Abstract
A novel proactive method to defend against false-data-injection (FDI) attacks is proposed in this paper. FDI attacks have a high degree of concealment, which can seriously threaten the security of cyber-physical systems (CPS). Therefore, a new watermark-based encryption defense strategy is proposed to improve the attack detection rate. Moreover, the proposed watermark-based approach cannot affect the system performance in the absence of attacks, and the
Introduction
Cyber-Physical Systems (CPS) are complex systems, which use computing, control, and communication to connect the network to the physical environment.1–3 CPS can improve the ability of traditional engineering systems, and it can be applied to different environments, such as intelligent transportation systems, 4 water supply systems, 5 intelligent grids, 6 etc. On the other hand, the network security of CPS is also facing great challenges. So far, many malicious attacks against CPS have been reported, such as the Stuxnet virus targeting Iranian nuclear facilities in 2010, and an upgraded version targeting Iranian nuclear facilities in 2018. 7 The Ukrainian power grid was attacked in 2015, causing a massive blackout. 8 If CPS is attacked, it may cause great loss to the economy, society and security. Therefore, researchers have paid extensive attention to the attack detection.
To ensure the safety of CPS, the defense technology is essential. For example, the authors in 9 proposed three security vulnerabilities, that is, privacy, integrity, and effectiveness, which are considered to be important for protecting the information. According to, 10 the attacker’s ability depends on the knowledge of the system model, disruptive resources, and disclosure resources. The FDI attack studied in this paper belongs to deception attacks, such as the false data injection attack (FDIA) mentioned in 11 and dynamic false data injection attack (DFDIA) mentioned in. 12 which are highly concealed and destructive.13–16 To ensure that the bad value detection of the detector is bypassed and the control performance of the system is affected, attackers can use information transmission network vulnerabilities to inject false data carefully into sensors and/or actuators. Through careful design, an attacker can destroy the system’s control performance and deceive the abnormal detector. Thus, FDI attacks have a greater threat to the security of CPS.
The approaches to detect malicious attacks can be divided into passive and active detection methods.
17
As we all know, most anomaly detection algorithms are passive, such as the residual-based
In this paper, a novel proactive watermark-based defense strategy is proposed to improve the detection rate of false-data-injection attacks. The contributions of this paper are summarized as follows:
A new watermark-based encryption strategy is designed, which can guarantee that the system performance cannot be affected by the watermarks in the absence of attacks. Different from the existing static watermarking methods, dynamic watermarking implements encryption through time-varying random parameters, which not only avoids the long-term monitoring and cracking risk, but also ensures the system performance without any attack.
FDI attacks are divided into two different types, namely, additive and multiplicative FDI attacks. Moreover, three different attack detection situations are analyzed and the proactive attack detection method proposed in this work can greatly improve the detection rate.
The rest of the paper is given as follows. Problem formulation is introduced in Section 2 and the main results are provided in Section 3. Attack detection in different scenarios is given in Section 4 and the simulation results are shown in Section 5. Finally, some conclusions are given in Section 6.
Problem formulation
In this section, the system block diagram under a watermarking encryption proactive defense strategy is provided, which is shown in Figure 1. The system uses dynamic watermarking encryption strategy to improve the detection capability of FDI attacks. It is composed of plant, sensor, encoder, decoder, estimator, detector, and attacker modules.
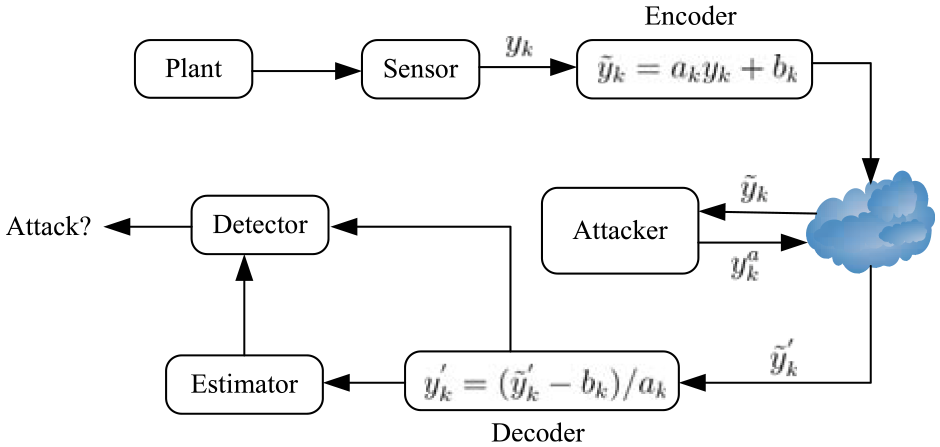
The system block diagram under the watermarking encryption defense strategy.
After the sensor collects the physical state data
System model
Consider the following linear time-invariant (LTI) system:
where
Kalman filter
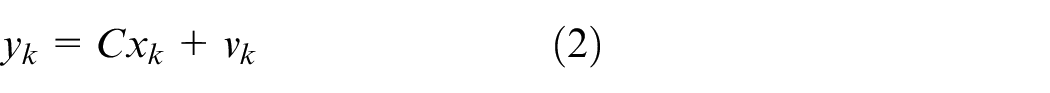
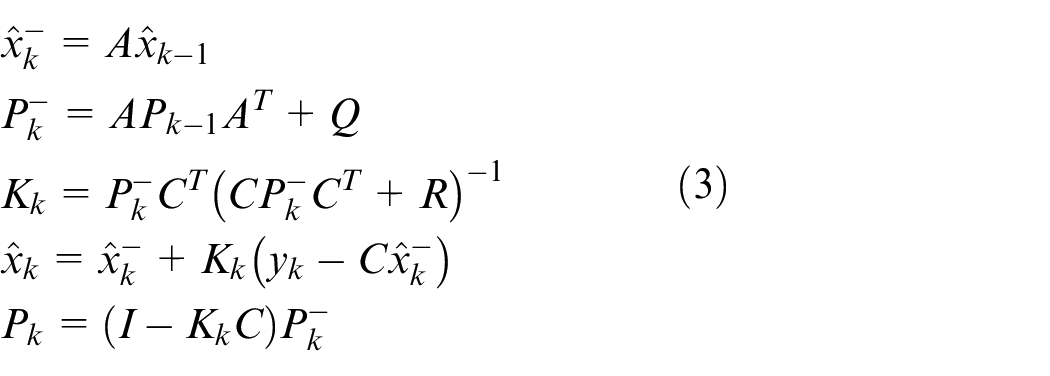
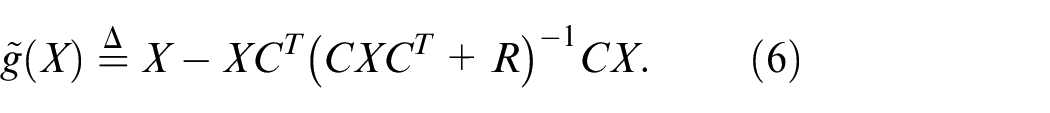
For the LTI system (1)-(2), Kalman filter is employed to estimate the state
where
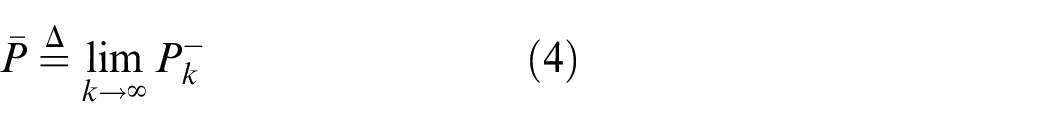
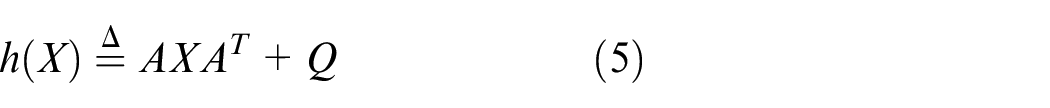
It should be pointed out that if the system is detectable, the Kalman filter gain and error covariance will converge to a stable value in a short period from the any initial conditions. 25 Therefore, it is assumed that the filter starts to operate from a steady-state, and the steady-state value of the priori error covariance is defined by
where
For simplicity, the Kalman filter is assumed to start from the steady state, that is,
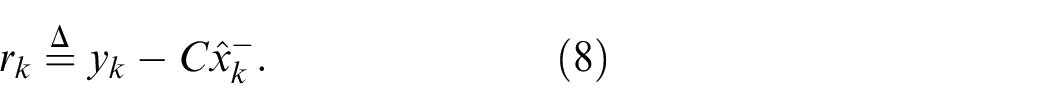
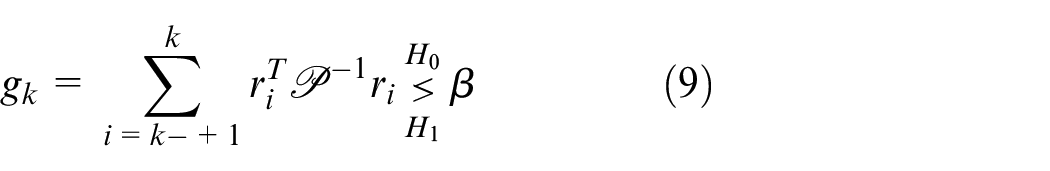
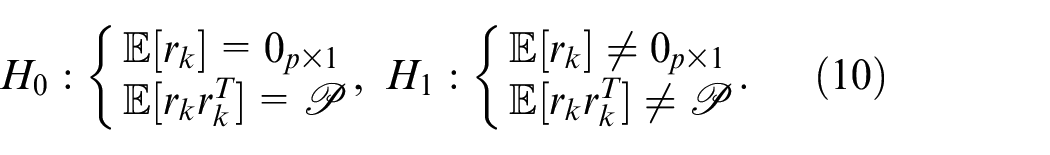
detector
The
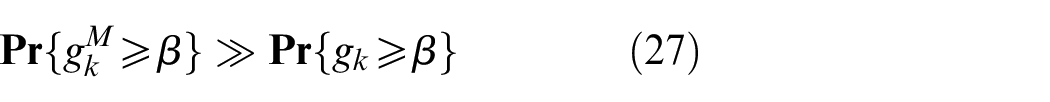
When the system is attack-free, the residual
where
Attacks model
It is assumed that an attacker can intercept the transmission data. Two different attacks will be introduced with the concept of linear man-in-the-middle (MITM) attack in this paper. In, 18 the linear MITM attack is designed as follows
where
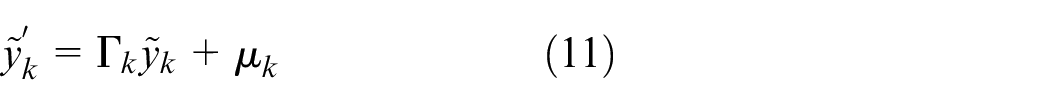
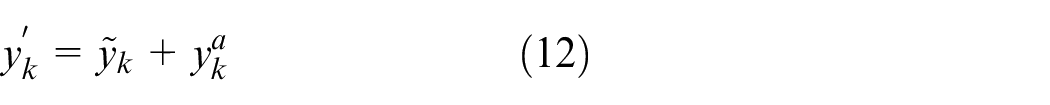
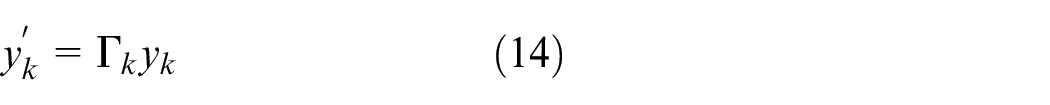
In this paper, we will re-consider the MITM attack carefully. It can be seen from (11) that when
where
where
If the residual
On the other hand, as studied in,
18
the MITM attack is optimal with
In this paper, the attack matrix
Main results
In this section, the watermarking-based defense strategy is introduced, and the defense algorithm is given. Furthermore, the influence of the designed encryption defense strategy on the system performance is analyzed as well.
Watermarking-based active defense strategy
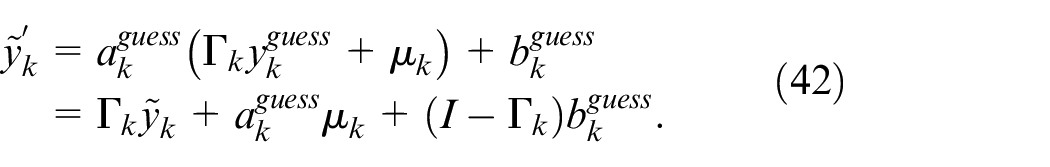
The watermarking encryption module and decryption module are added to the cyber-physical system, which can be utilized to detect malicious attacks by the system. When sending data, the transmitted data is encrypted into the following form:
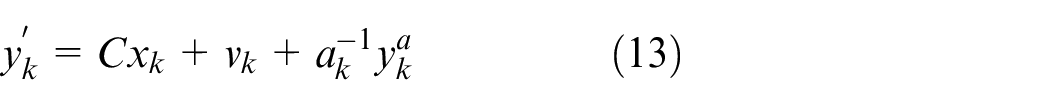
where
Note that the decoder will receive
where
Based on the dynamic parameter design of the pseudo-random number generator, the attacker cannot crack the watermark through traditional statistical analysis, and the synchronous decryption mechanism of the receiver ensures the accuracy of the state estimation without attack.
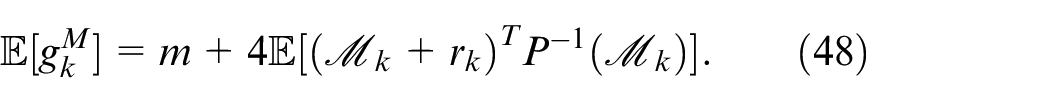
Performance analysis when the system is attacked
When the A-FDI attack is considered, then
After the receiving end receives the attacked vector
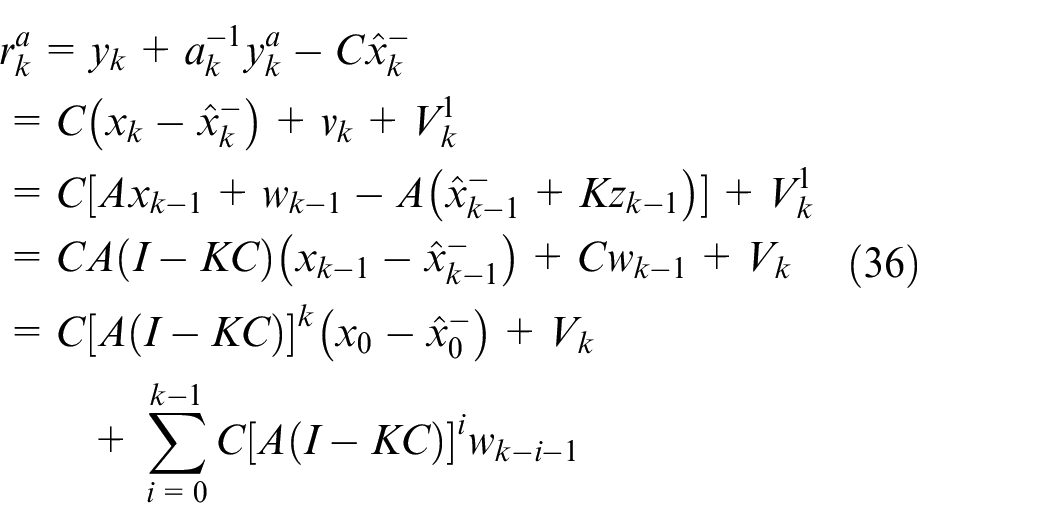
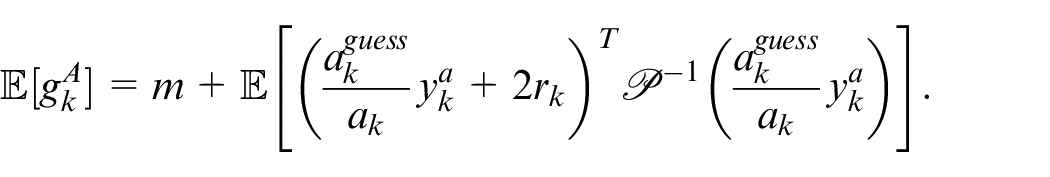
As a result, the residual of Kalman filter can be computed as follows:
at time step
When the system is attacked by an A-FDI attack at time step
When the parameter
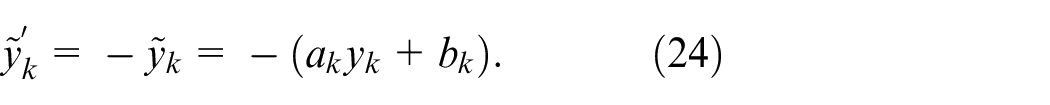
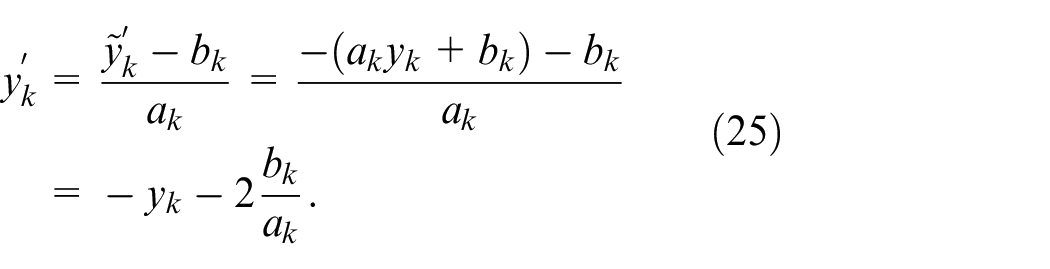
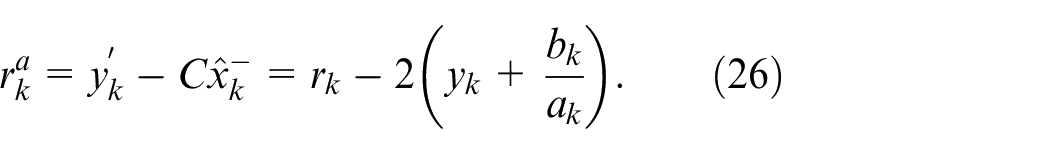
When the M-FDI attack is considered, then
After the receiving end receives
As a result, the residual of Kalman filter
at time step
When the parameters
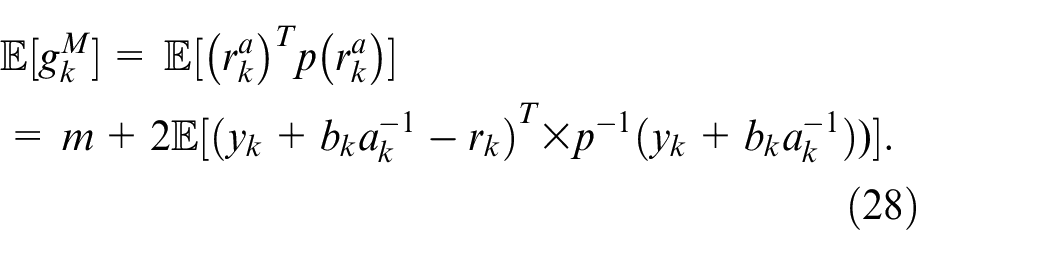
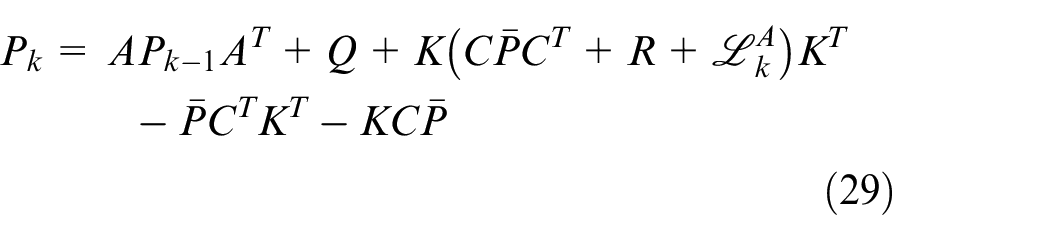
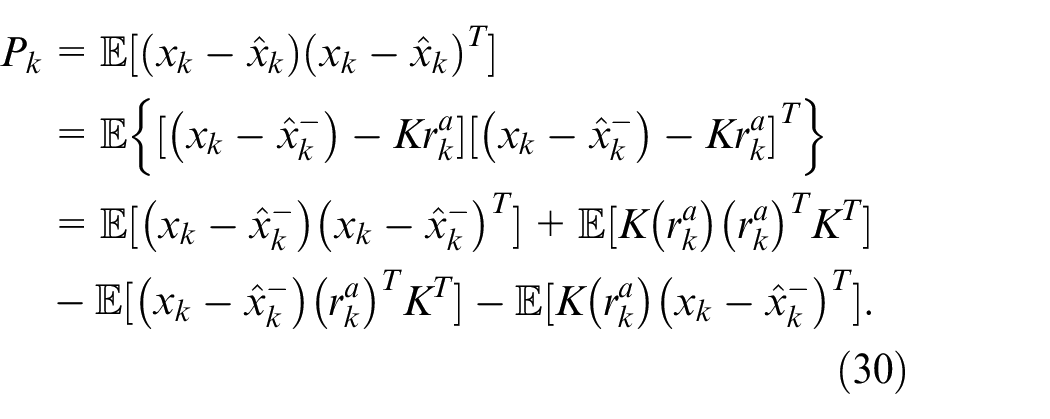
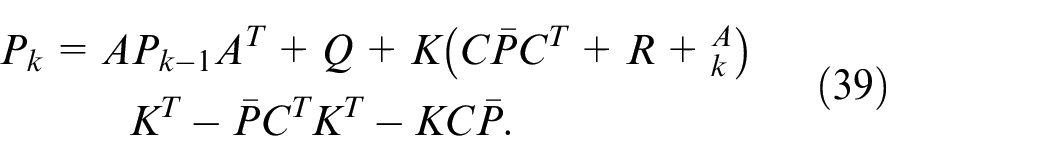
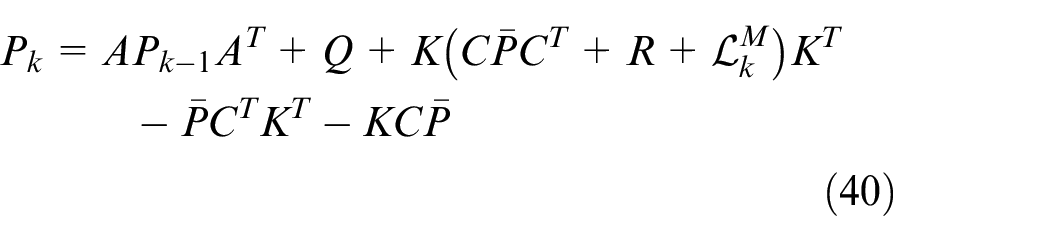
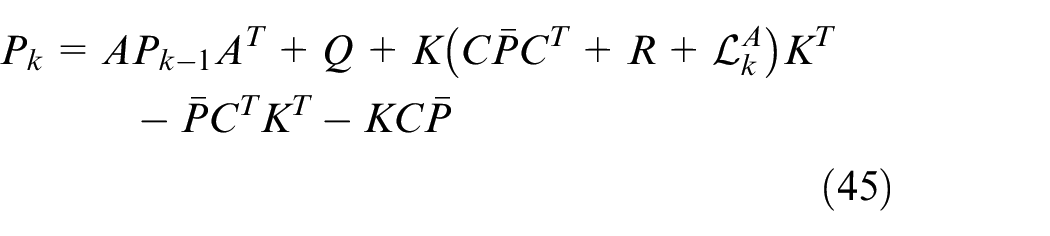
The estimated error covariances of Kalman filter under both A-FDI and M-FDI attacks will be given in the following theorems, and the impact of both types of attacks on system performance is analyzed as well.
where
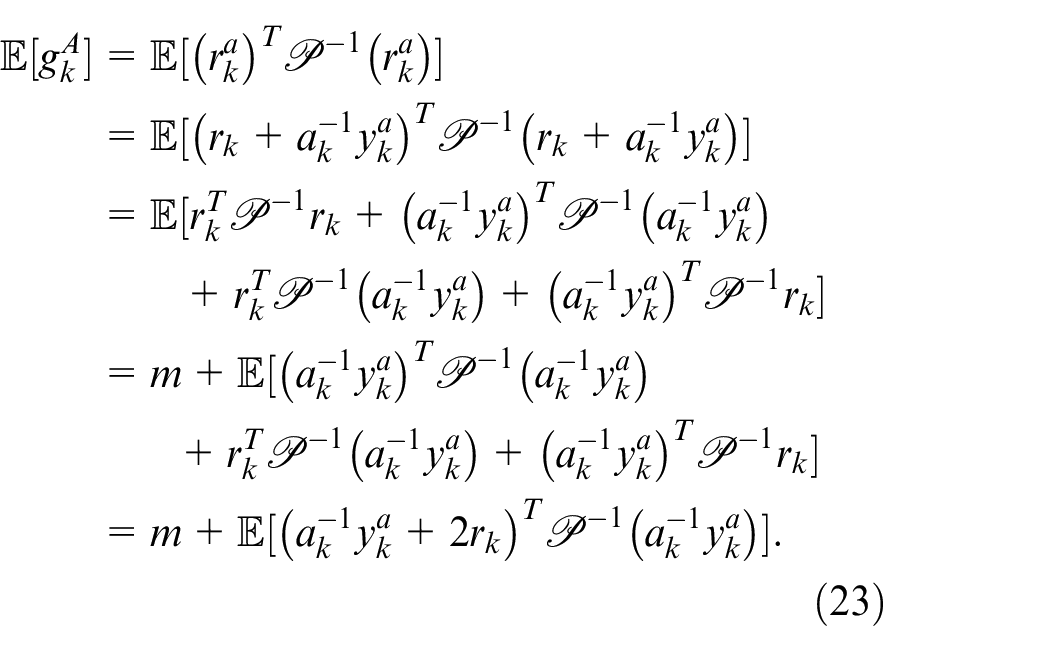
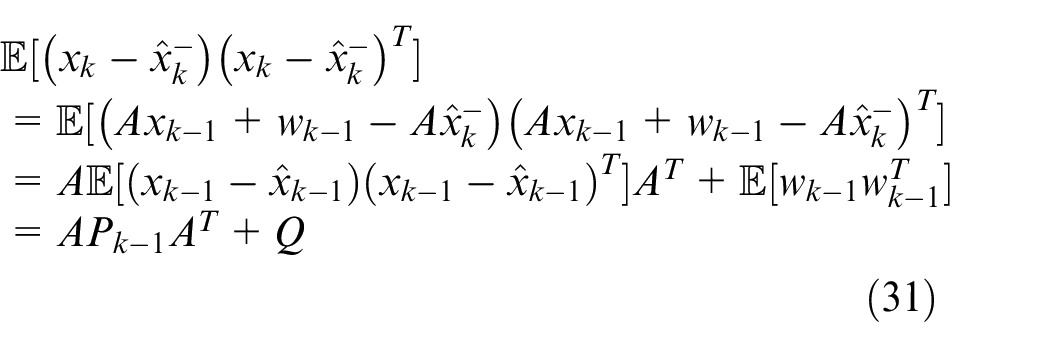
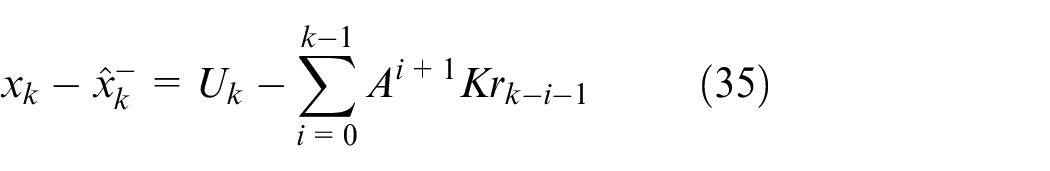
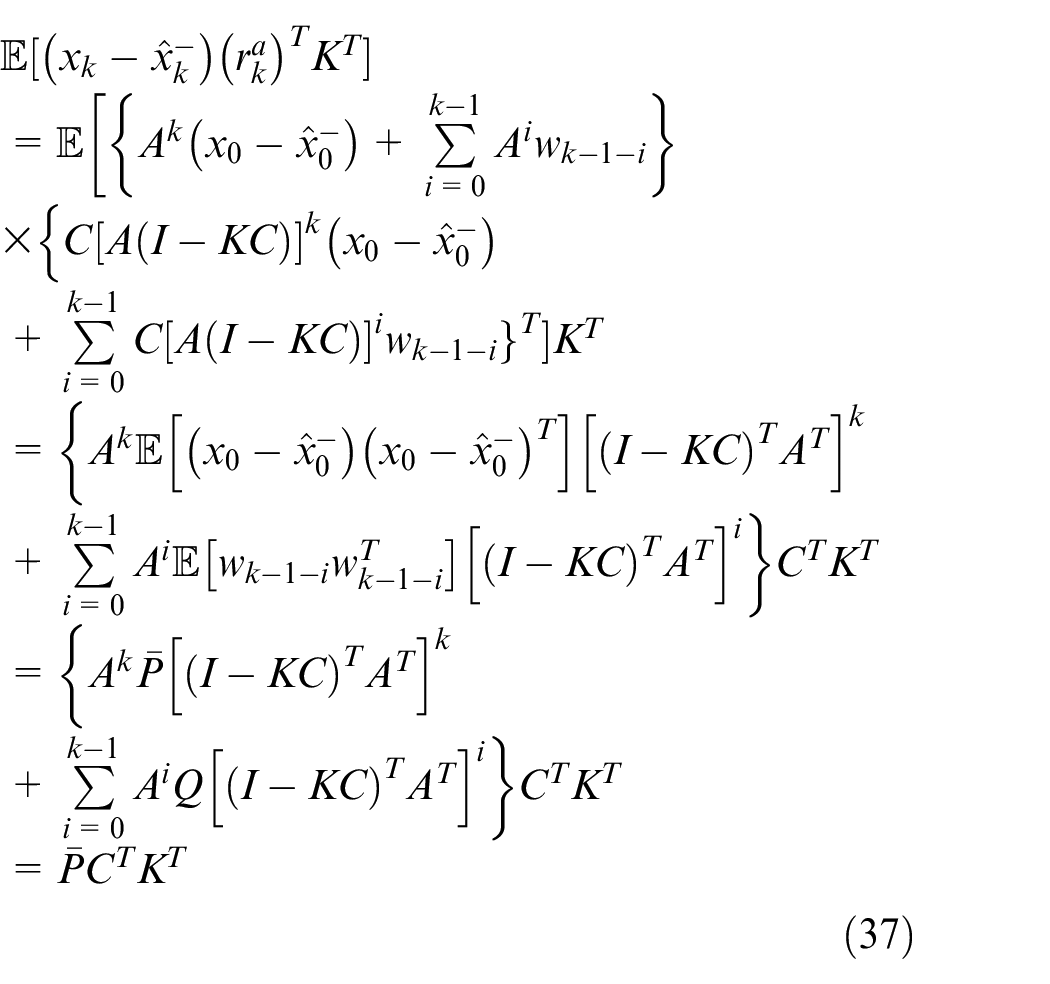
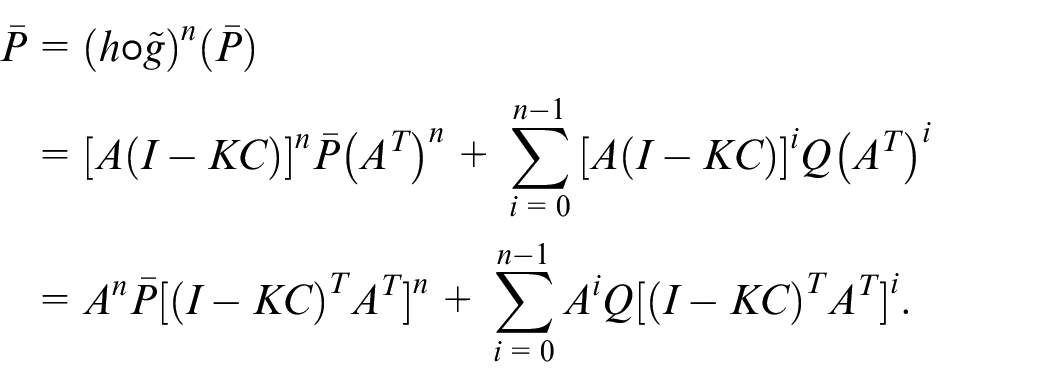
For the first term of (30), we can obtain that
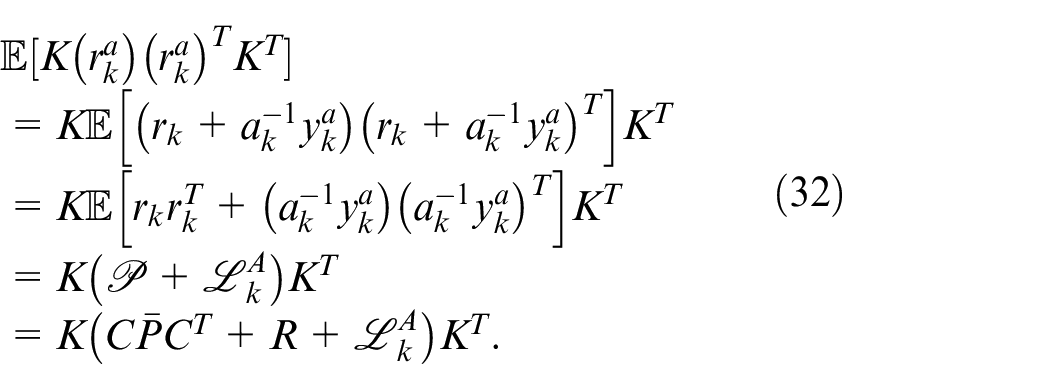
For the second term of (30),
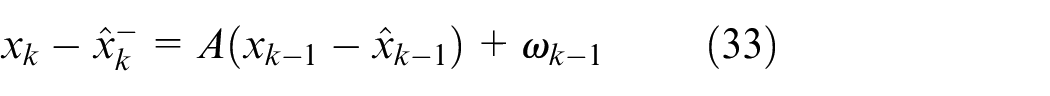
For the third term of (30), the relationship between
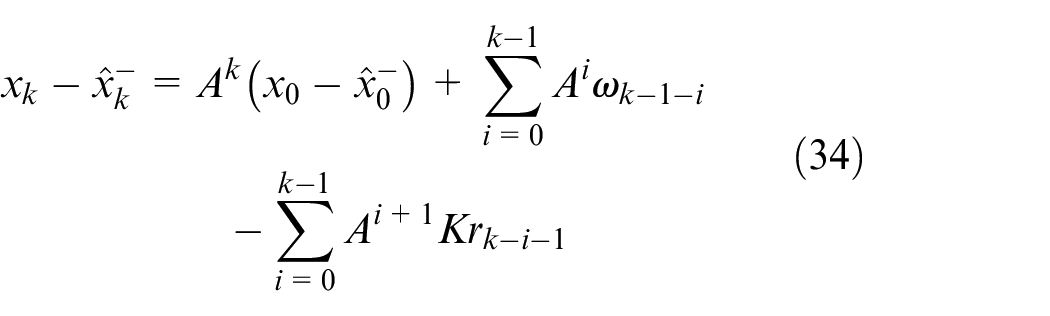
Further recursive expansion to the initial moment, get:
According to the definition of
where
where
Similarly, the fourth term of (30) can be derived as follows
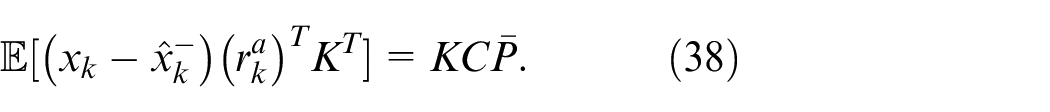
Substituting (31)–(32), (37) and (38) into (30) yields
which completes the proof.▪
where
Attack detection in different scenarios
In the section, four different situations will be discussed. Note that it is assumed that the attacker already knows the structure of
Both
and
are not available to an attacker
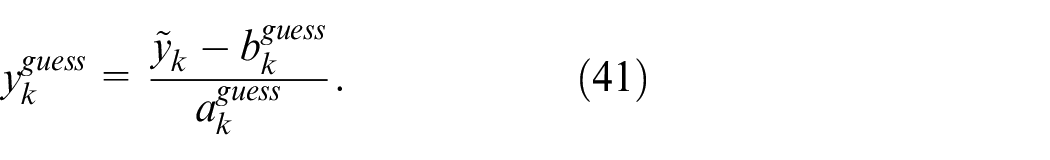
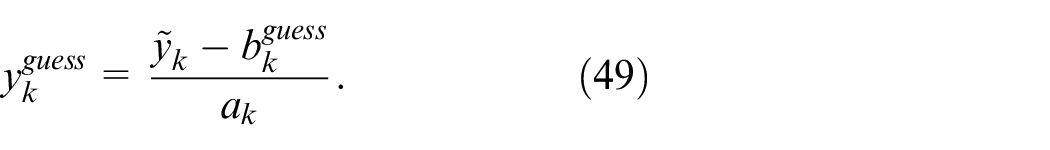
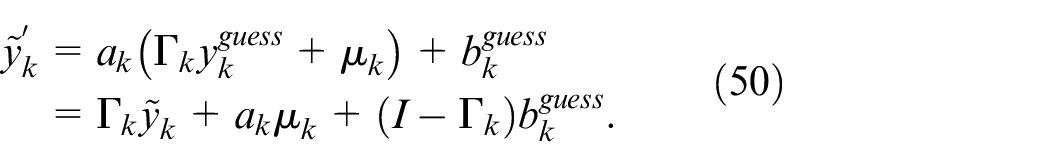
In this case, the attacker can guess the values of
Then, the MITM attack can be designed as
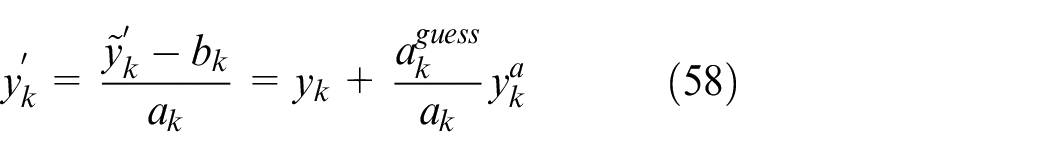
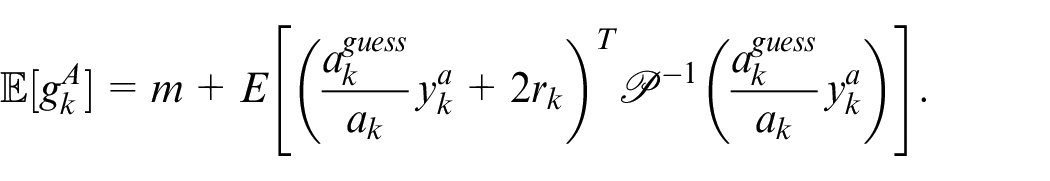
For the A-FDI attack,
Thus, one can get
From (29), the estimated error covariance of the state can be calculated by
where
Furthermore, one can obtain that
In order to bypass the detector, the A-FDI attack should satisfy
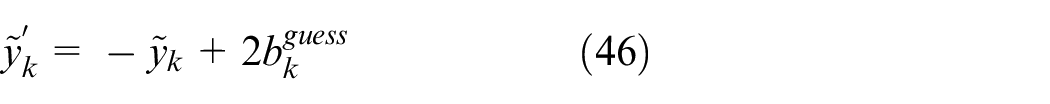
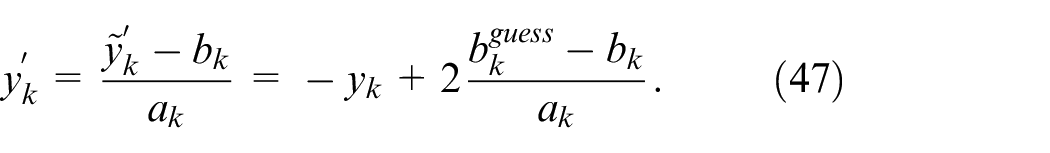
On the other hand, for the M-FDI attack,
and
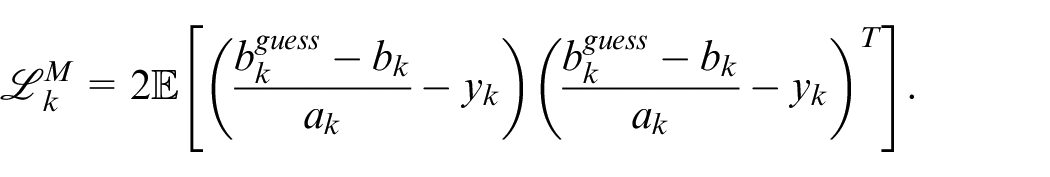
The estimation error covariance can be obtained similar to (40), where
Furthermore, one can derive that
where
Only
is available to an attacker
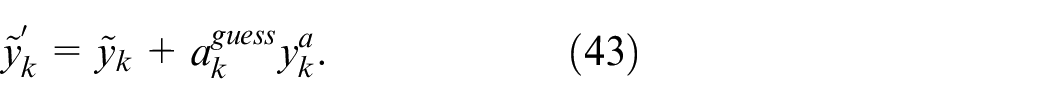
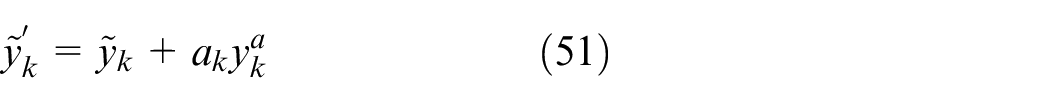
In this case, it is assumed that the attacker has obtained the watermark
Then, the MITM attack can be represented by
For the A-FDI attack, one can derive that
and
Furthermore, one can calculate
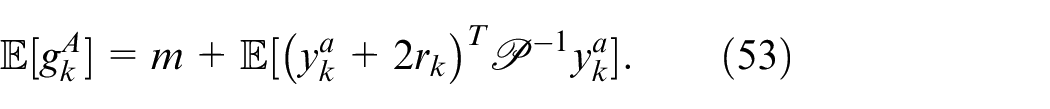
It can be seen from (53) that if
On the other hand, for the M-FDI attack, one can derive
It is noted that this situation is the same as discussed in (46), that is,
Only
is available to an attacker
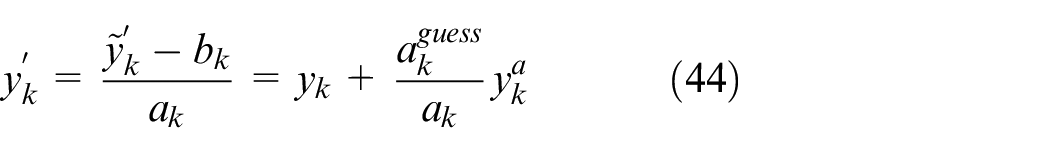
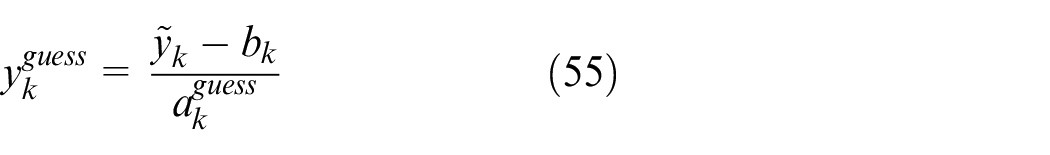
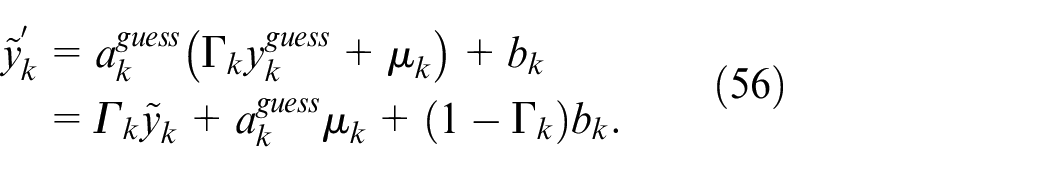
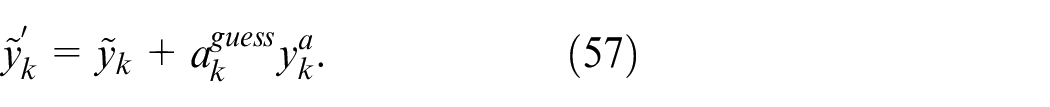
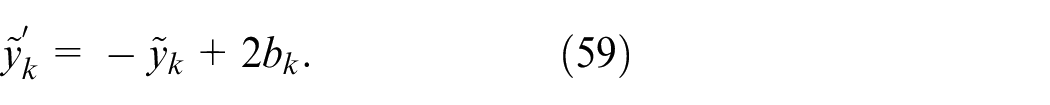
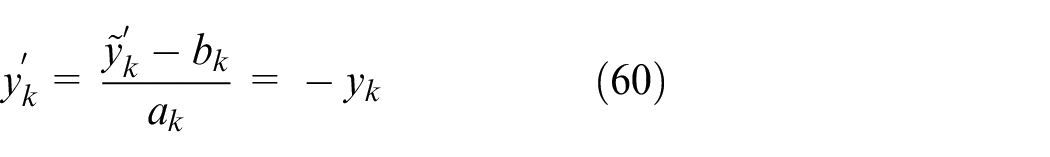
When the adversary can only obtain the information of
which implies
For the A-FDI attack, one can derive that
and
It is noted that (58) is the same as given in (44), which implies
Similarly, when the M-FDI attack is considered, one can compute
and
which implies that the corresponding M-FDI attack is the optimal linear attack without being detected.
Numerical examples
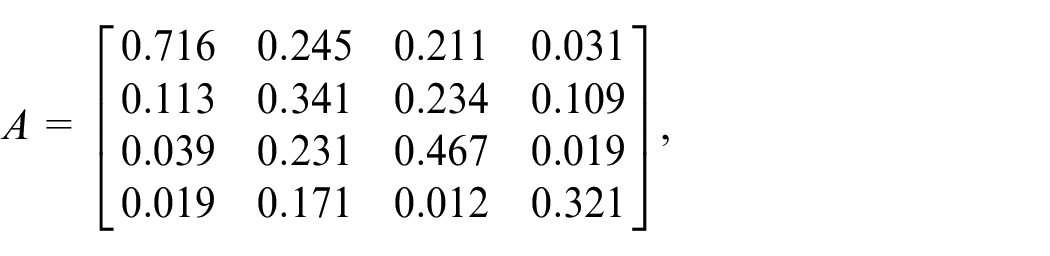
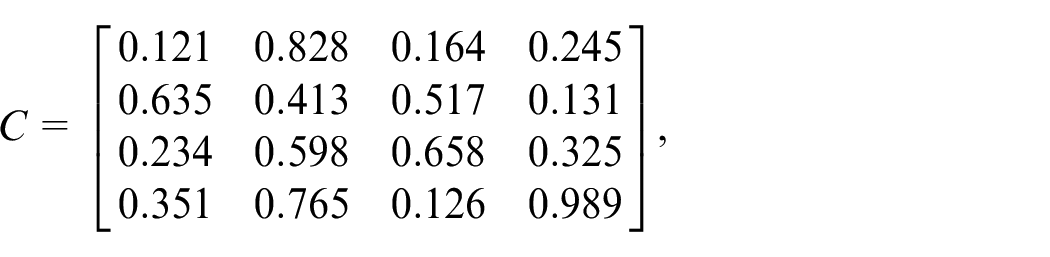
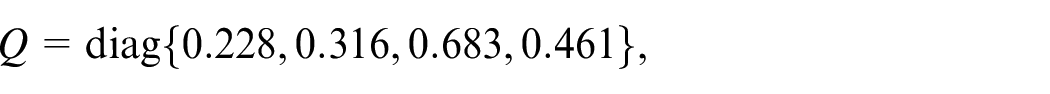
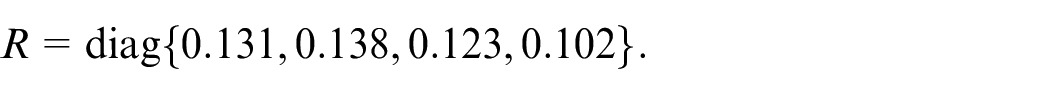
In this section, numerical simulation will be given to illustrate the effectiveness of the proposed results. For the linear system described by (1)–(2), we adopt the same system parameters as that utilized in, 29 where
The window size
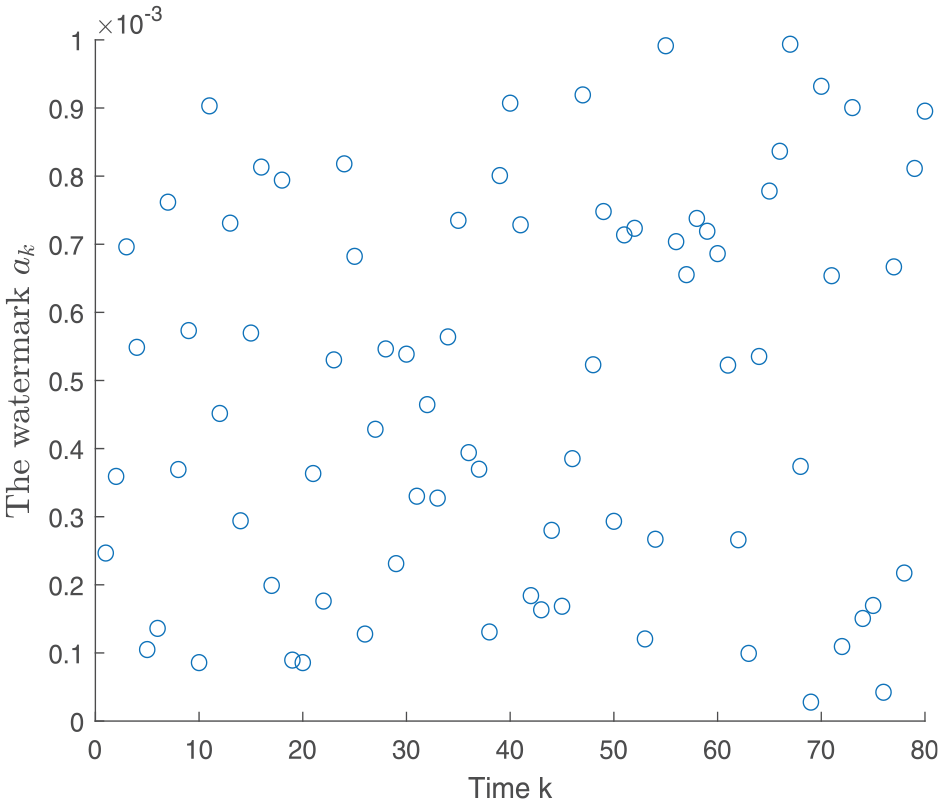
The watermark
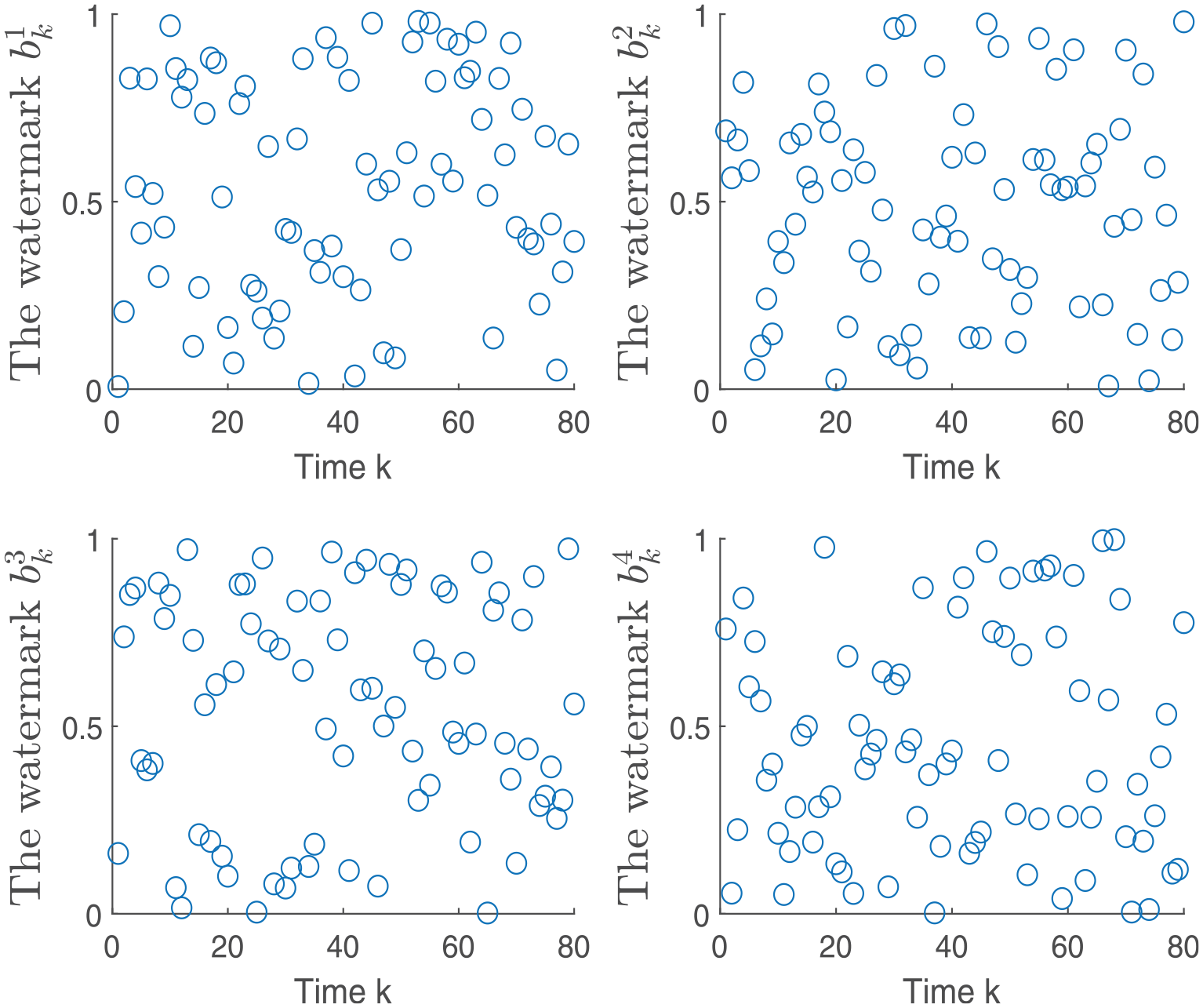
The watermark
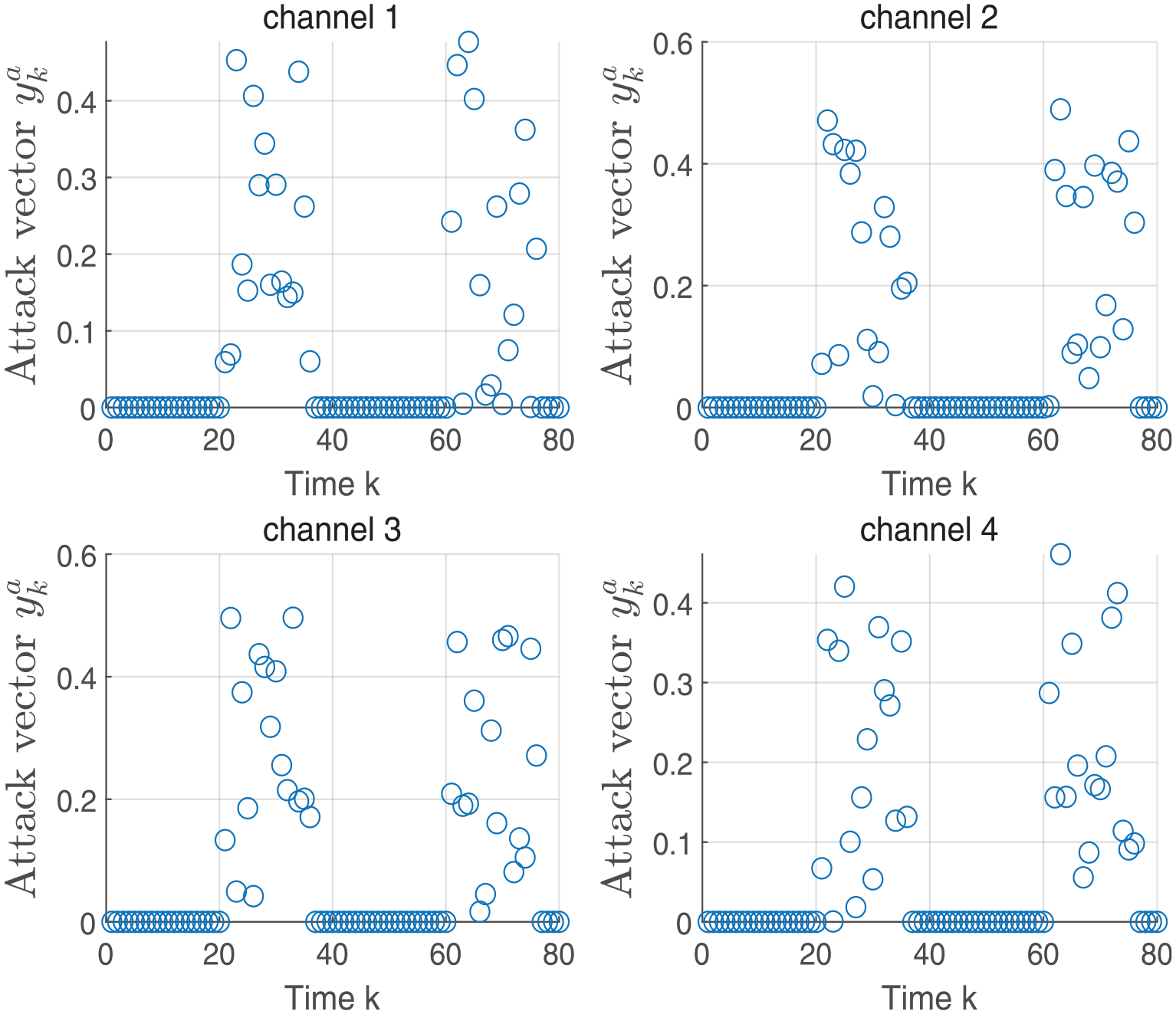
The attack vector
Case 1: Both
and
are not available to an attacker
In this situation, both watermarks
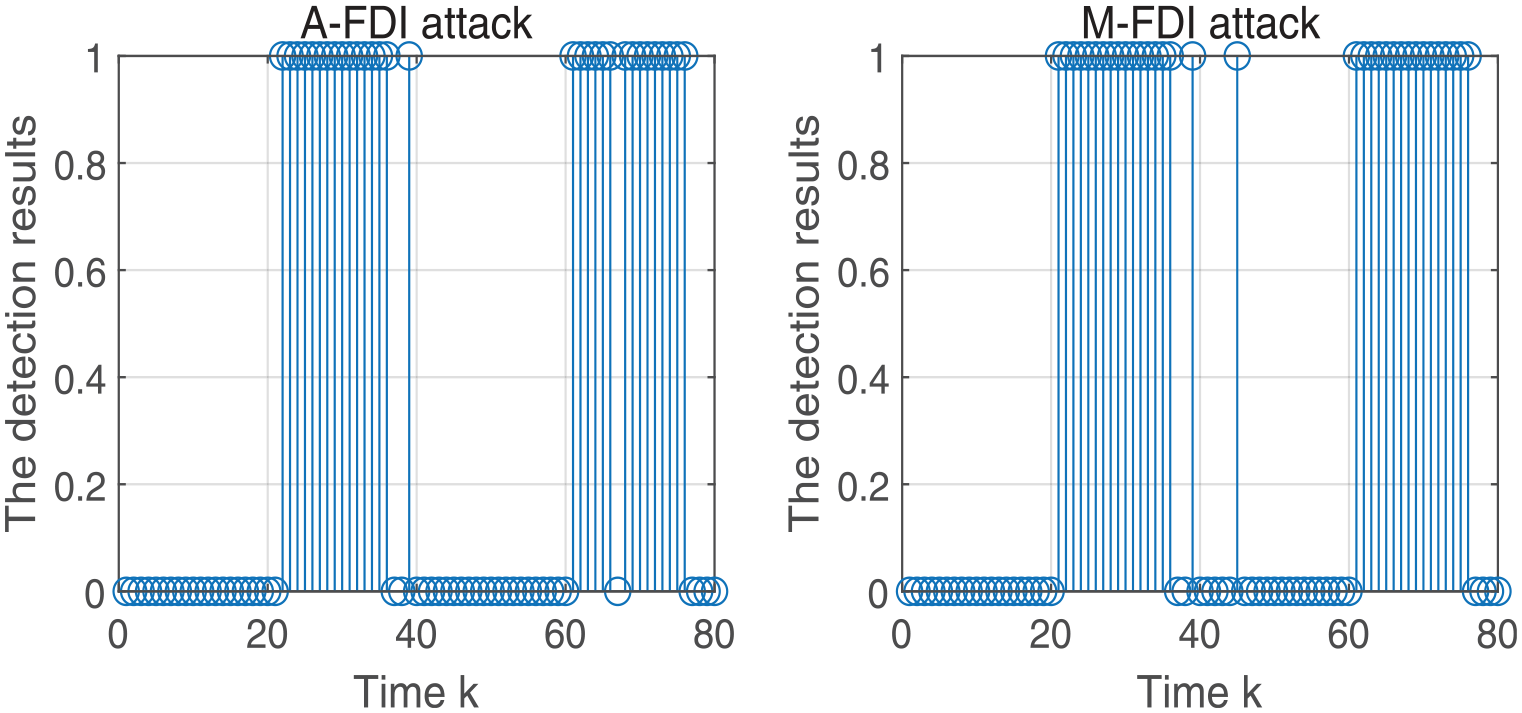
The attack detection result when both
Case 2: Only
is available to an attacker
When an attacker can only obtain the knowledge of
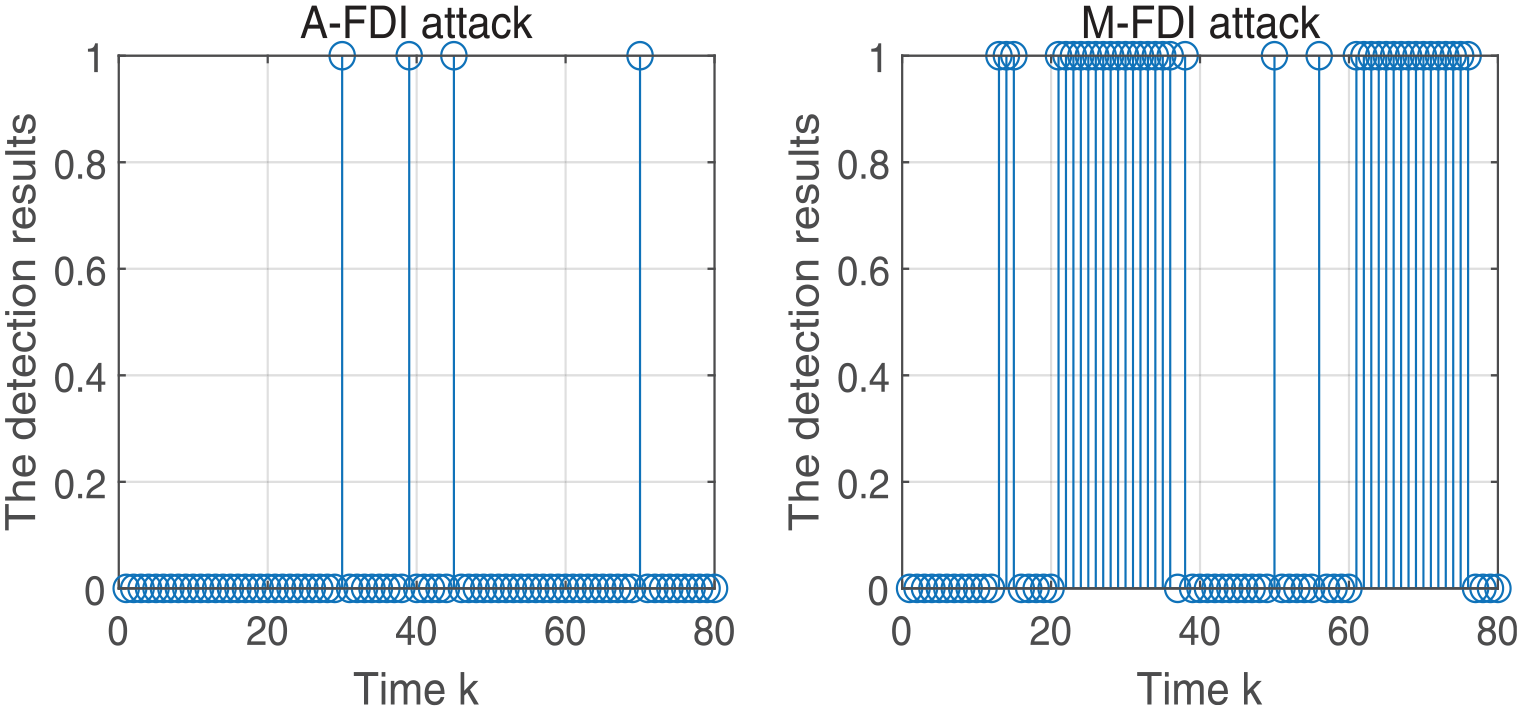
The attack detection result when only
Case 3: Only
is available to an attacker
In this case, an adversary can only obtain the information of
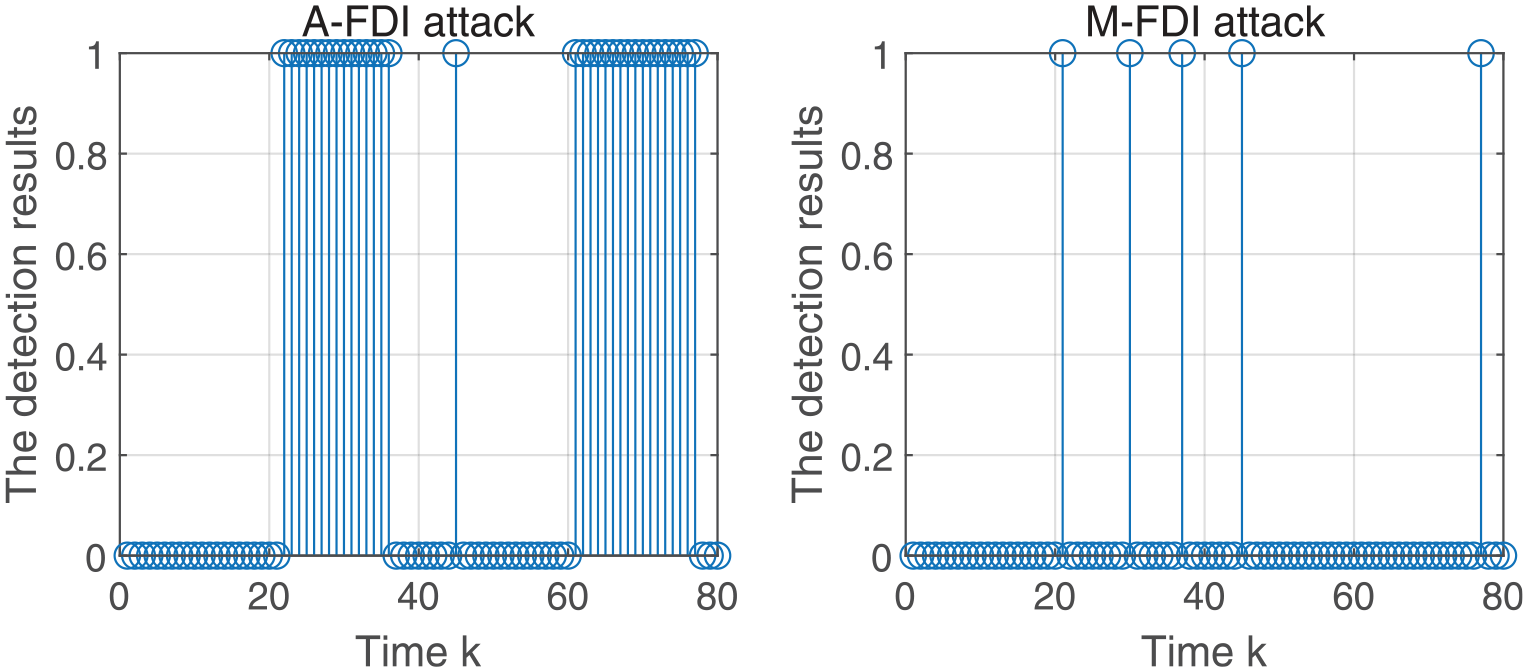
The attack detection result when only
Conclusions
In this paper, a proactive defense strategy based on dynamic watermark encryption is proposed to detect both A-FDI and M-FDI attacks. In addition, the data output by the sensor is encrypted and decrypted, which could greatly improve the attack detection rate. Moreover, the watermarks do not affect the system performance in the absence of attacks. When the watermarks are well designed, the attack detection rate of
Footnotes
Informed consent/Patient consent
Written informed consent for publication was obtained from all participants
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by the project of Wenhua College(2024T01)
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data availability statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
Trial registration number/date
Not applicable