Abstract
The article introduces a new dataset on terrorist attack activity by jihadis in Western Europe. The dataset was built over nearly two decades at the Norwegian Defence Research Establishment. It records not only attacks that were launched, but also plots that were foiled by counterterrorism. The rationale behind the dataset is that analyses based on launched attacks may misrepresent the scale and nature of terrorism. The article shows that if we were to measure the jihadi threat to Europe by attacks only we would miss out on 58.2% of the total attack activity. We also show that while attack data signify a trend towards small attacks by individuals, these data hide the fact that terror networks persist in plotting big attacks that get foiled. We discuss how analyses based on attacks only may distort comparative analyses of different types of terrorists across countries, as well as causal analyses of terrorism drivers. By including foiled plots we gain a fuller picture of terrorism. The Jihadi Plots in Europe Dataset allows the gauging of different aspects of the threat from Al-Qaida and Islamic State in Europe. The dataset documents when and where terror plots occur, whether or not they result in attacks, and different types of information about perpetrators and how they operate. The Dataset offers a reliable overview of jihadi terrorism in Europe for research and policy.
Introduction
The Jihadi Plots in Europe Dataset (JPED) records attack activity by jihadi terrorists in Western Europe since 1994. JPED registers attacks (launched plots) and attacks that are prevented (foiled plots). The dataset includes information about the date and location of plots and the number of people killed and injured, as well as information about perpetrators, their tactics, weapons and targets. The rationale behind JPED is the need for terrorism research to exploit data on foiled plots. Nearly all quantitative studies of terrorism use attacks as a metric. These studies may misrepresent the scope and nature of terrorism since attacks are ‘the tip of the iceberg’ (LaFree & Dugan, 2007).
Many terror attacks are never completed because counterterrorism intervenes. In JPED, as many as 58.2% of plots are foiled. This means that we cannot get an accurate understanding of the jihadi threat to Europe based on attacks. By counting attacks only we will misinterpret both the scale of jihadi terrorism and trends in the modus operandi. JPED shows, for example, that 79.8% of terror plots involving multiple perpetrators are foiled while only 35% of plots involving single actors are foiled. Because groups tend to launch bigger and deadlier attacks than singletons, this makes the threat seem smaller than it is simply because counterterrorism has prioritized stopping large-scale operations.
If we only count attacks we will also misjudge the relative threat from different terrorists when counterterrorism prioritizes one threat over others. This is relevant to debates over, e.g. the threat from jihadism vs. right-wing terrorism. Last, a focus on attacks may distort causal analyses, because one gets statistically significantly different results using attacks as a metric, vs. including foiled plots (Hegghammer & Ketchley, 2020). Despite these problems, attack data dominate research and policy. Because effective counterterrorism requires an accurate understanding of threats, we must grasp the relationship between attacks and foiled plots. JPED offers data to that end.
Notwithstanding growing awareness about the need to study foiled plots, very few datasets include them. Most existing data on foiled plots are incident lists published with case studies, not tabulated data. The main challenge when building datasets of foiled plots is reliability. It is harder to obtain reliable sources on foiled plots than attacks. Maintaining datasets of foiled plots is labour-intensive.
The article first offers background for JPED. Second, it presents key definitions and inclusion criteria. Third, the article examines challenges related to sources and coding. Fourth, it reviews existing data on foiled plots. Fifth, the article mentions JPED’s key variables, before exemplifying how the dataset can be used to gain a fuller picture of terrorist attack activity.
Background
In 2003 the Norwegian Defence Research Establishment (FFI) started mapping the activities of Al-Qaida in Western Europe. Most of these activities revolved around propaganda, recruitment, financing and gun running.
There was also an emerging pattern of attack plotting. Cells linked to Al-Qaida plotted attacks on US and Jewish targets in European countries. These first Al-Qaida plots were foiled by counterterrorism. We decided to focus our data collection on attack-geared activity and assembled information about the terror plotting in a chronology (Nesser, 2008). Following the 2004 Madrid bombings and 2005 London bombings, we extended the chronology to include historical data on jihadi terrorism in Europe.
We traced its beginning to the mid-1990s bombing campaign in France by the Algerian GIA (Lia & Kjøk, 2001). The chronology became a dataset, maintained through monitoring of media and other sources. JPED covers three waves of terror plotting: the GIA wave in the mid-1990s; the Al-Qaida wave in the 2000s; and the Islamic State (IS) wave from the mid-2010s. The reason for including historical data was that the three waves are interconnected. People involved in the GIA wave reappeared in Al-Qaida cells during the 2000s. Former Al-Qaida personnel then came to play roles in the IS wave (Nesser, 2018).
Definitions
JPED tracks jihadi terrorist attack activity. ‘Terrorist attack activity’ includes ‘terrorist plots’, which are ‘launched’ (attacks) or ‘foiled’ (derailed attacks). The terrorist plot must be attributed to a ‘jihadi’ perpetrator. JPED can only record terrorist plots documented in open sources. A system was developed to avoid generalization from dubious cases. The system is presented in the section on reliability.
‘Jihadi’ denotes groups or individuals linked to Al-Qaida or IS, or motivated by their ideology. 1 ‘Terrorism’ is rational, planned, politically motivated violence, by non-state actors, aiming to spread fear beyond the immediate target and cause political change. 2
JPED applies a narrow understanding of terrorism. It excludes non-lethal, lower-scale politicized violence, such as sabotage/vandalism and street violence/beatings (hate crime). Observations recorded in JPED pertain to distinctly politically motivated and lethal/potentially lethal bombings, shootings, stabbings or prepared plans thereof, associated with wider terror campaigns. This falls within a narrow definition of terrorism. A main coding challenge is determining as to whether or not perpetrators are rational. JPED seeks to exclude cases involving severe mental illness. Establishing what counts as ‘severe’ boils down to case-by-case assessment.
JPED narrowly defines ‘terrorist plots’ as launched attacks, or well-documented plans to launch attacks, where steps are taken to prepare. A plot is ‘foiled’ when an attack plan derails. Plots usually derail owing to counterterrorism, but also for internal reasons, such as loss of resolve or practical difficulties.
JPED only includes plots that are publicly documented and seem viable. We exclude threats or expressed intentions to launch attacks with no evidence of preparation. We cannot record potential plots security services may/may not have prevented through early interventions. One cannot tell as to whether or not such potential plots would have materialized absent intervention. There is no way of confirming that security services have stopped potential plots. We have not found statements by European security services indicating that they have stopped a myriad of potential plots unknown to the public. We assume there are dark figures regarding potential terror plots, but contend that these are limited because of incentives for security services to report on what they foil. We also contend that the number of terror plots being terminated by terrorists themselves without intervention is limited. Because terrorists tend to tell others about their intentions (Schuurman et al., 2018), most viable terror plots will probably become known.
‘Europe’ refers to Western Europe, not including former Eastern Bloc states. For a terrorist plot to be included, it should be prepared within Europe and target Europe/Europeans. This includes plots to target airliners taking off from a European country, e.g. the 2006 foiled plot to attack trans-Atlantic airliners departing from the UK.
Sources
Terrorism is secret activity, and information about foiled terrorist plots usually comes from law enforcement and leaks from investigations. It may be in the interests of states to manipulate information to justify countermeasures. Such manipulation of information is probably limited in democracies as there are institutionalized checks on what security services can and cannot do.
Media sources have been the main tool when building JPED. Looking at transnational terrorism, media sources are a valuable source. Working with media sources has its challenges. The quality of the reporting varies across publications, between countries and between journalists. Sometimes reporters exaggerate to make headlines. When possible, we have cross-checked media reports against judicial documents, official reports, other research and interviews with investigators or former extremists. All these sources come with biases, so there will always be an element of uncertainty.
Reliability
To secure the reliability we maintain a chronology of thick plot descriptions. This means that every plot is described in detail and (if possible) based on more than one source. Secondly, we developed a classification system distinguishing well-documented cases from dubious ones. It classifies JPED’s plots into three categories based on documentation. For an incident to be included we need documentation that the perpetrator is jihadi. Secondly, we need documentation that an attack was launched, or in the making (e.g. bomb-making). Last, we need documentation about targeting. If all aspects are well documented, the case is category 1 (C1). If two aspects are well documented, it is category 2 (C2). If there are uncertainties regarding two or more aspects, the case is defined as category 3 (C3). The purpose is to avoid generalizing from dubious (C3) cases.
An example of a C1 case is the 2015 attacks on the offices of Charlie Hebdo in Paris. Perpetrators launched a mass-casualty attack and reliable sources tied them to Al-Qaida (Shoichet & Levs, 2015). An example of a C2 case is the 2018 plot to launch an attack with ricin in Germany. The perpetrator was in contact with IS and produced poison and explosives (Fade, 2018). The case was coded C2 because of lack of documentation concerning the target. Typical C3 cases are reports about arrests of people suspected of plotting attacks, revealing little about their connections, target and preparations.
Category 3 is also used to handle cases that may/may not involve ‘severe’ mental illness. Plots by people reported to have mental health issues/challenges are generally coded C1 or C2 in JPED, as long as they they meet the inclusion criteria. Sociological–psychological challenges are commonplace among extremists, and do not rule out rational behaviour. This is reflected in legal cases where people with personality disorders get convicted. However, cases that seem to involve severe illness are coded C3, awaiting confirmation. JPED demands that perpetrators are rational. Plots confirmed to involve severe mental illness which overshadows political motives should not be counted.
An example is a British IS-inspired convert, serial fraudster and former porn director, who suffered from severe personality disorders. He contemplated assassinating Prince Harry. The convert received a three-year sentence in 2014, but was released in 2015 (Woodhouse, 2018). The case was first coded C2 and then categorized C3. While technically this was a C2 plot, the circumstances were too bizarre to represent jihadism. An opposite example is the 2019 knife attack at a French police station by an employee (Schofield, 2019). The case was initially coded C3 owing to reports about the mental state of the perpetrator. He had also been involved in workplace disputes that cast doubts about the terrorist motive. However, further investigations confirmed that the attacker was radicalized, putting the case back into C2. We keep C3 cases in JPED until they can be ‘dismissed’.
JPED does not demand a terrorism verdict. A verdict strengthens reliability, but failure to reach a verdict does not necessarily mean an attack was not in the making. Terrorism laws vary between countries and over time to deal with evolving threats. For a dataset designed to capture trends in terrorist attack activity it makes sense to include based on what was revealed during investigations rather than applying a legalistic principle.
Another exception from the main coding rules is that a small number of plots have been coded C2 rather than C3 even though we lack information about the target type and preparations. This is done when authorities firmly declare an attack was in the making, and link the case to well-known terror networks. One example is the 2016 detection of an IS ‘sleeper cell’ in Germany (Eckardt, 2016). No evidence was released to the media concerning the type of attack and target, but German authorities maintained that the plotters had received training, travel documents, money and communication apps from IS in Syria, and were waiting for attack orders. They also announced that the plotters had ‘overlapping relationships’ with a well-known IS network behind multiple attacks. The case was coded C2 because the statement from German authorities and the context of the plot trumped lack of details surrounding the attack plan. We argue that such judgement calls are justifiable when looking at democratic states, but less so in authoritarian systems. Challenges of ensuring reliability adds to the labour-intensiveness of maintaining a plot dataset and helps explain why such datasets are rare.
Limitations
JPED provides a fuller picture of the jihadi threat to Europe than we can glean from attack data. Yet despite our efforts to secure reliability, data on foiled plots involve more uncertainty than attack data. As noted, there may also be dark figures (probably limited) concerning unknown potential plots.
The inclusion of data on foiled plots primarily implies a risk of over-reporting attack activity. By employing strict inclusion criteria this risk is mitigated. We posit that some level of over-reporting is less of a problem than a high level of under-reporting when it comes to measuring terrorism.
As we cannot record unknown potential plots we also risk under-reporting terrorists’ capability to recruit potential plotters as well as security services’ capability to intercept potential plotters. We contend that this risk of under-reporting is limited because security services have strong incentives to show the public what they manage to prevent. We acknowledge this measurement problem in plot research.
Existing data
Quantitative studies of terrorism apply attacks as metric and ignore foiled plots. The databases used in most quantitative studies, the Global Terrorism Database (GTD) and the International Terrorism: Attributes of Terrorist Events, never included foiled plots (LaFree & Dugan, 2007; Mickolus et al., 2021). GTD records ‘failed attacks’ according to an ‘out-the-door-principle’ (GTD, 2019). This includes when perpetrators are intercepted en route to their target. GTD does not record plots that were intercepted before the plotters moved in on their target. The number of Islamist attacks in Western Europe from GTD corresponds roughly to the number of launched plots in JPED. 3
Security services consider foiled plots (e.g. PST, 2020), but rarely share data . Europol presents data on foiled plots in their T-Sat report (Europol, 2020). This report emerged in 2007. T-Sat’s inclusion of foiled plots has not been systematic.
Before the mid-2000s qualitative terrorism research examined foiled plots in types of terrorism where few attacks materialized, such as chemical, biological or nuclear (CBRN) terrorism (Tucker, 2000) or maritime terrorism (Jenkins et al., 1983). From the mid-2000s qualitative research on jihadism began examining foiled plots (e.g. Sageman, 2004). From the mid-2010s research on jihadi and right-wing terrorism employed mixed methods on samples of foiled plots (Nesser & Stenersen, 2014; Gruenwald, Freilich & Chermak, 2019). This research focused on modus operandi and countermeasures.
Qualitative research (e.g. Inserra & Phillips, 2015; Bergen et al., 2020) has produced data mainly in the form of incident lists. These studies typically focus on one type of terrorism (e.g. jihadism), in one region (e.g. the USA), in a limited time interval.
We are only aware of three tabulated ‘plot datasets’ like JPED which systematically include foiled plots and code for multiple variables, multiple countries and multiple years: the POICN dataset (CBRN incidents worldwide by non-state actors 1993–2017; Binder & Ackerman, 2021), the RTV dataset (right-wing violence in Western Europe since 1990; Ravndal, 2016) and a dataset by Crenshaw et al. (jihadi plots in NATO, EU, Australia and New Zealand 1993–2017; Crenshaw, Dahl & Wilson, 2017).
These datasets employ similar collection methods to JPED, but differ in focus, scope, inclusion criteria and coding (Online appendix 2). RTV and POICN are wider in scope than JPED, but focus on different actors and types of incidents. RTV records all types of severe violence by right-wing extremists, whereas POICN records only CBRN incidents.
Variables
Average deaths and injuries
Lethal attacks
Variables
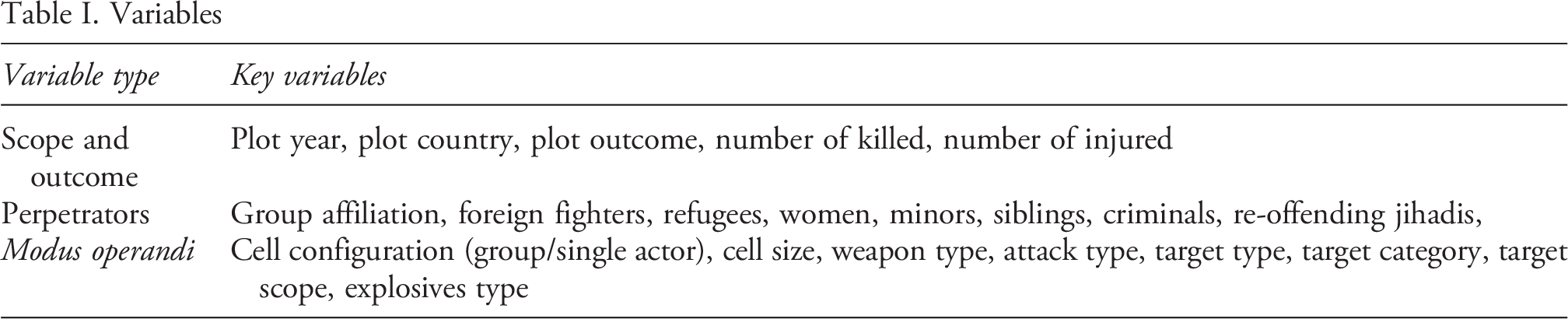
There are three types of variables in JPED (Table I). One type addresses the scope and outcome of plots. Another describes the attributes of perpetrators. The last type pertains to the modus operandi, including weapons, tactics and targets. Variables, values and coding rules are explained in the codebook.
Examples on usage
JPED can be used for description, comparative and causal analysis. We now offer examples on what we can learn from incorporating foiled plots when studying the scope, nature and drivers of terrorism. In the following, statistics on ‘all plots’ represent what extra information can be gleaned from foiled plots, compared with looking at launched attacks only.
Scope and outcome
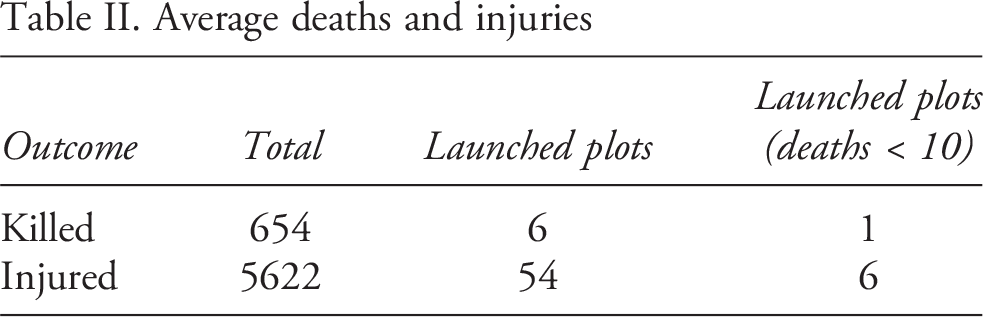
JPED contains 381 observations. A total of 249 cases are sufficiently documented (C1 and C2) for meaningful analysis. Of the 249 observations, 104 (41.8%) are launched and 145 (58.2%) are foiled. The 104 launched plots have caused a total of 654 deaths and have injured 5622. On average the 104 launched plots killed 6.3 people and injured 54.1 (Table II).
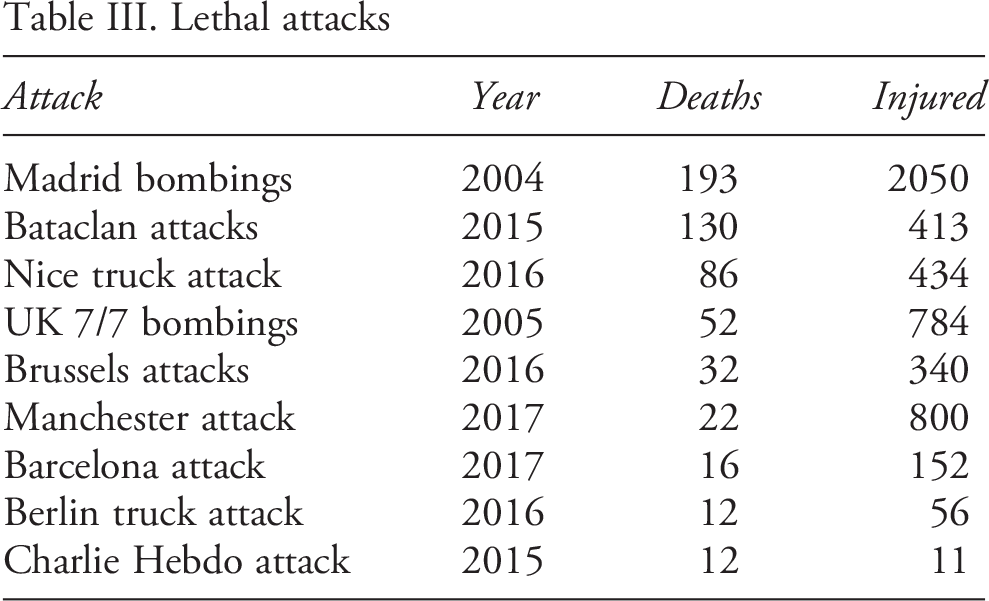
Of the 104 launched plots, 59 did not cause casualties, giving a wide range (193). The average is driven up by nine mass casualty attacks that killed more than 10 people, four of them killing more than 50 (Table III). If we only count plots that killed fewer than 10, the average drops to 1. Owing to the mode being zero and the wide range, the median number of people killed in launched plots is 0. The median number injured is 2.
Estimated deaths for foiled plots are rare, although some exist. For example, in the trial against the perpetrators of the failed 2006 Cologne train bombings, the prosecution estimated that 72 people could have been killed (BBC, 2008). In the case of Al-Qaida’s 2006 plot to bomb trans-Atlantic airliners departing from the UK, investigators estimated that 1,500 would have perished (Dodd, 2009).
An overview of foiled vs. launched plots over time (Figure 1) shows that attack activity is persistent since 1994, and fluctuates. We see a spike in 1995 when the Plots per year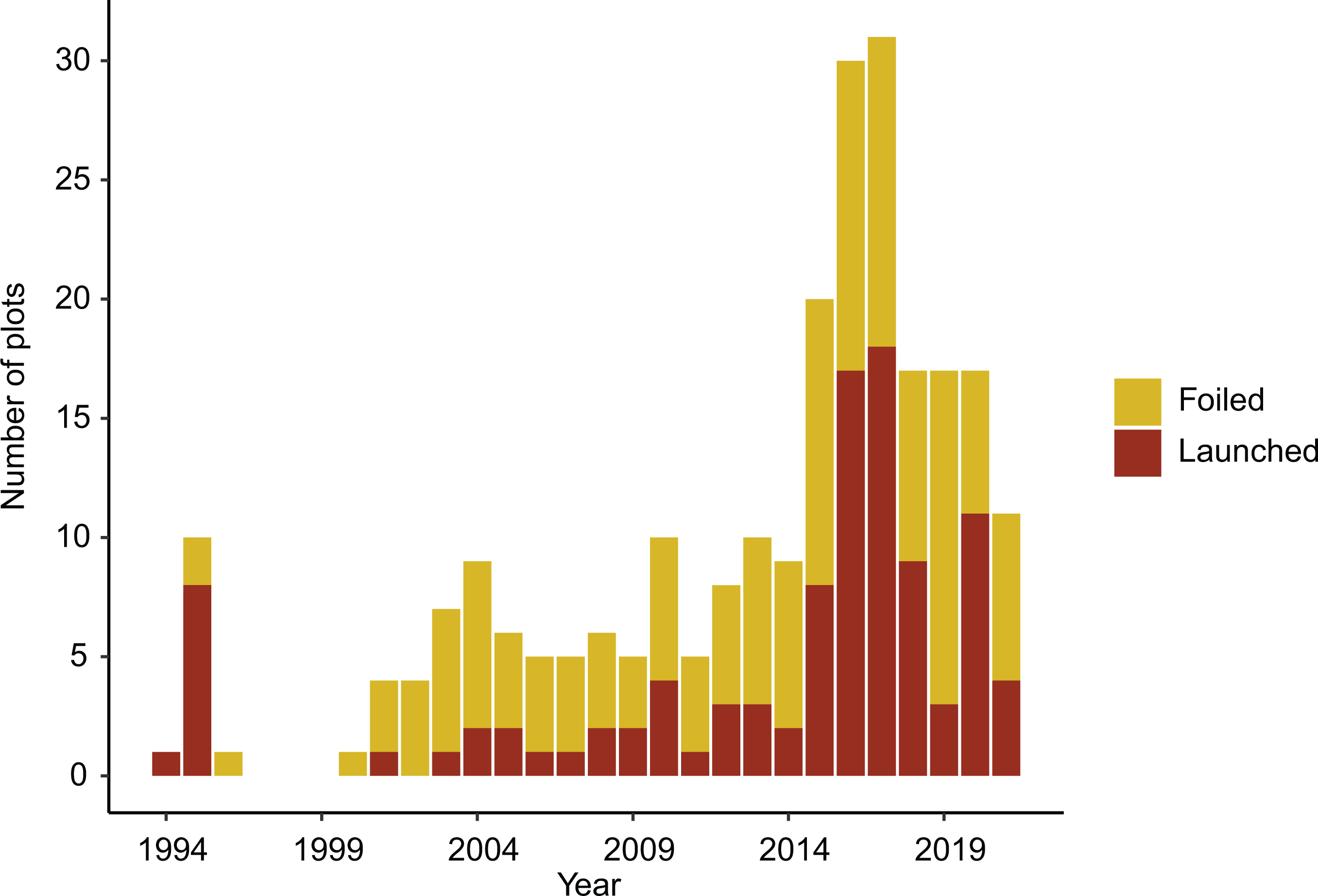
If we look at variation between countries (Figure 2), we see how France, the UK and Germany face the highest threat, but that the threat affects the whole region. The data further show how a higher proportion of plots gets launched in France and Belgium, compared with the UK, Germany and Italy, or the Nordic countries.
Plausible explanations for variations include the countries’ history with colonialism and policies towards Muslims, their history with Islamism, the size of their foreign fighter contingents, counterterrorism regimes, geography and factors such as the economy or immigration.
An overview of plots per country per year (Online appendix 3) shows how the threat grew increasingly transnational: starting out in France, before affecting central and southern Europe, then hitting northern parts from the mid-2000s. The threat to Nordic countries started with the 2005 publication of the Mohammed cartoons in Denmark. The Danes experienced a string of plots during the ensuing years. France experienced relatively low levels of plotting in the mid-2000s, compared with Britain. One possible explanation is that France did not join the US-led coalition invading Iraq in 2003.
Perpetrators
Because of debates over the alleged threat from foreign fighters, women and children, converts, refugees, criminals or re-offending terrorists, we added dummy variables for the involvement/non-involvement of a minimum of one person from each category. JPED defines a foreign fighter as someone who joins a jihadi conflict in a third country (Online appendix 1). When assessing the threat from different perpetrators, we need to factor in how plots involving certain categories are foiled at a higher rates. Table IV shows the number and percentage of plots for each type, and the number and percentage foiled per category.
Foreign fighter appears frequently in plots, but these plots are foiled at a high rate. Converts also appear frequently in plots, reflecting how jihadism is multinational. Some 51.2% of these plots get foiled. The involvement of refugees reflects the 2015 refugee crisis, and how jihadis exploited the situation. Fewer than half of plots involving refugees get foiled. Woman and Plots per country Perpetrator types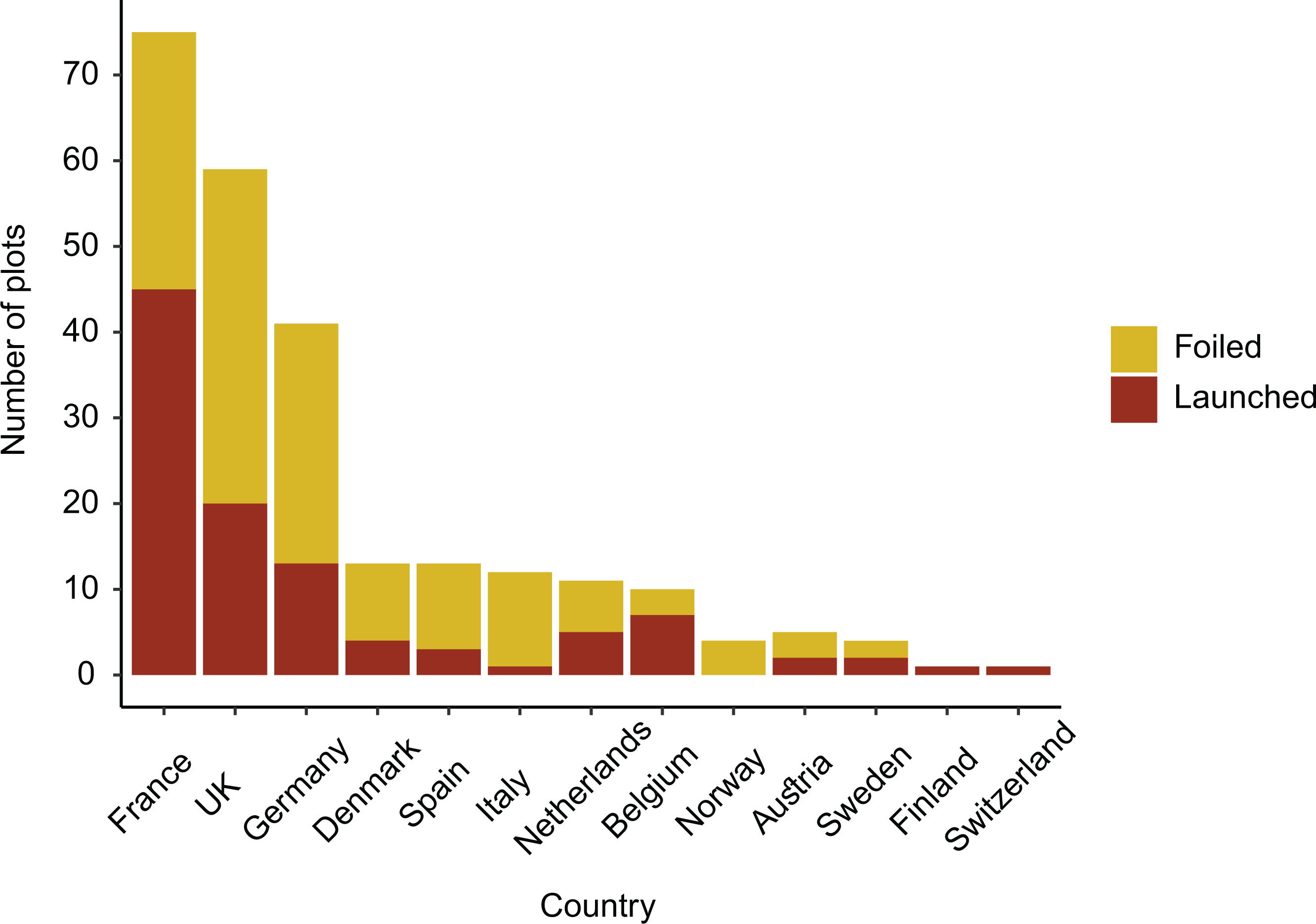
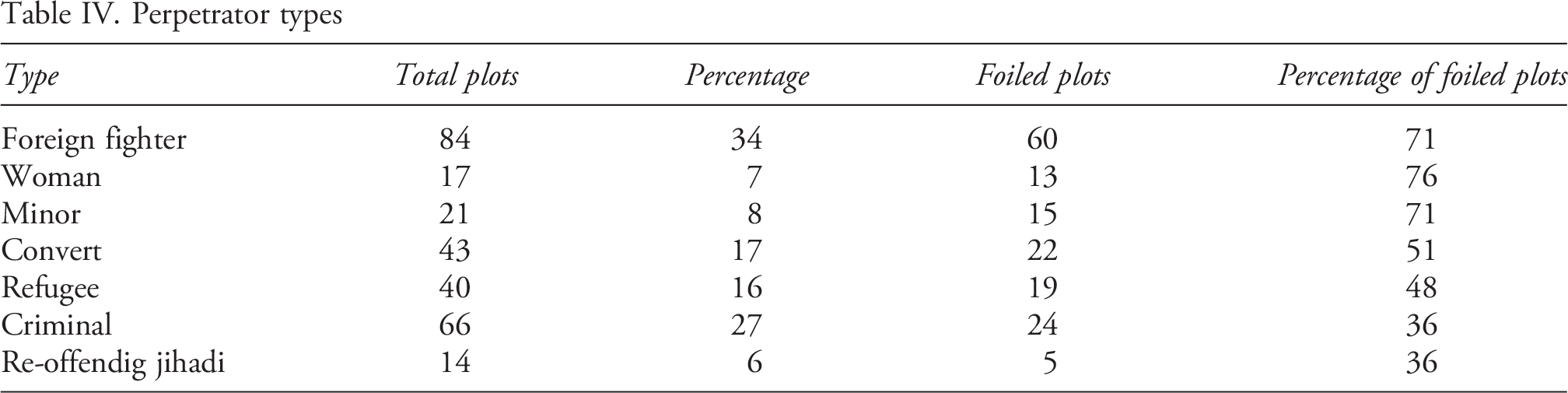
Foreign fighters
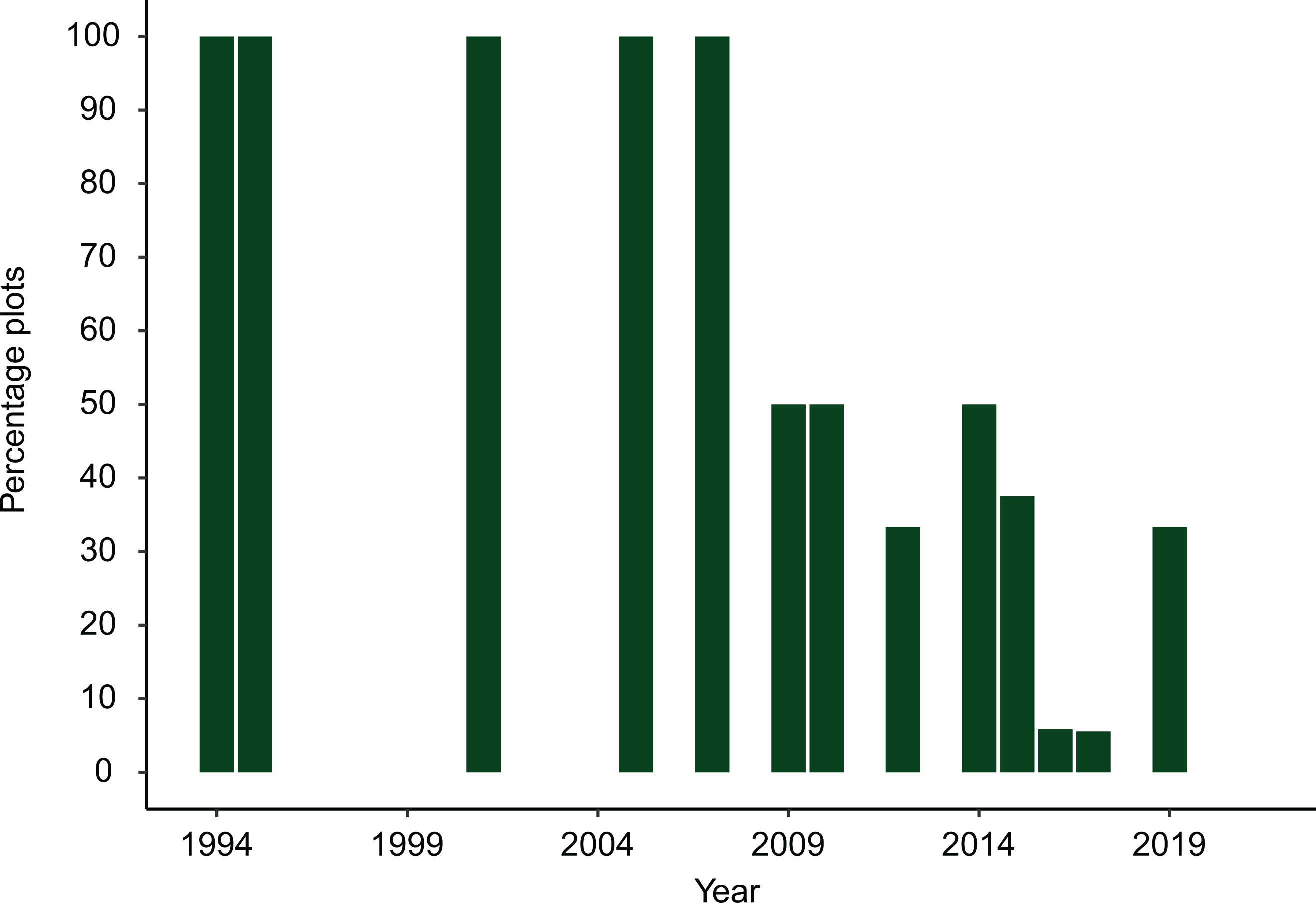
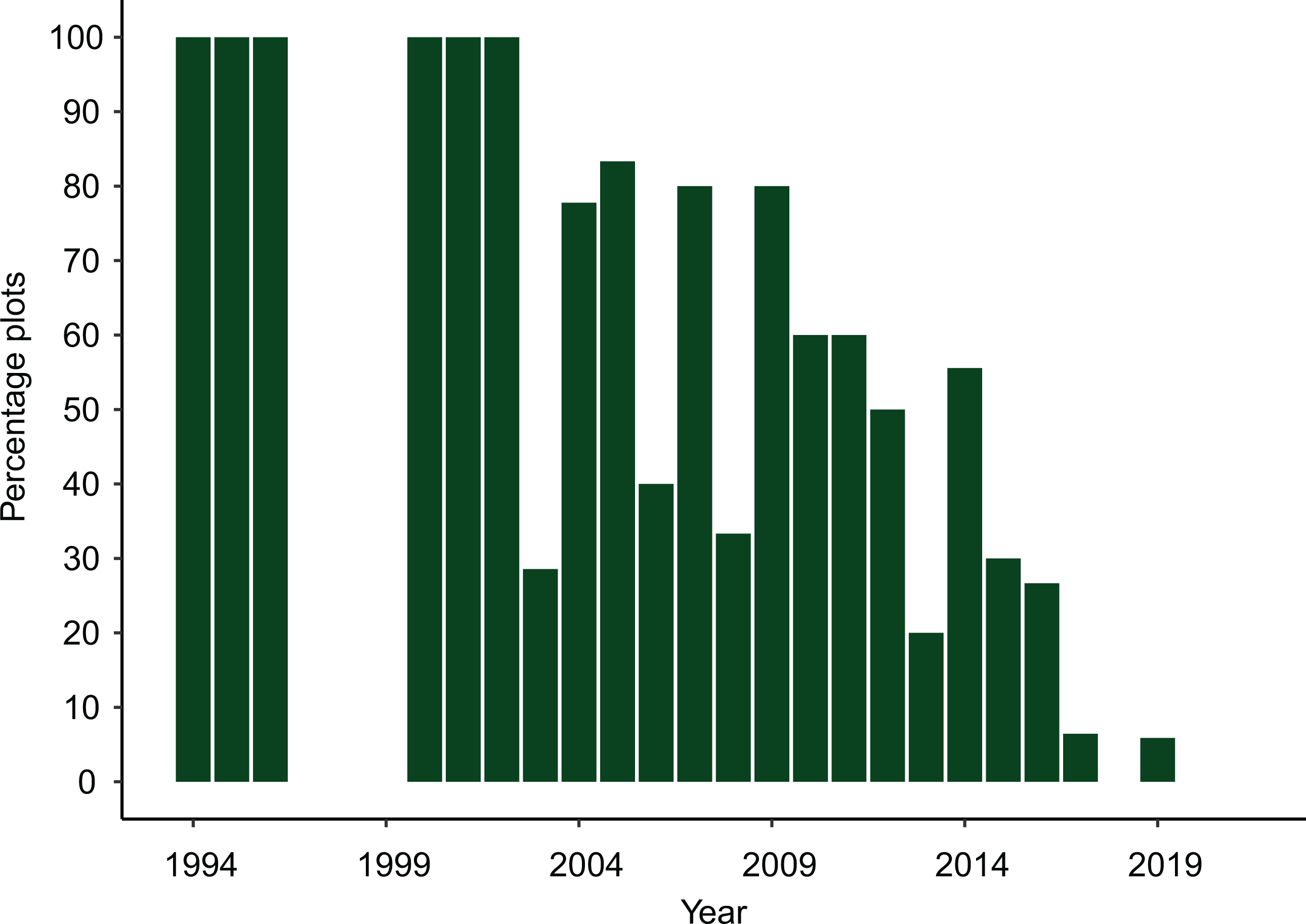
Foreign fighters played pivotal roles in European jihadism (Nesser, 2018). Foreign fighters participated in some of Europe’s deadliest attacks, such the 2005 London bombings or IS’s 2016 Brussels attack. Since the rise of IS, European states have stepped up their countermeasures against foreign fighting. This is reflected in the data.
Of 249 C1 and C2 plots, 84 (33.7%) involved at least one foreign fighter. The data measure direct involvement, i.e. that the foreign fighter physically joins a terror cell. In launched plots (Figure 3) we see a distinct pattern that Foreign fighter decreases over time and has been absent since 2019.
When we include foiled plots (Figure 4), the decrease is much less pronounced. Cells with foreign fighters are an important part of the European threat matrix. The difference between launched and ‘all plots’ reflects how European security services prioritize the foreign foreign fighter threat. Some 71.4% of plots involving foreign fighters are foiled, and the foiling rate increases over time.
However, direct involvement does not represent the whole story of how foreign fighters shape the threat. Since the rise of IS, there have been multiple examples of foreign fighters instructing plotters in Europe from conflict zones, via communication apps. Such ‘virtual entrepreneurs’ have become part and parcel of international terrorism and are registered in JPED (Meleagrou-Hitchens & Hughes, 2017).
Foreign fighter – launched plots
Foreign fighter – all plots
9.3 Modus operandi
We now turn to how the terrorists have operated and look at cell configuration and attack type.
Cell configuration
Cell configuration measures whether perpetrators operate in groups of two or more, or as single actors. Data on launched plots (Figure 5) show a clear trend towards single actors. While group plots dominated in the 1990s and 2000s, single actors have become most common. Since the collapse of IS, there have not been any attacks in Europe by groups.
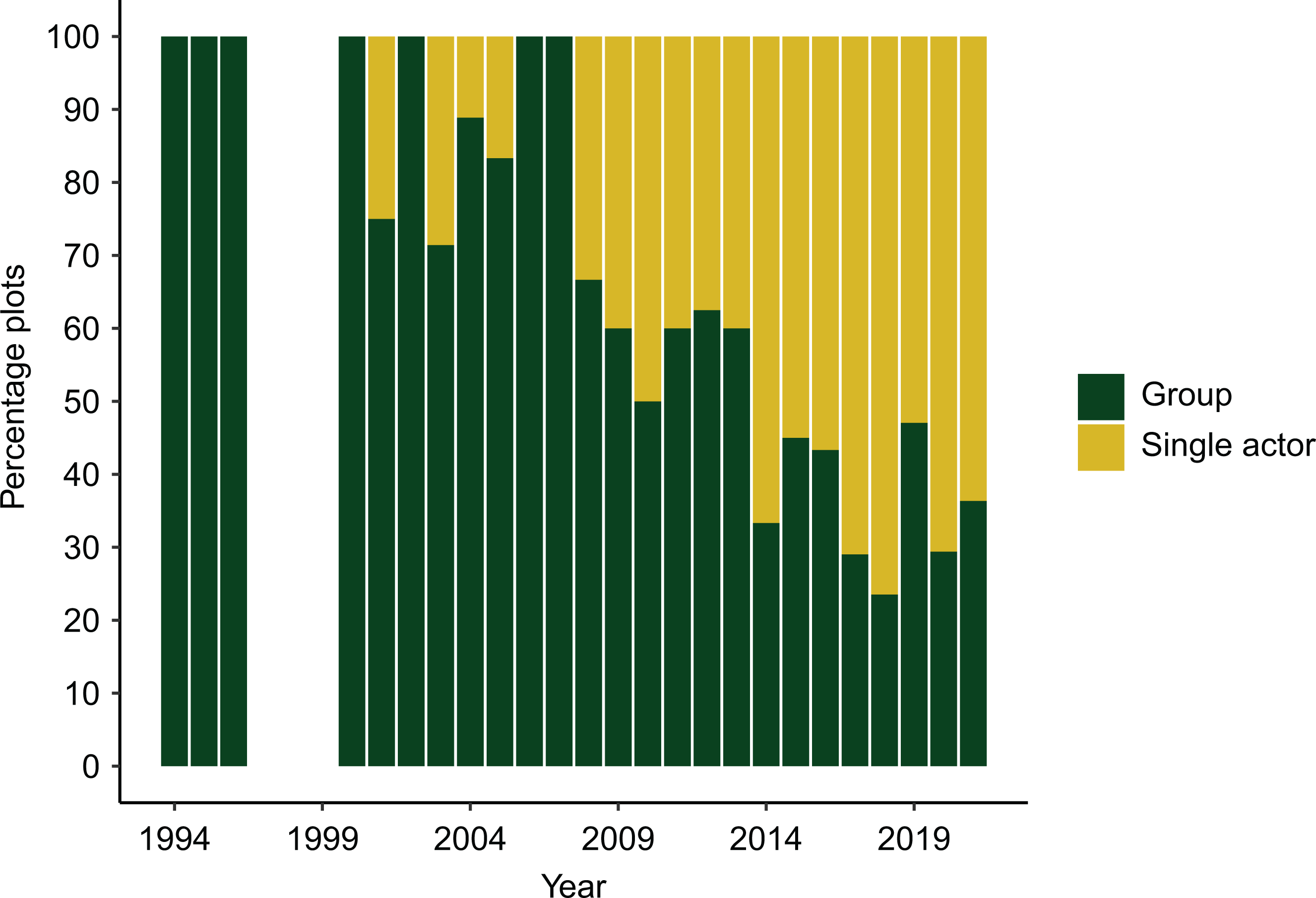
In ‘all plots’ (Figure 6) we see a different picture. The data indicate that jihadis prefer to operate in groups. The terrorists continue to plot attacks as cells, composed of two or more. This, despite the fact that as many as 79.8% of group plots get foiled.
Attack type
In launched plots (Figure 7), armed assaults (with hand-held weapons such as guns or knives) dominate
Cell configuration – launched plots Cell configuration – all plots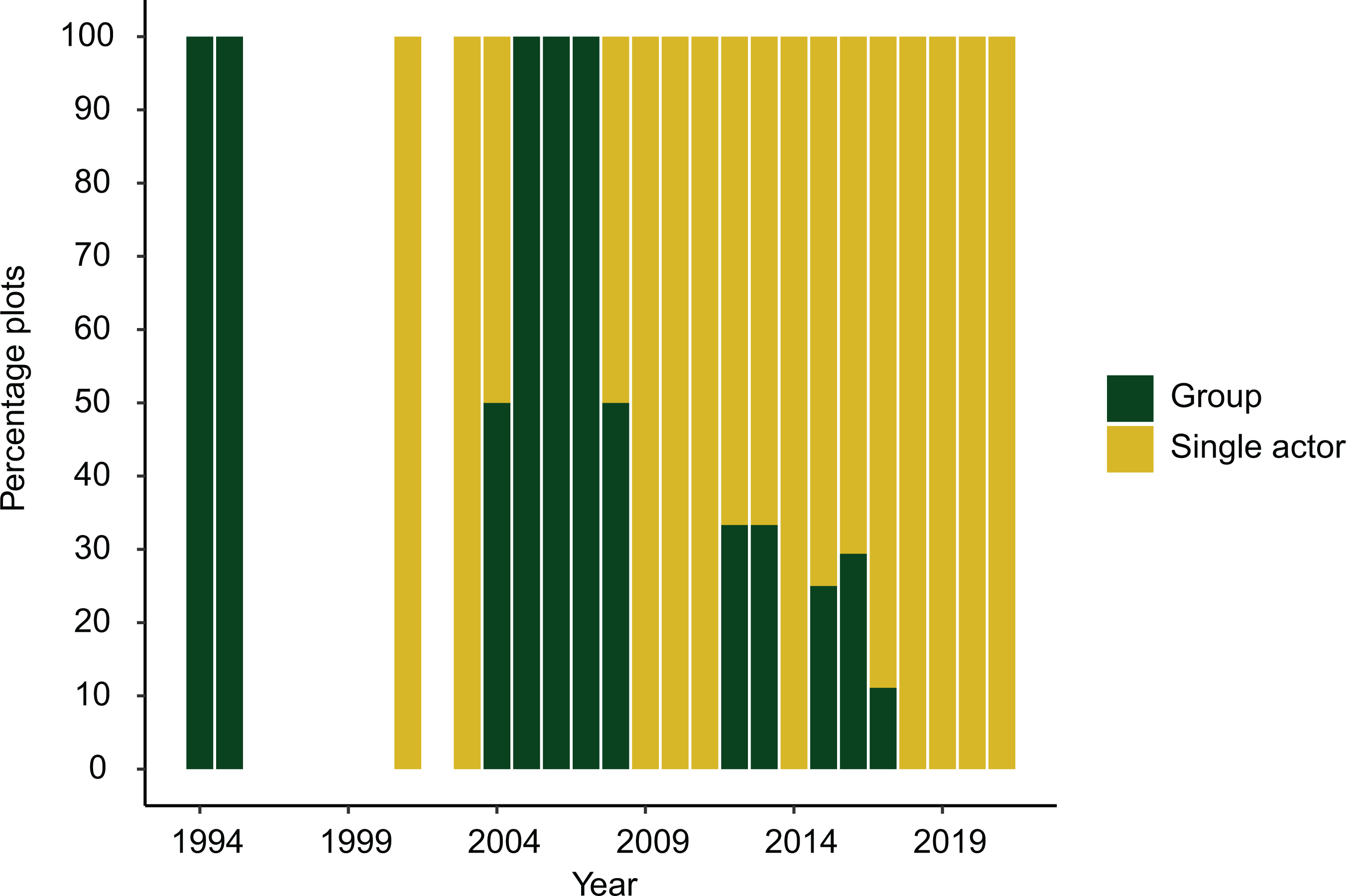
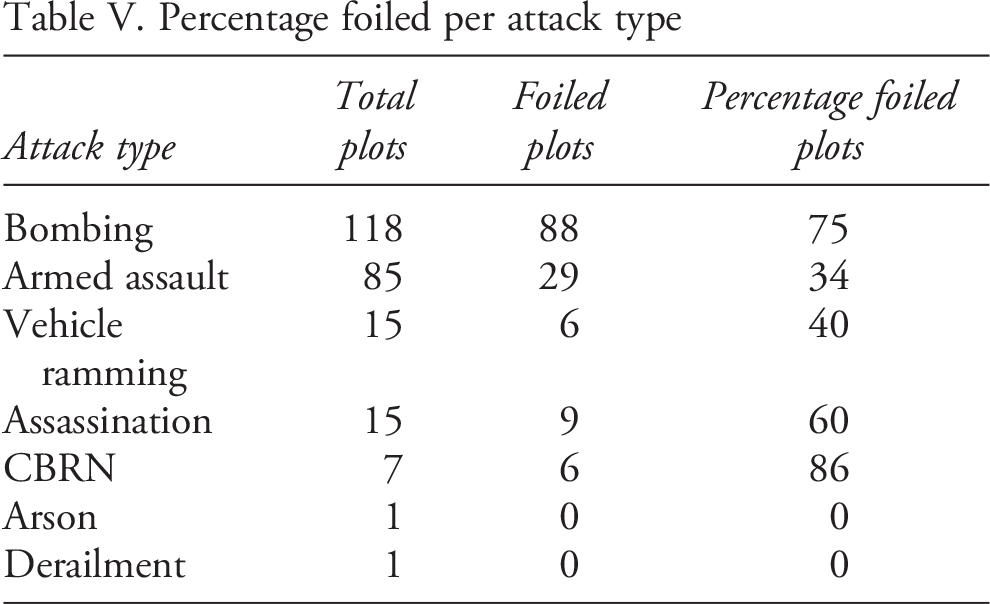
As can be read from Table V European counterterrorism has been effective at foiling bombing plots.
Therefore the trend towards armed assault is probably not by choice, but a tactical adaptation. Data presented in Figure 8 indicate that jihadis prefer to launch bombing attacks if they can avoid detection.
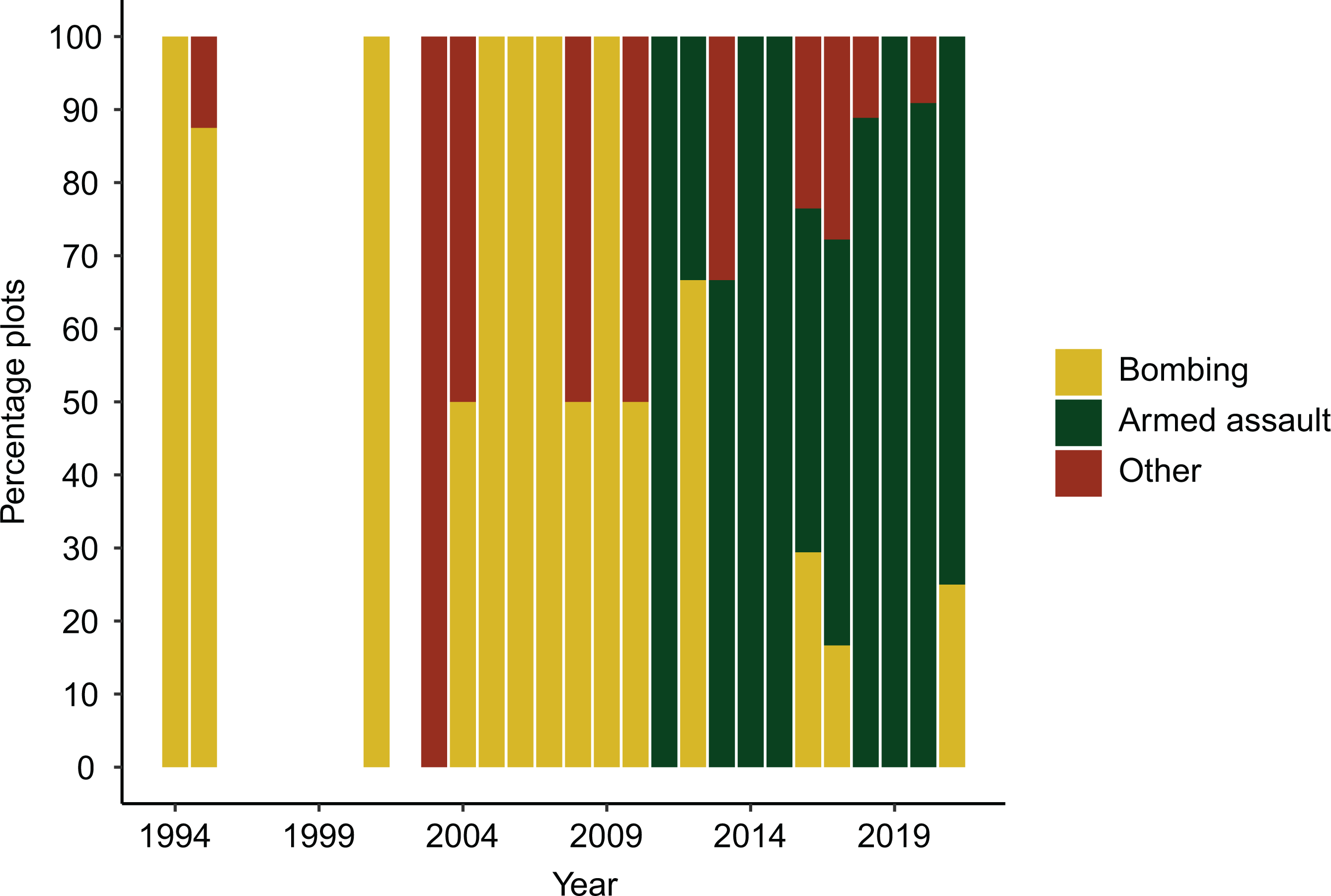
Figure 9 shows the trend in the proportion of bombing vs. armed assault in launched plots, and how the latter surpasses bombing in the 2010s.
Figure 10 illustrates how bombing plots dominate ‘all plots’. Jihadis persist in plotting bombings in Europe, but these plots tend to get foiled.
Comparative and causal analysis
A valid comparison of the terror threat from different actors (e.g. jihadi vs. right-wing), requires similar datasets including launched and foiled plots, based on similar
Attack type – launched plots Percentage foiled per attack type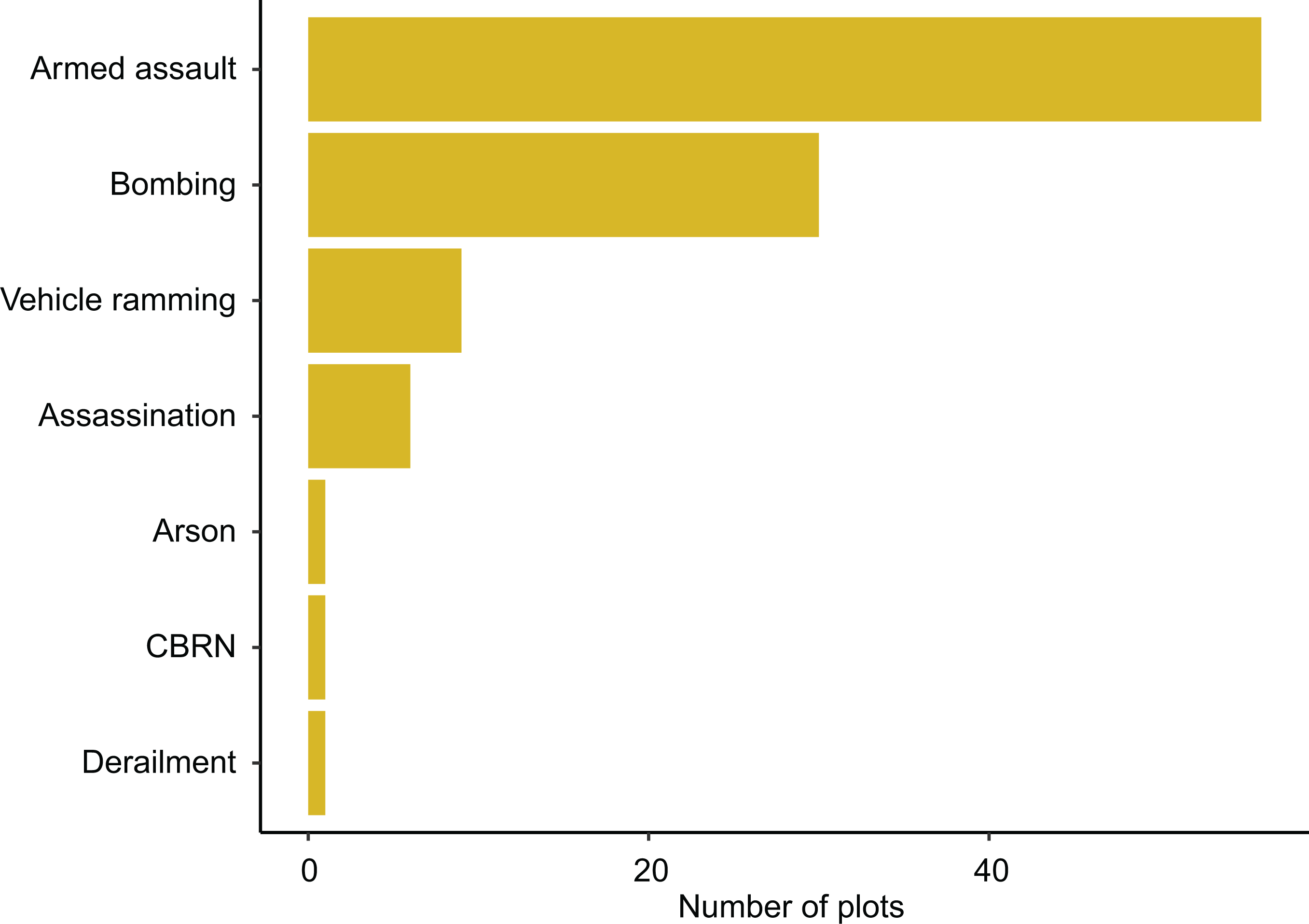
JPED also illustrates the importance of including foiled plots in cross-country comparisons. For example, if we operationalize terrorism as attacks, the jihadi threat to France is 125% higher than that in the UK. If we include foiled plots, the difference is 27.1%. Terrorist attack activity in France and the UK is more similar than the attack count suggests because the UK’s foiling rate is 66.1% against France’s at 40%.
A focus on attacks could cause problems for causal analyses. For example, the high number of attacks in France has led some to hypothesize that the French approach to Islam (secularism/assimilation) is the driver (McCants & Meserole, 2016). Such a hypothesis seems plausible in light of the fact that the UK pursues the opposite policy of multiculturalism, and experiences far fewer attacks. When we include foiled plots, however, the basis for the hypothesis becomes weaker.
In a forthcoming study, Hegghammer & Ketchley (2020) use JPED in combination with other datasets to show how one gets statistically significantly different results when measuring the effects of variables such as economic factors, demographics, state characteristics, political grievances and events on the incidence of terrorism operationalized as attacks vs. plots. This finding potentially challenges results from quantitative terrorism research using attacks as the dependent variable.
Conclusion
This article introduced the JPED, which records data on launched and foiled terror plots. The data can be used to gauge patterns in scope and modus operandi, and conduct comparative or causal analyses. Measuring terrorism operationalized as attacks risks misjudging the scale, nature and causes of terrorism. If we were to measure the jihadi threat to Europe by attacks, we would ignore 58.2% of the total attack activity.
If we counted attacks only, the European jihadi threat would seem smaller than it is, at a juncture when European states prioritize jihadism. By ignoring foiled plots we may misinterpret trends in modus operandi, as they Attack type – all plots Trend in attack type – launched plots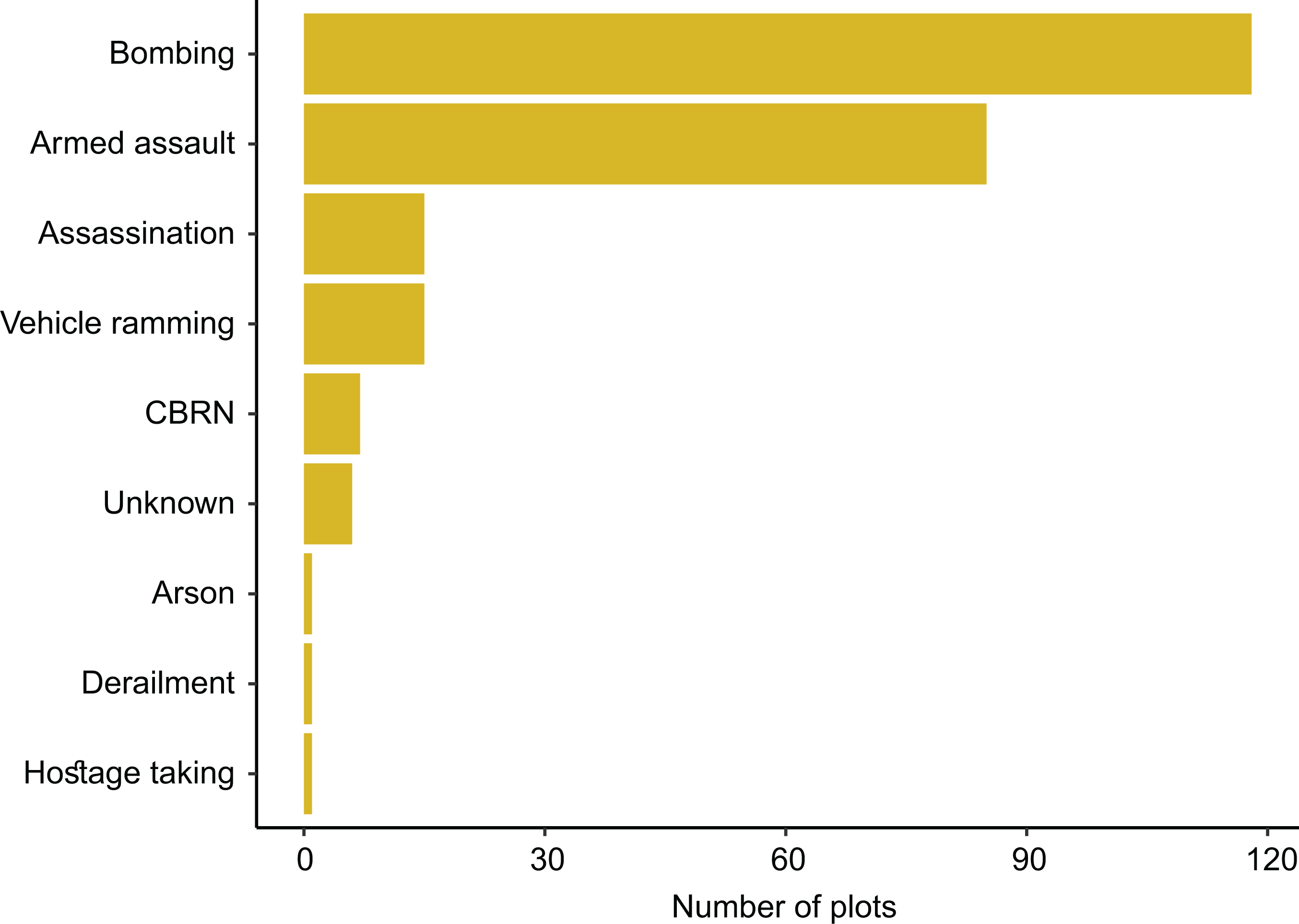
Counterterrorism is not constant. States must tackle multiple security challenges and prioritize resources. If jihadism were down-prioritized, more attacks would materialize. Some of these could be large scale, perhaps of a magnitude that could increase polarization or trigger war. Effective counterterrorism depends on an accurate understanding of the threat. Such an understanding is only possible if we consider foiled plots. If we fail to do so we may end up with countermeasures incapable of mitigating tomorrow’s threat. As research influences policy, quantitative terrorism studies should include foiled plots and strive to build ‘plot datasets’ for all types of extremism.
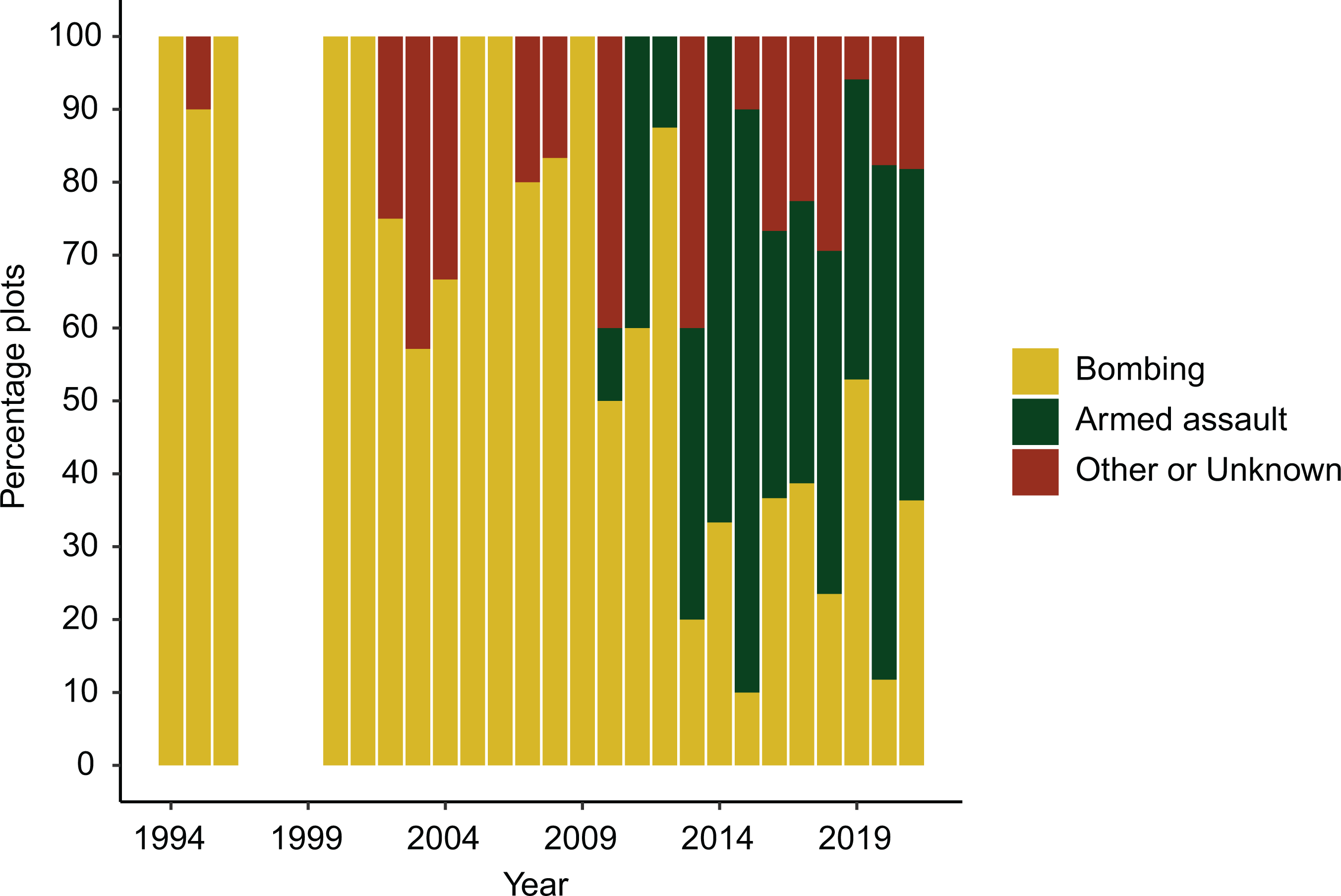
Trend in attack type – all plots
Footnotes
Acknowledgements
I thank Thomas Hegghammer, Anne Likuski, Vidar Skretting and Henrik Gråtrud for key contributions to JPED. I thank the JPR editors and reviewers for valuable input. The research was funded by the FFI.
