Abstract
Since 2009, over 176 million patients in the United States have been adversely impacted by data breaches affecting Health Insurance Portability and Accountability Act–covered institutions. While the popular press often attributes data breaches to external hackers, most breaches are the result of employee carelessness and/or failure to comply with information security policies and procedures. To change employee behavior, we borrow from the organizational climate literature and introduce the Information Security Climate Index, developed and validated using two pilot samples. In this study, four categories of healthcare professionals (certified nursing assistants, dentists, pharmacists, and physician assistants) were surveyed. Likert-type items were used to assess the Information Security Climate Index, information security motivation, and information security behaviors. Study results indicated that the Information Security Climate Index was related to better employee information security motivation and information security behaviors. In addition, there were observed differences between occupational groups with pharmacists reporting a more favorable climate and behaviors than physician assistants.
Keywords
Introduction
Despite both legislation and sophisticated technology designed to safeguard patients’ electronic health records, data breaches have been on the rise1–4 with over 2100 reported data breaches affecting Health Insurance Portability and Accountability Act (HIPAA)-covered US healthcare providers since 2009. These breaches exposed the data of over 176 million patients, with the pace of breaches ramping up in recent years. Importantly, this figure represents a significant underestimate of data breaches and of the number of patients impacted as US federal reporting guidelines only apply to data breaches affecting over 500 patients. Moreover, a recent study by the Ponemon Institute
5
indicated that the majority of breaches reported affected
Based on this research and answering a recent call 12 for research on information security within healthcare, we directly target employees’ attitudes and behavior surrounding IS, by taking an organizational climate approach, a concept which is distinct from but often used interchangeably with organizational culture. Organizational climate, “the shared perceptions of and the meaning attached to the policies, practices, and procedures employees experience and the behaviors they observe getting rewarded and that are supported and expected,” 13 approaches have been used successfully to change employees’ domain-specific attitudes and behaviors. Examples include but are not limited to ethics climate, 14 safety climate, 15 diversity climate, 16 and service climate. 17 Common across these areas is that while relevant rules, policies, procedures, and training often existed, they were not sufficient to change corresponding behavior. Therefore, organizational climate approaches were employed to highlight social aspects of the work environment, making certain characteristics more salient to employees, thus cueing a change toward desired behaviors. 18 The goal of this study, therefore, is to provide healthcare researchers and practitioners with a validated, parsimonious tool to assess the climate surrounding IS throughout their organizations. As such, it would provide practitioners with information regarding where IS interventions should be targeted.
A contextual approach: organizational culture/climate
There has been a growing body of research that focuses on the use of environmental cues to encourage employee compliance with existing IS policies and procedures.19–30 Most research in the area takes an organizational culture approach over that of organizational climate (exceptions25,26). Although similar, these two constructs differ along several key points.
First, since organizational culture has both sociological and anthropological roots, it is understood at a deeper, almost unconscious level.
31
As such, it is most often studied qualitatively, allowing researchers a more in-depth examination of these embedded processes.13,31 Indeed, most efforts to study organizational culture quantitatively have been unsuccessful in the organizational studies literature.
32
These difficulties extend to the IS literature where in order to measure key components of Schein’s
33
model, one instrument
27
consisted of 85 items assessed across seven dimensions. This makes for a lengthy organizational survey, especially when trying to assess additional variables. These challenges in quantifying organizational culture are consistent with Schein’s
33
explanation that culture is best revealed through interaction … [and that] this process of deciphering [culture] cannot be standardized because organizations differ greatly in what they allow the outsider to see. Instead you have to think like the anthropologist, lean heavily on observation, and then follow up with various kinds of inquiry.
Second, values, a key component of Schein’s 33 model, can be difficult to change and tend to be distal predictors of workplace behavior.33–35 Given that the central focus of the organizational culture approach is to fundamentally change employees’ values, this method might not be as effective as an organizational climate approach, which focuses directly on changing employees’ behavior.
A third inherent component of the organizational culture approach, and by extension, existing scales, is the focus on the role of top management20,24 with an underlying assumption that if top management values IS, these values will trickle-down throughout the organization. While top management’s commitment to the domain-specific goal is important, organizational climate research suggests that the direct supervisor has more of an impact on employee behavior than does the top leadership.36,37 This is because while top management might set policies and procedures for the entire organization, the implementation of these policies and procedures occurs at lower levels of the organization, often in the form of supervisor discretion in the support of daily practices and enforcement of policies and procedures. It is then this implementation that drives employees’ climate perceptions and subsequent behaviors. 36
Finally, inherent to the organizational climate approach is its focus on a specific domain and operationalization in relation to a competing priority. 36 Often employees disregard existing policies and procedures surrounding the domain-specific area because these policies and procedures conflict with a competing priority. For example, Zohar and Luria 38 consider safety in regard to expediency. In a strong safety climate, the focus is on ensuring that employees behave safely and comply with safety policies and procedures, even when doing so compromises expediency, and ultimately, productivity. Therefore, an organizational climate approach is applicable to IS since researchers20,39 suggest that employees compromise IS to be more productive. Within a healthcare setting, the competing priority is more serious given that in addition to productivity, healthcare providers must also balance patient safety/care with patient confidentiality.
This study
For many of these reasons, organizational culture approaches in the IS literature have taken more of an in-depth case study of a single organization’s approach to IS. However, an organizational climate approach is quantitative with the goal of improving organizational effectiveness in a specific area. 31 Organizational climate researchers15,16 have had much success in developing parsimonious and well-validated measures of domain-specific organizational climate scales. These scales focus on contextual aspects of the environment with the goal of changing domain-specific employee behavior. 31 These approaches have been quite successful, particularly in the safety domain, as both primary 40 and meta-analytic research41–44 have linked safety climate to an increase in employees’ safety-related behaviors, ultimately reducing accidents. While safety regulations already existed, the organizational climate was often the mechanism used to secure employee compliance with these regulations. Given the success of organizational climate approaches in the workplace safety domain and following the call of researchers45,46 to treat IS like workplace safety, we apply the approach to IS. To do this, we build on validated and well-known safety climate measures to develop the Information Security Climate Index (ISCI).
We define IS climate as a multidimensional construct consisting of the shared perceptions of the IS policies and their manifestations in the organization. These can be categorized into the following: what is practiced in the organization, the observed importance placed on IS in the organization, and the laxness surrounding IS activities. That is, organizations with strong IS climates have clear rules and procedures for employees’ handling of confidential data. Moreover, importance is placed on keeping data secure, even if it means employees taking extra time to do so. This is manifested in management’s, particularly the direct supervisor’s, encouragement of the secure handling of confidential data and the correction of instances where employees treat data in an insecure fashion. We propose that the ISCI will be related to employees’ IS motivation and behaviors and empirically test this proposition. This prediction is grounded in the safety climate literature where research41–44 has linked safety climate to employees’ motivation to engage in safety-related behaviors and engage in actual behaviors such as safety compliance and safety participation.
Methods
Sample
Participants were recruited through email addresses contained in a public database available on the Florida Department of Business and Professional Regulation website. We chose four of the larger healthcare occupations to represent a wide range of activities and settings. These included certified nursing assistants (CNA’s), dentists, pharmacists, and physician assistants (PA’s). Given inaccuracies of the database including retirements and incorrect data listed for individuals, it was not possible to calculate the number of eligible participants who received invitations to participate.
Survey instrument
Likert-type scale surveys were used to assess each variable. The ISCI was used to assess IS climate. The ISCI was developed using two previous pilot studies, which are detailed in Supplemental Appendix 1. The scale contains 9 items along three subscales. These resulting items were based on a series of factor analyses designed to reduce the initial item pool to a reasonable number of items. After examining the resulting items, we subsequently named the three subscales: practices (i.e. behaviors and discussions that are actively initiated by the supervisor in the interest of promoting IS), importance (i.e. the importance placed on the protection of confidential data), and laxness (i.e. the prioritization of other activities, particularly work activities, over IS). The laxness subscale was reverse coded so that higher scores on all subscales indicated a stronger IS climate. Items were assessed along a 5-point Likert-type scale with 1 indicating “strongly disagree” and 5 indicating “strongly agree.”
To assess IS-related motivation and behavior, we adapted three commonly used safety indicators 47 to the IS domain (see Supplemental Appendix 2). These include one indicator of motivation and two indicators of behavior (i.e. compliance and participation). Consistent with the definition of safety motivation, IS motivation refers to the extent to which employees believe that IS is worthwhile or of value. Along these lines, IS compliance refers to the degree to which employees abide by core rules that concern the protection and usage of private data. Finally, IS participation refers to extra role behaviors in which employees go above and beyond simple rule application or compliance and engage in behaviors that promote the safe handling of data throughout the workgroup and organization. Each scale contained three items assessed along a 5-point scale with 1 indicating “strongly disagree” and 5 indicating “strongly agree.” Higher scores indicated a higher level of motivation, compliance, or participation.
Given that these three measures were general in nature, we designed a checklist of specific high-risk IS behaviors (also referred to as high-risk security behavior checklist) to cross-validate with a behavior-specific scale. The checklist contained seven items focusing on the frequency in which the healthcare professional engaged in behaviors that could expose confidential patient data here. These items aligned with some of the frequently cited employee behaviors that led to the exposure of patients’ data in reported US healthcare data breaches. 5 All items were assessed along a 4-point scale with 1 indicating “none” and 4 indicating “three times or more” (with the exception of the first two items where 4 indicated “five or more times”). Examples include “How many times in the past year have you taken a laptop or other device home that had sensitive information?” and “How many times in the past year have you left a computer unlocked with patient data showing?” To obtain a score, we took an average of each participant’s responses across all seven items. Higher scores indicate higher risk security behaviors. Original items are depicted in Supplemental Appendix 3.
Analyses
Demographic statistics were calculated using SPSS version 24. As a first step, we provide demographic information such as gender, age, race/ethnicity, highest level of education, and work setting for the total sample as well as for each of the four occupational groups.
We then conducted a factor analysis on the ISCI. Factor analyses are used to group like scale items together. Researchers typically use two types of factor analyses: exploratory factor analysis (EFA) and confirmatory factor analysis (CFA). An EFA is used when researchers are unsure of the number of predetermined factors. This helps researchers to set the number of factors and determine which items load onto each factor through an inspection of item loadings. As can be seen in Supplemental Appendix 1, a series of EFAs were conducted early in the scale development process (Supplemental Appendix 1, pilot study 1). Once a preliminary factor structure is set using the EFA, a CFA is used to “confirm” or test these results (as was done in pilot study 2 reported in Supplemental Appendix 1). In this study, using the Mplus 7.1 program, 48 we use a CFA to confirm the ISCI’s factor structure obtained from the prior two studies.
In the third step of our analyses, we used SPSS version 24 to calculate the mean, standard deviation, potential range, and observed range for each study variable. We also calculated Pearson product-moment correlation coefficients between all study variables and use the correlations between the ISCI and the motivation/behavior variables to demonstrate the utility of implementing an IS climate. As part of this analysis, we also explore the relationships between the ISCI, motivation, behavior variables, and demographic variables (i.e. age, sex, and education). Finally, in order to detect whether there were differences among occupational groups on the ISCI, motivation, compliance, participation, and high-risk security behavior checklist, we conducted a one-way multivariate analysis of variance (ANOVAs) using SPSS version 24. A MANOVA is used to detect differences among factors (i.e. the four occupational groups) on multiple variables, in this case, the ISCI and the motivation/behavioral variables under investigation. A MANOVA is preferable over a series of univariate analyses of variance (ANOVAs) equations because it helps to reduce Type I error rates, takes into account relationships among dependent variables, and provides an overall index of significance. If the MANOVA is significant, it is then appropriate to examine the one-way ANOVA results for each variable. If the one-way ANOVA results are significant, post hoc tests are used to pinpoint the mean differences.
Results
Demographics
A total of 261 employees across the four occupational groups responded to the survey, with usable data received from 252 employees (male = 91, female = 136, with the remaining 25 individuals declining to provide that information). The mean age was 46.57 (SD = 13.45) and the sample was mostly white (67.5%). Participants worked in a variety of medical settings including hospitals, physicians’ offices, rehabilitation centers, and nursing homes. On a whole, the sample was well educated with 34.9 percent reporting their highest degree earned was at the doctoral level and 26.9 percent reporting their highest degree earned was at the master’s level. Table 1 contains a breakdown of demographics of each of these groups.
Sample demographics.
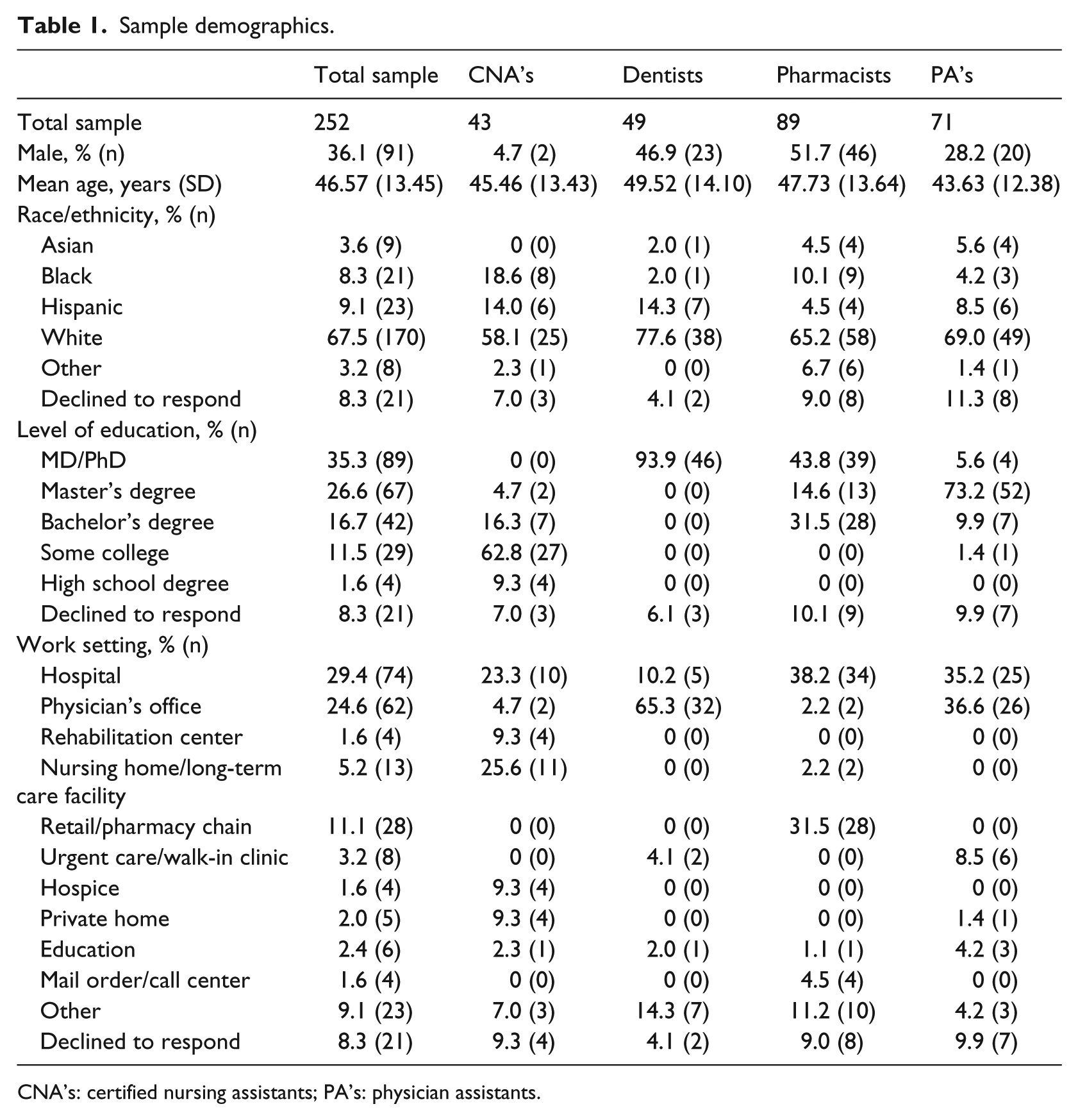
CNA’s: certified nursing assistants; PA’s: physician assistants.
ISCI CFA
A second-order CFA was conducted using Mplus 7.1.
48
Each scale item was loaded onto the proposed scale factor. Then, each of the three first-order factors was loaded onto a second-order latent factor, representing overall IS climate. Based on recommendations in Gefen et al.,
49
results indicated adequate fit for the proposed factor structure (
Linking the ISCI to employee motivation and behavior
The full correlation matrix is available in Table 2. Cronbach’s alphas were above the 0.70 threshold 50 with the exception of the high-risk security behavior checklist variable. This scale was designed as a formative and not a reflective scale, rendering Cronbach’s alpha, and other internal consistency metrics, an inappropriate measure of reliability. 51 This practice is not uncommon in the behavioral sciences and can be seen with a number of scales. 51 Overall, correlations among study variables indicate significant relationships between the ISCI and outcome variables of IS motivation and IS behavior. Correlations between sub-factors of the ISCI and the motivation as well as three behavior variables were significant and in the expected directions (r’s ranged between 0.25 and 0.47, p’s < 0.01). In addition, correlations between the overall ISCI and motivation (r = 0.50, p < 0.01), compliance (r = 0.57, p < 0.01), participation (r = 0.57, p < 0.01), and high-risk security behavior checklist (r = –0.46, p < 0.01) were significant and in the expected directions. Results also suggest that older employees were significantly more likely to engage in IS participation and significantly less likely to engage in high-risk security behaviors. In addition, females reported a significantly poorer IS climate than males but also reported engaging in significantly more IS participation behaviors and significantly fewer high-risk security behaviors.
Study correlations.
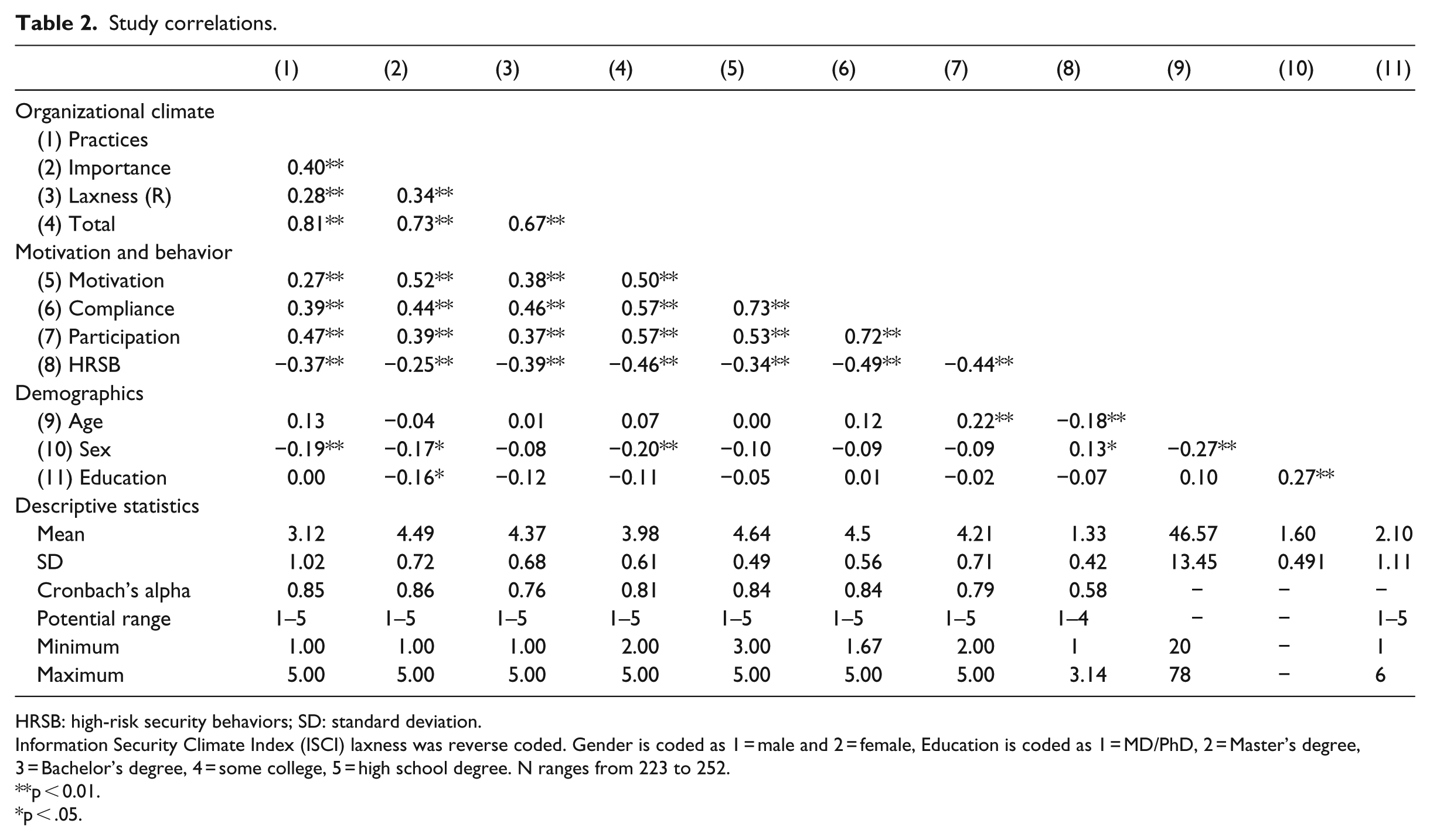
HRSB: high-risk security behaviors; SD: standard deviation.
Information Security Climate Index (ISCI) laxness was reverse coded. Gender is coded as 1 = male and 2 = female, Education is coded as 1 = MD/PhD, 2 = Master’s degree, 3 = Bachelor’s degree, 4 = some college, 5 = high school degree. N ranges from 223 to 252.
p < 0.01.
p < .05.
Differences among occupational groups
Results of the one-way MANOVA indicated support for a multivariate main effect for occupational groups (Wilks’ λ = 0.841, F(15, 643.612) = 2.770, p < 0.001, partial eta squared = 0.057). The observed power to detect a significant effect was 0.996. Given the detection of a significant main effect, we inspected the resulting univariate main effects (one-way ANOVAs), which examined whether there were differences in occupational groups for each variable. Significant main effects were detected for all variables: ISCI total (F(3, 240) = 4.324, p < 0.01, partial eta squared = 0.052, power = 0.864), motivation (F(3, 240) = 5.260, p < 0.01, partial eta squared = 0.062, power = 0.926), compliance (F(3, 240) = 6.396, p < 0.01, partial eta squared = 0.984, power = 0.967), participation (F(3, 240) = 3.519, p < 0.05, partial eta squared = 0.043, power = 0.778), and high-risk security behavior checklist (F(3, 240) = 7.389, p < 0.01, partial eta squared = 0.086, power = 0.984).
The significant ANOVA results indicate that there are mean differences among the occupational groups but do not pinpoint these differences. Therefore, Tukey post hoc tests were used to compare the mean scores among all occupational groups on the variables of interest. The occupational group means and standard deviations are reported in Table 3 and significant results of Tukey post hoc tests are reported in Table 4. Tukey post hoc test results indicate that for both motivation and compliance, the pharmacists’ mean scores were significantly better than for the other three occupational groups. For the ISCI, the pharmacists’ mean score was significantly better than only the PA’s. Finally, for the high-risk security behavior checklist, the PA’s engaged in more high-risk security behavior than the other occupations. There were no significant differences between the pharmacists and the other occupational groups.
Group means.
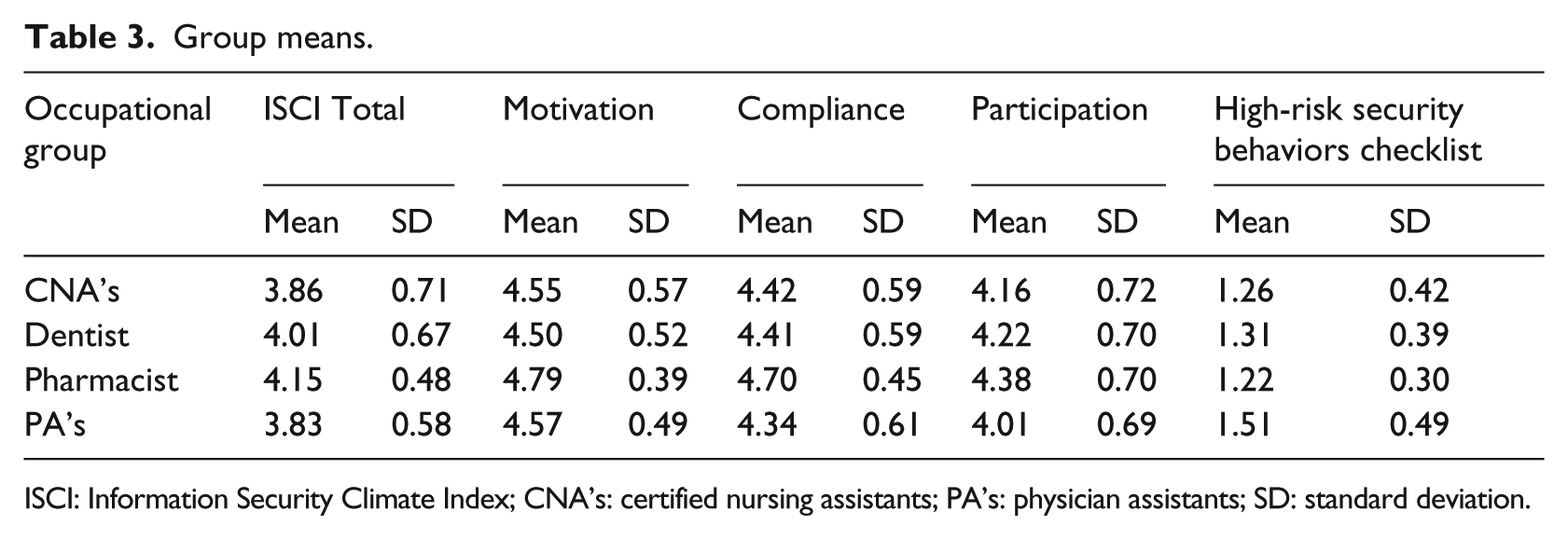
ISCI: Information Security Climate Index; CNA’s: certified nursing assistants; PA’s: physician assistants; SD: standard deviation.
Significant post hoc tests (Tukey).
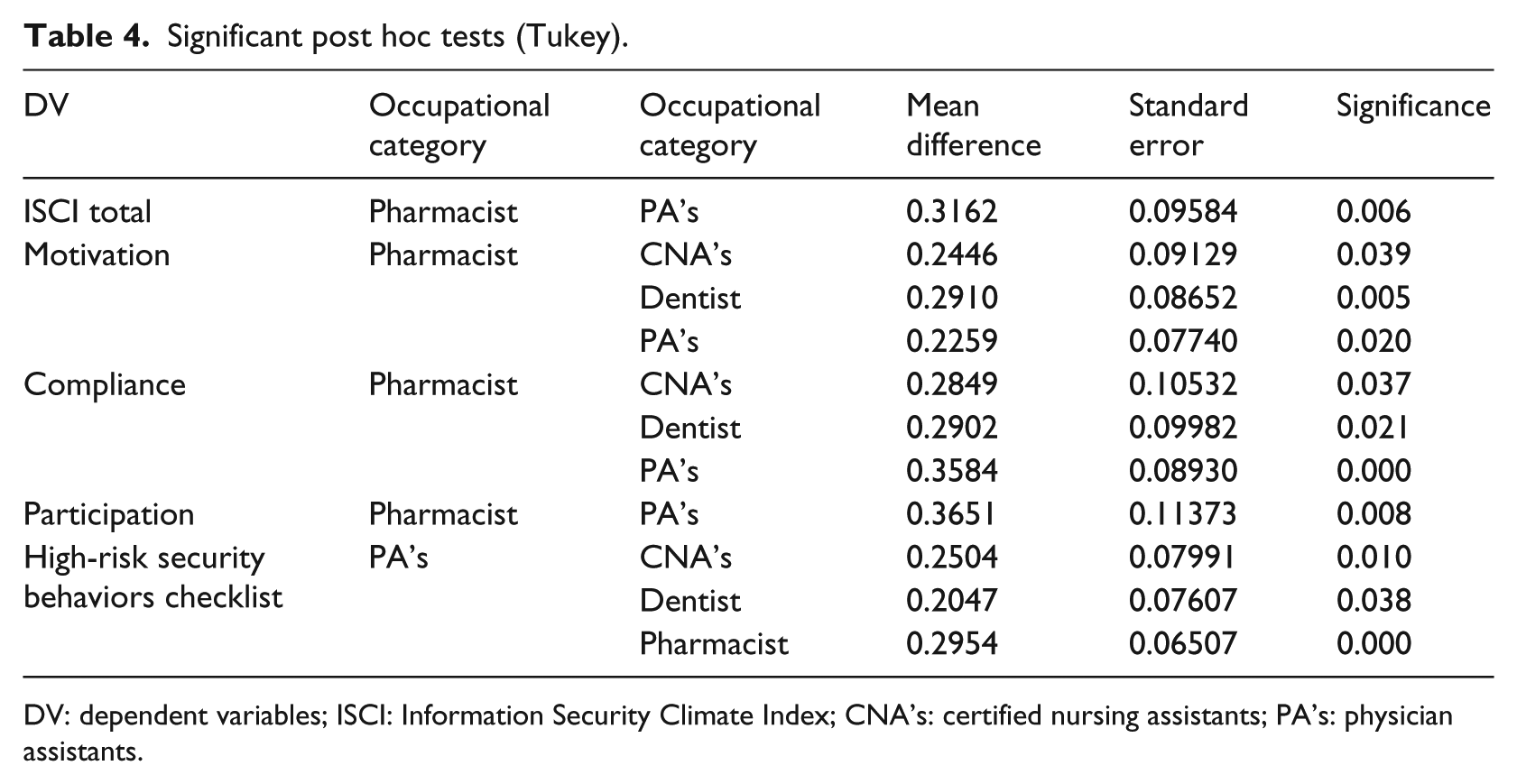
DV: dependent variables; ISCI: Information Security Climate Index; CNA’s: certified nursing assistants; PA’s: physician assistants.
Discussion
The root of the majority of breaches lies with employee negligence and/or carelessness surrounding IS, something that cannot be fully mended through legislative or technological remediation.8–11 As a result, it is necessary to focus on changing employees’ behavior surrounding IS. To do this, we introduce the ISCI, a parsimonious (i.e. nine items) tool that was developed using two pilot studies, representing an extensive validation effort based on best practices in scale development.50,52 The ISCI can be used by a variety of healthcare organizations to quickly and inexpensively assess their IS climate. This will allow these organizations to make decisions regarding where they should target IS interventions. The current approach differs from that of other instruments that take a case study approach to auditing organizations’ policies, regulations, and training as opposed to employees’ behavioral reactions to them.
Implications
The results of this study have important practical implications. Fundamentally, IS climate has the potential to positively impact employees’ motivation and behavior, thereby ultimately reducing the number of data breaches. Given most data breaches are due to insider actions or lack of actions, a focus on organizational features that might affect employee behavior would be an obvious point of intervention. A number of studies in the safety climate literature have shown that training can be used to improve climate. 53 Such approaches could be modified to improve the IS climate of organizations that deal with sensitive data. Second, it seems that older employees are more careful with confidential data than are younger employees. Given that younger employees are often considered to be more “tech savvy,” this finding was unexpected. It could be that older employees are more conscientious and therefore are more careful with patient data. Another interesting finding was that despite HIPAA laws governing all occupations, pharmacists seemed to have the best IS climate, motivation, and behaviors while PA’s had some of the worst scores. Perhaps this occurred because the pharmacists, who often handle patients’ sensitive data in front of other members of the public, are more aware of the importance of IS. Regarding PA’s, it could also be the case that they sometimes consult with patients in waiting rooms in front of other patients and prioritize discussing a patient’s health information over IS. Regardless of the reasons underlying the observed occupational differences, these results point to the need for additional IS training, especially for PA’s. While some training should target the incumbents, research 38 suggests that training for the incumbents’ supervisor might be more important given the central role he or she plays in shaping the organizational climate.36,37
Limitations
There are several limitations that should be kept in mind when interpreting the results of this study. First, the focus on IS could conflict with patient safety and care. This type of tension between competing priorities is inherent to the organizational climate approach and specifically exists in the safety climate domain between safety and expediency. That is, in order to behave safely, employees often have to work more carefully and slowly, thereby reducing productivity. The same tension likely exists in the IS climate domain as data security could compete with providing expedient or quality care. This study did not directly address this underlying tension, but future studies should directly examine these competing priorities.
Another limitation is that the ISCI did not assess opportunities for training, which could reinforce desirable IS practices. Although the initial set of items contained several items related to training, the factor analysis did not support the inclusion of these items, indicating that these items were strongly related to other practice items and therefore subsumed within this factor. One reason for this could be that training supports the organizational climate but might not be a central component given organizational climate’s focus on policies, practices, and procedures. In other words, training programs may alert employees of the proper practices and existing policies and procedures but that does not necessarily mean that IS will be prioritized in the workplace.
Furthermore, only four occupation groups in a single state were surveyed. Additional research, including additional occupational groups, throughout the United States is needed to generalize study findings. In addition, it is important to note that study data were cross-sectional and therefore causality cannot be inferred. Finally, this study did not examine whether IS climate differs among settings. It could be that retail pharmacies, where pharmacists are most often employed, have stronger IS climates than private practices. Future research should examine these settings to tease apart the role of the setting and the role of the occupation.
Conclusion
In conclusion, data breaches will likely continue to occur for the foreseeable future. Despite concerns about external hackers, much of the danger originates within organizations in the form of careless and/or negligent employee behaviors. An organizational climate approach represents a promising way to fundamentally change behavior. Study results indicated that an IS climate is related to desired employee behaviors, and thus, it can be potentially helpful for changing behavior surrounding information privacy and security.
Supplemental Material
Appendix_1 – Supplemental material for Information security climate and the assessment of information security risk among healthcare employees
Supplemental material, Appendix_1 for Information security climate and the assessment of information security risk among healthcare employees by Stacey R Kessler, Shani Pindek, Gary Kleinman, Stephanie A Andel and Paul E Spector in Health Informatics Journal
Footnotes
Acknowledgements
All authors made a substantial intellectual contribution to the body of work.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Supplemental material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
