Abstract
Do states constrain non-state hackers? This article extends research on the role of transnational cyber aggression in international relations, showing that governments can be incentivized to mitigate non-state hacking. To test this argument, I leverage competitive elections to the International Telecommunication Union (ITU), which requires states to campaign on their cybersecurity record. By exploiting this variation, I demonstrate that states are responsive to incentives. Candidates reduce non-state cyber aggression to increase their likelihood of election. This finding demonstrates the potential utility of international institutions as a policy solution to transnational hacking, suggesting that structural incentives can induce states to constrain hackers operating in their territory.
Actors known as hackers now regularly exploit digital weaknesses across state boundaries, imposing considerable costs on their targets. In the last decade, state leaders have increasingly expressed support for international cooperative efforts to address the growing transnational threat of non-state hackers (Gedeon 2024). Attempts to establish cooperative institutions have achieved notable traction. In 2015, a UN Group of Governmental Experts created a list of norms for responsible state behavior in cyberspace, establishing that “states should not knowingly allow their territory to be used for internationally wrongful acts using ICTs (Information Communication Technologies)” (Maurer 2018, 237). More recently, the UN initiated negotiations on a cybercrime treaty that would formally obligate signers to police hackers within their territory (Wilkinson 2023). In August 2024, the draft treaty received a unanimous vote of approval by the UN’s Committee on Cybercrime and was moved to a vote in the UN General Assembly.
Despite increasing support for cooperative efforts, skeptics have called into question whether governments will abide by the requirements of cooperative institutions in cyberspace. These pessimists have suggested that governments lack the capacity and willingness to constrain hackers, and that the failure to regulate activity in the cyber domain may be an inevitable reality. In this article, I seek to empirically inform the debate over whether states can achieve cooperation in cyberspace. To do so, I assess whether states can reduce transnational hacking originating from their territory when given adequate incentives to act.
I employ a research design that exploits competitive elections to the International Telecommunication Union (ITU). The ITU is the specialized agency of the UN responsible for developing global technical standards and improving the cybersecurity capabilities of its member states. Every 4 years, members are elected to serve on governing boards. States that campaign for these positions are evaluated on the basis of their cybersecurity record, providing an incentive to mitigate transnational hacking during their candidacies. I find that candidates reduce non-state cyber aggression during campaign periods. The measurable decrease in transnational hacking provides evidence that states can respond when incentivized to constrain non-state hackers in their territory.
The finding has important implications for policymakers and scholars of international relations. Constraint in the ITU context should prompt policymakers to consider the utility of international institutions to reduce non-state hacking. Although the ability of states to constrain non-state hacking is not complete, the empirical test demonstrates that states care about their reputation for responsible cyber behavior and affect meaningful change in the activities of non-state hackers to manage this reputation. Having shown that governments can exercise the requisite ability to constrain non-state hacking, this article urges further investigation of what kinds of institutional arrangements could enhance the incentives for states to cooperatively mitigate hacking.
The Hacking Problem
The digital revolution has provided non-state actors with a new medium through which to influence international affairs. Non-state hackers can use cyber tools to disrupt communication, spread propaganda, and expose the digital weaknesses of state actors. Because hacking does not require extensive resources or high expertise, non-state hackers can come in many different forms. Organizations, private companies, or even individuals can initiate an array of operations that cause considerable impact.
Non-state actors can engage in data theft, which involves the unauthorized extraction of proprietary or sensitive information. Often non-state actors will hold stolen data for ransom or leak sensitive information to embarrass their target. Non-state hackers can also disrupt technological processes. These interruptions tend to hinder a target’s ability to communicate information. Non-state actors often vandalize websites as a form of protest, replacing content with political or ideological messages. Hackers also cause disruption by flooding servers with fake traffic. When hackers overload servers, online operations become inaccessible, preventing users from accessing services entirely.
Non-state actors in cyberspace can leverage these tools for many different purposes. Scholarship has broadly separated non-state cyber actors into criminally and politically motivated hackers (Borghard and Lonergan 2016). The former pursues financial gain while the latter seeks to promote some political end. Politically motivated hacking encompasses a range of motivations. For example, hacktivists typically protest government policies or perceived social injustices whereas patriotic hackers cite nationalism to justify their cyber operations. In practice, the distinction between these two types is often blurred. Anecdotal evidence suggests that politically motivated hackers often engage in criminal activity and criminal groups have conducted attacks in support of a country or political cause (Borghard and Lonergan 2016, 410).
While academics have categorized hackers as either criminal or political in their efforts to understand the causes of non-state cyber aggression, legal frameworks have rarely made this distinction. International and domestic regulatory frameworks criminalize the tools of hacking (unauthorized computer access, system interference, etc.), employed by political and criminally motivated hackers alike (Murphy 2024). For example, the current draft of the UN cybercrime treaty requires that signatories criminalize unauthorized access or interference with ICT system/electronic data, but does distinguish between those non-state actors that would use these tools for political purposes from those that would use them to secure personal gain (Plumb 2024).
Government’s Capacities and Incentives to Constrain
As the prevalence and impact of transnational hacking has increased, policymakers and scholars alike have advocated for international cooperative efforts. Transnational hacking shares features with many other global dilemmas that have been addressed through formal cooperation; governments impose negative externalities on other states (e.g., transboundary malicious activity) when they choose to abstain from taking measures to further the collective good (e.g., practicing cybersecurity). International relations scholars have long studied how formal instruments can help states resolve these types of cooperative problems.
A critical function played by formal institutions is that they provide agreed upon standards for what constitutes acceptable behavior (Abbott and Snidal 1998). These standards can sustain cooperation by helping domestic and international observers define compliance, providing a shared understanding of what behavior violates international norms, laws, or agreements. If a government’s behavior does not align with agreed upon standards, then observers can call attention to this inconsistency and cast doubt on whether the government truly supports the institution’s purpose (Voeten 2014). Scholars have argued that governments seek to avoid inconsistencies between previous commitments and current behavior because this information can be used to trigger interstate retaliation, cast doubt on the state’s reputation as a cooperative partner, or even catalyze domestic political opposition (Dai 2005; Kelley 2007; Simmons 2009; Tomz 2007; Voeten 2014).
While a well-established literature in international relations has shown that international institutions can shape state behavior across different policy areas, the cyber domain seems to pose unique challenges that scholars have suggested could inhibit compliance with cooperative institutions. The first challenge is that governments may not have the capacity to constrain hackers in their territory. Early assessments were pessimistic, arguing that government actors could do little to stem the wave of transnational hacking. The consensus seemed to be that states were largely “helpless to prevent attacks from [their] territory” (Healey 2011, 63). This position was echoed by government officials, who often emphasized their inability to police cyberspace. For example, when Russian hackers leaked documents stolen from the Democratic National Committee, Russian President Vladimir Putin maintained that the Kremlin could do little to restrain patriotic hackers (Higgins 2017).
More recently, policymakers and analysts have argued that states can leverage an array of tools to mitigate hacking originating from their territory (Hollis and Waxman 2018, 154). First, governments have made direct appeals to hackers. In these cases, some hackers respond to government directives because they seek to align their activities with the government’s interests. For example, patriotic hackers in China have responded to government officials when asked to restrain their activities against the US during periods of heightened tension (Fletcher 2011). Second, governments leverage the threat of prosecution to dissuade non-state hackers. Researchers have found evidence in certain settings that increasing penalties or the threat of punishment can reduce criminal hacking within a country (Hui et al. 2017). Finally, governments can disrupt the tools that hackers need to conduct attacks. A common strategy for disruption is targeting hacking forums. Forums serve as a key source of information for hackers “where novice posters seek attack scripts, and veteran attackers solicit help to illegally intrude on online information systems” (Wang et al. 2012, 143). When governments block access to these forums through domain deregistration or server takedown, the activities of hackers can be seriously impaired (Hutchings and Holt 2017). Governments can also limit the availability of online black markets where stolen data is sold. Traffic to these sites can be disrupted through internet censorship techniques like IP filtering and DNS tampering (Hutchings and Holt 2017).
The second challenge that scholars have noted is that governments often have strategic reasons to exploit the anarchic nature of cyberspace rather than constrain the activities of non-state hackers (Katagiri 2021). In the study of cyber norms, scholars have noted that governments avoid consenting to hard law instruments and typically refuse to invoke international law when targeted by cyber operations (Bogdanova and Callo-Muller 2023; Finnemore and Hollis 2020). These rejections of formalized cooperation have been interpreted as evidence that “states may value the lack of clear rules,” particularly with reference to non-state hackers in their territory (Finnemore and Hollis 2020, 999).
Why would governments prefer ambiguity over cooperation on transnational hacking? Governments often use non-state hackers as proxies. A key benefit of these proxy relationships is the ability to deflect blame away from the state. By contracting offensive operations out to non-state hackers, governments can deny their targets the political justification for retaliation or escalation. Public opinion research has supported this argument, finding that public support for retaliation decreases when a hack is attributed to individual or civilian actors (Leal and Musgrave 2023). Because states may “have an inherent interest” in maintaining the appearance of separation from hackers, they may refuse to constrain hackers because doing so would reveal that they can direct the activities of these actors (Katagiri 2021, 7).
Governments can also face a domestic security tradeoff. In certain countries, transnational hackers operate with a high level of impunity (Maurer 2018; Sherman 2021). To explain this phenomenon, analysts have argued that governments provide non-state hackers with free reign in terms of transnational activities to dissuade them from hacking domestic targets. For example, observers have argued that China encourages transnational hacking to “distract hackers from turning their talent to more anti-state activities” (Klimburg 2011). Similarly, analysts have argued that Russia allows hackers to operate freely “so long as they focus on foreign targets, do not undermine the Kremlin’s objectives, and answer to the state when asked” (Sherman 2022). These assessments suggest that governments may strategically permit criminal hacking to redirect cyber aggression outside their borders.
To prevent states from leveraging non-state hackers, scholars have suggested adopting legal strategies that would prevent states from avoiding consequences by deflecting responsibility onto non-state hackers. Some scholars have advocated for the creation of an international mechanism that would attribute cyber-attacks (Shany and Schmitt 2020). Others have argued for an international dispute resolution system that would make determinations about culpability after the aggrieved party presented evidence against the attacker (Khan 2020). The strategy that has received the most traction has been the application of a “due diligence” norm for assigning responsibility. Akin to environmental norms, the due diligence standard articulates an expectation that governments can be held responsible for malicious activities emanating from their territory because they failed to exercise reasonable precautions to prevent transnational harm (Healey 2013).
Under this standard, state culpability could be established even if accusers could not prove that state actors directed the activities of non-state hackers. In 2022, President Biden applied this standard against Russia. He promised retaliation against Russia for ransomware attacks against US companies even though evidence did not suggest that the attacks were “sponsored by the state,” arguing that Russia had the “responsibility” to address ransomware attacks emanating from its territory (Healey and Grinberg 2022). Efforts to institutionalize cyber norms have also promoted a due diligence approach. NATO’s Tallinn Manual, which is a non-binding interpretation of international law applicable to cyber warfare, states that a government must not allow its territory “to be used for cyber operations that affect the rights of, and produce serious adverse consequences for, other States” (Schmitt 2017).
While discourse on the capacities and willingness of state actors to address non-state hacking has evolved, these debates have yet to be informed by systematic empirical evidence. To answer whether states can mitigate non-state hacking, I propose a research design that leverages ITU elections. ITU elections provide an observable instance in which governments have strong incentives to constrain non-state hackers in their territory.
ITU and Cybersecurity
The ITU is the specialized agency of the UN responsible for setting international standards related to communication networks and promoting development to close the global digital divide. The ITU develops technical standards and fosters digital advancement in areas of radiocommunication, mobile phone networks, and internet connectivity. The ITU is composed of several bodies. The Plenipotentiary Conference is the governing body of the ITU, which includes representatives from all 193 member states. It meets every 4 years to steer the ITU by amending the organization’s constitution and electing officers.
In the 1990s, the ITU was relegated to a limited role in internet governance. Democracies feared that an international regime would allow autocrats to restrict information access across borders by institutionalizing sovereign control (Farrell and Newman 2021). Over time though, the proliferation of cross-border network contact became a source of vulnerability for states (Calderaro and Craig 2020). Attackers in the cyber domain leveraged unsecured networks as “‘spring boards’ for attacks on third parties” (Hansel 2013). Poor cybersecurity became an asymmetric negative externality that imposed the greatest cost on digitally dependent countries. This is evidenced by the US cyber strategy, which asserts that “in an interconnected global environment, weak security in one nation’s systems compounds the risks to others” (White House 2011).
To address this problem, the UN amended the ITU’s responsibilities, tasking the organization with improving the cybersecurity capabilities of its member states. In keeping with this mandate, the ITU developed a Global Cybersecurity Agenda (GCA). The GCA aims to help members build legal, technical, and organizational capacities to protect against cyber threats and cybercrime. The ITU also regularly evaluates the progress of its member states by ranking countries according to their cybersecurity development with the Global Cybersecurity Index (GCI). The GCI measures cybersecurity capacities along several dimensions to capture a state’s commitment to deter, identify, mitigate, and punish criminal activity in their sovereign cyberspace.
The cybersecurity function of the ITU attempts to achieve regulatory harmonization by disseminating the capacities and technical expertise needed to secure digital systems. Simmons (2001) provides a framework to understand this process. She argues that the politics of regulatory harmonization depends on whether fragmented regulation imposes significant costs on dominant states and whether peripheral states have incentives to emulate the institutions of dominant states. If the negative externality is costly for dominant states and peripheral states have incentives to resist adjustment, then heavy-handed enforcement is required to achieve harmonization. However, if peripheral states want to emulate the regulatory institutions of dominant states, then harmonization can be achieved through information provision and broad-based technical assistance (Simmons 2001).
In the case of cybersecurity, the negative externality in question imposes a significant cost on dominant states (digitally advanced countries like the US, China, and Russia), but peripheral states want to emulate the regulatory structure of dominant states because improved cybersecurity carries domestic benefits. In the Global South, internet penetration is increasing rapidly, but governments have found that they lack the “technical and policy capacity to reap the benefits of connectivity, while limiting their exposure to threats emerging from digital infrastructure” (Calderaro and Craig 2020, 919). Weak cybersecurity exposes domestic industries to exploitation, meaning that states have incentives to provide cybersecurity within their borders to attract and retain high-tech industries (Vasiu and Vasiu 2018).
ITU Elections
In the lead-up to the Plenipotentiary Conference, member states can campaign for election to the ITU Council and the Radio Regulation Board. The ITU Council is a 48-member body that acts on behalf of the membership between Plenipotentiary Conferences. The ITU Council votes on policy issues originating from all sectors of the ITU and guides organizational direction by deciding on the emphasis of ITU activities. The 12-member Radio Regulation Board performs a similar function, except that oversight is restricted specifically to the topic of radiocommunication, including measures to secure communication networks. Council and Board seats are distributed among 5 geographic regions. ITU members vote for candidates in each region by secret ballot, and the seats in each region are awarded based on a plurality system.
States seek representation on these bodies for many reasons. ITU Council membership allows governments to define the scope of the ITU’s standardization and capacity-building activities. Moreover, these bodies can make decisions that directly implicate a member’s national interests. Consider the Radio Regulation Board’s authority to allocate radio frequencies used by government and commercial actors. This function has been cited by American officials as a reason why “the election of a U.S. national to the Board is important in order to protect U.S. economic and national security interests” (Goss 2006).
I argue that ITU elections create incentives for states to moderate non-state cyber aggression originating from their territory. These incentives emerge because the general ITU membership shares an interest in appointing states that can effectively manage the ITU’s bureaucracy to achieve cybersecurity development. Scholars have used the principal-agent framework to explain the delegation of authority to bureaucrats within international organizations (Hooghe and Marks 2015; Johnson and Urpelainen 2014; Nielson and Tierney 2003). Application of the principal-agent model to international organizations requires modification though. Under the simple framework, a principal can expend effort to regulate their agents. In an international organization, the principal is not singular. Each member is a principal, meaning that any attempt to regulate international bureaucrats requires the collective effort of the membership. If members cannot achieve coordination, then bureaucratic agents will pursue their independent interests unchecked (Nielson and Tierney 2003). To address this structural challenge, international organizations can reduce the cost of coordination among principals by selecting a subset of its membership to perform oversight functions.
In the context of the ITU, the elected bodies comprise a subset of principals that will vote on policies and guide the organization for a four-year period. The membership of the ITU seeks to elect states that possess the technical expertise to ensure that bureaucrats effectively prosecute the task of cybersecurity development. How can ITU members screen whether states have the expertise to perform this function? A critical source of information is a state’s cybersecurity record. Transnational attacks initiated by non-state actors signal an inability or unwillingness to prevent the misuse of information and communication technology within one’s borders, which casts doubt on a government’s claims of cybersecurity expertise.
Candidate states demonstrate an awareness that the ITU membership will consider their cybersecurity capacities when deciding how to cast their votes. When states campaign they highlight their cybersecurity record. For example, in the 2022 ITU election, the Philippines emphasized its cybersecurity capacities, stating that the country had a “cybersecurity land-scape adhering to international standards” (Department of Information and Communications Technology 2022). Candidate states also cite their placement by the ITU’s Global Cybersecurity Index to illustrate the state’s expertise in cyber capacity building. Turkey’s campaign brochure for the 2022 election remarks that “Turkey attaches great importance to developing up to date methods of combating cybercrime … as a result of the continuous efforts in this field, Turkey was ranked sixth in Europe and 11th in the world” (Ministry of Transport and Infrastructure 2022).
It is important to note that this awareness holds for powerful states that select into ITU candidacy as well. For example, Russia’s campaign statements in 2018 emphasized that Russia “intensifies its efforts in combating the criminal use of the Internet and ICTs in general” (Noskov 2018). Given research that suggests that powerful states often perform better when running for election at international organizations, readers may expect that powerful states may feel less need to run on the basis of their cybersecurity record (Dreher et al. 2014). However, an institutional feature of the ITU helps mitigate this concern. Beyond the Council or the Radio Regulation Board, major powers (like Russia, China, and the United States) also choose to run for the ITU’s General Secretariat. Powerful states compete among each other for these executive positions, which prevents dominant countries from simply relying on power or status to win elections. Instead, we observe powerful countries behaving similarly to peripheral states, campaigning on the basis of their cybersecurity and technological records.
As a plausibility probe of the argument that a candidate’s cybersecurity record matters in ITU elections, I assess whether a candidate’s ranking on the ITU’s Global Cybersecurity Index (GCI) positively correlates with the number of votes they received and their likelihood of being elected to the ITU council. As noted above, the GCI aims to measure a state’s commitment to exercising effective cybersecurity. To do so, the GCI ranks states according to (1) legal measures adopted to deter cybercrime, (2) technical practices used to secure computer networks, (3) organizational coordination on cybersecurity, (4) investment in capacity building programs, and (5) engagement in international cooperation on cybersecurity. Across these five pillars, the ITU collects a number of different indicators, surveying member governments and leveraging open source information. Using data on these indicators, the ITU creates the composite weighted GCI. A drawback of the GCI for the purposes of probing whether ITU members care about a candidate’s cybersecurity record is that many of the indicators measure relatively static behavior. This means that more variable cybersecurity efforts like criminal prosecution or the disruption of hackers’ activities will not contribute to a state’s GCI rank. Still, the GCI has become a widely used short-cut for assessing a government’s commitment to practicing cybersecurity, meaning that GCI ranking provides member states with a clear baseline with which to compare candidates according to their willingness to develop and employ cybersecurity expertise.
I take a candidate’s position on the GCI in the most recent release of the index before the 2018 and 2022 ITU election. 1 Because candidates compete within ITU regions, comparisons among candidates occur within regional groupings. To account for this feature of the ITU electoral process, I include region fixed effects. A concern with this analysis is confounding from a candidate’s international power or geopolitical relationships with other countries. As noted above, previous work has shown that a candidate’s status as a powerful state or their proximity to powerful states can influence the results of elections at international organizations (Dreher et al. 2014). Dreher et al. (2014) found that powerful states (measured by metrics such as national wealth and population) were more successful in UN Security Council elections. They also found evidence that alignment with majors powers in UN General Assembly (UNGA) voting predicted success in contested elections. Extending these findings to the ITU context would lead to the expectation that state strength and geostrategic ties to powerful countries would help states garner votes in ITU elections. However, these factors may also correlate with greater cybersecurity capacity. Stronger states have the financial and technical capacity to invest in cybersecurity development, and recent evidence suggests that cyber capacity can diffuse through interstate ties like alliances (Kostyuk 2024).
To recover the unconfounded relationship between GCI rankings and ITU elections, I include controls that capture a candidate’s strength and geostrategic ties. Following Dreher et al. (2014), I control for a candidate’s GDP per capita and population. I also include binary variables for whether a candidate holds a membership with the European Union, G77, Organization of Islamic Cooperation, and NATO. I control for proximity to major powers like the US and Russia with a measure of UNGA voting alignment (Bailey et al. 2017).
GCI and ITU Electability.
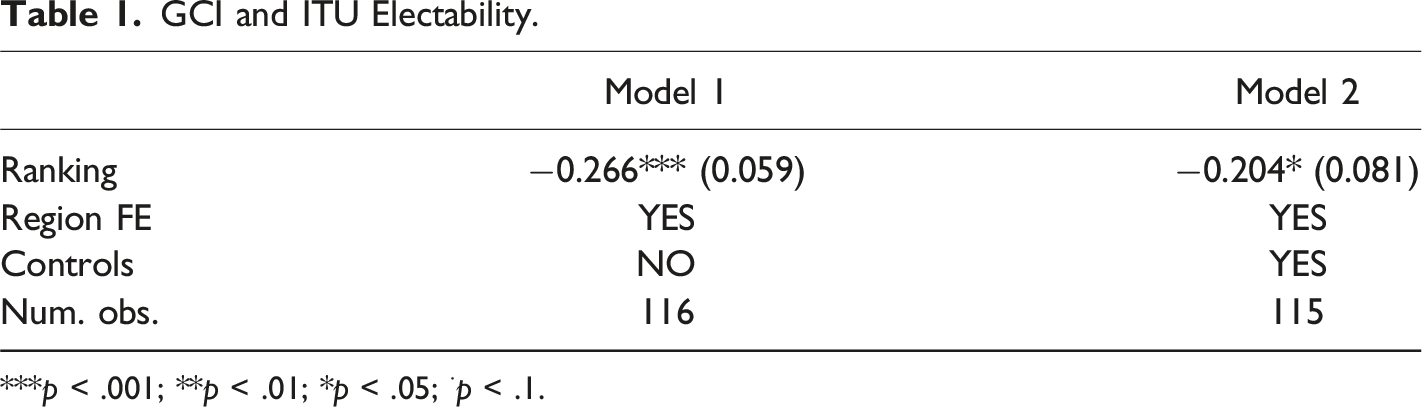
***p < .001; **p < .01; *p < .05; ⋅p < .1.
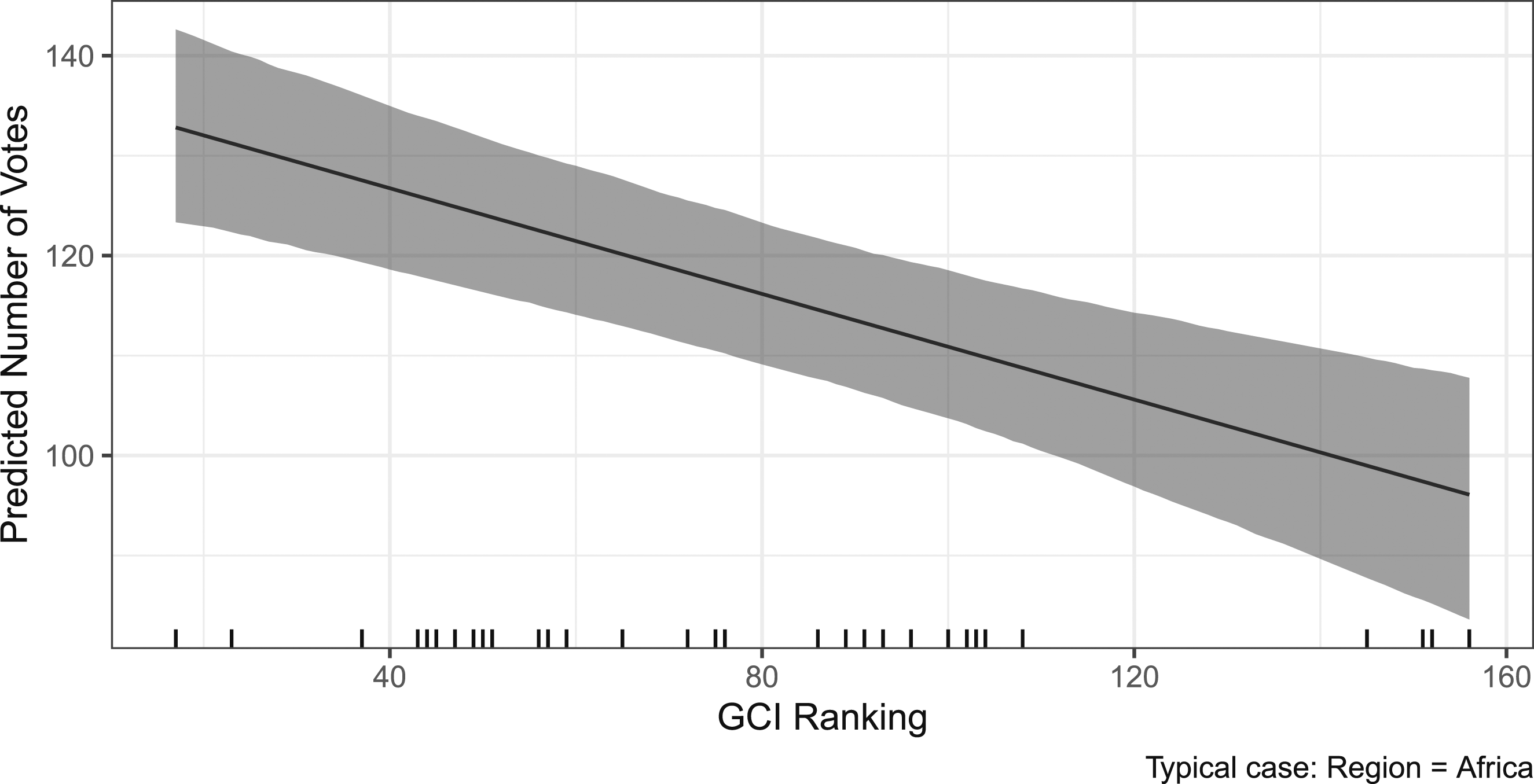
Predicted candidate performance across GCI rankings.
Because ITU members want to delegate authority to actors that have a demonstrated capacity in cybersecurity, I argue that members running for election to governing bodies will seek to manage their reputation. More specifically, I expect that in election years states running for election at the ITU will face incentives to reduce non-state cyber aggression originating from their territory. I expect that these incentives will be particularly salient during election years because the dynamic nature of cybersecurity threats makes recent information about a candidate’s cybersecurity record more valuable in assessing a country’s current capacities. New cybersecurity vulnerabilities constantly emerge as technology evolves. To exercise effective cybersecurity, governments must regularly adapt regulatory models, monitoring capabilities, and disruptive methods to keep pace with technological development and the growing sophistication of hackers. For these reasons, observers will assign greater weight to more recent information about a candidate’s cybersecurity record. Because candidate’s know that recent failures to mitigate hacking will inform the assessments of voting members in ITU election years, I expect them to exert greater effort to address malicious activity by non-state hackers in this time period. 3
I limit the empirical focus of my theoretical expectations to non-state hackers because ITU elections primarily invoke a candidate state’s reputation for mitigating cybercrime, which implies the ability to constrain cyber actors that do not fall under the command and control structure of the government. As noted earlier, The ITU’s cybersecurity initiatives focus on developing and extending the capacities of member states to address cybercrime. Employing a standard definition of cybercrime, the ITU aims to help members mitigate offensive cyber operations initiated by non-state actors, including those attacks that were intended by the non-state actor to achieve some political goal (Gercke 2011). Because members want to elect candidates that will successfully prosecute the ITU’s cybersecurity functions, they will prefer candidates that have demonstrated relevant cybersecurity expertise (i.e., the mitigation of malicious cyber activity by non-state actors). Because the ITU mechanism specifically invokes a country’s reputation for addressing cyber actors that do not fall under the command and control structure of the government, I do not extend the theoretical expectation to those attacks overtly initiated by governments (either accepting responsibility or acting through government affiliated actors like proxies). Put simply, if states respond to incentives, then I should observe a decrease in the number of offensive operations originating from a candidate state in the year of the election. However, if states do not respond to incentives, then the ITU election should not affect the frequency of non-state hacking.
In ITU election years, the number of non-state cyber operations originating from candidate states will decrease.
Leveraging ITU elections offers several empirical advantages. First, the selection process is observed. States must declare candidacy, which allows for the identification of interest variation for a relevant sample of states. Second, ITU candidacy is plausibly unrelated to often-cited pursuits of non-state actors such as financial gain or patriotism (Collier 2017, 39). ITU candidacy should not change the value of cyber theft or impact nationalist fervor, increasing confidence that an observed decrease in cyber-attacks reflects constraint by state actors rather than idiosyncratic alignment between the interests of states and non-state actors.
Research Design
Outcome
I conduct analysis with the European Repository on Cyber Incidents (EuRepoC), which records cyber incidents with attribution information drawn from news sources, IT companies, and state agencies from 2000 to 2022 (Steiger et al., 2018). EuRepoC collects cyber incidents that have a “political dimension,” which is defined as incidents that have (a) have targeted “political or state actors/institutions,” (b) have been attributed to “state-actors as the actual ‘masterminds,’ ” (c) exhibit a political motivation, or (d) have been “publicly politicized” (perceived as politically motivated by the target or media) (Steiger et al., 2018). This broad inclusion criteria ensures that the dataset captures a sample of cyber incidents initiated by non-state hackers. The EuRepoC also requires that a cyber incident involves some violation of the CIA-triad of information security (Confidentiality, Integrity, and Availability), meaning that cyber incidents initiated by non-state hackers capture instances in which an actor has gained unauthorized access to an ICT system, illegally intercepted and/or released data, or interfered with the operations of an ICT system. These scope conditions ensure that non-state cyber incidents in the data constitute cybercrime as defined by most international and domestic standards.
To create a yearly count of cyber incidents, I count the operations initiated by non-state actors. The EuRepoC records whether a non-state actor has been identified as a proxy of a government. I exclude those attacks that have been attributed to non-state actors that act as proxies. Cyber operations that span across multiple years are counted as separate observations, meaning that an attack that starts in 2010 and ends in 2011 is recorded twice in the dataset. To create this outcome variable, I count attacker-target pairings in each year, meaning that if a single attack targets 5 different states then each of the 5 pairs involved in this incident is counted separately. 4 For operations targeting international organizations or regions, I only code the attack once rather than creating an attacker-target pair for each member of the organization or region.
The scope of EuRepoC’s data collection effort and variability in what gets reported by media outlets results in the exclusion of some non-state hacking incidents. These limitations are not exclusive to EuRepoC. Efforts to collect data on cyber-attacks necessarily miss incidents because (1) hackers avoid detection, (2) reporting is inconsistent, or (3) researchers do not have the resources to collect incidents exhaustively. For any study of non-state hacking then, it is necessary to consider the systematic reasons that data is missing, so that researchers do not erroneously conclude that their inferences will hold in the general population of hackers. In this study, the primary concern is whether the hackers in the empirical sample differ from out-of-sample hackers in systematic ways that should prevent researchers from drawing conclusions about whether state constraint will hold among the larger population of hackers.
I acknowledge that the subset of hackers that can be consistently attributed to a country of origin by media or other sources is likely not representative of all hackers. This subset likely oversamples actors that have made expressions of patriotism or have adopted some other political motivation that revealed their nationality. I argue that these politically motivated hackers differ in ways that should make them a group for which constraint is most likely to be observed. Actors that have engaged in hacking because they sought to promote some political goal often differ from other hackers (i.e., cyber criminals) in that they do not anticipate some private financial gain. Because they do not expect to personally profit from hacking activity, politically motivated hackers may be easier to dissuade. The subset of politically motivated hackers also captures those patriotic hackers that should seek to promote the government’s interests, meaning that constraint can be exercised through low-cost means like direct appeals. Given these systematic differences, I caution against generalizing the finding of state constraint in the EuRepoC sample to all contexts. However, the finding is informative because if control is not observed among this sample, then this provides strong evidence against the assertion that states can constrain hackers.
EuRepoC data relies on public reporting. Because EuRepoC data draws from attributions made by targets, this presents the possibility that selective reporting is contributing to the empirical results. If targets do not want other states to believe that they have poor cybersecurity, then they may not report when they fall victim to hacking. In the context of ITU elections, this logic would imply that candidates may decrease reporting of their own victimizations. Empirically, this would mean that an observed decrease in hacking during ITU elections could be the product of less self-reporting rather than constraint.
To address this concern, I leverage a separate data source. Zone-H is an online archive of website defacements that receives hundreds of thousands of reports annually. For over two decades, hackers have used Zone-H to self-report the websites that they have vandalized. Zone-H requires hackers to submit verifiable information about defacements. Each defacement is linked to a unique notifier handle that identifies the hacker, which allows researchers to collect the defacement histories for specific actors. Because Zone-H data is reported by hackers and not targets, any observed relationship between non-state hacking and ITU elections cannot be the product of whether the target chooses to report victimization.
To collect a sample of non-state hackers with an identifiable country of origin, I begin with the EuRepoC data. As noted above, a central challenge to data collection efforts in the cyber domain is attribution uncertainty. Attackers often attempt to conceal their identities, using pseudonyms or fake addresses that mask their name and location. This makes it difficult for analysts to attribute operations to specific actors or countries with certainty. While this difficulty is inherent to the study of cyber operations, the EuRepoC’s data collection process helps mitigate attribution uncertainty. The EuRepoC collects and updates attribution information by checking multiple sources (media reporting, IT organizations’ investigations, and government statements). This helps coders determine whether an actor’s country of origin is reported consistently.
To expand my sample, I also leverage the University of Maryland’s CISSM Cyber Event Database (Harry and Gallagher 2018). The CISSM data collects hacking incidents by regularly scraping media sources. While this generates a large sample of non-state hackers, CISSM does not validate attribution information. To avoid misattribution, I only include hacking groups identified in the CISSM data that have been attributed consistently across media outlets and cybersecurity or intelligence reports. For example, the Ashiyane Digital Security Team is coded as an Iranian hacking group in the CISSM Cyber Event Database. This designation is based on media attributions made in the aftermath of several high-profile cyber attacks. I include the Ashiyane Digital Security Team in my sample because this group has also been attributed to Iran by cyber threat research organizations such as Insikt Group and the International Institute for Counter-Terrorism (INSIKT 2019; Spadoni 2019). Based on digital forensics and interviews with Iranian hackers, these organizations have concluded that the Ashiyane Digital Security Team operates from Iran. In total, I compile 78 hackers with an identifiable country of origin who have reported defacements on Zone-H (see Appendix A2). Scraping the defacement histories for these actors results in a dataset with 10,628 unique defacements from 2000 to 2022.
Treatment
The unit of analysis is country-year. I code a dummy variable as 1 when a country runs as a candidate in a ITU election year. According to ITU rules, a member state may announce their candidacy up to 6 months before the election. Because each Plenipotentiary Conference is always scheduled between September and November, the campaign period always falls within the calendar year that the election is held, which makes year an appropriate temporal unit of analysis.
Selection
A research design that leverages ITU candidacy must confront selection bias. States that choose to run for ITU bodies consistently have populations with greater technical capacity than non-candidate states. This technical advantage manifests in a greater capacity for non-state hacking. The annual average number of cyber operations originating from candidates is greater than non-candidates across most years in the sample (see Appendix B1). The selection problem is compounded by ITU rules that allow states to run for reelection without restriction, meaning that technically advanced states like Russia, China, and the US return as candidates in every election cycle.
Using a cross-national approach requires comparison with a control group that approximates the treatment group’s unobserved counterfactual. However, selection complicates the identification of the treatment effect size by obscuring the proper counterfactual. In short, ITU candidates lack an appropriate control group among non-candidates. To illustrate this point, I explore whether candidate status remains a positive predictor of non-state cyber-attacks across different subsets of non-candidate states. Even when limiting the comparison to non-candidate states that have ever run for ITU election or states that average at least 25 percent internet usage among their population from 2000 to 2018, the non-candidate control group is systematically different when compared along the dimension of non-state hacking (see Appendix B1).
To address the selection problem, I conduct a within-case comparison across time for each country-election spell. I define an election spell as a 4 year period (3 years prior to an election and the year of the election). Because 101 countries selected candidates at least once from 2000 to 2018, I have a reasonable sample that allows comparison between election years and non-election years. I use a country-election spell fixed-effects approach to mitigate concerns that changes over time could explain both ITU candidacy and the exercise of control over cyber-attacks. 5 Although it is unlikely that variation in technical capacity should correspond with ITU election years across time, circumscribing the temporal range to four-year election spells prevents any secular trend from explaining variation in the technical capacity of all states.
To further address this concern, I also control for several confounders that could explain both the decision to select into ITU candidacy and a government’s cybersecurity capacity. A government’s cybersecurity capacity is likely a function of the latent technical knowledge available within their society. Scholars have found positive correlations between measures of science and technology (S&T) knowledge and countries’ rankings on various cybersecurity capacity indices (Calderaro and Craig 2020). While latent knowledge could explain a government’s ability to better identify and mitigate non-state hacking, it could also lead the government to assign greater importance to representation on bodies that formulate global network standards.
A key driver of S&T knowledge is a country’s ICT industry. As commercial activity in the ICT sector grows, governments will have a larger pool of expertise that they can draw on to improve their own technical proficiency. However, ICT industry should also lead governments to be concerned with the ITU’s standard setting activities. The ITU’s regulatory decisions can have important implications for the global competitiveness of a country’s ICT companies. The ITU can advantage certain companies over others by issuing standards that require technology producers to adopt patented technology. These standards known as standard essential patents (SEPs) can “provide enormous economic advantages to companies that hold patents on technologies essential to those standards” (Schaefer and Pletka 2022, 7). To block the confounding path between ICT industry and cybersecurity capacity, I control for a country’s annual ICT service exports (WDI 2022). I exclude ICT good exports to avoid measuring low-skill production of physical components for technological goods. I also include controls for the number of S&T journal articles published and the percentage of the population that uses the internet for each country-year. 6 These variables help proxy for the sophistication of a country’s ICT industry even if their economy is not export-oriented. These controls vary considerably from year to year, meaning that short-term changes in ICT industry should not confound the empirical results.
Findings
Statistical Models.
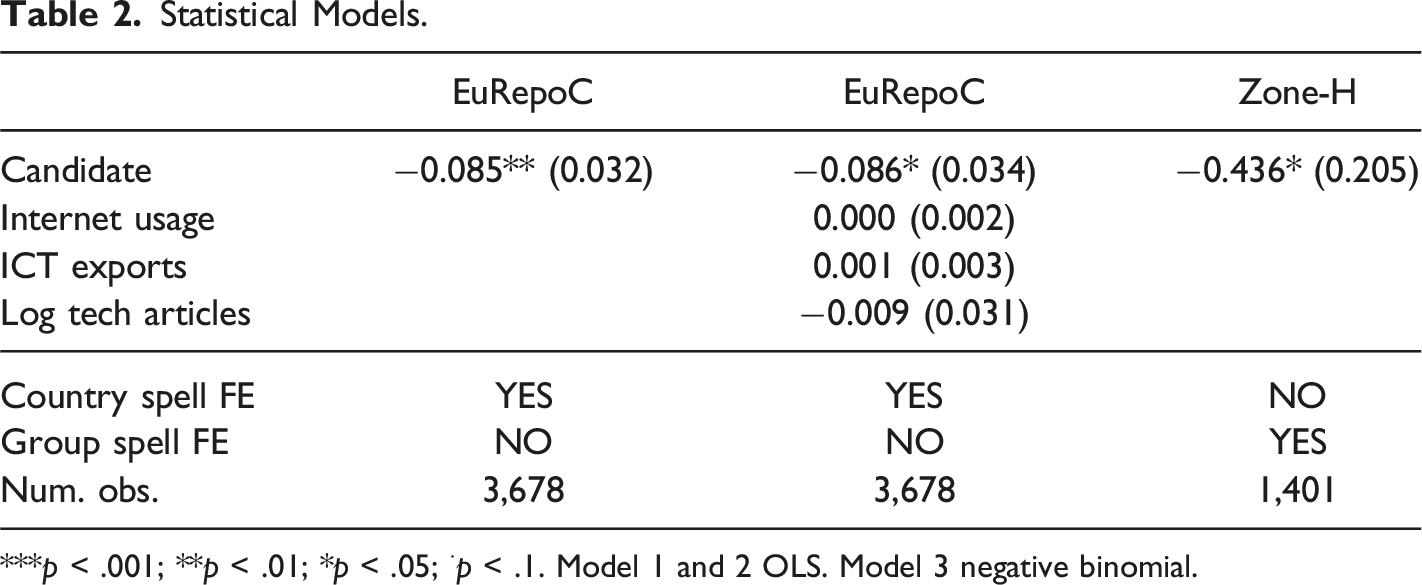
***p < .001; **p < .01; *p < .05; ⋅p < .1. Model 1 and 2 OLS. Model 3 negative binomial.
When characterizing the substantive effect, it is important to note that only 39 countries in the EuRepoC sample experience variation in the number of non-state hacking incidents during their candidacies. This means that the negative effect observed depends critically on the variation experienced by a sub-sample of candidate states (see Figure 2). This suggests that the substantive effect may be underestimated. Outcome invariant units likely depress the size of the reported coefficient. In terms of generalizability, the negative relationship cannot describe control for those countries that never experience variation in the EuRepoC data. However, the states that experience outcome variation within country-spells account for 86 percent of all non-state attacks in the total sample of states. In other words, while the negative relationship cannot generalize to most states, it describes the ability to constrain non-state hacking for those states that experience the most non-state cyber incidents in the EuRepoC data. Candidates experiencing variation in attack initiation (EuRepoC).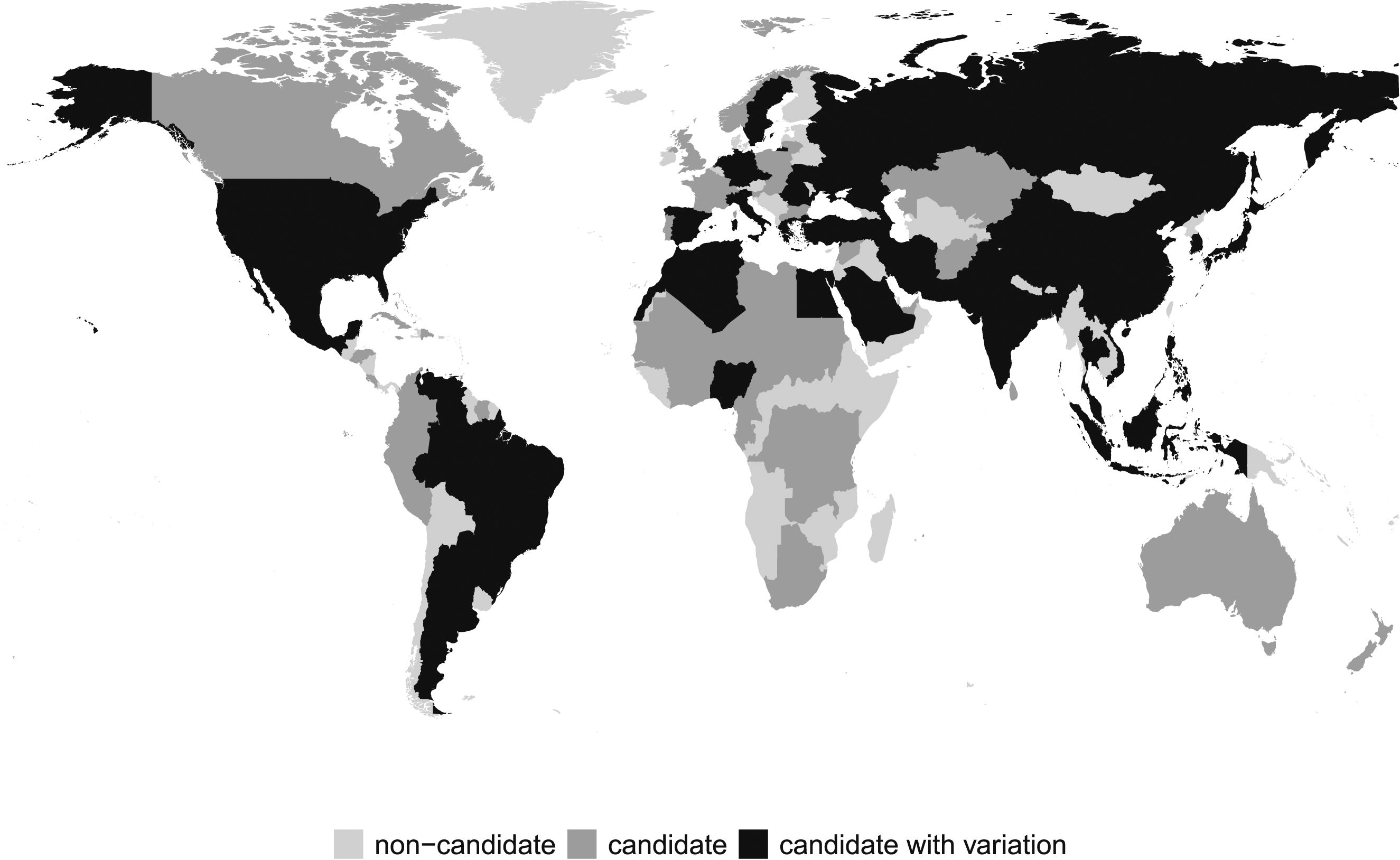
Model 3 leverages the Zone-H data. Because the unit of analysis is hacker-year rather than state-year, I use hacker-spell fixed effects to estimate the difference in the number of attacks initiated by each hacker in the year of the election compared to the 3 years prior to the election. To handle overdispersion of the outcome variable, I use a negative binomial regression. 7 The selection problem observed in the EuRepoC data holds in the Zone-H sample as well. Candidate states experience more non-state attacks originating from their territory than non-candidate states. To address the selection effect, I again conduct a within-case approach.
The model produces a statistically significant negative coefficient, confirming the results from the EuRepoC data. The average marginal effect across hacker-spells is 1.93 fewer attacks, which is substantively significant considering that this represents the average reduction across more than 350 group-spells. To calculate the average marginal effect for Model 3, I generate fitted values for each row of the original data and take the mean. I calculate confidence intervals around this average using parametric bootstrapping. Ultimately, the Zone-H data provides strong evidence that the negative relationship between ITU elections and non-state cyber aggression is directly related to the aggressor’s decision to initiate cyber operations rather than strategic reporting by targets.
Some qualitative examples can help illuminate how the mitigation of non-state hacking during ITU elections occurs in practice. Tanzania heavily emphasized the government’s cybersecurity efforts in their 2014 candidacy for the ITU council. In his call for “ITU members to vote for Tanzania to the ITU Council,” Tanzania’s Minister of Communications, Science, and Technology highlighted several programs that began in the lead up to the 2014 ITU election. The Minister noted that Tanzania had initiated their National Computer Security Emergency Response Team (TZ-CERT) earlier in the year “to coordinate responses to cyber incidents at national level” (Marawa 2014). TZ-CERT began efforts to investigate and mitigate cybercrime incidents, including a program that gathered information on cybercriminals by baiting them into exploiting fake network vulnerabilities. The Government of Tanzania also called attention to their implementation of the Domain Name System Security Extensions (DNSSEC) to enhance the DNS security (Marawa 2014). DNSSEC helps authenticate websites by ensuring that data coming from a queried domain originates from an expected source, which helps prevent cyber-attacks that reroute users to malicious sites.
In 2018, the Philippines’ campaign for the ITU Council emphasized the adoption of their National Cyber Security Plan (Rio 2018). This executive action established a national database for monitoring and reporting cybercrimes, and required victims to report network security breaches to this database. The National Cyber Security Plan also set out to build cybercrime law enforcement capacity, leading the Philippines to increase the personnel of the National Police Anti-Cybercrime Group (ACG) from 162 to 888 in 2018 (NPC 2018). These regulatory changes coincided with a spike in cybercrime arrests in the Philippines. The ACG reported a 291 percent year-over-year increase in the number of cyber criminals apprehended in 2018 (Tupas 2019). In the same election year, Mauritius’s campaign highlighted the establishment the Cybercrime Online Reporting System, which also allowed citizens to report cybercrime incidents. The program was cited as evidence that the Government of Mauritania had taken steps to address the “the costs and frequency of cybercrime incidents” in their country (Sawmynaden 2018).
Beyond augmenting technical and law enforcement capacities, ITU candidates have also been observed developing legal frameworks and increasing penalties for cybercrime during their candidacies. In 2022, Uganda ran an aggressive campaign for the ITU Council. The country requested support for their candidacy during high-level diplomatic visits to other African countries (Asiimwe 2022; Kiiza 2022). In their campaign, Uganda listed cybersecurity as a top priority (UCC 2022). The prioritization of cybersecurity was also evidenced by a 2022 amendment to the criminal code that required 10 years imprisonment for individuals who “without authorization, access another person’s data or information” (Malik 2022). In a similar move, Bahrain issued their first cybercrime law (Law no. 60) during their candidacy in 2014, which observers labeled as a “crack down on cybercrime” (IP 2014). The legislation set criminal penalties for gaining “unauthorized access to a computer system or network” (IP 2014).
While not exhaustive, these examples show some of the tools that candidates have leveraged to increase the costs associated with hacking. Governments have adopted technological changes, increasing the level of technical sophistication needed by hackers to successfully breach network security. They have also increased the potential costs associated with hacking, making the threat of criminal punishment more salient (1) by expending resources on the prosecution of cybercrimes and (2) by adopting regulatory changes that impose steep penalties for malicious cyber activity.
Discussion
The empirical analysis provides evidence that state actors do exercise constraint over non-state hackers. Scholars of cyber norms have previously suggested that anarchy may be the “the dominant outcome” in cyberspace, but governments demonstrate a willingness to mitigate non-state hacking despite the apparent advantages of feigning incapacity (Finnemore and Hollis 2016). Having demonstrated that states can achieve a necessary condition for successful international cooperation on non-state hacking, this article prompts further investigation of the institutional arrangements that would best facilitate this cooperation. Several features of constraint in the ITU context provide helpful indicators that can inform this investigation.
First, governments achieved measurable constraint because they expected to be evaluated on the basis of their cybersecurity reputation. During ITU campaigns, states exhibit an awareness that their record of mitigating non-state hacking will inform ITU members’ assessments of whether they will continue to act responsibly in cyberspace. International relations scholars have argued that reputation can facilitate cooperation when (1) reputation is used by observers as a source of information about future behavior and (2) when a good reputation is valuable to state actors (Axelrod 1981). The dynamics of ITU campaigns demonstrate that the first requirement can be met. Governments appear to believe that observers will use their cybersecurity reputation as a source of information to predict future behavior in cyberspace.
Second, governments achieved constraint even without a formal definition of what constitutes due diligence or acceptable behavior in cyberspace. Legal scholars have argued that a barrier to cooperation in cyberspace is that governments do not share an understanding about what actions must be taken to show due diligence in the mitigation of non-state hacking (Lemnitzer 2022). These scholars have called for a universal definition of what “practices should be considered due diligence duties that bind rich and poor states alike” (Lemnitzer 2022, 806). However, the lack of a unified definition did not hinder constraint in the ITU context. This suggests that states may already share a baseline understanding of acceptable behavior in cyberspace, cultivated by ongoing efforts to articulate normative frameworks and collective efforts to globally address cybercrime. In short, articulating specific obligations may not be a precondition to successful cooperation. Governments seem to demonstrate a shared understanding about acceptable behavior in cyberspace that is sufficient to impel constraint.
Finally, international efforts to achieve cooperation on non-state hacking must account for limitations in the ability of governments to exercise constraint. Evidence of constraint during ITU elections is not complete. I find a measurable decrease in the number of cyber operations, but the effect is not total. Many incidents of non-state cyber aggression still originate from candidate states in ITU election years. This result shows that states are neither powerless to restrain nor capable of exerting complete control over non-state hackers. For policy practitioners, this suggests that obligations to prevent transboundary cyber aggression can meaningfully reduce cyber aggression, but that states will be unable to comply if requirements are too strict. Akin to international agreements on environmental pollution, policymakers will need to carefully calibrate expectations so that cooperation is not hindered by the imposition of terms that governments cannot fulfill.
The ITU case highlights a mechanism through which international institutions could calibrate expectations. In the ITU case, states did not exert effort to mitigate non-state hacking because they sought to align with universally agreed upon standards. Instead, states were impelled to exercise constraint because they knew that their efforts would be evaluated relative to the efforts of other states. This mechanism suggests that governments could make progress by participating in an international regime premised on relative standards, similar to those institutions that have arisen to promote business-friendliness norms (Doshi et al. 2019; Towns and Rumelili 2017). In this type of regime, governments would not exert effort to comply with some absolute benchmark, but rather “pay attention to the activities and position of others” to determine what constitutes acceptable behavior (Towns and Rumelili 2017). The benefit of this approach is that states would compete with peers according to their capacities rather than meeting a minimum standard. Future work that pursues this line of inquiry would need to assess the mechanisms by which international institutions could pull states into competition with each other over their cybersecurity reputation.
Conclusion
Policymakers have called for cooperative agreements to address transnational cyber aggression by non-state actors. However, empirical tests using large-N quantitative analysis have yet to show that states demonstrate the capacity to constrain transnational hacking when incentivized to do so. This article addresses this gap. I develop a strategy that leverages variation in the observable interests of state actors. In a sample of attacks initiated by hackers with known countries of origin, I find that governments reduce cyber incidents originating from their territory to manage their reputation during ITU candidacy. This finding has important implications for the study of conflict and cooperation in the cyber domain.
First, the empirical finding highlights the need for research on what factors shape a government’s ability to influence the frequency and timing of non-state cyber operations. My empirical test only identifies a reduction among a subset of countries. While this subset includes countries that experience a large number of non-state attacks originating from their territory, the results cannot speak to whether other countries are similarly capable of exercising control over non-state hackers. It is plausible that ITU candidates are systematically different along dimensions that could also explain their ability to constrain. For example, candidates may have a higher baseline level of technological sophistication in their population, which correlates with a more sophisticated governmental capacity to identify or disrupt non-state cyber actors. Studies that investigate whether constraint can be similarly exercised by all states would help inform how interstate agreements should calibrate requirements for each country according to their capacities.
Second, scholars should study cyber conflict at the level of nonstate actors. This research article signals that non-state hackers adjust their activities in accordance with the interests of governments, which suggests that researchers can uncover patterned behavior among non-state hackers that reflects the strategic calculations of state actors. Political scientists should build on these findings by characterizing the logic behind a government’s decision to either constrain or empower non-state cyber actors in their territory. States that choose to constrain hackers must expend considerable resources and make important strategic tradeoffs. Still, this article shows that international political factors can lead governments to accept these costs. To improve our understanding of what interstate dynamics will cause governments to confront non-state hackers, future work should aim to develop a theoretical understanding of why governments choose to constrain hackers.
Supplemental Material
Supplemental Material - Do States Constrain Non-State Hackers? International Telecommunication Union Elections and Non-State Cyber Aggression
Supplemental Material for Do States Constrain Non-State Hackers? International Telecommunication Union Elections and Non-State Cyber Aggression by Conner B. Joyce in Journal of Conflict Resolution
Supplemental Material
Supplemental Material - Do States Constrain Non-State Hackers? International Telecommunication Union Elections and Non-State Cyber Aggression
Supplemental Material for Do States Constrain Non-State Hackers? International Telecommunication Union Elections and Non-State Cyber Aggression by Conner B. Joyce in Journal of Conflict Resolution
Footnotes
Acknowledgments
I thank the anonymous reviewers and editor at JCR, Brett Ashley Leeds, Songying Fang, Randolph Stevenson, Connor Huff, Amorae Times, Trang Huynh, Zheng He (Frederick), Alejandra Gonzalez, and the participants of Texas Triangle 2024 for providing insightful comments and suggestions.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Data Availability Statement
The replication files for this article are available at: https://dataverse.harvard.edu/dataset.xhtml?persistentId=doi:10.7910/DVN/SETYU7 published in Harvard Dataverse (view at: ![]() ).
).
Supplemental Material
Supplemental material for this article is available online.
Notes
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
