Abstract
This paper proposes a novel exponential hyper–chaotic system with complex dynamic behaviors. It also analyzes the chaotic attractor, bifurcation diagram, equilibrium points, Poincare map, Kaplan–Yorke dimension, and Lyapunov exponent behaviors. A fast terminal sliding mode control scheme is then designed to ensure the fast synchronization and stability of the new exponential hyper–chaotic system. Stability analysis was performed using the Lyapunov stability theory. One of the main features of the proposed controller is the finite time stability of the terminal sliding surface designed with high–order power function of error and derivative of error. The approach was implemented for image cryptosystem. Color image encryption was carried out to confirm the performance of the new hyper–chaotic system. For image encryption, the DNA encryption-based RGB algorithm was used. Performance assessment of the proposed approach confirmed the ability of the proposed hyper–chaotic system to increase the security of image encryption.
Keywords
Introduction
Nowadays, we are in a brilliant era of digital communication, where millions of digital images are transmitted and stored on the internet. Digital images play an important role in multimedia images and is widely applied in military, political, commercial, medical, and other fields, which have high confidentiality requirements. Meanwhile, information security becomes a factor that cannot be ignored. It is imperative that the security of digital images with tremendous quantities of information should be guaranteed by reliable techniques. One way to increase data and image communication, is through robust control 1 and encryption using chaotic functions.2,3
Chaotic systems have various characteristics such as highly perceptive of initial state, pseudo randomness, and unpredictability. 4 Two key features of these systems are their uncertainties in the system parameters, and extreme sensitivity to very small changes in their initial conditions. Chaotic programs and methods of analysis were developed over the years. Given that chaotic systems are unpredictable, this key feature can be used in many fields such as: image encryption,5,6 robotic, 7 biological networks, 8 neuroscience, 9 secure communication 10 and information processing. 11 The research on chaotic systems has achieved considerable progress. Many new 3D chaotic systems were adopted, among them the Chen and Ueta, 12 Lü and Chen, 13 and Qi et al. 14 systems, which are generic. This is due to the fact that they are simple in structure and have only one Lyapunov exponent, these chaotic systems have faults of feeble security which make them easily cracked. An important difference between chaotic and hyper–chaotic systems is the fact that high–order hyper–chaotic systems have more complex behavior and higher volatility.15,16 The design of high–order chaotic and hyper–chaotic systems along with the analysis of their intrinsic properties and the stability analysis of these systems are among the studies that have been conducted in this field.17–21 Dong et al. 22 a high–volatility 4D hyper–chaotic system was introduced. The various states of the system were then analyzed with respect to changes in the system’s equilibrium points. It was confirmed that the more sensitive the system is to the change in the initial conditions, the higher the oscillations. In recent years, many hyper–chaotic systems have been built using various functions, including exponential function, sign function, and trigonometric function.23–26 The common features of all these designed systems, compared to conventional hyper–chaotic systems, are their greater fluctuation and their sensitivity to the initial conditions.27–29 A four-wing hidden attractor chaotic system, which only has one stable node-focus equilibrium point was reported Deng et al. 30 The new system can generate a hidden attractor with one-wing and hidden attractors with quasi-periodic and periodic coexistence. In addition, by adjusting the parameters of the new system, a self-excited attractor with one wing, is created. The hidden attractions of the new system are confirmed by the cross section of the adsorption basins and the hidden behavior is analyzed by selecting different initial states. The dynamic properties of the new system have been proven by the Lyapunov exponents spectrum, bifurcation diagram and Poincare map. Finally, the novel hidden attractor system with four-wings and one-wing has been implemented by electronic circuits. The obtained results showed that the new system has a complex structure and a good performance.
To create a hyper–chaotic system, it is necessary to increase the system dimension, however, this may lead to instability. In a chaotic secure communication system, to ensure secure message transmission, similar systems must be used on both sides of the master and the slave. In order to have a complete and successful transmission, chaotic systems in the master–slave must be synchronized. Dynamic synchronization of these systems, is a very important phenomenon, 31 which has been displayed in many scientific structures. 32 The synchronization of chaotic system’s is a major control approach that has been considered for many years. For synchronization, an appropriate control technique is employed to move the systems of the master to the slave. In recent years, several controllers have been utilized to synchronize hyper–chaotic systems.33–37 Since time plays a key role in the transmission of information, ensuring a transmission with the fastest time possible is crucial. Among existing methods, the sliding–mode control (SMC) has special features such as: robustness to parametric uncertainties, simple implementation, suitable transient response, reduced order of the system, reduced sensitivity to bounded disturbances and computational simplicity. 38
Over several years much research has been devoted to the development and application of SMC design.39–42 Although SMC is very popular and efficient, this method suffers from a major drawback; the chattering phenomena. In practice, chattering is a very undesirable phenomenon because it can increase energy consumption, cause mechanical wear in systems and actuators and deteriorate controller performance. Hence, in designing the controller we will have two objectives, eliminating the chattering phenomena and controlling the function as quickly as possible. A lot of research has been done to solve these problems. For instance, a new chattering–free sliding mode control technique with both–differential and integral operators was proposed Li et al. 43 for the synchronization and control of nonlinear perturbed systems with unknown parameters. A new PID sliding mode control was synthesized Mobayen 44 to eliminate the chattering phenomena and achieve high accuracy in the presence of system disturbances.
In recent years, we have witnessed the emergence of new powerful controllers with the ability to limit time and eliminate deleterious effects on the system.45,46 The new controllers were developed for the secure communication of two various chaotic systems with unknown parameters, external disturbances and systemic uncertainty, by combining adaptive back–stepping in a finite–time and terminal sliding mode control (TSMC). Compared with the traditional sliding-mode control, the TSMC introduces a nonlinear term in the sliding surface function to improve the system’s convergence characteristics, to ensure the convergence of the system states to a given trajectory in finite time. Thus, among the advantages of TSMC are its fast dynamic response, finite-time convergence, and high steady-state tracking accuracy. 47 However, some engineering problems are expected to reach synchronization within a finite–time. The finite–time synchronization has many advantages, such as optimality of the convergence time, disturbance rejection properties and improved robustness. Generally, the synchronization refers to the tendency of the states of all coupled dynamical systems to converge to a common behavior as time evolves.
Decoding for an unauthorized receiver without knowing the initial conditions and dynamics of a hard–working system is difficult. One way to increase security in chaos communications and image transmission, is by using high–order dimensional dynamics. This is due to the fact that high–order dynamic regeneration and discovery of messages for unauthorized recipients using difficult timescale reduction methods are difficult.48–50 Other ways to enhance security in chaotic secure communications include pointing out the complexity of the system’s dynamics, because the more complex the structure of the system and the higher the number of its more parameters, the more difficult the decoding of the system. The design of high–order chaotic and hyper–chaotic systems as well as the analysis of their intrinsic properties and the stability analysis of these systems constitute some of the studies that have been conducted in this field.17–20
Images are one of the most important carriers of information that are abundantly stored and distributed in various structures. Because most networks are open, image encryption can be an effective method. Using hyper–chaotic systems to encrypt images can increase network security and make decryption difficult.51,52 There are many ways to encrypt an image, such as: Advanced Encryption Standard, 53 Data Encryption Standard 54 and International Data Encryption Algorithm. 55 Due to the large size of the images and the strong correlation in the images, these methods usually will not be effective.56,57 Almost all of the chaotic and hyper–chaotic image encryption algorithms, are based on changes in the values and position of the pixels.58–61
Nowadays, DNA computing has permeated the domain of cryptography. DNA cryptogram utilizes DNA as information carrier and takes advantage of biological technology to achieve encryption.62,63 Kang et al. had proposed a character encryption algorithm based on pseudo DNA operation, 64 it made use of central dogma which belongs to molecular biology to implement encryption. Wang et al. 65 introduces a new DNA-based hyper-chaotic encryption algorithm that has features such as high sensitivity, large key space, and resist differential attacks. The proposed algorithm was able to reduce the time complexity and the space complexity of the permutation while achieving good permutation effects. However, DNA encryption methods have disadvantages such as expensive experimental equipment, complex operation and difficult to grasp its biotechnology, and still cannot be efficiently applied in encryption field.66,67 To overcome the disadvantages of this method, RGB encoding68,69 based on DNA encryption can be used. In this method, DNA encoding is first performed to encrypt RGB. Then three images are received after decryption. Finally, RGB components that use Logistic chaotic images recover images. 70 The main contributions of this paper are as follows:
Proposing a novel exponential four–dimensional hyper–chaotic system and analyzing its inherent properties.
Designing a new FTSMC-based controller for the fast synchronization of two different exponential hyper–chaotic systems.
Performing color image encryption using the novel exponential hyper–chaotic system.
The remainder of the paper is organized as follows. Section 2 provides the dynamical model of the high–complexity hyper–chaotic system, displays its features and formulates the finite–time synchronization problem. Section 3 presents the design and proof of the terminal sliding–mode controller for finite–time synchronization. Section 4 discusses the implementation of the proposed chaotic system to images’ cryptosystem. In section 5, synchronization and image encryption issues are discussed using the new high–complexity hyper–chaotic system and a numerical simulation is performed to validate the methods. Some concluding remarks are finally provided in section 6.
Problem description and preliminaries
Model of the hyper–chaotic system
The dynamics of the new four–dimensional system is described as:

where

Basic properties and dynamic behaviors of the hyper–chaotic system
This section presents the natural properties of the new exponential hyper–chaotic system such as chaotic attractor’s, equilibrium point’s, Kaplan–Yorke dimension, Eigen values, Lyapunov exponents, Poincare map and Bifurcation diagram.
Analysis of equilibrium points and eigenvalues
By setting the differential equations in (1) to zero, the equilibrium points are equal to:
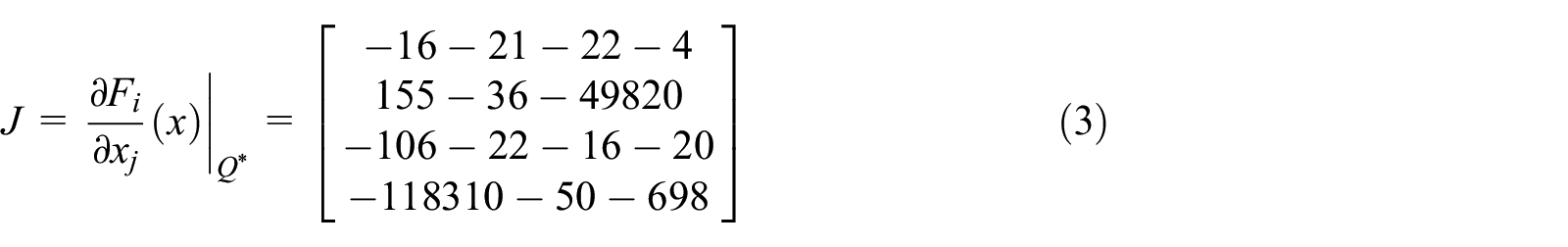
According to (3), the system eigenvalues are found as follows:

According to equation (4), the eigenvalues are
Chaotic attractors analysis
In hyper–chaotic systems, the phase portraits of the system start from one point and fluctuate within a certain range. Figures 1 and 2 depict the phase portrait diagrams of system (1) in 2–D and 3–D modes.

2–D phase portrait diagrams of the system (1) in: (a)

3–D phase portrait diagrams of the system (1) in: (a)
According to Figures 1 and 2, the system’s trajectories oscillate around their modes and the signal has a quasi–random behavior.
Lyapunov exponents and Kaplan-York
The divergence and convergence of the states of a nonlinear system, are determined by its LES representation. If LEs are positive, it indicates the chaotic behavior of the system.72,73 A system is hyper–chaotic if there are two or more positive LEs. The LEs using Wolf et al.
72
method of the exponential hyper–chaotic system (1) with different initial conditions

which is fractional.
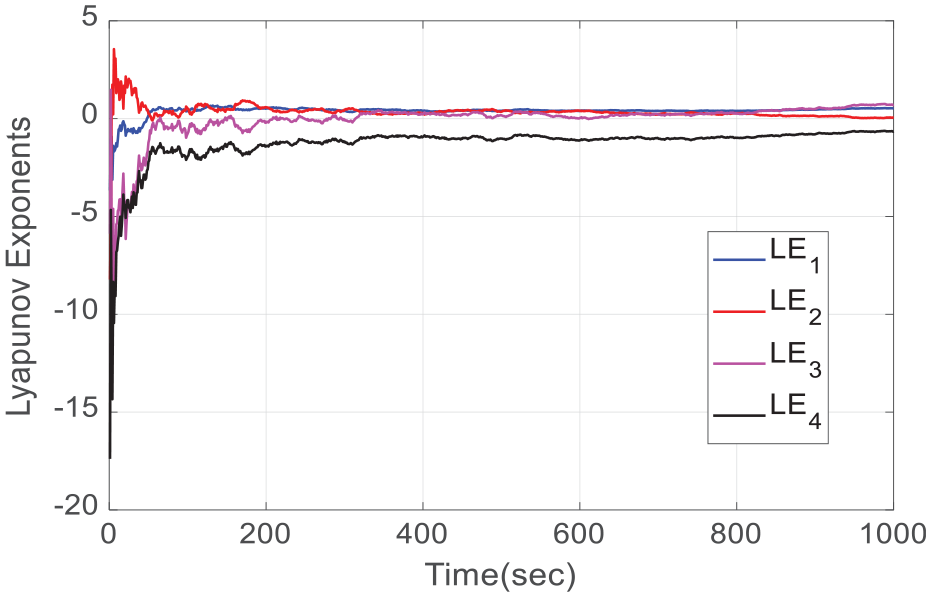
Dynamics of LEs of the novel hyper-chaotic system (1).

LEs spectrum of the system (1) in: (a) LE1, LE2 and (b) LE3, LE4.
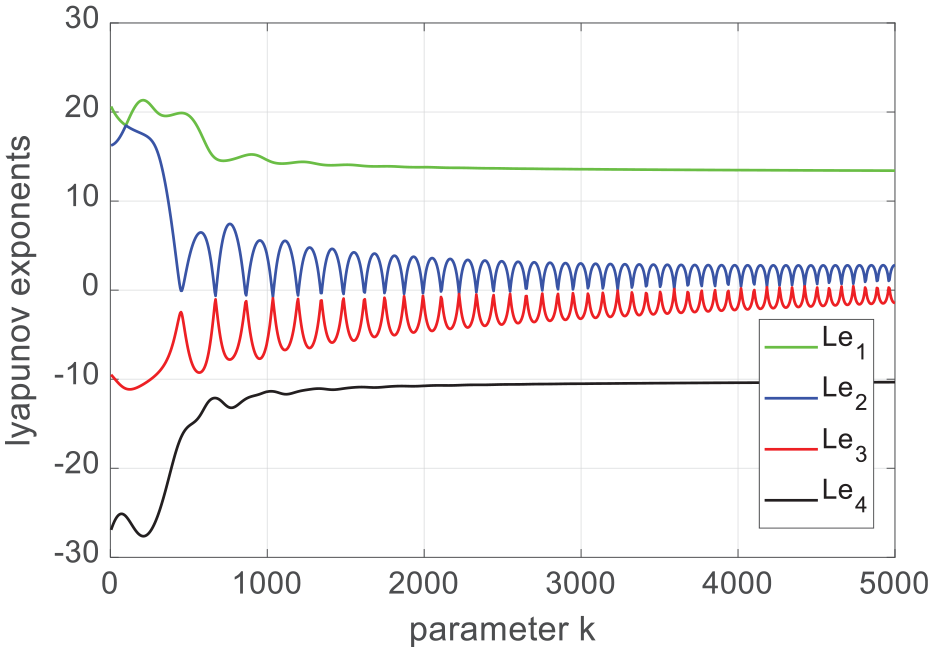
Lyapunov exponents of the system (1) with
Table 1 numerically compares the maximum Kaplan–Yorke dimensions with a number of similar complex 4D hyper–chaotic systems (systems that have the following functions: exponential, logarithmic, trigonometric, and hyperbolic) and System (1) to determine the best system performance.
The maximum Kaplan–Yorke of similar complex hyper–chaotic systems.

According to the results depicted in Table 1, the Kaplan–Yorke dimensions of the exponential hyper–chaotic system (1), are larger than similar systems.
Bifurcation diagram analysis
To investigate the dependence of the parameters of the new exponential hyper–chaotic system (1), we need to draw and analyze the bifurcation diagram. In Figures 6 and 7. bifurcation diagram’s of the system (1) is plotted. The system enters into chaotic oscillations with routine period doubling. Bifurcation diagrams display the behavior of a system with respect to changes in the system parameter and explains the system’s absorbent behavior.83,84
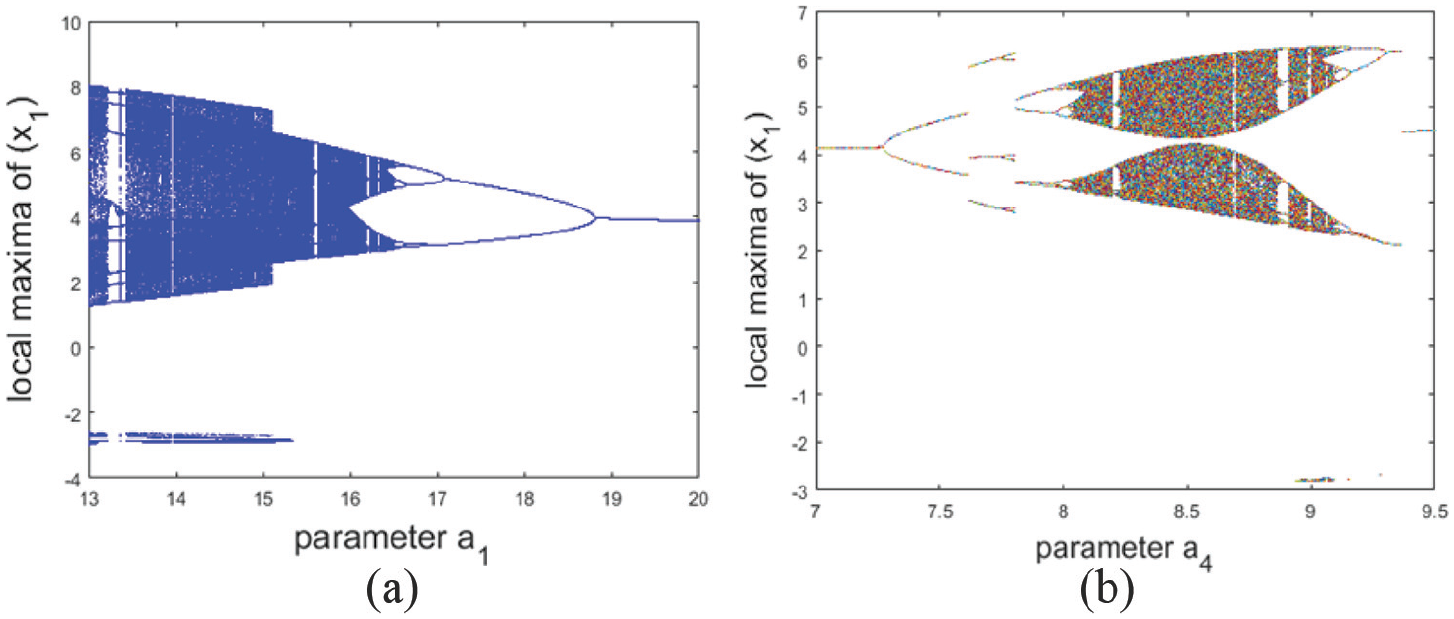
Bifurcation diagrams of the system (1) in: (a)

Bifurcation diagrams of the system (1) in: (a)
Poincare map analysis
As an interesting method, we used the Poincare map to describe the folding attributes of the chaotic system. To study the performance and behavior of continuous dynamical systems, similar to the designed system (1), we can use the Poincare map, one of the common and popular topics in nonlinear dynamic analysis. Figure 8(a) and (b) display the Poincare maps of system (1). According to Figure 8(a) and (b) the regular set of points depicted in the Poincare maps is an indication of the system’s chaotic behavior.

Poincare map of the system (1) in: (a)
Parametric analysis
One of the effective parameters in system (1) is parameter

Bifurcation diagram in

We can conclude from Figures 9 and 10, that the more the system becomes more chaotic, the more its attractors converge to their equilibrium points. Also, Figure 11 displays 1–D and 3–D behaviors, and Figure 12 shows the Poincare map and 2–D behaviors of the hyper–chaotic system with changes in the

Phase portrait trajectories (up panel) and time series (down panel) showing routes in the System (1) for varying

2–D trajectories (up panel) and Poincare map (down panel) showing routes in the System (1) for varying
Hence, by increasing the value of the parameter from
Problem formulation of finite–time fast synchronization
In this section, synchronization and its theorems are presented between two new and overly hyper–chaotic systems with indefinite parameter’s and uncertain disturbance’s. At this point, we use the system represented by equation (1) and modify the initial conditions and parameters for both the master–slave systems for fast synchronization. Consider the hyper–chaotic system that refers to the master system

The basic parameters and initial conditions of the master system (6) are defined as follows:

where

where
where

where

where

and

with the settling time


for all times

Main results of fast synchronization
Consider the dynamical model as:

where

where
In order to satisfy

where

where

Then, the states of the dynamical system (17) move to the sliding surface (18) in finite–time and remain on it.

From (19), the time–derivative of the fast terminal sliding surface is found as:

where using (17) and (18), we have:

Differentiating the Lyapunov function (22) and using (24) yields:

where substituting (20) into (25), yields:

Using (21) and (26), we can write:

where
Application in images’ cryptosystem
In this section, the proposed 4D hyper–chaotic system (1) is implemented to an image cryptosystem. Without loss of generality, an 8–bit RGB color image of size
Image encryption and decryption
One of the newest and most successful methods of chaos encryption is DNA–based encryption. The development of DNA encryption is due to the advancement of DNA computing.
89
In genetics, each DNA contains four basic types: Cytosine–Guanine–Adenine–Thymine (C–G–A–T). According to the DNA algorithm, the coding corresponds to four nucleus (A–G–C–T) bases using four digits (0,0), (0,1), (1,0), (1,1). So, there are
DNA encryption and decryption algorithm.

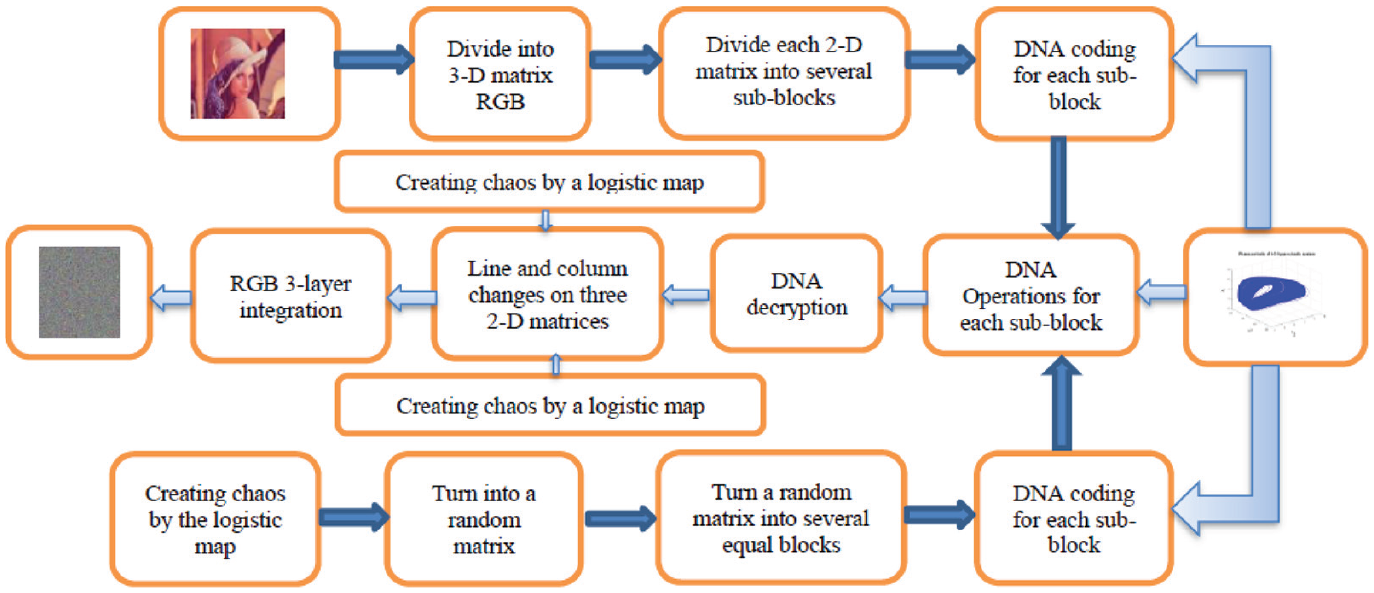
DNA color image encryption flowchart using hyper–chaotic system (1).
Details on the encryption and decryption process are described as follows:
(1) The digital image is divided into three two

(2) Dividing RGB into sub–matrices and converting the analyzed matrices into binary matrices under:

(3) Create

(4) Set the trail length on

where,
(5) Convert

where the value of
(6) Since 4 algorithms are used for DNA, the

where the
(7) The original image can be recovered by applying a reverse operation in the encryption process.
Simulation results
Simulation results of fast synchronization
In this section, we perform a fast synchronization between two four–dimensional hyper–chaotic systems with unknown disturbances and parametric uncertainty to the system. Here, we used both the System (6) and System (8) for the synchronization. Figure 14 display the amazing hyper–chaotic attractors of the master (6) and slave (8) systems with initial conditions and parameters (7) and (9).

Hyper–chaotic time series of the master–slave systems (6) and (8).
According to Assumption 2, disturbances have been applied to the slave system (8). It is worth noting that although the systems (6) and (8) are the same, for their simulation during synchronization, we considered unequal parameters and different initial conditions. According to Figure 14, all the modes of the master–slave systems behave differently. Based on Assumption 1, to study chaos synchronization, the error according to systems (6) and (8), can be computed as follows:

where

The systems (34) and (35) can be represented in matrix form as follows:

where
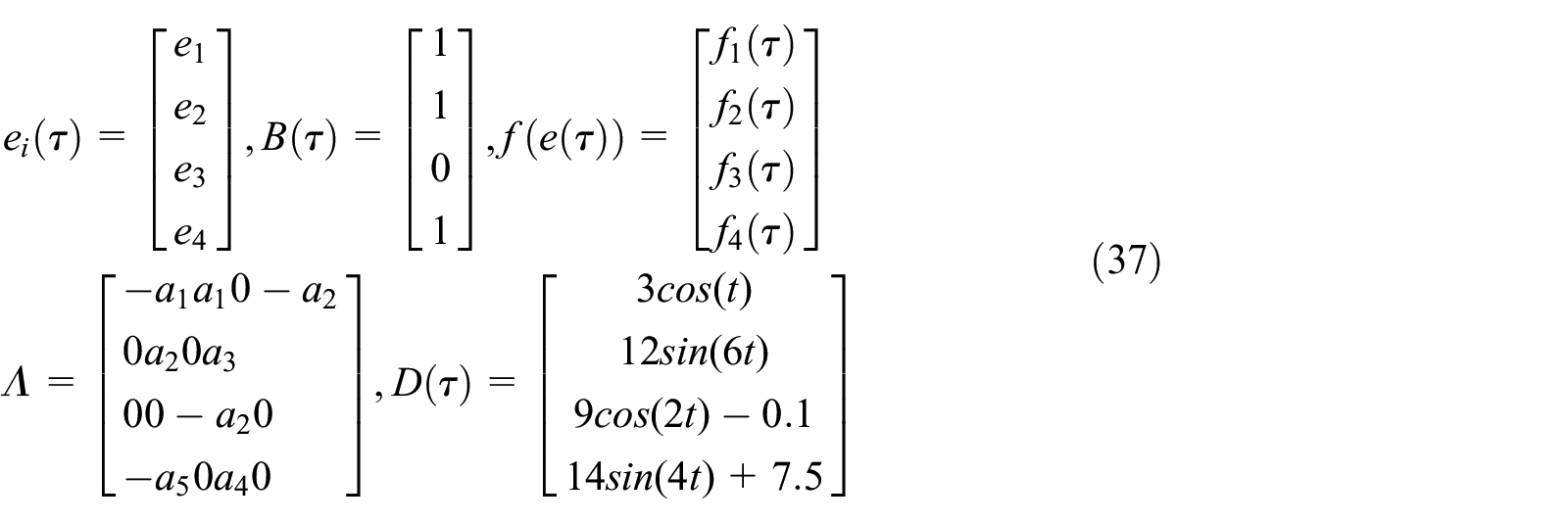
Then, based on Theorem 1, we trust that the fast synchronization between system (6) and system (8) with error equation (36), will be achieved in finite–time. In the TSMC design, we use the controller defined in (20). According to the SMC law, gains are selected as:

The functions

Synchronization between master-slave systems.
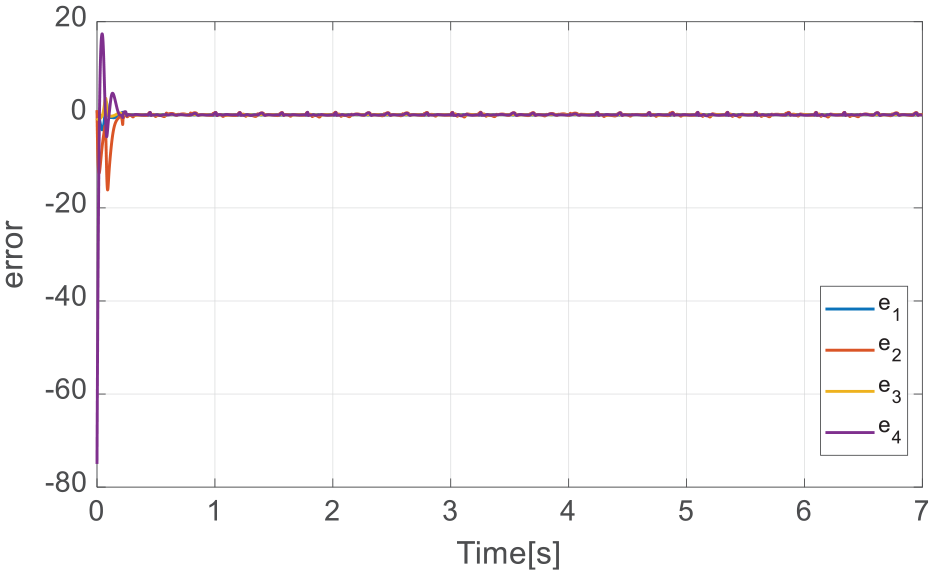
The errors of fast synchronization with the controller.
According to the simulation results (see Figures 15 and 16), despite the fact that we proved that the exponential hyper–chaotic system (1) has a lot of fluctuations, the controller (20) was able to reduce the error to zero in
In what follows, to further assess the performance of the control approach, we compare its performance to the observer-based composite adaptive terminal sliding-mode approach proposed Liu et al. 1 Figure 17 displays the output of the system using the controller (20) compared to the outputs of the reference model and method Liu et al. 1 The time response of the tracking errors are shown in Figure 18. From Figure 18, it is demonstrated that the tracking error signal appropriately converges to the origin and provides faster tracking performance than method. 1
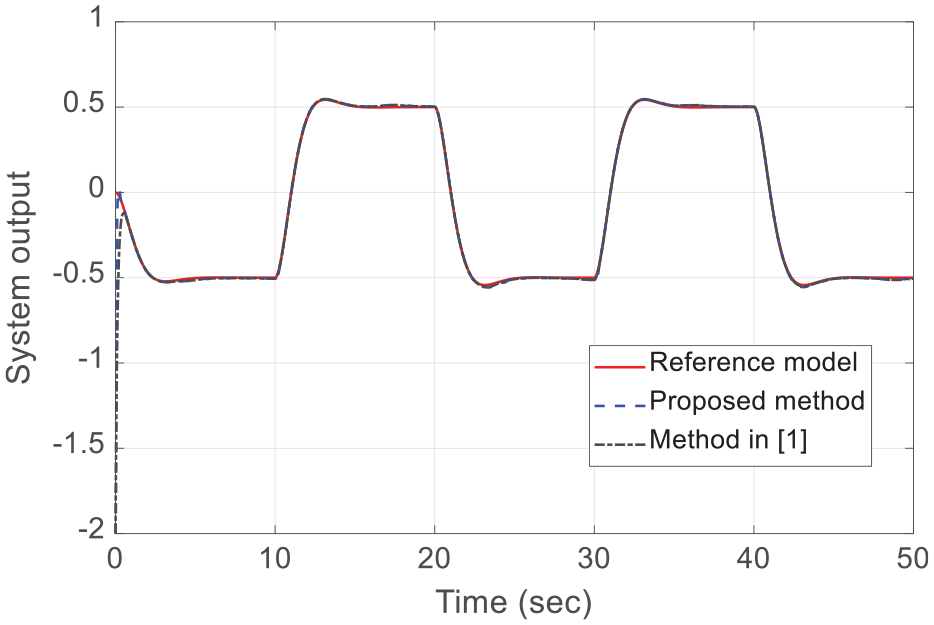
Outputs of the system.
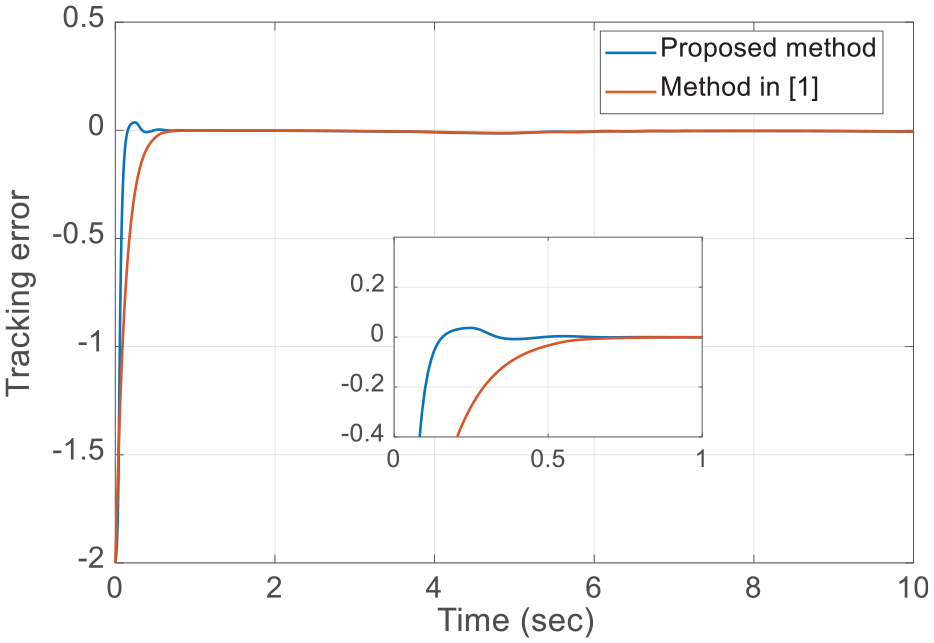
Tracking error.
Results of images’ encryption
In this subsection, the usefulness of the application of the proposed scheme for image encryption is validated using numerical simulations. “Lena” image in PNG format are used in this simulation as the original data which must be encrypted (see Figure 19(a)). The encryption keys are generated by the encryptor hyper–chaotic system. By applying these chaotic keys and the encryption method described in Subsection 4.1, the original image is encrypted. Figure 19 shows the obtained encrypted image. At the decryptor, the exponential hyper–chaotic system is used to generate the decryption keys. The decrypted “Lena” image can be obtained after the synchronization procedure and the above-mentioned decryption process (see Figure 19(c)). From these figures, it can be observed that the encrypted image have a uniform distribution, and the encrypted image are similar to the noise. It is demonstrated that in terms of visual impression, the suggested method has a good encryption performance.

Original (a), encrypted (b), and decrypted (c) images for Lena image.
Performance analysis of the proposed cryptosystem
Security analysis is performed to analyze the robustness and demonstrate the efficiency of the proposed method. In order to show the efficiency of hyper–chaotic cryptography, key space analysis, histogram analysis and correlation test have been used.
Key space analysis
The key–space size for a cryptosystem is based on the total number of various keys that are utilized in the encryption. A successful cryptosystem should possess a key space which is great enough to resist all kinds of brute–force attacks. These types of attacks are actually based on the exhaustive key search. In the proposed algorithm, if the eavesdroppers want to extract the original satellite image from the encrypted image, they will require the system initial conditions and the parameters of the hyper–chaotic system (equations (3) and (4)) as secret keys. All of these secret keys are considered as type double, which has 15-digit accuracy. Therefore, the key space becomes as huge as
Histogram analysis
To barricade the revelation of image information by an eavesdropper, it is useful if the encrypted image has no or very few statistical similarities to the original image. The distribution of pixel elements in an image with the color intensity of each pixel element is displayed by the image histogram. Histogram analysis is performed to detect the distribution of pixel values and uniform coding. Once this chart is uniform, we will have secure encryption. Figure 20 illustrates the histograms of the red–green–blue color channels of the original and encrypted images of the “Lena.”
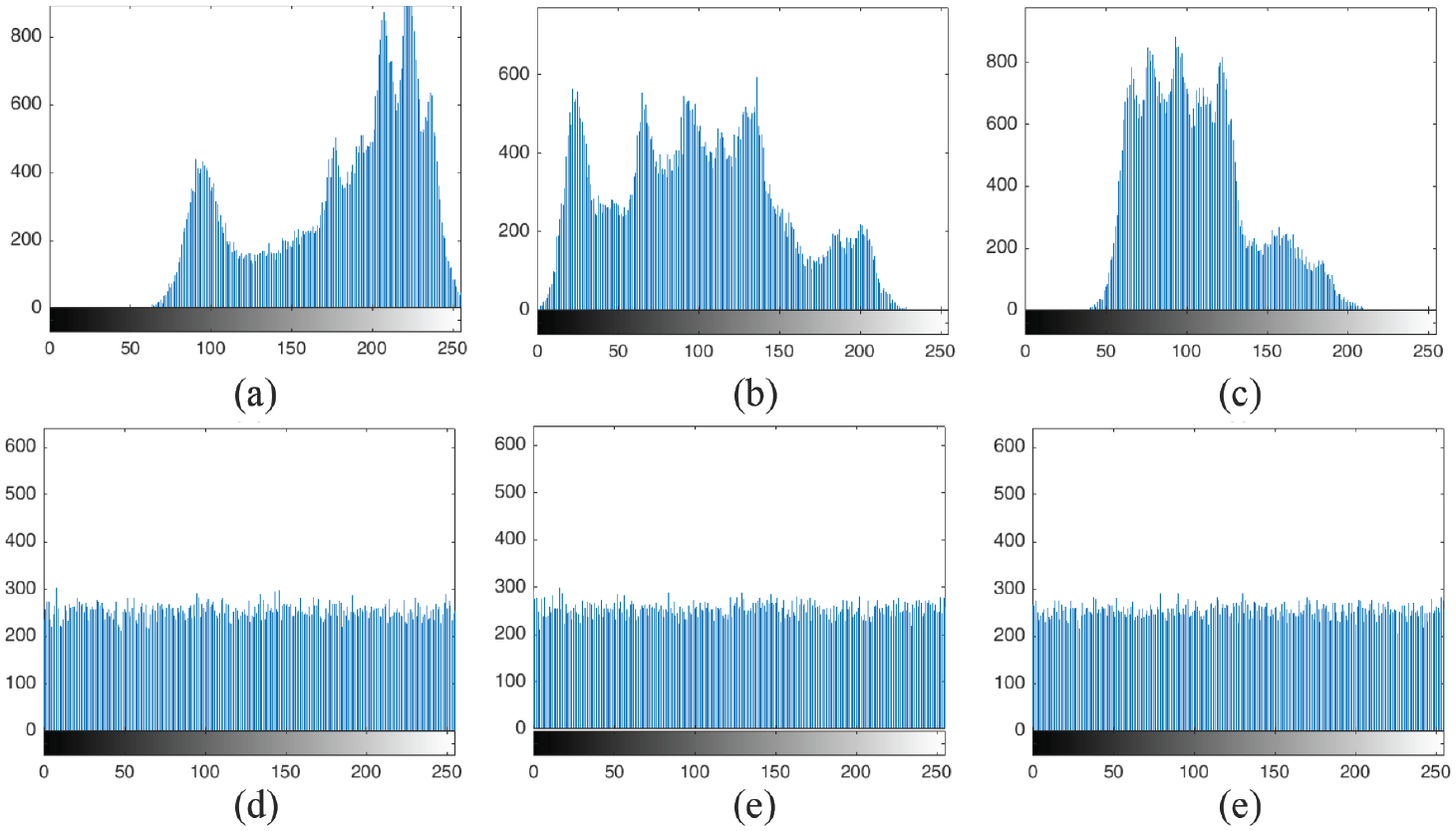
RGB color histograms of “Lena” image for: (a–c) original image and (d–f) encrypted image.
As shown in Figure 20(d–f), the dissemination of the pixels is evenly distributed, so no information about the original image can be obtained from Figure 19.
Correlation test
Another indicator in statistical analysis is the use of adjacent pixel correlation, which includes vertical–horizontal–diagonal correlation. The degree of image resistance to attack is proportional to the correlation of the location data adjacent to the pixels. Figure 21 demonstrates the correlation between the pixels in the ‘Lena’ shape. In this figure, 5000 pixel points are used.
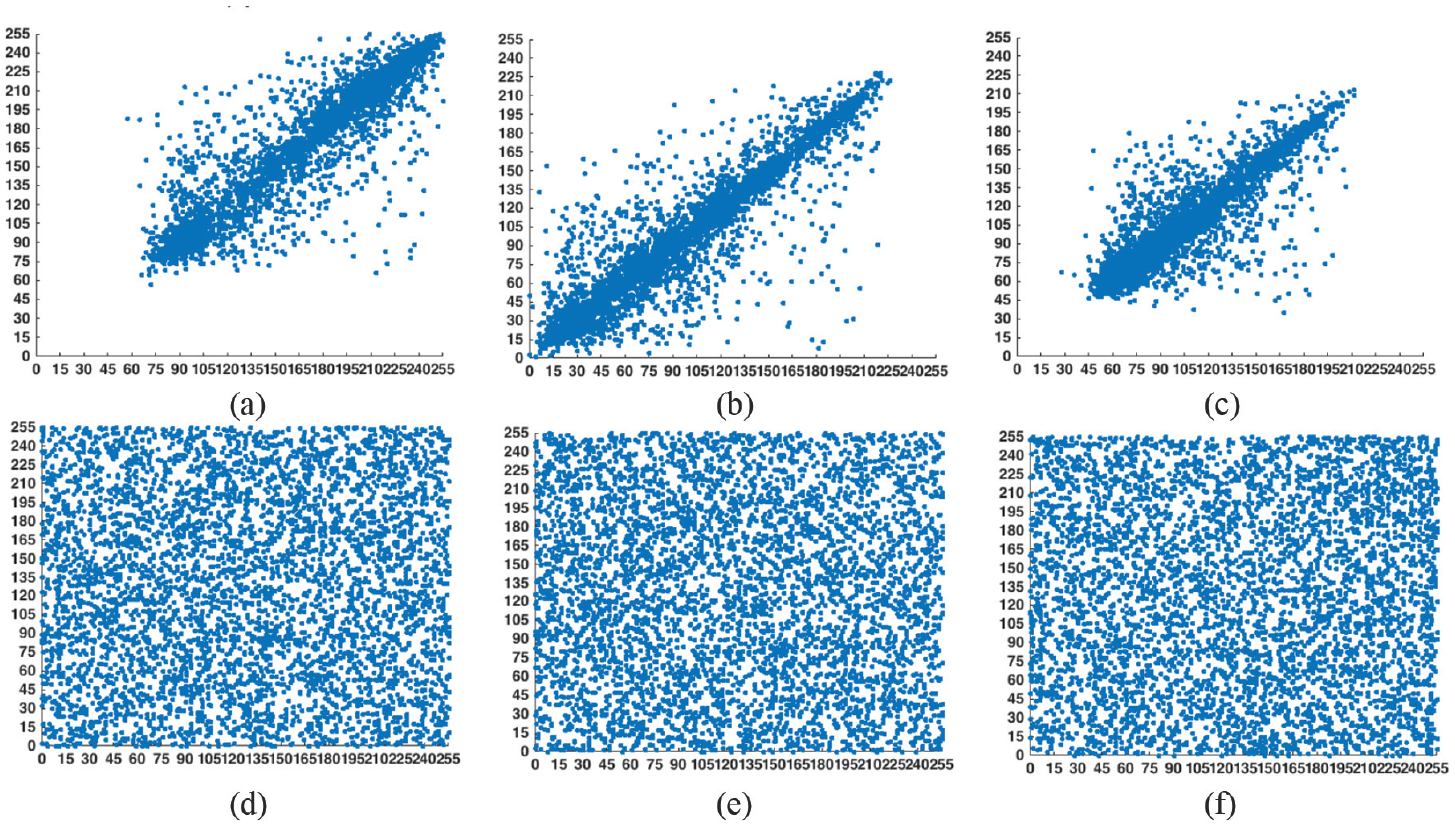
Correlation between pixels of “monkey” image for: (a–c) original image and (d–f) encrypted image.
According to Figure 21, the values of vertical–horizontal–diagonal correlation are approximately close to one, indicating a high–correlation between pixels. The correlation values of the encrypted image are close to zero, and this indicates that the values of vertical–horizontal–diagonal correlation of the channels have nothing to do with each other. Table 3 compares the vertical–horizontal–diagonal correlation of the Lena image.
Comparison between horizontal–vertical–diagonal correlation coefficient of Lena image.
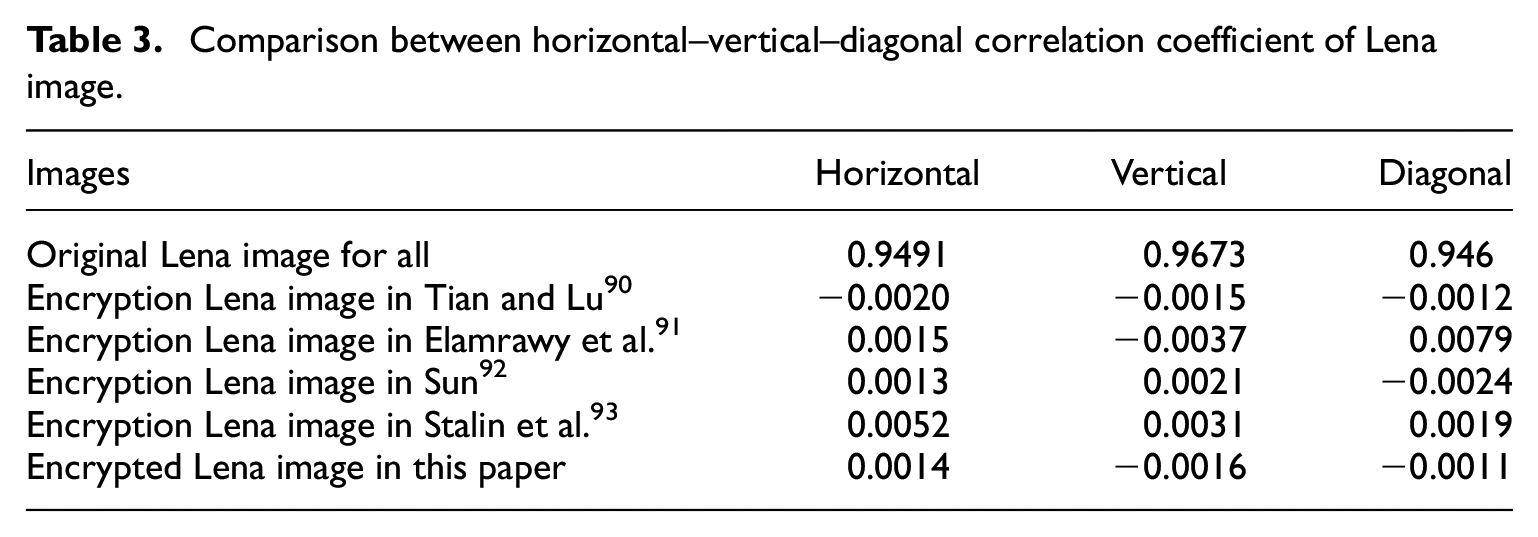
The correlation data of the pixels adjacent to Lena’s image in Table 3 after encryption in three directions are very small and this proves that the image is encrypted with a higher degree of confusion.
IE, NPCR, and UACI metrics
At last, in this subsection, the other useful metrics for image cryptosystem quality measurement such as IE, UACI, and NPCR are computed. In information entropy theory, the complexity of encrypted data is specified. We can determine complexity of the encrypted data with information entropy theory. The information entropy for an image is calculated as

where
Moreover, to measure the robustness of the encryption process in differential attacks, the NPCR and UACI values are considered. In fact, the rate of change in the result of encryption process when the difference between the original images is very small can be measured by the NPCR and UACI quantities. Suppose that

Now, the NPCR and UACI quantities are calculated as

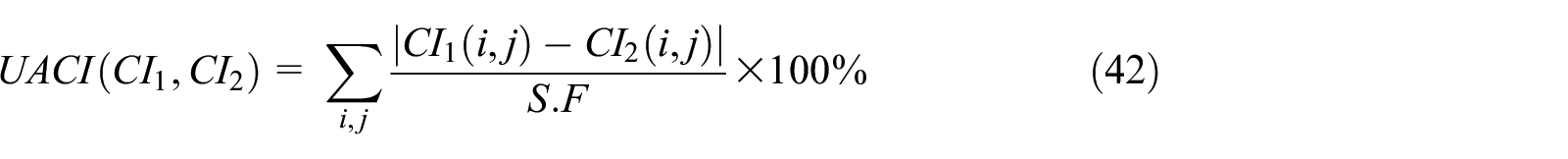
where
Conclusions
This paper proposed a novel exponential 4D hyper–chaotic system with extremely complicated dynamics and structure. It also analyzed the dynamic behaviors of the proposed using phase portraits, Lyapunov exponent, Poincare map, Kaplan–Yorke dimension and bifurcation diagram. Then it proposed a terminal sliding mode controller to stabilize the new hyper–chaotic system with uncertainty and unknown disturbances. Stability analysis was established using the Lyapunov stability theory. The controller is designed to ensure the fast synchronization between two similar proposed hyper–chaotic systems in the presence of unequal parameters, different initial conditions and matched disturbances for transfer industrial automation information. The approach was implemented for images cryptosystem. Color image encryption was also carried out to confirm the performance of the new hyper–chaotic system. For image encryption, the DNA encryption-based RGB algorithm was used. Performance assessment of the proposed approach confirmed the ability of the proposed hyper–chaotic system to increase the security of image encryption.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
