Abstract
BACKGROUND:
Patient data in current computed tomography scanner machines are transferred through several communication channels, such as WiFi, to the mobile channel platform. Therefore, patient information is an important security concern. Medical imaging must be protected using various methods.
OBJECTIVE:
The current hardware-dependent method for generating random bits exhibits predictable or inconvenient physical characteristics. Therefore, a more flexible random-bit generation technique is to be devised.
METHODS:
We propose a deterministic random bit generation algorithm that uses a mathematical periodic function.
RESULTS:
After randomizing the image using the proposed random bit, the performance is analyzed and compared with that of the processed image.
CONCLUSION:
The random bit generation method using a mathematical algorithm shows higher entropy than the random bit generated by hardware.
Introduction
Current medical machines can share patient data through secured communication channels, such as wirelines of the cable network and wireless transmission lines [1, 2, 3, 4]. However, access from secured channels to private communication devices, such as tablets or cellular phones, has been adopted because of immediate data necessity to healthcare workers [5, 6, 7, 8, 9].
Several algorithms have been investigated for various medical equipment to protect patient data, such as text and image data [10, 11, 12]. The Rivest-Shamir-Adleman (RSA) algorithm has been widely used for encrypting information in medical equipment [13, 14, 15]. A 2048-bit RSA, secure hash, and advanced encryption standard algorithm were used for the data distribution of protected information [16, 17, 18]. A prime-number-based RSA-encrypted algorithm was developed to improve security [19, 20, 21].
Among these systems, CT provides the highest spatial resolution with the high amount of image data [22, 23, 24]. The image data in a CT scanner with a secured encrypted password must be used. Therefore, information security must be protected using cryptographic algorithms to protect patient information. However, data from scanners to private devices can be leaked when transferred [25].
Methods
In this study, a true random bit is generated when the probabilities
True random bits are impossible to generate or identify [28]. Thus, the random bits are deterministic random bits. A deterministic random bit must satisfy the functional relationship of one-to-one correspondence between the independent variable and the dependent variable as shown in Fig. 1 and Eq. (2) [29, 30].
Onetoone mapping function.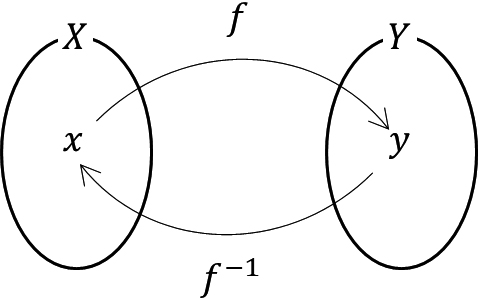
Equation (3) represents the periodic function. The
The proposed algorithm utilizes the characteristics of digital systems, in which mathematical continuity is impossible [31, 32]. In other words, it is expressed as shown in Fig. 2.
Periodic function in digital system.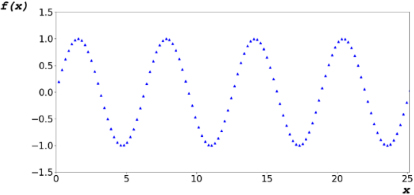
The algorithm determines the dependent variable of the codomain by adding variable
The periodic function contains irrational numbers as the period exhibits one-to-one correspondence [34]. The values of the dependent variable corresponding to independent variable.
The developed algorithm was applied on the obtained image data to verify the encryption capability because the developed system should be used for CT scanners. The image data of the phantom in the axial direction were obtained using a CT scanner (Aquilion ONE
(a) Image of random bit based on time stamp and (b) from proposed algorithms. (c) Randomized image obtained using time stamp noise and (d) proposed algorithm.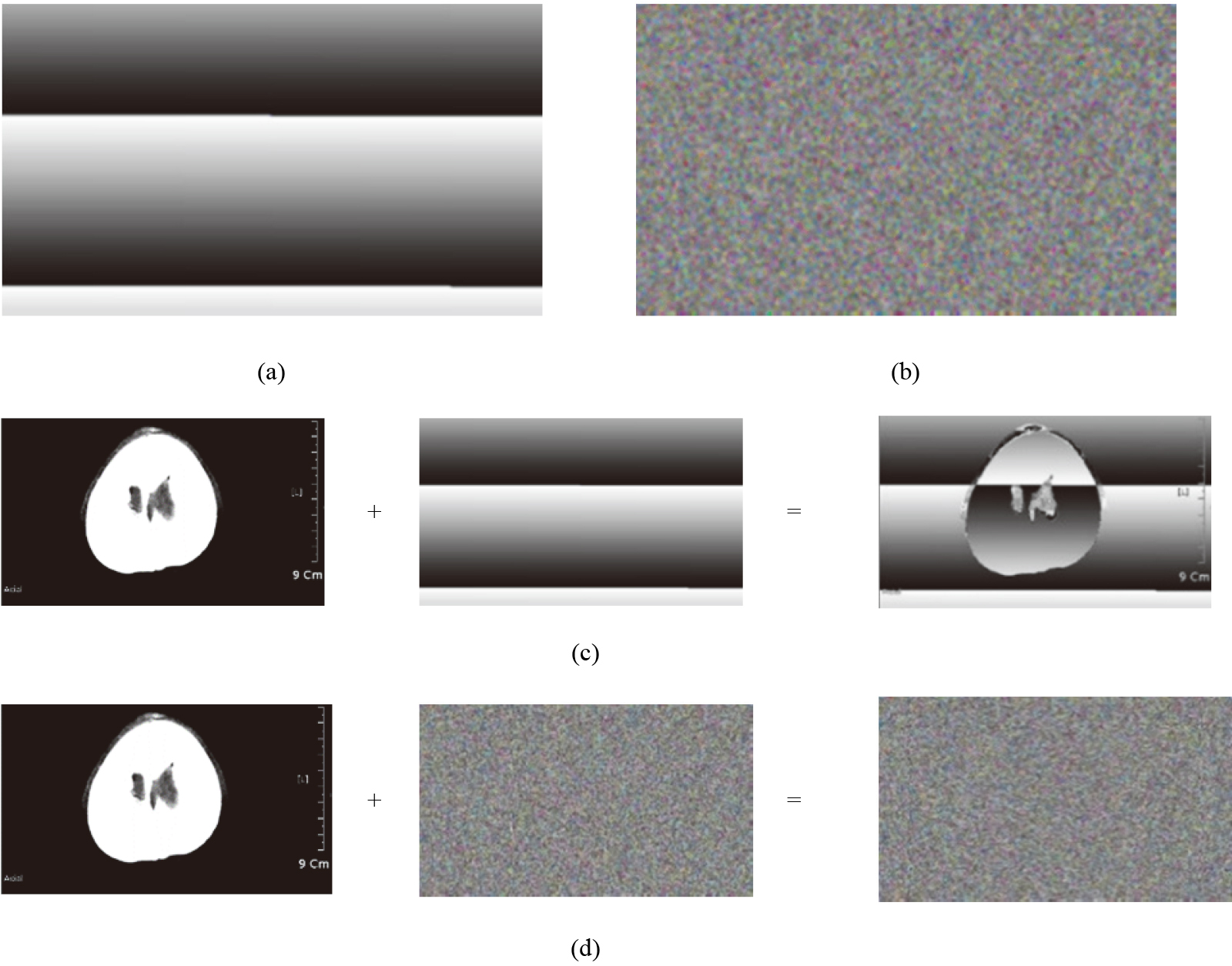
Figure 3a shows an image obtained using the noise of a time-based system. Figure 3b shows an image captured using a random bit generated using the proposed algorithm. As confirmed from the image, the noise generated based on the time stamp exhibits a regular pattern. However, the proposed algorithm exhibits characteristics.
When generating a random bit whose size is equal to that of the entire image, the proposed algorithm can confirm that the generated numbers are independent of each other’s independent previous events and they are generated as unpredictable numbers. To verify the performance of the proposed algorithm, we conducted an experiment.
Figure 3c and d show the mixed result with the original image after imaging the random bit generated using the time stamp and proposed algorithm, as shown in Fig. 3a and b, respectively.
The most famous one is RSA-based encrypted algorithms [35, 36]. However, these previous RSA-based encrypted algorithms such as 2048-bit RSA and prime-number-based RSA algorithms could be hacked because they have limited numbers of the encrypted keys produced by computer hardware [37].
Compared to previous studies, we use the proposed algorithms. This proposed technique has the functional relationship such that the developed encryption algorithm could be first applied to commercial CT scanners [38]. Therefore, the proposed algorithm could produce the randomized images in the digital system because it could not be produced by the hardware.
A random bit algorithm using mathematical modeling was proposed to randomize CT scanner image containing personal information, and randomization using actual CT scanner images was confirmed. The current random bit generation method uses noise provided by a hardware-dependent system.
The disadvantage is that the frequency of noise generation can be predicted. However, the proposed algorithm combines the mathematical periodic function. We observed that when the combinations of periodic functions and initial values for generating random bits and the amount of change were determined, random bits can be generated via the proposed algorithms.
Footnotes
Acknowledgments
This work was supported by the ‘Customized technology partner’ project funded by the Korean Ministry of SMEs and Startups in 2022 (project no. 202201580001).
