Abstract
Nigeria is home to a variety of terror groups, some of which receive little scholarly or media attention, but whose violent attacks cause significant casualties and instability. This analysis uses a bipartite network approach to examine terror groups in Nigeria between 2009 and 2019. We capture substantial variation among terrorist groups by state, target type and attack mode, and consider “unknown” terrorist offenders. Although Boko Haram is the dominant terrorist group, the Fulani extremists, IPOB, and others, are also prominent, with MEND especially active against oil infrastructure and in the Niger Delta region. This research finds that a bipartite network approach is effective for providing a more comprehensive understanding of terrorism dynamics, which is essential for effective counterterrorism policy and analysis.
Despite recent rapid, economic, and political progress in the most populous country in Africa, terrorist groups conducting frequent, deadly attacks continue to plague Nigeria, resulting in tens of thousands of deaths, and displacement and food insecurity for millions more (Abbass, 2014; CIA, 2021; Raineri & Martini, 2017). Terrorism in Nigeria has worsened ethnic and religious divisions, functioned as an accelerant for Islamic fundamentalism, and threatens the domestic security of neighboring countries (Adesoji, 2011; Chukwuma, 2014). These violent actions have led to an array of ineffective domestic and global responses, leading to the question: Why have security efforts in Nigeria, a country with both significant economic resources and supportive global partners, not effectively dampened terrorist behavior?
We believe that one reason for this lack of effectiveness is that counterterrorist efforts, and discussions about Nigerian terrorism in much of the academic literature and Western Media, often focus solely on the actions of a single terrorist group, Boko Haram and often a particular type of action, the kidnapping of children. Violent attacks by other groups such as the Fulani Extremists or other types of attacks, including those against oil resources, receive less policy, scholarly and media attention, outside of a few key efforts (e.g., Ojo, 2020). While Boko Haram is a prominent terrorist group in Nigeria in recent decades (Ajah et al., 2020), and the kidnapping of children is heinous, a near singular focus on this group and their crimes provides an incomplete picture of the full range of extremist violence in Nigeria. Terrorism in Nigeria, despite having become synonymous in the West with Boko Haram, is not confined to one group of perpetrators, method of violence, or location. Rather, multiple groups routinely execute deadly attacks throughout Nigeria, and the actions and networked patterns of these groups influence the future violence of others (Dorff et al., 2020).
Nigeria did not enact anti-terrorism legislation until June 2011, after Boko Haram had been operating for 2 years, and some have criticized the government for using a violent, military-style response with questionable effectiveness (Allen, 2019; Okunade, 2021; Ugwueze & Onuoha, 2020). The fact that the Nigerian military experiences rampant corruption and lacks resources continues to hamper government actions (Brechenmacher, 2019), and the insurgency has seen recent gains (Allen, 2019). In addition, while there has been significant government and media attention on Boko Haram, the Niger Delta has seen a resurgence of militancy groups in recent years whose violent actions have pushed Nigeria’s oil output to record lows (Onuoha, 2016). Peaks in attacks on critical infrastructure such as oil pipelines are associated with public hangings of environmentalists, shifts from military to civilian government administration, and regional frustration with politicians (Anifowose et al., 2012).
Without a complete profile of terrorism in Nigeria, misunderstandings arise regarding the dynamics of this form of violence, which in turn may limit the effectiveness of local, national, and international counterterrorism policies (LaFree & Dugan, 2009). Unsuccessful policies, moreover, may contribute to long-lasting, political distortions regarding the problem. Criminological research on terrorism has frequently addressed similar issues of target selection and group patterns in other countries (e.g., Lafree, Yang, Crenshaw, 2009; McMillan et al., 2020). Our goal here is to undertake an in-depth analysis of 10 years of violent, Nigerian terrorist behavior, in which we identify bipartite network ties between the group perpetrators and their attack locations, as well as links to their target types and attack styles. This approach will enable us to develop a more complete profile of terrorism in this country that extends beyond conventional analyses that often remain confined to one group, Boko Haram, and with little attention paid to the wide variety of target types, locations, and attack styles.
Bipartite Network Approach
To gain a deeper understanding of terrorism in Nigeria, we employ a bipartite social network model. Network approaches are useful because they influence our insight into the linkages and structures driving terrorist or state behavior (Corradi et al., 2022), and they also affect operational decisions critical to counterterrorism (Dahl, 2002; Malm et al., 2017). Standard network approaches examine ties between the same “type,” such as ties between people. Bipartite, or two-mode network approaches include ties between two different types, such as people and events (in this case, terrorist groups and their terrorist acts). This advantage of bipartite network methodology has been useful in analyzing patterns of extremist violence in other countries, such as India (Yarlagadda et al., 2018). We use this methodology to address the following questions: What groups have a prominent terrorist presence in Nigeria? Where do their incidents occur within Nigeria at the state level? On what kind of target does each group focus their efforts? What types of attacks do they employ?
We begin by examining terrorist groups and their network connections to attack locations, where the bipartite actors consist of Nigerian terrorist groups and the events are the locations of the attack (at the state level). In subsequent analyses, we examine the kinds of targets linked to each terrorist group and their types of attacks. Note that target selection closely connects with the group’s ideology, goals, and fear of repercussions (Abrahms, 2006; Abrahms et al., 2018). Target selection represents a consistent predictor of the likelihood terrorist groups will achieve their policy goals (Abrahms, 2006), and ideology often closely guides the selection of targets. Target selection in Nigeria differs by grievance but also may have important roots in access to resources.
Background
Nigeria is a former British colony that achieved independence in 1960. Nigeria’s 36 current states break down into two main regions; the South that has rapidly urbanized and become densely populated, and the North that has remained more rural (Agbiboa, 2013). Corruption is endemic to many aspects of Nigerian politics (Duke et al., 2017; Evans & Kelikume, 2019; Uzodike & Maiangwa, 2012). Power is concentrated in the hands of a few, with a small number of families holding access to many political, economic, and religious positions in Northern Nigeria across much of its history (Raineri & Martini, 2017). The government consistently fails to address major issues facing Nigerians, such as rampant poverty, illiteracy (particularly in the North), violence and religious uprisings (Onuoha, 2010). These failures have led to the perception that some areas of Nigeria are “ungoverned” (Ojo, 2020), with the population paying the cost through both government repression and violent terrorist attacks (Nnam et al., 2020). The stark divisions in Nigeria, as well the inadequacy of responses to major issues facing the inhabitants, help to drive terrorist violence. In line with relative deprivation theory (Gurr, 1970), ongoing, worsening local and national grievances, and a perceived lack of legitimate options to resolve these grievances (Rosenfeld, 2004), combine to increase assessments of the utility of violence.
Regional Political Violence
To understand security and conflict in Nigeria, one also must understand the role of religion. Throughout the country, religion is heavily politicized (Agbiboa, 2013), with over half of the population being Muslim (53.6%) and concentrated in the North, while the rest are mainly Christian (45.9%) and tend to congregate in the South (CIA, 2021; Raineri & Martini, 2017). Between 1999 and 2010, religiously spawned violence led to the deaths of more than 10,000 people (Agbiboa, 2013). During 1999 to 2012, 12 Northern states (Zamfara, Kano, Sokoto, Katsina, Bauchi, Borno, Jigawa, Kebbi, Yobe, Kaduna, Niger, and Gombe) became ruled by enforceable Sharia legal codes. The majority of Nigerian Muslims support nation-wide Sharia Law, which the majority of Christian Nigerians vehemently oppose it (Agbiboa, 2013). Both Christians and Muslims who do not abide by the strictest tenets of Islam are frequent targets of Boko Haram (Raineri & Martini, 2017). The disparate experiences of terrorism and a fractured response have led to a lack of unity in combating terrorism (Owojori et al., 2020).
We display the geographic distribution of Nigerian terrorist attacks from 2009 to 2019 in Figure 1. Orange dots represent higher concentrations, with yellow and green dots denoting more middling and smaller numbers of attacks, respectively. The numbers inside the dots display how many attacks occurred in that area. The distribution of intense violent actions by the terrorist group Boko Haram concentrate in Northern Nigeria, especially in the Northeast states that have multiple orange dots - some of which have had to declare states of emergency at various points in time due to extremist violence (Chukwuma, 2014; Raineri & Martini, 2017). The highest number of attacks (963) appeared in the Northeast state of Borno, and most of these were undertaken by Boko Haram. Boko Haram’s violent campaign in Nigeria began in July 2009, when there was a conflict between members of Boko Haram and Bauchi state’s security agency, culminating in the death of 17 members of Boko Haram (Agbiboa, 2013). These deaths resulted in 5 days of rioting, spreading into the states of Kano, Yobe, and Borno, leading to the extrajudicial killing of Mohammed Yusuf (the leader of Boko Haram at the time) and other high-ranking members of the group (Adesoji, 2011; Onapajo & Uzodike, 2012).
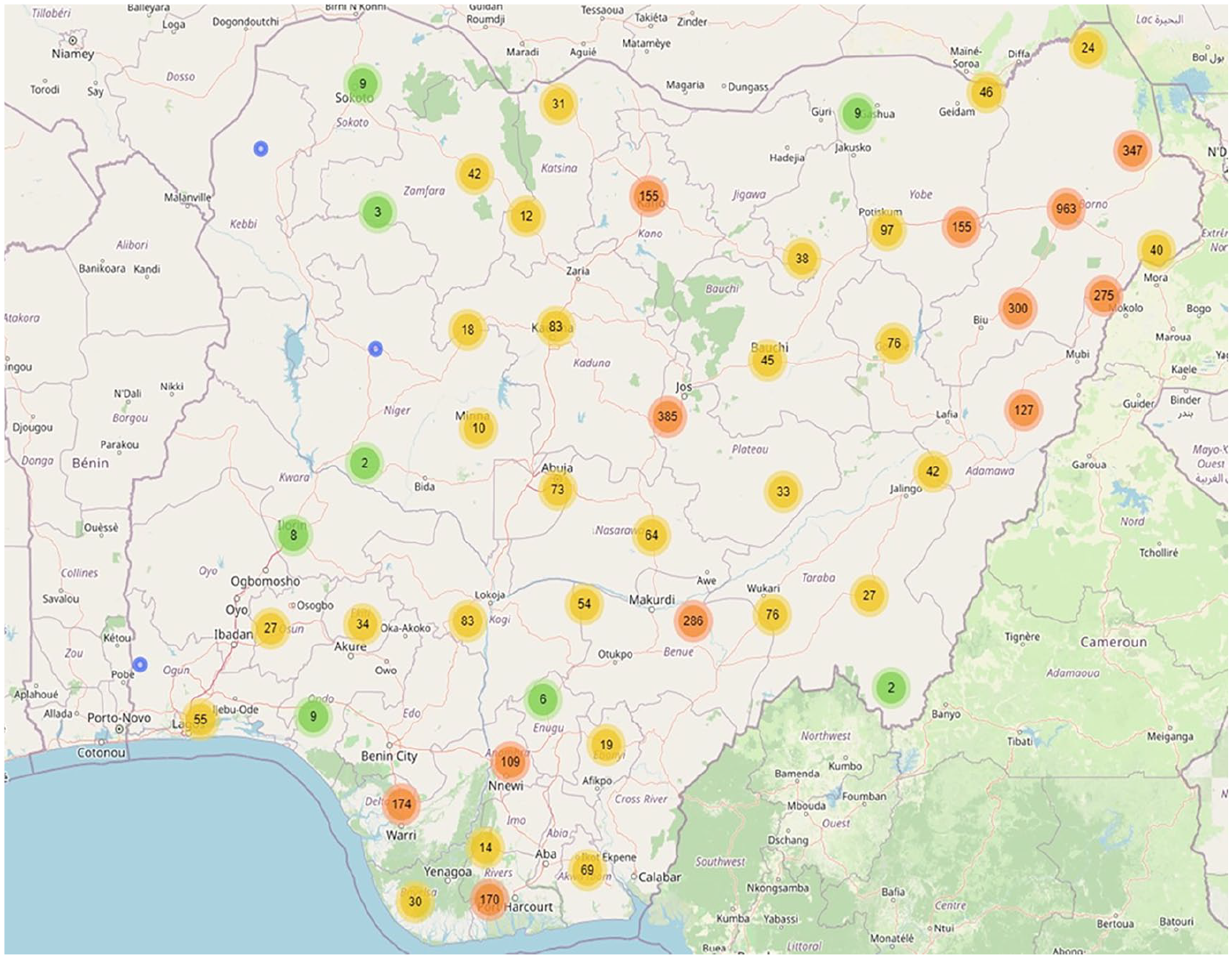
Map of terror attacks in Nigeria.
Many claim that Boko Haram has existed since the early 2000s under a variety of names, including the Nigerian Taliban (Adesoji, 2011). While associated with Nigeria, this Jihadist militant group has also infiltrated Cameroon, Niger, and Chad (Chukwuma, 2014). Boko Haram often targets Islamic scholars that provide them with any opposition, or Muslims they deem to be not radical enough (Onapajo & Uzodike, 2012). Due in part to processes of globalization, Boko Haram has been closely linked to ISIS, the Taliban, al-Qaeda, and al-Shabaab (Adesoji, 2011; Onapajo & Uzodike, 2012; Raineri & Martini, 2017).
In the network of violence shown later in Figure 2, we can see other groups that have widespread reach, such as the Fulani Herdsmen. Before British colonial rule Northern Nigeria was part of the Sokoto Caliphate, an expansive largely Islamic state. (Lovejoy, 1978). The Fulani people are an ethnic group that had a large presence in Western Africa, which was undermined by colonial intervention. Fulani Pastoralists have resorted to militancy to battle with farmers in Nigeria that encroach on their traditional practices, especially in Southern Nigeria (Abbass, 2014). The Fulani (often known as Hausa-Fulani) own the vast majority of livestock in Nigeria, tying them to issues of food security (Abbass, 2014). Fulani herdsman represented a powerful group during both the Sokoto Caliphate and British colonial rule (Abbass, 2014). British rule exacerbated existing tribal/ethnic tensions, and the repercussions of the arbitrarily drawn territorial divisions still in existence today are often a barrier to Nigerian unity and to the development of the primacy of a “Nigerian” identity (Davis & Kalu-Nwiwu, 2001). The Fulani herdsman conflict has caused the death and displacement of thousands of Nigerians. Despite receiving little attention in the West, violence from the Fulani in the last half decade arguably represents as great if not a greater security threat to Nigeria than Boko Haram (Adebayo, 2018). While in many ways the product of an ethnic conflict, the Fulani Ethnic Militia, or the Fulani herdsmen frequently perpetrate political violence against civilians that meets the definition of terrorism, and those incidents are thus included here.
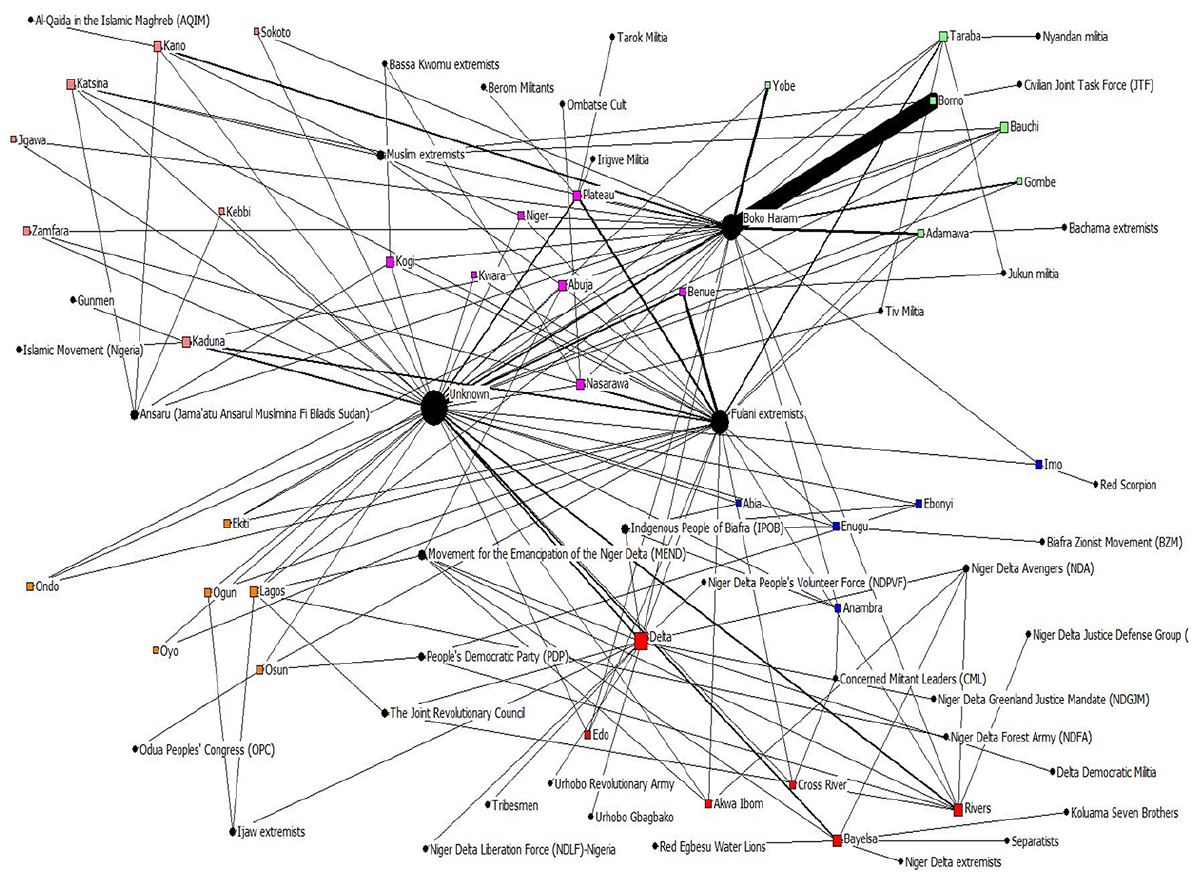
Group name (black circles) and state (squares, color based on region).
Among the other groups effective at sponsoring Nigerian violence, is the Movement for the Emancipation of the Niger Delta (MEND), a militant group that often kidnaps oil workers and destroys oil facilities in the Niger Delta Region. This group tends to feud both with multinational corporations and the Nigerian government. The militancy began in 2004 over the exploitation and marginalization of minority ethnic groups in the region, such as Ijaw and the Ogoni (Evans & Kelikume, 2019). MEND’s central aims are to draw global attention to the living conditions of the citizens of the Niger Delta Region (Sampson, 2016). However, some argue that over time this struggle has devolved into criminal and economic profiteering, driven by militias and ethnic and political unrest (Evans & Kelikume, 2019). Importantly, like the reaction to Boko Haram, the response of the Nigerian state to unrest and terroristic acts in this region has been repressive. This reaction has inspired retaliatory violence and furthered instability (Sampson, 2016).
Critical Infrastructure and Resources
Conflicts over resources frequently act as a spark for Nigerian violent extremism. The following sections delineate those resources and explain their specific importance.
Oil
Nigeria has a lot of oil. Oil and gas exports account for around 80% to 90% of the income generated by Nigeria (Ogundiya, 2009; Watts, 2004). Oil reserves are concentrated in the Niger Delta Region (NDR), which subsequently has experienced extensive conflict between the government, citizens, and multinational corporations. Multinational corporations have an immense amount of power in Nigeria due to the tremendous reliance on oil as an export and the lack of corporate regulation. Despite this power, kidnapping of foreign oil workers is a rampant and daily occurrence. Multiple groups, including MEND, are responsible for these kidnappings and for widespread damage to oil facilities and associated workers (Ogundiya, 2009). Boko Haram also perpetrated a deadly attack in 2017 that killed more than 50 members of an oil exploration team in Borno (Al Jazeera, 2017).
The Niger Delta militancy and social and political unrest are a result of conflict between minority ethnic groups such as the Ijaw and the Ogoni who feel exploited by foreign oil corporations and foreign governments. The position of the U.S. in the control over oil production is a contentious issue; Nigerian oil accounts for 10% of U.S. oil imports (Watts, 2004). There is some concern that the U.S. may try to use conflicts in the North caused by radical Islamic groups such as Boko Haram to sever the largely Christian and oil-rich South (home to the Niger Delta Region) from the North (Anyadike, 2013).
Outside of the role of multinational corporations in conflicts in Nigeria, there are also the issues of job generation and environmental degradation (Stanley, 1990) The frequency of terrorism in the Niger Delta stems from frustration and anger predicated on common feelings of injustice by its citizens, and the view that the government has ignored the area’s exploitation, inequality, environmental insecurity, and infrastructural problems (Amaraegbu, 2011). Unlike the nonexistent state response to exploitation, the Nigerian reaction to the terrorists operating in the NDR often represents the maximum use of force (Okafor, 2011).
Agriculture
The network of extreme political violence in Nigeria strongly tracks along with the distribution of agricultural resources across Nigeria. Terrorism by Fulani herdsman is tied to food security, as the Fulani own 90% of Nigeria’s livestock, which represents a crucial piece of the food system. Thus, the Fulani hold an immense amount of power in the country (Abbass, 2014). Another of the biggest threats to food security has been the presence and expansion of Boko Haram. Some of the main practices of Boko Haram include exploiting local economies and controlling areas that are important for agriculture (Raineri & Martini, 2017). Boko Haram’s reliance on agriculture for resource generation was so large that at one point, the government banned agricultural activities in regions of Borno state to cut off a major supply source for Boko Haram. However, effectively this caused mass unemployment and resulted in large flocks of people joining the ranks of Boko Haram (Raineri & Martini, 2017). The size of the impact of Boko Haram as a terrorist group on agriculture has been compared to an entire armed conflict, due to the scale of the land abandonment and disruption of markets (Adelaja & George, 2019).
While research often focuses on the direct effects of violence, such as deaths, injuries, and property damage, terrorism in Nigeria is a clear example of the need to focus on indirect effects as well. Violence by Boko Haram and Fulani Herdsman has caused the direct deaths of thousands of people, yet millions more have been displaced or cut off from food supplies (Abbass, 2014; Raineri & Martini, 2017). These types of indirect effects are less common in Western Europe and the U.S. and demonstrate why we require a more nuanced understanding of the impacts of terrorism in Nigeria, and for extremist violence in Africa more generally.
Theoretical Perspectives
Terrorism straddles the line between multiple disciplines; it can be an inherently political or social act, but it also involves the commission of a crime. Historically, theoretical explanations of terrorism and crime have many similarities, although research has shown that causal mechanisms often differ (Frelich et al., 2015). Theories of deprivation are commonly used to explain terrorism from multiple perspectives (e.g., Gurr, 1970; LaFree & Schwarzenbach, 2021). Through a criminological lens, inequality has been linked to differences in the distribution of terrorists ideologically both in the US and Western Europe (Gries et al., 2011; Varaine, 2020). Additionally, there is some evidence that rational choice or deterrence perspectives can be applied to terrorism in relation to perceived benefits and costs accrued through governmental responses (Dugan & Chenoweth, 2012; Fisher & Kearns, 2023) and potential backlash (Argomaniz & Vidal-Diez, 2015; LaFree, Dugan & Korte, 2009). For Nigeria, government response to terrorism has been largely repressive (Nnam et al., 2020), both against terrorist groups and often against civilians. Such actions by the government have been by criminologists linked to an increase in terrorist participation in other contexts (LaFree, Dugan & Korte, 2009) as well as affecting the perceived legitimacy of counterterrorist efforts (Ali et al., 2022), and could be contributing similarly there as well. The Nigerian government represses many, and due to corruption often allows others to escape accountability, exacerbating tensions and failing to clamp down on much of the violence at the same time.
In Nigeria, ideological grievances associated with deprivation and government response are difficult to delineate. The perception that the Nigerian government is overly oppressive to its’ citizens while allowing multinational companies to profit is the source of anger for many, but widespread corruption contributes to perceived ineffectiveness of the government and thus potentially a lowered deterrent effect. In this way, economic inequality (Krieger & Meierrieks, 2012), heavy-handed government responses intertwined with other failures to act (LaFree, Dugan & Korte, 2009), the ability to purchase government incendiary devices on the black-market, and widespread corruption (Ali et al., 2022) combine to create an environment in which terrorism can thrive. Thus, further attention on Nigeria from a criminological perspective, is necessary to contribute to understandings of group dynamics in such conditions.
Methodology
We examine the networks of groups, actions, modes of violence, and geography to understand the network structure of extreme violence throughout Nigeria. First, we describe the data used before specifying methods of analysis.
Data
The Global Terrorism Database (GTD) is an open-source database that documents many details of terrorist attacks that have occurred worldwide since 1970. Developed by the National Consortium for the Study of Terrorism and Responses to Terrorism, and led by the University of Maryland (GTD, 2018), the GTD defines terrorist attacks as “the threatened or actual use of illegal force and violence by a non-state actor to attain a political, economic, religious, or social goal through fear, coercion, or intimidation” (GTD, 2018, p. 11). The GTD uses media articles to identify information such as an attack’s location, targets, casualties, motives, tactics, weapons, and property damage. It also includes data regarding who perpetrated an attack and whether a group has claimed the incident, or whether attribution was assigned by another source (such as law enforcement).
As is the case with many countries, data on terrorism perpetrated in Nigeria before the turn of the 21st century is extremely sparse, with most of the information pertaining to attacks that occurred during and after 2009. Out of the 5,070 incidents listed for Nigeria between 1976 and 2019, only 276 occurred before 2009, and 200 of those 276 incidents have an unknown perpetrator. Critically for Nigeria, the Boko Haram crisis began in 2009. Therefore, to provide a more accurate landscape of recent and ongoing threats, we focus our analyses on the post-2009 period. Incidents in the database account for 26,027 known fatalities of terrorism in Nigeria from 2009 to 2019. Many incidents do not have casualty information, however, so this figure is likely to be notably higher in actuality.
Missing Data
One of the main obstacles that terrorism research of any kind faces is that of missing data. Due to the nature of terrorist violence, perpetrators often die in the attack or the fallout, and groups are notoriously insular in their attempt to avoid law enforcement. For example, about 40% of the GTD has missingness on the group perpetrator level for all countries (Arva & Beieler, 2014). Recent government data is often unavailable due to ongoing investigations and cases, so researchers obtain most terrorism data from open-sources (Safer-Lichtenstein et al., 2017). The issue of missing data is particularly evident regarding the identification of a perpetrator group. In many cases, the perpetrator is unidentified, which poses challenges when examining patterns of group attributes (Arva & Beieler, 2014).
During the entire time-period (2009–2019), 25.2% of attacks in Nigeria are committed by “unknown” groups; they were neither claimed nor was responsibility attributed. Terrorism is often referred to as a weapon of the weak, or a symptom of asymmetric warfare (Min, 2013). Claiming a terrorist attack can provide a group with power they would not otherwise have, but also may incur counterterrorism attention. When a terrorist attack occurs, three potential situations can arise regarding claiming the attack: (1) a group perpetrates an attack and claims it; (2) an attack occurs, and a group other than the true perpetrator claims it; or (3) an attack occurs, and no one claims it. There are a number of factors that may contribute to how likely it is that responsibility for an attack will be acknowledged, including target type (Abrahms & Conrad, 2017), attack type (Kearns, 2019), organizational characteristics (Abrahms & Potter, 2015; Asal et al., 2009), strategic cooperation by sects to appear more credible and capable (Brown, 2020), ideology (Carter & Ahmed, 2020), and the ability of a group to make a credible claim through established infrastructures and networks (Wilkenfeld & Kaufman, 1993). Additionally, recent research has found that groups are more likely to claim in their early years of their lifespan, but that claims are often costly which is contributes to their decrease over time (Onder, 2023). Therefore, we believe there may be substantive differences between “unknown” attacks and those with known perpetrators, and we have chosen to include incidents with missing group attribution to demonstrate potential differences in unknown and known patterns in terrorist offending in Nigeria. 1
Network Analysis Approach
Bipartite networks are comprised of two node types consisting of “actors” and “events,” with direct ties connecting individual actors to events (Felmlee et al., 2024; Wasserman & Faust, 1994; Yarlagadda et al., 2018). We examine centrality in three, separate bipartite networks, each of which specifies terrorist groups as the “actors.” We analyze three types of “events,” including (1) attack location at the state level, (2) type of target, and (3) the type of attack. We constructed bipartite networks with rows representing the group perpetrators, and columns representing the focal event characteristic. A tie between a pair of groups in the state location bipartite matrix, for example, indicates that both groups committed a terrorist incident in the same state, and a tie between two states in the matrix means that a particular terrorist group committed a violent act at locations within the same two states. Following Yarlagadda et al. (2018), we dichotomize the matrix to perform two-mode centrality analyses (Borgatti & Everett, 2000). Centrality measures indicate the proportion of times two actors were involved in the same events out of all possible events.
Measures
Group
Each bipartite network includes the terrorist group as one mode of the network, with the other mode representing either: (1) location (state) of attack, (2) target type, or (3) attack method. We identify a terrorist group from a standard list of group names used by the GTD, which reflects the perpetrator attribution provided in open-source accounts (GTD, 2018). The group perpetrator is sometimes a generic identifier assigned by the GTD, and for the purposes of these analyses, we employ generic identifiers in a way that most closely represents their interests (such as “Muslim Extremists, or Tribesman”).
Attack Method
The GTD variable regarding the method of attack is representative of the general tactics used in the incident. There are eight possible categories, and when there are multiple attack methods used, the highest category in the hierarchy is listed. The hierarchy is as follows: Assassination, Hijacking, Kidnapping, Barricade, Bombing/Explosion, Armed Assault, Unarmed Assault, and Facility/Infrastructure Attack (GTD, 2018). For this time-period, there were 228 incidents with missingness on attack method. The sample for the group-attack network was 4,546.
Nigerian State
The GTD collects a variety of incident location information including country, state, city, and longitude and latitude. Due to the wide variation of circumstances and population between states in Nigeria, and the challenge of obtaining more disaggregated data, comparing patterns of group perpetration in Nigeria at the state level represents the most effective sampling strategy. Nigeria has 36 states and one Federal Capital Territory, and the group-state network demonstrates the states where each incident took place, with a line (edge) demonstrating which group carried out an attack in that state. Of the 4,774 incidents, 15 were missing a location; therefore, the group/state network was comprised of 4,759 incidents, at least one of which occurred in all states/territories.
Target Type
The GTD measures target type to reflect the motive of the attack rather than the actual target in isolation. For example, the GTD would code an attack on a government official that occurred in a commercial setting as belonging to the government category of target types (GTD, 2018). Up to three targets are recorded for each incident, but due to extremely high levels of missingness in any target type after the first, and for ease of interpretation, the current analyses only use the first-listed target type. In addition, 121 incidents were missing target information, therefore the sample for the group/target analyses was 4,653.
Results
Between 2009 and 2019, there were 40 groups associated with 4,774 terrorist attacks in Nigeria. 2 Importantly, Boko Haram was the perpetrator in just over half of the attacks (2,571), while the next most frequent offenders are Unknown (1,077), Fulani Extremists (913), Niger Delta Avengers (50) and MEND (45). Of the 4,759 incidents for which we have complete location information, terrorist attacks occurred mostly frequently in Borno (1,838), Benue (329), Plateau (299), Yobe (286), Adamawa (276), and Kaduna (209). Of the 4,653 incidents with non-missing target information, the category of private citizens and property was the most frequent target type (2,340) followed by the military (506), general government institutions (434), the police (363), and religious figures/institutions (277). Lastly, 4,546 incidents have complete information about the attack method. Terrorists employed Armed Assaults the most frequently (2,248), followed by Bombings/Explosions (1,206), Hostage Taking that included kidnapping (531), and a Facility/Infrastructure attack (287).
Bipartite Networks
The following section includes figures of each bipartite network and a table displaying the degree centrality scores for each network (Figure 2: Group/State; Figure 3: Group/Target Type; Figure 4: Group/Attack Method). The edges of each figure are weighted to show the number of times a group was associated with that event, with thicker lines being demonstrative of a higher frequency. Additionally, node sizes correspond with degree scores that are found in the related table for each graph; the larger the node, the higher degree score it has. In line with previous work (e.g., Breiger et al., 2014; Stadtfeld & Geyer-Schulz, 2011), we conducted the analysis of degree centrality on dichotomized networks, where any connection between an actor and event characteristic leads to a “1” in the matrix. Degree centrality when applied to bipartite networks represents the proportion of the number of events to which an actor is connected, or vice versa, on a scale from 0 to 1 (Faust, 1997). A number closer to 1 means that the actor or event had a higher number of distinct connections, with a value of 1 representing that an actor was connected to all events. Therefore, each analysis measures the number of unique connections for each, such as the number of states in which a group committed a terrorist act.
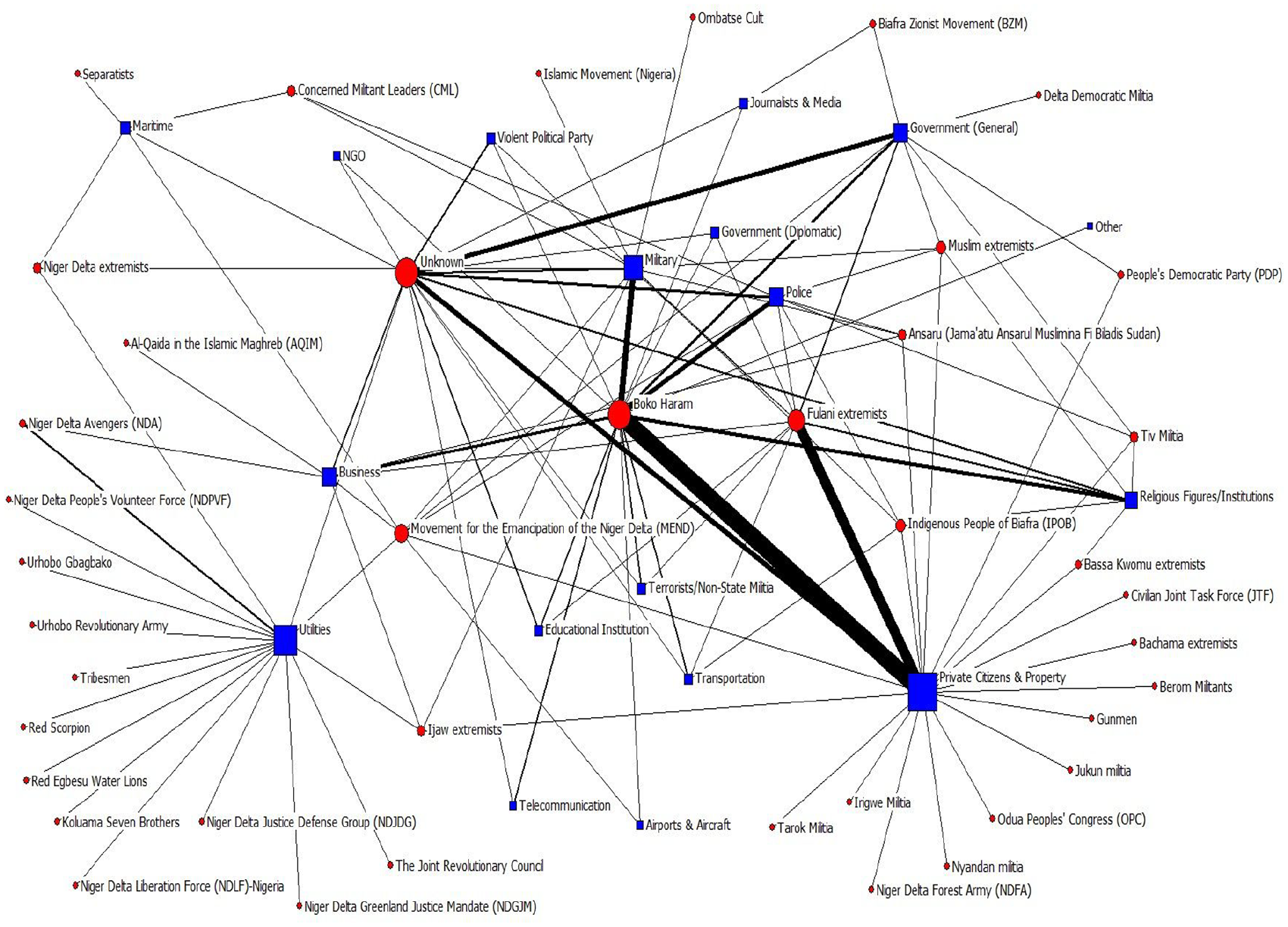
Group name (red) and target type (blue).
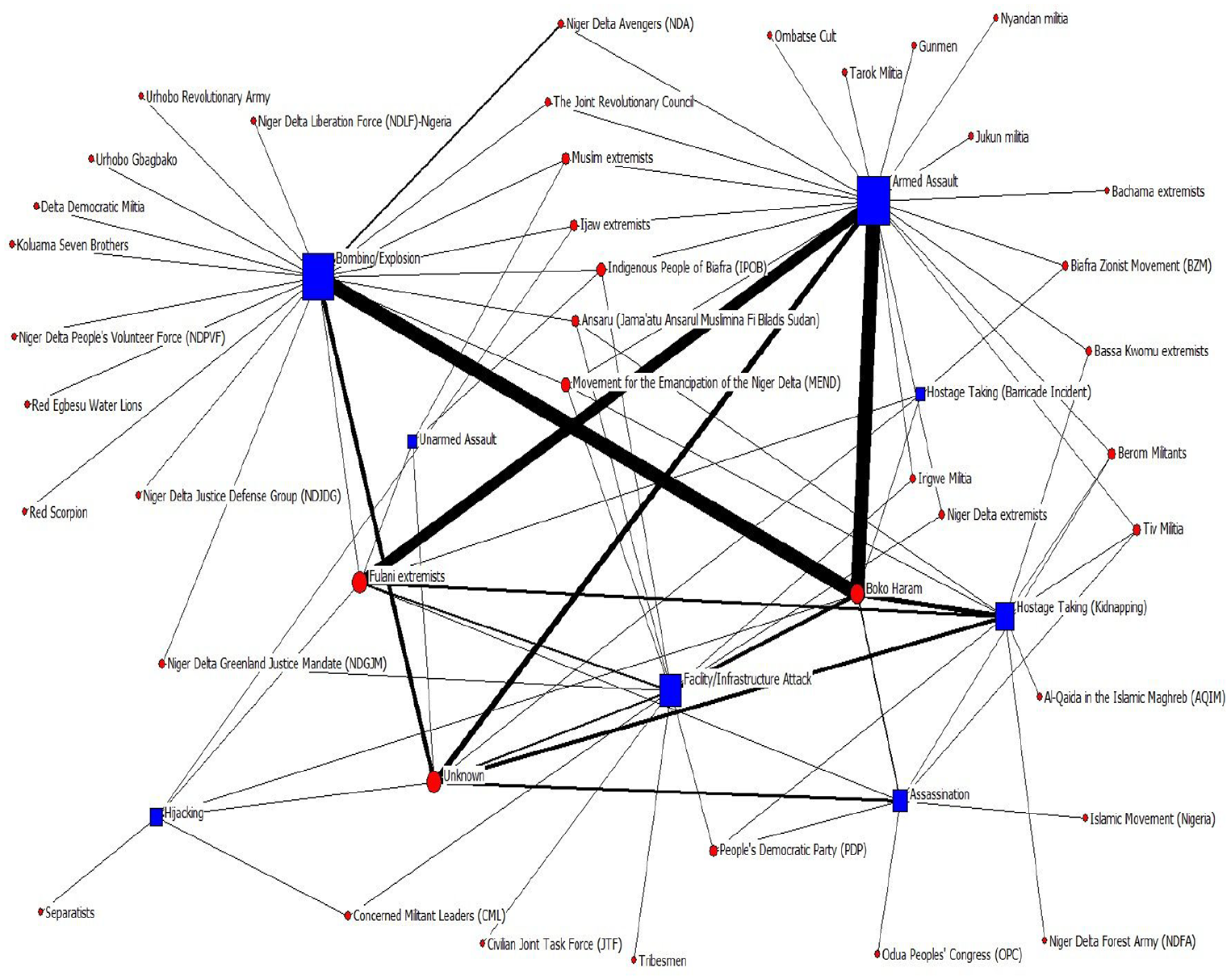
Group name (red) and attack method (blue).
Bipartite Network of Groups and Locations (by State) of Attacks
As we show in Figure 2, the most common terrorist event during this time-period was an attack by Boko Haram within the state of Borno, which is evident from the large dark edge connecting the two nodes, representing the high frequency of incidents. Figure 2 depicts group nodes as black, and state node colors correspond with the region in which they are a part based on the work of Okorie et al. (2013). 3 In alignment with the extensive differences in the Northern and Southern regions of Nigeria, and to demonstrate differential patterns between the regions, nodes related to states in the North are at the top, and states that are in the South are near the bottom.
Boko Haram also attacks frequently in Yobe and Kano, while the Fulani extremists tend to target locations in Benue and Plateau. Outside of Boko Haram, the Fulani Extremists have the greatest geographical reach. Boko Haram tends to focus their violence within states that are in Northern Nigeria, while the Fulani extremists are more prominent in the middle and South-West of Nigeria (e.g., Oyo, Niger, and Edo). However, this network analysis paints a picture of additional terrorist groups that are active in other regions of the nation. Several groups conduct attacks exclusively in the states Delta and Bayelsa, for example, likely due to the region-specific resource conflicts in those areas (Okafor, 2011).
The inclusion of attacks perpetrated by “unknown” terrorist groups further captures the complexity intrinsic to networks. Incidents may go unclaimed for a variety of reasons, such as strategy and capability (Min, 2013). The highest number of attacks with unknown perpetrators occurs in Plateau, Rivers, Kano, and Borno. Based on other general patterns of offending, one could assume that Boko Haram might be responsible for at least some of the events in Kano and Borno, and that the Fulani Extremists undertook some of the unknown attacks in Plateau. However, there are more unknown attacks in Rivers than from any one known group. Rivers is at the Southern tip of Nigeria, rich with oil, and the site of many conflicts over legal and illegal resource use (Chukwu, 2022). Discrepancies in patterns between known and unknown terrorist offenders should be analyzed for information that may allow for speculation on local and contextual reasons for claiming or not claiming such attacks (Verma et al., 2020).
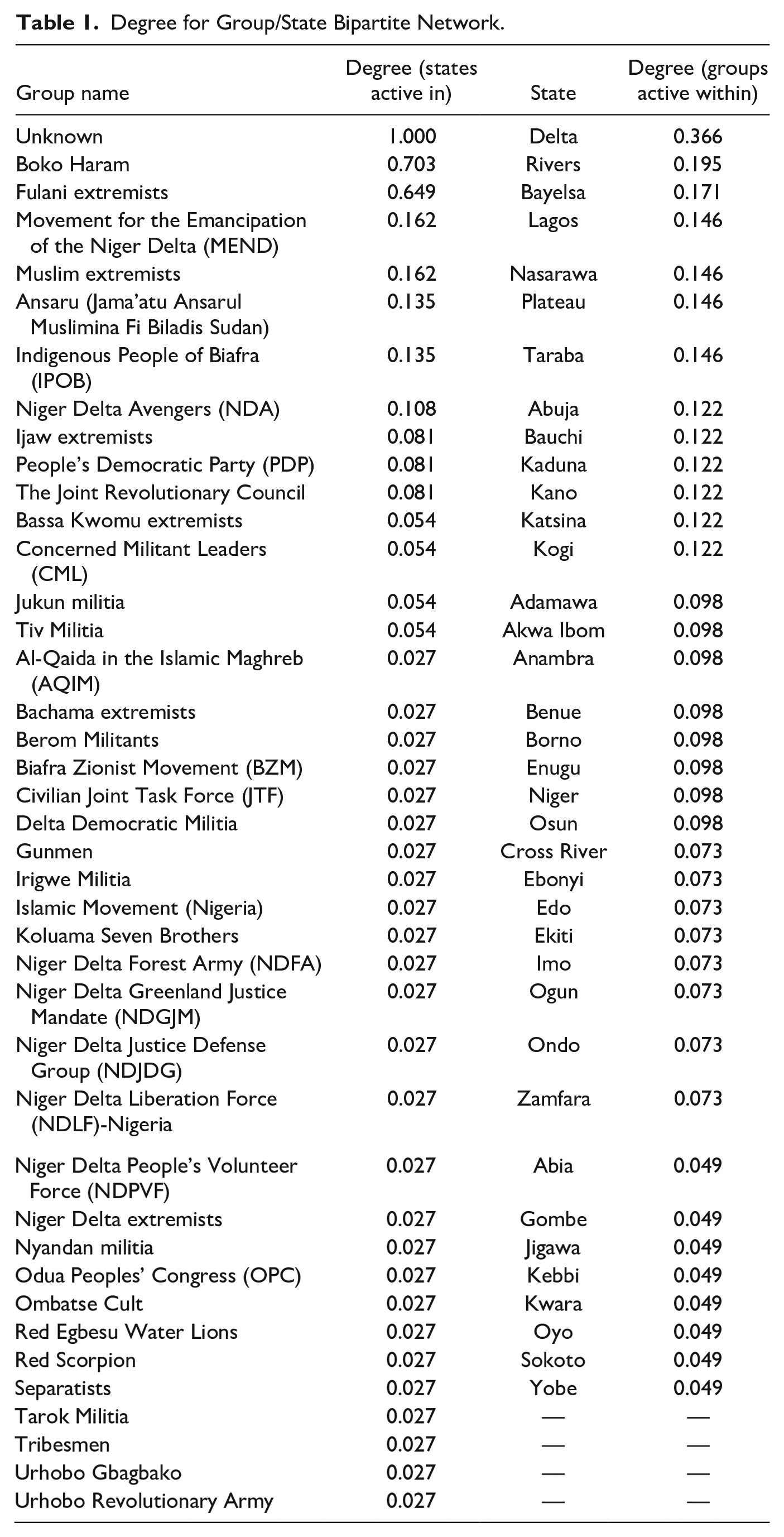
Next, we examine the relative centrality of the groups and the locations in the network. As shown in Table 1, Unknown perpetrators committed at least one attack in each state and territory in Nigeria (with a degree score of 1). Boko Haram had the next widest geographical reach (0.703), with at least one act of violence in approximately 70% of the states. Interestingly, only the Fulani Extremists were able to rival Boko Haram’s and the Unknown perpetrator’s range of impact, with incidents undertaken in close to two-thirds of states (0.649). Most groups, on the other hand, have low degree scores that suggest activity in only one to three states. Additionally, the analysis demonstrates which regions host the largest number of active terrorist groups (see Table 1, columns 3–4). While the Nigerian states of Borno, Adamawa, Plateau, Benue, and Yobe experienced the most attacks overall, they do not have the highest number of groups operating within them (i.e., they do not have the highest bipartite degree). Instead, Delta (0.366), Rivers (0.195), and Bayelsa (0.171) are victims of the widest range of terrorist groups, all of which are situated in the oil-rich Niger Delta region. The state of Delta, for example, has been the object of violence by over one-third of the terrorist groups (known and unknown).
Degree for Group/State Bipartite Network.
Bipartite Network of Groups and Type of Target
We show details regarding the target types that each group has attacked in Figure 3, with thicker lines denoting a more frequent focus on that type. Red nodes are groups and blue nodes are target types. Private citizens and property are by far the most frequent victims of attacks from both Boko Haram and the Fulani Extremists. The larger groups tend to focus on numerous types of targets, while some smaller groups concentrate solely on specific forms of targets, such as utilities. Many of the same groups (e.g., Niger Delta Liberation Force, Red Scorpion, Niger Delta Avengers, and the Urhobo Revolutionary Army) that are only connected to infrastructure attacks in Figure 2, exclusively perpetrate events in the Niger Delta region. Private citizens and property are also common targets of such singularly focused groups, including the Tarok, Ingwe, and Nyandan militias.
Comparing patterns of attacks by Unknown organizations to the larger network demonstrates an interesting dynamic. Attacks against the Government are connected to Unknown groups more frequently than to any one known group. This dynamic could imply that there is an incentive to avoid claiming an attack on the government, including that such an attack increases the chances of pursuit with deadly force by counterterrorism units.
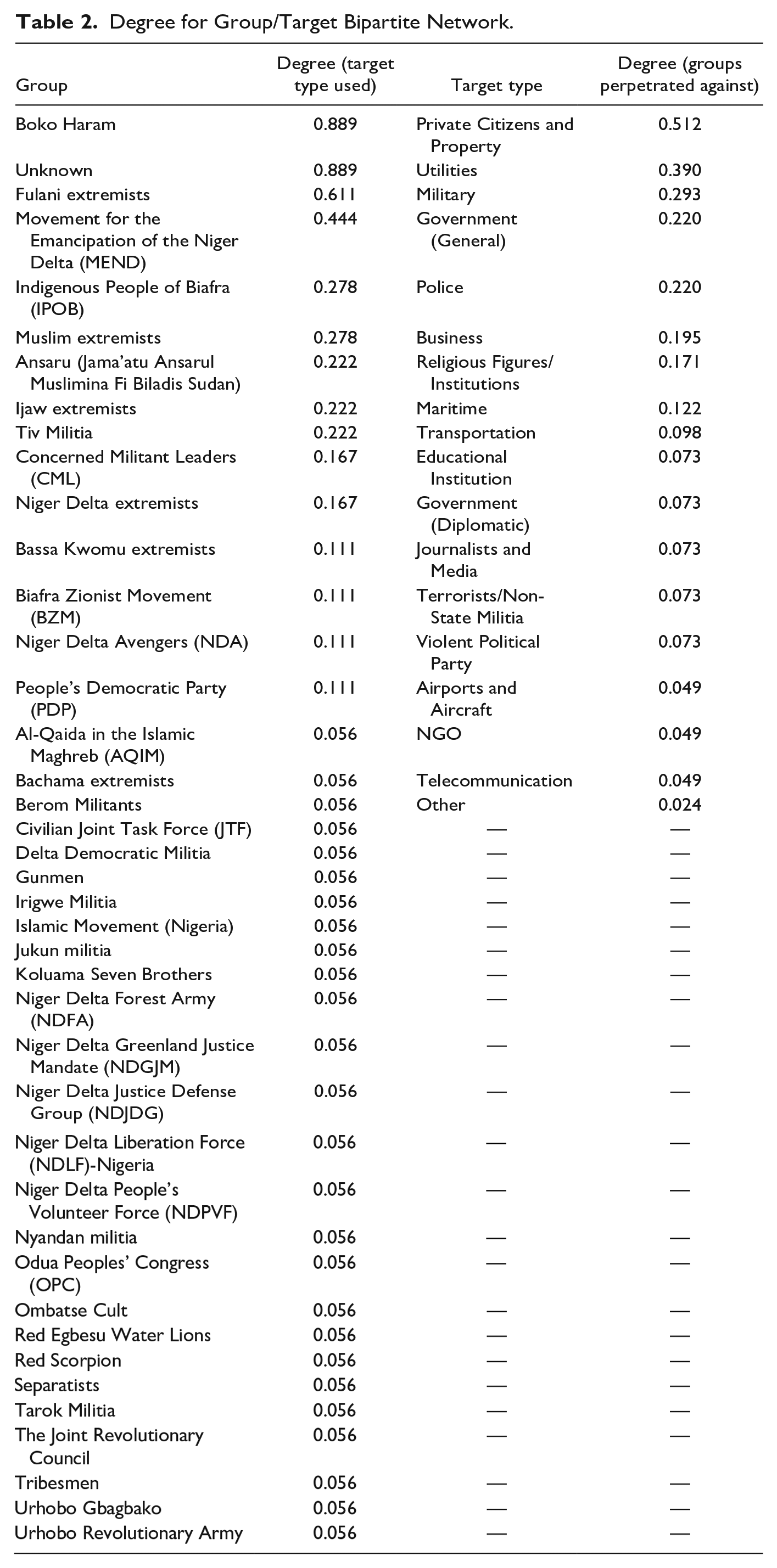
We next examine the bipartite degree centrality of groups by the type of target that they select. Table 2 delineates the degree scores for the Group/Target bipartite network. One sees that attacks on private citizens and property are the most common, with the degree score of 0.512 denoting that slightly more than half of the groups are involved in these sorts of incidents. We find that over a third of the groups targeted utilities (degree of 0.390), representing the importance of terrorist attacks against oil resources to groups beyond just Boko Haram and the Fulani Extremists.
Degree for Group/Target Bipartite Network.
Bipartite Network of Groups and Method of Attack
We highlight the methods of attack that each group employs in Figure 4. Red nodes are groups and blue nodes are attack types. Attack types can shed light on both capability and strategic choices of a group. As evident by this network graph, Boko Haram and the Fulani Extremists tend to use Armed Assaults most commonly, with Boko Haram also frequently using Bombings and Explosions. In addition, there appears to be patterns in the choices of some terrorist organizations, linking groups with the same areas and attack methods. For example, the same groups connected to infrastructure violence in the Niger Delta region tend to exclusively use Bombings/Explosions or Armed Assaults. Some of these groups (such as the Niger Delta Greenland Justice Mandate) also utilize direct facility attacks, but these are less common.
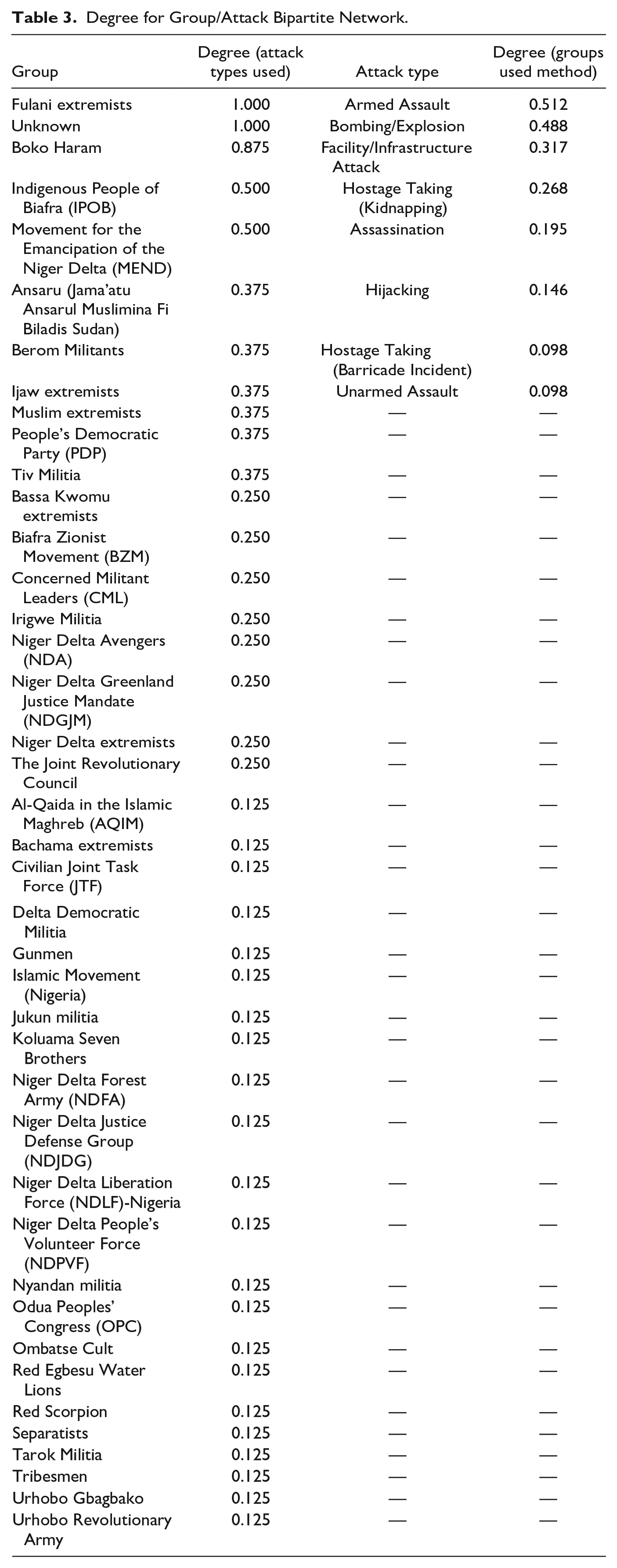
We provide an analysis of the degree centrality for groups by attack method in Table 3. This analysis shows that only Fulani Extremists and Unknown groups (degree scores of 1.00) were able to utilize all types. In other words, Fulani Extremists have a wide array of resources, tactics, and weapons available to them, and apparently on an even slightly broader scale than those accessible to Boko Haram (degree score of 0.875). Other groups also demonstrate a proclivity to use multiple means of enacting violence, including the Indigenous People of Biafra (0.500) and MEND (0.500). Overall, half of the perpetrator affiliations were able to utilize two or more methods, demonstrating that although Armed Assaults are frequently used, counterterrorism strategies need to account for a variety of attack tactics. Armed Assaults are by far the most common attack method (shown in Table 3) and are used by the highest number of groups (degree score 0.512). About fifty percent of the groups also have the capability to use Bombings/Explosions (0.488). This figure seems to indicate a higher level of sophistication of groups than previously acknowledged.
Degree for Group/Attack Bipartite Network.
Attack methods that require a significant number of resources to enact and sustain such as Hostage Taking (which is differentiated by kidnapping or the use of barricades), Assassination, or Hijacking are tactics used by a much smaller number of groups. In addition, these types of incidents often draw an immense amount of global media attention (e.g., the kidnapping of 276 Nigerian schoolgirls in 2014 by Boko Haram), which can result in an inordinate amount of counterterrorism action against the perpetrators. For example, following the 2014 kidnapping, First Lady Michelle Obama got involved in raising awareness of the issue with the hashtag “#BringBackOurGirls”, and the U.S. government became closely involved in the incident (McKelvey, 2016). Many groups may prefer to avoid the intense pressure that can come with these types of attacks (Mandala, 2017; Rasmussen, 2017), making them less likely to claim such acts (Verma et al., 2020), which could contribute to the comparatively large number of Hostage Takings and Assassinations shown as connected to Unknown perpetrators in Figure 4.
Discussion and Conclusion
We conducted a bipartite social network analysis of 40 groups associated with 4,774 terrorist attacks in Nigeria between 2009 and 2019. This section describes core takeaways from our study, highlights the important role of “Unknown” perpetrators in Nigeria, and importantly, delineates the policy implications derived from this analysis. Not surprisingly, Boko Haram in Borno represents the most common combination of terrorist group and targeted region. The actions of Boko Haram are more predominant in Northern Nigeria; Fulani extremists, the second most networked group, tend to concentrate their efforts in the middle and South-West of Nigeria. We saw that attacks against private citizens and property were the most common targets, especially from both Boko Haram and the Fulani Extremists. Boko Haram and the Fulani Extremists each most often committed Armed Assaults, although Boko Haram also frequently employs Bombings/Explosions. The Fulani Extremists alone employ all attack methods. The oil infrastructure in the Niger Delta represented a unique intersection of region, target type and attack technique that led to differential patterns compared to other parts of Nigeria.
These results demonstrate several important findings: (1) A one-size-fits-all approach to counterterrorism research and action in Nigeria neglects the relevance and repercussions of other actors. Focusing counterterrorism resources only on Boko Haram’s patterns of offending will miss a large segment (close to half) of other violent groups and targets. Fulani extremists, for example, are active in close to as many states as Boko Haram, focus efforts on a relatively wide array of targets, and employ every possible category of attack method; (2) Armed assaults are frequently the only way that many small and local groups perpetrate terrorist acts, and also represent a major method used by larger groups like Boko Haram and Fulani Extremists. Clamping down on the networks that facilitate the weapons trade could severely limit these activities. While the ability to access such large amounts of assault rifles and incendiary devices (including grenades and mortars) might seem out of reach for many terrorist organizations, in Nigeria, these are frequently pilfered from the Nigerian military itself or acquired on the black market (Windrem, 2014); (3) Differential patterns of offending exist for “Unknown” groups compared to those whose perpetrators are identified. Unknown groups tend to be active widely across the country. Likely due to the severity of reprisals, Unknown perpetrators are the group most often associated with assassinations and attacks on the government.
For Nigeria, theoretical perspectives focused on deprivation and governmental responses appear to be the most salient (e.g., Freilich et al., 2015; LaFree, Dugan and Korte, 2009; Varaine, 2020). A criminological focus on terrorism in Africa has been less commonly applied than in other contexts such as the U.S. or Western Europe, but due to the immense inequality experienced in Nigeria that is inextricably linked to the violence in the Niger Delta Region, deprivation models (both relative and criminological) appear to carry merit. Group patterns of offending lend some credence to the argument that economic grievances are tied to the ideologies of many groups in Nigeria, as has been found in other contexts (e.g., Pridemore & Freilich, 2006). Additionally, as is further described regarding policy implications below, it is likely that the government plays a role in both facilitating violence through corruption and exacerbating it due to repressive and indiscriminate responses.
Limitations and Future Research
Although there are strengths to this study, there are also limitations. For example, both Nigeria and the global community need additional information about the actions and targets of terrorist groups outside of Boko Haram to understand fully how frustration and perceived deprivation likely contribute to terrorist violence in Nigeria. Incorporating other data about Nigeria and its circumstances could aid the analysis of how Nigerian terrorism is linked to contextual factors such as economic distribution, population growth, food scarcity, and political or social division. However, such information is difficult to acquire across substantial time periods and the reliability of said data is questionable (Fawehinmi, 2018; Okoye, 2018). Investment into reliable data collection methods in Nigeria could go a long way toward enabling future analyses. We also need more information about groups, including about what factors determine the identification of a new or separate group. Particularly due to the way that the GTD codes actions under general names such as “Tribesmen,” it is possible or even likely that groups are interlinked in a way that is not easily gleaned from these data. These links could reflect group or leader structures (Freeman, 2014). Future analyses could identify incident patterns that can indicate which perpetrators are not acting in isolation. While other data such as Armed Conflict Location & Event Data Project (ACLED) has its’ own advantages, the threshold for inclusion in the GTD is specifically terrorism, which is the focus of this paper. Incidents in other datasets are beyond the scope of this analysis but would be interesting avenues of research for the future.
Our results suggest that including unknown perpetrators provides a better understanding of the terrorism network dynamics in Nigeria, suggesting a critical, future research question: how can we begin to identify some of the unknown perpetrators of Nigerian terrorism? Our bipartite analysis provides a lead. The largest numbers of attacks with unknown perpetrators occur in Plateau, Rivers, Kano, and Borno, and there are more unknown attacks in Rivers than from any identified group. We found frequent enclaves, with particular groups that operated in particular areas with particular means. Attacks with unclaimed offenders are often conducted against the Government, suggesting fear of retaliation (Onder, 2023) may drive claiming behavior. On the other hand, due to the immense interconnection between corrupt government officials and terrorist groups in Nigeria (e.g., Ojo et al., 2020; Suleiman & Karim, 2015; Windrem, 2014), attacks may remain unclaimed because they were supported by corrupt insiders and thus claiming may be risky or unnecessary. Terrorist attacks can be used to exploit public reaction for private gain by corrupt officials (Asongu & Nwachukwu, 2017). While claiming attacks can often be a way terrorist groups achieve power, unclaimed attacks could be used to serve political goals of corrupt elites such as heightening the perception of crisis. Researchers need to analyze this issue further, especially given that unknown terrorist actions occurred in each state and territory in Nigeria. Such an analysis could use event and contextual characteristics with artificial intelligence and machine learning techniques to identify patterns that denote likely perpetrators (Verma et al., 2020). The lack of reliable data is a large stumbling block for this endeavor but focusing on a specific number of cases and utilizing intensive data collection techniques rather than relying on secondary sources could aid in this attempt. Additionally, an analysis that includes mixed methods with a focus on group claiming behavior in an environment of both corruption and violent retaliation could be helpful to shed light on this complex dynamic.
Policy Implications
What is the policy value of a network study of terrorism in Nigeria? Analysts frequently critique the application of counter-terrorism resources (Allen, 2019; Okunade, 2021). A more complete picture of terrorism networks may better inform the government, helping to formulate improved counter-terrorism policy, directing resources more accurately, and thereby generating less resistance through collateral damage or mass repression. In addition, research that portrays analytical, comprehensive, and dynamic visualizations of violent non-state actors in Nigeria supports efforts to assess the effectiveness of Nigerian counterterrorism. With a wider lens, our analysis attempts to provide a comprehensive, and thus a germane, understanding of the array of factors that contribute to counterterrorism success and failure, allowing the Nigerian government and its global allies to generate and refine policy appropriately.
Our findings further demonstrate that areas with critical oil infrastructure experience frequent violent incidents. Thus, energy policy in Nigeria could also be framed to represent counterterrorism policy. For example, an energy policy that provides localities more voice may lead to less hostility, as research has shown that areas where local ethnic groups can express grievances with the federal government experience far less violence (Koos & Pierskalla, 2016). Placing an emphasis on not only preventing extremist violence through militaristic avenues, but also on systemic change in the distribution of political will and power (Dmello et al., 2022) in Nigeria would be an effective way of slowing the intent to commit terrorism, rather than only focusing on disrupting the means and the terrorist networks.
In addition, it is possible (and in some cases likely) that the widespread corruption in Nigeria hampers counterterrorist policy and law enforcement intervention. The Fulani Herdsmen and Boko Haram, for example, have considerable access to resources that can be used to protect terrorist actors, facilitating the expansive reach that our analyses have demonstrated. Additionally, the complex interplay between corruption, multinational companies, extremists, and government officials in the Niger Delta Region contributes to a hazy environment where, as evidenced by the high degree scores of Delta, Rivers, and Bayelsa, many extremist groups are able to flourish. It is not a stretch of the imagination to assume that if military resources are being sold to extremists (Windrem, 2014), that government protection can also be purchased. Additionally, there is evidence that the activities of Boko Haram have been used as a cover for pilfering state resources by military and political elites (Ojo et al., 2020). Due to this, the corrupt are incentivized to keep crises and instability going (Asongu & Nwachukwu, 2017) and are disincentivized to create meaningful change through effective counterterrorist policy. Terrorist groups in the 21st century have been known to operate in a similar fashion to or even merge with organized crime groups (Rodermond & Thijs, 2023; Viano, 2020), which poses operational needs for counterterrorism that go beyond grievance alleviation. Counterterrorist policy may be best served by providing avenues to express and rectify legitimate grievances for the people, but also by combatting the corruption that is both contributing to the rise of inequality based grievances (Suleiman & Karim, 2015) and allowing extremists to evade meaningful consequences when money is placed in the right hands.
In conclusion, the common understanding of terrorism in Africa reflects a “vast oversimplification” (Piombo, 2007), and that perspective is especially the case in Nigeria. To better capture the complexity of violent extremism in Nigeria, we employ a bipartite social network approach to develop a comprehensive understanding of multiple terrorism networks in Nigeria. Our study demonstrates that while Boko Haram is the dominant national terrorist group, there is substantial variation among Nigerian terrorist groups by state, target type and attack mode. Unclaimed terrorist actions by “Unknown” perpetrators, for example, capture the efforts observed in a large number of events, especially when government response is likely, suggesting that some counterterrorism (perhaps by being overly repressive) may effectively decrease terrorist activity (but at a national cost). At the same time, we observe several strong combinations of: group and incident state (e.g., Fulani/Bayelsa, Boko Haram/Rivers, and MEND/Lagos), group and target type (e.g., Boko Haram/people and property, Fulani/military, and MEND/government), and group and attack method type (e.g., Fulani/Armed Assault, Boko/Infrastructure, and IPOB/Hostage taking). Overall, our study demonstrates the viability of a social network analysis of African terrorism data and the importance of avoiding oversimplification by presenting a more complete picture of terrorism activities.
Footnotes
Author Note
The views presented are those of the authors and do not necessarily represent the views of the US Department of Defense, the Department of the Navy, or the Naval Postgraduate School.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received financial support for this research from the Penn State Criminal Justice Research Center, the Penn State Center for Security Research and Education, and the Naval Postgraduate School Global ECCO Program.
