Abstract
With the rapid growth of information technologies, mobile devices have been utilized in a variety of services such as e-commerce. When a remote server provides such e-commerce services to a user, it must verify the legitimacy of the user over an insecure communication channel. Therefore, remote user authentication has been widely deployed to verify the legitimacy of remote user login requests using mobile devices like smart cards. In this paper we propose a smart card-based authentication scheme that provides both user anonymity and mutual authentication between a remote server and a user. The proposed authentication scheme is a simple and efficient system applicable to the limited resource and low computing performance of the smart card.
The proposed scheme provides not only resilience to potential attacks in the smart card-based authentication scheme, but also secure authentication functions. A smart card performs a simple one-way hash function, the operations of exclusive-or and concatenation in the authentication phase of the proposed scheme. The proposed scheme also provides user anonymity using a dynamic identity and key agreement, and secure password change.
1. Introduction
The main aim of the remote authentication scheme using smart cards is to identify and verify the smart card holder with valid access rights and access to the remote server. It has been widely accepted that the smart card-based remote user authentication is one of the most reliable and secure forms of electronic identification for authentication. Therefore, a variety of password-based authentication schemes have been proposed for remote authentication using smart cards. In a traditional remote authentication scheme, a user has to register her own identity and password to the server in advance, and she has to submit the identity and password information to the server during a login process. On receiving a login request, the remote server authorizes the user to access facilities provided by the remote server, if the pair of identity and password is equivalent to the one stored in the server's password table. Otherwise, the access request is rejected.
The desirable security requirements of an authentication scheme using smart cards are as follows. The scheme should resist malicious insider, replay, guess, stolen-verifier and impersonation attacks. Also, the scheme should provide both forward secrecy and known-key security, guaranteeing user anonymity.
The desirable functionality requirements of an authentication scheme are as follows. A user chooses her identity and password freely and changes her password securely, and a remote server does not maintain a verification table to authenticate the user in the server. Due to the power constraints of smart cards, the computational cost of the scheme has to be low and the scheme should provide mutual authentication, user anonymity and session key agreement between a user and a server without requesting time-synchronization between user and server.
In this paper we propose an enhanced authentication scheme using smart cards. Our scheme satisfies the security requirements and functions.
The remainder of this paper is organized as follows: section 2 reviews related works; section 3 details the proposed authentication scheme; section 4 analyses its security; section 5 analyses its performance and functionality. Finally, Section 6 draws brief conclusions.
2. Related Works
A number of remote authentication schemes have been suggested by researchers from time to time. When a server authenticates a user, the server verifies the user with the entered user's identity and password, and the corresponding values in the verification table of the server. In 1981, Lamport [1] presented a remote authentication scheme using password tables, but security holes and maintenance responsibilities for the verification table exist because it must always maintain the verification table. Also, a stolen verification table may cause many security threats, therefore, in 1990, Hwang [2] presented a remote authentication scheme without password tables. Many other studies have also proposed a scheme that does not maintain the verification table to authenticate the remote user.
Numerous studies [7–16] have proposed a scheme using the one-way hash function and exclusive-or operation due to the constrained resources and computing power of a smart card.
After the user's authentication is completed, the communication channel for a message may be insecure. If the message is not encrypted, then the message is revealed to an adversary. Therefore, previous studies [11–14, 16] have proposed session key generation schemes using key agreement between user and server, and researchers have also pointed to the weaknesses of other schemes [3, 4].
Because the user's anonymity is very important in many e-commerce applications, several schemes [5, 6, 9, 12-13, 15, 16] have been proposed to achieve user anonymity in the authentication phase.
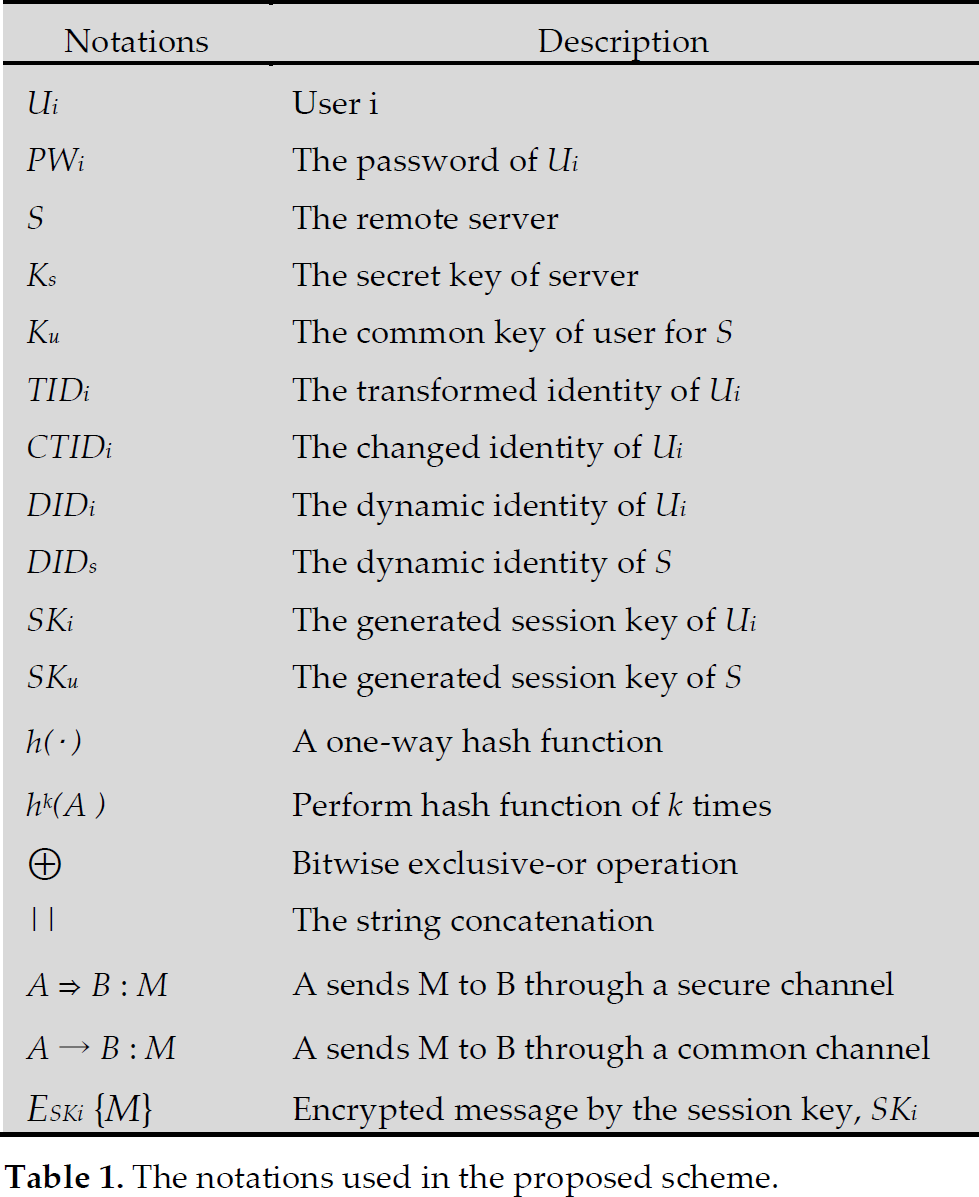
The notations used in the proposed scheme.
Bindu et al. [6] showed the possibility of insider attack, Main-in-Middle attack, in the scheme of Chien et al. [5] and presented an improved scheme preserving user anonymity. However, the scheme does not provide a password change phase and uses time-stamp to resist replay attack. Lin et al. [8] presented a new strong-password authentication protocol that can withstand a stolen-verifier attack and other possible attacks, but the scheme cannot change passwords and does not provide mutual authentication, session key agreement and user anonymity. Juang [10] presents a simple authentication scheme, but the scheme cannot change passwords and does not provide mutual authentication. Recently, Khan et al. [13] and Tseng et al. [16] presented authentication schemes providing user anonymity and mutual authentication. With the scheme proposed by Tseng et al. [16] the user can freely choose the password and securely change the password, however, both schemes require time synchronization to protect from replay attack.
Here, we point to security issues related to Das et al.'s scheme [15] and Liao et al.'s scheme [14].
1) Both schemes submit a user password directly to the server in the registration phase. Thus, their schemes are vulnerable to insider attacks. If a malicious insider obtains a user password in the registration phase, she may be able to access the other server over a network, because generally, a user is apt to use the same password for convenience, even for most other servers.
2) Neither scheme provides user anonymity. Although Das et al.'s scheme uses a dynamic identity in the verification phase as the user login in the remote server, she always sends the user specific value, Ni. Therefore, the user's location is revealed to the adversary. In Liao et al.'s scheme, a user sends her identity directly via a common channel. Thus, an adversary can know the user's location.
3) Neither scheme provides secure password change as their password change phase is insecure. When a user inputs the wrong password by mistake, the smart card's password is changed to the wrong password.
4) Das et al.'s scheme does not provide mutual authentication. The server can authenticate a user, but a user cannot authenticate the remote server.
5) Das et al.'s scheme does not have a session key agreement. After mutual authentication between user and server, important messages have to be protected from adversaries, thus, session key agreement is needed. However, Das et al.'s scheme does not provide session key agreement.
6) Das et al.'s scheme requires time synchronization and uses time-stamp for replay attack. Thus, it requires time synchronization between user and server.
3. Proposed Authentication Scheme
In this section, we propose an enhanced security scheme for mutual authentication and user anonymity using a smart card. The proposed scheme overcomes the weaknesses of Das et al.'s scheme and Liao et al.'s scheme, while it enhances security compared to the existing schemes. The proposed scheme is composed of four phases: registration, login and authentication, key agreement and secure password update. Table 1 is the notation used in the proposed scheme.
3.1 Registration Phase
When user U i wants to access a remote server for a service legitimately, U i should perform the following registration steps before the access. The procedure is as follows:
Step 1. U i ⇒ S: ID i , h(PW i )
U i chooses her identity, ID i , and password, PW i , for registration and submits ID i and, h(PW i ) hashed value of PW i , to the remote server via a secure communication channel. Both ID i and PW i are selected by the user freely.
Step 2. After receiving ID i and h(PW i ) from U i , the remote server, S performs the following steps:
S generates transform identity TID i = h(ID i ‖ h(PW i )), and checks the existence of the transformed identity in the database. If the identity already exists in the database, S requests U i to re-initiate the registration procedure with a different ID i or PW i . Otherwise, S stores TID i in the database. This process ensures the uniqueness of the user's transformed identity.
Compute A i = (h(K u )⊕K s ), where K s is a secret key of S and K u is a common key of user for S. K u is used to generate a dynamic identity, DID i in the login and authentication phase.
Compute Bi = (gAi mod p)⊕h(PWi), where g is a primitive element in Galoisfield GF(p) and p is a large prime positive integer.
Store the values DID i , B i , h(·) and K u in a smart card and issue the smart card to U i .

Registration phase.
3.2 Login and Authentication Phase
After U i registers to S, when U i wants to log into the server, U i will send a, login message to S. The login message contains a dynamic identity, DID i to guarantee user anonymity. After successful verification of the login message, U i can authenticate S and S can authenticate U i . That is, our scheme provides mutual authentication. The login and the authentication phases work as follows:
Login phase: U i → S: DID i , CTID i , C i , k i
User, U i , connects her smart card to a reader She inputs her identity, ID i and password, PW i . The smart card performs the following processes:
Generate nonces, n i and k i .
Compute CTID i = TID i ⊕n i .
Compute C i = h(B i ⊕h(PW i ))⊕n i .
Compute M i = K u mod k i .
Compute DIDi = hMi(TIDi⊕Bi⊕h(PWi)).
U i sends DID i , CTID i , C i and k i with the login request message to S.
Authentication phase:
The proposed scheme provides mutual authentication. U i and S perform the following processes to achieve this, after U i sends the request message to S.
Step 1. S → U i : DID s , CTID s
S does the following processes to authenticate U i :
Compute A i = h(K)⊕K s .
Compute gAi mod p and execute the hash operation for this value, h(gAi mod p).
Execute exclusive-or operation the received C i and the value, h(gAi mod p) for the value ni′ = Ci⊕h(gAi mod p).
To compute TID i ′, S executes exclusive-or operation with the received value, CTID i and the generated value n i ′, TID i ′ = CTID i ⊕n i ′. Then, S checks that TID i ′ is the registered transform identity in the database. If the value is not valid, terminate the connection, otherwise, continue the process.
Compute M i = K u mod k i .
S computes DIDi′ = hMi(TIDi⊕h(gAi mod p)) and compares the received value, DID i and the generated value, DID i ′ by the server. If DID i ′ = DID i , S authenticates the legitimate user, U i . Otherwise, S fails authentication of U i and S terminates the connection with U i .
Generate nonce n s .
Compute DID s = h(DID i ⊕n i ⊕n s ) and CTID s = CTID i ⊕n s .
S sends DID s and CTID s to U i .
Step 2. U i → S : DID is
User, U i , authenticates S and mutual authentication is completed according to the following processes:
Compute n s ′= CTID s ⊕CTID i .
U i computes DID s ′ = h(DID s ⊕n i ⊕n s ′) and compares the received value, DID s and the generated value, DID s ′. If DID s ′ = DID s , the user, U i authenticates the remote server, S. Otherwise, U i fails server authentication and terminates connection with S.
U i computes the value, DID is = DID s ⊕n i ⊕(n s +1) and sends DID is to S.
S computes (n s +1)′ = DID is ⊕n i ⊕DID s , compares the value, (n s +1) and the generated value, (n s +1)′. If (n s + 1′ = (n s +1) mutual authentication is complete. Otherwise, S terminates connection with U i .
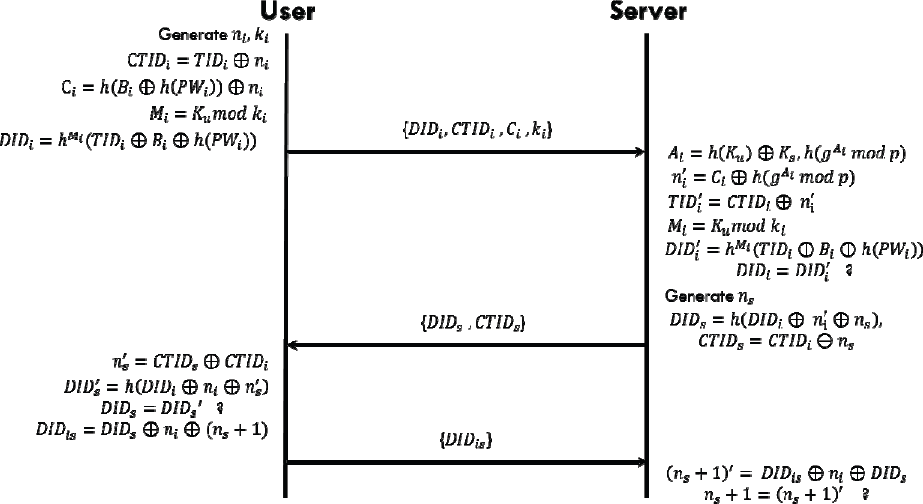
Login and authentication phase.
3.3 Key Agreement Phase
After U i and S bring mutual authentication to completion, they generate the session keys for secure transmission of messages to each other. Then the session key is generated using information (values) in the authentication phase.
Step 1. User, U i , generates session key, SK i .
U i computes SK i = h(B i ⊕h(PW i )⊕n i ⊕n s ), SK i is the session key generated by the user. Then, values, B i , h(PW i ), n i and n s are not revealed in transmission via a common channel.
Step 2. Remote server, S, generates session key, SK s .
S computes SKs = h((gAi mod p)⊕ni⊕ns). SK s is the session key generated by the remote server In addition, values gAi mod p, ni and n s are not revealed in transmission via a common channel.
SK i and SK s are the same values, since (gAi mod p) = B i ⊕h(PW i ), Thus, the session key is created safely between the user, U i and the remote server, S.
3.4 Secure Password Update Phase
When user U i wants to change her password for personal reasons or for the sake of security, U i can change her password freely. The proposed scheme provides secure password change The procedure is as follows:
U i →S : DID i , CTID i , C i , k i , M request-change-PWi U i inserts the smart card into a reader and sends DID i , CTID i , C i , and k i with the request message, M request-change-PWi to S.
Mutual authentication is performed between U i and S, as in the login and authentication phase, mentioned earlier.
U i generates new password, PW i * and computes TID i * = h(ID i ⊕h(PW i * ))
U i → S : E SKi {TID i * } U i encrypts new transform identity TID i * using session key SK i and sends the encrypted message to the server.
S decrypts the received message using SK s and then replaces the value, TID i with the received value TID i * . S sends the response message to U i .
After receiving the response message from S, U i computes B i * = B i ⊕h(PW i )⊕h(PW i * ) and replaces stored values in the smart card TID i and B i with TID i * and B i with each other.

Secure password update phase.
4. Security Analysis
In this section, we analyse the security of the proposed scheme. The proposed scheme can resist insider, replay, guessing, stolen-verifier and impersonation attacks, and provide user anonymity, forward secrecy, known-key security and mutual authentication for enhanced security.
4.1 The proposed scheme can resist an insider attack
In the registration phase, U i submits her identity, ID i and the hashed value of password, h(PW i ) instead of PW i for remote-access services. Due to the employment of the one-way hash function h(·), it is impossible for an insider to derive the user's password PW i from the hashed value, h(PW i ). That is, even the server does not know PW i . Therefore, the proposed scheme can prevent insider attack.
4.2 The proposed scheme can resist a replay attack
Assume that an adversary eavesdrops on the login message sent by U i when logging into the server in a later session. However, the replay of U i 's previous login message will be detected by the server. In Step 2 of login and authentication, the adversary computes the value (DID is = DID s ⊕n i ⊕(n s +1)) for mutual authentication and the value is sent to the server. The adversary generates n a and computes DID as = DID s ⊕n a ⊕(n s +1), because she does not know the value, n i and sends DID as to the server. The server will derive the value (n s +1)′ from the value DID as sent by the adversary. However, it is (n s +1)′ ≠ (n s +1), since DID as ⊕DID s ≠ DID is ⊕DID s . Therefore, the adversary cannot launch a replay attack.
4.3 The proposed scheme can resist a guessing attack
Suppose an adversary finds out the identity and the password of a legitimate user by guessing. She can compute valid values, TID i = h(ID i ‖PW i ) and CTID i = TID i ⊕n i *. However, she does not know B i and K u . Thus, she cannot compute valid values, C i and DID i . Hence, the adversary cannot generate a valid login message.
4.4 The proposed scheme can resist a stolen-verifier attack
The server stores only the transformed user's identity in the database and does not store the user's other secret information corresponding to her transformed identity in the proposed scheme. Thus, only the malicious insider or intruder gets the table of the user's transformed identity. Hence, the adversary cannot launch a stolen-verifier attack.
4.5 The proposed scheme can resist impersonation attack
If an adversary wants to impersonate U i , she has to create a valid login message: DID i , CTID i , C i and k i . First, she has to choose a nonce n i * and compute CTID i * = TID i ⊕n i * , C i * = h(B i ⊕h(PW i ))⊕n i * , M i * = y mod k i * , DIDi* = h i *(TIDi⊕Bi⊕h(PWi)). Next, she summits the login message : DID i * , CTID i * , C i * , k i * to the server. The adversary cannot forge a valid login message as she has no idea about B i , PW i , and y. Hence, she cannot launch an impersonation attack.
4.6 The proposed scheme can provide user anonymity
Consider an adversary eavesdrops on the login message, DID i , CTID i , C i and k i . Here, DID i is the dynamic identity and as CTID i and C i are computed by nonce, n i , they are different in the login phase. In addition, the value k i is not the same in each login phase. Thus, the login messages submitted to the server are different in the login sessions. Hence, it is difficult for the adversary to discover a user's identity.
4.7 The proposed scheme can provide forward secrecy
Suppose, the long-term secret key material (e.g. server's secret key K s and user's password PW i ) is revealed to an adversary. Although the adversary knows the secret key material, she cannot compromise the secrecy of the agreed keys in earlier runs because the session key is computed using the long-term secret key material and nonce ni(j-th) and ns(j-th). Thus, if the adversary does not know the values ni(j-th) and ns(j-th), she cannot derive the j-th session key. Hence, the proposed scheme provides forward secrecy.
4.8 The proposed scheme can provide known-key security
Suppose that in the j-th session, the session key SKi(j-th) is compromised by an adversary. Then the adversary cannot further compromise other secret keys or session keys because the session key SKi(k-th)(j≠k) uses nonce ni(k-th) and ns(k-th). Hence, the proposed scheme can achieve known-key security.
4.9 The proposed scheme can provide mutual authentication
In the login and authentication phase, U i and the server securely exchange a nonce of user, n i and a nonce of server, n s respectively. Thus, U i generates session key SK i = h(B i ⊕h(PW i )⊕n i ⊕n s ) and the server generates session key SKs = h((gAi mod p)⊕ni⊕ns). (gAi mod p) = Bi⊕h(PWi) and the values n i and n s are not revealed in a common channel. Thus, the values SK i and SK s are the same and are secure.
5. Performance and Functionality Analysis
The proposed scheme achieves mutual authentication using only a one-way hash function and bitwise exclusive-or operation in a smart card. We prefer to adopt modular exponentiation, a relatively expensive operation, in the registration phase. However, it is performed only at the remote server. Thus, the proposed authentication in this paper is pertinent to using a practical smart card. In addition, it provides session key agreement and a secure password change. Table 2 compares performance.
Performance comparisons of authentication schemes.

C : Concatenation
H : One-way hash function
⊕: Bitwise exclusive-or
M : Modular exponentiation
E : Encryption
D : Decryption
A : Arithmetic operation, such as add, subtraction and absolute value.
O : Comparison operation
+ : More
We summarize the functionalities of our proposed scheme in this section. The crucial criteria in the user authentication scheme are listed below:
F1. Freely chosen password: in the registration phase, a user can choose her identity and password freely for remote-access services.
F2. Secure password change: the user can change her password when she wants to change her password for the sake of security. In our scheme, after the user and server are authenticated, the password change is securely accomplished. Then, the generated value TID i * is encrypted by the session key and transmitted to the server.
F3. No verification table: if the server maintains the verification table, when the verification table is revealed to an adversary, the overall authentication mechanism breaks down. Our scheme does not maintain the verification table with the user identity and corresponding password for user authentication. Only the server has a transformed identity table for user authentication.
F4. Low computation: computation overhead must be low in smart cards due to their constrained resources. Our scheme accomplishes mutual authentication merely by hash operation and bitwise exclusive-or operation.
F5. Mutual authentication: a malicious person can disguise herself as the server or can disguise herself as the user. However, our scheme can provide mutual authentication between user and server.
F6. Session key agreement: the user and the server communicate via a common channel after mutual authentication is accomplished. The session key agreement is provided for secure transmission of the important messages. The security of the session key is very important. Our scheme provides session key agreement and at the end of the key exchange, the session key is known to nobody but the user and the server.
F7. Avoiding time synchronization: our scheme adopts a nonce instead of using a time-stamp to prevent replay attacks and a synchronization problem. Thus, our scheme does not need time synchronization between user and server.
F8. User anonymity: our scheme uses dynamic identity for user anonymity. Whenever a user connects to the server for remote-access services, she sends a different identity. Thus, our scheme provides user anonymity.
Table 3 compares functionality. The proposed scheme satisfies the required functionalities.
Functionality comparisons of authentication schemes.

F1. Freely chosen password
F2. Secure password change
F3. No verification table
F4. Low calculation for authentication
F5. Mutual authentication
F6. Session key agreement
F7. Avoiding time synchronization
F8. User anonymity
6. Conclusion
In this paper we proposed a security enhancement scheme of mutual authentication and user anonymity using smart cards. The proposed scheme does not send the user specific value in the login and authentication phase. Thus, it achieves user anonymity. The proposed scheme can resist insider, replay, guessing, stolen-verifier and impersonation attacks, and provides forward secrecy, known-key security and mutual authentication to enhance security. A user can freely choose her password and can change the password safely. In addition, our scheme provides the following functionalities: no verification table, avoiding time synchronization, eviction mechanism, session key agreement and low computation.
Footnotes
7. Acknowledgments
This research was supported by the MKE (The Mnistry of Knowledge Economy), Korea, under the Convergence-ITRC (Convergence Information Technology Research Center) support programme (NIPA-2011 C6150-1101-0004) supervised by the NIPA (National IT Industry Promotion Agency).
