Abstract
Consider deploying a team of robots in order to visit sites in a risky environment (i.e., where a robot might be lost during a traversal), subject to team-based operational constraints such as limits on team composition, traffic throughputs, and launch constraints. We formalize this problem using a graph to represent the environment, enforcing probabilistic survival constraints for each robot, and using a matroid (which generalizes linear independence to sets) to capture the team-based operational constraints. The resulting “Matroid Team Surviving Orienteers” (MTSO) problem has broad applications for robotics such as informative path planning, resource delivery, and search and rescue. We demonstrate that the objective for the MTSO problem has submodular structure, which leads us to develop two polynomial time algorithms which are guaranteed to find a solution with value within a constant factor of the optimum. The second of our algorithms is an extension of the accelerated continuous greedy algorithm, and can be applied to much broader classes of constraints while maintaining bounds on suboptimality. In addition to in-depth analysis, we demonstrate the efficiency of our approaches by applying them to a scenario where a team of robots must gather information while avoiding dangers in the Coral Triangle and characterize scaling and parameter selection using a synthetic dataset.
1. Introduction
Consider a scenario where mobile robotic sensors are used to monitor a number of regions of the ocean, each of which may require different sensing capabilities. Due to uncertain and possibly adversarial events (e.g., bad weather or piracy), there is a risk that robots may “fail” when traveling from one region to another. A fleet manager seeks a set of paths which maximizes the expected number of sites monitored while satisfying various resource constraints. For example, there may be limits imposed by the number of available robots of each type, the logistics of deploying the robots, the probability a given robot reaches its destination, or the amount of traffic a given region can support. If these constraints are “downward closed” (meaning any subset of a feasible set of paths is feasible) and satisfy an exchange property, then we can represent them using a matroid (Schrijver 2002), which generalizes linear independence to set systems and has structure amenable to optimization.
We formalize this class of exploration problems as a generalization of the orienteering problem (Golden et al. 1987), where one seeks a path which visits as many nodes in a graph as possible given a budget constraint and travel costs. In our earlier example the travel costs are the probability that a robot fails while traversing between sites, and we are looking for a set of such paths which is an independent set of a matroid, maximizes the expected number of nodes visited by at least one robot, and ensures that the probabilities each vehicle reaches its destination is above a specified threshold.
We call this problem formulation the “Matroid Team Surviving Orienteers” (MTSO) problem, illustrated in Figure 1. Illustration of an ocean monitoring scenario with various regions and sites to visit within each region marked by “X,” and the heat map indicates the risk of robot failure inferred from piracy incidents. The objective is to find a set of paths for a heterogeneous team which maximizes the expected number of sites visited subject to several constraints. Data is from the Coral Triangle Atlas (Cros et al. 2014) and the International Chamber of Commerce: Commercial Crime Services (2017).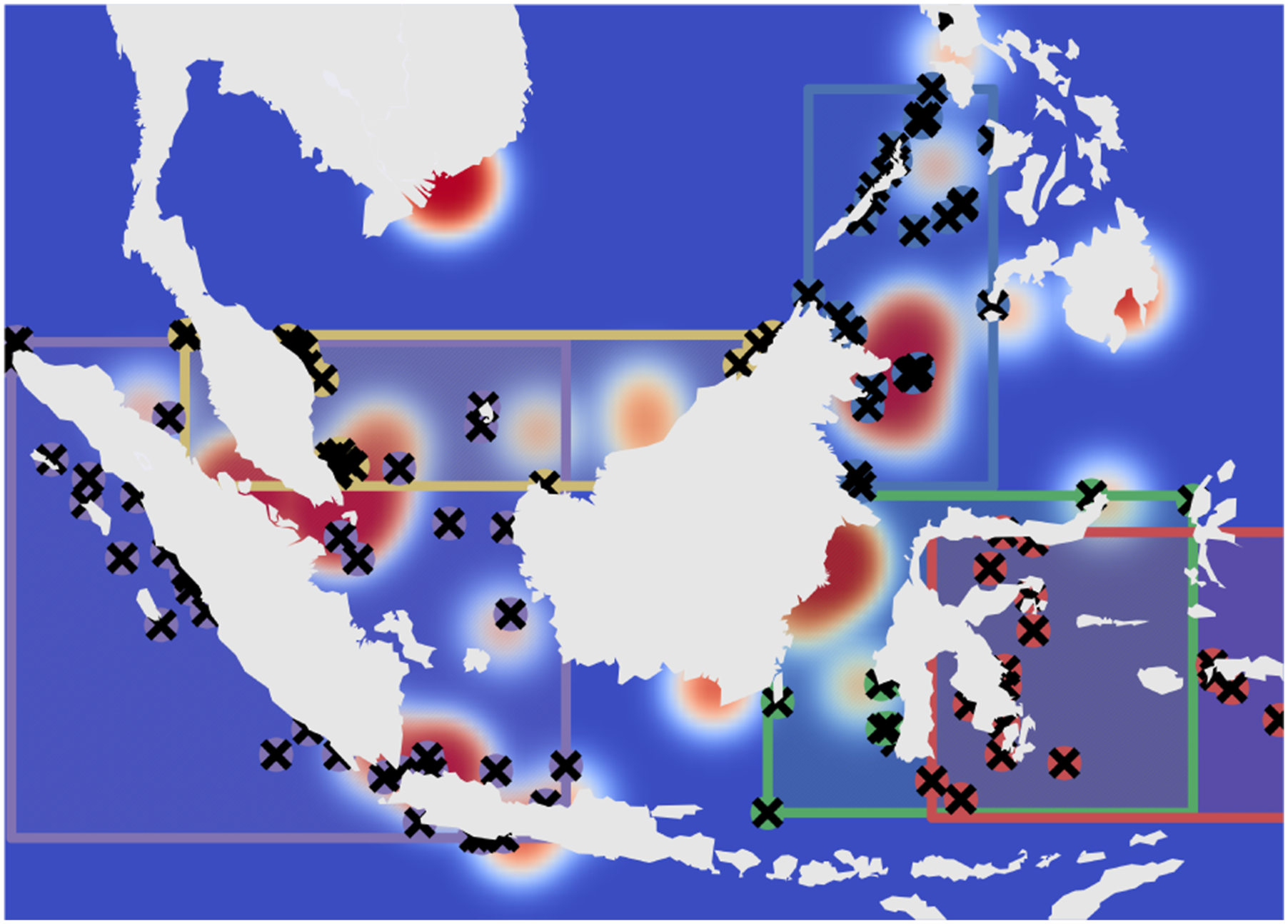
The MTSO problem is a significant generalization of our earlier work on the Team Surviving Orienteers (TSO) problem (Jorgensen et al. 2018), which only imposes a maximum team size constraint (a very special case of a matroid constraint). Both the MTSO and TSO are distinct from previous work because of the notion of risky traversal: when a robot traverses an edge, there is a probability that it fails and does not visit any other nodes. This creates a complex, path-dependent coupling between the edges chosen and the distribution of nodes visited, which precludes the application of existing approaches available for the traditional orienteering problem. The objective of this paper is to devise constant factor approximation algorithms for the MTSO problem. An efficient algorithm for the TSO was designed by exploiting a diminishing returns property known as submodularity (Jorgensen et al. 2018), which for set function f and sets A and B means that f(A ∪ B) + f(A ∩ B) ≤ f(A) + f(B). Our key technical insight is that we can further exploit submodularity of the objective function to design efficient solution algorithms for the much more general MTSO problem. We describe numerous applications of matroid constraints to path planning problems, and describe an approximate greedy algorithm which enjoys a constant factor approximation guarantee. We then develop an approach based on the accelerated continuous greedy algorithm (Badanidiyuru and Vondrák 2014) which is the state of the art for matroid optimization and provides tighter guarantees that are easily extended to more general settings. Although a number of works have considered routing problems with submodular objectives (Chekuri and Pál 2005; Campbell et al. 2011; Zhang and Vorobeychik 2016), chance constraints (Gupta et al. 2012; Varakantham and Kumar 2013), or downward closed constraints (Koç et al. 2016; Lahyani et al. 2015; Hoff et al. 2010) separately, the MTSO is novel because it combines all three aspects.
1.1. Related work
The orienteering problem (OP) has been extensively studied (Gunawan et al. 2016) and is known to be NP-hard. Over the past decade a number of constant factor approximation algorithms have been developed for special cases of the problem. The submodular orienteering problem considers finding a single path which maximizes an arbitrary submodular reward function of the nodes visited. The recursive greedy algorithm proposed in Chekuri and Pál (2005) yields a solution in quasi-polynomial time with a constant factor guarantee, and the cost-benefit greedy algorithm proposed in Zhang and Vorobeychik (2016) yields a solution in polynomial time but only has a constant factor guarantee with respect to a relaxed problem. Our work is distinct from these efforts because we consider a specific submodular function, but find a set of paths rather than a single path formed by a set of edges. The risk-sensitive orienteering problem (Varakantham and Kumar 2013) considers random edge weights and seeks to maximize the sum of rewards subject to a constraint on the probability that the path cost is large. Only a single path is considered, so there is no notion of independence between paths as in the MTSO.
A second closely related area of research is the vehicle routing problem (VRP) (Psaraftis et al. 2016), which is a family of problems focused on finding a set of paths that maximize quality of service subject to budget or time constraints. The rich vehicle routing problem (RVRP) (Lahyani et al. 2015) considers settings such as routing heterogeneous teams (Koç et al. 2016), “fleet dimensioning” (choosing team composition) (Hoff et al. 2010), and incompatability constraints (Kelareva et al. 2014). The vast majority of solution algorithms for the RVRP are heuristic (Lahyani et al. 2015) and do not consider risky traversal. A notable exception are linear temporal logical (LTL) constraints, which have exact integer programming formulations (Karaman and Frazzoli 2011) and transition system formulations (Smith et al. 2011; Ulusoy et al. 2014), the complexity of which grows exponentially in the team size. In our work, we consider a narrower yet still expressive set of constraints and derive polynomial time solution algorithms with constant factor approximation guarantees.
A third related branch of literature is the informative path planning problem (IPP), which seeks to find a set of paths for mobile robotic sensors in order to maximize the information gained about an environment. One of the earliest IPP approaches Singh et al. (2009) extends the recursive greedy algorithm of Chekuri and Pál (2005) using a spatial decomposition to generate paths for multiple robots, and provides performance guarantees using submodularity of information gain. While the structure of the IPP has many similarities to the MTSO problem (it is a multi-robot path planning problem with a submodular objective function which is non-linear and history-dependent), it captures neither the constraints nor the notion of risky traversal which are central to the MTSO problem. Our general approach is inspired by works such as Atanasov et al. (2015), which iteratively assigns paths to each robot, but for the MTSO problem we further exploit the problem structure to derive constant factor guarantees.
A handful of papers apply submodular maximization and matroid constraints directly to robotics applications. In Jawaid and Smith (2015), path constraints are represented using a p-system (which generalizes a matroid), and a submodular maximization problem with p-system constraints is solved to find the approximately most informative path for a single agent. Multi-robot task allocation problems are cast as decentralized submodular maximization problems with matroid constraints by Segui-Gasco et al. (2015) (who considers private reward functions), and Williams et al. (2017) (who considers communication constraints). In both cases the objective is to assign robots to tasks, rather than to find a high reward set of paths for a team of robots. Recent work by Corah and Michael (2019) and Robey et al. (2021) consider the distributed optimization setting for applications in informative path planning and task assignment—though neither setting considers risky traversal. The work by Segui-Gasco (2017) and Robey et al. (2021) is notable as it uses the (accelerated) continuous greedy algorithm which is the most similar to our work (despite a different application). In our work we use an orienteering problem oracle in order to find high quality paths for each robot while considering risky traversal. This requires different analysis which utilizes results on approximate greedy algorithms for submodular maximization subject to matroid (Fisher et al. 1978) and p-system (Calinescu et al. 2007) independence constraints.
Statement of Contributions: Matroids have been applied with great success to many fields of engineering such as electrical and structural network design (Murota 2009), but they have rarely been used for robotic routing problems. The contribution of this paper is six-fold. First, we propose a generalization of the TSO problem, referred to as the Matroid TSO problem. By considering matroid constraints, we extend the state of the art for the team orienteering problem, and by considering the risky traversal model we extend the state of the art for the rich vehicle routing problem. Second, we demonstrate how to use matroids to represent a variety of constraints such as coverage, deployment, team size limitations, traffic constraints, team-wise risk constraints, and nested cardinality constraints. Third, we extend the approximate greedy algorithm from Jorgensen et al. (2018) to the MTSO setting, and prove that the value of its output is at least
This paper is a significant expansion of our conference paper Jorgensen et al. (2017a), which introduced the MTSO and greedy algorithm. In particular, we present and analyze the accelerated continuous greedy algorithm which is a new approach to the problem that provides stronger guarantees with broader applications. As mentioned above this requires extending the analysis from Badanidiyuru and Vondrák (2014) to apply to the case where the greedy problem can only be approximately solved and providing a novel method of evaluating the multilinear extension for the MTSO problem. We have also significantly expanded the numerical experiments and discuss extensions beyond matroids.
Organization: The rest of this paper is organized as follows. In Section 2 we review key background information necessary for our results. In Section 3 we present the formal problem statement for the MTSO and describe several applications in Section 4. In Section 5 we outline the algorithms and give performance guarantees. Section 6 demonstrates the practicality of our algorithm via numerical experiments. In Section 7 we discuss a number of extensions of our work which can be solved using the continuous greedy algorithm. Finally, in Section 8, we draw our conclusions and discuss directions for future work.
2. Background
2.1. Sets and submodular functions
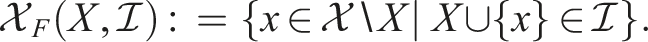
Submodularity is the property of “diminishing returns” for set functions. The following definitions are summarized from Krause and Golovin (2014). Given a set
The quantity on the left hand side is the discrete derivative of f at X with respect to x, which we write as Δf(x∣X).
The multilinear extension of a submodular function f at
The multilinear extension of f at y is then defined as the expected value of f(R(y)):
For optimization problems the multilinear extension is used in a similar fashion as a linear programming relaxation of a mixed integer program, where integer variables (i.e., whether element x is in the solution) are replaced by continuous relaxations (i.e., y x ∈ [0, 1]), and the resulting solution is rounded to get a set. We discuss this optimization framework more in Section 2.3.2.
2.2. Independence systems and matroids
The following definitions are summarized from Schrijver (2002). An independence system is a tuple of a finite ground set
2.3. Approximate greedy algorithms
Given a matroid
2.3.1. Greedy algorithm
Given a matroid
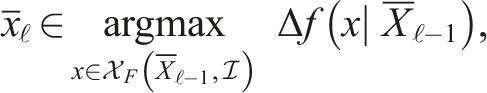
The greedy algorithm constructs a set
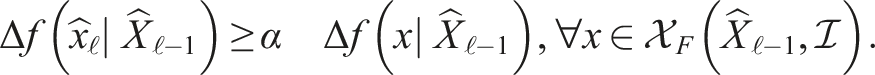
An α–approximate greedy algorithm constructs the set
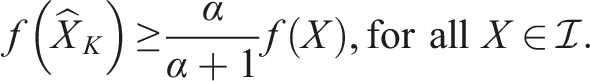
Approximate greedy guarantee Calinescu et al. (2007). Let Note that while the approximate greedy algorithm is simple and relatively fast, in the best case (α = 1) the guarantee is 1/2, but the state of the art has a 1 − e−1 ≃ 0.63 guarantee with matching hardness bounds.
2.3.2. Accelerated continuous greedy algorithm
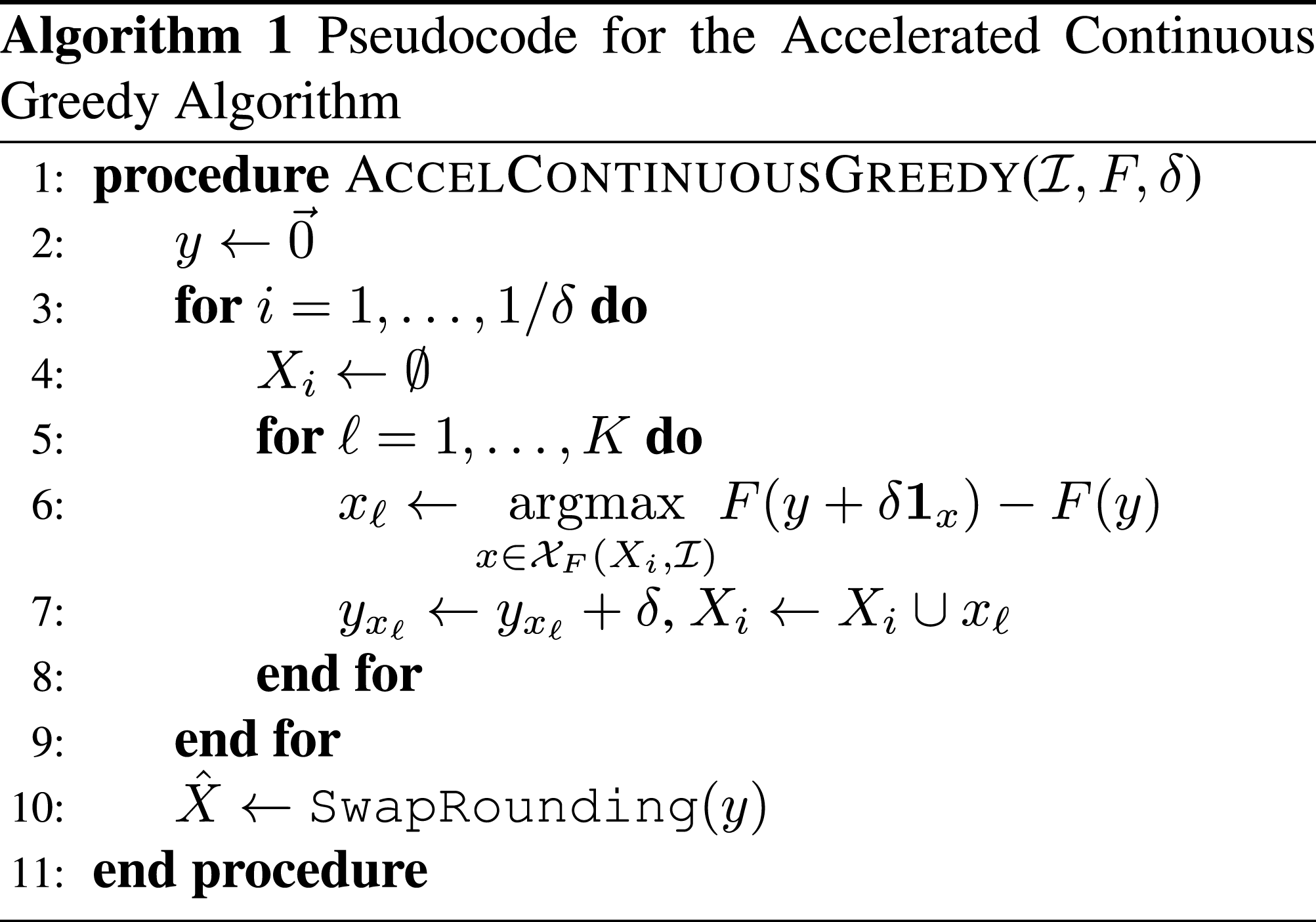
The accelerated continuous greedy algorithm (ACGA) recently proposed by Badanidiyuru and Vondrák (2014) optimizes the multilinear extension using coordinate gradient ascent (see pseudocode in Algorithm 1) and achieves a 1 − e−1 guarantee. For practical implementations the algorithm is discretized using steps of size δ ≪ 1. During each step the algorithm constructs an independent set by greedily maximizing the multilinear extension (line 6). After selecting each item, the corresponding component of the vector y is incremented by δ. After 1/δ independent sets are selected, the fractional solutions represented by y are rounded into an integral solution by calling the SwapRounding procedure from Chekuri et al. (2010). In particular, Theorem 2.1 from Chekuri et al. (2010) states that if X is the output of SwapRounding given a vector y in a matroid polytope (which always holds in the context of this paper), then X is independent,
2.4 Graphs
Let
3. Formal problem statement
Let Illustration of the notation used. A robot plans to take path ρ, whose edges are represented by lines. The fill of the lines represent the value of s
n
(ρ). In this example s3(ρ) = 0, which means that a3(ρ) = a4(ρ) = a5(ρ) = 0. The variables z
j
(ρ) are zero if either the robot fails before reaching node j or if node j is not on the planned path.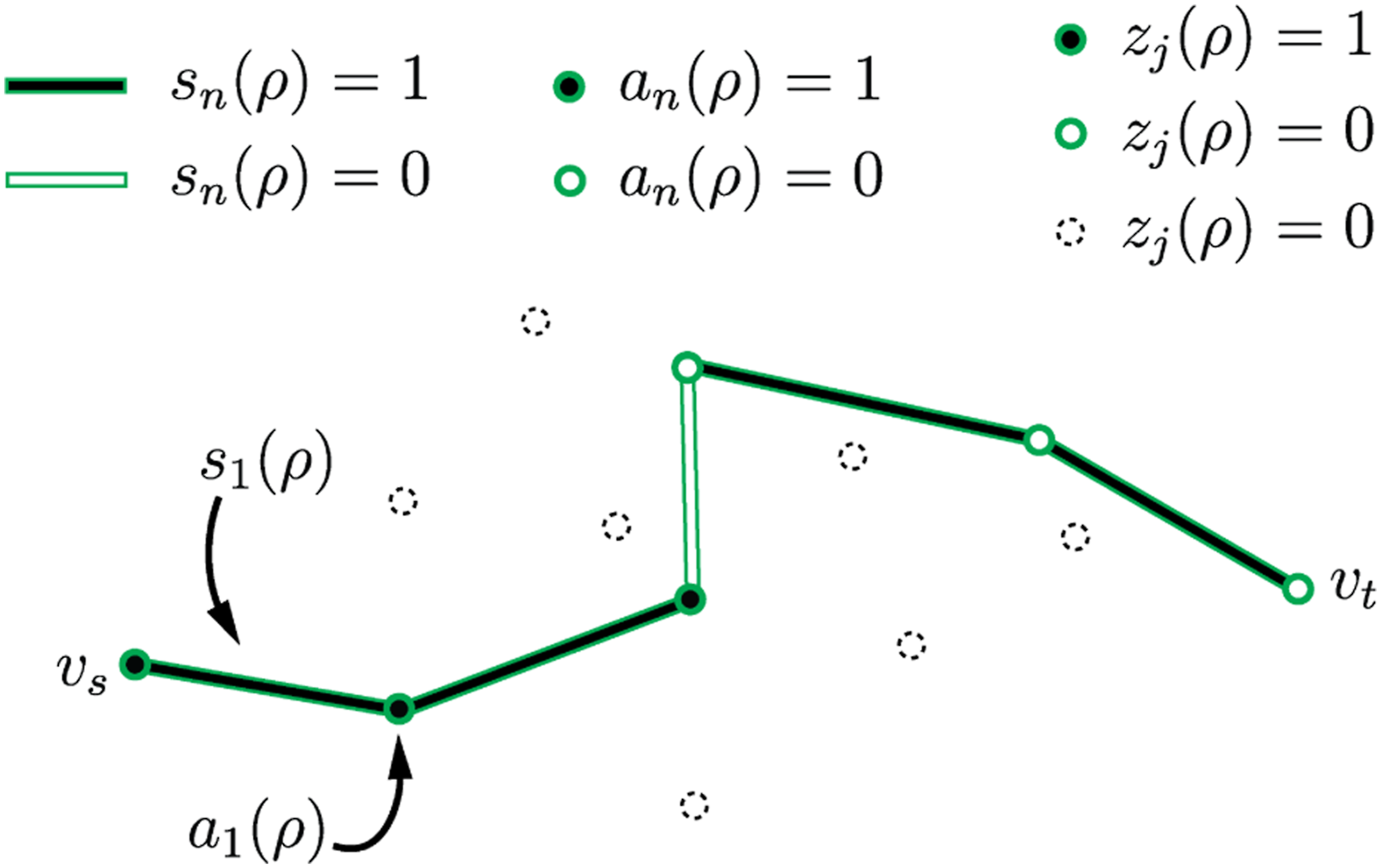
Given a start node v
s
, a terminal node v
t
, and survival probability p
s
we must find at most K ≥ 1 paths
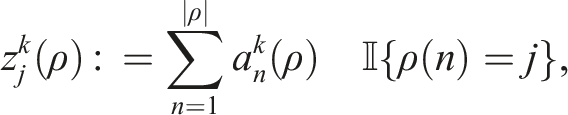
Define the indicator function
Let d
j
> 0 be the reward accumulated for visiting node j at least once, and define
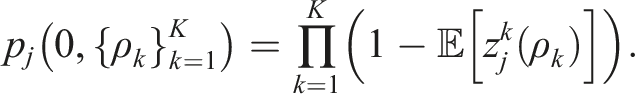
The optimization is over the independent sets of the matroid, and the solution is a set of K paths. The objective represents the cumulative expected reward obtained by the robots following the selected paths. The first set of constraints enforces the survival probability, the second and third sets of constraints enforce the initial and final node constraints. Note that we can also consider an “unrooted” variant by adding a new start and end node which have zero-weight edges to all nodes in
The MTSO problem can be viewed as a set maximization problem with a matroid constraint, where the domain of optimization is the family of independent sets
4. Examples and applications
In this section we highlight several examples of matroids and their applications in the context of the MTSO problem.
4.1. Uniform matroid
Given a positive integer K, the independent sets of a uniform matroid are all subsets of the ground set
4.2. Binary matroid
Given a function
Application to coverage: Consider a setting where we require each robot to focus on a different region. Define the regions as M node subsets
4.3. Transversal matroid
Given subsets
Application to coverage: Note that the coverage constraint from Section 4.2 can be represented via a transversal matroid.
Application to launch constraints: Consider a scenario where only one robot can start on each outgoing edge of v
s
. This could arise, for example, when robots are aerial vehicles which must launch from runways, and only one can launch from a runway in each direction. Let N(v
s
) be the set of nodes with an edge to v
s
, and define the subsets
Application to heterogeneous teams: Suppose we have M types of robots, a robot of type m has feasible path set
Application to traffic constraints: Suppose we have a scenario with disjoint regions of interest, each robot may visit exactly one region, and each region has a traffic constraint which limits the number of agents which can visit it. We represent the regions by disjoint node sets
Application to risk constraints: Suppose we have M survival probability thresholds
4.4. Gammoid
Gammoids allow us to express (among other things) nested cardinality constraints such as “select up to N1 elements with trait 1, and of those elements up to N2 can have trait 2, and of those elements, …” A Gammoid is represented formally by defining a graph to represent the notion of independence (see Figure 3 for an example). Illustration of multi-partite graphs which form the gammoid described in Section 4.4. A subset 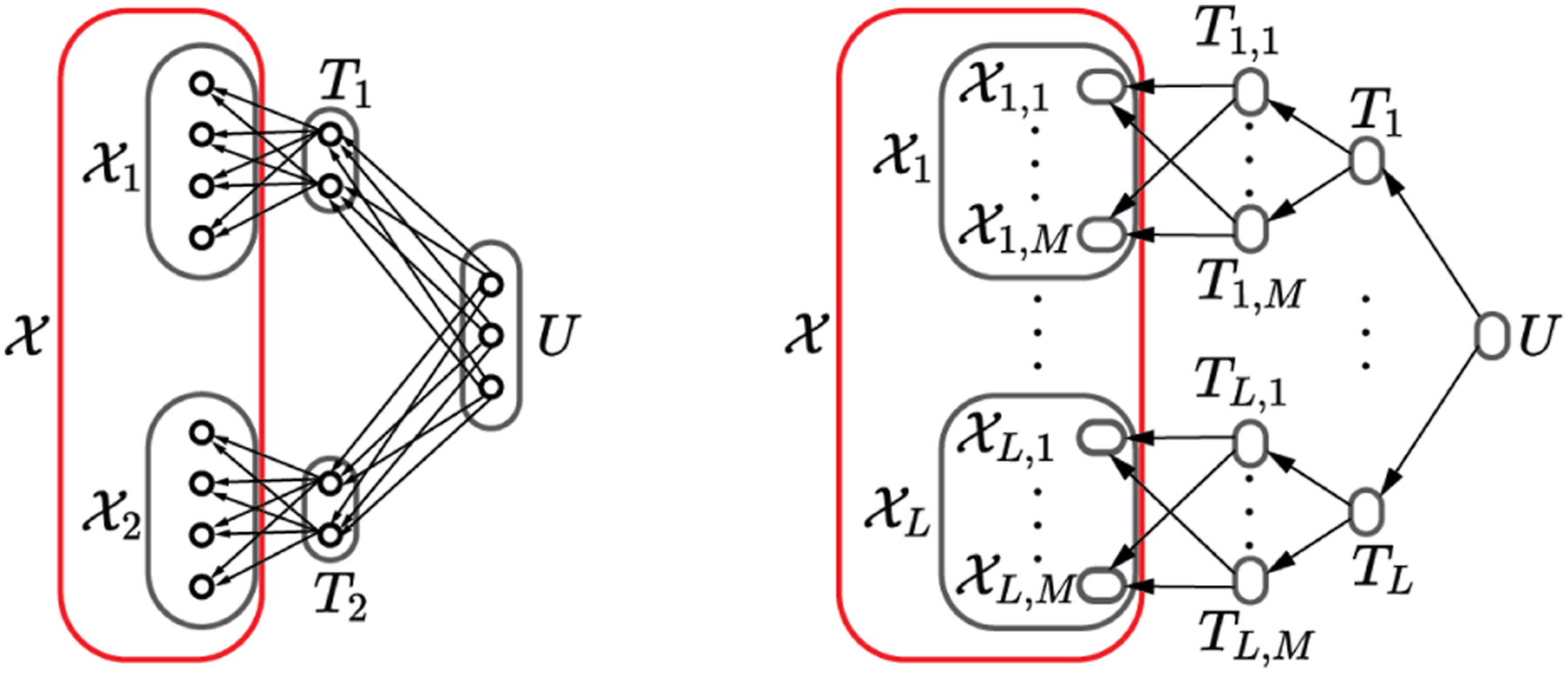
A gammoid is induced by a directed graph D(S, E) with a subset of nodes corresponding to elements in the ground set, for example,
Application to nested cardinality constraints: Consider a simple setting where the ground set is partitioned by the sets
This form of a gammoid is also known as a laminar matroid. It is important to note that this method of combining constraints is different from a matroid intersection—matroid intersections form a p-system and have weaker theoretical results described in Section 7.1.
4.5. Truncation
Given
5. Algorithms
In this section, we give greedy and accelerated continuous greedy approaches to solving the MTSO problem and give bounds on their suboptimality. Both algorithms solve single-robot sub-problems where a path from the feasible set is sought which approximately maximizes a path-dependent reward function. Accordingly we start by describing this sub-problem in detail in Section 5.1, which shows how to solve it as a series of orienteering problems, provides guarantees on the path quality, and a detailed discussion of implementation considerations for the examples given in Section 4. We then describe the greedy and accelerated continuous greedy approaches in Sections 5.2 and 5.3, respectively. Both of these sections describe how to form the appropriate sub-problem, the complete algorithm, performance guarantees, and computational complexity.
5.1. The greedy sub-problem
In this section we discuss the greedy sub-problem, giving a description of our solution approach in Section 5.1.1, discuss performance considerations in Sections 5.1.2, and its applications in Section 5.1.3.
5.1.1. Objective and algorithm
Given a (possibly empty) previously selected set of paths,
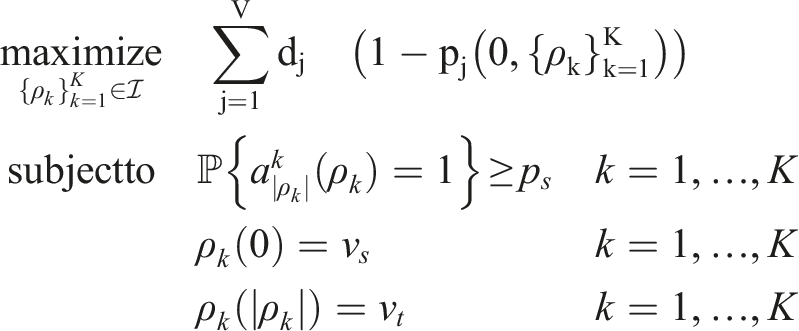
We address the path dependence by using a path independent approximation,
We give concrete examples for computing
We address the matroid constraint by noting that the feasible set,
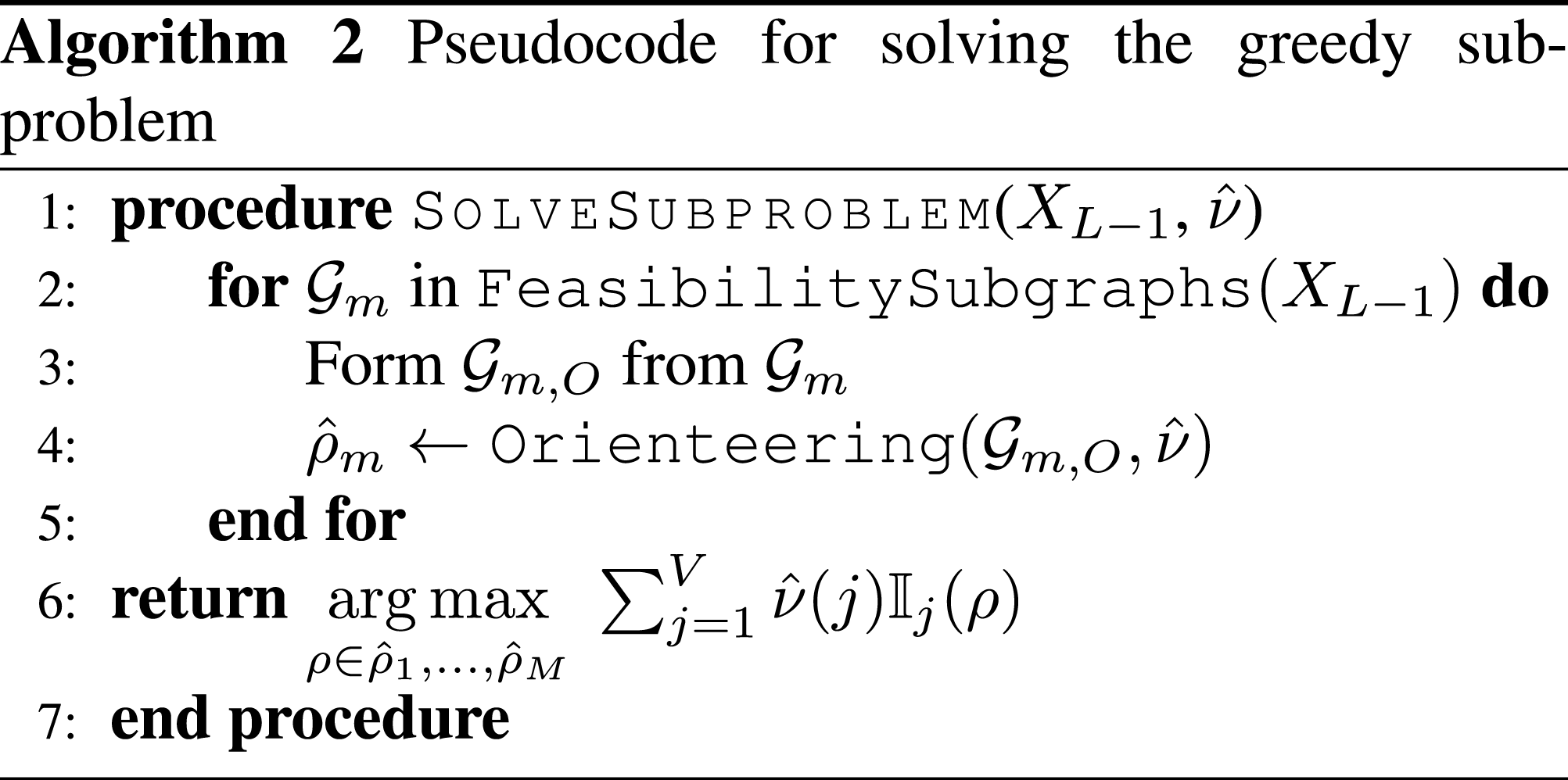
Our approach to solving the sub-problem is given as pseudocode in Algorithm 2. We begin by calling the
The following lemma guarantees that the path returned has similar value as the optimum:
Sub-problem guarantee. Consider an MTSO problem with node weights d
j
, let ρ be a feasible path in
By definition of Suppose the computational complexity of the Orienteering routine given any subgraph is bounded by C
O
, the complexity of the FeasibilitySubgraphs routine is bounded by C
F
, and the FeasibilitySubgraphs routine returns at most M subgraphs. Then, the complexity of the SolveSubproblem routine is C
F
+ MC
O
. We describe each of these terms in more detail below.
5.1.2. Complexity of the orienteering problem
Although the orienteering problem is NP-hard, various communities of researchers have developed solution approaches focusing on different properties of the solution—performance guarantees, on-line bounds, and run time. Depending on the oracle routine used, the SolveSubproblem routine has different guarantees and properties, namely,
Complexity theory guarantees—From a theoretical standpoint, if a polynomial time approximation scheme (PTAS) for the orienteering problem is used and the FeasibilitySubgraphs routine is polynomial time (meaning M is also polynomial), then our algorithm is a PTAS for the greedy sub-problem. Since our higher level routines call SolveSubproblem a polynomial number of times, this is a meaningful result on the complexity of the MTSO problem: although the MTSO is NP-hard, it can be approximated within a constant factor in polynomial time when there is an efficient FeasibilitySubgraphs routine. The complexity of the best known PTAS routines for the orienteering problem and its variants are high order polynomials—for example, Chen and Har-Peled (2006) gives a λ = 1 + ϵ PTAS for the case where points are on a d − dimensional plane that runs in
Certifiable performance guarantees—Practitioners who require guarantees on the quality of the solution and more modeling flexibility can use mixed integer linear programming (MILP) formulations of the orienteering problem (e.g., Kara et al. (2016)). Commercial and open-source software for solving MILP problems are readily available, and return an optimality gap along with the solution. Such solvers can be configured to terminate after a set amount of time or when the ratio between the current solution and upper bound becomes greater than 1/λ.
Real-time properties—Finally, practitioners who require fast execution but not guarantees can use a heuristic to solve the orienteering problem. There are a number of fast, high quality heuristics with open-source implementations such as Wagner and Affenzeller (2005); Vansteenwegen et al. (2009). While these heuristics do not provide guarantees, they often produce near-optimal solutions and are capable of solving large problems in seconds.
5.1.3. Efficiently covering the feasible set
For many examples we can cover the feasible set using a small number of subgraphs, as detailed below. These descriptions are brief, but we also provide a GitHub repository with implementations for the following examples (ASL Github 2023).
Coverage—We can cover the sets for the coverage example by adding a constraint to a mixed integer formulation which requires the solution to have a specific focus. In this case M would be the number of regions to be covered.
Launch constraints—Given a set X
k
, all paths which take edges (v
s
, ρ
ℓ
(1)), ℓ = 1, …, k are infeasible. Hence M = 1 and the subgraph is the graph induced by the edges
Heterogeneous teams—The feasible sets are already covered by graphs
Traffic constraints—Since the feasible path sets
Risk constraints—Given a set of paths X
k
, the FeasibilitySubgraphs routine finds the smallest value
Nested cardinality constraints—Given a set of paths X
k
, the FeasibilitySubgraphs routine tests whether a path can be added to each of the sets in the deepest layer (which partitions
5.2. The approximate greedy algorithm
In this section we describe a greedy algorithm for solving the MTSO problem. We describe the objective function and detailed algorithm in Section 5.2.1, then give performance guarantees in Section 5.2.2, and characterize the complexity in Section 5.2.3.
5.2.1. Objective and algorithm
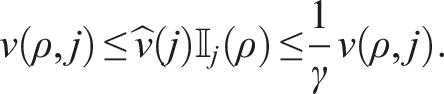
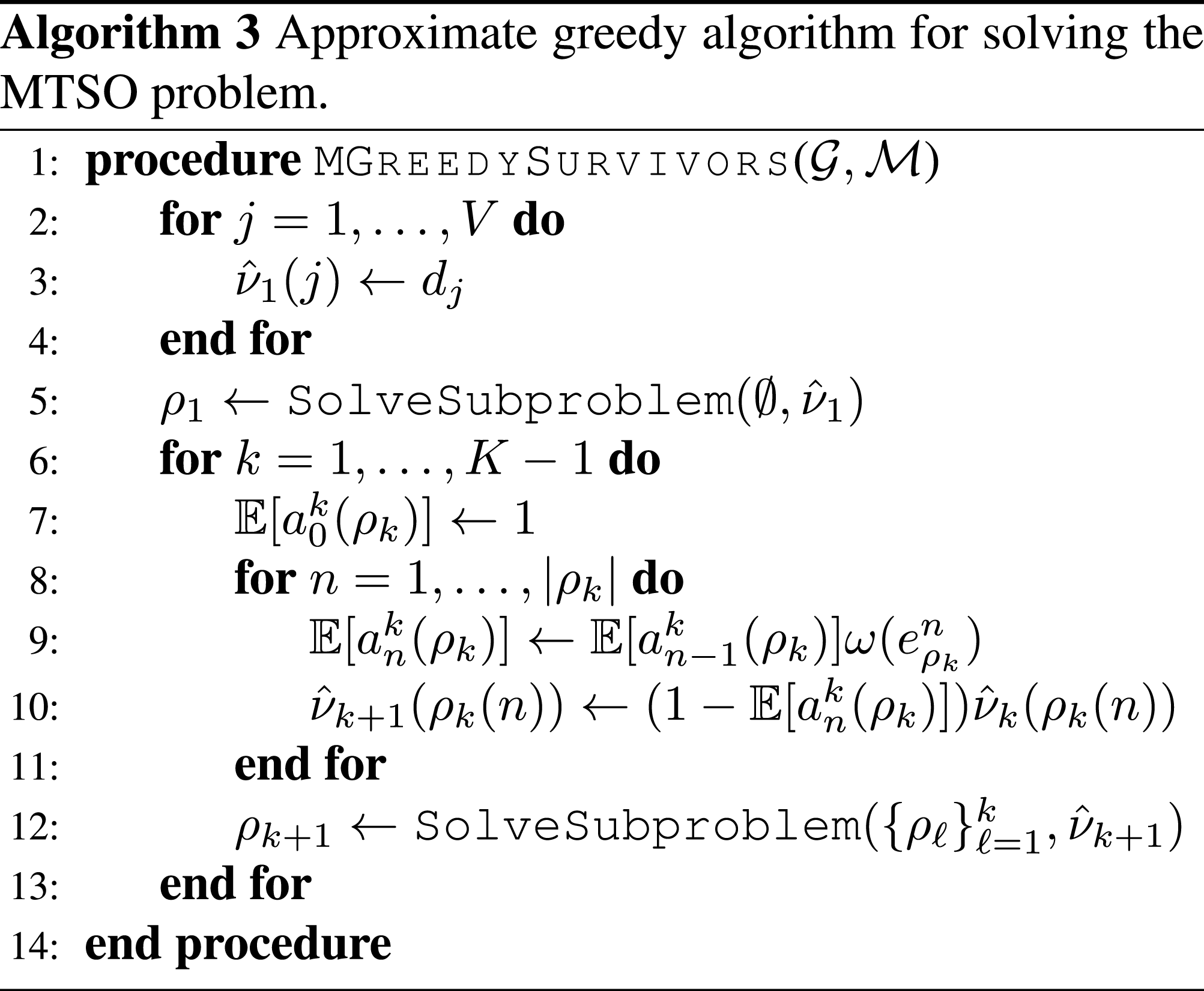
The greedy algorithm operates by iteratively selecting a path which maximizes the discrete derivative of the objective function for the MTSO given the set of previously chosen paths
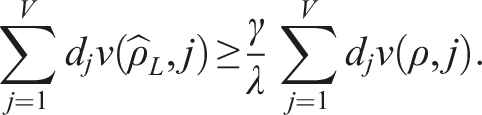
5.2.2. Guarantees
We combine the results from Section 2.3 and 5.1.1 to guarantee that the value of the output of Algorithm 3 is close to the value of the optimal solution to the MTSO problem.
Approximate greedy guarantee. Let X* be an optimal solution to the MTSO problem, and
Setting In many scenarios robots are either valuable or difficult to replace, and so operators will choose survival probability thresholds p
s
which are close to 1. Combined with an effective oracle routine, Theorem 2 guarantees that the greedy approach never collects less than approximately half of the optimal reward. This is a strong statement, since solving this problem optimally is extraordinarily difficult (especially as the team size grows).
5.2.3. Complexity
Algorithm 3 has complexity O(KV2 + K(MC
O
+ C
P
)), where the first term is the complexity of updating the V node weights K times (each update costs at most V multiplications), and the second term is the complexity of calling the
5.3. The accelerated continuous greedy algorithm
In this section we describe an accelerated continuous greedy algorithm for solving the MTSO problem. We begin by describing the objective function and detailed algorithm in Section 5.3.1, then give performance guarantees in Section 5.3.2 and characterize the complexity in Section 5.3.3.
5.3.1. Objective and algorithm
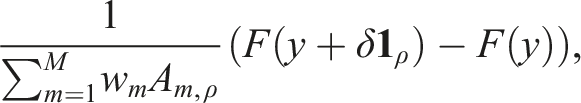
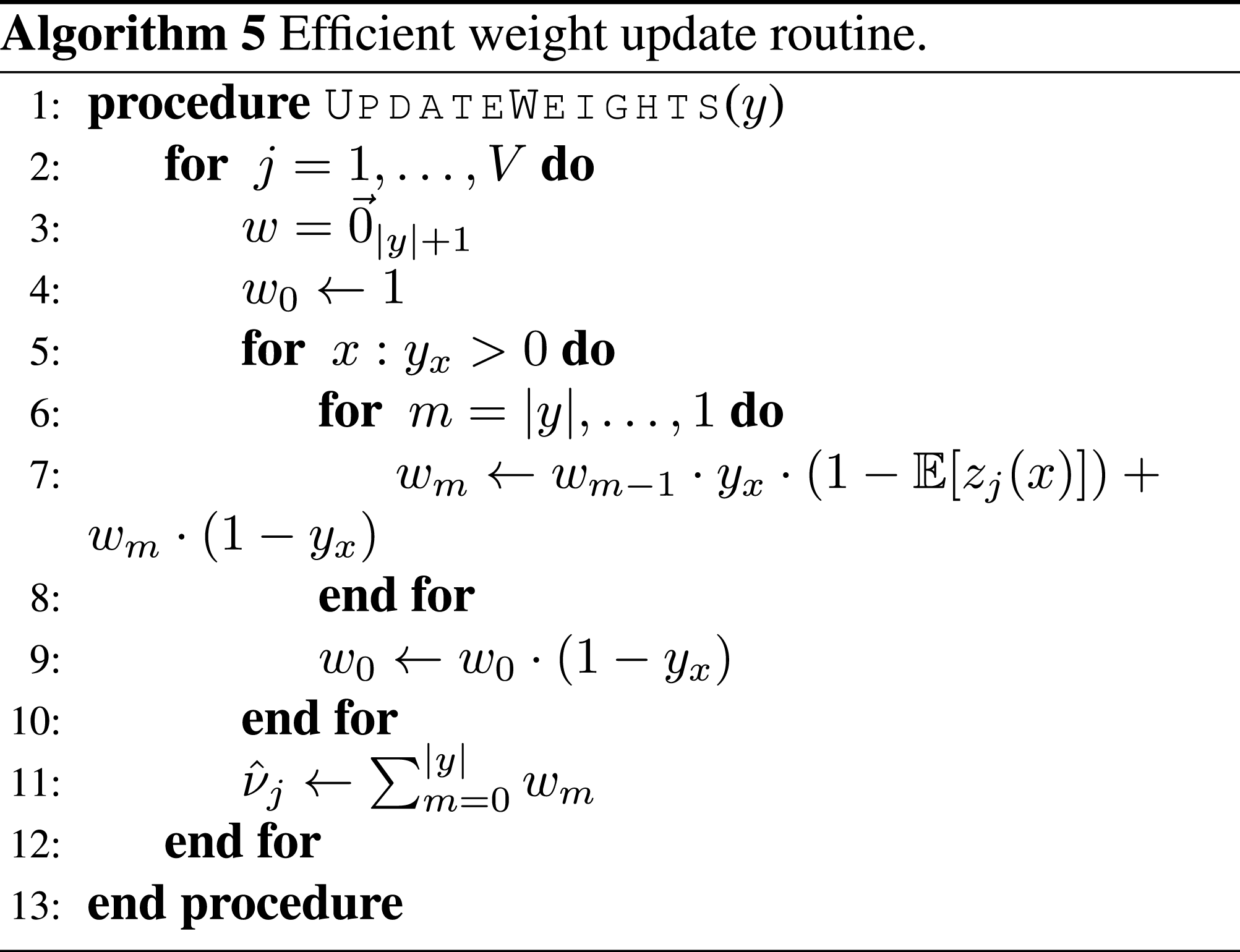
The accelerated continuous greedy algorithm (Badanidiyuru and Vondrák 2014) performs a discretized coordinate gradient ascent which optimizes the multilinear extension along “coordinates” corresponding to independent sets in the matroid. The state of the algorithm is given by a sparse vector
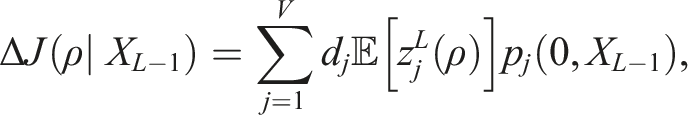
The objective for the ACGA can be written as an expectation with respect to the random set R(y), which contains elements in
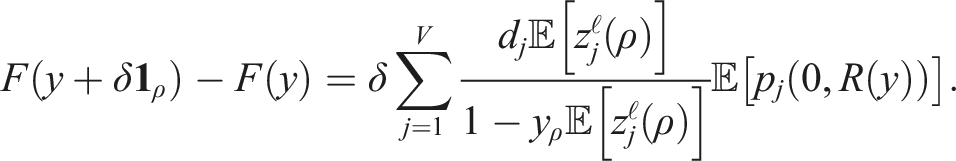
The following lemma gives an alternate expression for the objective in terms of a sum over path-dependent node rewards:
Objective function for the ACGA. Let f be the objective of the MTSO and F its multilinear extension. The objective for the ACGA with state y during the ℓth iteration of the ith step can be written as This result is derived directly from the definitions of the relevant variables (a detailed proof is given in the Appendix). Pseudocode for our algorithm is given in Algorithm 4, which consists of three main parts: (1) efficiently computing 1) Efficiently computing 2) Removing path dependence for the sub-problem: The objective is path-dependent because the term 3) Rounding the solution: We use the SwapRounding procedure to round y in order to get our final solution. In order to ensure that we achieve a good result we repeat the rounding procedure until the result is at least (1 − δ)F(y). The expected number of calls to the rounding routine is upper bounded by
Note that the set X
F
is sparse because y has at most K/δ non-zero entries—the search over a large set of paths is encapsulated within the SolveSubproblem routine.
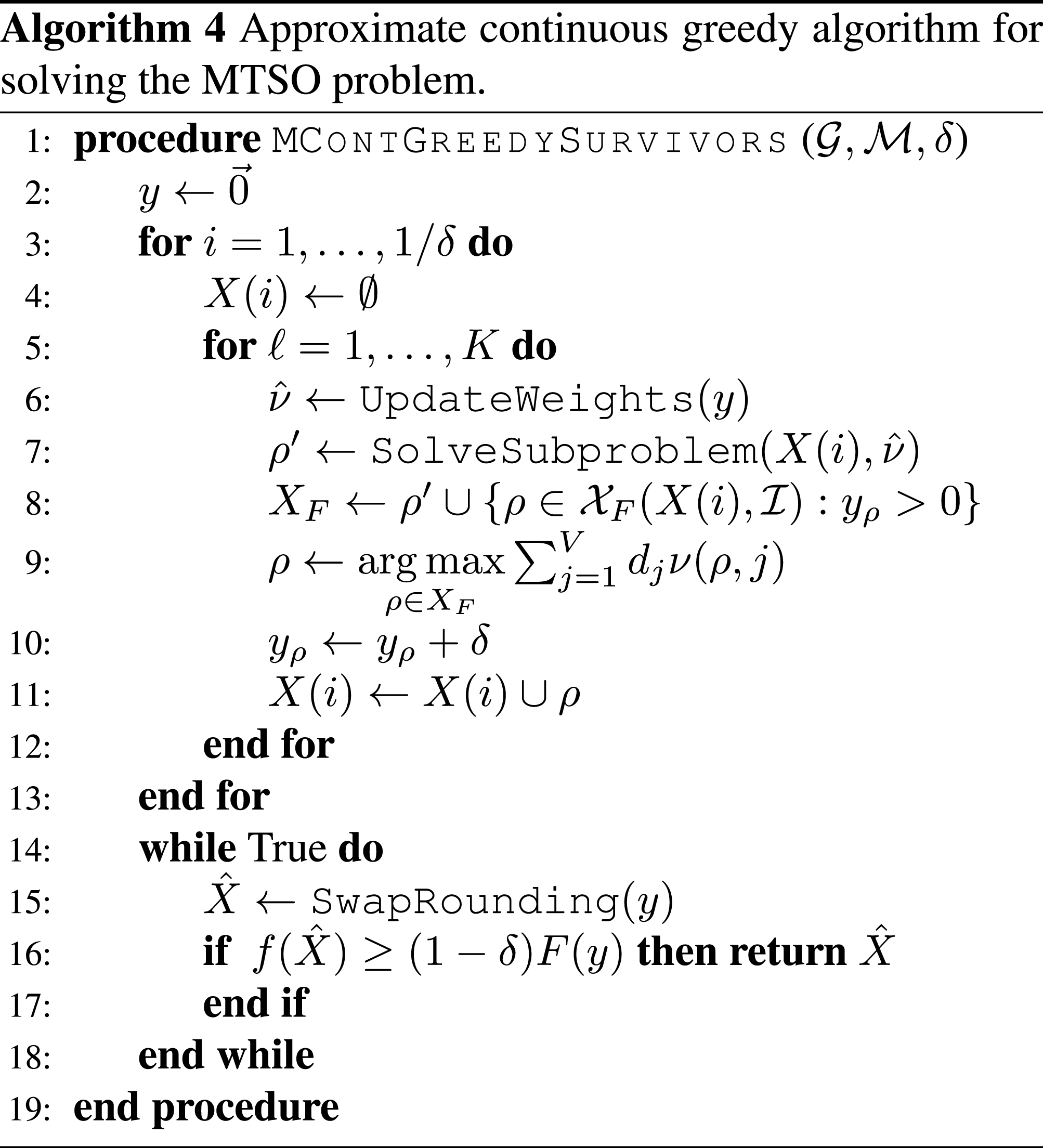
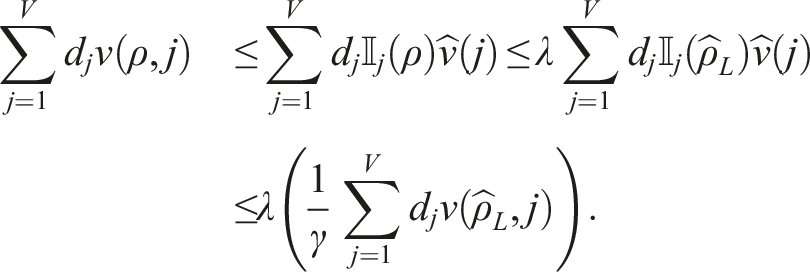
5.3.2. Guarantees
Combining our results from Sections 2.3, 5.1.1, and 5.3.1 we provide the following performance guarantee for Algorithm 4:
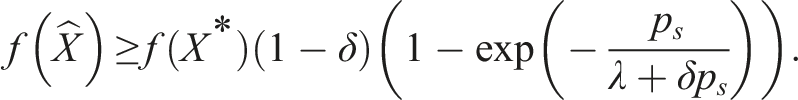
Suboptimality bound. Let X* be an optimal solution to the MTSO problem and The detailed proof is given in the Appendix. The basic idea is to first use the properties of the SolveSubproblem routine to lower bound the incremental increase in the multilinear extension between subsequent steps of the algorithm, then to use a recursive argument to show that F(y) satisfies the desired inequality, which in turn ensures that Tightness of the guarantee—As the approximation parameters converge to their ideals (δ → 0, λ → 1, p
s
→ 1), the guarantee converges to
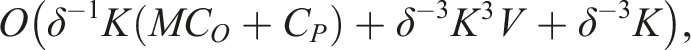
5.3.3. Complexity
Algorithm 4 calls the UpdateWeights routine K/δ times, solves K/δ sub-problems, and calls the
6. Experimental results
In this section we validate and compare our solution approaches using simulations. In particular, we demonstrate the rich sets of constraints a matroid can model in Section 6.1, where we consider a challenging environmental monitoring scenario and compare two choices for the Orienteering oracle. Section 6.3 quantifies the empirical scaling of our algorithm using synthetic data. In particular, section 6.3.1 shows that Algorithm 3 scales as expected as the team size and number of sub-problems required to cover the feasible set grows, and Section 6.3.2 shows that the runtime of Algorithm 4 scales as expected with respect to δ. Finally, in Section 6.4 we compare Algorithm 3 and Algorithm 4 approaches for a range of δ values and discuss the strengths of each approach.
6.1. Environmental monitoring application
We consider the application illustrated in Figure 1: the Coral Triangle has a diverse ecosystem and the goal is to use a robotic fleet with multiple sensor configurations to monitor the wildlife populations in “Marine Protected Areas.” We use piracy incident data International Chamber of Commerce: Commercial Crime Services (2017) and model attacks as a Poisson random variable in a manner similar to Vaněk et al. (2013). We selected 106 marine protected areas from Cros et al. (2014) as nodes in a complete graph and computed the shortest (minimum risk) paths between each pair of sites to find the edge weights. In our scenario, we can deploy up to 25 robots of three types (at most twelve of each type), and each robot type has a different utility in each region. Each region can support the traffic of at most three robots of each type.
We require that the expected losses over the worst 5% of outcomes be no more than five failed robots (this is called the Conditional Value at Risk, and denoted CVaR0.05). For the data shown, the most difficult node to reach requires survival probability 0.64, but if we use a uniform survival probability threshold p
s
= 0.64, the risk is unacceptably high (CVaR0.05 = 16.26). We satisfy the constraint CVaR0.05 ≤ 5 by setting
We consider two choices for the Orienteering routine: an open-source Variable Neighborhood Search (VNS) heuristic produced by HeuristicLab (Wagner and Affenzeller 2005) and a mixed integer linear program (MILP) formulation solved using CPLEX with a 5% tolerance. We observe that the VNS heuristic gives near-optimal paths, and solves all of the sub-problems for each of the twenty five robots in 51 seconds on a quad-core 4GHz processor with 32GB RAM available. The MIP oracle takes 60 seconds and yields nearly the same results. While the MIP oracle can find high quality paths quickly, as the tolerance is decreased the computation time dramatically increases. Optimally solving the sub-problems does not necessarily lead to better overall behavior, as shown in Figure 4. The upper bound shown is computed as the smaller of 1) the upper bound found using the greedily selected paths and the approximation ratio, and 2) the sum of all node rewards Cumulative reward for paths planned by Algorithm 3 using the MIP and VNS Orienteering routines. Both approaches compute high quality sets of paths, though VNS is somewhat faster.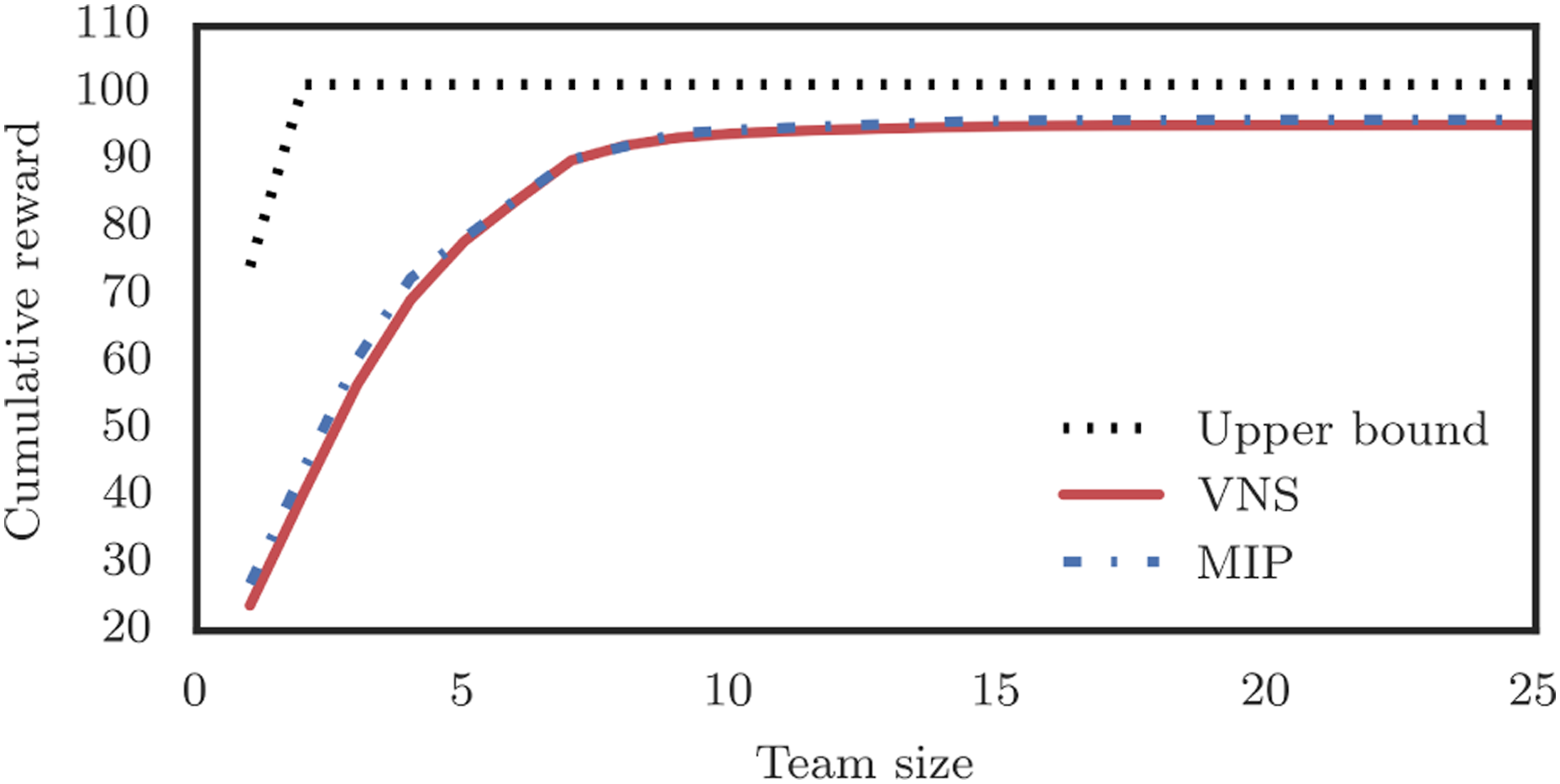
6.2. Lazy evaluations
Lazy evaluation (Krause and Golovin 2014) is an important practical modification to submodular maximization algorithms. Each time an orienteering problem is solved, we can use the optimality gap from the solver to bound the maximum reward of any path in the subgraph. Since the value of a path is a decreasing function as the algorithm progresses (due to submodularity), these bounds can be used in the following iterations.
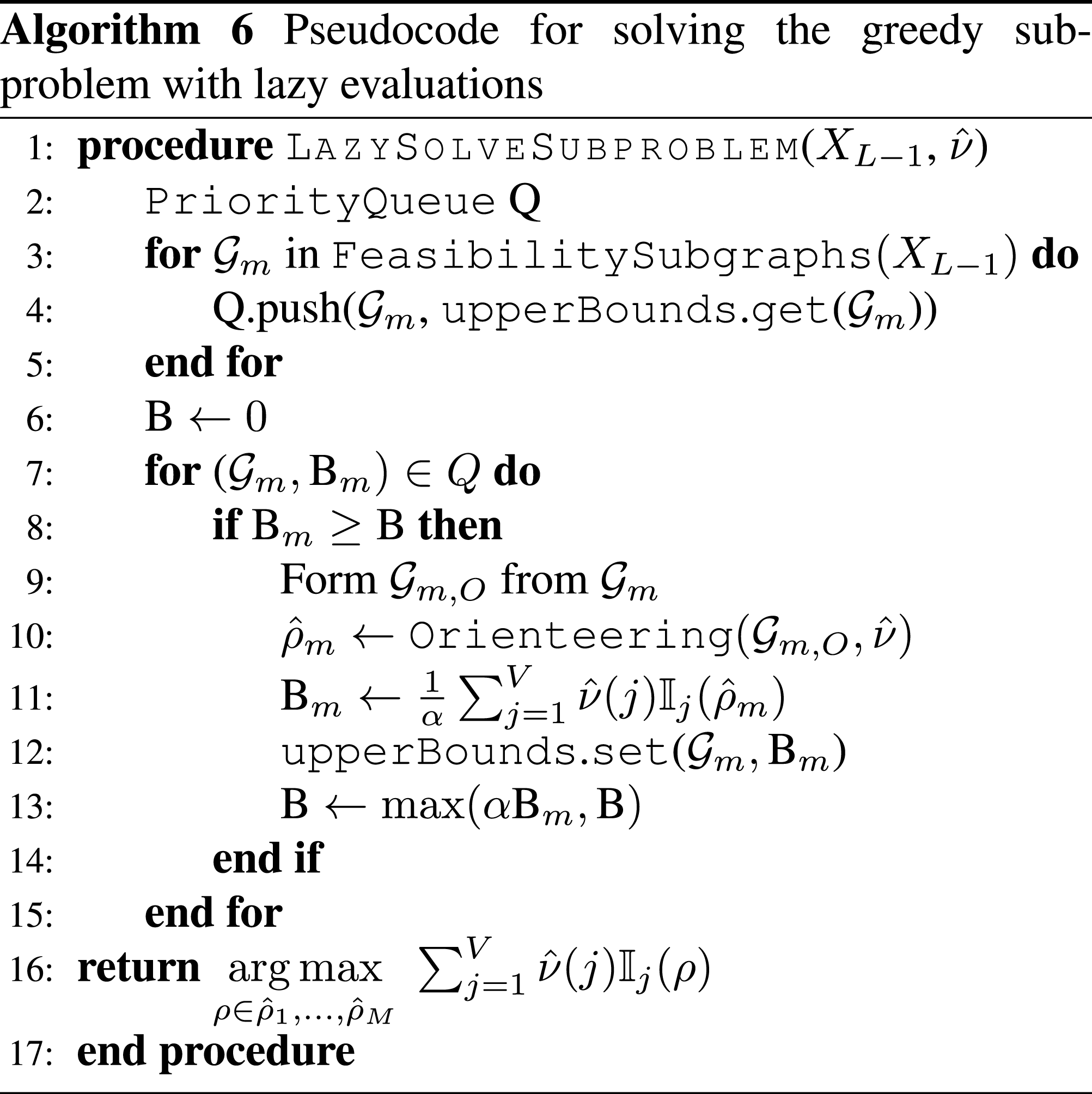
We implement this LazySolveSubproblem routine by adding a priority queue to sort subgraphs based on their upper bounds, and a database to track the upper bounds between calls to LazySolveSubproblem. Let upperBounds be a persistent map data structure with method set(key, value) which assigns the value associated with the key, and method get(key) that returns the stored value for that key or ∞ if no value is stored. The pseudocode for this approach is given in Algorithm 6 and a more detailed example is provided in the GitHub repository (ASL Github 2023).
6.3. Synthetic problem generation
We demonstrate the scaling properties of Algorithm 3 and Algorithm 4 using synthetic data. Nodes are placed randomly on a 2D plane and clustered into groups of 15-20 nodes. This ensures the complexity of solving the orienteering problem, C O , is constant and allows our analysis to focus on the other aspects of our algorithm. We refer readers interested in the complexity of the orienteering problem to the literature in Section 5.1.2 which treat the subject in detail.
We consider a traffic constraint with subgraphs induced by the clusters. Edge weights are chosen so that −log(ω(e)) is proportional to the length of the edge e, the survival probability threshold is set to 0.7, and we use a MILP formulation for the planar orienteering problem with tolerance 5%. An illustration of the paths selected for one instance is shown in Figure 5 Illustration of a set of paths produced by our algorithm for a synthetic data set. Colors are used to distinguish paths taken by different robots (the lines) and nodes in different regions (the dots).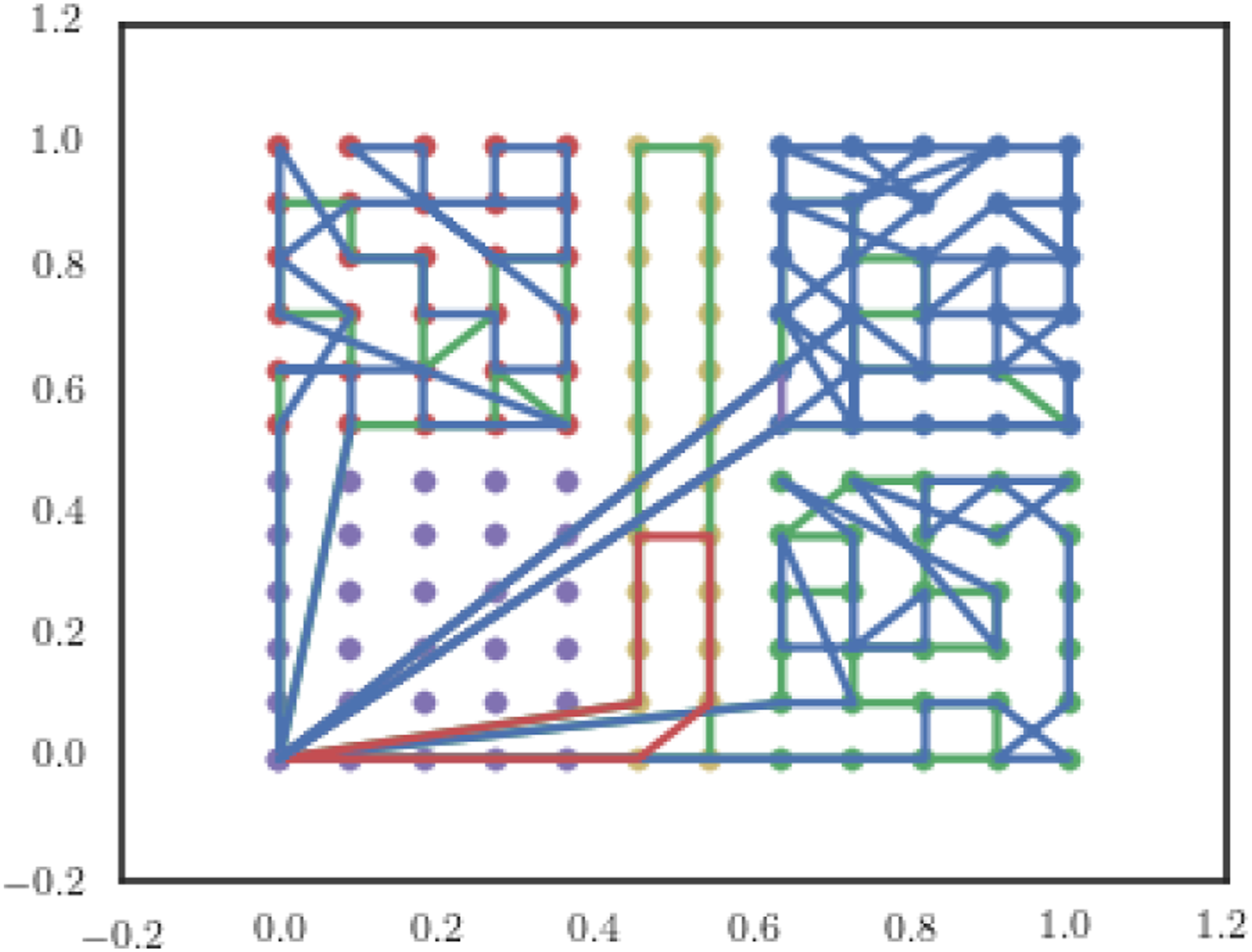
6.3.1. Sub-problem complexity scaling
We demonstrate the complexity of the Algorithm 3 with respect to K and M using the synthetic dataset described above. Using the lazy evaluation strategy described in Section 6.2 allows us to skip 75% of the sub-problems in this experiment. The median computation times are shown in Figure 6. Scaling of Algorithm 3 as K and V grow. Data shown is the median of 110 samples, and agrees with an Θ(MKC
O
) trend.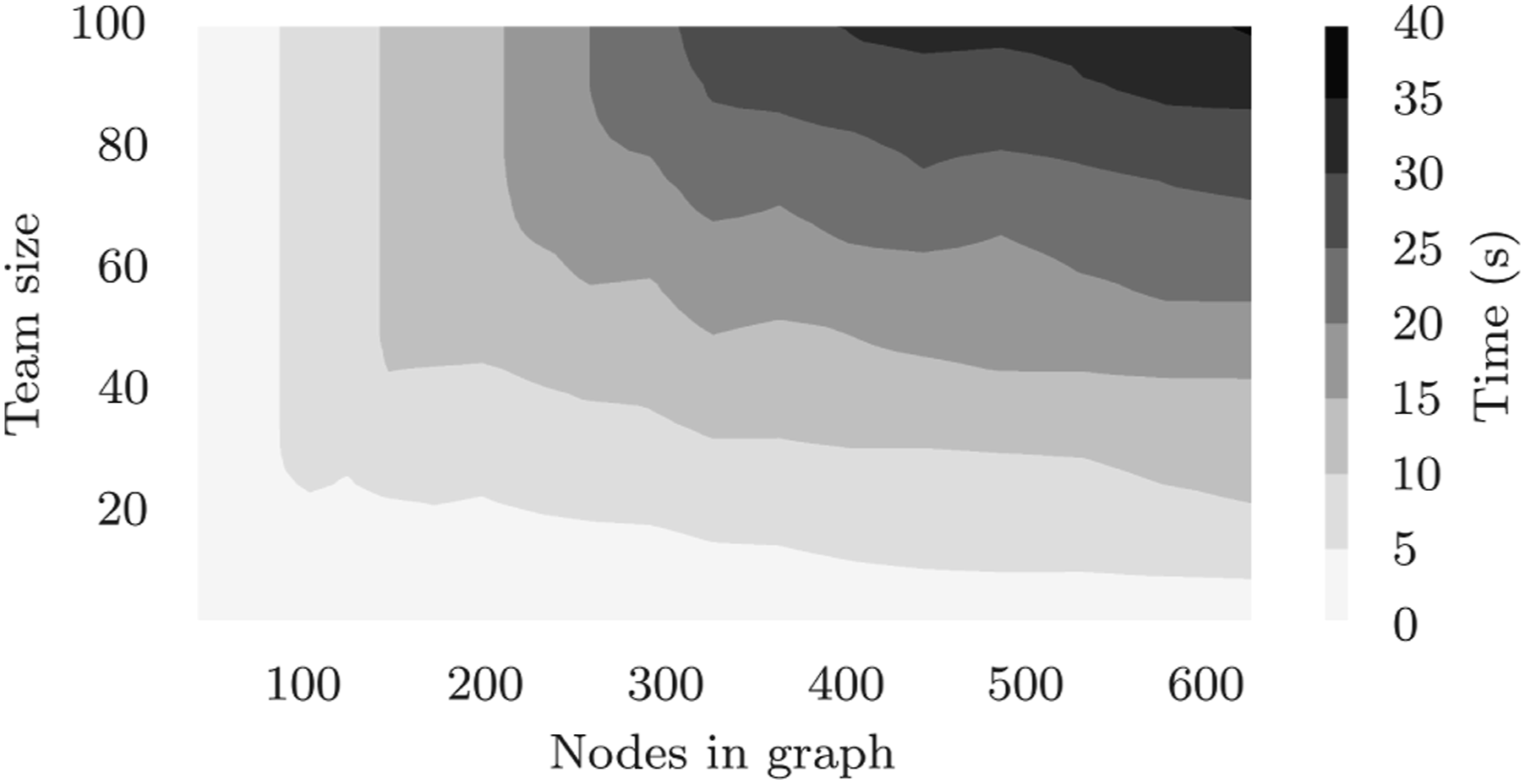
The complexity analysis from Section 5.2.3 suggests that since C O is constant, compute should scale as the product MK. The x-axis in Figure 6 is proportional to M, and the y-axis is proportional to K. A visual comparison of this figure with a contour plot off(x, y) = xy verifies that the compute scaling is consistent with the predicted O(MKC O ) complexity.
For this size of sub-problem our approach solves large problems with very large teams in under a minute—the reasons for this are threefold: First, any given subgraph has a small size; Second, we permit the solver to terminate once it finds a solution within 5% of the optimal; and Third, we are using a high performance solver (Gurobi). In practice there are many approaches to solving the underlying orienteering problems (as discussed in Section 5.1.2) and solvers should be tuned to the hardware and particulars of an application, so these figures should be viewed as a baseline.
6.3.2. Discretization complexity scaling
As discussed in Section 5.3.3, we expect the run time of Algorithm 4 to be roughly δ−1 times that of Algorithm 3 (which is Algorithm 4 with δ = 1). We demonstrate this trend empirically by using the synthetic data generated as described at the beginning of this section (with V = 82 and K = 8). For each problem we compute the baseline by averaging the run time of 5 calls to Algorithm 3. We then measure the run times of Algorithm 4 with the desired δ values and use the ratio of Algorithm 4 run times to the baseline run time as our datapoints. We repeated this for 30 randomly generated problems and show the results in Figure 7. The randomness in run times is due to several factors (1) lazy implementation allows for problems to be skipped when good bounds are available, (2) MIP solver time can depend significantly on the particular problem, and (3) MIP solver times are not deterministic. Scaling of the run time of Algorithm 4 relative to Algorithm 3 as the number of discretization steps increases. Note that run time increases approximately linearly with δ−1, as predicted in Section 5.3.3.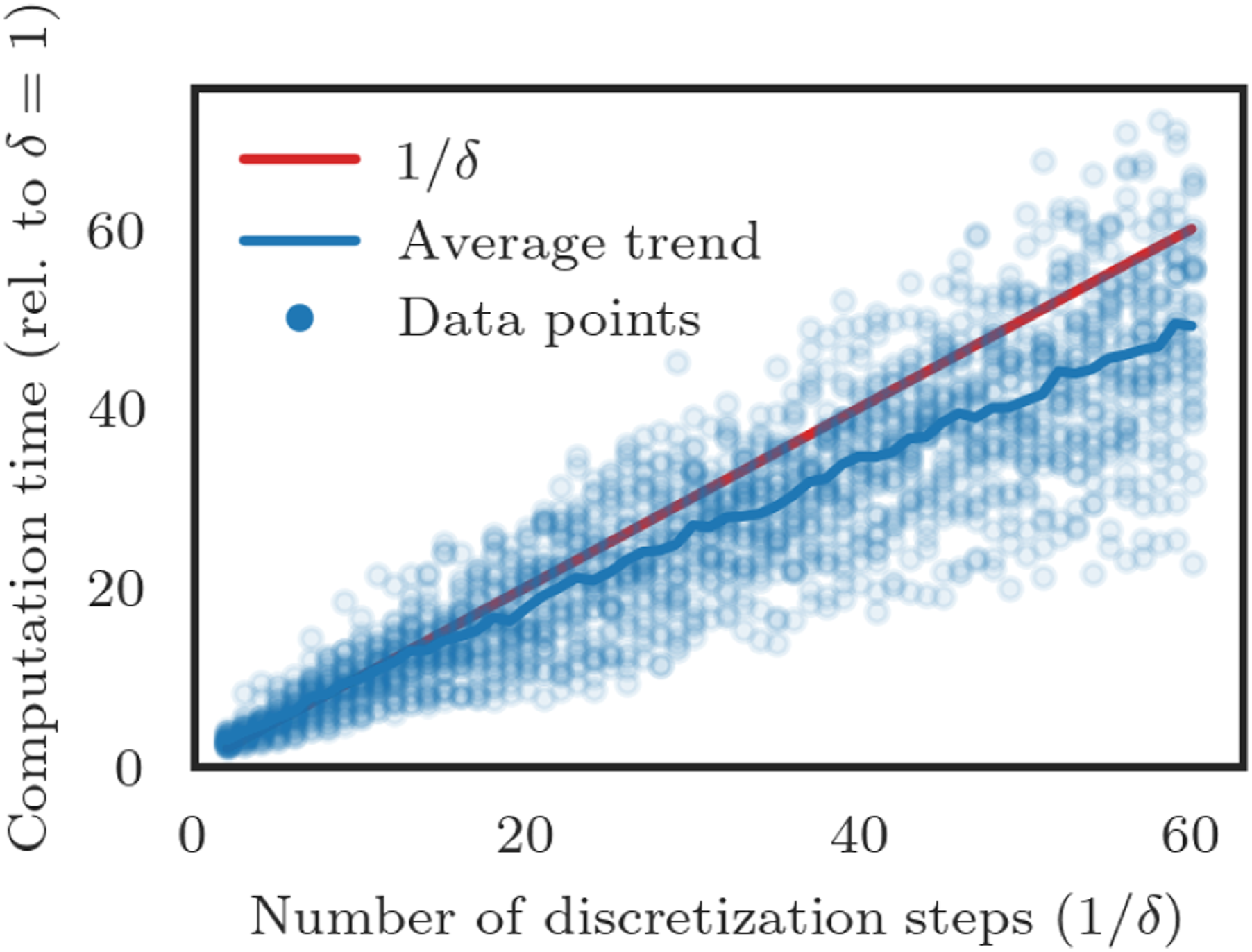
6.4. Effect of discretization on performance
Using the same data as in Section 6.3.2, we analyze the influence of the discretization parameter on the performance of Algorithm 4 relative to Algorithm 3 in terms of the value of their solutions. As shown in Figure 8, increasing δ−1 generally improves the performance, and generally increases the chance that the result produced by Algorithm 4 will be better than the result produced by Algorithm 3. Note that the benefits of smaller discretization sizes drop off faster than the increase in computation time, so in practice a relatively small value of δ−1 (e.g., 8 or 16) should be used. In scenarios where computation time is paramount, Algorithm 3 provides a fast way of achieving high quality solutions. Comparison of objective achieved by Algorithm 4 and Algorithm 3 with δ−1 ∈ {2, …, 60} for 30 random MTSO problems. Note that as δ−1 increases the Algorithm 4 more consistently outperforms the baseline and average performance increases.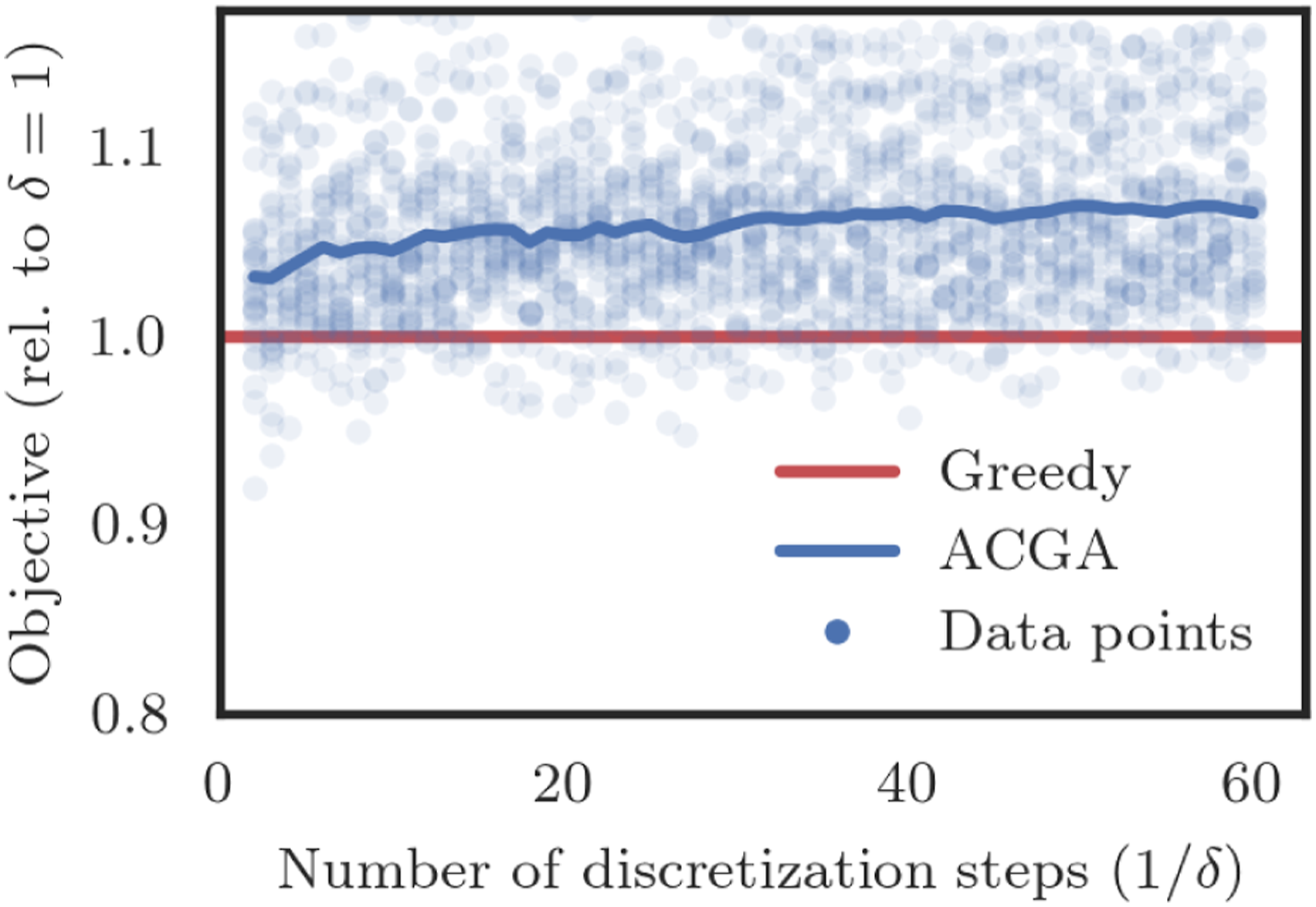
7. Extensions
In this section we discuss additional extensions and applications of our work. In Section 7.1, we describe p-systems and their applications to robotics. Minor modifications to algorithms presented above have constant factor guarantees for p-systems. In Section 7.2 we describe the coverage variant of the MTSO, which is closely related to our other work in Jorgensen et al. (2017b). Results from Chekuri et al. (2010) can be applied to provide guarantees for Algorithm 4 in this setting.
7.1. p-system constraints
Consider the MTSO where the matroid
7.1.1. Applications to robotics
Many common constraints in robotics can be modeled as a p-system:
Collision avoidance—Consider a setting where we do not allow two robots to simultaneously traverse the same edge in the graph (this also requires us to introduce a notion of time, which we discuss more in our work Jorgensen et al. (2018)). One can easily verify that collision avoidance is downward closed—any subset of a set of collision free paths will also be collision free. The value of p is easily bounded by the smaller of the out-degree of the starting vertex and the number of robots allowed.
Capacity constraints—Collision avoidance can be generalized to a capacity constraint, where each edge has a capacity, and each robot has a demand. We can require that the sum of demands for robots simultaneously traversing an edge must be below the capacity of the edge. Note that collision avoidance is a special case where all demands and capacities are equal. This scenario can model road networks as well as communications networks, where a video sensor may demand much more bandwidth than other types of sensors.
Matroid intersections—The intersection of p matroids is also a p-system. This can allow us to simultaneously enforce risk constraints, sensor availability, and traffic constraints. Note that this is different from the nested cardinality constraints used in the experiments. For example, we could require that at most 5 of the 25 paths planned are risky and that at most 12 of each robot type can be selected (rather than the nested case, which would say, e.g., at most 12 of the risky paths can be of a given type, and at most 12 of the safe paths can be of a given type).
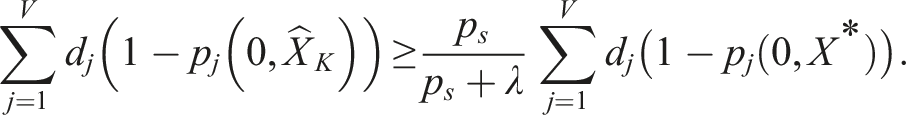
7.1.2. Algorithms and guarantees
We can use a slightly modified version of our algorithms above to find a set which is in the independent family of sets for a p-system and (approximately) maximizes the expected number of nodes visited. The only difference is that now the feasible set
The guarantee we state in Theorem 1 is a special case of the more general statement from Appendix B of Calinescu et al. (2007), which for a p-system gives the constant factor guarantee α/α + p. For our applications, we will typically constrain teams to have at most K robots which implies p ≤ K (since no set can have more than K elements). Using α = p s /λ this means that the guarantee can be written as p s /p s + Kλ, which while a constant factor, quickly becomes loose as the team size grows.
7.2. Multiple objectives and coverage problems
Consider a problem where we are given a set of submodular functions f1, …, f N , corresponding values V1, …, V N , and want to find a set X such that f n (X) ≥ V n for n = 1, …, N.
7.2.1. Applications to robotics
This problem could model a coverage variant of the MTSO, where we are seeking a set X which satisfies a matroid constraint while also ensuring that the probability node j is visited satisfies a given threshold, p v (j). In this setting we define the functions f j (X) = min{1 − p j (0, X), p v (j)} and set V j = p v (j). This is similar to the coverage variant of the TSO given in Jorgensen et al. (2017b), where we seek the smallest team which satisfies the desired visit probabilities.
7.2.2. Algorithm and guarantees
The algorithm for this case only requires minor modifications to our proposed algorithms, and would leverage the modifications to the continuous greedy algorithm outlined in Chekuri et al. (2010). Theorem 2.5 from Chekuri et al. (2010) guarantees that the output of the modified algorithm satisfies F
n
(y) ≥ (1 − e−1)V
n
for n = 1, …, N, or returns a certificate of infeasibility. In our case Algorithm 4 has a weaker
8. Conclusions
8.1. Summary
We formulate the Matroid Team Surviving Orienteers (MTSO) problem, where we seek a set of paths which forms an independent set of a matroid, maximizes the expected number of nodes visited by at least one robot, and ensures the probabilities each robot reaches its destination are above a threshold. This problem is a significant generalization of our earlier work on the Team Surviving Orienteers problem (Jorgensen et al. 2018), and is distinct from previous work because it combines a submodular objective, chance constraints, and matroid constraints. We give numerous applications of matroids to robotic path planning such as coverage, launch constraints, limits on the number of available robots of multiple types, restrictions on the amount of traffic which can flow through a region, and combinations of the above. The MTSO is particularly challenging to solve because of the risky traversal model (where a robot might not complete its planned path) which creates a complex, history-dependent coupling between the edges chosen and the distribution of nodes visited. We present two solution algorithms: an approximate greedy algorithm for solving the MTSO problem which guarantees that its output achieves at least
8.2. Future work
There are many directions for future work beyond those outlined in Section 7. The most promising is the extension to linear packing constraints (also called knapsack constraints). The multiplicative weight update (MWU) framework was used by Chekuri et al. (2015) to find a set X which optimizes a submodular function subject to linear packing constraints,
Footnotes
Acknowledgments
The authors would like to thank Jan Vondrák for helpful discussions about the accelerated continuous greedy algorithm and multilinear extension which started this work. The authors are also grateful to Robert H. Chen and Mark B. Milam for their contributions to the conference version of this work.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the National Science Foundation (DGE-114747).