Abstract
The Russian-sponsored influence campaign targeting the 2016 US Presidential Elections surprised policy-makers and scholars, highlighting a gap in theories of (cyber) power. Russia had used information technologies to project power, yet more subtly than prevailing militarized conceptions of cyber power predicted. Rather than causing damage and disruption, it turned sources of American power into vulnerabilities. Recent scholarship emphasizes this mechanism’s technological novelty. Instead, I argue this campaign demonstrated the importance of an undertheorized instrument of power: subversion. Integrating Intelligence scholarship and International Relations theory, this article develops an innovative theory of subversion as reverse structural power. Structural power shapes structures of interaction and the capacities of structural positions to the benefit of the holder of such power. Subversion reverses these benefits into harms. It exploits vulnerabilities in structures to secretly manipulate them, leveraging the capacities of structural positions to produce outcomes neither expected nor intended by the holders of structural power. Traditional subversion targets social structures, while cyber operations target sociotechnical structures: namely, Information Communications Technologies (ICTs) embedded in modern societies. The targeted structures differ, yet both rely on subversive techniques of exploitation that reverse structural power. Cyber operations are means of subversion. This theory helps explain two unresolved issues in cybersecurity: the capability–vulnerability paradox and the outsize role of non-state actors. Finally, I demonstrate the theory’s utility in a plausibility probe, examining the 2016 Election Interference Campaign. It shows this campaign did not use new “weapons,” but rather integrated traditional and sociotechnical means of subversion.
The foreign interference campaign targeting the 2016 US Presidential Elections surprised policy-makers and scholars alike. It used information technologies to exert influence, yet it resembled neither the visions of cyberwar, nor critical infrastructure disruptions and “Cyber Pearl Harbor” scenarios that have long-shaped cybersecurity debates (Dunn Cavelty, 2013; Lawson and Middleton, 2019). Instead, Russia had turned sources of American strength, its computerized and open society, into vulnerabilities. As Special Counsel Robert Mueller’s investigation revealed, Russia attempted to sway voter opinion by “leaking” embarrassing information obtained through hacking and by spreading narratives damaging the Democratic Party through social media (Mueller, 2019). The more details emerged, the more they underlined the shadowy and “soft” nature of the interference campaign. It remained far below the threshold of armed aggression. Most public and academic discourse nonetheless continued to describe it in martial language, calling the interference “an act of war” (Hertling and Mckew, 2018) where Russia had used “the perfect weapon” (Sanger et al., 2016) to wage “cyberwar” (Jamieson, 2018). Yet, just like Moscow’s involvement became increasingly clear, so did the mismatch to prevailing conceptions of cyber power.
Established cyber power theories see it primarily as a new form of military power (Betz and Stevens, 2011: 12; Kuehl, 2009: 39; Nye, 2011; Starr, 2009: 57). However, the election interference campaign had no military component. Alternative models of cyber power as forms of “structural power”—defined as “the production of structural positions that determine the capacities of actors within it” (Barnett and Duvall, 2005: 53)—fall similarly short of capturing the mechanisms involved. At closer look, this campaign turned the very features supposed to enhance the United States’ structural (cyber) power against itself: its powerful technology industry shaping the global expansion of the Internet in line with American norms and interests (Betz and Stevens, 2011: 49–50; Carr, 2016: 71–76; McCarthy, 2015: 98–100), its resulting central structural position in information networks (Farrell and Newman, 2019), and its dominant position within global security structures (Winecoff, 2020). In short, there is a gap between theories of cyber power and its use in practice. Accordingly, an emerging set of scholarship instead suggests cyber operations offer a novel instrument of power below the threshold of war, creating a new strategic space of competition (Buchanan, 2020; Harknett and Smeets, 2022; Kello, 2017).
I argue that rather than a new means of power, the campaign highlights an understudied yet well-used instrument of power: subversion. The Cold War literature on covert operations is studded with references to subversion, broadly defined as “aggressive but non-combatant intervention by one state in the internal affairs of another” (Blackstock, 1964: 21). The mechanisms involved remain murky, however, since this literature is mostly historical and narrative (Beilenson, 1972; Dear, 1996; Kitson, 1971), grouping a wide range of activities under the term (cf. Beilenson, 1972: vii–viii; Blackstock, 1964: 21–23). Scholarly interests in covert operations has surged recently, but primarily focuses on secret warfare (Carson, 2018; Cormac and Aldrich, 2018; Poznansky, 2019). An emerging body of work also examines subversive strategies and practices in different contexts of world politics (Gläßel et al., 2020; Kurowska and Reshetnikov, 2021; Lee, 2020; Wohlforth, 2020), yet apart from these context-specific investigations, the field still lacks a theory of subversion as power.
This article contributes the foundation for such a theory, identifying its distinct mechanism of reversing structural power. Building on work by Susan Strange (1998) and Michael Barnett and Raymond Duvall (2005), I define structural power as the capability to shape structures of interaction and determine the capacities of structural positions. Subversion reverses this power, I argue, turning the capacities of structural positions into sources of harm. It does so by secretly exploiting vulnerabilities in structures of interaction to manipulate them and produce outcomes neither expected nor intended by holders of structural power as well as agents interacting within a structure—to the advantage of the subverter. For example, a state may send spies to infiltrate a political institution in state B who exploit lax security vetting, attain positions of influence by bribing other officials and, finally, use this subverted institution and the capacities of its structural position to challenge and undermine state B’s government. This mechanism, I show, escapes established conceptions of relational and structural power in International Relations.
The range of effects subversion can produce is as varied as the availability of vulnerable institutions, agents, and the capacities of their respective structural positions. It ranges from influence on public opinion or government policy to infrastructure sabotage and economic warfare (Beilenson, 1972; Blackstock, 1964). Accordingly, the more structural power a targeted state holds, and the more dominant its position within relevant structures, the greater the potential harm subversion can produce against this state. It thus provides opportunities for the weak to challenge the strong. However, I show that the significant challenges involved in exploitation and the capabilities required to overcome them typically reserve subversion to the most powerful states. In other words, one needs structural power to reverse it.
Building on recent work showing the subversive nature of “hacking” (Maschmeyer, 2021), I argue that cyber operations are new instruments of subversion that reverse structural power. Cyber operations exploit vulnerabilities in Information Communications Technologies (ICTs) and the way they are used in modern societies to manipulate the former into producing outcomes neither expected nor intended by their designers or users. Hacking, the exploitation of technical or social vulnerabilities to gain unauthorized access to ICTs in order to manipulate them (Erickson, 2003: 115–116) is a key mechanism. However, it is not the only one. Rather, I show that ICTs, through their embeddedness in societies, form complex sociotechnical structures constituted from a five-layered set of shared rules, practices, and understandings. Cyber operations exploit vulnerabilities in these rules, practices, and understandings to manipulate the structures they constitute, turning the capacities of structural positions into sources of harm for holders of structural power. Through cyber operations, state A thus secretly subverts ICTs embedded in state B’s society to undermine or manipulate these ICTs to produce a variety of effects (e.g. influence, sabotage, and/or economic warfare).
I then apply this theory to the topic of cyber power, showing why it helps explain two unresolved issues in the literature: the capability-vulnerability paradox and the outsize role of private actors. Finally, I demonstrate the theory’s analytical utility through a plausibility probe of the US Elections Interference Campaign. It shows how the campaign combined sociotechnical subversion of computer systems and social media services with traditional subversion techniques targeting the mass media. Building on this analysis, the conclusion discusses the implications for world politics.
This article makes three main contributions. First, it contributes an innovative yet historically grounded theory of subversion as reverse structural power that expands the toolset of International Relations theory. In doing so, it also contributes to Intelligence Studies by refining existing contextual investigations of subversion with a more systematic model. Second, it clarifies how technological change provides new opportunities and challenges for the exercise of power by identifying both the layered set of rules and practices that constitute ICTs and make subversion possible, and the specific mechanisms required to subvert each of these layers—and their limitations. Third, it contributes a theory of cyber power that explains paradoxes confounding existing theories.
The 2016 election interference as anomaly
The revelation of foreign interference in the 2016 US Presidential Elections was a watershed event. It shocked analysts not only because its sponsor, Russia—recently slighted as a declining “regional power” by former President Obama (Julian Borger, 2014)—had struck at the “heart of American democracy” (US Government Publishing Office, 2018), but also because this apparent attack constituted an anomaly for established theories of (cyber) power.
Cyber power theories primarily conceive it as a new form of military power, involving coercion and force projection (Betz and Stevens, 2011: 12; Kuehl, 2009: 39; Nye, 2011; Starr, 2009: 57). Yet, the cyber-enabled election interference campaign had no military component, instead deploying soft instruments exerting a more “subtle influence” (Hansen and Lim, 2019). Rather than hard (coercive) power, the campaign “successfully undercut American soft power” (Joseph Nye, 2019: 3). Consequently, military cyber power falls short of explaining this case—in line with growing evidence of the limited effectiveness of cyber operations in force projection (Gomez, 2016; Lindsay and Gartzke, 2018; Rid, 2013).
Subsequent investigations showed this campaign involved three main components. First, compromises of the computer systems of the Democratic National Convention (DNC) and email accounts of leading figures in the US Democratic party (CrowdStrike, 2016; Mueller, 2019: 38–41; Secureworks, 2016). Second, a coordinated release of information gathered in these compromises through proxies (Mueller, 2019: 44–49). Third, a network of “bots” and false personas to disseminate narratives through social media (Mueller, 2019: 19–28). These components escape militarized perceptions of cyber threats as “attacks” causing economic devastation, disrupting infrastructure, or causing physical harm (Clarke and Knake, 2010; Stoddart, 2016). Nonetheless, many perceived the campaign to have caused a significant effect, reflected in the martial language used to describe it (as discussed further earlier). Hertling and Mckew underline the surprise and fundamental rethinking it triggered, comparing it to other past “earth-shaking events that forced a forward leap in our strategic thinking about the defense of the American homeland and the projection of American power” (Hertling and Mckew, 2018).
Military conceptions of cyber power thus fail to capture the mechanisms used in this campaign, yet alternative theories of structural cyber power fall similarly short. Existing analyses focus primarily on the United States, examining its structural power to shape the Internet according to its interests (Carr, 2016; McCarthy, 2015), leveraging the global reach of its large technology firms to promote foreign policy goals (McCarthy, 2015: 85, 98–100), while “weaponizing” its central position in the network for espionage (Farrell and Newman, 2019). Yet, in this case Russia, located at the relative periphery of this structure (Malecki, 2002: 405), turned these features against the United States. It exploited vulnerabilities created by the United States’ high degree of computerization to obtain information, then used the reach of US-based social media firms to spread it (Mueller, 2019). The campaign thus turned sources of strength into weaknesses.
This mechanism links to a central puzzle existing concepts of cyber power struggle to explain: why are the most capable actors with the most advanced technology also among the most vulnerable? As the 2010 United States National Security Strategy highlighted, “the very technologies that empower us to lead and create also empower those who would disrupt and destroy” (Obama, 2010: 27). Conventional wisdom attempts to explain this paradox militarily through offense–defense theory, diagnosing a strong offensive advantage for cyber weapons (Betz and Stevens, 2011: 39; Lynn, 2010; Nye, 2011: 125). This theory faces significant theoretical and empirical challenges, however (Gartzke and Lindsay, 2015; Libicki, 2009; Slayton, 2017). More recent work aims to explain this “capability vulnerability paradox” through resource dependence, drawing parallels to previous revolutions in military affairs (Schneider, 2019). Yet, as discussed, military affairs are precisely not where cyber operations have been most relevant.
Accordingly, an alternative set of emerging scholarship suggests cyber operations constitute an entirely novel instrument of power that revolutionizes conflict short of war (Buchanan, 2020: 3; Harknett and Smeets, 2022: 24; Kello, 2017: 1). However, this strand of scholarship does not develop a theory of power, and thus falls short of explaining the paradox just outlined. While Lucas Kello proposes cyber operations constitute an entirely new “virtual weapon” (Kello, 2017: 2), most other scholars in this camp identify their heritage in covert operations—but speculate that information technology has expanded their scope and scale to such an extent it creates a strategic revolution (Buchanan, 2020: 5; Fischerkeller and Harknett, 2020: 9; Harknett and Smeets, 2022: 23–24).
The parallels to covert operations these scholars identify show cyber operations are not a sui generis phenomenon, and underline the need to examine these parallels more systematically. An emerging field of scholarship does this (Brantly, 2016; Gartzke and Lindsay, 2015; Rovner, 2019), most recently highlighting the subversive nature of cyber operations (Maschmeyer, 2021). Rather than a new “weapon” or instrument of power, I argue the 2016 election interference campaign thus highlights the importance of subversion, a key instrument used in covert operations. Even military analysts highlight this campaign’s subversive nature, noting that “no one expected that ‘subversive instruments’ would be used in such a way as to create intra-societal tensions through exploitation of civil society organizations” (Jayamaha, 2018). However, subversion remains understudied. Existing work examines various strategies of subversion rather than developing a theory of power (Beilenson, 1972; Blackstock, 1964; Kitson, 1971). More recent work also follows this pattern, examining the escalatory potential of (perceived) subversion through labor strikes (Gläßel et al., 2020), Russia’s subversive approach to foreign policy (Kurowska and Reshetnikov, 2021), subversion as a strategy to exploit incomplete state consolidation (Lee, 2020), and its strategic role in world politics (Wohlforth, 2020). In short, conceptualizing cyber power requires a theory of subversive power—which this is still lacking.
Subversion as reverse structural power
Identifying the specific form of power subversion constitutes requires first establishing a general concept of power. Unfortunately, power is an “essentially contested concept” whose fundamental meaning is subject to controversial debates (Lukes, 2004: 30). Inevitably, tracing its evolution thus introduces some entropy. Robert Dahl’s concept of power offers a useful baseline to start because it remains agnostic about both instruments and resources, and instead defines power relationally. In this view, between two actors A and B, “A has power over B to the extent that he [or she, or they] can get B to do something that B would not otherwise do” (Dahl, 1957: 203–204). This relational concept requires a direct connection between actors, “there is no action at a distance” (Dahl, 1957: 203). Actors include “individuals, groups, roles, offices, governments, nation-states, or other human aggregates” (Dahl, 1957: 203). However, this concept specifies neither the base of power, namely the “sources–opportunities, acts, objects, etc.-that he can exploit in order to effect the behavior of another,” nor the means involved (Dahl, 1957: 203). In fact, Dahl lists a range of means, from promises over threats to the “exercise of charm” (Dahl, 1957: 203).
Classical International Relations theory distinguishes two main forms of power with distinct means and bases: war and diplomacy. Warfare uses material capabilities to generate force to produce a desired outcome. As Von Clausewitz (2006) defines it, war is “the use of physical force to compel an enemy to one’s will” (p. 13). It is the core instrument of power in Classical Realism, where “armed strength as a threat on a potentiality is the most important material factor making for the political power of a nation” (Morgenthau, 1948: 33). Accordingly, a sizable section of Morgenthau’s (1948) book identifies “elements of national power” (pp. 127–181) to allow measuring relative power. This approach of counting things to determine who is strongest has prevailed. Neo-Realist Kenneth Waltz (1979: 99–103, 131), for example, strived to develop further measures of the balance of power as the distribution of material capabilities in the international system. Diplomacy in contrast relies on communication, either verbal or non-verbal (Bull, 1977: 163). In the ideal case, diplomacy works through persuasion (Risse, 2000), or even attraction as in Joseph Nye’s concept of “soft power” (Nye, 2005). When there is no common ground, diplomacy can also devolve into bargaining (Koremenos et al., 2001), sanctions, or threats of force, all backed up by material capabilities (Schelling, 1966: 66). Hence, while the means differ, the base of power is largely the same as in warfare: material capabilities.
Warfare and diplomacy thus fit well within Dahl’s concept. Yet, they do not define it. While for some scholars Dahl has become synonymous with a Realist notion of power based on force and compulsion (Barnett and Duvall, 2005: 49), Dahl’s concept clearly includes a wider range of means, including attraction (through “charm”; see also Baldwin, 2016: 40–42).
Subversion, however, escapes Dahl’s model. As I explain below, subversion has the following three “deviant” characteristics: (1) it relies on the adversary’s base of power, (2) it does not involve a direct connection, and, indeed, (3) it obscures the existence of a power relationship. Subversion itself is an ill-defined and contested concept (Spjut, 1979), complicating analysis. However, I argue the various strategies and means of subversion existing literature identifies share one distinguishing characteristic: a reliance on different mechanisms of exploitation. Accordingly, Paul Blackstock (1964: 49–50) notes subversion targets “political or social institutions” by “exploiting political, psychological, and sociological vulnerabilities”. Mahoney, Thelen, and Faletti specify the mechanism involved, whereby subversive actors are “following institutional expectations and working within the system” but then exploit ambiguities in rules and practices to use “crucial gaps and openings for action” as a way to “work against the system from within it” (Mahoney and Thelen, 2010: 25–26). Bringing this back to Dahl’s model, if A and B are state actors, state A subverts institutions within state B to get it to do something it would otherwise not do. Clearly, this mechanism escapes Dahl’s conception.
Its secret and indirect nature further evade the model. The classic subversive agents are spies, infiltrating institutions under cover identities to establish access and influence—such as the KGB’s infamous “illegals” (Andrew, 2000). Doing so requires secrecy, obscuring the process of exploitation to the victim because the latter can usually arrest or eliminate spies upon discovery (Beilenson, 1972: 63). Subversion also proceeds indirectly (Lee, 2020: 9), because it produces effects through exploited institutions and agents embedded within the latter. In other words, subversion enables “action at a distance” without a direct power relation between A and B. In a subversive operation of the kind laid out above A uses its spy to establish a covert power relation to an institution C. The spy then uses the capacities of this institution to influence B. There is no direct connection between A and B, and, moreover, A uses B’s own “power base” against B to produce effects—the institution is a part of B’s political or economic system.
Alternative conceptions of power fall similarly short. Bachrach and Baratz’s (1962) influential critique of Dahl emphasizes the importance of indirect power relationships. They build on Schattschneider’s concept of “mobilization of bias” as a foundational mechanism of any human organization, discussing hidden structures of power (Schattschneider, 1975). Arguing in the same vein, Bachrach and Baratz (1962: 948) identify a “second face” of power whereby actors can influence not only the outcomes in decision-making processes, but also shape institutional practices constraining which decisions are being considered. Susan Strange’s (1998) influential concept of structural power involves this mechanism, evident in the capacity to “shape and determine the structures of the global economy,” which “confers the power to decide how things shall be done, the power to shape frameworks within which states relate to each other, relate to people, or relate to corporate enterprises” (pp. 24–25). Whereas this second face primarily concerns constraints to behavior, Steven Lukes (2004) has identified a third dimension of “ideological” power, defined as “the capacity to secure compliance to domination through the shaping of beliefs and desires” (pp. 143–144). This “third face” thus not only influences behavior, but shapes identity and underlying preferences.
Finally, Barnett and Duvall (2005) categorize these competing concepts using the main hammer in the political scientist’s toolbox, a 2 × 2, distinguishing the following four forms of power: compulsory, institutional, structural, and productive power. Confusingly, however, what they call “institutional power” in fact corresponds to Strange’s notion of structural power. Barnett and Duvall’s (2005) concept of institutional power involves, control of others in indirect ways, “namely through” formal and informal institutions that mediate between A and B, as A, working through the rules and procedures that define those institutions, guides, steers, and constrains the actions or nonactions and conditions of existence of others. (p. 51)
Structural power as they define it involves the same mechanism of shaping structures and deriving advantages from them as Strange’s concept (Barnett and Duvall, 2005: 53). The influence goes deeper, however, because the “social structure not only constitutes actors and their capacities, it also shapes their self-understanding and subjective interests” (Barnett and Duvall, 2005: 53). The constructivist term of a “social agent” captures this constitutive relationship (Wendt, 1995: 72). Constructivist theory shows social structures are more or less stable patterns of interaction among a set of internally related elements based on shared understandings, knowledge, rules, and practices that evolve in a mutually constitutive iterative process where interaction shapes the identities of agents, while agents in turn shape structure (Wendt, 1987: 357–358; 1995: 72–74; 1999: 4). However, constructivists underappreciate the varying capacity of agents to shape such structures in order to gain advantages—namely, the exercise of structural power (Barnett and Duvall, 2005: 40). Structural power thus involves the capacity to shape structures of interaction and the capacities of structural positions of agents.
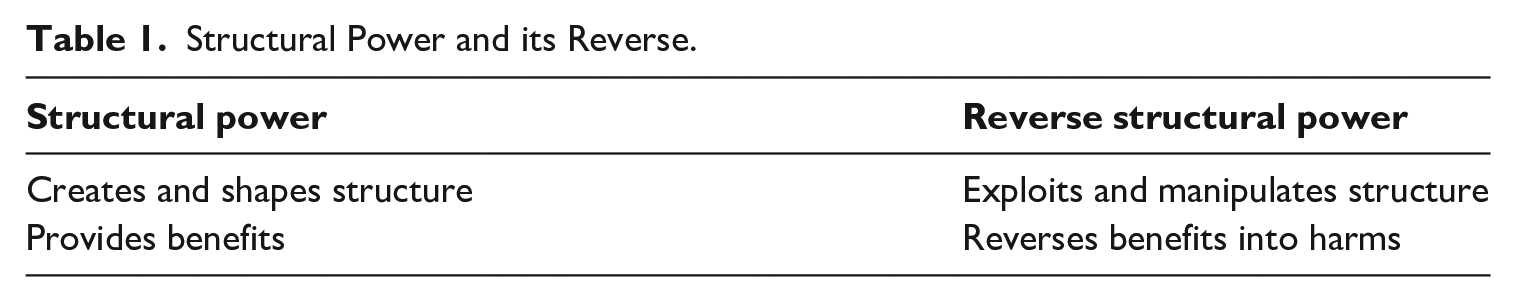
Subversion, however, exploits structures to reverse such advantages and benefits into harms, as simplified in Table 1. Institutions are constituted by rules and practices that constrain interactions (March and Olsen, 1998). Subversion exploits weaknesses in these rules and practices, or the agents that interact within and through the institution. Consider a spy infiltrating an industrial facility by targeting a lonely employee, starting a relationship with the latter and proceeding to pursue employment at the facility with the employee’s support. The spy exploits the employee’s individual vulnerability (loneliness), uses the capacities of the latter’s structural position and the institution’s insufficient security practices to gain access. Now the spy could sabotage equipment, causing damage and, depending on the facility targeted, economic losses. Subversion can not only target rules and practices that constrain behavior, however, but also constitutive shared understandings and identities. Consider a subversive operation aiming to replace a government by infiltrating a political opposition group with spies who coordinate and mobilize the group. If successful, and the opposition group comes to power it changes the very preferences of the state itself (O’Rourke, 2018: 5). Because subversion has this potential to affect preferences and identities, I use structural power and its reverse in the wider sense, including both constraining and constitutive influence—corresponding to the second and third faces of power discussed earlier. Importantly, subversion thus produces outcomes by using the very structural features holders of structural power have shaped against the latter, as well as agents embedded in the structure.
Structural Power and its Reverse.
To illustrate this mechanism, below I offer several examples. Subversion can target structures and agents at all three levels of analysis in the international system—which makes intuitive sense since these levels refer to different, overlapping social structures (Temby, 2015). At the individual level, the Byzantine empire’s strategy of subverting adversaries by bribing and charming influential officials or leaders offers a useful example (Luttwak, 2009: 63). It exploited individual weakness, that is, greed and ego, to turn these individuals into agents of the empire’s interests, using their structural position and capacities to benefit the empire, producing corresponding harms for victims. For example, in 626, the Byzantines apparently succeeded in compromising the commander of the Persian army, who subsequently overthrew the Persian ruler just as the Byzantines were close to military defeat (Luttwak, 2009: 64).
At the domestic level, a key example is the “Guillaume Affair” in Germany. In the 1970s, the East German Intelligence service targeted a political organization at the very top of Germany’s political system, the Federal Chancellery. It managed to infiltrate the institution with a spy, Gunter Guillaume, who attained employment under a false identity, exploiting insufficient security practices (Michels, 2013). That spy gained chancellor Willy Brandt’s trust and was thus able to influence the latter (Michels, 2013: 278). While the actual impact is uncertain, this operation illustrates the use of a powerful domestic institution to use its capacities—determined by its structural position—as a means of pursuing the subverter’s interests against the target government.
At the international level, international regimes are a prime target of subversion. The Soviet Union’s World Peace Council offers an example, a purportedly pacifist activism organization that was in fact a front organization for Soviet interests (Andrew and Mitrokhin, 1999: 486–487). Contemporary Russia’s use of “trickstery,” and subversion of existing rules and practices in international law provides another illustrative case—for instance, by casting its invasions as “humanitarian interventions” (Kurowska and Reshetnikov, 2021: 12). In doing so, Russia uses existing rules to justify actions in violation of international law, diffusing meaning and diluting repercussions, and turning the structure of international law supposed to protect states from intervention into a justification for it—to the detriment of the victim, and the legitimacy of the structure itself.
These examples underline how subversion reverses the logic and directionality of structural power. It exploits structures and their constitutive elements to turn them into means of the subverter’s power. It then uses the capacities of the formers’ structural positions as resources to exert influence—that is, the base of power in Dahl’s conception. As such, subversion reverses the role of an actor’s (material) capabilities as established realist theory sees it. Accordingly, it provides opportunities for weaker actors to use the very structures of domination the stronger have shaped to produce unexpected outcomes to the advantage of the former. As Rumelili (2012) has shown, “subaltern” actors in “liminal spaces” of global power structures can exploit ambiguities in these structural categories to gain advantages, and consequently “the colonised is able to subvert the dominance of colonial authority . . . through an agency that emerges within the master discourse” (p. 501). Despite these opportunities to subvert and resist structures of dominance, however, subversion is not necessarily a “weapon of the weak” (Scott, 1985) because of the considerable requirements its implementation poses.
These challenges result from the fact that the means of subversion are techniques of exploitation, while the base of subversive power is determined by the capacities of targeted entities and the subverter’s skill and creativity in exploiting them. There are various techniques of exploitation, but all share a reliance on deception and manipulation, making others do things they would not otherwise do without revealing influence being exerted, and maintaining an appearance of “normal” activity (Maschmeyer, in press). For example, apart from using undercover spies to infiltrate institutions, one alternative way is to recruit or co-opt individuals within adversary power structures. The Soviet reliance on “useful idiots” to unwittingly spout its propaganda and help pursue its aims (The New York Times, 1981) illustrates this technique.
Two key factors determine the power base of subversion and the range of effects it can achieve: (1) the structural position of the target entity and (2) the depth of the subversion of the latter. The subverter cannot change structural positions, but only exploit existing ones. Hence, the availability of suitable targets is a necessary condition for subversion to work. For example, if the aim is influencing public opinion by spreading disinformation through the media, a media organization with a sufficient national audience, and a suitable vulnerability that the subverter’s agents are capable of exploiting is necessary. The depth of subversion—defined by the type of understandings, rules, and practices it exploits and corresponding levels of access to, and control over, the target structure or agent—however, depends primarily on the subverter’s capacities. Subverting any target requires identifying vulnerabilities and developing suitable means to exploit them. In interstate competition, doing so requires considerable intelligence capacity to conduct reconnaissance, train spies, and deploy them (Blackstock, 1964: 5). This requirement highlights a key point: reversing structural power requires familiarity with the type of structure targeted, hence states with comparable structures “at home” (and corresponding levels of structural power) face lower barriers than those without. In sum, the more intense the effects a subversive operation pursues, the greater the depth of subversion required, and the greater the corresponding challenges.
Consequently, the more structural power an agent has to start with, the greater the scope and scale of effects the agent can likely produce through subversion. Subversive operations or campaigns capable of measurably changing outcomes in world politics will thus likely be reserved to all but a few of the most capable states. A good example is the Byzantine Empire’s systematic use of bribes to subvert adversaries’ governments, leveraging its superior economic capacity to exploit the greed or need of vulnerable individuals (Luttwak, 2009: 63). Accordingly, existing research identifies significant challenges in conducting subversive operations. It shows mounting large-scale subversive operations requires considerable organizational capacity (Johnson, 2022: 170–175) as well as subversive agents skilled enough to infiltrate and exploit the target undetected (Beilenson, 1972: 63). Finally, the latter point highlights a potential qualification of the argument about reversing structural power, as (human) agents possess an intrinsic capacity for action. Hence, provided one has an agent in place at the appropriate structural position, say close to a foreign leader, some effects are possible only because of the agent’s intrinsic capabilities. For example, with a sufficient level of access, an undercover agent trained in violence can use their infiltration of a foreign government to “simply” assassinate its leader. As the next section will show, cyber operations share most of the characteristics just laid out except for this intrinsic potential for action.
The subversive nature of cyber operations
Cyber operations are instruments of sociotechnical subversion that reverse structural power. They exploit ICTs and the way they are used in societies, going after different targets but as I will illustrate below, using the same means as traditional subversion. A key mechanism of exploitation is “hacking,” which “is simply a clever way of getting the computer to do what you want it to do, even if the currently running program was designed to prevent that action” (Erickson, 2003: 115). It does to by exploiting vulnerabilities, which can be both technical or social. Technical vulnerabilities refer to flaws in the design of computer systems, and specifically to flaws in the logic of programming code that determine what the machine does. Computer programs are constituted of code, a set of logical instructions and routines that determines the behavior of the system (Lessig, 2000). Social vulnerabilities involve pathologies in the behavior of human users of these systems. Exploiting such flaws is called “social engineering,” for example, through “phishing” emails that trick users into unwittingly providing access credentials or installing computer viruses on their systems (Rajivan and Gonzalez, 2018). Hackers can gain control over computer systems through either of these ways. Hacking does not involve force (Libicki, 2009: xiv), but rather creativity and cunning—“hacked solutions follow the rules of the system, but they use those rules in counterintuitive ways” (Erickson, 2003: 2). The parallels to Thelen, Mahoney, and Faletti’s description of institutional subversion as “working within the system,” but using “crucial gaps and openings for action” to “work against the system from within it” are striking (Mahoney and Thelen, 2010: 25–26)—underlining the subversive nature of hacking (Maschmeyer, 2021). Cyber operations thus subvert ICTs using different techniques of exploitation.
The ICTs that are increasingly embedded in modern societies are constitutive elements of a structure of interaction, forming complex sociotechnical systems comprised technological artifacts and social agents (Balzacq and Cavelty, 2016; Deibert, 2013: 102; Herrera, 2006). Sociotechnical systems are assemblages of varying complexity that are constituted of both technological artifacts and social actors and relations (Latour, 1992). The core idea is that “the social” and “the technological” are not separate, independent variables, but interlinked in a mutually constitutive relationship (Law, 1991: 10). Hence, they constitute sociotechnical structures comprised both of the technological infrastructure itself, as well as the individual and collective agents who use it and interact with and through it (Harvey, 1968). In fact, Alexander Wendt (1987: 357) already lists technologies as constitutive elements of social structures in his classic article on the agent-structure problem.
Computerizing social interactions and processes, and thereby building and expanding this structure, promises significant benefits in productivity, efficiency, and convenience (Dedrick et al., 2003). Accordingly, financial transactions (Aitken et al., 2017), industrial production processes (Zhong et al., 2017), energy grid operation (Appelrath and Kagermann, 2018), and even romantic partner search (Pagon and Bizjak, 2009) are increasingly computerized. Shaping the ICTs involved, the interactions they enable and, thereby, the capacities of both the ICTs’ structural positions as well as of the agents who interact with and through them provides significant structural power—as recent scholarship correctly points out (Betz and Stevens, 2011: 49–50; Carr, 2016: 71–76; McCarthy, 2015: 98–100). However, crafty actors can subvert these sociotechnical structures to reverse benefits into harms.
Subversion is possible because the sociotechnical structure of globally interconnected ICTs is constituted by a set of shared understandings, rules, and practices. There are five different layers. The first layer comprises the laws of physics and engineering principles that shape the design of the technology (Kuehl, 2009). Second, logical rules in programming code and networking protocols constitute and control the behavior of the technology and interactions with and through it (DeNardis, 2009; Lessig, 2000). At the third layer are the rules and practices regulating the use of ICTs within an organization or institution (Dupont, 2019). Fourth, the formal and informal social and legal rules, norms, and practices that regulate interactions through this technology in a society. A straightforward example of legal rules are laws prohibiting the sharing or storing of child pornography. An example of informal rules is the concept of “netiquette” (Shea, 1994). The fifth layer concerns the legal rules and practices that regulate which physical and social processes are computerized in a society, and to what extent. The current push to ban autonomous weapons systems is a key example of the latter (Human Rights Watch, 2020).
These shared understanding, rules, and practices contain different vulnerabilities that subversive agents can exploit to reverse the benefits of computerization into harms. The first two layers are constitutive. They enable the creation of hardware and software, interactions with and through the latter, and they define the roles and capacities of users. Hacking is a powerful instrument because it exploits these constitutive layers, and in doing so, changes the very “identity” of ICTs and their roles. Just like spies can infiltrate social institutions and secretly turn them into agents of the subverter, computer viruses or malware can infiltrate targeted systems and secretly turn them into agents of the sponsor of the cyber operation, producing outcomes in direct conflict with the ICTs intended and designed purpose. Accordingly, recent literature suggests the term “non-anthropocentric agents” (Fouad, 2021).
While exploitation of the constitutive layers thus enables the “deepest” reach of subversion, targeting the primarily constraining rules and practices at layers 3–5 still allows significant effects—and they can be combined. Consider the NotPetya virus, which caused massive disruptions and economic damage worldwide in 2017 by irreversibly encrypting data on affected systems (Greenberg, 2018). While the virus itself exploited technical vulnerabilities in software (layer 2) to produce its disruptive effects, its massive spread resulted from an insidious exploitation of a security “best practice” (layer 3) offered by the provider of the software affected: automated updates (ESET, 2017). Customers trusted the firm to automatically install updates on their computers to make sure software is always up to date, a key “best practice” of cyber resilience—yet the hacking group behind NotPetya exploited this trust to turn the automated update mechanism into a vehicle of spreading a virus that disabled computers and destroyed data. An example of sociotechnical subversion that does not involve hacking is the use of targeted advertising offered by social media services to spread of political propaganda and disinformation—exploiting the algorithms designed to deliver “content” and ads to users as means of conducting influence operations (Bradshaw and Howard, 2018). In short, by exploiting vulnerabilities in the shared understandings, rules, and practices that regulate and constitute human interactions with and through ICTs cyber operations turn these ICTs against their designers, owners, and users—and, by extension, against targeted states.
In short, cyber operations rely on the same functional means of reversing structural power as traditional subversion, namely techniques of exploiting structural vulnerabilities. Accordingly, they also utilize a similar power base to produce similar types of effects. However, there are important differences. The power base that determines the effects “cyber subversion” can produce are the same as in traditional subversion, namely the target’s structural position and depth of subversion. First, the targeted system’s structural position determines the maximum potential harm. The more central its structural position, and thus, the more societal processes it affects, the greater the potential scope and scale of effects. However, as in traditional subversion, the actual harm achieved depends on the depth of subversion—and achieving and extending such depth involves significant challenges that require considerable resources and structural power to overcome. Above all, it requires sufficient familiarity with the target system to identify vulnerabilities and develop means of exploitation, skilled operators to do so, as well as organizational capacity to manage these complex tasks over extended periods of time (Lindsay, 2013; Maschmeyer, 2021; Slayton, 2017; Smeets, 2022). Hence, while the material resources required are relatively minimal, cyber operations are by no means as cheap and easy as often suggested (Lynn, 2010; Nye, 2011: 116). Rather, mounting successful cyber operations requires significant structural power, especially in building up the technology sectors, training programs, and organizational capacity they require.
Cyber operations thus share the subversive mechanism of reversing structural power, its means and the base of power with traditional subversion. However, they differ in an important respect already briefly touched upon: the reliance on immaterial and non-human agents. The previous section highlighted how traditional subversion can leverage the intrinsic action potential of human agents. Cyber operations lack this potential, because they rely upon immaterial informational agents—electronic messages, data, and code (i.e. malicious programs). Cyber operations could thus be considered a “pure” form of subversion: they depend entirely on the capacities of targeted entities to produce effects. An actor may have an abundance of skilled hackers and organizational capacity, yet without a suitably embedded, vulnerable target there is no way to produce effects. For this reason, the “cyber power indexes” that have recently gained popularity (Voo et al., 2020) have very limited analytical value. To put it pointedly, cyber operations are rather useless against a club-swinging stone age tribe. This reliance on immaterial agents without intrinsic action potential also helps explain the relative ineffectiveness at producing physical effects by cyber means that a growing literature points out (Borghard and Lonergan, 2019; Rid, 2013; Slayton, 2017).
Reverse structural power and cyber power
Applying the theory developed earlier to the topic of cyber power helps explain two unresolved issues in cybersecurity scholarship. First, the mechanism of reversing the benefits of structural position explains the capability–vulnerability paradox. Structural power theories explain why the growing reach of ICTs into social processes provides not only efficiency and productivity gains for states, but also why the more central a state’s position is in the global structure of cyberspace, the more benefits it can also accrue from accessing and controlling information flows. The greater these benefits are, however, the greater the potential harms become that subversive actors can cause by reversing this structural power. In other words, the more structural power a state holds, the greater the potential opportunities for subversive actors become. Accordingly, in theory states on the relative periphery of this structure (the global Internet) have considerable opportunities to harm those closer to the core. However, due to the challenges involved in subversion of such complex structures, in practice, the revisionist potential of subversion, and the range of states capable of carrying out operations that produce significant outcomes at the international level, is likely very limited. This dynamic also helps explain why, despite 30 years of warnings of cyberwar, it has not happened.
Second, the theory explains the outsize importance of non-state actors in cyber conflict as holders of structural power—shaping the structure that states (and other agents) subvert. Non-state actors in cyber conflict not only play an important role as proxies (Maurer, 2018) but increasingly turn into what Egloff (2022) calls “semi-state actors” who “fundamentally shape the security and insecurity experienced worldwide” due to their “interlinkages with the international political system” (p. 2). Egloff’s point regarding shaping alludes to the structural power wielded by such actors. The extent of their influence is unsurprising when considering the layers of understandings, rules, and practices they can shape. In the traditional political economy, states are the dominant wielders of structural power, while non-state actors are constrained by the properties of the structures created by the latter (Strange, 1998: 236–239). This situation makes intuitive sense since the institutions involved are social structures constituted primarily of social understandings, rules, and practices.
In the political economy of cyberspace, a sociotechnical structure, these roles are reversed. Technological artifacts are a constitutive element of this structure, and these artifacts—namely networked computer systems and programs that run on them—make it possible for humans to interact with and through this structure. Importantly, private actors produce the vast majority of these artifacts, and thus exert a fundamental, constitutive influence on the underlying structure of cyberspace (Ruiz and Barnett, 2015). These firms thus shape the constitutive layers of the structure of cyberspace, namely design principles and the logical rules that enable interconnected computer systems to function and thus allow people (and states) to interact through them.
In theory, governments can influence infrastructure development and technological design as well. Accordingly, the very existence of today’s Internet goes back to a project by a government-funded research agency in the United States (DARPA; Lukasik, 2011). In practice, however, most governments have taken a laissez-faire approach, hence business incentives and market dynamics primarily shape design (Dunn Cavelty and Suter, 2009; Eichensehr, 2017). In fact, business incentives are a key reason for the abundance of vulnerabilities in ICTs (Anderson and Moore, 2006). This laissez-faire approach makes intuitive sense since states depend on vulnerabilities to conduct cyber operations. Accordingly, states have primarily focused on setting constraining rules for the use and spread of ICTs. The ubiquitous and yet—at least so far—inconsequential initiatives to promote “cyber norms” to regulate competitive cyber operations constitute a key example. In short, private actors are the primary holders of structural power shaping the constitutive features of the structure of cyberspace. States subvert the latter to gain advantages, producing harm against these private actors, their “host” states as well as other states using the structure private actors have created.
Case study: 2016 US elections
To illustrate the practical utility of the theory, this section applies it to the case of the 2016 Election Interference Campaign, identifying the mechanisms and types of power involved. It will show that the theory captures not only the role of hacking but also the instruments of influence deployed afterwards. This analysis will underline that this campaign involved no military power, but rather show how it integrated sociotechnical and traditional subversion techniques. Counterintuitively, considering prevailing perceptions of a “hacked election” (Justice and Bricker, 2019), hacking was only a minor component of the campaign. This campaign proceeded in three main steps, and I will examine each below.
First, compromises of the DNC and prominent email accounts turned the benefits of embedded ICTs into harm at the organizational and individual levels. The hackers exploited both social and technical vulnerabilities to subvert the infrastructure of the DNC and the Democratic Congressional Campaign Committee (DCCC) and obtain sensitive information. They acquired initial access to the targeted systems through a targeted phishing email, tricking a staffer into disclosing their access credentials (Mueller, 2019: 38). This subversion exploited vulnerabilities in human behavior as well as prevailing security practices. Once access was established, the hackers proceeded to install malicious programs on the targeted computer network, designed to secretly exfiltrate information without alerting the victim to its presence (Mueller, 2019: 38–39). In this subversive process, the hackers turned the benefits of computerization into harms for the targeted organizations. In parallel, they targeted the email accounts of key personalities such as Hillary Clinton’s campaign manager John Podesta with further targeted phishing emails (Franceschi-Bicchierai, 2016), exploiting vulnerabilities in human behavior (Brandom, 2016). In doing so, the hackers turned the benefits of interacting through email—speed and convenience—into harm for the targeted users, and by extension the organization they worked for, resulting in a loss of privacy and sensitive information. Importantly, in contrast to prevailing language of a “weapon” used in an “attack” resembling an “act of war,” this compromise simply exploited human gullibility and fallibility to gain access to sensitive information.
Second, the hackers and the sponsoring intelligence organization, Russia’s Main Intelligence Directorate GRU (Mueller, 2019: 37), used the information obtained through above compromises to exert influence on the US populace, turning the benefits of an open media system into harms at the national level. This component did not involve hacking, but rather the exploitation of the interests of media outlets in exclusive and embarrassing information. In particular, WikiLeaks became a key proxy actor co-opted by the GRU as its own dissemination efforts faltered (Rid, 2020: 390–395). As such, this component of the operation leveraged traditional institutional subversion, playing within the rules of the target system but exploiting them to serve the subverter’s ends—exacting harm on the victim. Even the New York Times story labeling this operation as the “Perfect Weapon” in fact precisely captures the subversive nature of this mechanism: Every major publication, including The Times, published multiple stories citing the D.N.C. and Podesta emails posted by WikiLeaks, becoming a de facto instrument of Russian intelligence. Mr. Putin, a student of martial arts, had turned two institutions at the core of American democracy—political campaigns and independent media—to his own ends. (Sanger et al., 2016)
In short, this second component of the influence campaign subverted the rules and practices of the free media, turning their intended role in the United States political system as democratic institutions into instruments of foreign influence.
Third, the campaign employed targeted dissemination and amplification of misleading narratives through false online accounts and “bots” on social media platforms, primarily Twitter and Facebook (Bovet and Makse, 2019; Kim et al., 2018), subverting their design features. Specifically, it exploited the algorithmic routines intended to maximize user engagement and advertising sales to instead maximize the reach and impact of these narratives (Lazer et al., 2018: 105). These design features provide the benefit of free political expression and entertaining content to users (Lischka, 2021) and business growth from advertising (Liew et al., 2014). The Russian subversion turned these benefits into the harm of deceptive influence on users and, due to the central structural position of these platforms, reached a massive audience. Due to the lack of regulation, these platforms exert structural power not only over a massive scale of users, but also at significant scope. The extent of the latter was most recently illustrated by the ban of Donald Trump’s Twitter account—unilaterally censoring a leading political figure without any democratic process involved (Twitter Inc., 2021). In other words, the outsize structural power of non-state actors provides outsize power potentials for subversive (state) actors.
In the ideal case, from the Russian perspective, this campaign helped elect President Donald Trump—thus shaping US preferences and influencing its foreign policy toward Russia. However, its actual impact on election outcomes remains unclear and there are important reasons to doubt its effectiveness (Jamieson, 2018; Kalla and Broockman, 2018; Persily, 2017). While further research is needed to assess this impact, however, this analysis clearly demonstrates the strength of the theory as both an analytical tool and explanatory model.
Conclusion: reverse structural power in world politics
This article has developed a theory of subversion as a distinct form of power that produces outcomes by reversing structural power. The latter shapes structures of interaction and the capacities of positions within, usually toward the benefit of the holder of structural power and those with privileged positions. Subversion secretly exploits vulnerabilities in structures and their constitutive elements to manipulate them toward turning these benefits into harms. Traditional subversion targets social structures, while cyber operations target sociotechnical structures—namely, networked computer systems and services embedded in societies. These structures differ in composition, but the analysis revealed the mechanisms of exploitation and the reversal of structural power they enable function the same way. The article then applied this theory to the topic of cyber power. Doing so helped resolve the capability–vulnerability paradox: the greater an actor’s structural power is, the greater the potential harm subversion can cause against this actor. Furthermore, the theory also explains the outsize role of private actors in cyber conflict, who shape the structures that states exploit. Finally, I demonstrated the analytical and explanatory utility of the theory through a case vignette of the 2016 US Election Interference campaign. This analysis underlined that rather than using a novel weapon, this campaign integrated different techniques of subversion to turn the United States highly digitized society and open government system—two key manifestations of its structural power—into sources of harm.
Having established the theory and its utility, in the remainder of this conclusion I examine the implications for world politics, identifying three specific consequences and addressing the wider question of technological change. The first key implication from the theory is that in practice subversion is unlikely to be the great leveler that its theoretical potential may suggests. However, subversion offers a way to harm powerful actors by turning the very sources of their strengths against them. This mechanism does open opportunities for the weak to challenge the strong, yet as discussed doing so comes with its own distinct set of challenges that are exceedingly difficult to meet without sufficient structural power—that is, organizational capacity, skills, and infrastructure. Accordingly, throughout the Cold War subversion has primarily been an instrument for the two superpowers to gain advantages by undermining and influencing weaker states (Andrew and Mitrokhin, 1999; Blackstock, 1964; O’Rourke, 2018). The situation in cyber conflict today is similar, as the handful of cyber operations of significance in world politics have been mostly reserved to a small club of large states with strong intelligence traditions and capacities, namely the United States, China, and Russia. Moreover, subversion not only involves significant challenges to implement, these challenges also limit its impact on the balance of power (Maschmeyer, 2021). Although there are widespread fears about the efficacy of propaganda and disinformation campaigns through social media, there is still a lack of systematic evidence proving it has a significant impact at scale—and some countervailing evidence (Yevgeniy Golovchenko et al., 2018). Consequently, subversion is more likely to provide additional, if marginal, advantages to powerful actors, rather than allow weaker actors to significantly shift the balance of power.
Second, the “pure” form of subversion the analysis revealed cyber operations to be helps explain the persistently low intensity of cyber conflict, not only compared to warfare but also compared to traditional subversive operations. Cyber operations are “pure” forms of subversion since the immaterial agents they utilize exclusively depend on targeted systems (i.e. structural elements) to produce effects whereas human agents in traditional subversive operations have an intrinsic action potential themselves. This situation has two consequences. First, some effect types that human agents can produce through their own physical force, such as kidnapping people, breaking their way into a facility or even assassinating people, are beyond the reach of cyber operations. Second, and correspondingly, cyber subversion only reaches as far as computerization goes. Diplomacy and warfare, meanwhile, continue to take place primarily through traditional structures of interaction. Both the subjects (politicians and government institutions, armies) and the objects (material capabilities, diplomatic agreements) are at most partially computerized. Consequently, it is unsurprising cyber operations have remained largely irrelevant or ineffective in both warfare and (coercive) diplomacy (Borghard and Lonergan, 2017; Buchanan, 2020; Kostyuk and Zhukov, 2017; Lindsay and Gartzke, 2018).
Third, and conversely, while their impact on international politics is likely limited, the considerable structural power wielded by private actors explains why cyber operations can have significant effects on individuals and (vulnerable) groups. Contrary to prevailing conceptions of cyber conflict as high-level interstate conflict and economic espionage, a significant proportion of cyber operations target civil society—although it is rarely reported (Maschmeyer et al., 2020). The networked ICTs that private actors design and build—foremost mobile phones—provide continuing advances in convenient and efficient communication across vast distances. Especially, civil society organizations use these benefits to mobilize and coordinate resistance against repressive regimes within and across borders. Authoritarian states, however, can subvert ICTs to reverse these benefits into harms—exploiting the reach of ICTs into people’s professional and personal lives to monitor communication, disrupt communication, steal data, and locate dissidents (Al-Jizawi et al., 2022). In the worst case, the result is persecution by law enforcement, incarceration, or even death (Crete-Nishihata et al., 2014). As such, private actors—if unwittingly—build the structures that repressive regimes subvert to target civil society. Because more and more interactions in our professional and personal lives are computerized, this potential for subversion continues to increase. Moreover, private actors not only shape the structures enabling exploitation, but an emerging and growing business sector engages in active exploitation, selling “privatized subversion” services using capabilities rivaling those of some nation-states (Deibert, 2022).
Apart from these specific points, the larger question how the continuing spread of ICTs shapes and interacts with world politics remains a looming issue in International Relations, reflecting the field’s long neglect of the role of technology. While a universal answer will likely remain beyond reach, to understand at least the implications for the exercise of power more theoretical and empirical research examining the scope and scale of outcomes different types of actors can achieve by subverting this sociotechnical structure is urgently needed. Because this structure continues to spread and evolve—all indications point toward its growing expansion due to the benefits it provides to both the actors enabling and exploiting it—this effort will require both persistence and flexibility.
Footnotes
Acknowledgements
The author is grateful to Max Smeets, James Shires, Ronald Deibert, and Myriam Dunn Cavelty as well as the anonymous reviewers for their feedback on previous drafts that helped him improve the argument.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
