Abstract
The aim of this study was to investigate a framework for security measures in the protection of personal identification information within public agencies in Mozambique. This quantitative multimethod study used a survey research design with a questionnaire as the main quantitative data collection tool, triangulated with limited data from content analysis, interviews, and observation. The study found that physical security measures, such as those applied to facilities, technical access controls, and employee training, were not covered by the personal information management framework. Furthermore, regarding physical information security measures, the security equipment, layout and design of most of the existing facilities did not meet the archival needs. In terms of electronic information security, a number of electronic systems for personal identification information were installed within public government agencies. In ensuring the security of personal identification information within these public government agencies, regular backup and testing backups of existing electronic systems are performed to monitor the audit trail, metadata inspection, virus scanners, firewalls, and password change control systems. If they hope to improve service delivery, Mozambique's government agencies should implement effective security measures. The study proposed a framework for security measures on protection of personal identification information in Mozambique.
Keywords
Introduction and background
It cannot be overemphasized that information security play a significant role in preventing any countless number of threats against the information (Smedinghoff, 2015). The threats may jeopardise both information and related transactions as well as people and state (Marciano and Lima-Marques, 2006). Some of the least recognised threats are security lapses and the omission of information (Workman, Bommer and Straub, 2008). The Pacific Northwest National Laboratory (PNNL) (2015) in the US views information security as the protection of organisational information assets, data, and information systems. All organisations are currently facing explosive information growth as a strategic business asset that poses a challenge to management (Fischer, 2017; Junior and Santos, 2015; Rouse, 2016). This information may be retained by organisations beyond its legal, regulatory, or operational value. This practice may result in a number of consequences, such as straining of information technology resources as well as litigation and governmental investigations. In the digital environment, the confidentiality, integrity, and availability of information have become at risk or vulnerable to threats (Bourgeois and Bourgeois, 2014; Workman, Bommer and Straub, 2008).
It is accepted that organisational information such as that pertaining to personal identification information should be protected against any security threats. These security threats can be created by third-party, illegal, or unwarranted entities or by professional hackers. Jouinia, Rabaia and Aissab (2014) assert that security threats can have negative impacts on information systems, such as the fabrication (falsification or alteration) of information, the modification of information, the interception, and the interruption of information. To cope with this, information security has also become a crucial aspect of information technology (IT) (Bourgeois and Bourgeois, 2014; Workman, Bommer and Straub, 2008). The purpose of computers is to process and distribute data without any risks (Bosworth and Jacobson, 2014; Evans, 2011). Computer security needs physical protection of locations, hardware, and software from any threats. Organisations cannot survive without using IT, which is seen as a vital part of organisational needs, but it remains vulnerable to internal and external threats (Barrenechea, 2013). Along these lines, information security focuses on the practice of defending or protecting digital information from unauthorised access, use, recording, disruption, modification, and destruction (Fontes and Balloni, 2016). Hence, the information security measures also cover “information security governance” (Rouse, 2016). Some precautions need to be taken to avoid significant civil losses and crimes (Workman, Bommer and Straub, 2008).
For instance, information security governance is necessary as the process of “establishing and maintaining a framework and supporting” management structure to avoid compromising the integrity of organisational information (Bowen, Hash and Wilson, 2006). The information security governance structure of each organisation should identify or determine the specific needs or requirements for the successful adoption of information security measures to ensure continuity of activities (Junior and Santos, 2015). The information security governance should also consider both technical-administrative security measures (Bowen, Hash and Wilson, 2006) and information security policies, procedures, and methods (Bourgeois and Bourgeois, 2014). Simply because information security measures cover administrative issues while complementing technological and physical issues (Marciano and Lima-Marques (2006). The administrative issues are crucial in order to change human behaviour in the organisation. According to the Brazilian Association of Technical Standards; Sêmola (2014); Fontes and Balloni (2016), different controls, organisational structures, policies, procedures, and technology should form security measures. These regulations and statutes act as a form of administrative control (Bourgeois and Bourgeois, 2014). This provides assignment of responsibility to manage risk (Rouse, 2016) by imposing obligations on organisations to ensure the integrity of business information so that the organisation's business information can remain intact, pristine, defensible, discoverable, and unmodified (Barrenechea, 2013; Fontes and Balloni, 2016). Various laws and regulations, including security standards, often mention the general categories of security measures for integrity, confidentiality, and availability of the organisational information system (Workman, Bommer and Straub, 2008). A judicial system enacts and enforces a law as a rule created by the lawmakers of a country. Information security laws and regulations govern the privacy, acquiring, protecting, transmitting, and deleting of information and how businesses can become compliant (Fontes and Balloni, 2016; Stewart, Chapple and Gibson, 2015).
In the United States, there are a number of laws and regulations that govern information security issues (Hutter, 2016). The first corporate obligations to provide security for personal information appeared in the Health Insurance Portability and Accountability Act of 1996 (HIPAA), which regulated the healthcare sector. In 2003, the security regulations under HIPAA were released (Smedinghoff, 2015). Since then, all sectors in the US have been able to impose security obligations to protect personal information matching the European Union approach. For example, in terms of the state security laws in California, reasonable security procedures and practices are required. However, there are four legal trends shaping information security in the US that include the expansion of the role of information security, the use of a legal standard for compliance, the focus on security obligations regarding specific information and controls, and the imposition of a duty to warn people (Hutter, 2016; Smedinghoff, 2015).
Every country in Europe is obliged to implement the European Union Data Protection Directive. For this purpose, they must use the security measures that are appropriate to protect the privacy of personal data or information of European Union residents. This directive applies to all companies that use equipment within the European Union or in another jurisdiction where a European Union member country's law applies by virtue of private international. Furthermore, the directive imposes such a requirement for security on all organisations (Smedinghoff, 2015).
International research has shown that the information security policy is still a problematic area regarding its implementation and compliance (Sookdawoor, 2005, p. 1). Without the proper information security policies, procedures and practices, the existence of an organisation is threatened in this world of fierce competition. To avoid this, organisations are required to put a sound records management policy in place (Peltier, 2002; Sookdawoor, 2005). It is imperative for institutions to put in place information security systems with solid policies (Peltier, 2002). According to King (1997), hospitals should establish and implement effective record management policies to prevent and address challenges such as the lack of security or access control. This may help to avoid poor record security with weak access control and the lack of records movement control procedures affecting the Eastern and Southern African Branch of the International Council on Archives (ESARBICA) nations. Such policies can assist in avoiding serious challenges to the provision of service in government departments (Wamukoya and Mutula, 2005).
Furthermore, most organisations do have a set of data security policies and procedures, but sometimes these do not comply with best practices. As a result, the organisations are still exposed to dangers that can compromise their survival. It is therefore important that an information security policy be implemented systematically and that it be aligned with established security standards such as the British Benchmarks (BS) 7799, ISO 17799 and ISO 27001 Security Guidelines, although the implementation of these standards remains a logistical problem when developing, adhering to, and monitoring them (Peltier, 2002).
According to Ngulube (2004) and Alshboul (2010), negative issues can arise as a result of a weakness in information security measures. Some of the weaknesses include a lack of compliance with information security policies and regulations; an absence of properly defined security policies; and low participation or commitment of top management in certain areas of security implementation. Kumar, Park and Subramaniam (2008) add other negative aspects such as financial losses, loss of reputation, loss of customer confidence, and loss of personal information as well.
However, security measures are often considered less effective than awareness-creating activities (Hagen, Albrechtsen and Hovden, 2008). Information security is no longer the sole responsibility of a small, dedicated group of professionals. Collaborative and multi-network channel approaches are needed for delivering efficient information and services (Butler, 2013). Nevertheless, other factors are crucial and should be considered, such as education of employees on security measures, the monitoring and testing of security measures and reviews, and the adjustment of security measures (Smedinghoff, 2015).
Problem statement
The main problem of the study was related to the weakness in personal identification information security measures. The existing Civil Personal Identification Information Code Act (No.12/2004 of 2004) (Malunga and Oliveira, 2005) and legislative framework on records and archives management did not comply with security measures. This scenario was associated with the lack of legal security measures for data protection of personal identification information (STV report 2019) and a lack of proper records management programmes within the civil personal identification information agencies in both paper-based and electronic or digital environments, respectively. The failure to create secured and authentic records storage facilities can lead to serious consequences (ISO, 15489–1 2016; Ngoepe, 2014, p. 7; Shepherd, 2006). These include such things as lack of record controls, inability to prevent unauthorised access, and the falsification or alteration and destruction of records. Records produced under these circumstances may not be used as evidence to support business continuity (Ngoepe, 2014; Shepherd, 2006). In addition, the existing legislative framework must be revised or updated in order to provide for timely retrieval of information and provision of records when requested by citizens.
The purpose of the study
The purpose of this study is to investigate security measures for protection of personal identification information that would ensure access controls, prevent unauthorised access, falsification, and destruction of records within government bodies in Mozambique.
Objectives of the study
Objectives of the study are as follows:
To establish the availability of physical security measures for personal identification information in public government agencies in Mozambique. To establish the availability of electronic personal identification information security measures in public government agencies in Mozambique.
Literature review
It cannot be overemphasized that information is a corner stone in business success and growth and need to be secured against all odds. According to Smedinghoff (2015), “Information security is the protection of information” from any number of threats. Nterful, Adam and Umar (2024) shows that “globally, information security has become a paramount concern, especially for increasingly digitalized and interconnected organizations”. Marciano and Lima-Marques (2006) states that, the information security threats may jeopardise both information and related transactions and people. Some of the least recognised threats are security lapses and the omission of information (Workman, Bommer and Straub, 2008). The Pacific North West National Laboratory (PNNL) (2015: iii) in the US views information security as the protection of organisational information assets, data, and information systems. This idea is supported by Beal (2005), Donner and Oliveira (2008), and Sêmola (2014). Information security is a process and it involve protection of information against people who are not authorized to access, use, disclose, destroy or dispose information or system that preserve such information which serve to make the information available, accessible and usable (Aguboshim, Ezeife and Obiokafor, 2022). Nterful, Adam and Umar (2024) shows that in Africa, developing countries has never experienced significant number of studies addressing security of information and theories. Most developing countries like Ghana, experience failure always or in most instances when the put information security measures in place (Koranteng, Apau, Opoku-Ware and Ekpezu (2020).
Every organisation today faces exponential information growth as a business strategic asset that poses a challenge for its management (Fischer, 2017; Nterful, Adam and Umar 2024; Rouse, 2016). This information may be retained by organisations beyond its legal, regulatory, or operational value. Since the introduction of technology cyber threats becomes rive (Nterful, Adam and Umar 2024) to make information management and security part of everyday organizational activity (Chopra and Chaudhary, 2020). This practice may result in a number of consequences, such as straining of information technology resources as well as litigation and governmental investigations. In the digital environment, the confidentiality, integrity, and availability of information has become at risk or vulnerable to threats (Bourgeois and Bourgeois, 2014; Nterful, Adam and Umar 2024).
It is accepted that organisational information, such as that pertaining to personal identification information should be protected against any security threats. These security threats can be created by third-party, illegal, or unwarranted entities or by professional hackers (Jouinia, Rabaia and Aissab 2014). Some of these threats may come from information sers or clients (Merhi and Ahluwalia, 2019). Alshboul (2010) assert that security threats can have negative impacts on the information system, such as the fabrication (falsification or alteration) of information, the modification of information, the interception, and the interruption of information.
To cope with the above scenario, information security has also become a crucial aspect of information technology (IT) (Bourgeois and Bourgeois, 2014; Workman, Bommer and Straub, 2008). The purpose of computers is to process and distribute data without any risks (Bosworth and Jacobson, 2014; Evans, 2011). Computer security needs physical protection of locations, hardware, and software from any threats. Organisations cannot survive without using IT, which is seen as a vital part of organisational needs, but it remains vulnerable to internal and external threats (Barrenechea, 2013).
Along these lines, information security focuses on the practice of defending or protecting digital information from unauthorised access, use, recording, disruption, modification, and destruction (Fontes and Balloni, 2016). Hence, the information security measures also cover “information security governance” (Rouse, 2016). Precautions need to be put in place to avoid significant civil losses and crimes (Workman, Bommer and Straub, 2008). “As information assets and their protection are becoming more and more significant, it is crucial to accurately gauge an enterprise's level of information security awareness (ISA)” (Nterful, Adam and Umar 2024). This implies that organization need to focus more on ensuring that staff members comply with security measures in place (Hong and Furnell, 2022).
Like many other functions, information security needs appropriate governance. Bowen, Hash and Wilson (2006), describe information security governance as “the process of establishing and maintaining a framework” and supporting management structure to avoid compromising the integrity of organisational information. International standards and models guide organisations on best practice for the implementation of information security measures or programmes (PNNL, 2015). According to Alshboul (2010); Junior and Santos (2015), the information security governance structure of each organisation should identify or determine the specific needs or requirements for the successful adoption of information security measures to ensure continuity of activities. The information security governance should also consider both technical-administrative security measures (Bowen, Hash and Wilson, 2006) and information security policies, procedures, and methods (Bourgeois and Bourgeois, 2014; Hagen, Albrechtsen and Hovden, 2008).
Furthermore, Marciano and Lima-Marques (2006) underscore that, information security measures cover administrative issues while complementing technological and physical issues. The administrative issues are crucial in order to change human behaviour in the organisation. According to Sêmola (2014); Oriyano (2014); Fontes and Balloni (2016), different controls, organisational structures, policies, procedures, and technology should form security measures. These regulations and statutes act as a form of administrative control (Bourgeois and Bourgeois, 2014). This provides for the assignment of responsibility to manage risk (Bowen, Hash and Wilson, 2006; Rouse, 2016) by imposing obligations on organisations to ensure the integrity of business information so that the organisation's business information can remain intact, pristine, defensible, discoverable, and unmodified (Barrenechea, 2013; Fontes and Balloni, 2016).
Various laws and regulations, including security standards, often mention the general categories of security measures for integrity, confidentiality, and availability of the organisational information system (Workman, Bommer and Straub, 2008). A judicial system enacts and enforces a law as a rule created by the lawmakers of a country. Information security laws and regulations govern the privacy, acquisition, protection, transmission, and deletion of information and how businesses can become compliant (Barrenechea, 2013; Fontes and Balloni, 2016; Stewart, Chapple and Gibson, 2015).
In the United States, there are a number of laws and regulations that govern information security issues. These include the Federal Information Security Management Act (FISMA) and the 20 Critical Security Control guidelines created by the following bodies: National Security Agency (NSA), International Organization for Standardization (ISO), National Institute of Standards and Technology (NIST), Department of Homeland Security (DHS), and Government Accountability Office (GAO) (Hutter, 2016). The first corporate obligations to provide security for personal information appeared in the Health Insurance Portability and Accountability Act of 1996 (HIPAA), which regulated the healthcare sector. In 2003, the security regulations under HIPAA were released (Smedinghoff, 2015). Since then, all sectors in the US have been able to impose security obligations to protect personal information matching the European Union approach. For example, in terms of the state security laws in California, reasonable security procedures and practices are required. However, there are four legal trends shaping information security in the US, which includes the expansion of the role of information security, the use of a legal standard for compliance, the focus on security obligations regarding specific information and controls, and the imposition of a duty to warn people (Hutter, 2016; Smedinghoff, 2015).
Every individual country in Europe is obliged to implement the European Union Data Protection Directive. For that purpose, they must use the security measures that are appropriate to protect the privacy of personal data or information of European Union residents. This directive applies to all companies that use equipment within the European Union or in another jurisdiction where a European Union member country's law applies by virtue of private international. Furthermore, the directive imposes such a requirement for security on all organisations (Smedinghoff, 2015).
Nevertheless, the United Kingdom (UK) has several models of legislation relevant to information security. Such legislation ensures that an organisation remains legally compliant regarding the use, storing, and handling of information. Some of the legislation includes the Data Protection Act 1998, the Freedom of Information Act 2000, the Privacy and Electronic Communications Regulations 2003, the Regulation of Investigatory Powers Act (RIPA) 2000 and the Copyright, Designs and Patents Act 1988. As Smedinghoff (2015) observes, a number of privacy laws of other countries, such as those of Canada, Japan, Argentina, South Korea, Hong Kong, and Australia also impose a general duty on organisations or corporations to protect the security of personal information.
As stated by Smedinghoff (2015), “security” is viewed as a relative concept in law. In this way, Smedinghoff (2015) also points out that reasonable security depends on the situation. Legislation does not often provide any guidelines on how many security business measures should be implemented to satisfy the legal obligations. Accordingly, organisations may be unable to comply with legislation because specific requirements regarding a particular security measure are not generally included in legislation. Consequently, the choice of security measures and technology may vary with the situation.
International research has shown that the information security policy is still a problematic area regarding its implementation and compliance (Sookdawoor, 2005). Without the proper information security policies, procedures, and practices, the existence of an organisation is threatened in this world of fierce competition. To avoid this, organisations are required to put a sound records management policy in place (Peltier, 2002; Sookdawoor, 2005). It is imperative for institutions to institute information security systems with solid policies (Peltier, 2002). According to King (1997), hospitals should establish and implement an effective record management policy to prevent and address challenges such as the lack of security and access control. This may help to avoid poor record security with weak access control and the lack of records movement control procedures affecting the Eastern and Southern African Branch of the International Council on Archives (ESARBICA) nations. Such policies can assist in avoiding serious challenges to the provision of service in government departments (Wamukoya and Mutula, 2005).
Most organisations do have a set of data security policies and procedures in place, but sometimes these do not comply with best practices. As a result, the organisations are still exposed to dangers that can compromise their survival. It is therefore important that an information security policy be implemented systematically and aligned with established security standards such as the British Benchmarks (BS) 7799, ISO 17799, and ISO 27001 Security Guidelines. However, it needs to be mentioned that the implementation of these standards remains a logistical problem when developing them and adhering to and monitoring them (Peltier, 2002).
The information security plans and policies encompass security controls for application within the organisation. These plans should apply the defence in-depth method and need to be continually improved (Hutter, 2016). Individual organisations can frequently create an information security policy that is enforced by law or as part of regulatory information security policies. These organisational policies for information security must be based on the company's or organisation's needs. Such an information security policy is composed of standards, guidelines, and procedures (Stewart, Chapple and Gibson, 2015). The policy must define how information is protected and what the consequences are for violating the rules of maintaining access to information. It is composed of a set of framework policy documents created to guide the enforcement of measures protecting the information and data of an organisation against unauthorised access, sharing, loss, or damage.
Information security policies are classified as regulatory, advisory, or informative, but in each case the policy should cover a set of aspects such as the responsibilities assigned, the roles defined, the auditing requirements specified, the enforcement of the processes outlined, the compliance requirements indicated, and the acceptable risks defined (Stewart, Chapple and Gibson, 2015). By stating or outlining the key principles in the policy, organisational information can be kept securely, taking into account office security, the handling, transferring, and sharing of information, and the proper reporting of suspected or actual data breaches (General Optical Council, 2017). Hence, the policy should state the level of computer security clearly to guarantee that all the required information will be available only to authorised users with access to it in complete form with no interruption or alteration by intruders (Rouse, 2016; Workman, Bommer and Straub, 2008). An organisation can issue a data security policy that ought to meet the requirements and comply with the rules and guidelines related to the security of the data stored digitally at any point in the network or inside the organisation (InfoGov basics, 2019). This is supported by Awad (2018), who explains that information security covers user authentication, network security, hardware security, software security, and data cryptography.
The information security policy must secure the organisation from all sides, covering all software, hardware devices, physical parameters, human resources, information or data, and access control within its scope (InfoGov basics, 2019; Alshboul, 2010). Hardware and software issues, natural events, and willful, negligent, or accidental events may not protect the confidentiality, integrity, and availability of information against threats and damage (Che, Shaw and Yang, 2006; Johnson, 2008). If those aspects are not secure, the information becomes vulnerable to threats. However, InfoGov basics (2019) and Saleh (2010), points to other characteristics such as accuracy, possession, and utility of information over time.
The concept of “confidentiality” is referred to as information assets or personal data that “are protected from disclosure or exposure to unauthorised individuals or systems” by ensuring the associated actions are within the confines of the law and do not rely on common sense (Caldicott, 2013, p. 53). Such data or information is thus used through known processes, such as processing, recording, obtaining, and sharing (Caldicott, 2013). Other concepts and aspects related to confidentiality include sensitivity, discretion, criticality, concealment, “seclusion, and isolation (Stewart, Chapple and Gibson, 2015). However, these aspects may have different meanings in different circumstances. To combat any confusion, Padmapriya and Subhasri (2013) demonstrate that by using an encryption technique, the preservation of confidentiality can be ensured. The sensitive information is concealed when it is converted into a code to protect it from unauthorised persons accessing it. This is seen as one of the best ways of protecting confidential information assets within any organisation.
However, the integrity of information remains a critical aspect (ISACA, 2011). Confidentiality depends on integrity, and, in turn, integrity depends on confidentiality (Stewart, Chapple and Gibson, 2015). It means that confidentiality can only be maintained through integrity. As Zissis and Lekkas (2012) observe, in circumstances when authorised parties alter or modify information assets in acceptable ways, these information assets are considered to possess integrity. This concept is not just applied to the digital environment but also to the manual environment. Overall, the security levels determine the level of secrecy, meaning that only those with rights and access privileges to the assets are permitted to access the information. According to Whitman and Mattord (2012), when unauthorised individuals or systems view confidential information, confidentiality is considered to have been breached.
Furthermore, with confidentiality and integrity, availability should form part of the policy. Availability alludes to the ability of a system or information asset to be usable upon request by authorised personnel regardless of the type of environment. The availability includes both manual and digital environments of data, software, and hardware that are being made accessible to authorised end users upon request (Zissis and Lekkas, 2012). Bourgeois and Bourgeois (2014) presents information security tools that an organisation can utilise as part of its information security policy. These tools include authentication, control access, encryption, passwords, backups, firewalls, intrusion deletion systems, virtual private networks, and security policies.
According to Ngulube (2004) and Alshboul (2010), negative issues can arise from weaknesses in information security measures. Some of the aspects include a lack of compliance with information security policies and regulations; an absence of properly defined security policies; and low participation or commitment of top management in certain areas of security implementation. Kumar, Park and Subramaniam (2008) also add other negative aspects such as financial losses, reputation, loss of customer confidence, and loss of personal information.
However, security measures are often considered less effective than awareness-creating activities (Hagen, Albrechtsen and Hovden, 2008). Information security is no longer the sole responsibility of a small, dedicated group of professionals. Collaborative and multi-networked channel approaches are needed for delivering efficient information and services (Alshboul, 2010; Butler, 2013). Nevertheless, other factors are crucial and should be considered, such as education of employees on security measures, the monitoring and testing of security measures and reviews, and the adjustment of security measures (Smedinghoff, 2015).
Methodology
Methodology refers to the scientific methods that are used to produce knowledge in any scientific field (Ngulube, 2015). Multimethod research is seen from different perspectives. Hunter and Brewer (2015) defined multimethod research as research that utilises more than one method in a study. It differs from mixed-methods research that combines a variety of relevant methodologies. A multimethod is applied in a study in order to ensure that the study is understandable, makes sense, and is valid. This study applied a quantitative multimethod methodology that employed a survey research design, with the questionnaire serving as the primary quantitative data collection tool, triangulated with limited data from other qualitative data collection tools, namely content analysis, interviews, and observation (Ngulube, 2015). The survey questionnaire was developed in a semi-structured form for clarity in some statistical data. In ensuring validity and reliability the researcher submitted the tool to a limited number of study population who were not going to be considered for participation in the roll out of the study. The questionnaire testing was done with a checklist that serve as a tool for participants to give feedback for corrections of issues like grammar, spelling, vagueness in questions, and more other things. Interviews and observation was used in the study to augment questionnaire statistical data. In other words data from the two collection tools were only used to clarify statistical information as reported by the questionnaire. The interview questions were unstructured to allow explanations from views and experience of the participant to give insight that clarifies statistical information from questionnaire.
The study's target population included 2 790 civil servants from 24 government bodies, 2 central state departments, and 22 provincial government agencies across the Republic of Mozambique's 11 provinces. The study used stratified random sampling to collect questionnaire data, and purposive or judgmental sampling to collect interview data. Senior managers, human resource specialists, and heads of central state departments and provincial government agencies were stratified to complete the questionnaires in these institutions. As key informants, records managers and heads of records appraisal committees were purposively chosen. Document analyses were performed on the personal identification information governance policies, procedures, guidelines, and legislation in the 18 sampled institutions. Direct observations were conducted in the 18 respective institutions where the research was being conducted to see how personal identification information governance was carried out, revealing the state of governance exercised for existing information. The sample frame for central state departments and provincial government agencies was based on the Mozambique Government's administrative structure or organogram (
Questionnaire data was analysed using SPSS software before integrated into the thematical pool of other data from observation, Interview and content analysis for inclusive discussion and interpretations. Interview data was transcribed and coded thematically according to objectives with data presented as quotes from participants verbatim. Observation and content analysis data was consolidated, organised, cleaned and presented thematically to address objectives. Data from questionnaire, interview, observation and content analysis was at the end interactively analysed thematically in line with the study objectives.
This study was partially extracted from a PhD research study of the main author supervised by the second author. Before conducting the study, the study was issues ethical clearance number 57637776_CREC_CHS_2021 by the University of South Africa and permission was granted by target institutions. The target institutions provided a written permission to collect data. Participants completed informed consent before researcher commenced with data collection as a form of agreement to take part in the study.
Findings
This section presents the findings of the study. Figure 1–4 present demographic information of the participants. Figure 1 present demography of the respondents in institutions.
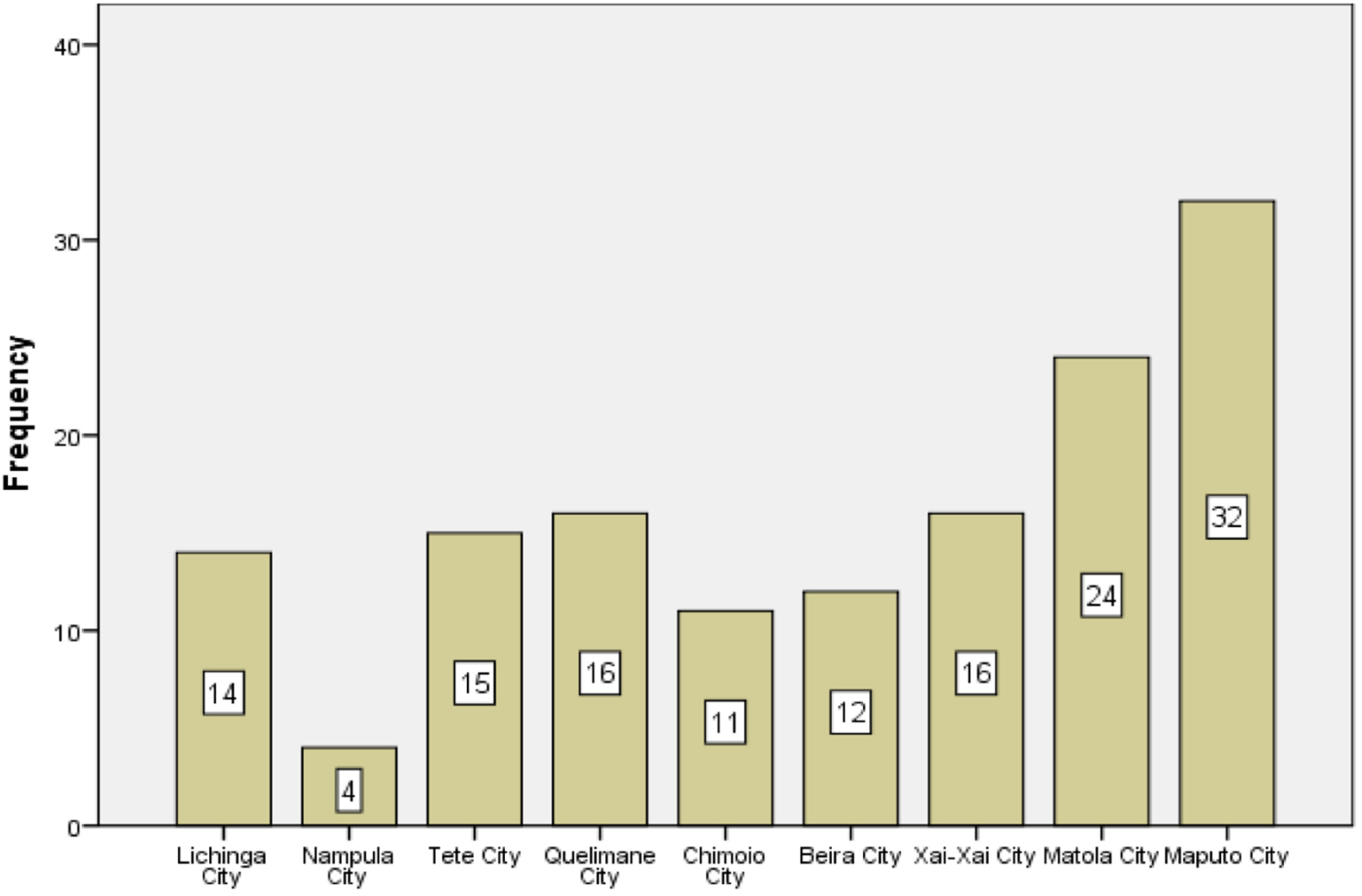
Respondents per demography (
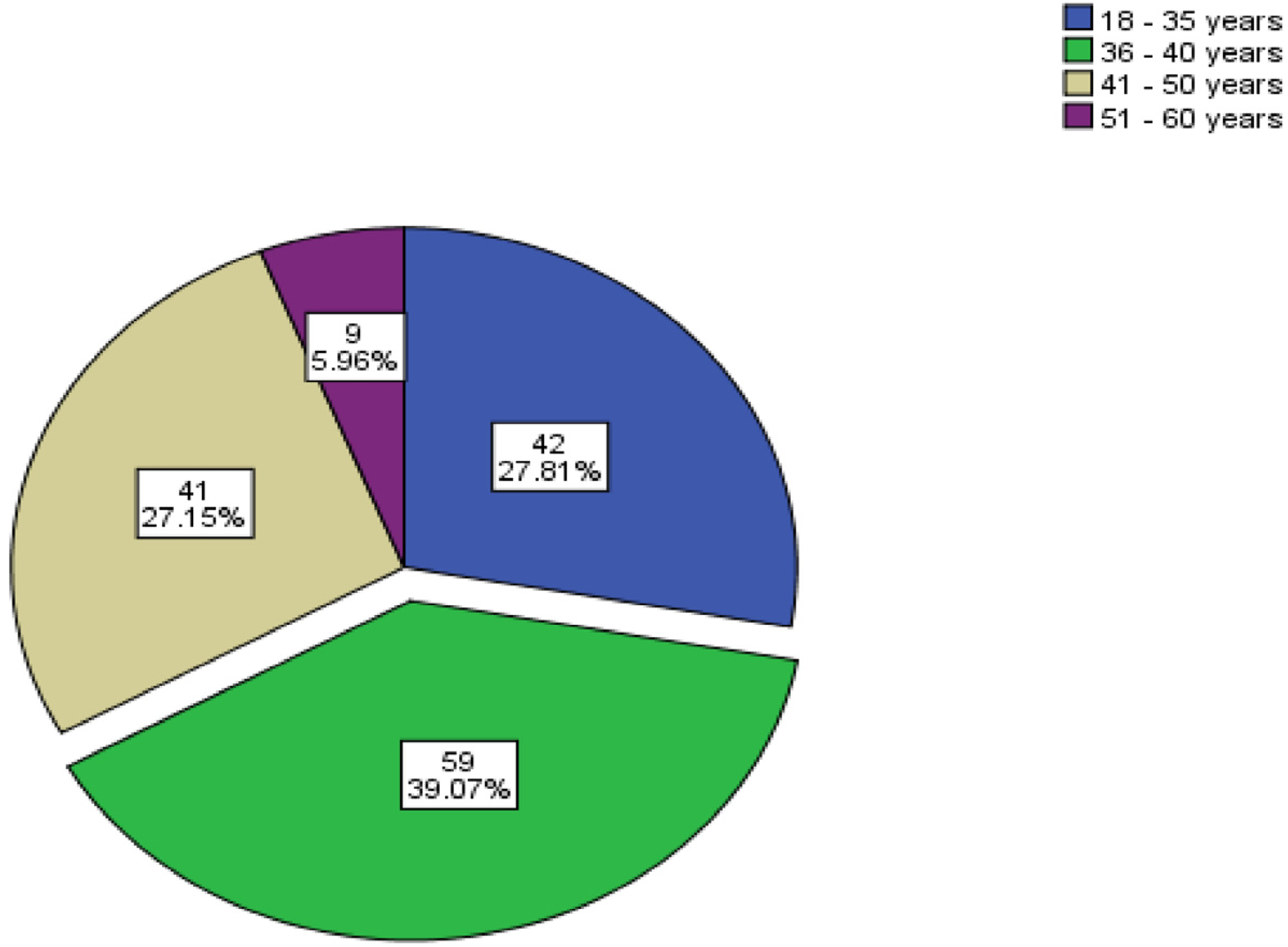
Respondents per age group (
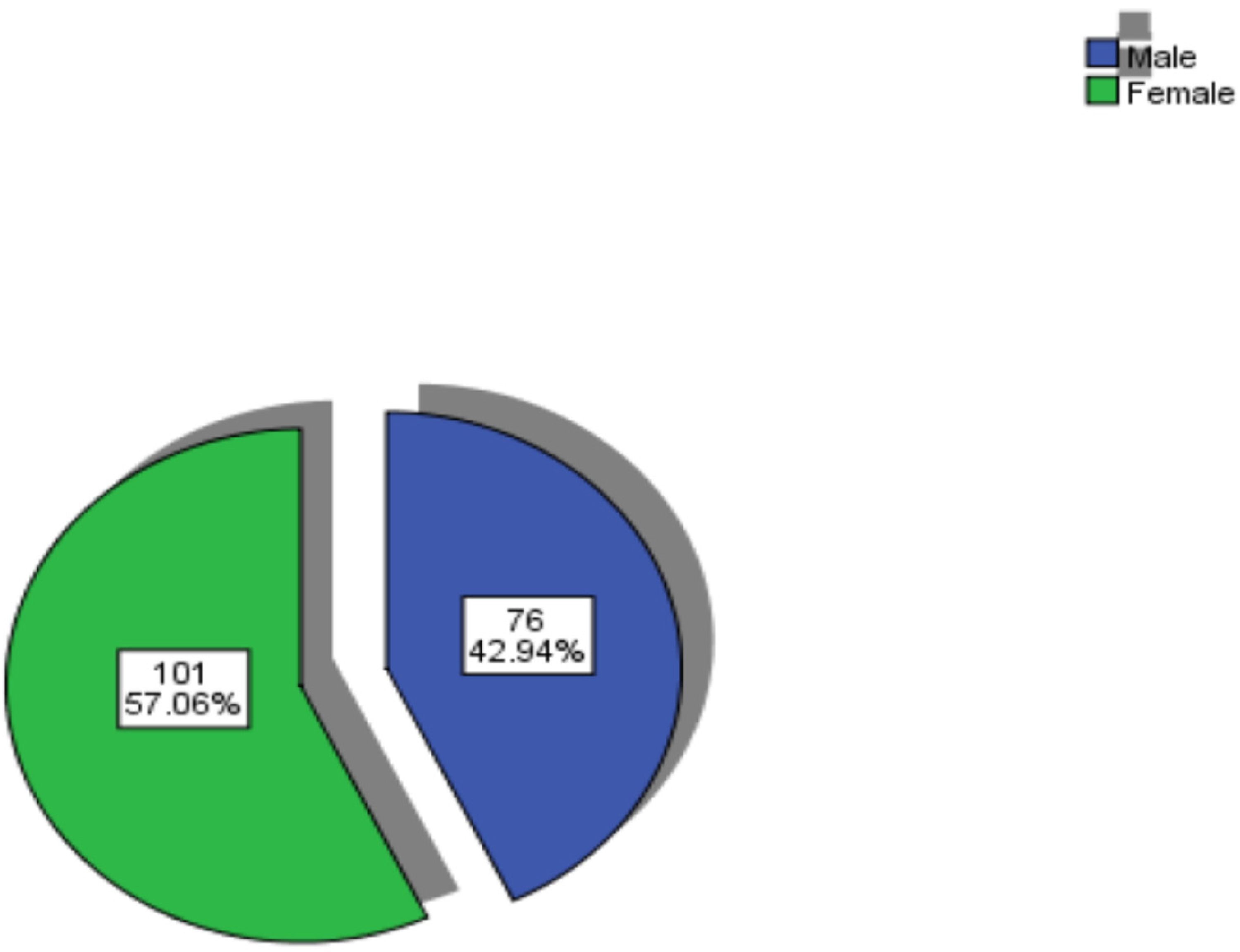
Respondents per gender (
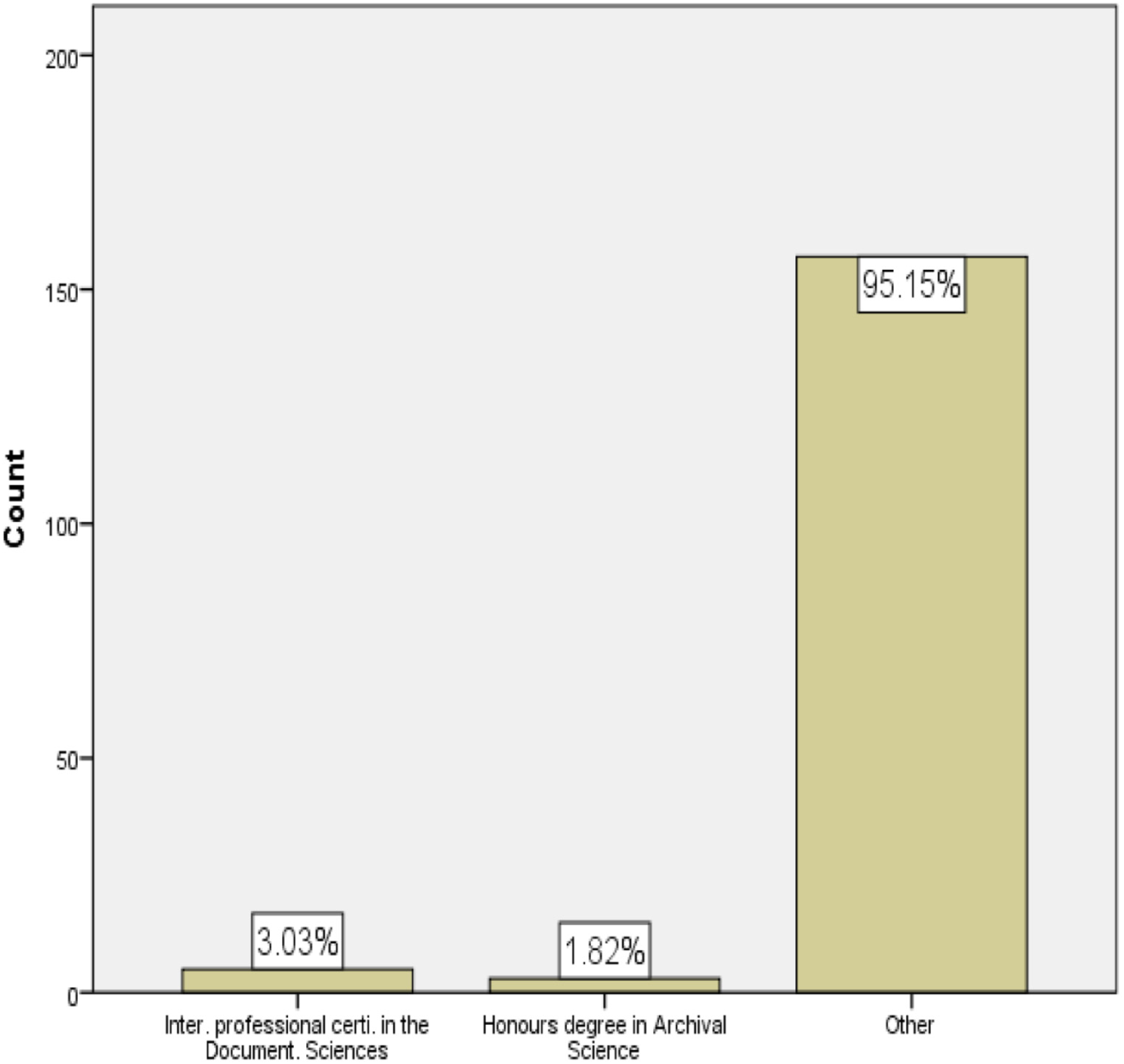
Respondents per educational level (
Figure 2 present respondents per age groups and figure 3 present respondents per gender respectively.
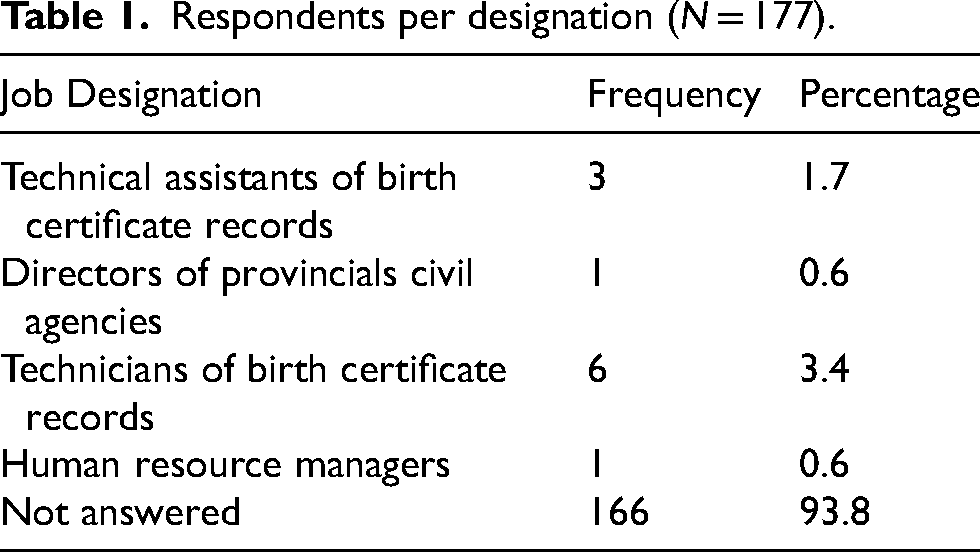
Figure 4 present respondents per educational levels and Table 1 present respondents per designations.
Respondents per designation (
Security measures for personal identification information
This section presents the data by addressing the objectives of the study.
Physical security measures for information
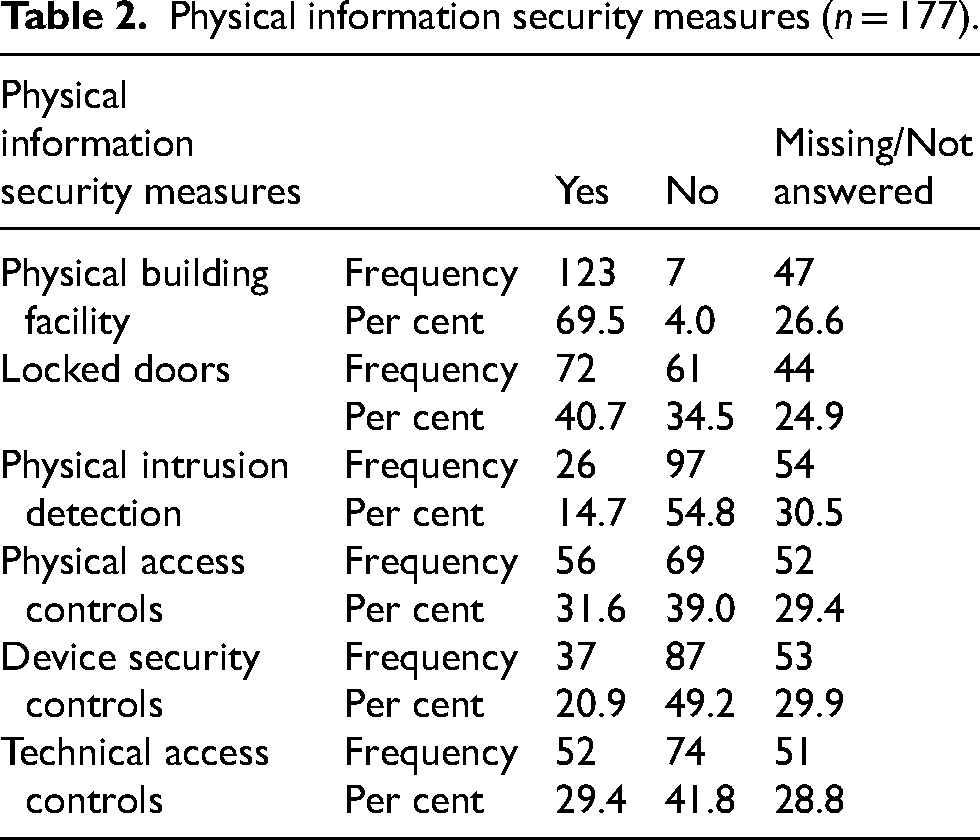
Records can be physically safeguarded against unauthorised access. In this research study, respondents were asked whether there were security measures in place to protect personal identification information within Mozambique's public government agencies.
Physical facility
The researcher wanted to know if the existing records facility in the public government agencies to which the respondents belonged was physically secure. Table 2 indicates that the majority of respondents, 69.5% (123), said “yes”, only 7% said “no” and 26.6% (47) did not respond to this question.
Physical information security measures (
The observations revealed that there was no effective records facility that was physically protected in each organisation, because all personal identification information facilities were inadequate in the public government agencies under study.
The layout and design of the majority of the facilities visited did not correspond to the needs or purposes of records and archives. The majority of the existing buildings were in poor physical condition, with dilapidated floors and walls, ceilings damaged by rainwater infiltration, and broken windows. Interviewees provided the following varying responses:
The respondents were also asked whether the doors of the existing records storage areas in their respective public government agencies were locked. Table 2 reports that the majority, namely, 40.7% (72) of the respondents said “yes”, 34.5% (61) said “no” and 24.9% (44) did not answer this question. However, the observation showed that a significant number of the doors of the existing record storage areas in public government agencies were not locked because most of the records within the public government agencies were stored in the workplace and other open areas such as corridors, balconies, and also on top of shelves and cupboards. Furthermore, although there were some record storage areas with doors, most of them were not locked, and some were just obsolete and not suitable for maintaining or protecting the existing records securely.
However, many interviewees provided different responses, as follows:
Respondents were also asked in the questionnaire whether physical intrusion detection was in use in public government agencies’ records storage areas. Table 2 indicates that a small group, that is 14.7% (26) of respondents answered in the affirmative while the majority, 54.8% (97) indicated that there was no physical intrusion detection mechanism. A sizable proportion of respondents, 30.5% (54) did not answer this question. The observation demonstrates that physical intrusion detection mechanisms were not installed in public government agencies’ records facilities. Many interviewees gave contradictory responses. Some of the responses were as follows:
The frequency with which respondents confirmed that there were no physical access controls in public government agencies in Mozambique attested to the fact that personal identification information had no physical access control mechanisms. Table 2 shows that a considerable percentage, that is 31.6% (56) of the respondents said “yes” there were access controls, whereas the majority (39% (69) said “no”. A total of 52 (29.4%) respondents did not answer this question. Overall, the researcher found through observation that there were some rules with regard to physical record access controls posted on the doors of storage facilities, but the organisational staff did not comply with these rules. Users from outside the organisation were the only ones who had to follow the physical access control measures. Users from inside the organisation could access personal identification records without formal permission. Some interview participants provided different answers. Their answers were presented in this way:
When asked in the questionnaire whether there were security control devices in place for access to personal identification information in Mozambique's public government agencies, Table 2 shows that 20.9% (37) said “yes”, the majority, 49.2% (87), said “no”, and 29.9% (53), did not respond to this question. The observations revealed that some device security controls, such as fingerprinting for organisational staff and a security camera, were in place. Furthermore, security control devices pertaining to personal identification information were mostly installed in directors’ work offices in Mozambique, with a few exceptions where they were installed at the building's main access doors. However, these security control devices did not extend to the record storage areas. Furthermore, some interviewees contradicted one another in their responses. These responses are as follows:
Finally, as can be seen in Table 2, respondents were asked whether there were technical access controls with regard to personal identification information governance in Mozambique's public government agencies. A significant number of respondents, that is 52 (29.4%) answered in the affirmative but the majority, 74 (41.8%) said “no” with 51 (28.8%) who did not respond to the question.
Interviewees provided the following individual responses:
The document analysis revealed that processes related to technical access controls in a manual environment were regulated, but they had not yet been implemented by public government agencies for personal identification records.
Measures for electronic information security
This section focuses on whether public government agencies were successful in implementing electronic information security measures such as user authentication, network security, database/software security, data cryptography, virus scanners, firewalls, password change control systems, and regular backups.
The questionnaire asked respondents to confirm whether their organisations had managed to implement some electronic information security measures in terms of “user authentication” within Mozambique's public government agencies. Table 2 reports that the majority, namely 90 (50.8%) respondents answered “yes”, 9 (5.1%) said “no”, and a significant number, namely 78 (44.1%) did not respond.
According to the document analysis report, a number of electronic systems for personal identification information were installed within public government agencies. According to the interview report, many respondents provided the following responses:
The respondents were asked in the questionnaire whether organisations in Mozambique's public sector had implemented some electronic information security measures in terms of “network security”. Table 3 indicates that the majority of respondents 70 (39.5%) said “yes”, a small group 28 (15.8%) said “no”, and the majority 79 (44.6%) did not respond to this question. IT personnel were more knowledgeable than administrative personnel in government agencies. Interviewees provided the following responses:
Electronic information security measures (
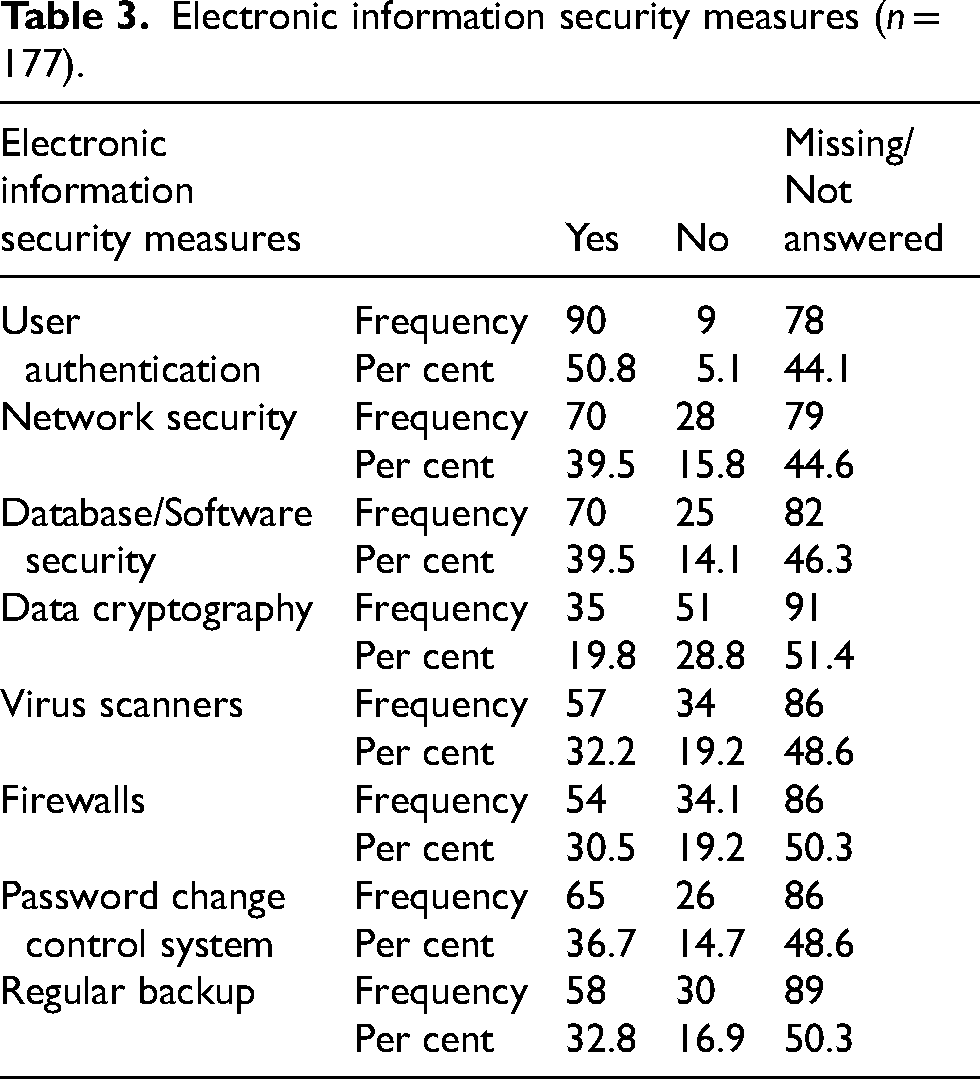
Another question in the questionnaire asked respondents if they had managed to implement some electronic information security measures in terms of “Database/Software security” in Mozambique's public government agencies. Table 3 reports that 70 respondents (39.5%) said “yes”, a significant number, namely 25 (14.1%) said “no”, and the majority of the respondents, namely 82 (46.3%) did not respond to this question. More information about database/software security was yet again provided by the IT organisational staff. However, there was a wide range of responses, as shown below.
Data for this section are reported in Table 2 below.
Furthermore, respondents were asked in the questionnaire if they had managed to implement some electronic information security measures in terms of “data cryptography” within Mozambique's public government agencies. Table 3 reports that a small group of 35 (19.8%) respondents said “yes”, a sizeable number, namely 51 (28.8%) said “no”, and the overwhelming majority, that is 91 (51.4%) of respondents did not respond to this question. Unlike the general organisational staff, the IT staff provided more information about data cryptography. However, there was still a wide range of responses. The following are the opinions expressed by interview participants:
The respondents were asked if they had been able to implement electronic information security measures such as “virus scanners” in Mozambique's public government agencies. Table 3 reports that the majority of respondents, that is 57 (32.2%) said “yes,” a small group of 34 (19.2%) respondents said “no”, and the majority, namely 86 (48.6%) did not respond to this question. More information about the use of virus scanners was provided by the IT staff. Some of the interviewees provided the following responses:
Respondents were asked if they had implemented electronic information security measures such as “firewalls” within Mozambique's public government agencies. Table 3 reports that a significant number of respondents, namely 54 (30.5%) said “yes”, a small group of 34 (19.2%) said “no”, and the majority of the respondents (50.3%) did not respond at all. The IT staff once again provided more accurate information about the use of firewalls. The interviewees provided the following responses:
In terms of electronic security, respondents were asked in the questionnaire if they had implemented a “password change control system” in Mozambique's public government agencies. Table 3 reports that 65 (36.7%) of the respondents said “yes”, 26 (14.7%) said “no”, and 86 (48.6%) did not respond. The following information was provided by interview respondents regarding the password change control system:
Finally, regarding another form of electronic security, respondents were asked in the questionnaire if they had implemented electronic information security measures such as “regular backup” within Mozambique's public government agencies. According to Table 3, 58 (32.8%) participants responded “yes”, a small group of 30 (16.9%) said “no”, and the majority, 89 (50.3%) did not respond to this question. The respondents shared information about regular backup processes and other related topics. Participants provided the following responses:
Discussion of the findings
This section discusses findings of the study concerning personal identification information security measures, specifically physical information security measures and electronic information security measures for personal identification records under the management of organisational units.
The Records and Archives Management Act No 84/2018 of 2018 states that, among other issues, the Central Director Body of the National System of State Archives is responsible for the promotion of the construction of permanent archive buildings and the preservation of institutional memory over time (Moçambique, 2018). It means that each public government agency at central, provincial, district, and municipal levels must provide record storage areas for current and semi-current records. According to the Records and Archives Management Act No 84/2018 of 2018, each public government body at the various levels may build, rehabilitate, and adapt a records storage area (Moçambique, 2018). However, existing records in Mozambique's government bodies were not physically protected and were vulnerable to a variety of threats (Smedinghoff, 2015). The majority of respondents, namely 123 (69.5%) confirmed that this was the case because balconies, corridors, and workspaces were used as storage areas for current and semi-current birth records. Furthermore, the doors of the existing record storage areas were not locked. The majority of the respondents, namely 72 (40.7%) confirmed this. This situation may impact negatively on the existing records, such as falsification or alteration of information (Alshboul, 2010; Jouinia, Rabaia and Aissab 2014). Locks and physical intrusion detection systems (PIDS) are important systems because they can deter or detect unauthorised access to information (New Zealand Intelligence Service 2021). However, there were other security measures that continued to affect the integrity and authenticity of existing records. For example, most of the respondents (97 [54.8%]) did not confirm that public government agencies did not install any physical intrusion detection systems in the records storage areas. Most of the respondents, (69 [39%]) confirmed that the public government agencies did not apply any type of physical access controls. Furthermore, the majority, namely 87 (49.2%) of respondents, did not confirm that there were no adequate security control devices for personal identification information within public government agencies in Mozambique.
Device control is currently a critical component of data protection strategies for organisations. There are several benefits of device controls because they prevent data loss and theft, and provide media encryption, detailed monitoring and forensics, and malware protection (Payaslioğlu 2021). As Payaslioğlu (2021) attests, device control requires end users to encrypt data being copied to removable devices. It enforces encryption policies on all data transfers to USBs or DVDs/CDs, limits the amount and types of data that can be transferred, and provides visibility into what data is being transferred onto devices from endpoints.
Security measures should also prioritise awareness creating activities (Hagen, Albrechtsen and Hovden 2008). Information security is a collaborative and multi-networked channel of approaches so information security measures may not be delivered through a small, dedicated group of professionals only (Alshboul, 2010; Butler, 2013). Other factors, such as monitoring, testing, training reviews, and the adjustment of security measures should also be considered (Smedinghoff, 2015).
Recommendations of the study
In an electronic environment, information security measures should also deal with confidentiality to prevent the unauthorised disclosure and use of information. This would ensure that records are secured and protected against wrongful recipients (Alshboul, 2010). Regarding security measures put in place within public government agencies in Mozambique, 90 (50.8%) respondents confirmed that user authentication was in place; 70 (39.5%) respondents confirmed that the agencies assured network security; however, 53 (29.9%) of the respondents did not confirm that a testing backup was in place. Overall, the public government agencies responsible for personal identification information in Mozambique have developed security measures to protect their electronic records. These components play an important role because they enhance access control measures for systems, applications, processes, and information (Hernandez, 2022). According to Harris and Maymi (2016), firewalls, encryption, and identification and authentication mechanisms are examples of technical controls. These are software and hardware components that protect a system against cyber-attacks. In the majority of interviews, participants indicated that there were effective security measures in place within public government agencies. Due to the augmenting of the workflow process, the existing electronic personal identification information systems regularly go offline, thus limiting local people's access to the services provided by public government agencies for up to two or three days. This situation poses a challenge for its management (Beach and Oates, 2014; Fischer, 2017; Junior and Santos, 2015; Rouse, 2016). The existing firewall system should be updated for it to cope with the workflow problem.
Personal identification information security measures need to be controlled or regulated with legislation, policies, procedures, programmes, standards, and physical and electronic measures. Organisational staff need to be familiarised with legislation governing personal identification information security and the staff of public government agencies for personal identification information must be sufficiently informed about the existence of legislation. This should be done through training programmes dealing with the existing legislation governing information and security within Mozambique's public government agencies. It is also incumbent upon senior management to disseminate information to organisational records and archives management staff.
The requirements stipulated in the policy and procedure manual must be followed by public government agencies dealing with personal identification information because these key documents provide proper guidelines based on the legislative framework governing records management in personal identification information institutions. For full implementation of the legislative framework, policies, and procedures within Mozambique's public government agencies, public government agencies must ensure the provision of materials, as well as a higher level of human and financial resources. In terms of security measures, public government agencies for personal identification information in Mozambique must draft a written security programme to protect personal identification information from falsification or alteration, security breaches, and unauthorised destruction. Furthermore, public government agencies must make available a specific national standard on information governance for personal identification information.
In terms of physical information security, Mozambique's public government agencies must establish an effective records facility for physical protection in each organisation. Furthermore, the layout and design of existing facilities must correspond to the needs or purposes of records and archives. Existing buildings should have their physical condition upgraded with adequate floors, walls, and ceilings to prevent rainwater infiltration. The existing record storage areas in Mozambique's public government agencies must be lockable, and all records stored in the workplace must be removed and stored in adequate storage areas, rather than in corridors, on balconies, and on the tops of shelves and cupboards, as is currently the case. Also, dilapidated or damaged doors must be replaced in order to secure the existing records storage facilities. Physical intrusion detection for access control must also be installed in records facilities. Organisational staff and users must follow the existing rules regarding physical record access controls that have been placed on storage facility doors.
Installing formal authorisation device security controls, such as security cameras and biometrics, for organisational staff is critical. These device security controls must be installed not only in the directors’ work offices, but also at the main entrance doors of buildings. In terms of technical access controls for records and archives management, public government agencies must implement them as physical security measures within public government agencies. Personal identification records must be regulated and implemented by public government agencies. Personal identification information classification must be fully implemented. Moreover, records appraisal committees and records management units must be established to oversee the records management issues covered by legislation. To keep track of the movement of records, public government agencies must also use new approved standardised registration books for incoming and outgoing records. The Records and Archives Management Act requires that these records processes be followed. Figure 5 presents a framework illustrating the implementation of security measures for the protection of personal identification information in Mozambique as recommended here. The framework was developed or crafted based on the findings and recommendations informed by the raw data and literature reviewed in addressing the objectives of the study.
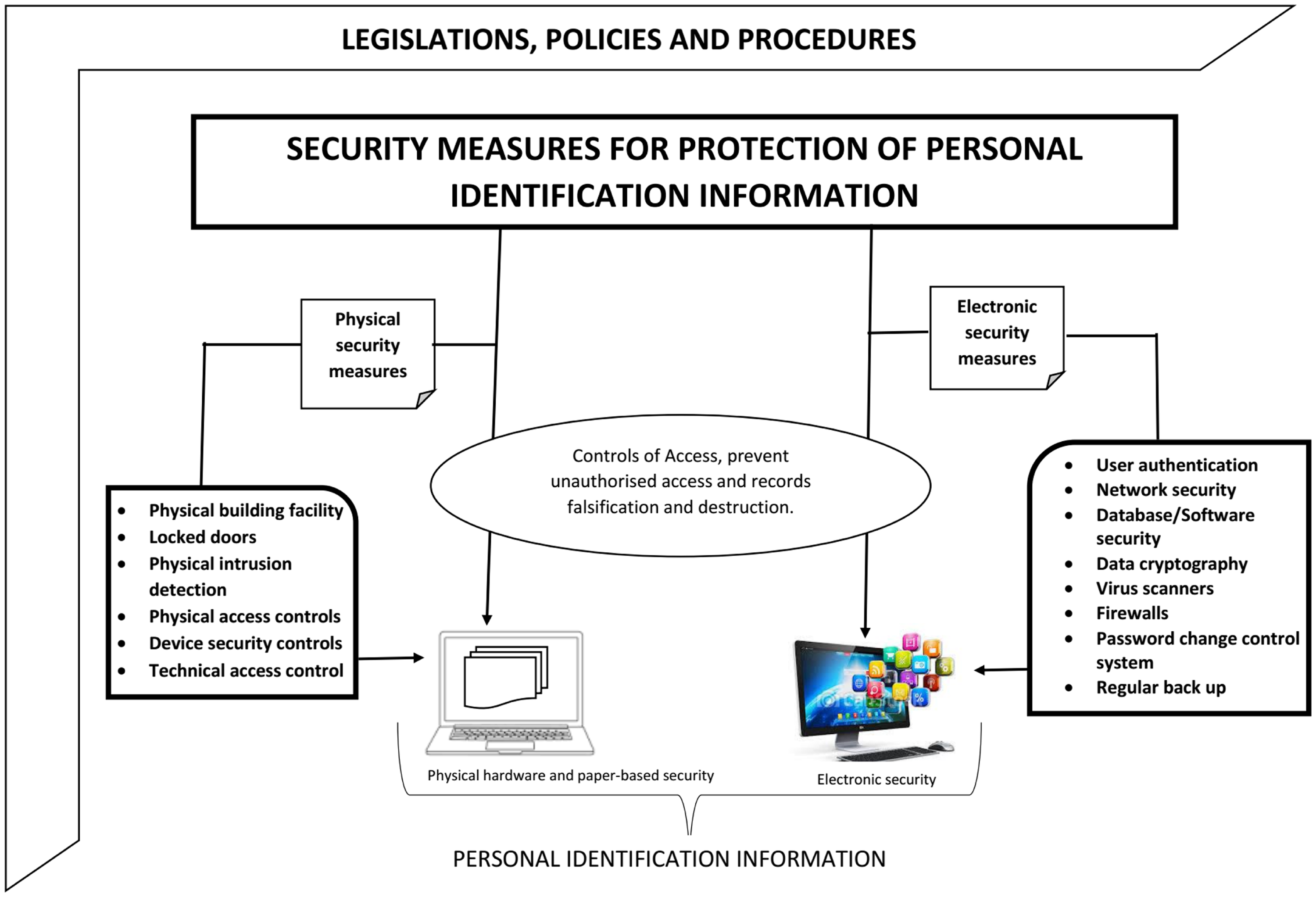
Framework for security measures on protection of personal identification information in Mozambique.
A vital records schedule must be established to manage personal identification information in accordance with the current Records and Archives Management Act. The document's creation is thus an essential responsibility of senior management as well as the organisation's staff. Since the current Records and Archives Management Act No. 84/2018 of 2018 covers disposal schedules for administrative and specific records, public government agencies must implement a disposal schedule for the management of personal identification information. The organisational staff must be adequately informed about the schedules and they must be made available to anyone who needs them for a variety of valid reasons. The disaster preparedness guidelines for archival materials must be well understood by all organisational staff members. CEDIMO 2009 approved these archival material guidelines as part of the current Records and Archives Management Act for the protection of personal identification information.
Furthermore, the public government agencies for personal identification information must establish a policy for reviewing and adjusting information security policies. In public sector organisations, well-defined procedures for reviewing and adjusting information security policies are required. A monitoring system must be put in place to protect the record creation and receipt processes. Within the organisation, there must also be a single point of record creation. When establishing the new approval procedures for record creation, public government agencies must adhere to standardised formats for official correspondences within public government agencies. Records must be captured and classified correctly in the relevant updated control register. Besides, these acts must be updated to regulate how records are to be protected during transportation from one agency to another that is in a different location to ensure the secure and safe receipt of the records. Existing records storage areas within public government agencies must be decongested through a process of appraisal, destruction, or transfer to provincial archives. Provincial archives must therefore be established since the Records and Archives Management Act No. 84/2018 of 2018 includes a provision for the establishment of provincial archives. The organisation's staff must be trained in following the approved access to information manual, which was created in 2015 and was included in the Records and Archives Management Act.
In terms of physical information security, Mozambique's public government agencies must establish an effective records facility for physical protection in each organisation and it is crucial that the layout and design of new and existing facilities must correspond to the needs and purposes of records and archives. In this study the focus is general security measures and future studies may focus on the specific matters or areas of information security like physical security, electronic security or cloud storage security for personal identifiable information.
Concluding remarks
It is hoped that the framework provided about security measures on protection of personal identification information will serve as a center of benchmark for every government agency across the universe. In terms of physical information security measures, Mozambique's public government agencies need to seek an effective records facility that is physically protected. The fact that layout and design of the existing facilities does not correspond to the needs or purposes of records and archives put the information at risk of damage and that need urgent attention. Buildings that are in poor physical condition, with dilapidated floors and walls, broken windows, and ceilings damaged by rainwater infiltration need to be fixed to avoid losing records and information. The organizations must make sure that records storage areas in Mozambique's public government agencies are lockable because records that are kept on corridors, balconies, and on top of shelves and cupboards are vulnerable to get damaged. It is important that all records storage rooms get lockable to ensure continuous safety and security of information and records. There should also be installed physical intrusion detection to detect and control access to information rooms. Rule that are put in place must be enforced and there must be some consequence management in case some officials do not follow or comply. Organization must maintain their good electronic networked security with data cryptography, hardware security, and software security for personal identification information. Also keep on maintaining regular backup and testing of backups on the existing electronic systems. This will continue to help in monitoring the audit trail, metadata inspection, virus scanners, firewalls, and password change control systems.
Implications of the study
The result of this study will help government agencies of Mozambique and other government agencies across the world to realise the importance of information security, especially personal identification information. The framework provided about security measures on protection of personal identification information will serve as a benchmark for many organisations across the world to implement security measures on protection of personal identification information. The framework may also be used in many academic in their studies that addresses topics related to security measures on protection of personal identification information as a theoretical framework or on informing their conceptual framework. The results of the study may also bring about social relieve to the communities currently struggling to access their personal information due to security cliches in case their organisations implement the recommendations of this study properly.
Footnotes
Data availability
The data that support the findings of this study are available from the authors upon reasonable request.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Ethical approval
This article does not contain any studies with human or animal subjects performed by any of the authors.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Informed consent
Informed consent was obtained from all individual participants included in the study.
