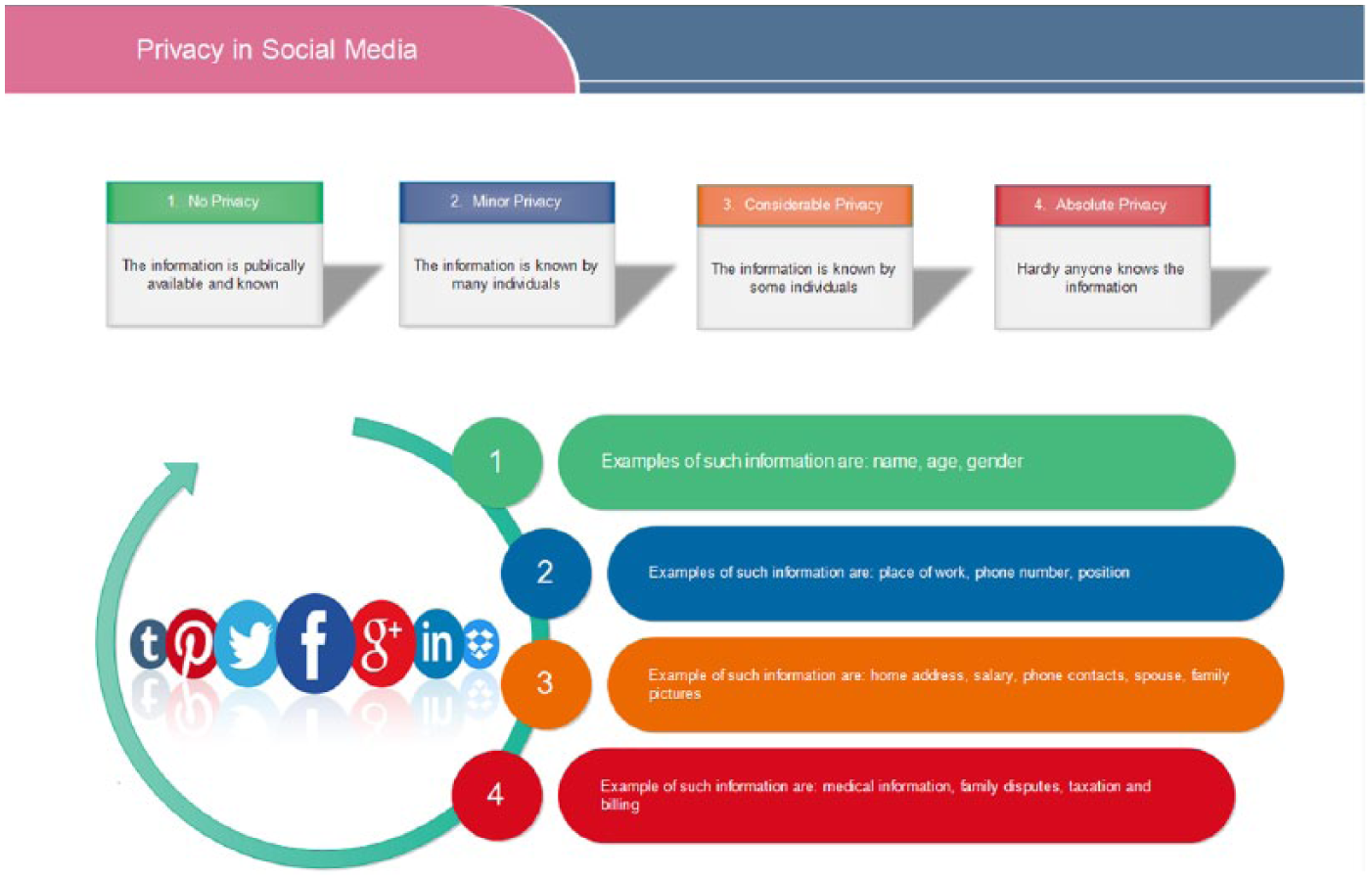
Privacy with respect to types of data.
Zhang et al. 53 have identified that the structure of online social networks (OSN) is such that it allows a user to flexibly share the information and in that effort to succeed, sometimes the privacy and security of the profiles and OSN are compromised. The threats to an OSN are diverse and can cause the security and privacy breaches if not addressed with high confidence. The potential challenges to security and privacy are discussed below.
User identification
The user identification syndrome is common in OSNs and is defined as a feature that helps the individuals recognize each other. For example, some social networks only allow viewing the first name of a user, while some others, such as
match.com
, assign an anonymous identification number to the user. However, the purpose of an OSN is compromised if the identification is not the real name but some arbitrary name or a number. Hiding the real identity of a user can be a solution in the friendship-seeking websites where the picture and other characteristics apart from the name also have a significant value, but in an OSN, like
Privacy of user’s personal space
The visibility of a social profile has a different type of presence on different social networks. Popular OSNs like facebook.com allow the user profiles to be seen and browsed unless the user has declared them to be private. However, once a user can have access to a private profile, the friends list of that private profile also becomes public, which in turn enables massive information-sharing. In healthcare-oriented social networks, the user’s profile will need to be kept private by default and the profiles of their friends and family will be kept private to secure the system from outside attempts of recognition.
Users’ communication
Along with the information that a user shares with the other OSN users, there is some default information-sharing that is done with the OSN provider. This default information includes the IP address, the time of connection, visited profiles, and the messages sent. It is also important to note that the digital footprints of any activity may also provide a ground for breaking into the personal profile of some individual, possibly making them a victim of cyberbullying, sexting, harassment, and/or Facebook depression. 54
Considering these aspects of security and privacy, the OSN and the user data are vulnerable to the attacks/information-seeking requests of unauthorized persons. Since the healthcare data are critical and required to be kept private, additional security and privacy filters are to be applied to ensure that the security and privacy of the system are not breached at any time and the data are consistently available with the prime focus of communication. For a healthcare system, we propose to have role-based security and privacy that is implemented with the concept of access control. As shown in Table 1, role-based access control provides an informatory look that describes the legitimate and illegitimate access controls based on the role of the user.
Role-based access control to implement extended privacy and security in healthcare-oriented social networks.
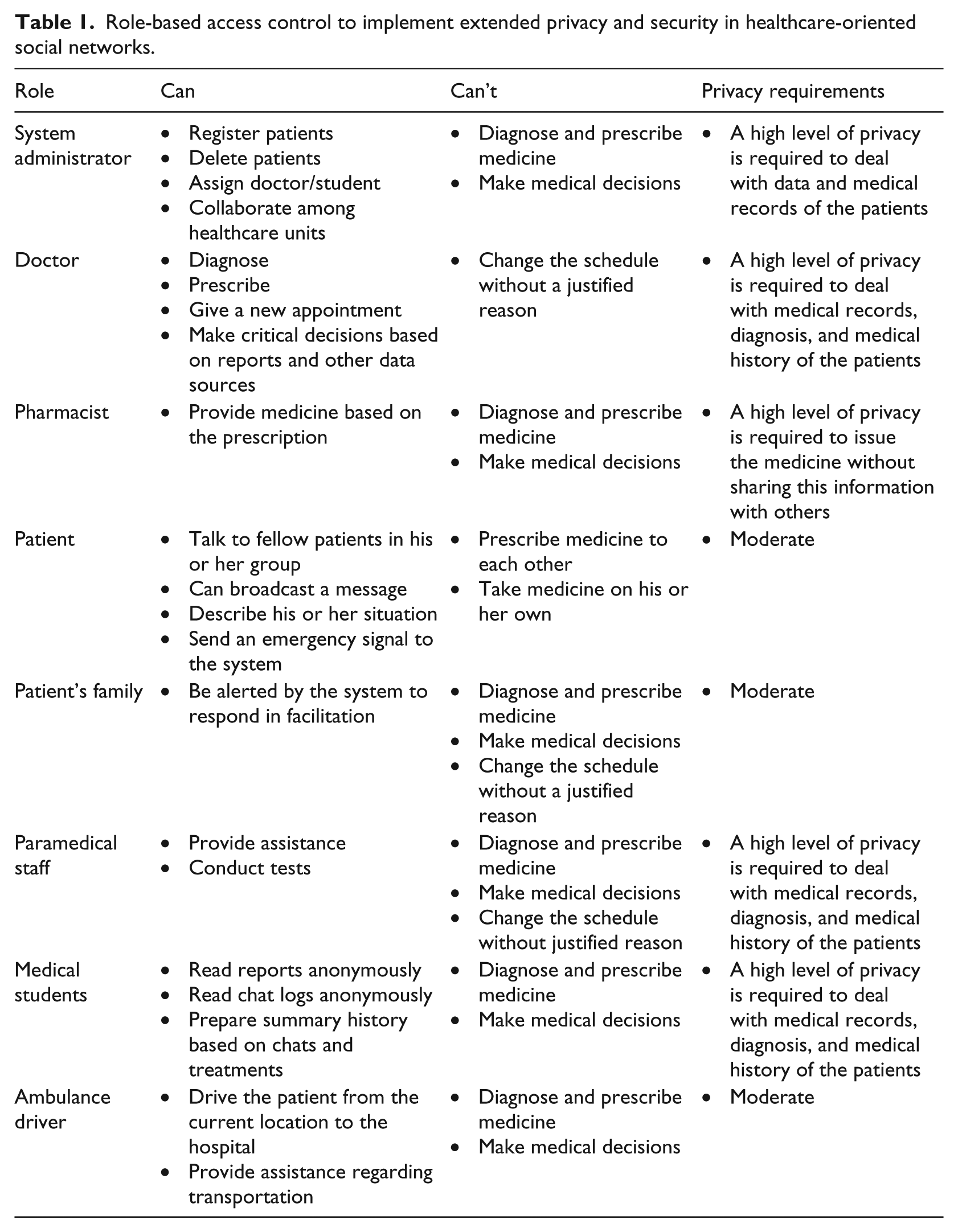
Table 1 shows what can be done (“can”) and what cannot be done (“can’t”) to elaborate the privacy policy. The “privacy requirements” column demonstrates the minimum privacy level that is required to make the system work effectively without breaching the privacy. In Table 1, it has been elaborated that the privacy requirements of each role are different based on the sensitivity of the information being handled by that specific role, for example, the system administrator’s role requires high privacy in conducting his affairs in accordance with the patient’s information, medication, stay, treatment, and communication. Consequently, the doctors and the pharmacists also need to observe a higher level of confidentiality in protecting the patient’s medical data. The moderate privacy requirement allows a patient and his or her family to share the information with the general public. If this minimum privacy level is observed within the system, it is expected that the system will no more be a subject of internal privacy breaches and more concentration can be given to handling the external attacks (if any).
Privacy and security
The concept of a privacy breach is associated with the intentional and un-intentional or conscious and un-conscious activities that may compromise the privacy of a patient. Although some measures can be taken to protect the privacy of data, the most significant part of privacy is yet to be implemented and ensured by the user. A significant privacy level can be achieved by communicating less and hiding the personal details and plans. For example, sharing too much information about our travel, visits, and personal likes and dislikes in public exposes us to the world where certain patterns about our lifestyle can be deduced with a significant level of accuracy. 55 In contrast to this concept, however, the attacks and exploitation of breaches in security of data are deliberate in nature and may come from outside. Security issues of the data are a superset of the privacy issues faced by the users on social networks. Some privacy concerns have been discussed in this article, and the mitigation strategies have been proposed while highlighting a number of security concerns. The privacy threats, however, can be considerably reduced if the communication of the user is not redundant and specific in nature. The specific communication provides the benefits such as follows: less data to be managed, no-unnecessary disclosure of data, and identity preservation (Table 2).
Security and privacy concerns for the data on social media.
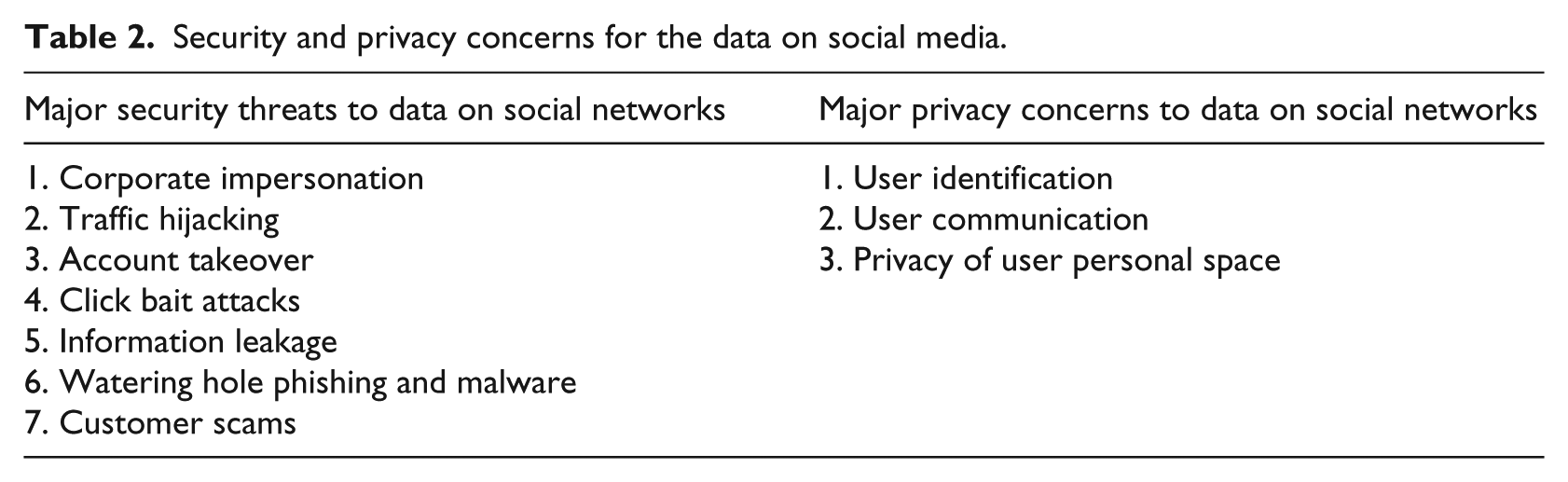
Nerney 56 has identified that there are some significant security concerns to the data on social media. Among the concerns, he has identified the “mobile apps” from unrecognized companies as a major security threat. One major reason for using third-party apps is that the user needs are extending and trusted apps are not always available. The user, while downloading an app, may regard the number of downloads as a feature of trusting the credibility of some application. Although this may be a feature in this regard, yet it is likely that the number of downloads does not truly reflect the credibility of the downloaded app. The user reviews about the app, however, can give some explanatory feedback about the quality and trust level on the application. Since a rating is a quantitative measure and users have to choose from, for example, a scale of 1–5, the application score is less illustrative in defining the problems faced by the application. The comments of the user or those of a trusted party about the quality of an application can however be a more important, realistic, and direct way of establishing the trust and quality for an application. Other major security threats are social engineering and malicious code on the social network sites.57,58 Nerney 56 further identified that the “employee trust” is also vital in training them in such a way that any internal communication, resentment, and policies of the firms are not shared in public. The ZeroFOX 59 has identified that many other security threats to data on social networks exist which include the following: executive impersonation, account takeover, watering hole phishing and malware, customer scams, corporate impersonation, information leakage, click bait attacks, and traffic hijacking. The “executive impersonation” can be overcome by introducing two-way authentication, education and by choosing the right financial partner. The mitigation of each of these can be made by following the respective strategies discussed in the literature.60–63 Since the healthcare data are very sensitive in nature and are not an exception from security breaches, mobile healthcare applications are more vulnerable to such attacks posing a threat to mobile devices or the information security otherwise. The healthcare data and applications, in association with the social networks, need to be doubly secured as a person’s social network’s security is more trivial to reach. In a multi-cloud environment, a small access point (security breach) can eventually compromise the significant part of the healthcare data on the cloud. By adopting the measures, suggested by Delerue and He, 60 the healthcare system can gain significant confidence, as far as the security is concerned. These measures include the following: developing a social media acceptable use and security policy, routine social media sites monitoring, monitoring employee’s Internet activity, user education and training program, archiving social media content, and developing a social media incident and response planning.
Conclusion
There are many threats/concerns to the data on social networks that may compromise the privacy and security of mobile applications and data. Since the healthcare data are of utmost interest to the phishers and intruders, making it available on social media for the purposes of discussion may actually invite the invasion. In order to address the visible threats of a diverse nature, a healthcare model has been presented in this article, which, in integration with the social media and physical infrastructure, presents a viable solution for ensuring the privacy and security of data. The architecture is based on a multi-cloud environment that ensures the availability of data and resources at all the times to deal with the catastrophic nature of the pressing healthcare requirements of a patient in need. The privacy concerns, such as user identification, user space, and user communication, have been discussed and the strategies to mitigate these risks have been elaborated. Along with this, the security concerns have also been identified and are important to be addressed to ensure the privacy and security of the data. Furthermore, the role-based privacy customization has been introduced that leads to the system security and privacy by defining the profile definition of the concerned individuals.
There are several promising research directions that deserve to be investigated in the near future. A detailed study can be conducted on the architectural composition of the multi-cloud environment for healthcare applications to investigate the possible computational gains that can be derived from such advancements. Another direction of work is to investigate the reliability of social media applications while working with the healthcare data in a multi-cloud environment, where the level of reliability, the threats, challenges, and opportunities of such a system can be identified.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The authors extend their appreciation to the Deanship of Scientific Research at King Saud University, Riyadh, Saudi Arabia, for funding this work through international research group project (No. IRG14-07B).
