Abstract
In modern cryptography, Substitution Boxes (S-boxes) are critical in introducing confusion into ciphertext, significantly enhancing encryption security. With the rising sophistication of hacking techniques, there is a growing need to develop stronger and more dynamic S-boxes. This paper proposes a novel method for constructing cryptographically secure S-boxes using graph theory, specifically based on the Minimum Spanning Tree (MST) of cycle graphs. The process begins by converting plaintext into vertices, forming a cycle graph. Special characters are incorporated, and ASCII-based values are assigned to vertices. The distance between vertices is calculated using their intersections, leading to the creation of an MST graph. The final step involves obtaining the adjacency matrix, which is further processed to generate the S-box. The S-box's unpredictability is enhanced by employing the S256 permutation from the symmetric group. Various cryptographic tests are conducted to evaluate the proposed S-box's performance, with results demonstrating its robustness when compared to existing S-box designs. Furthermore, this S-box is applied to an image encryption scheme, and its efficacy is thoroughly assessed. The findings highlight the potential of the proposed method to contribute significantly to cryptographic security.
Introduction
In recent years, the popularity of computers and their network connections has grown significantly. It goes without saying that since military communications gather an astounding amount of sensitive information, ensuring access control, confidentiality, and authentication in all defense communications is essential. This led to the realization of the need for authentication and the importance of protecting data and systems from network intrusions; as a result, research on cryptography and other security-related topics is currently happening. The importance of cryptography has grown and changed over time, therefore even a slight increase in the performance efficiency of the cryptographic algorithms is prized.
The main objective of data security is to provide safe data transit via erratic networks. In the context of contemporary digital communications, data security is a complex issue with numerous facets. Data security, which comprises robust data encryption techniques, secure communication protocols, and trustworthy third parties to maintain database security, is the primary subject of this research study. The sciences, in conjunction with graph theory, produce incomprehensible data that requires the use of cryptography to decipher for the intended recipient. By using encryption, change our data into cipher text or another unreadable format. Encryption and decryption are mutually exclusive processes. Therefore, in order to improve data security, effective encryption/decryption techniques must be implemented. The only established technique for preserving data security is encryption. The information might be accessed by an unauthorized person with malicious intent.
Network security and data transfer across wireless networks are achieved through the use of cryptography. The core idea behind safe data transfer on erratic networks is data security. In today’s world of data communications, data security encompasses a wide range of tasks, such as reliable third-party database maintenance, powerful data encryption methods, and secure communication connections. The safe transfer of sensitive (secretive) data is receiving a lot of attention due to the quick advancement and development of information technology. In network security, the neighboring matrix is essential for transmitting the secure keys.
The importance of cryptography has witnessed an immense increase lately, especially for secure sensitive information in the military communication system. In recent research studies, most studies have been toward cryptographic algorithms to achieve better performance and security. The scope of encryption methods-related study should be appreciated from these research studies. For instance, cross-channel color image encryption with a 2D hyperchaotic hybrid map distinctly delivered robust encryption capacities in multimedia applications. In return, such chaotic systems again apply successfully in complex encryption tasks. 34 Cross-channel color image encryption through a 2D hyperchaotic hybrid map of optimization test functions). Another is PSO which is recently used in image encryption. Modular integrated logistic exponential maps are used to enhance security and efficiency in this sense. In the use of a PSO-based image encryption scheme using a modular integrated logistic exponential map, very minimal cryptanalytic attacks were noted. Further, the newly proposed fractional-order 3D Lorenz chaotic systems and 2D discrete polynomial hyper-chaotic maps have demonstrated promising results in multi-image encryption applications for high performance. Exploiting newly designed fractional-order 3D Lorenz chaotic system and 2D discrete polynomial hyperchaotic map for high-performance multi-image encryption. 35
These studies reflect an area that has gained much interest in the intersection of modern cryptography and optimization methods with chaos theory, offering diverse means of improving the efficiency as well as security of encryption methods. Our work aims at integrating these approaches for developing cryptographic systems secure from intrusions. Some of the focus points are of significant importance: S-box designs prove to be crucial in data protection against intrusions into the network.
A novel approach to building durable S-boxes via linear transformation was put forth in. 20 This approach improves the output S-box using the permutation process. The authors additionally create DNA-based cryptographic ciphers and durable S-boxes by following the procedures described in.21–26 Wang et al. 27 proposed a genetic algorithm and chaos-based strategy for S-box construction after redefining the problem as a traveling salesman problem. Qin et al. 28 applied the algorithm from artificial bee colonies to the design of S-boxes. Wang et al. 29 proposed a strategy for S-box design that combines chaos with optimization of improved nonlinearity. Tian and Lu 30 developed a method for constructing S-boxes by integrating an interwoven logistic map with bacterial foraging optimization. Farah et al. 31 provided a method for creating S-boxes. Using a chaotic map and a teaching-learning optimization strategy,
Cryptanalysis of image encryption focuses on the strengths and weaknesses of image encryption algorithms. Cryptanalysis involves discovering weaknesses that may be exploited to break or reduce the security associated with these algorithms. In recent years, several image encryption methods that have their foundation based on quantum chaotic maps and DNA coding used randomness in conjunction with biological-inspired operations to achieve even better security.
For example, cryptanalyses on chaotic map algorithms usually look at the sensitivity to initial conditions and randomness properties of such maps. However, at times an attacker might use flaws in generating keys or odd behavior from chaotic maps for their advantage, so it is necessary to study this kind of cryptanalysis and ensure that the encryption is not easily reversible.
Image encryption cryptanalyses are also conducted to find the vulnerability using differential attacks, chosen-plaintext attacks, and brute force methods among others. Besides, it allows the decryption of such images using an encryption key, and an encrypted image such as this may expose vulnerabilities in an encryption scheme. The vulnerabilities help researchers enhance their algorithms in such a way that they become less vulnerable to attacks and improve data security in general. When it comes to image encryption cryptanalysis, it forms a major activity that helps researchers find the weaknesses in an encryption system and helps enhance cryptographic methods to protect digital images from potential threats. Khan et al.
32
outlined a systematic approach to S-box creation by integrating chaos with optimization of improving differential approximation probability. After studying chaotic maps and artificial bee colony optimization, Ahmad et al.
33
came up with a plan to construct S-boxes. An innovative method for post-processing to enhance the nonlinearity property in replacement boxes in Ref.
36
. But, the cryptographic features of AES S-boxes differ from those of S-boxes built using these methods.
Increased Need for Cryptography: in this direction, the growing use of digital communications, especially in military systems, has pointed out the necessity for cryptographic techniques to ensure data security, confidentiality, and authentication. Focus on Encryption for Data Security: Encryption is going to be a vital approach toward securing sensitive data mainly when transmitted across erratic networks. These effective encryption/decryption methods ensure that data security is not compromised by any unauthorized access. S-box Design for Enhanced Security: The work introduces novel and innovative techniques to design S-boxes using the principles of linear transformation, chaos theory, and optimization methodologies. Such designs result in more robust encryption against network intrusion attempts. Advancements in Cryptanalysis of Image Encryption: The role focuses on cryptanalysis, which is a crucial aspect for the exploitation of weaknesses in image encryption schemes. It also improves the cryptosystem because it makes it increasingly difficult to attack in differential mode as well as with key-recovery techniques.
In the “Definitions” section, some basic Definitions are discussed. The proposed algorithm and the algebraic structure underlying the suggested work for S-box generation are intended to be provided in the “Proposed Algorithm” section. The proposed S-box’s security analysis component is explained in the “Security Analysis” section along with a comparative examination of other S-boxes. Section “Majority logic criterion” of this paper focuses on implementing the suggested work using picture data and doing various tests. “Conclusion” section describes the conclusion of our work and its limits.
Definitions
Cryptography: This is the process of converting a normal communication into unintelligible cipher text and back again. Plaintext: is the term used in cryptography to describe the original, readable form of a message or basic text that needs to be encrypted to become unreadable. Cipher-text: The message that is changed in cryptography after a key is applied to plain text. Key: A variable that can be used with an algorithm to create encrypted text or decrypt encrypted text. Some unintelligible cipher text, known only to the sender and the recipient, is called a key. Encryption and Decryption: Encoding a communication with a key or other technique to make its meaning difficult to decipher is known as encryption and decryption. Decryption is the encryption technique’s opposite procedure, which turns cipher text back into ordinary language.
Adjacency matrix
This represents the graph in a matrix. Processors that use computers use it. Several matrix algebraic results may be voluntarily used to the study of graph structural properties, which is an advantage of adopting an adjacency matrix format. The vertices that are next to each other are specified in an adjacency list, which depicts a graph with a single edge. Choosing an ordering for the vertices is the foundation of this matrix. It is possible to depict directed and undirected graphs with this matrix.
Incidence matrix
The
Proposed Algorithm
Convert text into vertex. Give value to each vertex according to ASCII Table. Join each vertex to make a cycle graph. Calculate edge weight using the distance formula. Add a Special character (@) and find the minimum spanning tree of the cycle graph. Also, find the edge weight of the special character in the same way. Make an adjacency matrix of the data. Convert Diagonal Entries to x and apply summation on the matrix. Invert the summation and solve it under modulo 257 for the domain values 0 to 255.
Construction of S-Box
Let the text be “WATER” and convert all text into vertices. Add the vertices with each other which gives us the Cycle Graph and gives the Weight According to ASCII Table 1. Find out the Edge weight by using the ASCII distance Formula for two consecutive vertexes shown in Figures 1–4, respectively.

Convert text into vertices.

Join of vertex to make cycle graph.
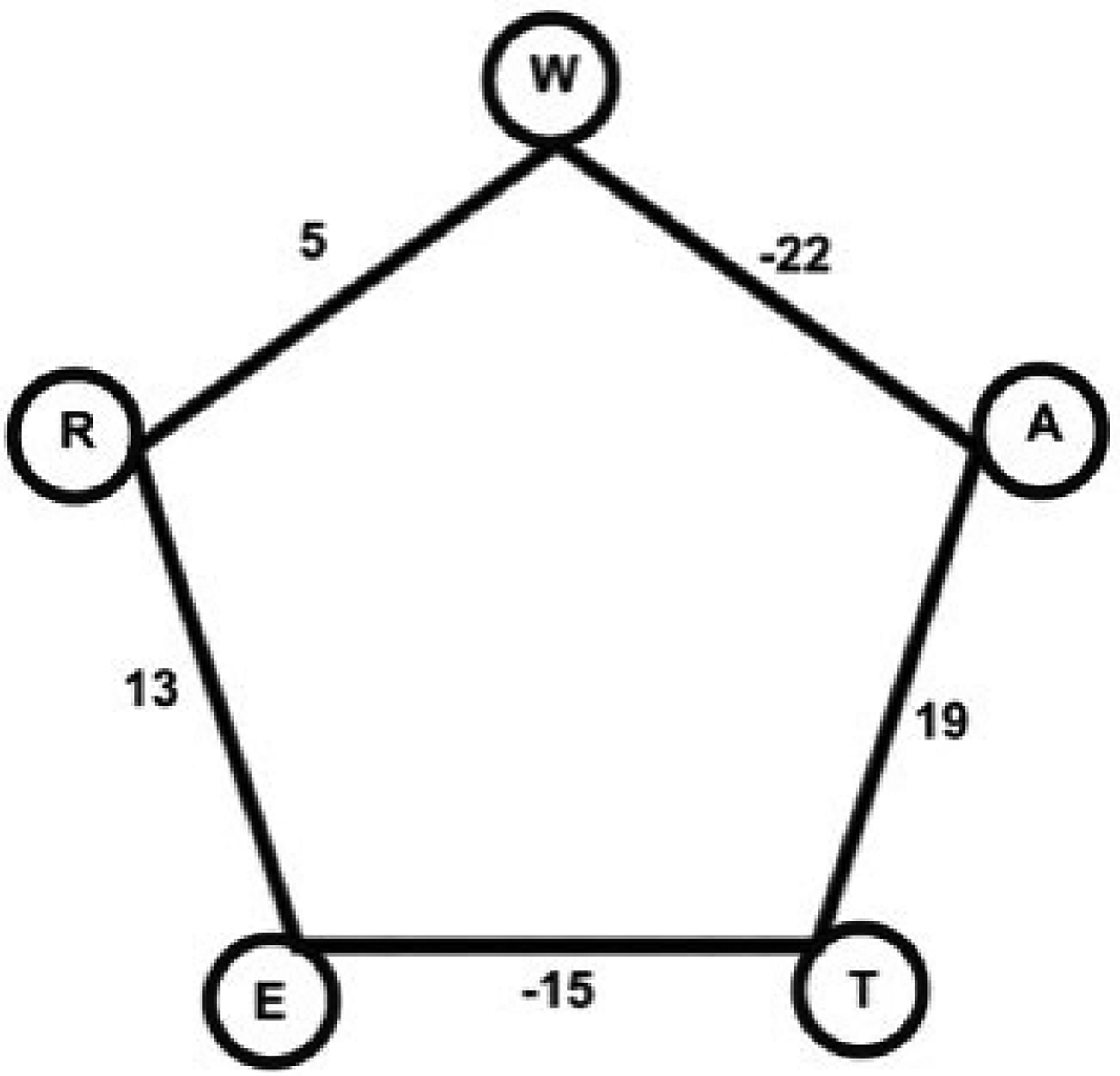
Edge weight with cycle graph.
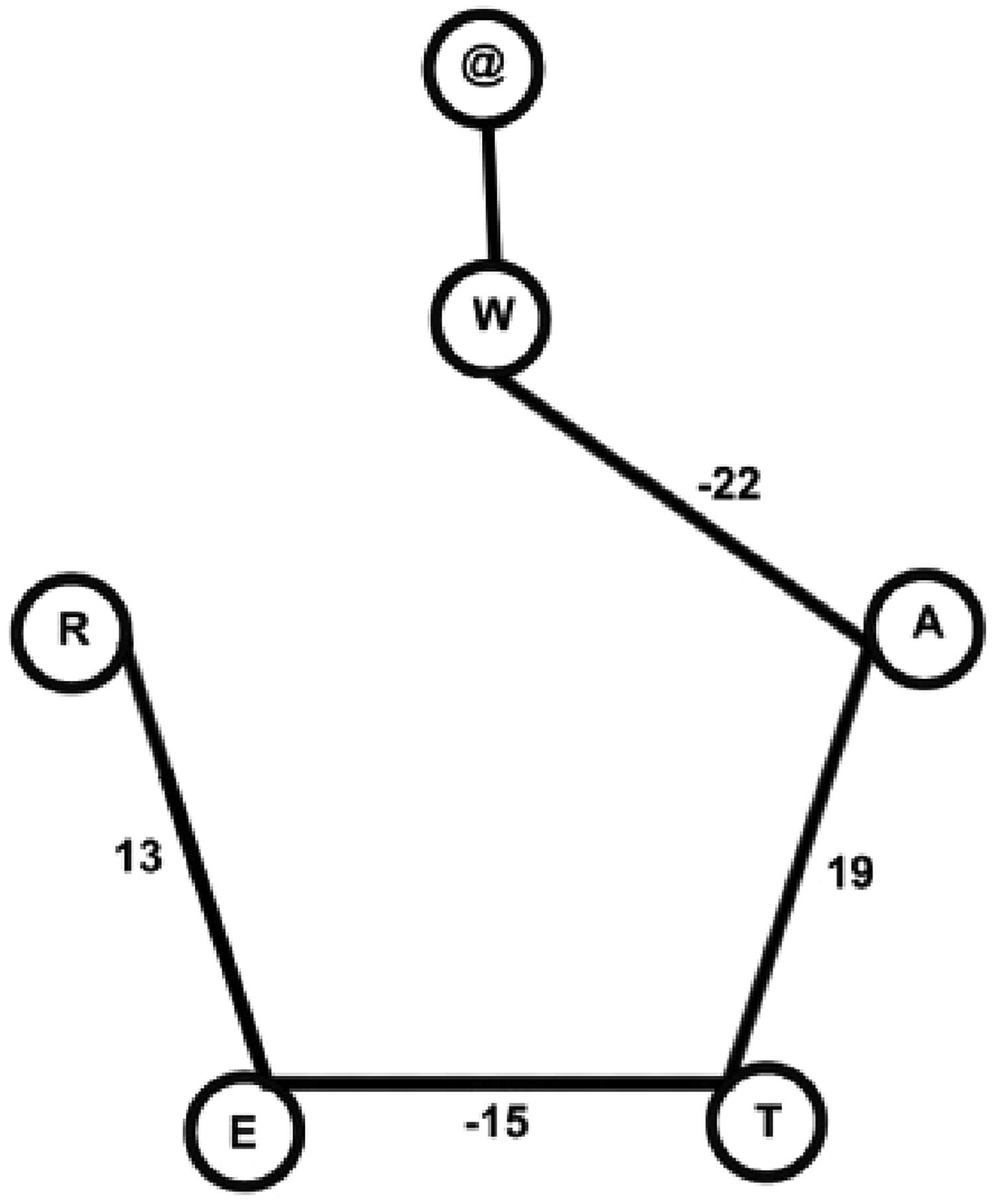
Special character with minimum spanning tree.
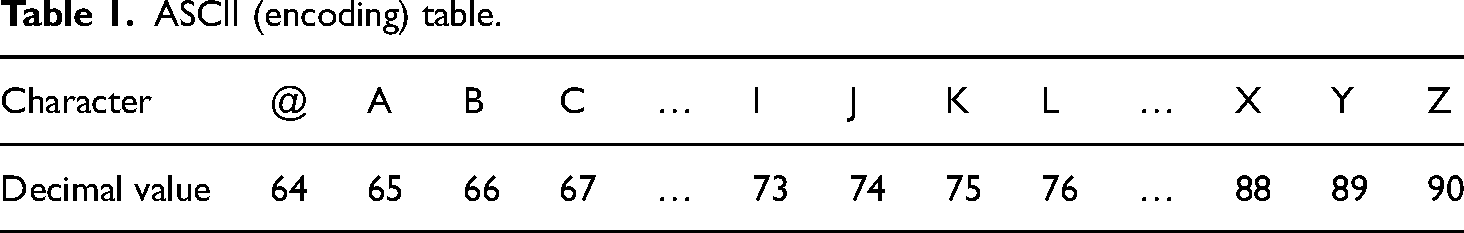
ASCII (encoding) table.
Add Special Character (@) and find its edge weight with connected Vertex. Find out the minimum spanning tree of a given graph that is produced and shown in Figure 4.
Now make the adjacency matrix by using edge weight


Initial S-box.
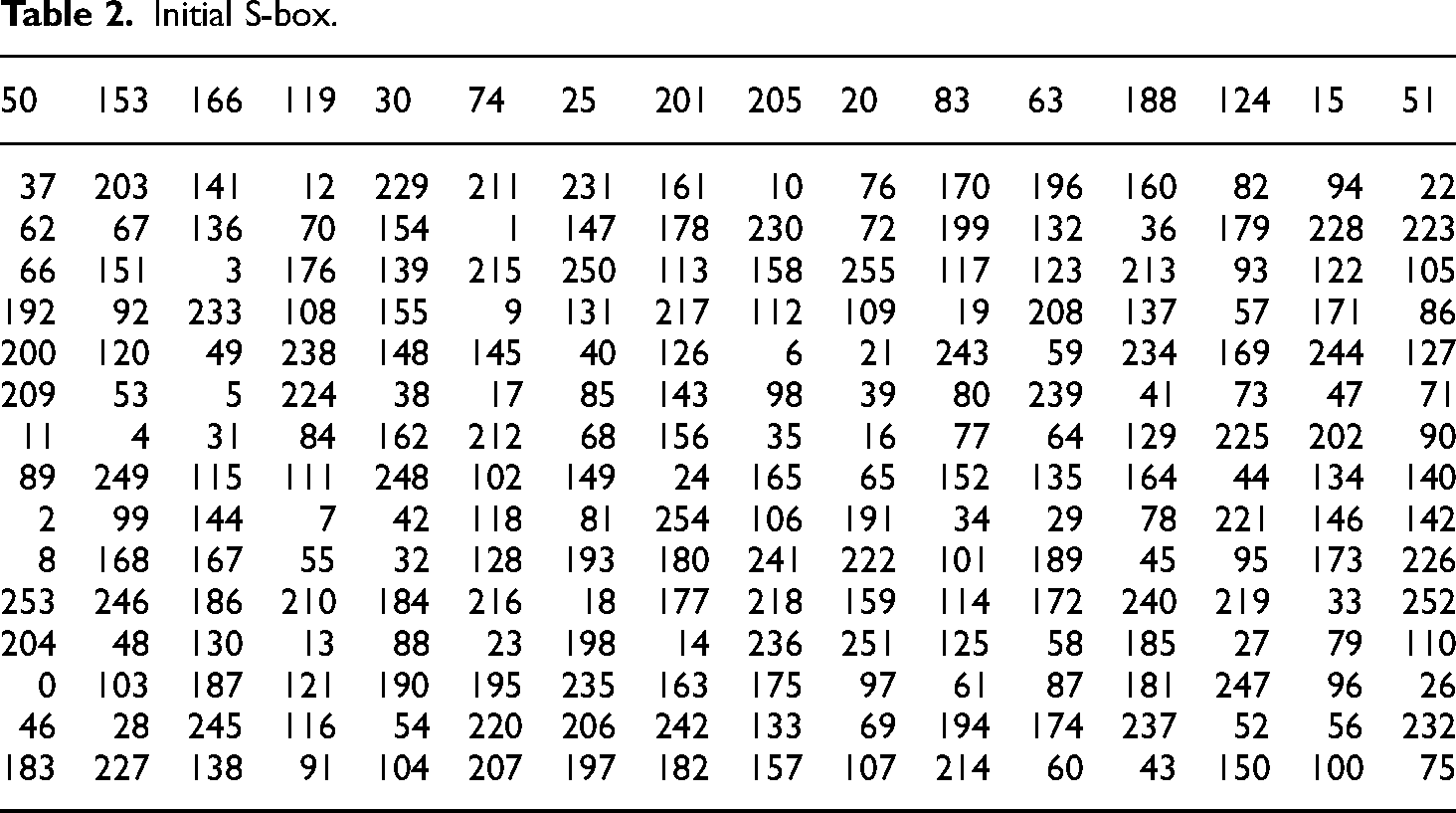
To create a highly nonlinear substitution box (S-Box), apply a symmetric permutation of 256 on the initial S-Box table. This resulted in Table 3, which exhibits greater security than the existing AES substitution boxes. Our proposed S-Box achieves an average nonlinearity value of 113, making it significantly more secure. The safety and robustness of the proposed S-Box have been validated through various cryptographic analyses. Additionally, we employed this S-Box in an image encryption application, demonstrating its practical effectiveness in enhancing security.
Proposed S-box.
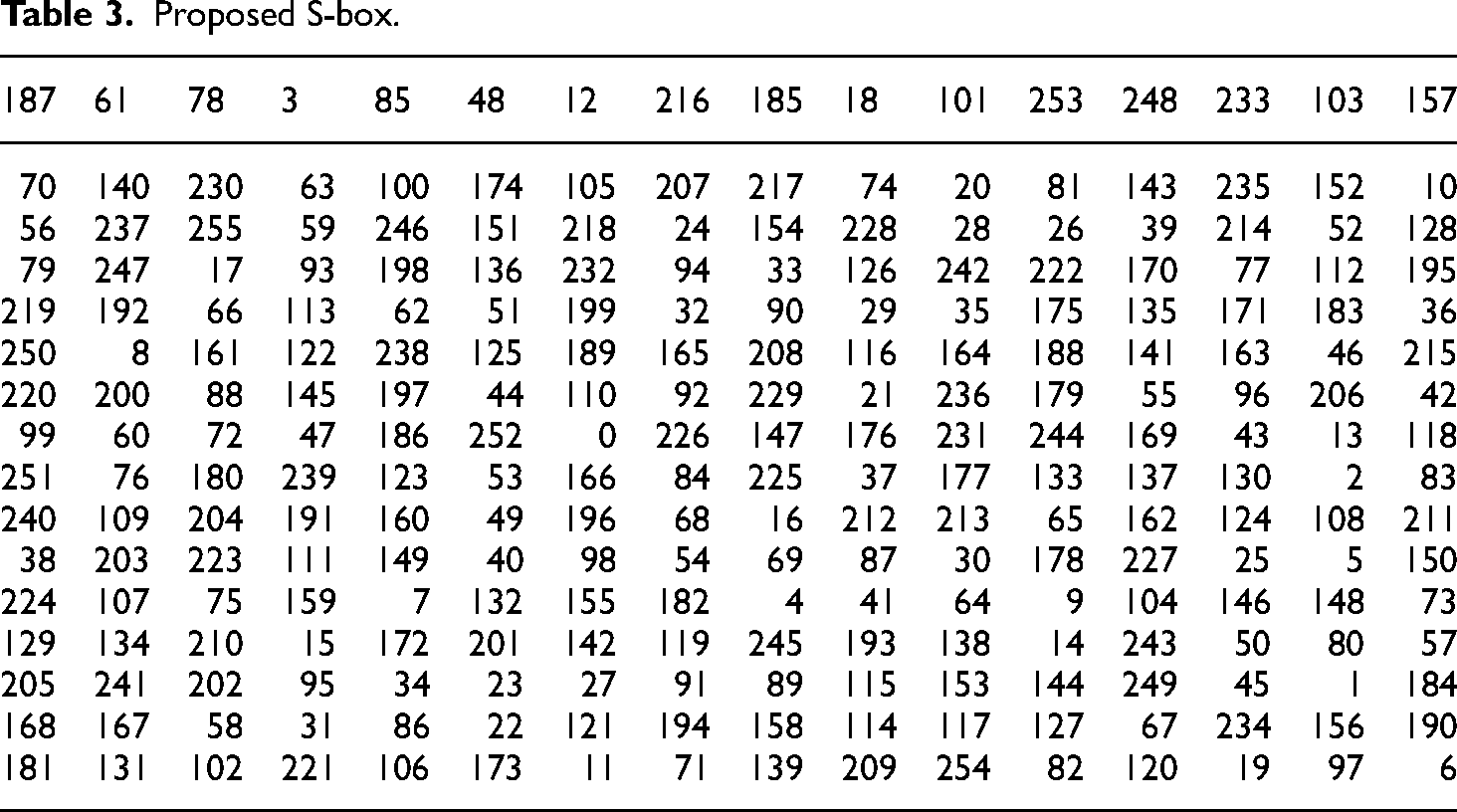
Symmetric permutation 256
(1,206,215,30,252,114,185,39,121,75,254,176,120,239,33,69,183,10,27,61,155,213,240,55,81,98,134,243,203,86,100,177,12,20,7,174,212,231,111,116,136,40,172,87,166,48,163,226,43,71,242,173,222,50,38,223,110,192,118,154,148,181,224,44,182,8,198,214,64,23,123,62,52,122,153,245,189,145,143,194,6,26,130,221,241,79,78,208,103,5,171,11,144,18,162,225,95,124,187,234,169,210,15,196,127,211)(2219)(3,135,165,72,25,32,230,97,250,178,37,41,19,93,238,47,42,115,228,90,106,45,80,229,168,131,218,255,21,105,167,202,129,217,76,89,256,179,115,157)(4,200,204,227,201,107,207,49,67,14,158,244,216,94,125,193,147,220,170,60,133,13,92,36,17,138,156,74,146,113,247,101,161,82,253,126,137,88,58,35,54,96,236,22,160,199,53,249,16,70,188,197,99,175,246,24,283,150,128,73,63,84,85,191,57,233,140,77,141,91,205,9,209,119,152,251,46,108,132,164,109,186,180,195,142,102,51)(28,151)(29,149,112,248,184,139,31,56,68,159,191,65,66,104)(34,237)(59,235,232)
Security Analysis
Strict Avalanche Criterion
According to the rigorous strict avalanche criterion (SAC), if you change an input, it will affect the output. This metric is a combination of the avalanche effect and completeness. The avalanche effect states that half of the bits in the cipher text should be affected by a one-bit change in the plaintext (see Table 4). If you want your output to be full, every bit of the plaintext has to go into it. By analyzing the cipher text, a cryptanalysis specialist can determine the key using a known plaintext attack, as long as they modify only a little piece of the plaintext. This is possible because of the relationship between input and output.
Strict avalanche criterion.

The SAC is an essential component of any cryptography S-box. This S-box can pass the rigorous avalanche tests if it meets the completeness and avalanche requirements. By changing the
Bit independent criterion
When one input bit changes, this test finds the correlation between each pair of output bits (as suggested by.
37
This test yields a 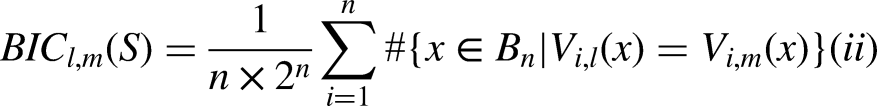
BIC-SAC.

BIC NL.

Linear approximation probability
A measure of the S-box’s fortitude or resistance to linear assaults is the linear approximation probability (LAP) criterion. The S-box’s security strength increases as the LAP value decreases. The resulting S-box’s LAP, which is 0.1484, is less than that of.2–13 This illustrates that the proposed technique has the capacity to produce a robust, effective, and attack-resistant S-box.
Differential uniformity
The differential probability (DP) or equiprobable input/output XOR distribution of a particular S-box can be found using the formula.
Input/output XOR distribution table.
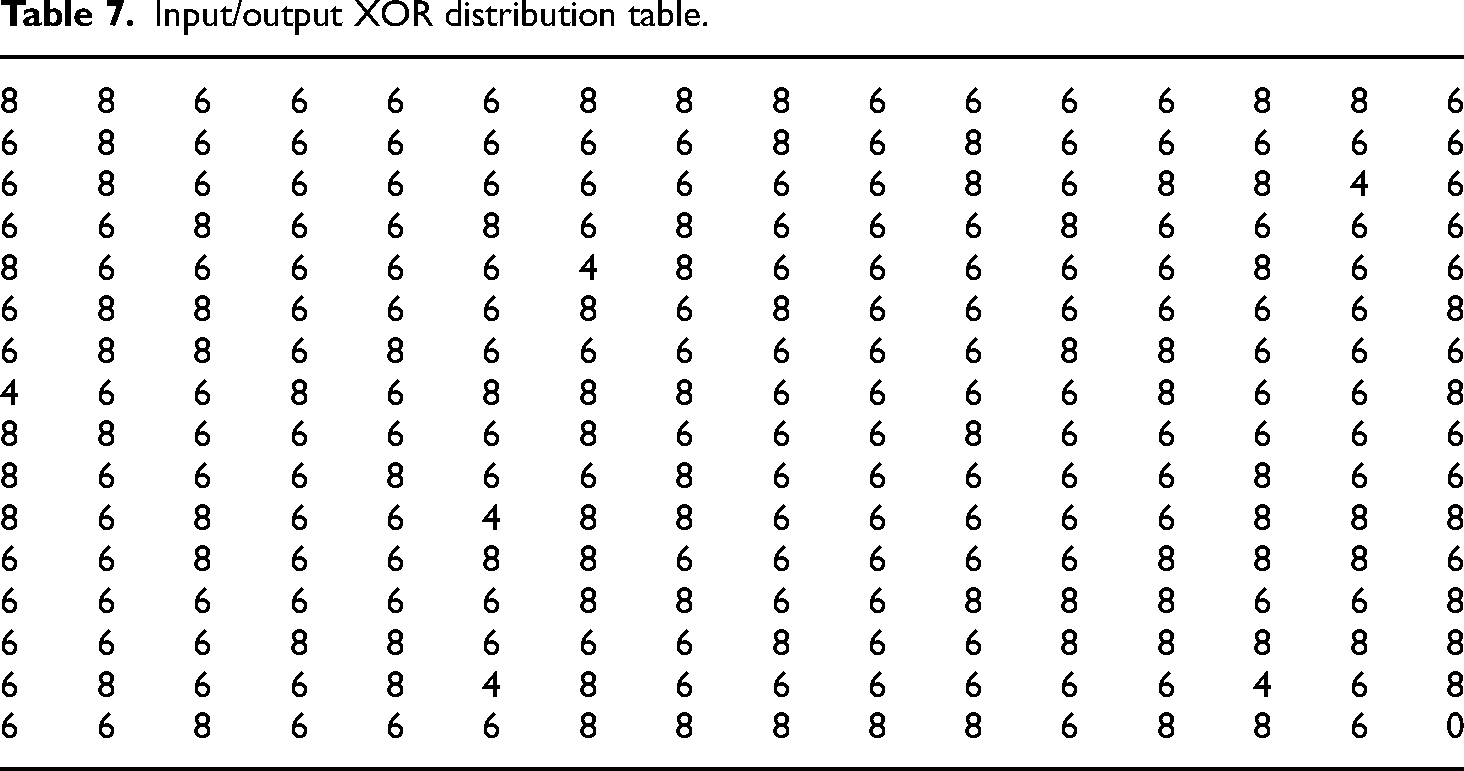
The suggested S-box is resistant to differential attacks since the anticipated S-box’s DP is 0.03137. Table 8 offers the differential approach table for the suggested S-box and the DP for different S-boxes. These tables corroborate the claim that the proposed S-box outperforms several other options
A comparison of BIC-NL, BIC-SAC, SAC and DP values of S-boxes.

Majority logic criterion
It is helpful to assess an S-box’s eligibility for usage in an encryption process by applying the majority logic criteria (MLC). Five analyses are used to determine the degree of randomness in the encoded picture: energy, entropy, homogeneity, contrast, and correlation.
The characteristics of the encoded image are recognized through the use of homogeneity and energy. The degree of similarity between the host and encrypted image is evaluated by the correlation test. A lower correlation coefficient suggests that encryption is causing more distortion. The plaintext image’s decreasing brightness is evaluated using contrast. The encryption process is more effective the higher the contrast value. The plaintext is distorted during the encryption process, and statistical characteristics describe the S-box’s resilience.
This S-box is then used to encrypt digital photos. To conduct MLC, four
The proposed S-box is employed in two substitution steps in the encryption process. Two phases are involved in the S-box replacement process to achieve encryption. During the first stage, the substitution is done backward after moving forward from the starting pixel to the last pixel. Every simulation was executed using MATLAB programming. The original and encrypted photographs are shown in Figure 5. The matched undistorted photographs and the distorted images differ significantly. There is a great deal of visual content, but there isn’t any structure that would induce security lapses from the host image. The results of every MLC test that was done are displayed in Table 9. The correlation coefficients for images that were calculated are shown in Table 9.
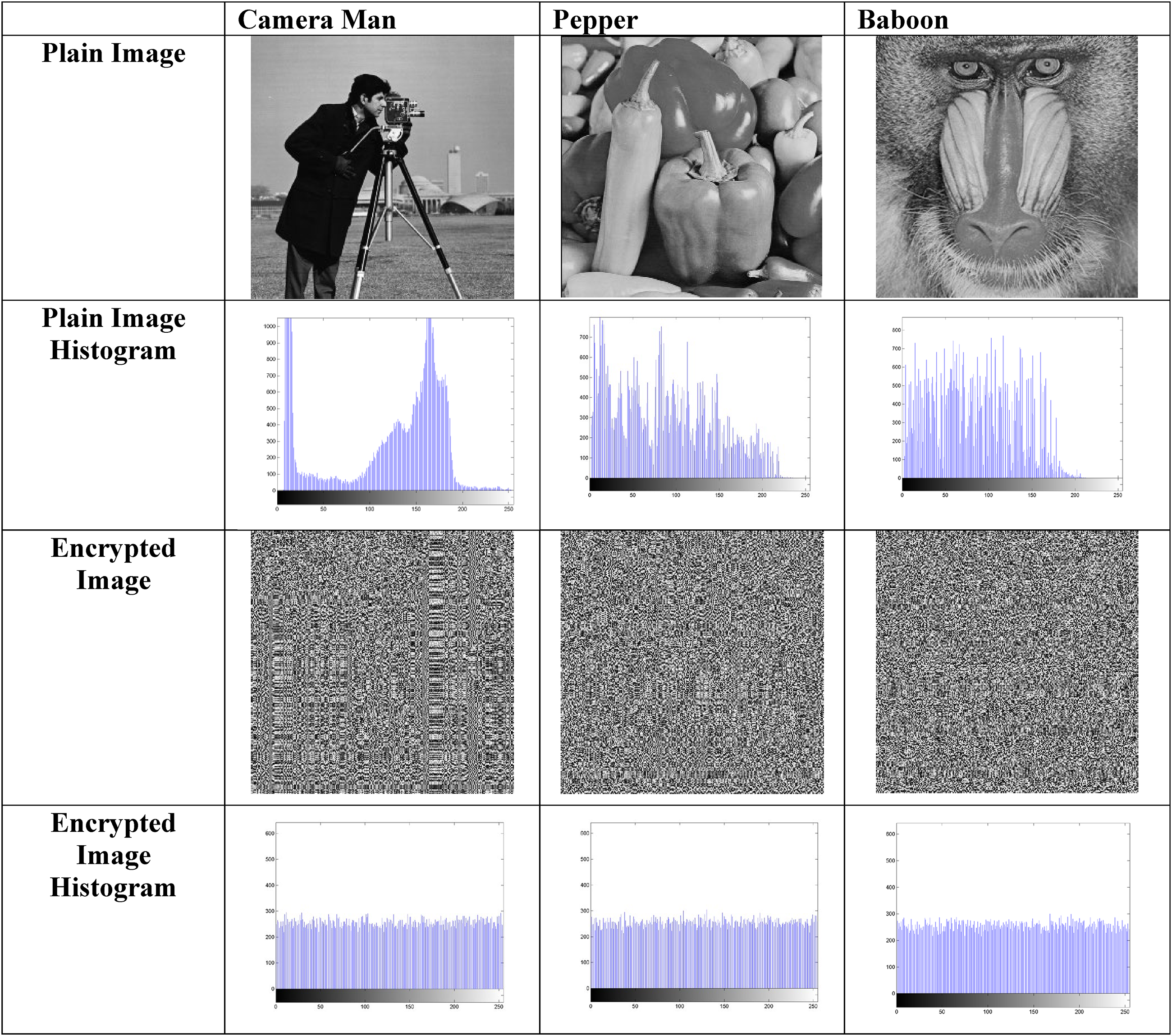
Image encryption.
Comparison table with different s-boxes image encryption results.

The findings show that the created replacement box is suitable for encryption and sufficient for use in systems meant to ensure the dependability and security of sensitive data.
Peak signal-to-noise ratio
A metric called PSNR (peak signal-to-noise ratio) is used to compare the quality of an original image or video to one that has been rebuilt or compressed. Higher values denote higher quality. It is commonly used in image processing to assess the integrity of compressed images. Decibels (dB) are used to express the PSNR.
Formula:
MAX is the maximum possible pixel value of the image (typically 255 for 8-bit images).
MSE (mean squared error) is the average squared difference between pixel values of the original and compressed image.
Results:
Cameraman Image (PSNR = 8.35 dB):
This PSNR value suggests the quality of the compressed or reconstructed image is quite poor, with noticeable differences compared to the original image. A PSNR of 7.94 dB is even lower, implying that the paper image reconstruction or compression resulted in heavy loss of information or increased noise. Similarly, a PSNR of 8.30 dB for the baboon image also indicates significant distortion or noise in the processed image.
Paper Image (PSNR = 7.94 dB):
Baboon Image (PSNR = 8.30 dB):
Requirements for performing image encryption
Hardware Configuration:
Intel i5, 4th Generation PC includes RAM size 12 GB and ROM size 128 GB SSD.
Software Configuration:
Windows 10.
Specify the version of MATLAB R2007b and some results found through Python Programs.
Benchmark Image Datasets:
Only one image in each dataset and their characteristics (e.g.
Conclusion
This work has focused on the development of a symmetric permutation approach for constructing S-boxes, leveraging the least spanning tree of the Cycle graph over a finite field of order 257. A key challenge in cryptography is improving the strength and efficiency of S-boxes, which are critical for secure encryption. By introducing an asymmetric permutation applied to the initial S-box, we address this issue and significantly enhance the performance and durability of the S-box, ensuring a more robust encryption process. The proposed method outperforms advanced S-box construction algorithms, achieving better results in terms of mean nonlinearity score, LP, SAC, and BIC scores. Evaluation of the S-box on specific plaintext images demonstrates its superior performance in secure encryption. The integration of symmetric permutation and minimum spanning tree significantly improves the encryption process by creating stronger, more efficient S-boxes. The comparative analysis confirms that the new S-box design excels in resisting cryptographic attacks through improved statistical measures. While the method shows promising results for certain types of plaintext images, its performance on other image types and larger datasets requires further exploration. The current study is limited to the application of the proposed S-box in specific encryption scenarios, lacking extensive real-world testing.
Footnotes
Future Work
Further research will explore the integration of chaotic systems with symmetric permutations to construct even more robust S-boxes. We also aim to evaluate the application of the proposed S-box design in broader contexts, including cloud encryption, to enhance data security in modern network environments.
Authors’ contributions
Muhammad Waheed Rasheed and Kiran Shahzadi contributed to conceptualization. Muhammad Waheed Rasheed and Muhammad Bilal contributed to methodology. Abid Mahboob contributed to investigation. Muhammad Bilal and Kiran Shahzadi contributed to writing–original draft preparation. Muhammad Waheed Rasheed contributed to writing–review and editing. Abid Mahboob contributed to supervision. All authors have read and agreed to the published version of the article.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
