Abstract
When it comes to cybersecurity incidents – public opinion matters. But how do voters form opinions in the aftermath of cyberattacks that are shrouded in ambiguity? How do people account for the uncertainty inherent in cyberspace to forge preferences following attacks? This article seeks to answer these questions by introducing an uncertainty threshold mechanism predicting the level of attributional certainty required for the public to support economic, diplomatic or military responses following cyberattacks. Using a discrete-choice experimental design with 2025 US respondents, we find lower attributional certainty is associated with less support for retaliation, yet this mechanism is contingent on the suspected identity of the attacker and partisan identity. Diplomatic allies possess a reservoir of good will that amplifies the effect of uncertainty, while rivals are less often given the benefit of the doubt. We demonstrate that uncertainty encourages the use of cognitive schemas to overcome ambiguity, and that people fall back upon pre-existing and politically guided views about the suspected country behind an attack. If the ambiguity surrounding cyberattacks has typically been discussed as an operational and strategic concern, this article shifts the focus of attention to the human level and positions the mass public as a forgotten yet important party during cyber conflict.
Introduction
When it comes to cybersecurity incidents – public opinion matters (Shandler and Canetti, 2024). You might not know this from a review of the cyber conflict literature, where prominent debates often ignore the public. One flashpoint regards the decision whether cyberspace is a new strategic domain or in fact a continuation of intelligence contests (Brantly, 2016; Gartzke and Lindsay, 2015; Maschmeyer, 2021; Rovner, 2019). Another prominent debate questions whether cyber operations complement or substitute for military operations (Egloff and Shires, 2023; Kostyuk and Gartzke, 2022; Schneider et al., 2022). Still another conceptual dispute focuses on the (de)escalatory properties of cyber conflict (Healey and Jervis, 2020; Libicki and Tkacheva, 2020; Maschmeyer, 2023b; Valeriano and Jensen, 2022). While these crucial debates play out at strategic, operational and international levels, a forgotten actor has fallen by the wayside – the general public.
It is easy to dismiss the relevance of public opinion when it comes to cybersecurity. Intricate dynamics of international relations take place above the heads of regular voters, who have historically deferred to co-partisan elites in matters of international relations (Berinsky, 2009). Moreover, the sheer complexity of cyberspace can leave the public at a loss. Yet for all their credulity, the public maintains a crucial role surrounding cybersecurity (Shandler et al., 2023b). Widespread exposure to cyberattacks has been shown to undermine trust in government (Gross et al., 2016; Shandler and Gomez, 2023), generate support for intrusive surveillance policies at the expense of civil liberties (Arsenault et al., 2024; Snider et al., 2021), and provoke public demands for retaliatory action that can place pressure on elected officials to escalate tensions (Leal and Musgrave, 2023; Shandler et al., 2022). On top of this, mounting evidence has demonstrated decision makers are at least somewhat responsive to public attitudes toward conflict (Lin-Greenberg, 2021; Sevenans, 2021; Tomz et al., 2020). Put simply, the general public’s reactions to cyberattacks can be politically consequential.
These outcomes are not mere scholarly conjecture. In a vivid case study, Baram (2023: 13) described how an Iranian cyberattack against Israeli water infrastructure was publicly revealed by Israeli authorities in part ‘to offset the humiliation caused by the public exposure and to control the narrative surrounding the incident.’ Authorities exhibited acute sensitivity to public reactions to cyberattacks, and indeed, intense public demands for retaliatory strikes weighed upon decision makers.
But how do voters form opinions in the aftermath of cyberattacks that are customarily shrouded in ambiguity? How do people account for the extensive uncertainty inherent in cyberspace to forge political attitudes following attacks? Common sense dictates that voters should exhibit restraint in forming policy positions when the facts of an attack remain unclear. If authorities are not fully certain who is behind an attack, or whether the disruption was an attack at all, voters should logically delay adopting extreme policy positions or demanding retaliation until the full picture emerges. However, the general public is not renowned for calmly and patiently collecting full information before forming positions. Voters react to security incidents in the heat of the moment, when uncertainty is rife, and in the context of typically hyperbolic media reporting (Loewenstein and O’Donoghue, 2007).
This study therefore examines how the public grapples with uncertainty surrounding cybersecurity incidents, focusing on attributional uncertainty – a facet of uncertainty characteristic of cyberspace. We theorize that greater uncertainty about a cyber attacker’s identity will reduce the extremity of public calls for revenge – and that in the context of incomplete information, people will employ information shortcuts to form political judgments. Specifically, we assert that the effect of uncertainty depends on the suspected identity of the country in question, and the forms of available responses. With this in mind, we introduce and empirically test an uncertainty threshold mechanism that predicts and explains at what level of certainty, and under what conditions, the attributional uncertainty dilemma will restrain public demands for economic, diplomatic or military responses.
We examine this mechanism by conducting a survey experiment that exposes voters to cyberattack scenarios under various thresholds of uncertainty, before gauging the extent of demands for economic, diplomatic, or military responses. Reflecting the exaggerated language employed by media outlets, our experimental scenarios depict a rich variety of cyberattacks, ranging from minor attacks that cause no physical consequences or economic damage, to major attacks against critical infrastructure. Our primary predictor variable is the authorities’ level of certainty as to the identity of the cyber attacker. For example, once it is concluded that there is a 60% likelihood that Russia is behind an attack, what does one do with that information? What would happen if it were 70% instead? What threshold of certainty is required for people to support some retaliatory response, and what psychological and situational factors guide this decision pathway?
To probe uncertainty’s influence on a broad spectrum, we employ a ratings-based conjoint experimental design on a nationally representative sample of United States respondents (N = 2025). The data reveal that medium to low levels of certainty about who launched a malicious cyber operation dramatically reduces the likelihood the public will support even minor retaliatory options. However, the exact threshold of this uncertainty mechanism is contingent on the suspected identity of the attacker and partisan identification. Diplomatic allies of the USA enjoy a reservoir of good will that that inhibits support for retaliation provided there is any uncertainty about the identity of the attacker in the public’s mind. By contrast, retaliation against rivals is accepted in the face of far lower certainty.
Our findings emphasize the need to pay attention to a frequently overlooked stakeholder in the cyber conflict literature – the general public. Voters experience cyberattacks as enormously threatening and anxiety-provoking (Shandler et al., 2022b). When cyberattacks spill over to critical infrastructure, the public is unlikely to simply ignore the attack as acceptable sub-crisis maneuvering. To the extent the public wields at least some influence on foreign policy decisions in the aftermath of attacks, their responses cannot be disregarded. In this light, our findings reinforce the public’s role during conflict and suggests that the exaggerated public experience of cyber conflict may pressure political elites, who would otherwise be willing to dismiss many cyberattacks, toward retaliation.
A spectrum of attributional uncertainty in cyberspace
The attribution dilemma in cyberspace refers to the common assumption that cyber attackers can obscure their identity due to the underlying architecture of the internet (Boebert, 2010; Rid and Buchanan, 2015). Several factors can impede effective attribution. Technical design features of the internet itself make tracing the source of an attack challenging, particularly if adversaries employ basic obfuscation (Clark and Landau, 2011). Malicious actors might also work via arm’s length cyber mercenaries to ensure plausible deniability (Maurer, 2018). Moreover, the sheer complexity of modern cyberattacks means gleaning clues to an attacker’s identity requires extensive expertise, and the prodigious data often available can give rise to contradictory results.
Although attribution questions pervade all security crises, the dilemma is particularly idiosyncratic of cyberspace. Physical or sovereign borders cannot effectively impede cybernetic attacks, and transnational reliance on common systems underpinning digital systems allows actors to easily project force (Fischerkeller and Harknett, 2017). This issue is compounded by the proliferation of state and non-state entities capable of conducting attacks. While only a few actors have access to intercontinental missiles, for example, the same cannot be said for computer code.
However, the perceived complexity of attributing cyberattacks has steadily eroded during the last decade. Rid and Buchanan (2015) argued that even without irrefutable technical evidence, states can match a cyber offender to an offence by combining tactical, operational and strategic analyses. Even if the pool of potential attackers is vast, cross-referencing those with capability and geo-political interest in waging an attack can assist attribution (Blagden, 2020; Rid and Buchanan, 2015). In fact, successfully identifying the parties responsible for cyberattacks is more common than people think (Boebert, 2010; Lupovici, 2016) – especially for the highest-profile attacks, where private cybersecurity companies supplement state analyses (Egloff, 2020b). While identifying the group or authority ultimately responsible for an attack remains a challenge, it is often solvable with enough time, expertise and will (Lin, 2016).
As sensationalist proclamations of inscrutable hackers have given way to more nuanced understandings of attributional processes, we have learned to avoid simplistic conceptualizations on an artificially binary scale. The ‘process of attribution is not binary, but measured in uneven degrees, it is not black-and-white, yes-or-no, but appears in shades’ (Rid and Buchanan, 2015: 7). This difficulty associated with attribution is not unique to cyberspace. Technical evidence is usually not sufficient to assign responsibility in other domains of international conflict, which are similarly fraught with an interplay of material evidence and inferential processes. Even with bullets, missiles and biological attacks, analysts can rarely provide 100% certainty about who is ultimately responsible for giving an order to attack. For example, a bio-terror attack in 2001 took place when numerous letters containing anthrax spores were mailed to media outlets in Florida and New York. Five people were killed. Yet despite concrete evidence and extensive chemical and biological analyses, analysts could not immediately and definitively identify the attacker (Koblentz and Tucker, 2010). Attribution is a complex art in all domains. Nevertheless, the absence of definitive assurance does not prevent political leaders and military officials from responding to attacks. They and we have learned to incorporate some uncertainty into decision-making processes. In this light, it is incumbent upon us to incorporate a spectrum of uncertainty into our cyber-attribution dilemmas, and avoid oversimplifying attribution as a binary construct.
How uncertainty alters support for retaliation – A situational and psychological account
To this point in the article, our analysis has focused on sense-making – the manner by which complex data are converted into attribution judgments (Egloff and Dunn Cavelty, 2021). However, attribution is not the end-point of the process. Attribution is central to cybersecurity politics precisely because it imbues technical phenomena with political consequences, creating truths that guide decision-making. Therefore, to understand how attributional uncertainty influences political outcomes, we need to progress to a second and often forgotten step of meaning-making. This step explores how attribution judgments exert concrete political effects (Egloff, 2020a). Once an attributional judgment has been made, at a given level of certainty, we must them examine how people interpret and act upon these judgments. If the first step is deliberate investigation of the empirical circumstances of an act, the second phase is entirely subjective, making it prone to psychological biases, political pressures, and competing narratives acting upon human decision-making (Egloff and Dunn Cavelty, 2021; Lindsay, 2015).
The mass public must frequently grapple with government assessments made with varying degrees of certainty. A model scenario emerged in 2023, where, amid acrimonious discussions on the origins of COVID, the US Energy Department and the FBI published reports concluding that COVID may have leaked from a laboratory, yet noted that the assessment was made with low or moderate confidence. Four other agencies declared that the virus arose naturally from an animal, with low confidence. The question for us is how people react to the proviso of confidence assessments – whether it exerts any effect, and if so, how strong.
In the context of cyberattacks, it is widely assumed that heightened uncertainty will diminish support for retaliation. On the most basic level, retaliating against an innocent actor, whether militarily or by imposing trade sanctions, could have severe consequences, and risk-aversion in foreign policy matters is likely to diminish support for aggressive steps under unclear circumstances (Hansel, 2018). To the extent the public acts rationally, lower attributional certainty should therefore decrease support for retaliation.
However, people do not always act rationally, and emotions exert a strong influence on decision-making – especially in cyberspace (McDermott, 2019). Recent studies have demonstrated that exposure to cyberattacks elicits strong emotional responses that can sway subsequent decision-making (Backhaus et al., 2020; Canetti et al., 2017; Shandler et al., 2023a). Specifically, to the extent that people experience anger following cyberattacks, they tend to lash out against perceived injustice and demand retaliation against responsible parties (Shandler et al., 2022a). Despite the centrality of emotional dynamics surrounding cyber threats, the process of converting uncertainty into policy judgment demands cognitive/evaluative processes, and we therefore suggest that uncertainty considerations will be more rational than emotional.
Weighing the foregoing factors, we formulate a pre-registered hypothesis that:
Hypothesis 1: lower attributional certainty will reduce public support for retaliation.
In addition to this primary theoretical expectation, we offer several additional hypotheses to tease out some nuances of when and why uncertainty can exert an effect on retaliatory preferences. Though these subsequent hypotheses were not pre-registered in advance of the data collection, we find the results persuasive, and offer a theoretical basis for the expectations to allow readers to reach an informed decision as to their validity.
A key factor guiding decision-making surrounding certainty assessments is people’s discomfort with complex numerical variables. It is easy to absorb the implications of uncertainty on a binary scale. Either we know who is behind the attack, or we do not. But what does it mean that officials are 70% certain a particular country is responsible for a military strike? If the level of certainty rises to 75% – what weight should we give to that incremental change? Extensive research has demonstrated that people struggle to effectively draw meaning from numbers (Peters et al., 2006). Due to people’s difficulty with numerical assessments, we further hypothesize that:
Hypothesis 2: respondents will internalize the uncertainty spectrum by treating any attribution above a threshold level as certain, while viewing any attribution below that threshold as uncertain.
For this expectation to be corroborated in our findings, we should see a steep drop off in support for retaliation at one particular level of certainty.
Beyond a general discomfort with complex analyses, there are cognitive schemas specific to cyberspace that guide decision-making in the aftermath of cyberattacks (Gomez, 2021; Hansel, 2018). These schemas form fallback tools that facilitate the processing of ambiguous information. For example, Gomez (2019: 1) introduced the concept of ‘seizing’ in cyberspace – ‘a pre-disposition to gravitate towards cues that appear to confirm pre-existing belief(s).’ This inclination, conceptually similar to more well-known confirmation biases, is associated with the need to maintain cognitive consistency despite uncertainties. As such, we can expect that faced with attributional uncertainty, people will search for cues confirming their existing beliefs. A significant cue in this regard would be their view of the country that is under suspicion. As a general rule, the public copes with a confusing world by adopting images about countries (friend or foe) that help guide their reasoning about world affairs (Brewer et al., 2004; Castano et al., 2016). People use these images as informational shortcuts to form political judgments and interpret confusing or contradictory data.
We therefore hypothesize that:
Hypothesis 3: country images will moderate the effect of attributional uncertainty.
In other words, to contend with attributional uncertainty, people will partly interpret events through the lens of foreign political alliances. For example, if the United Kingdom was suspected with 50% certainty of conducting an attack on the USA, we suggest the American public would grapple with the uncertainty of this claim by falling back upon their pre-existing view of the UK as a longstanding US ally. But if China, a rival, were suspected at the same level of certainty, the public would interpret the analysis through the lens of their pre-existing adversarial image of China to reduce cognitive dissonance. As partisanship is highly correlated with people’s trust in and view of foreign countries (Brewer, 2004), we further hypothesize that:
Hypothesis 4: the friend or foe heuristic will be contingent upon partisan identity.
Republican foreign policy rhetoric is harsher towards rivals and warmer toward allies than Democratic rhetoric (Ivie and Giner, 2009), meaning any moderating effect of country image should be steeper among Republicans.
A second schema that influences decision-making in an environment of uncertainty is people’s perception of the mode of military/diplomatic/economic retaliation. While the public is generally willing to support military escalation if the stakes are important and the prospects of victory are favorable, they are less likely to support forceful military retaliation for attacks experienced in the cyber domain (Kreps & Schneider, 2019; cf. Gross et al. 2016; 2017). This may result from increased attributional uncertainty in cyberspace dampening enthusiasm for aggressive retaliatory options (Hedgecock and Sukin, 2023). If the identities of cyber attackers are inherently uncertain, people may prefer retaliatory cyberattacks to cross-domain retaliation. We therefore hypothesize that:
Hypothesis 5: method of retaliation will moderate the effect of attributional uncertainty.
When uncertainty is greater, we expect that respondents will exhibit higher support for cyber retaliation, and that this relative preference for cyber retaliation will diminish when the identity of the attacker is more certain.
Experimental design
Traditional experimental techniques would find it difficult to effectively test the effects of a continuum of attributional uncertainty due to statistical power constraints. Since viewing attributional uncertainty on a spectrum is a key theoretical development of this article, we employ a discrete choice conjoint technique to study how different levels of certainty drive public support for retaliation. 1 A conjoint design allows us to hold fixed a range of additional relevant attributes of incidents that would otherwise confound observational studies. This experimental technique works by constructing randomly generated scenarios with interchangeable values drawn from a prepopulated list of attributes. Each attribute, outlined in Figure 1, has between four and nine values that are randomly selected to populate the scenario. For example, the attribute of ‘attributional certainty’ could be any of nine values on a spectrum from 10% to 90%, while the ‘suspected attacker’ attribute could be either Russia, China, Israel, India or the United Kingdom. In our conjoint structure, there are 32,400 unique permutations of the scenario that can be assembled by drawing a single value from each attribute. 2
The survey was distributed to a nationally representative sample of 2025 respondents in the USA via the Qualtrics survey company. 3 After viewing a scenario describing a cyberattack against the USA, respondents were presented with information about two possible perpetrators. For each suspected country, the randomly allocated information dealt with the certainty of the attribution, the proposed means of retaliating, the costs (economic and human) of retaliating, the chances of conflict escalation, and the identity of the attacker. Each respondent was asked to indicate which course of action they prefer in a head-to-head style matchup: retaliate against possible perpetrator A, retaliate against B, or avoid retaliation at this time. Each respondent evaluated a total of five scenarios, with two suspected attackers and proposed responses in each scenario, amounting to 20,050 retaliatory action decisions. Detailed balance checks and further information on sample demographics appear in Online appendix A. The experimental design and pre-registered hypotheses were submitted prior to data collection, and the pre-analysis plan appears in the Online appendix.
Survey instrument
In the experiment, we manipulate six attributes of a cybersecurity incident involving US critical infrastructure. In addition to the level of attributional uncertainty,
Attributes and values in conjoint treatment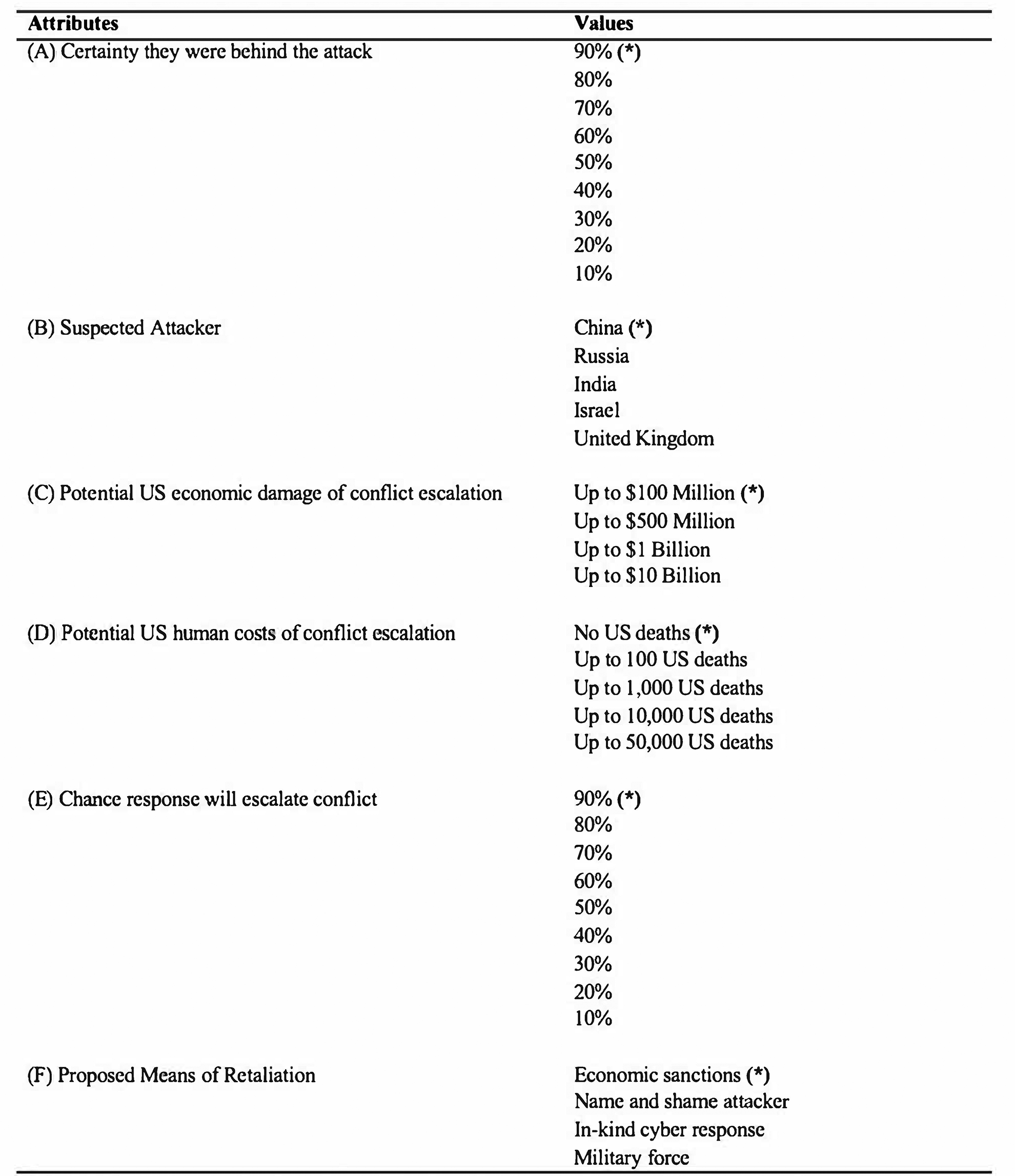
First, we manipulate the level of attributional certainty. We refrain from a pre-emptive binary categorization of certain versus uncertain, preferring to include nine possible values of attributional certainty ranging from 10% to 90% – increasing in 10% increments. We do not include a 0% certainty option, since there is no genuine prospect of retaliation against a country that is not at all suspected as a perpetrator. Likewise, we do not include a 100% certainty option, since this level of certitude is exceedingly rare for cyberattacks where adversaries employ even basic obfuscation steps. The highest level of certainty (90%) was selected as the baseline value against which progressively deteriorating confidence in the identity of the attack can be compared.
Second, we manipulate the identity of the suspected attacker. Possible attackers included China, Russia, 4 India, Israel and the United Kingdom. These countries reflect a mix of prominent allies (UK, Israel), rivals (Russia, China), and non-aligned countries (India). The US public holds remarkably consistent attitudes towards foreign countries (Castano et al., 2016), and these countries were included as a result of their ability to evoke instinctively positive or negative views. Right or wrong, Americans have coherent views of friends and foes, and these perceptions shape attitudes towards foreign affairs.
Third, we manipulate the economic cost of retaliation. Research has repeatedly shown that the public contemplates expected costs of military action in deciding whether to support military strikes (Tomz and Weeks, 2013). This logic extends to other retaliatory action, with higher economic costs leading to lower public support. Our conjoint structure includes four possible predictions of the potential economic cost of retaliation: $100 million, $500 million, $1 billion, and $10 billion. The lowest figure of up to $100 million serves as the baseline value.
Fourth, we manipulate the number of potential deaths expected to arise from any subsequent military escalation of the conflict. Public attitudes towards retaliation are directly associated with expected casualties (Fazal, 2021). Values for this attribute were set to randomly vary from either no US deaths, up to 100, up to 1000, up to 10,000 or up to 50,000 US deaths. These are not expectations of casualties stemming from a single strike, but rather the cumulative consequence of an escalating incident. Zero deaths serves as the baseline value.
Fifth, we manipulate the estimated probability of the conflict escalating into a broader conflagration following the proposed response to the current incident. Similar to financial costs and expected casualties, the public typically evaluates the likelihood of the mission being successful (Gelpi et al., 2009). We therefore offer a range of likelihoods that action will lead to further escalation, with values ranging from 10% to 90% by increments of 10%.
Sixth, we manipulate the proposed method of retaliation. The public possess keen views about appropriate modes of retaliation, a factor heightened in cyberspace due to people’s innate caution about escalating cyberattacks into the physical domain (Kreps and Schneider, 2019; Shandler et al., 2021). We include four options for retaliation: economic sanctions, naming and shaming the suspected attacker, in-kind cyber response, and military force. As naming and shaming a potential aggressor is the least destructive potential option, this value is the baseline against which the more serious retaliatory choices are compared. To ensure plausibility, when the proposed method was naming and shaming, only the zero-casualty condition was used.
The possible range of scenarios respondents may encounter via our conjoint technique is extremely broad. At one end of the spectrum, a randomly generated scenario might depict a physically destructive attack against critical infrastructure initiated by a state rival that paves the way toward a costly war. At the other end of the spectrum, a scenario might depict a minor cyberattack that causes no major consequences, little economic damage, and provokes a meek response involving the naming and shaming of the attacker. We emphasize that not all of these scenarios are equally likely to occur in reality. The inclusion of unlikely state-on-state attacks is not an endorsement of the discredited ‘cyber pearl-harbor’ perspective of cyber threats. Rather, we broadly operationalize cyberattacks as having minimalist and maximalist effects in order to test how different scenarios elicit public responses at different levels of severity, and with different levels of attributional certainty.
Results
Figure 2 displays the full conjoint plot showing the relative effect of each attribute. To analyze the respective influence of each value, we look to the average marginal component effects (AMCE). The AMCE statistic calculates the marginal likelihood that the inclusion of a particular value in our scenarios elicits support for retaliation relative to the baseline value in that attribute (Hainmueller and Hopkins, 2015). All standard errors are clustered by respondent in recognition of the fact that rating outcomes are not fully independent when respondents evaluate multiple scenarios. Lines indicate 95%
Effects of incident attributes on the probability of supporting retaliation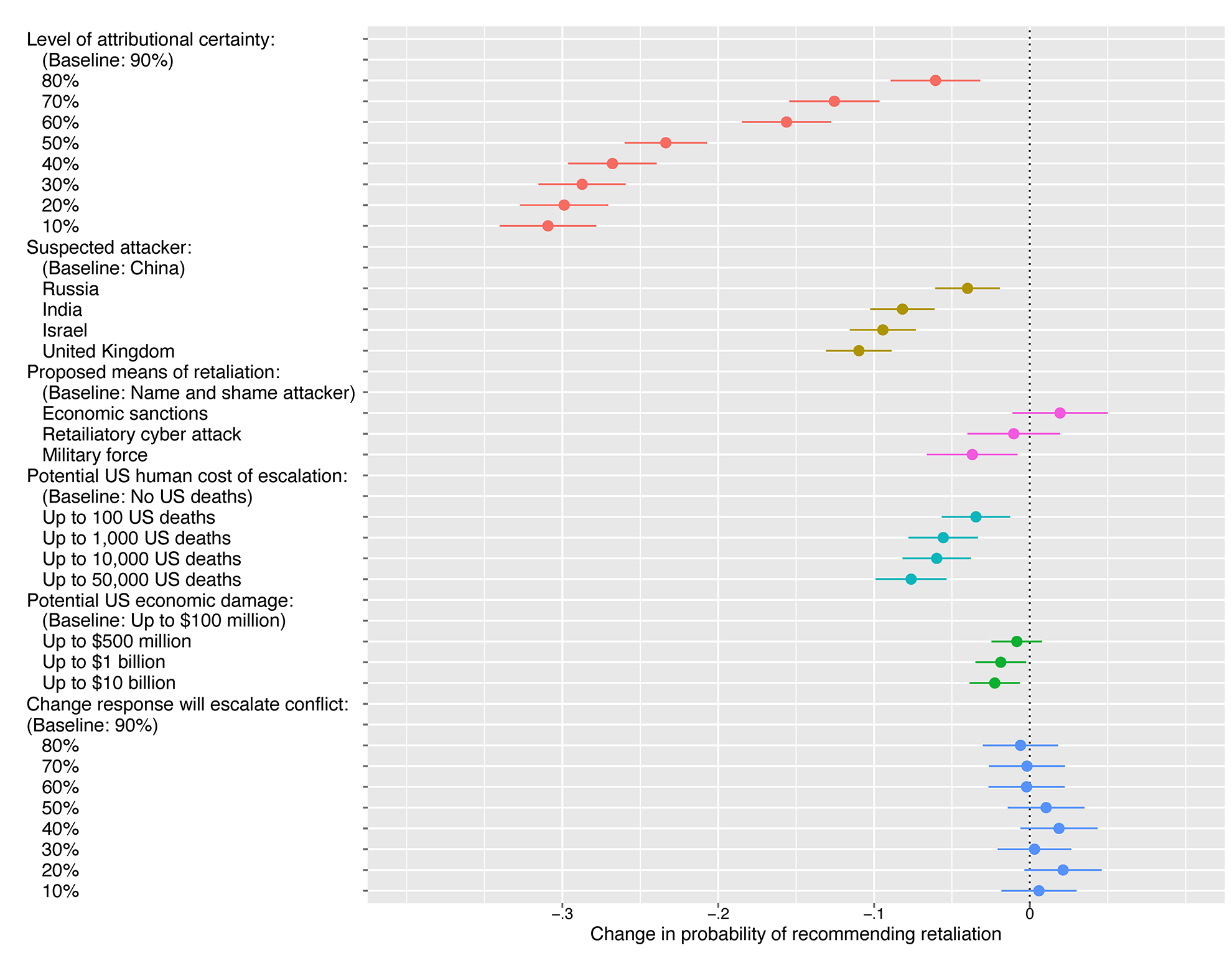
A number of trends immediately emerge from Figure 2. Taking note of the effect of
Looking closer at the trendline for uncertainty, we observe two statistically significant discontinuities. For incidents where the attacker’s identity is known with a 10% to 50% level of confidence – people exhibit a similar contraction of support for retaliation ranging from 23.4 to 30.9 percentage points. It is not that each consecutive reduction in certainty wipes away an equivalent level of support for retaliation in a linear additive manner. Rather, the public views all assessments at 50% certainty or less almost interchangeably, under the artificial category of low certainty. By contrast, attributional assessments ranging from 60% to 70% form a middle range and are, in effect, undifferentiable from each other. Again, 80 percent certainty qualitatively jumps from the 60% to 70% range, with the reduction of a willingness to retaliate dropping by just over 5 percentage points from the maximal certainty score in our data (90%).
The emergence of two empirical discontinuities in a numerically continuous uncertainty scale accords with our second hypothesis. We expected people’s tendency to simplify continuous spectra into discrete categories would lead to the adoption of guiding schema, and we find that the 50% or less, 60–70% and 80% or greater are the crucial levels at which the public ascribed different levels of attributional confidence from the numerical data. While we anticipated a single cut point, the occurrence of two distinct cuts fits with expectations.
Turning to the identity of the
The following three attributes investigate how potential future consequences of retaliation influence support for retaliatory action. Looking at the economic
The
Looking at another future-oriented attribute, we find evidence that
Finally, the
Interaction effects
Recognizing that attributional uncertainty does not operate in a vacuum, we consider several interaction effects. We hypothesized that the uncertainty in cyberspace would arouse a tendency to adopt cues confirming pre-existing beliefs (H3). In international relations, the most relevant guiding schemas are views of countries as either friends or foes. As such, we expect to see the uncertainty effect tempered for allies and inflated for rivals. In Figure 3 we present this interaction effect. We find that certainty’s effects are indeed sensitive to pre-existing diplomatic ties – though this interaction primarily occurs where attributional certainty rises into the ‘high confidence’ territory.
At the lowest end of the spectrum, where certainty about the identity of the attacker is a mere 10%, we
Certainty and country interactions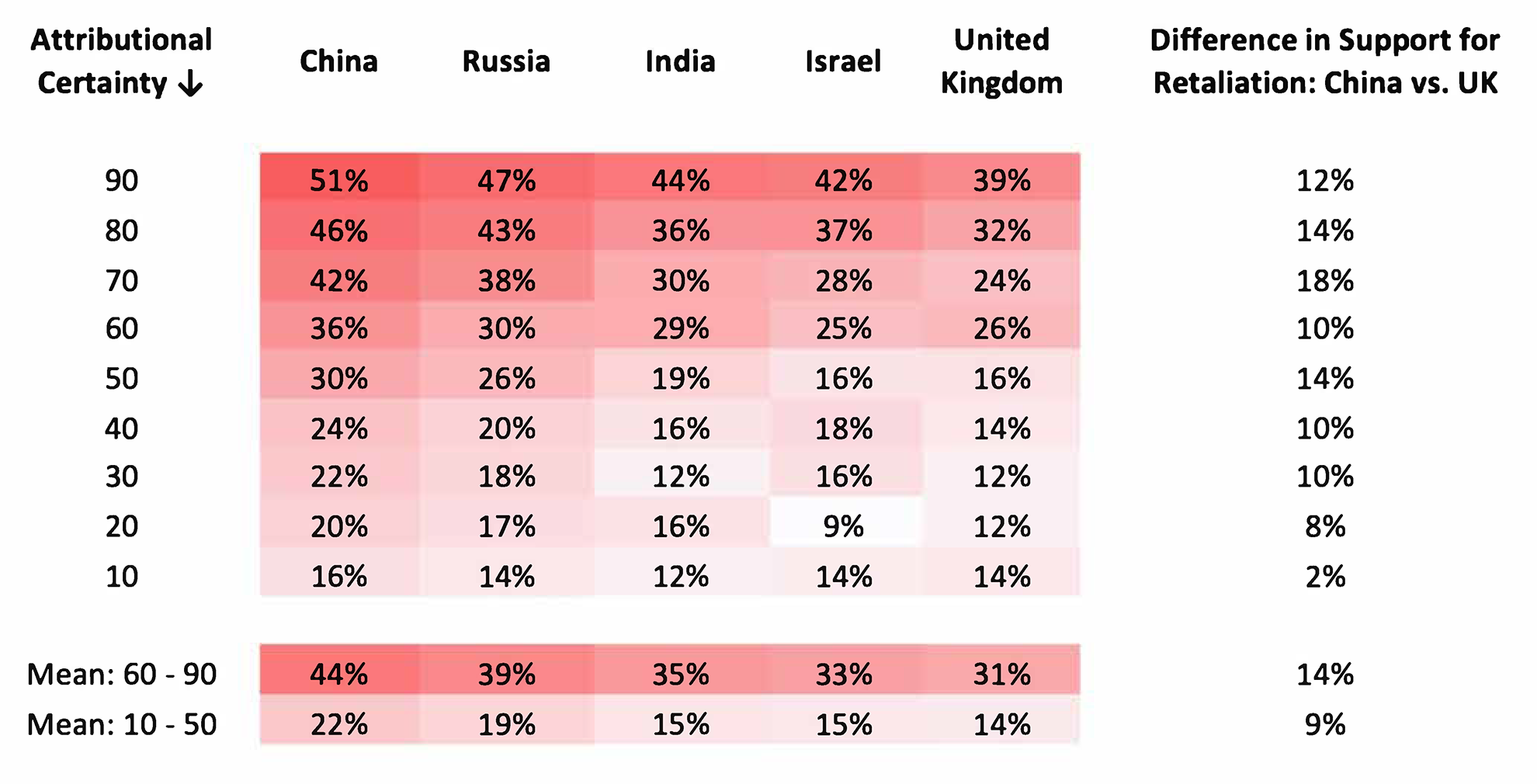
Put simply, perceptions of countries as adversaries or allies affect the way in which fluctuating certainty levels matter for the predicted probability that someone will choose retaliation. This is most true at boundaries between implicit categories of low, medium and high confidence discussed earlier, where the public may be seeking more information to determine how to decide liminal cases. Historical allies, such as the United Kingdom, possess a reservoir of good will that blunts the effect of increasing certainty once it passes the 50 percent level. Adversaries such as China do not. In this way, cyber uncertainty can hinder public support for conflict, depending on the way that the uncertainty interacts with pre-existing geopolitical realities.
Even though the public generally holds consistent attitudes towards foreign countries (Castano et al., 2016), foreign policy views are increasingly split according to domestic partisan identities (Mirilovic and Kim, 2017). We must therefore account for potential partisan divisions in understanding how attributional uncertainty interacts with people’s views of countries as friends or foes (H4). In Figure 4, we present the same certainty by country interaction results from Figure 3, this time disaggregated by partisan alignment. 5
The results indicate that the effect of uncertainty on support for retaliation against particular countries is largely contingent on partisan identity. For Republicans, the perception of a country as an ally or rival is a crucial signal, while Democrats are less sensitive to the identity of the suspected attacker. As a result, Democrats are less willing to retaliate against adversaries, and more willing
Certainty and country interactions – disaggregated by party identification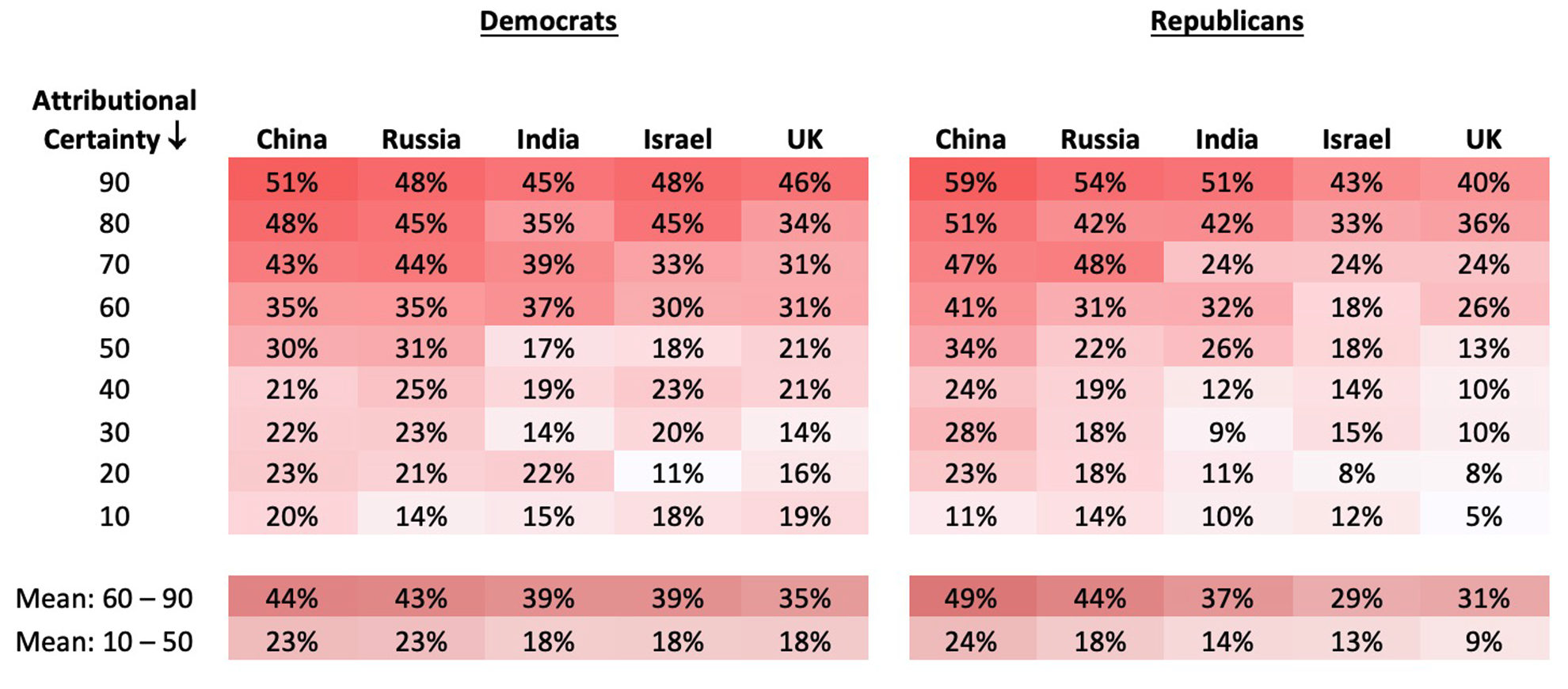
This ideological interaction effect is stronger than other heterogeneous factors such as digital literacy and education – both of which are significant predictors of attitudes following cyberattacks (Kostyuk and Wayne, 2021). The minimal role played by literacy, news consumption and education (discussed in Online appendix E) further highlights the importance of partisan identity in interpreting uncertainty.
Our final interaction analysis focuses on a second schema that we hypothesized to play a role during uncertain cyberattacks – the mode of retaliation (H5). We anticipated that respondents would exhibit high relative support for cyber-retaliation over conventional retaliation when the identity of the attacker is not completely known. In Figure 5 we present the interaction between attributional certainty and mode of retaliation.
What jumps out immediately is a consistently low willingness to retaliate across all modes of retaliation when certainty is at 50% and below. We had expected that at low levels of attributional certainty, the public would ‘hedge their bets’ by exhibiting a preference for less violent retaliation that would avoid escalatory behavior. But this preference does not manifest. Rather, when authorities are uncertain about the identity of the attacker, people equally spurn violent and nonviolent retaliatory actions (all weapons are equally ineffective against an unknown enemy). Yet where there is higher confidence about who is responsible for an attack – between 60% and 90% – retaliation becomes more palatable. Our fifth hypothesis is therefore partially verified.
Discussion
Uncertainty is a core and unavoidable facet of cyberspace (Dunn Cavelty et al., 2023). While it is futile to attempt to overcome uncertainty, its effects can be understood, measured, and incorporated into our thinking about cyber threats. To examine the effect of uncertainty, we proposed and tested an uncertainty threshold mechanism using a nationally representative sample of 2025 US respondents who were exposed to various cyberattacks for which authorities expressed differing levels of certainty about the identity of the responsible party. While lower certainty in attribution is associated with less support for retaliation, we find that this mechanism is contingent on the suspected identity of the attacker. Diplomatic allies possess a reservoir of good will that
Certainty and retaliation mode interactions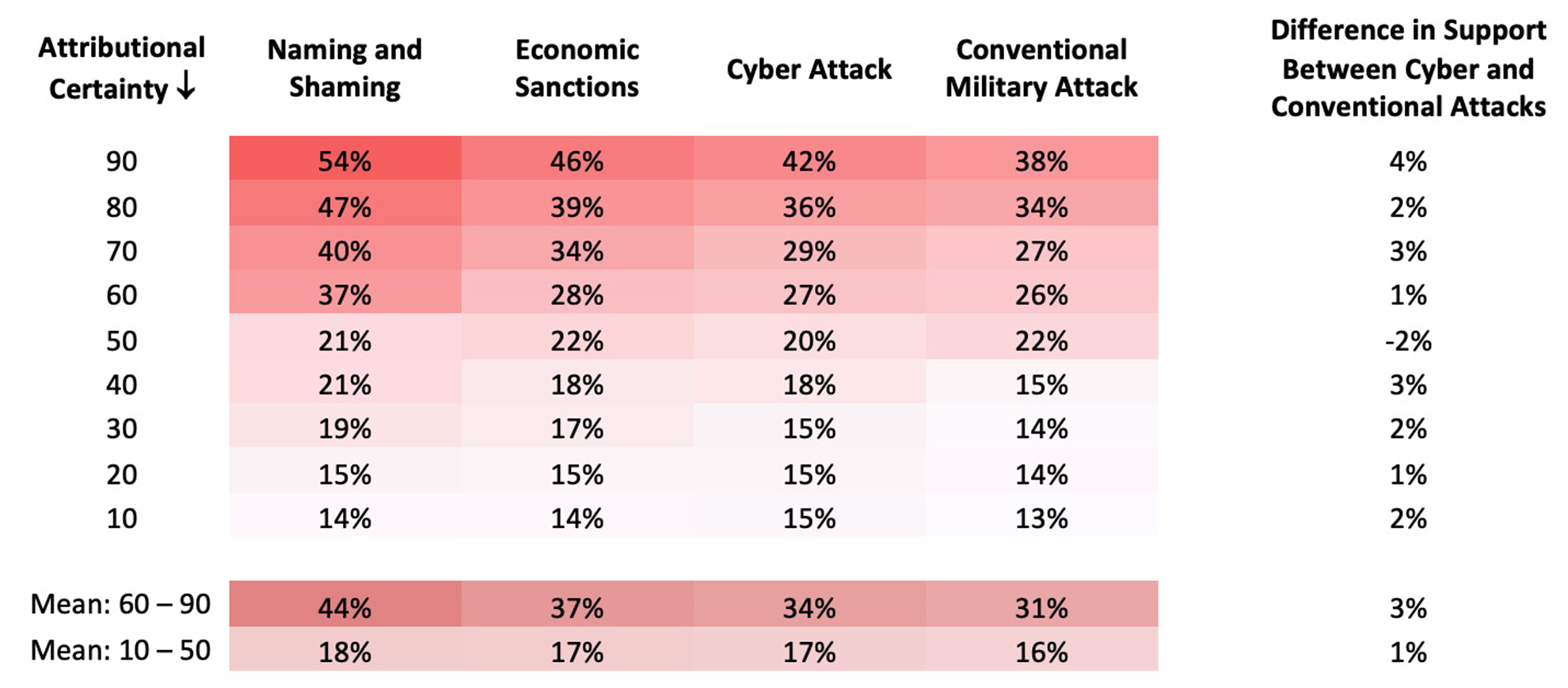
First, leaders should pay careful attention to public attitudes when considering retaliatory action following cyberattacks. The current findings clarify how much certainty is needed for the public to support retaliation against an aggressor nation. To the extent elites think like the public (Kertzer, 2022) or public attitudes shape foreign and defense policy decisions (Tomz and Weeks, 2013), the findings suggest that the certainty of blame assignment can influence geostrategic policy outcomes. This mechanism works in two directions – offensively and counter-offensively. From an offensive perspective, when planning cyber operations, military officials have a small yet crucial amount of flexibility in terms of leaving traces that can be ascribed back to the source of the attack. Contrary to popular accounts, cyberattack can never be fully anonymous since analyses of attribution incorporates technical and geo-political factors (Rid and Buchanan, 2015). Yet so long as overall confidence in ascribing a name to the source of the attack remains at 50% or below, officials can avoid added public pressure that would be placed on rivals to retaliate. From a counter-offensive point of view, authorities will need to swiftly formulate high-confidence projections about who is responsible for an attack, at 60% certainty or higher, to accrue public support for retaliatory strikes. To be clear, we are not arguing that the tail can wag the dog, and that public opinion can override strategic doctrine and compel leaders to retaliate. Rather, we emphasize that public opinion is an important factor that is undoubtedly part of the decision-making calculus considered by leaders.
Second, people compensate for the uncertainty of cyberspace by adopting images about countries as friends or foes, which guide their reasoning about world affairs. This particular mental shortcut manifests as a diplomatic good-will/aversion effect. If authorities are not entirely certain about who is responsible for an attack, and the alleged aggressor is an ally, the ambiguity will cause people to fall back on their view of the country as a friend, forestalling public support for retaliation. Counter-intuitively, this finding may encourage the ongoing use of cyber espionage among allies, since they can draw on a reservoir of good will to avoid reprisals so long as there remains at least some uncertainty about their responsibility. With cyber espionage norms still in flux (Libicki, 2017), our findings offer evidence about the interaction between alliances and uncertainty in cyberspace. Uncertainty, however, is less of a shield for countries perceived as adversaries. It has been customarily assumed that countries can leverage digital uncertainty to attack rivals so long as they maintain a veneer of doubt about whether they are truly responsible. We show that this expectation is unwarranted, and that the public will still support retaliation so long as it abides by their pre-existing view of the attacker as a rival. The fact that such viewpoints are guided to a large extent by partisan identification, offers a new way in which domestic partisanship intervenes in foreign policy attitudes.
Last, our findings add valuable nuance to an ongoing debate about public support for cyber strikes. Past research maintains that the general public enthusiastically supports the use of cyberattacks due to its low cost, limited destructiveness, and ability to avoid friendly and civilian casualties. However, we show that the public preference for employing cyber tools is not absolute. Had the public perceived cyber weaponry as a fully anonymous and non-escalatory tactic, then we would have seen strong support for its deployment even at low to moderate levels of attributional certainty. Yet this wasn’t the case, indicating the public has developed a keen understanding of the significance of cyberattacks following a string of highly destructive incidents. We learn from this that the public preference for cyberattacks does exist, yet only when certain conditions for military action are in place.
We underline a crucial proviso of any discussion about uncertainty. What is uncertain today, need not be tomorrow. When it comes to emerging technologies that carry with them the power to shock and awe, long-term exposure ‘mitigates the emotional response associated with it, normalizing novel threats over time’ (Gomez and Whyte, 2021: 1137). According to this view, the effect of uncertainty on public opinion may wane over time as the public becomes more acquainted with cyberspace and cyberattacks. Nevertheless, a decade of observational, experimental and physiological evidence of psychological distress stemming from cyberattacks (Shandler et al., 2023a), along with persistent media depictions of exaggerated cyber doom narratives (Bastug et al., 2023; Makridis et al., 2024), suggest that public trepidation surrounding cyberspace will endure for some time to come.
As a concluding note, the conspicuous absence of destructive cyberattacks has reinforced the idea that cyberattacks are used predominantly as a tool of sub-crisis maneuvering allowing states to operate below the threshold of armed conflict (Harknett and Smeets, 2022; Kostyuk and Gartzke, 2022; Maschmeyer, 2023a). This may be the case, yet what is more important from the public’s vantage point is not the objective reality of cyberattacks, but how the attacks are construed in the media. It is not uncommon for accidental digital mishaps to be hyperbolically reported as major cyberattacks (see for example Teale, 2023 on the Florida water plant, where the sensational hack turned out, several years later, to be an employee mistake). At the time, leaders had to endure significant public pressure to respond to the alleged attack, making the question of attributional confidence extremely salient.
In all, this article has contributed to our understanding of how uncertainty in cyberspace influences public reactions to cyberattacks. The discrete choice experiment at the heart of the study quantifies how much uncertainty about ‘who done it’ might inhibit public support for retaliation. The short answer is: uncertainty matters. The long answer reveals that 60% certainty is the threshold that must be achieved in attributional assessments to get the public on side, yet this is contingent on the identity of the purported attacker, and the type of policy response under discussion. Underlying both of these answers is the fact that public opinion matters, and we can now better assess how the uncertainty characteristic of cyberattacks influences the formation of public judgments.
Footnotes
Replication data
Authors’ note
This publication is not affiliated with Chainalysis and the views represented herein are those of the respective authors.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
