Abstract
How should we measure terrorism? Political scientists typically use executed attacks as the dependent variable and test covariates to identify factors that produce terrorism. But attacks are an imperfect measure of terrorist activity because of ‘plot attrition’ — the tendency for plots to derail due to police intervention or other factors. We examine whether the exclusion of foiled plots from event datasets constitutes a measurement problem in terrorism studies. Building on recent advances in plot data collection, we study the correlation between plots and attacks and conduct an original analysis of jihadism in Europe. Our results suggest common research designs predicting terrorism can produce different results depending on whether incidents are operationalized as plots or attacks. Adjusting for state security capability does not solve the problem. Despite its limitations, plot data is a more complete measure of terrorist activity that should be incorporated, when available, in quantitative studies of terrorism.
Keywords
Introduction
In early September 2006, within the space of 2 hours, five airplanes blew up mid-air over the Atlantic, killing over 1300 people. Days later, the militant Islamist group al-Qaida released a video claiming the attack and showing footage of the perpetrators in training. The events triggered an economic recession in Europe and ushered in a new, uglier phase in the post-9/11 War on Terrorism.
This attack never happened. But it could have, because in 2009, four men were sentenced in a British court to life in prison for having attempted it. Surveillance and searches showed the men to have been in possession of explosives, to have recorded martyrdom videos, and to have identified seven U.S. and Canada-bound flights for their operation (Cruickshank 2014; Nesser 2018, 190-198). They had devised a new technique to get bombs on airplanes: bring the ingredients in soda cans and assemble the device onboard after takeoff. This one plot is the reason why you still cannot bring liquids in containers of more than 100 mL on an airplane.
If we wanted to assess the terrorist activity level in Europe in the mid-2000s, it would make sense to take the 2006 Airliner Plot into consideration. However, because it did not reach execution, it does not feature in the terrorism event datasets that academics use to study terrorism quantitatively. In this article, we ask whether it matters for our knowledge about terrorism that near-misses are excluded from event datasets.
Counting attacks seems like a sensible and uncontroversial approach to measuring terrorism. But attacks are only the subset of terrorist activity that happen to reach execution. Many plots are foiled by police or derail for other reasons, never to enter terrorism datasets. In the following, we build on recent advances in plot data collection to conduct the first systematic examination of this potential measurement problem. We show that, while the incidence of plots and attacks are often highly correlated, they differ enough to potentially produce statistically different results in common study designs. Answers to the question “what causes terrorism” can therefore vary depending on how one operationalizes terrorist activity.
The inquiry matters because attack counts are central to the study of terrorism. A large proportion of quantitative studies on terrorism measure terrorist activity in executed attacks or their derivatives (such as casualties). The most widely used dataset by far is the Global Terrorism Database (GTD) (LaFree and Dugan 2007), which is explicit about only including attacks. 1 The other main terrorism dataset, ITERATE (Mickolus et al. 2022), includes foiled plots, but registers so few that it is arguably an attack dataset in practice. 2 GTD alone underpins thousands of studies into the causes and consequences of terrorism. 3 The accuracy of this knowledge hinges on executed attacks being a reasonably valid measure of terrorist activity.
Scholars have studied foiled plots, but not their statistical dimensions. The literature on plots has focused on the history of specific groups (Nesser 2018), the features of the plot preparation process (Cothren et al. 2008; Kaplan 2012; Gruenewald et al. 2019) and why some plots fail and others succeed (Gruenewald et al., 2019; Jackson and Frelinger, 2009; McCleskey et al., 2007; Strom et al., 2010). Several researchers have noted that attacks can misrepresent terrorist activity (Sageman 2009, 5; Crenshaw and LaFree 2017, 69), but the broader epistemological implications of this observation have not been explored. Meanwhile, the literature on measurement problems in terrorism research has barely noted the concern raised by foiled plots (Mickolus 2002; Young and Findley 2011; Sheehan 2011; Freilich, Chermak, and Gruenewald 2015; Dugan and Distler 2016; Freilich and Lafree 2016).
This article is the first to systematically examine the statistical relationship between plots and attacks. While some of the abovementioned studies have explored this relationship for small incident samples, we examine all the available multi-year and multi-country plot datasets in the hope of extracting more generalizeable insights. To do this, we exploit recent advances in plot data collection that provide fine-grained data on plots by jihadi groups in the West and on chemical, biological, radiological and nuclear (CBRN) plots worldwide over the last quarter-century. We then conduct two tests: first, we study the association between plot and attack counts in all the datasets across different temporal units and functional forms; second, we set up a plausible study of jihadi terrorism in Europe and compare how covariates of theoretical interest predict the incidence of plots and attacks. Our objective is to establish whether the correlates of plots are statistically different from the correlates of attacks in country panel studies of terrorism.
We find that they are. While the correlation between plots and attacks is relatively high, it varies across different units of analysis and functional forms. More importantly, we get statistically different estimates across a range of covariates when predicting the incidence of jihadi terrorism in Western Europe, depending on whether we use plot or attack data as the outcome. This is after adjusting for security spending, suggesting that there is no modelling quick fix to the measurement problem. Finally, we show that if scholars want to study the incidence of terrorist attacks, they should consider a two-step process that takes into account the number of plots that failed. Taken together, the findings suggest that plots should be taken seriously as a measure of terrorist activity and that political scientists studying other phenomena should pay attention to precursor events.
Conceptual Framework
We start by specifying the conceptual relationship between plots and attacks. Since our perspective is new, we describe what we see as the prevailing approach to terrorism measurement before presenting our alternative framework.
The Standard View: Terrorist Activity as Attacks
Political scientists have searched for the causes of terrorism with quantitative methods for over 40 years (Mickolus 1977). In the now substantial literature, the typical approach consists of examining the statistical relationship between theoretically relevant covariates and the incidence of terrorism.
Most studies examine country-level variables (Morris and LaFree 2017; Sandler 2014), and scholars have estimated the effect on terrorism of a long list of factors, notably
4
: • Regime type (Chenoweth 2013; Eubank and Weinberg 2001; Gaibulloev, Piazza, and Sandler 2017; Li 2005; Savun and Phillips 2009) • Demographics (Bove and Böhmelt 2016; Choi and Salehyan 2013; Helbling and Meierrieks 2020; Milton, Spencer, and Findley 2013) • Economic conditions (Blomberg, Hess, and Weerapana 2004; Caruso and Schneider 2011; Freytag et al. 2011; Keefer and Loayza 2008; Li and Schaub 2004) • Poverty and inequality (Abadie 2006; Enders, Hoover, and Sandler 2016; Franc and Pavlović 2023; Krueger and Malečková 2003; Piazza 2006) • State capacity (Coggins 2015; Dreher and Fischer 2010; Danzell and Zidek 2013; Daxecker and Hess 2013; George 2018; Lai 2007; Newman 2007; Piazza 2008; Tikuisis 2009) • Domestic policy (Burgoon 2006; Koch and Cranmer 2007; Walsh and Piazza 2010) • Political stability (Campos and Gassebner 2013; Fahey and LaFree 2015; Schumacher and Schraeder 2019) • Foreign policy (Kattelman 2020; Neumayer and Plümper 2009) • Culture (Böhmelt and Bove 2020; Gelfand et al. 2013).
The substantive findings in these works are numerous, and on any given topic there is a rich, nuanced, and sometimes contested literature. We choose not to summarise the substantive discussions here because our concern is not the findings themselves, but rather how scholars have been operationalizing terrorist activity.
The literature exemplified by this list is not marginal. Attack counting arguably represents the dominant approach to the study of terrorism in political science. Unlike qualitative studies, which tend to appear in specialist terrorism journals, country-year panel studies have featured in the leading journals of political science and economics and have attracted thousands of citations.
Practically all of these studies measure the incidence of terrorism in attacks only. They frequently refer to the dependent variable as “terrorism” — implying “terrorist activity” — but operationalize it exclusively as counts of executed attacks. Most do not control for measures of counterterrorism capacity, suggesting that plot attrition has not been a theoretical concern. The existing literature has effectively elided terrorist activity and executed terrorist attacks.
Moreover, the metrics used in many other quantitative research designs are derivatives of attack counts. Suicide terrorism, for example, is studied as a subset of executed attacks (Horowitz 2010; Pape 2003; Wade and Reiter 2007). Casualty counts are necessarily based on consummated attacks (Asal and Rethemeyer 2008; Sánchez-Cuenca 2009). Group-level tactical preferences are usually inferred from distributions of executed attacks (Brandt and Sandler 2010; Horowitz, Perkoski, and Potter 2018), and spatial diffusion of terrorism likewise (Polo 2020). Some studies that take individuals as the unit of analysis — to study what makes people become terrorists — also draw their sample from attack perpetrators (Lankford and Hakim 2011; Weinberg, Pedahzur, and Canetti-Nisim 2003).
Not all quantitative studies use dependent variables derived from attacks. Many individual-level studies examine group, movement, or plot participants (Bakker 2006; Cerina et al. 2023; Krueger 2007; Lee 2011), thus sampling beyond just attack perpetrators. Some country-level designs include terrorist group emergence (Chenoweth 2010) or group fate (Carter 2012) as outcome variables. But in the overwhelming majority of quantitative terrorism studies, the dependent variable is executed attacks or a derivative of it.
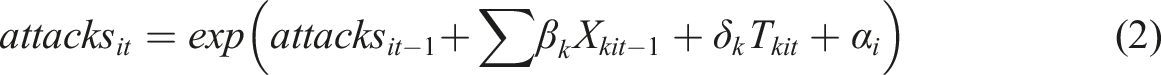
The existing approach to terrorism measurement is arguably based on an implicit understanding of a terrorism production chain with three ideal-type stations: causes, agents, and activity. First are the underlying causes, typically operationalized as societal features such as regime type or GDP. Second are the agents, who emerge due to the contextual factors and instigate the violence; they are usually studied through group traits such as ideology or organizational structure. Third is the resulting activity, nearly always operationalized as executed attacks. It is this last “activity box” that we wish to unpack.
Our Suggestion: Terrorist Activity as Attacks and Plots
We propose to widen the notion of terrorist activity to include both plots and attacks. Given the well-documented phenomenon of plot derailment, attack counts must underreport terrorist activity at least some of the time. We therefore suggest conceptualizing plots as an event type that can be used to measure terrorist activity alongside attack counts.
We posit that all terrorist attacks require at least some degree of preparation; i.e., that they are preceded by a process that takes an operational idea from the abstract to the tangible. At some point in the process, the operational plan will become sufficiently specific and viable to be considered a “plot”. A plot is an operational commitment developed enough to produce an attack absent subsequent external intervention.
Not all aspirations become executed attacks. A scaling off occurs, whereby some plans are discarded, prevented, or botched before reaching execution. Multiple factors contribute to the scaling off, but we distinguish between two ideal types of mechanisms – choices and externalities – and divide the production chain correspondingly into two stages. First is the selection stage, where terrorists evaluate operational ideas based on feasibility, discarding some and pursuing others. The latter become plots. Second is the attrition stage, where terrorists try to turn the plots into attacks, only to see some fail for unanticipated reasons, such as police intervention, technical problems, or mistakes. Figure 1 visualises our reconceptualization of the terrorism production chain. The terrorism production chain, disaggregated.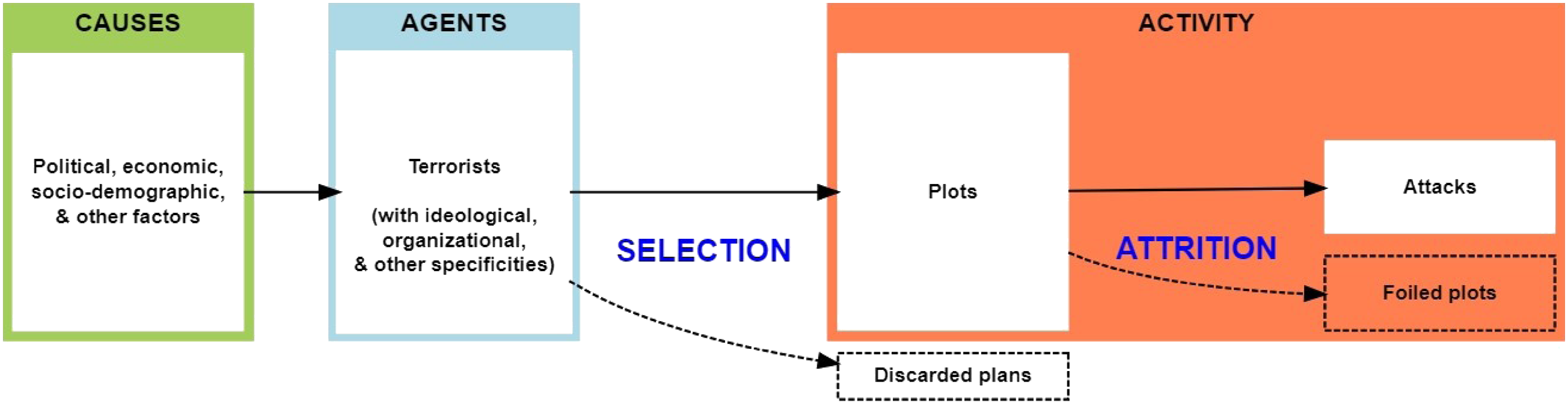
Plots are thus events on a par with attacks, but they provide a different measure of terrorist activity. Plot counts reflect the gross activity level, while attack counts measure the net. The gross level is of scientific interest because it represents the pre-treatment version of the phenomenon at hand. The net level, by contrast, has been reduced by counterterrorism and other intervening factors. Plots are not a perfectly pristine measure of terrorist activity, because terrorism is a strategic game in which countermeasures probably affect terrorists’ choices about which plots to pursue. Still, plot counts are less contaminated by intervening variables than attack counts.
Given that all attacks were once plots, we see no reason why plot counts would not be generated by the same causal processes — and thus be drawn from the same underlying distribution — as attacks. The only thing that distinguishes plot production from attack production is the late-stage intervening factors that foil plots. These intervening variables are of theoretical interest, but they can only be studied if we know the gross activity level. When we regress attack counts on broad country features such as GDP, as most studies do, we have no way of distinguishing between motivational and constraint-based determinants.
Note that we draw a distinction between plans (or aspirations) and plots. Plots are the subset of plans that are selected by terrorists for implementation. Discarded or abandoned plans are not plots by definition, and the causal process behind plans is likely different from that of plots and attacks. 5 This is not least because, in the plan-to-plot stage, state deterrence comes into play, bringing in a game-theoretic dimension to the decision-making. In the plot-to-attack stage, by contrast, only externalities affect the outcome. This article deals only with the plot-attack relationship, as the plan-plot relationship is more complex and requires separate treatment.
The factors that can derail plots are likely numerous and variable. This means we cannot assume that the relationship between plots and attacks is constant. In fact, existing data suggest the “plot attrition rate” – i.e., the percentage of plots in a given place-time unit that fail to reach execution – varies considerably. Crenshaw, Dahl, and Wilson (2017b, 34-35) found the attrition rate for jihadi plots in nine Western countries between 2010 and 2016 to vary between 38 and 89 percent across countries and between 47 and 93 percent across years. Strom, Hollywood, and Pope (2015, 8) found that, for terrorism in the USA from 1995 to 2012, the yearly attrition rate varied between 10 and 100 percent.
We currently know little about the determinants of this variation, and herein lies the potential for a measurement problem. If the rate varies in ways we cannot account for, then we cannot infer the gross activity level from the attack count. Glaciologists can predict the size of the submerged part of an actual iceberg (it is around ninety percent), but for our figurative icebergs, we do not know how much ice is below the waterline.
Plot Data
While the notion of plot may be conceptually intuitive, it is less obvious how it can be used to generate reliable data about terrorist activity. The fundamental problem is observability: while attacks cause physical damage in public, plots are unconsummated intentions. We contend that plots can still be observed because they need to leave the realm of thought in at least one of two ways: verbal articulation and practical preparation. We therefore operationalize the term plot as (1) a plan to deploy violence (2) of which a key feature has been verbally articulated and (3) for which observable preparatory steps have been taken.
In practice, it can be hard to identify plots consistently. Given the range of tactical possibilities in terrorism, there are no hard-and-fast rules for what constitutes a compromising statement or preparatory step, which leaves room for interpretation. Foiled plots attract less media attention than attacks, leaving less of a reporting trail for dataset-builders to follow, especially when the plot is foiled covertly and those involved do not go to trial. Public information on alleged foiled plot cases is vulnerable to biases such as media sensationalism and selective leaks from government investigators. In addition, national media might pay more attention to one type of terrorism than another depending on the political situation or the ideological leanings of the dominant media. One way of mitigating media bias is to include only plots that went to trial and resulted in conviction; this is the approach taken in the Crenshaw dataset (see below) and, with a few exceptions, in the Nesser dataset (also below). However, the availability of reliable case evidence depends on the existence of trustworthy police, independent judiciaries, and a free media. This means that in authoritarian countries, information regarding alleged plots should be treated with severe caution, and it is probably not possible to construct plot datasets for such countries at all. To these plot-specific problems must be added the general challenges faced by compilers of incident data, such as geographical and chronological reporting biases (more on this below). On the whole, there are unquestionably more potential sources of noise in plot data than in attack data.
We still argue that systematic plot data are not fundamentally elusive, just difficult to obtain. In some contexts, such as Western democracies in the digital age, the amount of open source information about political activism is so substantial that reasonably reliable plot data can be generated. But they are more labor-intensive to compile than attack datasets, and some areas and time periods might never be covered for lack of reliable sources. This is why existing plot data have tended to cover limited time periods and areas. 6
Recently, however, three larger and more comprehensive plot datasets have become available. These are Nesser’s (2023) data on jihadi plots in Western Europe 1994-2021 (henceforth “Nesser”), Crenshaw et al.’s (2017a) data on jihadi plots in the West 1993-2017 (henceforth “Crenshaw”), and the POICN (Binder and Ackerman 2019) dataset on CBRN plots worldwide 1990-2017 (henceforth “POICN”). Together, they form the universe of available plot datasets that cover multiple years and countries.
We consider all three datasets relatively reliable because they were compiled by academics who used largely the same procedures as other incident datasets and who discussed their inclusion criteria in depth (see Appendix Section 1 for details). We trust POICN despite its coverage of authoritarian countries because CBRN incidents attract special international scrutiny. The data generation process for plot data and attack data is the same as far as the collection procedure is concerned, although there may be slight differences in their respective sets of reporting biases.
We recognize that plot data are imperfect, but their flaws must be put in perspective. Global attack datasets are known to contain severe geographical reporting biases, yet scholars still use them. Behlendorf, Belur, and Kumar (2016) compared GTD data with local police data from a region in India and found that GTD recorded only two percent of the terrorist attacks recorded by police. A similar study on Turkey (Cubukcu and Forst 2018) found that GTD only contained three percent of the attacks recorded by local authorities. Whatever reporting biases exist in plot data from contemporary Western democracies, they are almost certainly less severe than this. And GTD contains other biases, too, such as that stemming from its particular definition of terrorism (Kaczkowski, Lokmanoglu, and Winkler 2022; McCann 2023) or the chronological one stemming from the switch to automated data collection in 2011, which led to a significant increase in globally reported incidents from 1 year to another (Jensen 2013).
In the following, we use Nesser, Crenshaw, and POICN to study the relationship between plots and attacks. Each dataset codes for execution, thus providing us with both plot and attack counts (see Appendix Section 3 for summary statistics). We examine the plot-attack relationship internal to each dataset and compare the results across them. 7 For all their limitations, these datasets offer the best available basis to explore the plot-attack relationship. As noted, there are no other reliable plot datasets covering multiple decades and countries, so our inquiry arguably exhausts the current possibilities for empirical testing.
The Relationship Between Plots and Attacks
We have suggested that attack data can underestimate terrorist activity. Given the difficulty of collecting plot data, the question is whether these two measures even out when many events are aggregated across space and time.
Figure 2 shows the relationship between plots and attacks when assigned to different units of analysis. We report associations as measured by both Pearson’s r and Spearman’s ρ. Aggregating to the country produces the strongest associations. Note, however, that the association between launched attacks and plots varies considerably when examining the across-country association on a year-by-year basis (see Appendix, Figures A4.1-4.3). We also find strong associations when aggregating to the year. This has positive implications for descriptive studies that aggregate attack counts to large geographic or temporal units. Bivariate correlations by units of analysis.
The relationship between launched attacks and plots is, however, attenuated when observing different countries over multiple units of time in a panel structure. When assigned to the country year, the typical observation in quantitative studies of terrorism, launched attacks and plots remain positively correlated, but the association is weakened. This is especially pronounced when measured using Spearman’s ρ, which does not assume linearity and is less sensitive to outliers. Disaggregation to smaller units of time attenuates the association further. Confining attention to Nesser and Crenshaw’s datasets, which allow for assignment to the country month, the association between plots and attacks remains positive, but is substantively diminished. Temporal disaggregation is important. Researchers often want to capture the effects of time-varying covariates — e.g., the impact of government policies at time t-1 on the incidence of terrorism at time t. But as our bivariate correlations show, attacks provide only a rough approximation of the intensity of terrorist activity in a country at a given point in time.
Another relevant consideration relates to functional form. Terrorism is a rare event: most countries will see few if any attacks or plots in a given year. In consequence, both launched attacks and plots follow heavy-tailed distributions: the modal observation is zero, while most events are concentrated in just a few units (see Appendix, Figure A5 for histograms). To minimize the influence of outliers, applied researchers often look to reduce the size of this tail by using different functional forms. Figure 3 shows how the association between launched attacks and plots in a country year varies by taking the square root and the inverse hyperbolic sine. The relevant comparison is the unbounded count of events in a country year reported in 2. In all three datasets, we see that reducing the influence of outliers further attenuates the association between plots and attacks when measured using Pearson’s r, as compared to an unbounded count. Applied researchers are also often interested in examining how the incidence of terrorism compares across spatial units that vary by population. Taking the per capita rate, we see that the correlation between launched attacks and plots is typically weakened across all three datasets. Bivariate correlations by functional form.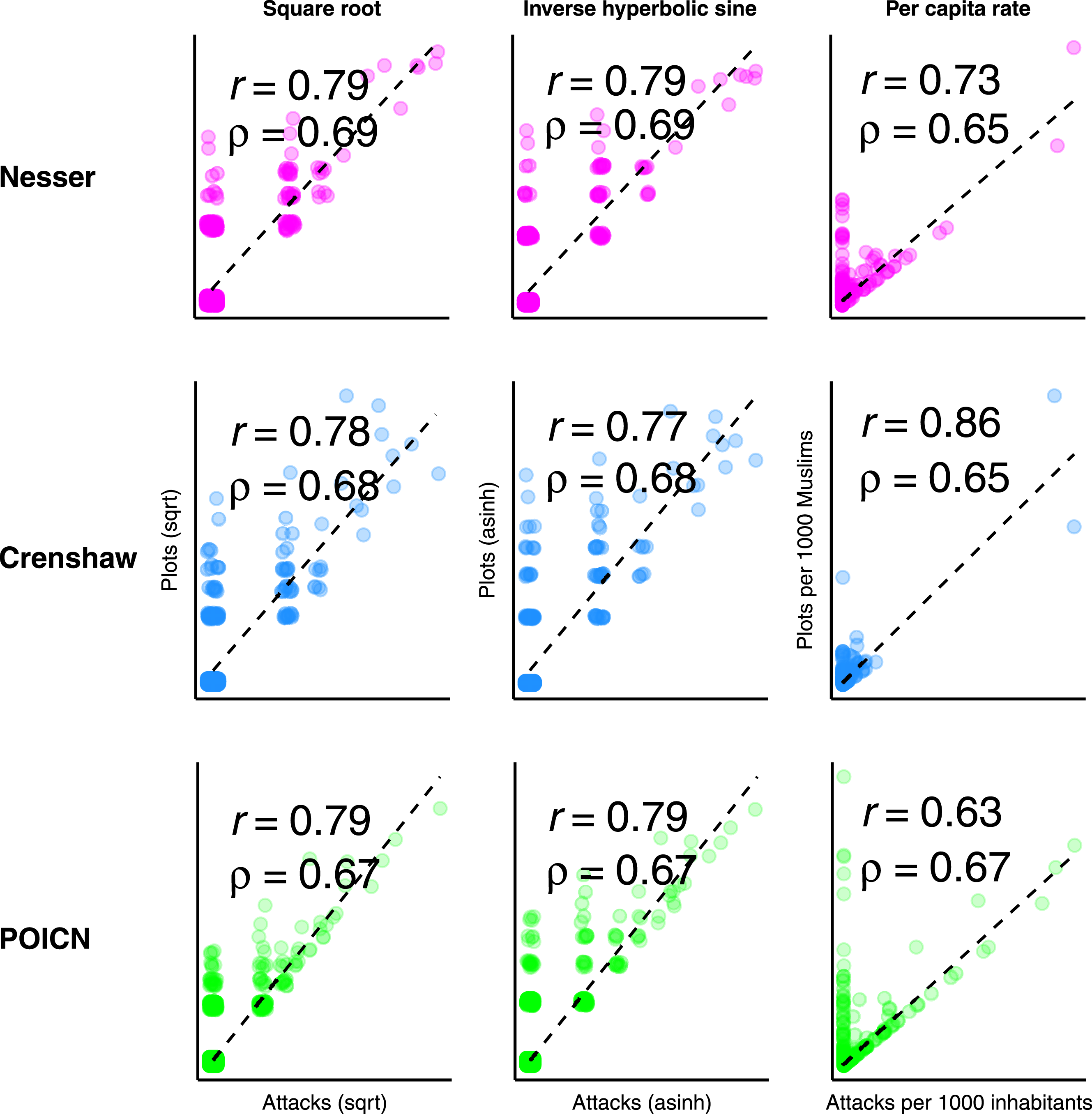
An alternative comparison examines the differences between launched attacks and plots when estimated as count processes. Here, the key statistic is the mean of the count of launched attacks and plots when assigned to their country year. Figure 4 provides an illustration, using the observed means and variance from our three datasets to simulate their respective Poisson and negative binomial distributions. While there is considerable overlap, taking launched attacks as the outcome measure will tend to overpredict the number of country years with zero instances of terrorist activity, and underpredict country years with one or more events. We examine this problem of excess zeros in a later section through a zero-inflated count process. Poisson and negative binomial distributions of expected counts (overlaid bars).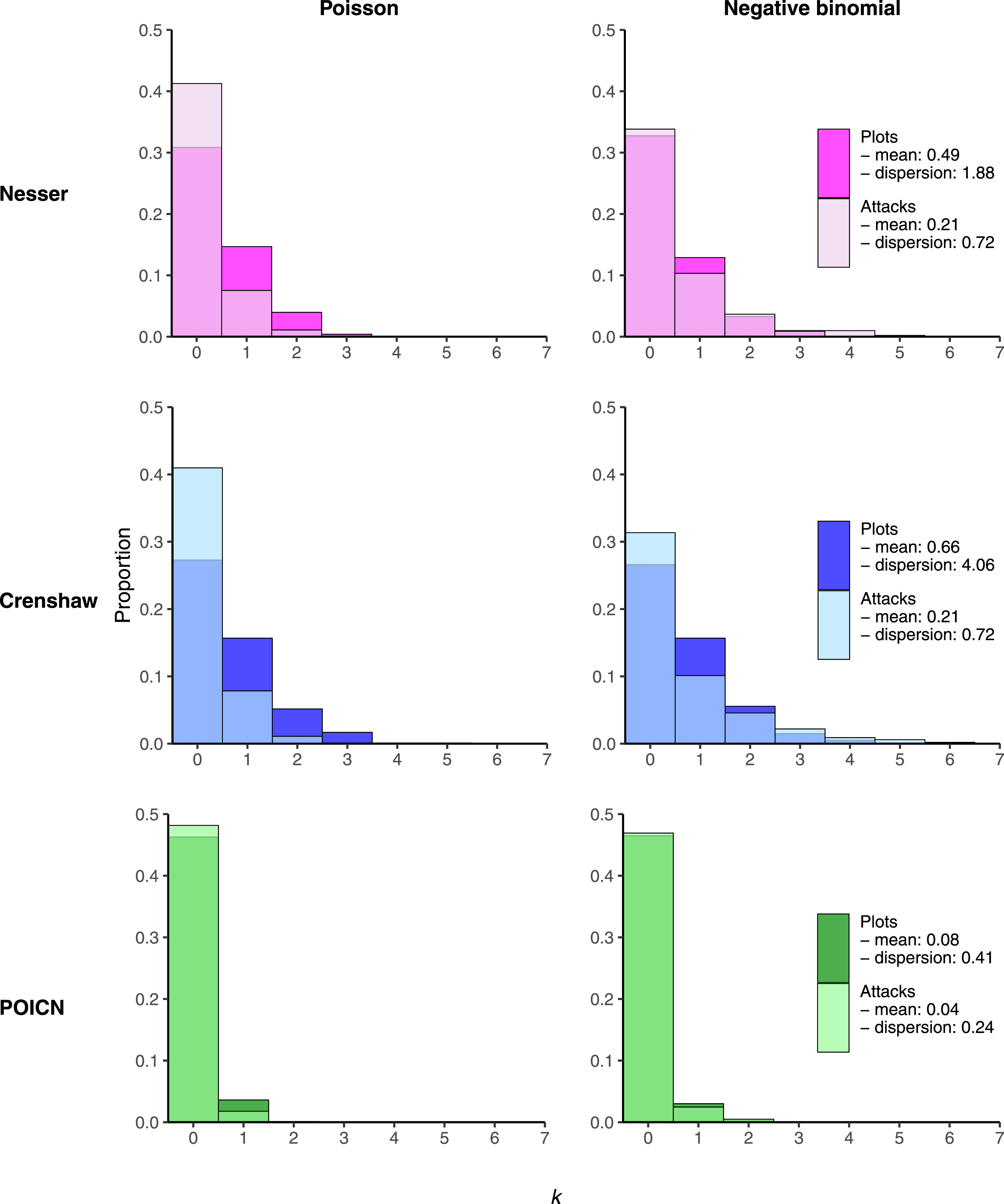
Predicting Terrorism
Does the choice between plots and launched attacks make a difference in practice? To find out, we conduct a new analysis of the country-level correlates of jihadism in Europe. The reason we do not re-analyse a published analysis is that there are no studies whose empirical scope matches that of the available plot data. We choose jihadism in Europe because we consider the Nesser dataset to be the most reliable of the three plot datasets. It also has the highest plot-attack correlation and so offers the toughest test for the proposition that attack and plot data are not interchangeable. As it happens, the correlates of jihadism in Europe have not actually been studied before, so the exercise also contributes to our substantive knowledge of the phenomenon.
Theoretical Motivations
We choose covariates following the literature on the causes of terrorism described in the “Conceptual Framework” section above. We start with demography and test logged population size, since the literature strongly associates it with increased terrorism in absolute terms (Morris and LaFree 2017, 112). We also enter variables related to migration, since the link between migration and terrorism risk is hotly debated (Choi and Salehyan 2013; Milton, Spencer, and Findley 2013; Bove and Böhmelt 2016; Forrester et al. 2019; Helbling and Meierrieks 2020) and since the populist right often claims that Muslim immigration leads to more jihadism. We operationalize this dimension with refugee numbers and the percentage of the population who are Muslim.
We also enter variables capturing economic conditions, since the relationship between economic development and terrorism is debated, with policy advocates often suggesting there is a negative relationship (Sokolsky and McMillan 2002; Sterman 2015) and terrorism scholars mostly saying the link is weak (Sandler 2014). We operationalize this as GDP per capita and CPI change.
A related set of predictions concern poverty and inequality, since this is also a major theme in the literature, with scholars being somewhat more divided on its effects and mechanisms (Franc and Pavlović 2023). We operationalize this using unemployment rates and social spending as a percentage of the central government budget.
We also account for domestic policy since the literature links left- and rightwing policy postures to terrorism levels in different ways. For example, some studies suggest leftwing governments are more vulnerable to terrorism because they are softer on national security (Koch and Cranmer 2007), others that economic redistribution and more human rights-respecting policing – both leftwing features – reduces terrorism (Burgoon 2006; Walsh and Piazza 2010). We operationalize domestic policy orientation as the rightwingness of cabinets measured by ParlGov.
State capacity is another key variable, since it is associated in the literature with lower risk of terrorism and conflict (Danzell and Zidek 2013; Daxecker and Hess 2013; Newman 2007; Lai 2007; Tikuisis 2009). We measure this as security spending as a percentage of the central government budget.
Likewise, foreign policy is of interest, because some research suggests that support for other countries in conflict or military expeditions in other countries is associated with increased vulnerability to international terrorism (Kjøk et al. 2004; Neumayer and Plümper 2009; Kattelman 2020). Moreover, a key claim from the political centre-left throughout the war on terrorism was that the West’s military interventions in the Muslim world provoked jihadism (Morrison and Oborne 2015). We capture this dynamic with the number of troops in Muslim-majority countries.
Finally, we also want to account for political instability, since it is sometimes predicted to increase terrorism (Campos and Gassebner 2013; Fahey and LaFree 2015; Schumacher and Schraeder 2019). In the context of jihadism, a particularly interesting subdimension is far-right militancy, which according to some scholars fuels militant Islamism in the West or contributes to escalatory cycles of violence (Mitts 2019; Lee and Knott 2020). We operationalize this as violent attacks by far-right militants.
Note that we make some small departures from the list in the “Conceptual Framework” section to reflect the region and actor type under consideration. We exclude regime type and culture, since they vary little inside Western Europe. Meanwhile, we add time trend variables related to the rise and fall of al-Qaida and Islamic State, since these organizations’ strength might plausibly have affected jihadi terrorism levels in Europe.
Most variables are assumed in the literature to operate on the motivation side of the terrorism production chain, i.e., as grievances suspected of increasing the intention to use terrorism. As such, they should affect plot and attack production similarly. One of our variables, security spending, represents a constraint and should capture plot attrition if the latter is merely a function of counterterrorism capacity.
Design
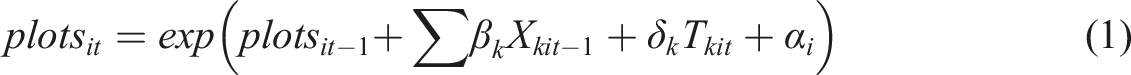
To model the incidence of events, we analyze the counts of plots and attacks using a cross-sectional, time-series structure. We choose this relatively straightforward and common design precisely because it is widespread. To model this, we follow Wooldridge (1999) and use Poisson regression. Here, the count of plots in country (i) at year (t) is estimated as:
Results
Predicting the Incidence of Jihadi Terrorism in Western European Countries, 1994-2021.
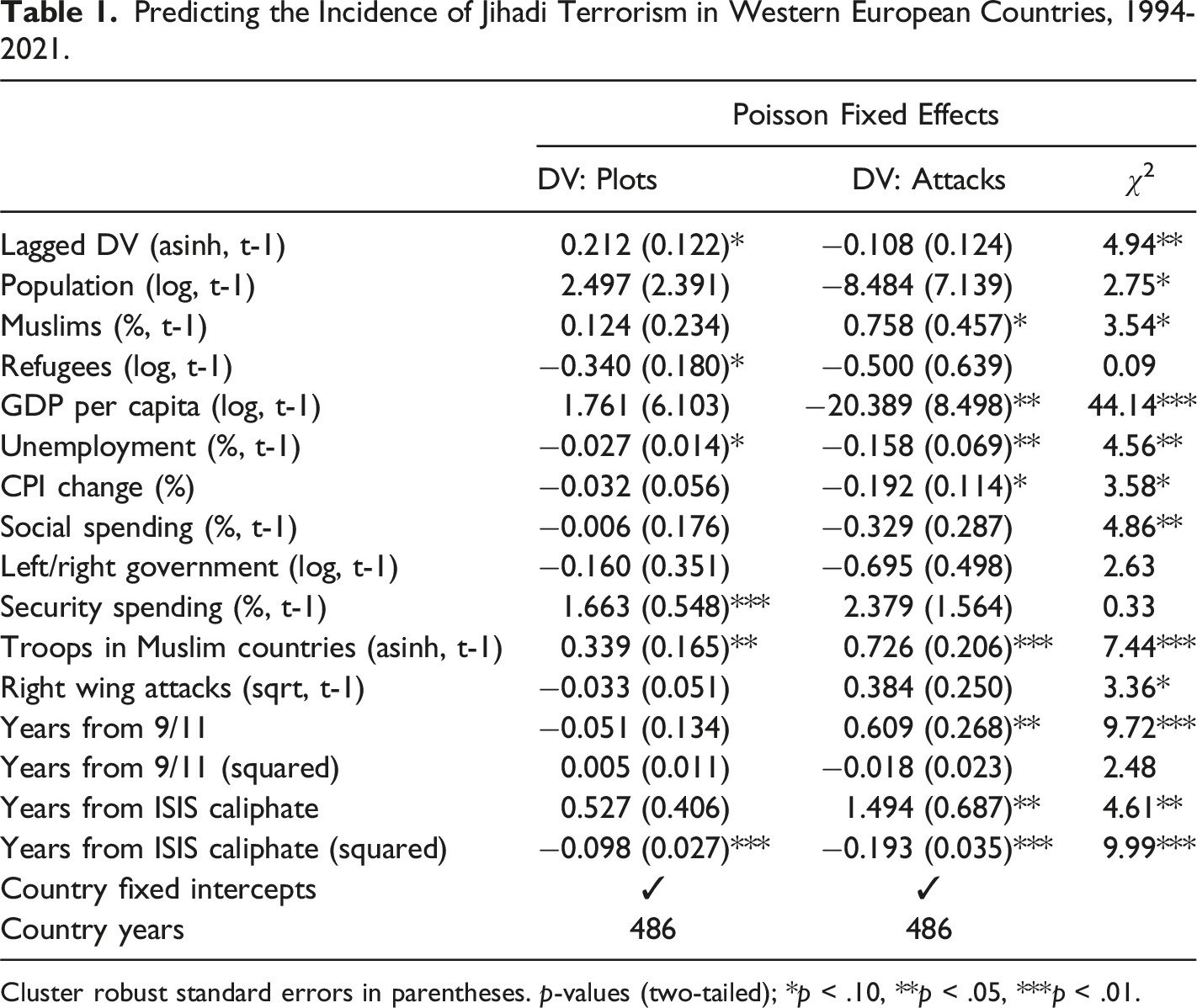
Cluster robust standard errors in parentheses. p-values (two-tailed); *p < .10, **p < .05, ***p < .01.
Our results indicate that an increase in plots the previous year is a positive and significant predictor of plots the following year. However, having more attacks at t-1 is actually significantly negatively associated with attacks the next year, and the difference between these associations is itself statistically significant. Increasing a country’s population is a significant and positive predictor of plots; however, the coefficient again changes sign when taking attacks as the outcome, albeit without approaching statistical significance. Importantly, these associations are also statistically significantly different from one another. Increasing the percentage of the population who are Muslim is positively associated with both plots and attacks. Note that only the coefficient for attacks is significant. Crucially, the chi-squared statistic indicates that these two coefficients are also drawn from different distributions, underlining the risk of spurious inference if only confining attention to attacks. Increasing the number of refugees in a country is negatively associated with both plots and attacks — and we cannot reject the null that the difference between these coefficients is zero.
Turning to economic explanations, we note that increasing GDP per capita increases the incidence of plots, but reduces the number of attacks. The difference between these associations is itself statistically significant. Unemployment reduces the incidence of both plots and attacks; however, the magnitude of this association is much stronger for attacks and this difference is significant. Increasing the cost of living is statistically significantly negatively associated with attacks but not plots, and these associations are themselves meaningfully different from one another. Social spending seems to reduce the incidence of both plots and attacks, but again this association is much larger when predicting attacks — and the difference is statistically significant.
Looking at state characteristics, having a more right wing government appears to reduce the incidents of both plots and attacks, and there is no difference between these associations. Increasing a country’s security budget is significantly positively associated with the number of plots in a given year. The coefficient for attacks is also positive, but not significant. The difference between these coefficients is not, however, statistically significant.
Perhaps unsurprisingly, countries with more troops in Muslim-majority countries suffer more plots. We find a similar relationship with attacks — but the size of the association is much larger, and this difference is again statistically significant. Increasing the level of right wing violence seems to increase the number of attacks, but not plots, and the coefficients are statistically significantly different from one another at p
Finally, we see markedly different time trends for both plots and attacks. The number of attacks seems to increase post 9/11, but the incidence of plots falls, and these differences are themselves statistically significant. Interestingly, we find a non-monotonic inverted U-shaped trend for attacks in the years following ISIS’ declaration of a caliphate, with attacks increasing and then declining, as indicated by the squared term. This trend is not visible for plots, and again these differences are themselves statistically significant.
For completeness, Appendix Table A7.1 reports the results from alternative estimators (negative binomial regression and OLS) and functional forms for our dependent variables. In Appendix Table A7.2, we extend the analysis to the Crenshaw dataset. After testing different distributional assumptions and functional forms, we find meaningful differences between how our covariates predict the incidence of terrorism depending on how terrorist activity is operationalized.
Country Years with Zero Terrorist Attacks
Of course, there may be good reasons to study the number of terrorist attacks in a given unit of time. In this mode, attacks are a measure of successful violence, rather than a proxy for terrorist activity. However, as we have argued, country years with zero attacks may not equate to country years with zero plots. It follows that country years with zero attacks may not be “true zeros” — we cannot observe an attack, because one or more plots have been foiled.
In such cases, country years with excess zeros (i.e., no attack is recorded) may be generated by a separate process from the count of attacks. To test for this, we draw on the Nesser dataset of jihadi attacks in Europe and re-run the models above using mixed effects zero-inflated Poisson regression. The dependent variable is the count of attacks in a country year. In the first stage we use a transformed count of failed plots in a country year along with the security spending variable. The covariates in the Poisson portion of the model follow those set out in Table 1. Country random intercepts account for the panel structure.
Predicting Country Years With Zero Jihadi Attacks.
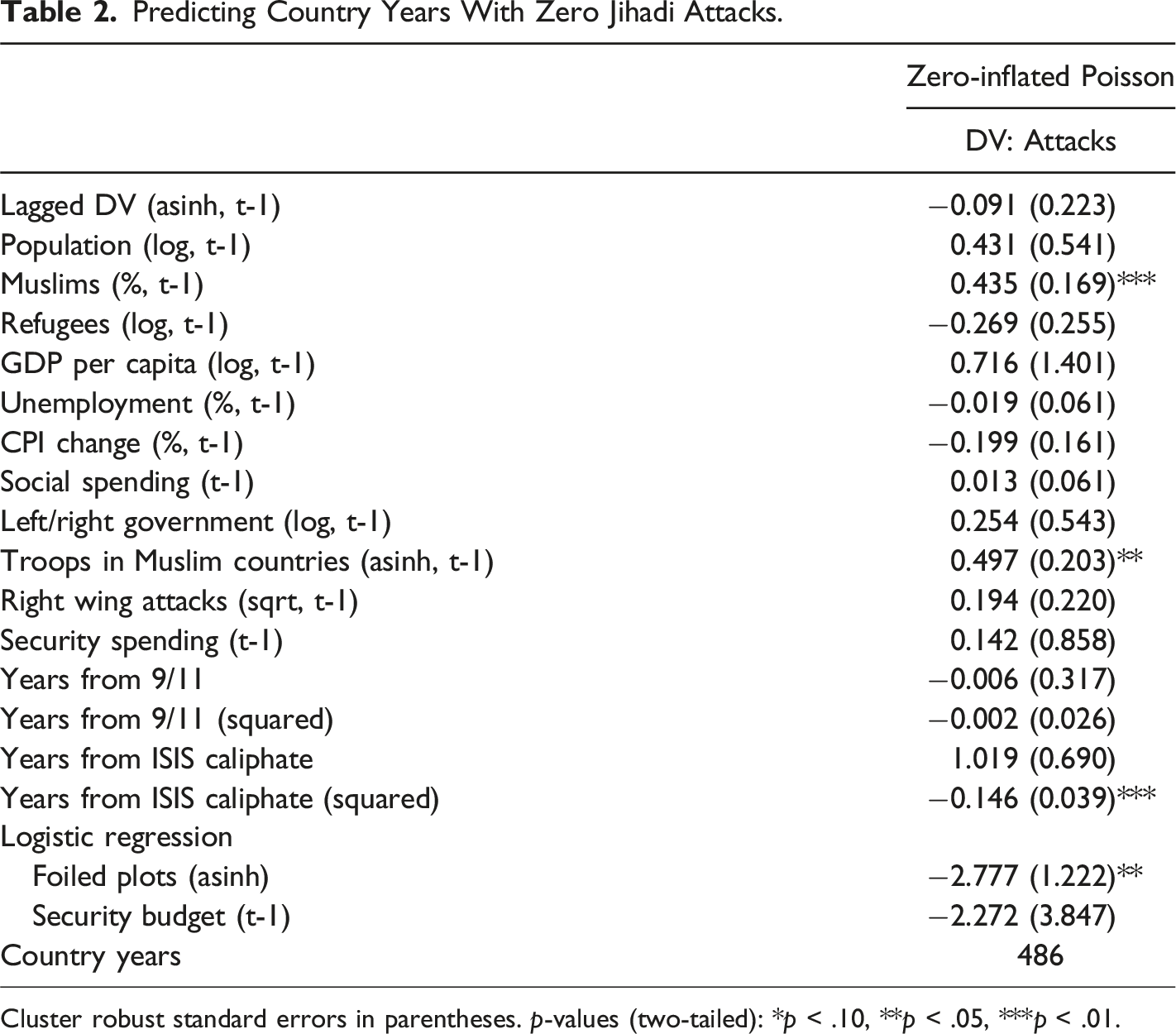
Cluster robust standard errors in parentheses. p-values (two-tailed): *p < .10, **p < .05, ***p < .01.
Most importantly, these results suggest that when predicting the number of launched attacks in a country year, researchers might consider a zero-inflated process that accounts for excess zeros. Should this approach be extended to studying terrorist activity more broadly, thus allowing us to retain attacks as the outcome measure? We think not. A two-step modeling approach can only differentiate between country years with zero or more than zero attacks, whereas we are often interested in country years that see multiple plots, some of which fail and some of which get through. If the number of failed plots is known, then the count of plots is the more relevant measure of terrorist activity. This also negates any need to model complex attrition processes that may be highly context and time specific.
Conclusion
This article has highlighted an understudied measurement problem at the heart of the study of terrorism. Attacks are an imperfect measure of terrorist activity, because they mask the number of plots that nearly reached execution. Analyzing plot and attack counts can yield different results in common research designs, including for covariates of interest to political scientists, such as time-varying economic factors, demographics, state characteristics, political grievances, and events.
Since police intervention is an important source of plot attrition, it is tempting to think that the measurement problem can be solved by controlling for counterterrorism capacity. But things are probably not that simple. For one thing, there are few good measures for counterterrorism capacity available. Conceptually, it is not clear which measures might represent it, and even if we knew, they might not be obtainable, since they likely reside in the closed world of intelligence and security. In our analysis, one of the best available measures, domestic security spending, did not account for all the plot attrition. For another, there is probably a game-theoretic element to plotting, whereby terrorists will adapt to increased risk by initiating fewer plots. This means that strong counterterrorism may produce both high attrition through interception and low attrition through deterrence. We suspect that attrition is at least partly rooted in plotters’ misjudgment of risk, which in turn may stem from information problems about their operating environment. This takes us into a fast-paced, micro-level territory which probably cannot be modelled with the country-year data available to political scientists today.
The scale of implications of this problem is difficult to assess. We do not wish to overstate it, since the correlations between plot and attack counts can be high depending on the unit of analysis and the differences revealed by our analysis are not benchmarked against existing claims in the literature. But it would be equally unreasonable to dismiss it. Plainly, our results can only speak to explaining jihadism in Western Europe. It is an open empirical question as to whether they generalize to other regions, periods, or ideological families. But this does not necessarily mean that the problem is smaller in those other cases — we simply cannot know at this time.
What we can say is that plot attrition likely impacts different inquiry types to varying degrees. Studies of the effects of terrorism — where terrorist activity is the independent variable — should be less affected by plot attrition, because they are often concerned with phenomena that presuppose attack execution, such as psychological trauma or economic disruption. Similarly, the literature on determinants of individual participation in terrorism should be less affected, since it already tends to take network or group membership (as opposed to attack perpetration) as the dependent variable.
In the absence of evidence that plot attrition is not a concern, scholars studying the causes of terrorism with attacks as the dependent variable would be well advised to take the problem seriously. We see at least three potential mitigation strategies. As a minimum, quantitative terrorism scholars should triangulate their findings against plot data where those are available. Another solution, as it applies to modeling successful attacks, is to develop a theory of plot attrition with a view to empirically observing it on the right hand side. This will require more research into the determinants of plot attrition, but it is an effort that we would encourage, as it would deepen our understanding of the production of terrorism. The third and ideal solution is to build larger plot datasets and study the causes of terrorism with plots as the dependent variable. A reliable global plot dataset is unrealistic, but there is low-hanging fruit, such as plots by non-jihadi groups in OECD countries. Overall we believe that paying more attention to near-misses will be beneficial to the field. Sometimes the things that do not happen are as important as those that do.
Supplemental Material
Supplemental Material - Plots, Attacks, and the Measurement of Terrorism
Supplemental Material for Plots, Attacks, and the Measurement of Terrorism by Thomas Hegghammer and Neil Ketchley in Journal of Conflict Resolution
Supplemental Material
Supplemental Material - Plots, Attacks, and the Measurement of Terrorism
Supplemental Material for Plots, Attacks, and the Measurement of Terrorism by Thomas Hegghammer and Neil Ketchley in Journal of Conflict Resolution
Footnotes
Acknowledgments
We thank Petter Nesser for contributing key data and ideas; Vidar Skretting and Frida Ekren for valuable research assistance; Thomas Ball, Bjørn Høyland, Anders Ravik Jupskås, Carl Henrik Knutsen, Matthew Koo, Eirik Lamøy, Jacob Ravndal, Tore Wig, and Elisabeth Jean Wood for helpful comments on early drafts, and Martha Crenshaw, Margaret Wilson, and Markus Binder for sharing data. We also thank Ramon Garibaldo and Louisa Lombard for the opportunity to get feedback from the “Political Violence and its Legacies” workshop at Yale University on 10 March 2022.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Data Availability Statement
All supplementary and replication material for this article are available online.
Supplemental Material
Notes
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.