Abstract
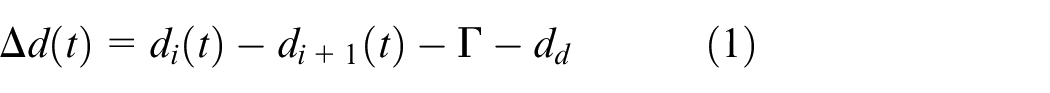
This paper aims at developing a novel detection and identification method against malicious attacks in intelligent transportation. Due to the development and applications of communication and advanced sensor technologies, intelligent transportation has faced new safety risks. In particular, the emerging malicious attacks, such as false data injection attack, can mask the destruction of physical dynamic by tampering with information in layer to fool the current detection methods. Because of this reason, an adaptive unknown input observer-based detection and identification method is developed. Firstly, a physical dynamics model of vehicle networking system is established by considering the actual physical state. Considering the spoofing characteristics of false data injection attack, an unknown input observer-based detection method is proposed. Through the design of adaptive unknown input observer parameters, the detection performance, can be improved by cutting down the state estimation error. Compared with the UIO-based detection method, simulations demonstrate that the false positive rate can be reduced 0.1%. Based on the feature of state residuals that is not sensitive to the attacked ith residual, but sensitive to other residuals, a novel identification criterion is developed. At last, simulation experiments on the Matlab verify the performance of the proposed detection and identification algorithm in intelligent transportation system.
Keywords
Introduction
As the cornerstone of future transportation, intelligent transportation system effectively applies advanced science and technology to traffic service control, and strengthens the connection among vehicles, roads, and users.1–3 As one of typical cyber-physical systems, intelligent transportation system can alleviate many traffic problems, such as traffic congestion, energy consumption, and environmental pollution.4,5 However, the openness and intelligence of communication network make intelligent transportation system more vulnerable to malicious attacks. 6 In particular, the emerging cyber-physical attacks on vehicle-to-vehicle communication can cause serious vehicle collisions. For instance, in 2019, a simulated cyber attack launched on Austin network shows the security risk on intelligent transportation system. 7 In addition, a group of hackers can remotely attack a Tesla Model. 8 For this reason, it is urgent to developing a novel detection and identification mechanism against cyber-physical attacks for intelligent transportation system.
In recent years, the safety of intelligent transportation system has been a hot issue concerned by scholars. There exist two kinds of approaches to ensure the traditional cyber networks security of intelligent transportation system, such as attack defense and attack detection. 9 In Dibaei et al., 10 lots of available attack defense methods on intelligent transportation system consisting of lots of networking vehicle are investigated. To ensure the security of vehicular ad-hoc network, a two-factor lightweight privacy-preserving authentication defense method was developed. 11 In Tan et al., 12 Tan et al. developed a novel defense method based on the authenticated key management protocol. Based on the differential game theory, an optimal defense strategy against Denial of service attack was developed. 13 By using the resilient distributed observer and distributed adaptive controller, a novel distributed control scheme against Dos was proposed in Zhang et al. 14 Fei et al. developed an attack-defense tree mode to deal with the advanced persistent threat attacks in Fei et al. 15 In Deng et al., 16 a novel resilient practical cooperative output regulation control scheme against Dos was developed. Since the above defense methods are passive defense against intrusion attacks, it is difficult for them to respond the injected attacks quickly.
To respond the injected Denial of service attack timely, a data driven-based attack detection method was proposed. 17 For detecting and mitigating the Denial of service attack (Dos), Haydari and Yilmaz 18 developed a nonparametric statistical anomaly detection-based security mechanism. A novel prevention and detection method against FDIAs was proposed to protect the power network. 19 In Wang et al., 20 an extended Kalman filter-based detection and isolation method against cyber attack was proposed. To enhance the safety of vehicle networking system, a sliding mode observer-based real-time detection method was developed in Abdollahi Biron et al. 21 Compared with the above Dos, the emerging FDIAs has a strong deceptive characteristics. By tampering with the information data in layer, FDIAs can mask the change of the physical system state. 22 For this reason, the spoofing characteristics of FDIAs can fool the above security detection mechanisms. In Guo et al., 23 Guo et al. analyzed the spoofing feature of FDIAs, and given the optimal attack strategy. In Kwon et al., 24 three kinds of stealthy FDIAs were studied based on the ability of attackers. In Taylor et al., 25 Taylor et al. studied the impact of FDIAs on the vehicular platoon that a hacker can inject false messages leading to a breakup of the vehicular system. Under limited sensor information, an AC state estimation (AC-SE) based coordinated cyber-physical attack was designed in Jena et al. 26 In a sum, the above works in Kwon et al., 24 Taylor et al., 25 and Jena et al. 26 have shown that the spoofing feature of FDIAs brings enormous challenge to the existing detection methods.
To detect the FDIAs timely, lots of research works have been devoted by scholars. A blockchain-integrated multi-agent deep reinforcement learning architecture was proposed to detect the malicious attacks in Raja et al. 27 In Karthikeyan and Usha, 28 a long short-term memory-based detection method was proposed to ensure the security of intelligent transportation. A novel reinforcement learning-based attack detection method was proposed in Li et al. 29 In Said et al., 30 a machine Learning-based detection method against FDIAs on the electricity price of electric vehicles was proposed. Considering the vulnerability of traditional communication, a state estimation and control algorithm against FDIAs was developed. 31 In Cabelin et al., 32 a machine learning-based detection and identification method against FDIAs was proposed. However, the above learning-based detection methods relay on the training of historical data. Thus, a physical dynamic model-based detection methods against FDIAs were proposed in Huang and Wang 33 and Yamamoto et al. 34 In Huang and Wang, 33 a robust state observer-based detection method against FDIAs was proposed. Yamamoto et al. 34 developed an UIO-based detection method against FDIAs in vehicle networking system based on a state residuals. Although the above detection works in Huang and Wang 33 and Yamamoto et al. 34 can reduce the complexity of attack detection, the accuracy of state estimation limits the detection performance of FDIAs. In addition, the existing detection works lack the research on the detection and identification of multiple attacks.
Motivated by the above problems, this paper develops an adaptive unknown input observer (AUIO)-based security method against FDIAs in intelligent transportation system. By considering the impact of FDIAs on the physical dynamics, a bank of parallel AUIOs are designed. Through the design of AUIOs parameters, the performance of state estimation errors can be improved. Based on the feature generated by AUIO, a novel detection and identification criterion is developed. The main contributions of this paper are listed as follow.
• An AUIOs-based detection method. Taking the change of physical dynamics into account, an AUIOs-based is proposed to address the problem that FDIAs can fool the Chi-square estimator. Compared with the existing method, the proposed detection method can improve the detection performance, such as false positive rate and state estimation error.
• A novel identification method against malicious attack. Through the design of AUIOs parameters, a bank of attack residuals can be obtained. Of noted, attack residuals are not sensitive to the attacked ith residuals, but sensitive to other residuals. Based on the above residual feature, a novel attack identification criterion is developed.
The framework of this paper is outlined as follows. Section II is the theory. The developed AUIO-based detection and identification framework against FDIAs is presented in Section III. Section IV, simulations are presented to demonstrate the performance of the developed method. Conclusion and discussion are given in Section V.
Theory
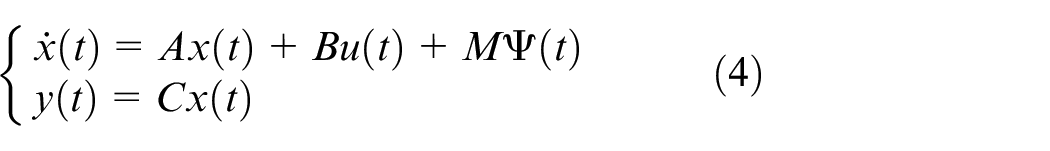
In this section, a physical dynamic vehicle networking system model is given. Then, the covert feature of FDIAs is shown. Finally, the addressing problem of this work is given.
Physical dynamic model of vehicle networking system
As shown in Figure 1, intelligent vehicle networking system consists of n vehicles, where each vehicle includes the measurement sensors and actuators. By monitoring the measured data, such as vehicle speed, acceleration and vehicle distance, the monitoring and control center can judge the running state of each intelligent vehicle. Then, the vehicle networking model can be established as follow. 35
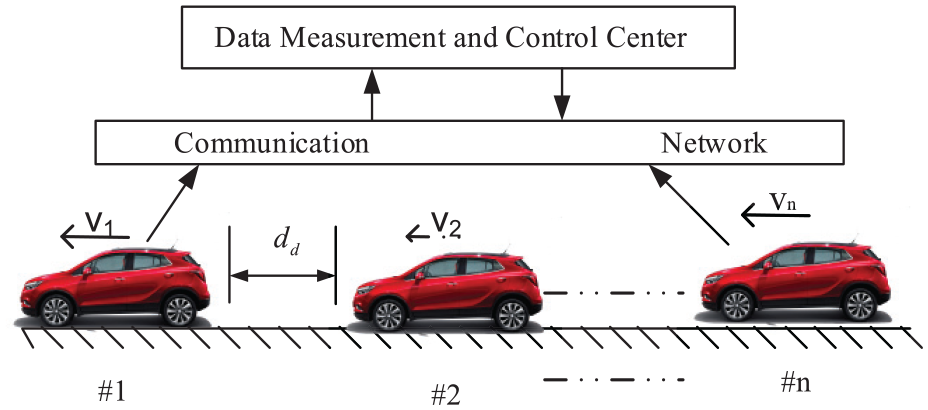
Intelligent vehicle networking system.
By using equations (1)–(3), the physical dynamic model can be rewritten as
where
Covert characteristics of FDIAs
As shown in Figure 2, data measurement and control center can monitor and control the running state of intelligent vehicle by communication channel. However, hackers can design FDIAs to tamper with the control data by stealing the communication information.
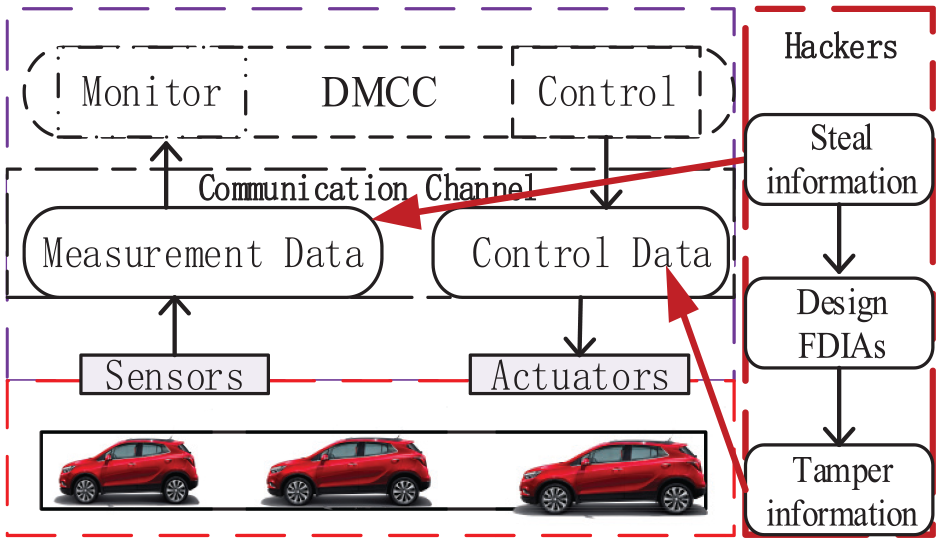
Running state of vehicle networking system under FDIAs.
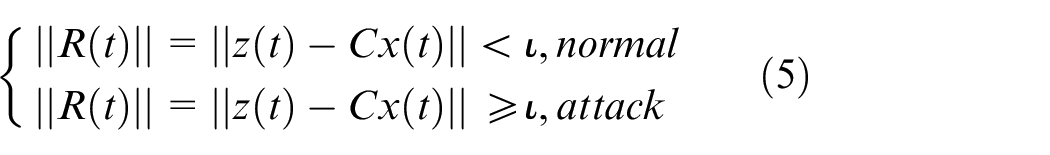
The designed FDIAs not only destroy the running sate of intelligent vehicles quickly, but also cheat the common Chi-square estimator-based detection method. According to Manandhar et al., 36 the detection criterion is given as follows.
Under Assumption 1, hackers can steal the relevant information of intelligent vehicle networking system. For this reason, the corresponding false data injection attack model can be modeled as follow. 33
with
where
Then, the measurement residual can be described as.
When the attack sequence is designed as
Obviously, the designed FDIAs can cheat the Chi-square estimator-based bad data detection method. Namely, hacker can change the running state of intelligent vehicle by injecting the above FDIAs without triggering the detection mechanism. Therefore, the detection and identification against FDIAs is urgent to ensure security of networking vehicle system.
Addressing problem
Taking the covert characteristics of FDIAs into account, this paper aims at developing a novel AUIOs-based detection and identification method based on the constructed dynamic model in equation (4) under FDIAs, that is,
where
Detection and identification framework against false data injection attacks
In this section, an AUIOs-based detection and identification method against FDIAs is developed. Based on the constructed physical dynamics model, a bank of parallel AUIOs are designed. Then, a novel detection and identification criterion is proposed, based on the feature of attack residuals.
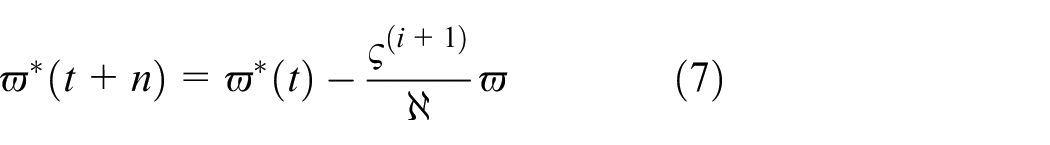
Design of parallel adaptive unknown input observer
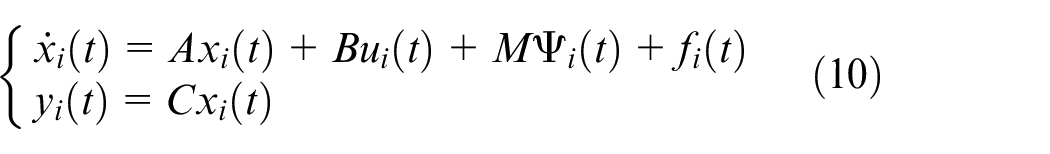
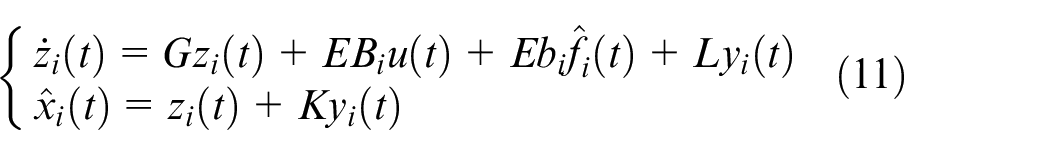
Through the physical dynamics model of vehicle networking system, the ith AUIO can be designed as.
where
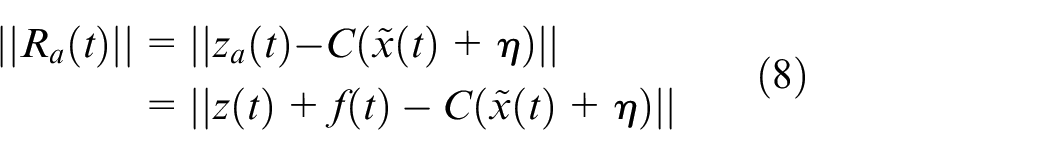
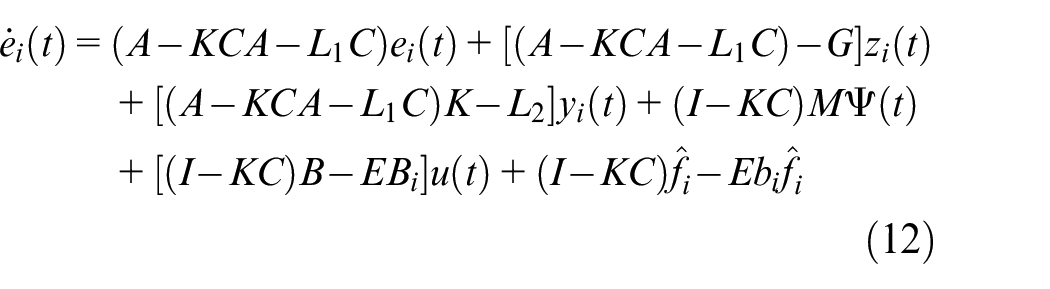
Based on equations (10) and (11), the estimation error can be obtained as
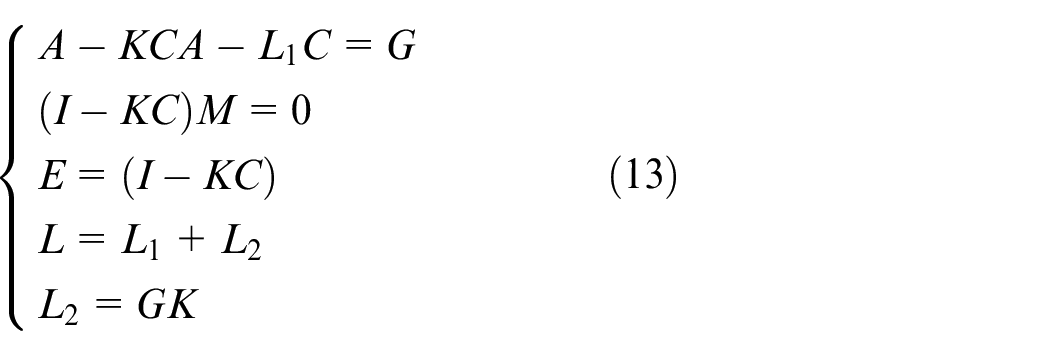
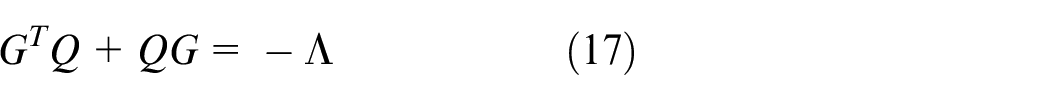
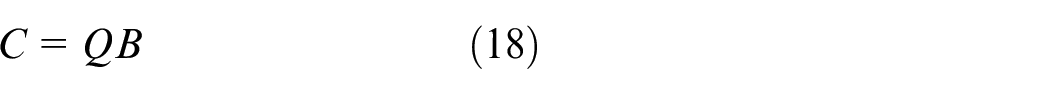
According to the work in Chen et al., 37 the above observer parameters can be chosen as follow.
To ensure the convergence of the above estimation
where
where
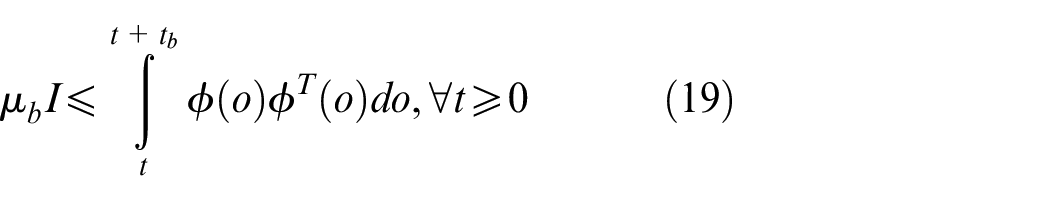
Before analyzing the stability of the designed AUIOs, the following Lemma is given. 38
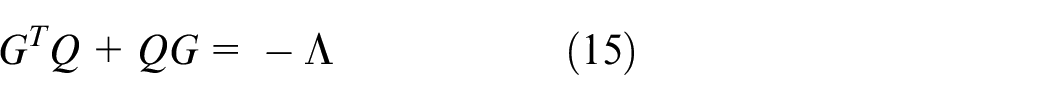
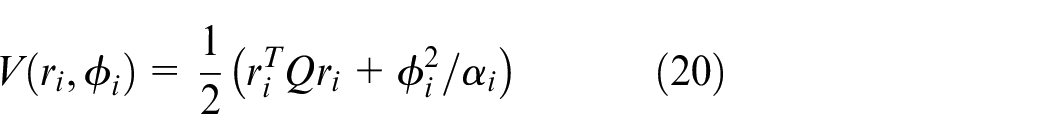
To ensure the stability of the proposed AUIO, the Theorem 1 is given as follow.
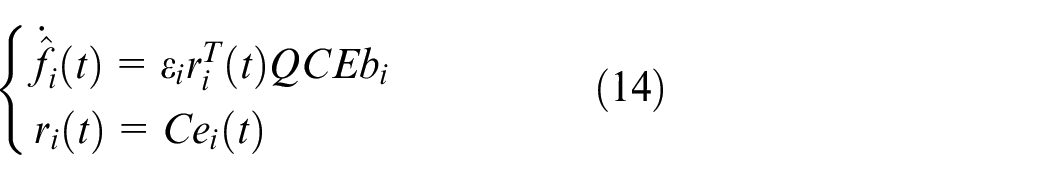
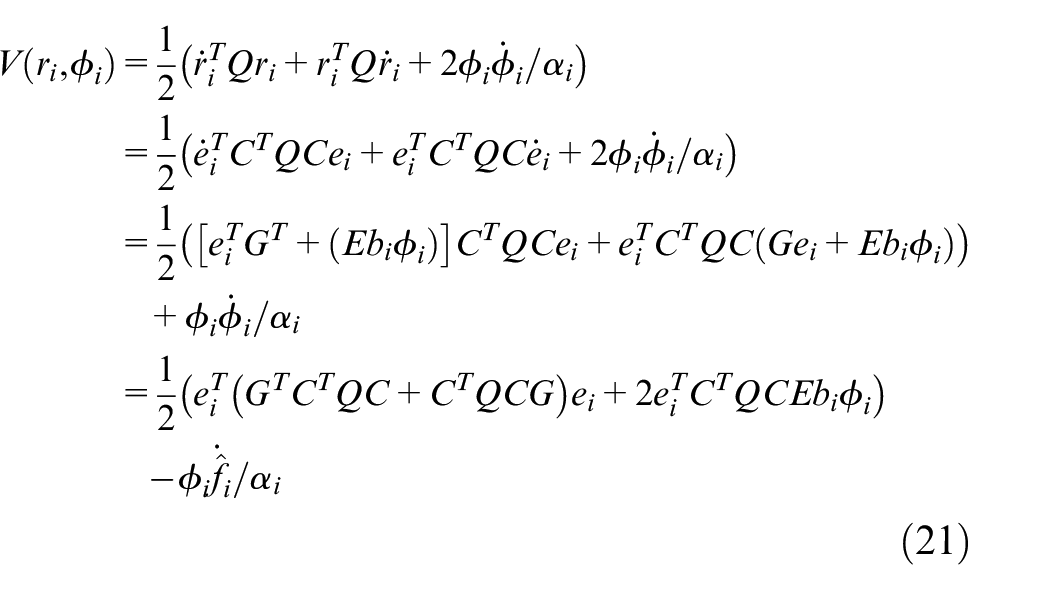
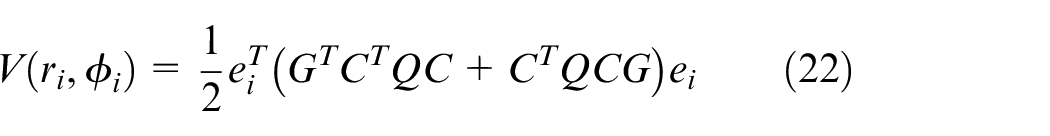
Based on equation (11) and (13), the derivative of equation (20) can be obtained as
By using equation (14), equation (21) can be rewritten as.
Since matrix
Based on equation (14), one can obtain
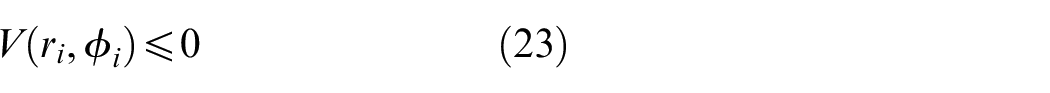
By using the Lemma 1, one can find that the residual
Theorem 1 ensures that the developed AIUOs are stable and residual
Detection and identification method against FDIAs
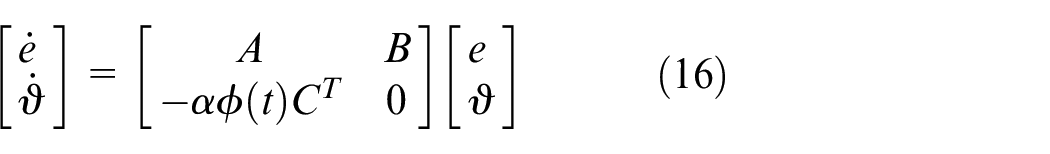
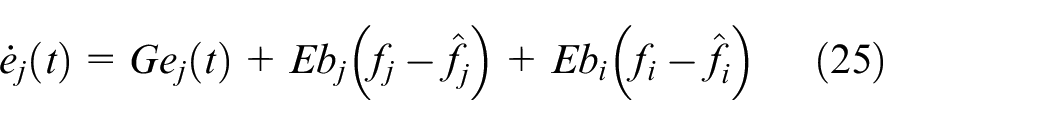
By using Theorem 1, one can obtain that the state estimation error on the ith intelligent network vehicle approaches zero. Then, the state estimation error on the jth intelligent network vehicle can be obtained as
Defining
Then, we have
Equation (27) indicates that the estimation error
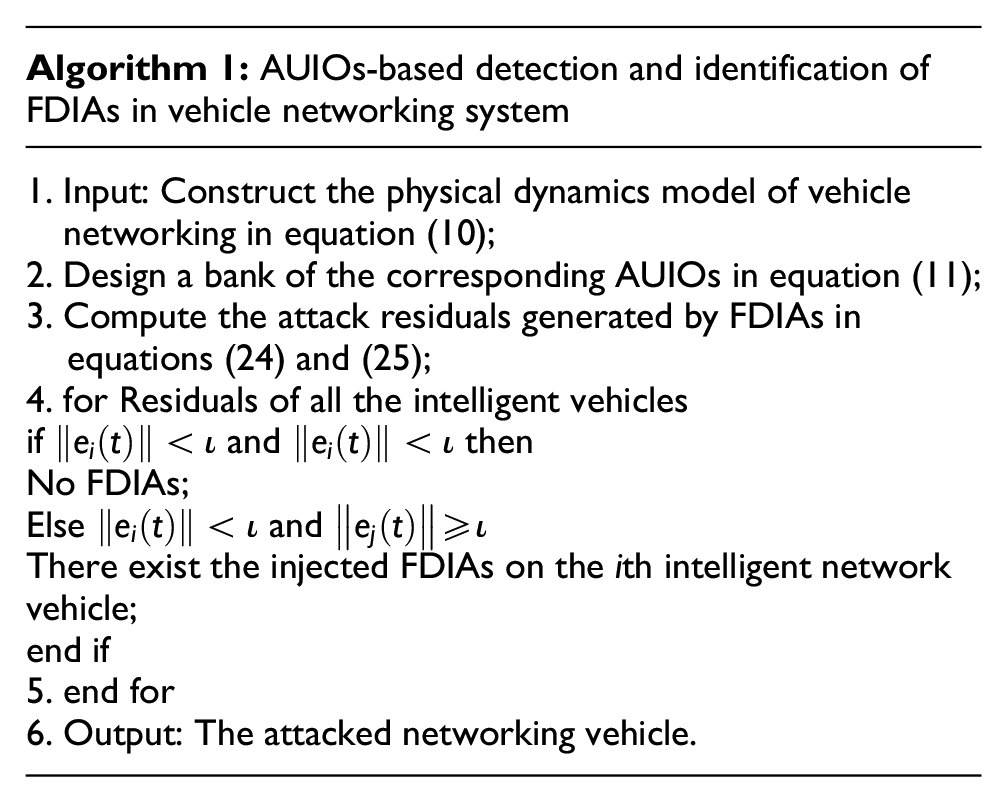
Assuming that there exist n the intelligent vehicles, the attack detection and identification process is given as follows.
Step 1: Based on the constructed physical model in equation (12), a bank of parallel AUIOs are designed.
Step 2: Based on generated attack residuals, one can judge whether there exist the injected FDIAs.
Step 3: If
Flowchart of detection and identification process against FDIAs.
Guidelines for manuscript preparation
This section presents simulation experiments on intelligent transport including of six networking vehicles to verify the effectiveness of the developed detection and identification framework against FDIAs. It is assumed that the above intelligent vehicles including of cruise control system can drive longitudinally on the road in Figure 1. Simulation part parameters are given:
Situation 1 is to consider the detection and identification of single FDIA injected on the intelligent vehicle networking system. Compared with the work in Huang and Wang 33 and Yamamoto et al., 34 the attack detection performance against FDIAs can be improved.
Situation 2 is to show the effectiveness of the proposed detection and identification method against multiple FDIAs on the intelligent vehicle networking system.
Situation 1 effectiveness of the developed detection and identification method
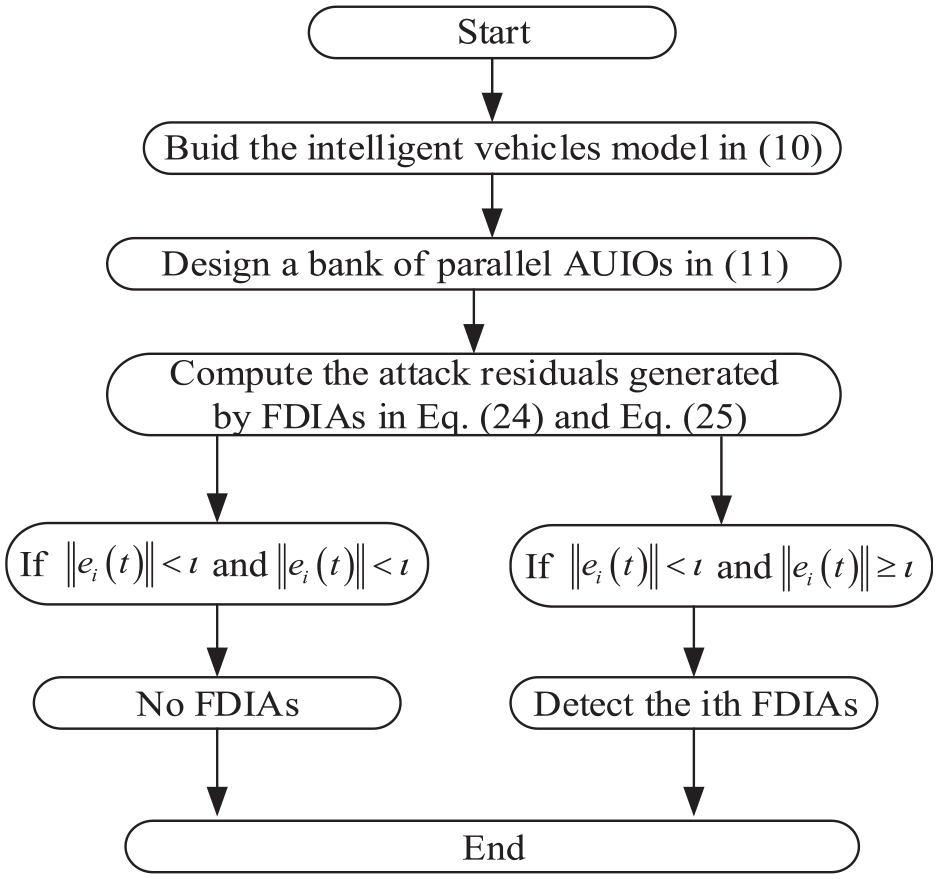
Detection and identification of single continuous attack
Assuming that hacker can inject the single FDIA into the third intelligent vehicle at
The change of attack residuals. (a) First vehicle, (b) second vehicle, (c) third vehicle, (d) fourth vehicle, (e) fifth vehicle, and (f) sixth vehicle.
Based on the above simulation results in Figure 4, one can find that only the attack residual does not exceed the precomputed threshold, namely,
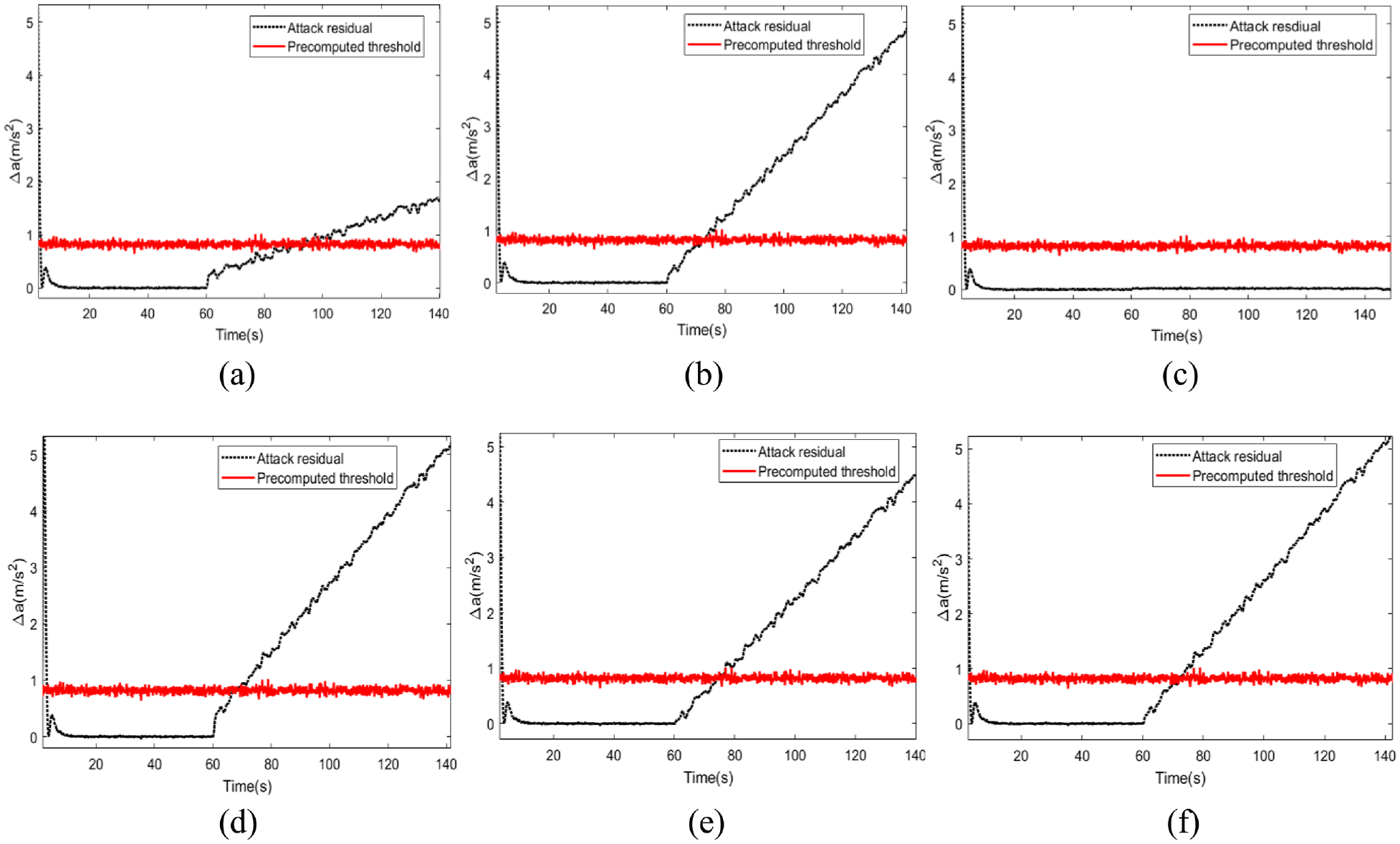
Detection and identification of single intermittent attack
Assuming that hacker can inject the single FDIA into the second intelligent vehicle at
The change of attack residuals. (a) First vehicle, (b) second vehicle, (c) third vehicle, (d) fourth vehicle, (e) fifth vehicle, and (f) sixth vehicle.
Based on the above simulation results, one can find that only the attack residual does not exceed the precomputed threshold, namely,
Performance analysis of the developed detection and identification method
To verify the detection performance of the developed detection algorithm, a bank of robust state observers and adaptive unknown input observers can be designed to observe the running state. Then, the corresponding errors of state estimation can be obtained, as shown in Figure 6(a). It is obvious that the error of state estimation under adaptive unknown input observers is smaller than that under robust state observers. Compared with the UIO-based detection work in Huang and Wang 33 and Yamamoto et al., 34 the performance of state estimation error can be shortened. Furthermore, the false positive rate under the precomputed threshold is used to evaluate the detection performance against FDIA, as shown in Figure 6(b). Obviously, the maximum false alarm rate can be reduced 1%. Meanwhile, the maximum detection rate can be enhanced 0.8%, as shown in Figure 6(c).
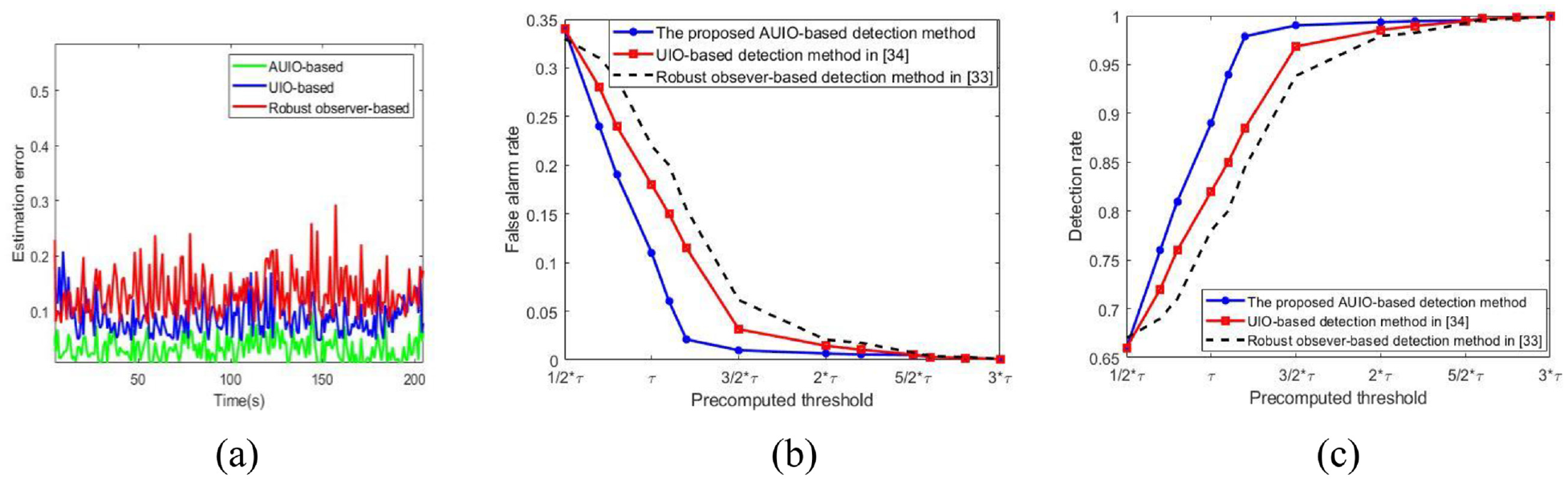
The analysis of detection performance against FDIAs under two detection methods. (a) comparison of state estimation errors and (b) comparison of false positive rate and (c) comparison of detection rate.
In addition, we have investigated the relationship of detection rate and attack strength under different precomputed threshold, as shown in Figure 7. With the increase of attack strength, the detection rate against FDIAs is the highest when the precomputed threshold
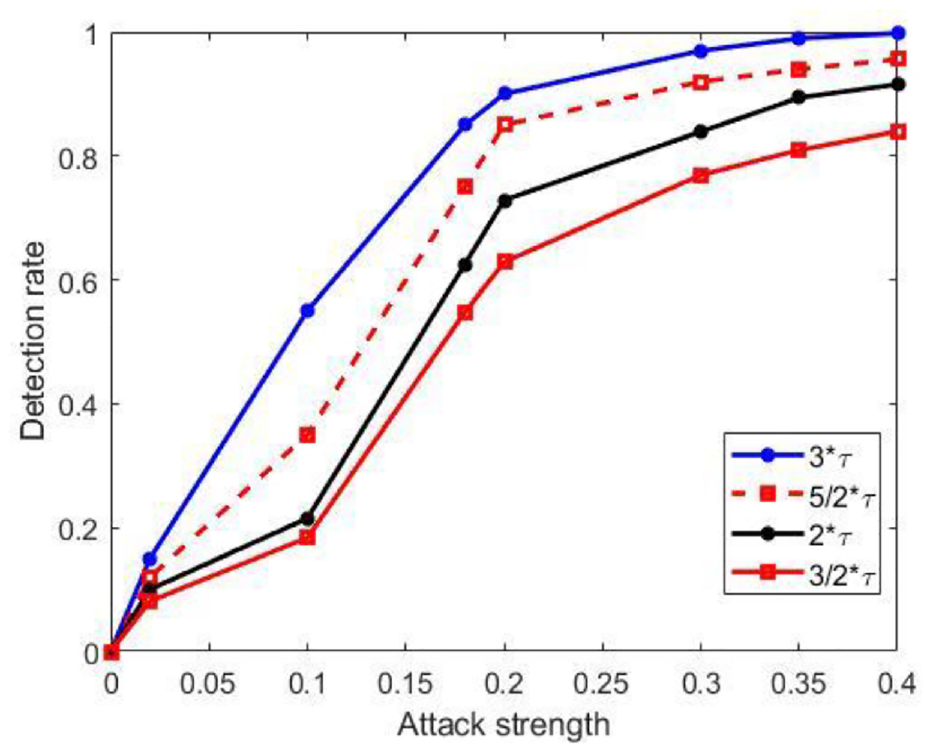
The analysis of detection rate and attack strength under different precomputed threshold.
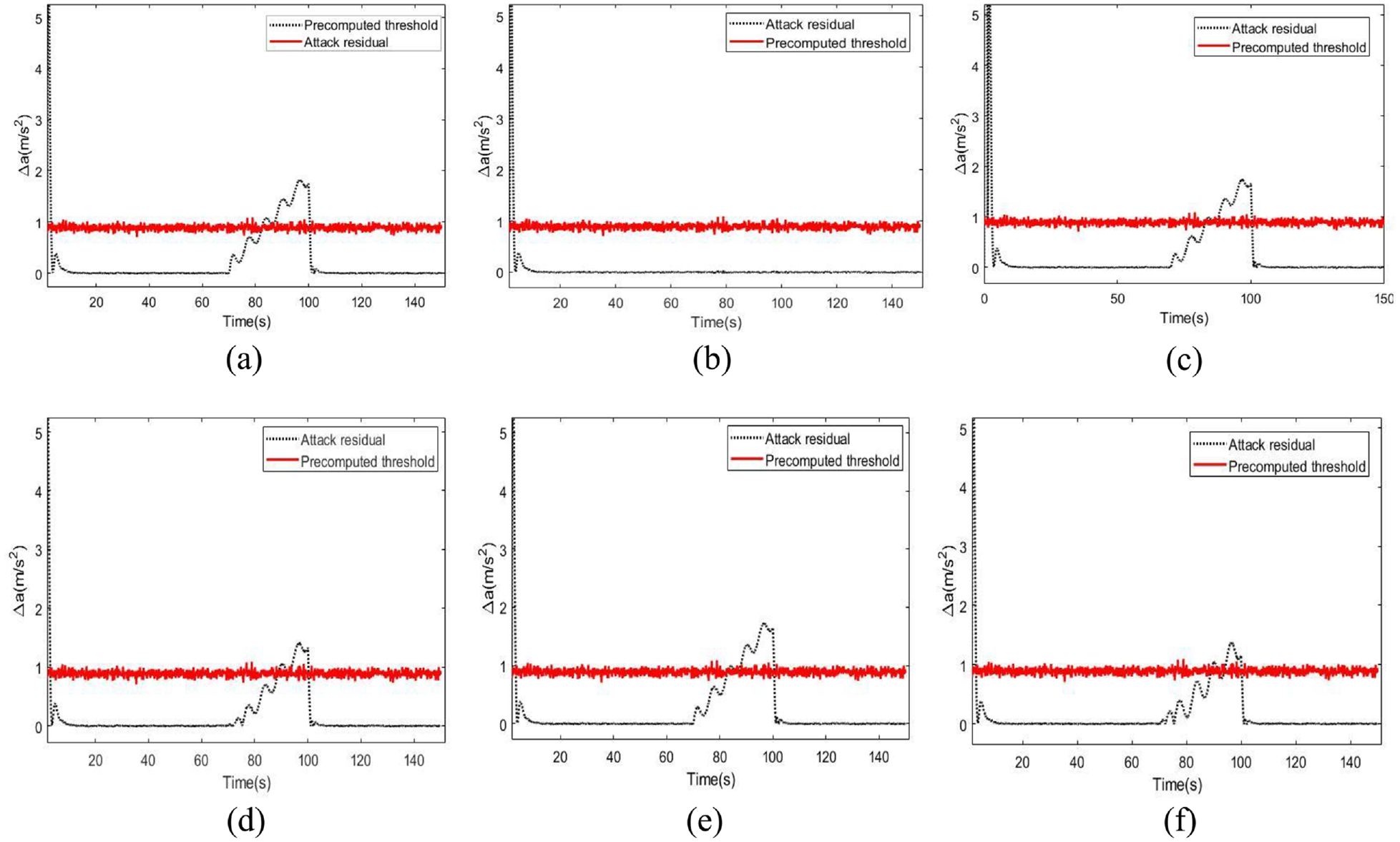
Situation 2 detection and identification of multiple FDIAs injected
It is assumed that multiple FDIAs can be injected into the second, fourth and sixth intelligent vehicles at
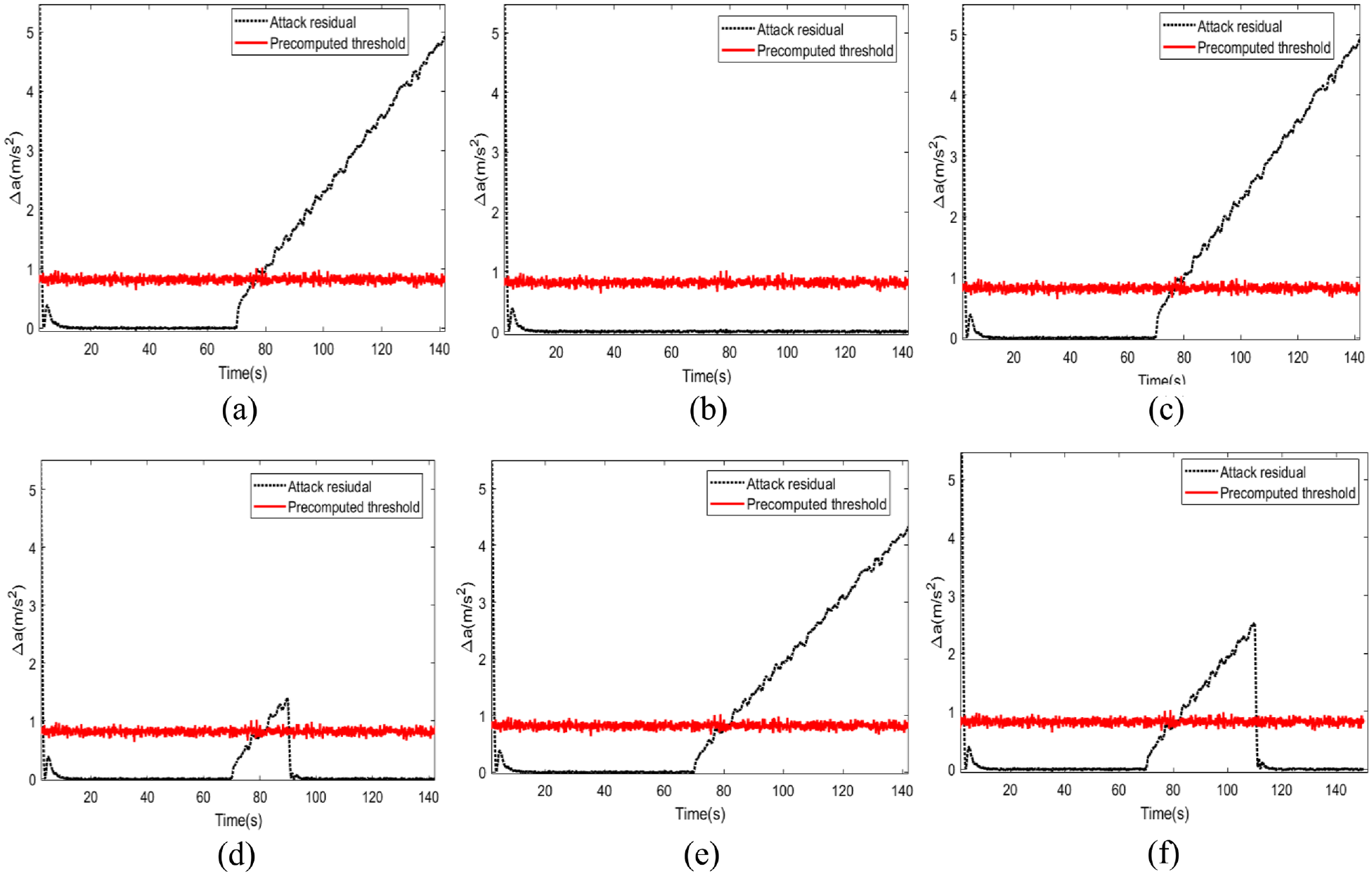
The detection and identification results of multiple FDIAs. (a) First vehicle, (b) second vehicle, (c) third vehicle, (d) fourth vehicle, (e) fifth vehicle, and (f) sixth vehicle.
Obviously, one can find that the attack residual
Through simulations in Figure 8, one can find that the attack residual is insensitive to the attacked ith residual, but sensitive to other residuals. In other words, attack residual is insensitive to the attacked second residual, but sensitive to the ith (i = 1,3,4,5,6) residuals at
Conclusions and discussion
An AUIOs-based detection and identification method against FDIAs in intelligent vehicle networking system is proposed. Through the constructed physical dynamics model, an AUIOs-based detection method is developed. And the error of state estimation can be improved to reduce the false positive rate. Furthermore, a feature of attack residuals-based identification method against multiple FDIAs is proposed. Finally, the simulation results verify the performance of the proposed detection and identification method on the intelligent vehicle networking system.
This paper proposes a mode-based detection and identification method against FDIAs, there still exist lots of problems needed to further study as follows. (1) The effect of the uncertainty under the proposed detection method. (2) How to deal with the influence caused by communication delay. (3) How to detect and identify the mixed attacks, such as FDIAs and Dos.
Footnotes
Appendix
Acknowledgements
Thanks to the financial support provided by the National Natural Science Foundation of China (Nos. 61803154).
Author Contributions
Conceptualization, P.C. and J.P.; methodology, J.P; data curation, J.P; writing—original draft preparation, P.C; writing—review and editing, P.C and J.P.; visualization, P.C.; All authors have read and agreed to the published version of the manuscript.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the National Natural Science Foundation of China under Grant 61803154