Abstract
An exponential growth of users demands ubiquitous connectivity, which requires the integration of new technology. Therefore, Device to Device (D2D) communication has been considered a promising technology that utilizes effective and efficient communication. Even though numerous studies have been conducted for establishing secure D2D communication, however, existing techniques face challenges like privacy, security threats, and poor generality. To overcome these issues a novel Deep-MAD model is proposed to preserve data privacy along with its access control in the D2D network and multiple attack detection in a fog environment. A Fully Homomorphic Elliptic Curve Cryptography (FHECC) is introduced to transmit data securely in a D2D network. The data owner uses FHECC algorithm to encrypt the plain text into cipher text before storing it on the fog. Whenever the user requests data from the fog, the fog service provider confirm the user’s access control. Furthermore, the deep learning-based Bi-LSTM is used to differentiate the device as an authorized or unauthorized user. If the IP address is genuine then the inverse FHECC is used to decrypt the data for authorized users. Otherwise, the particular device is blocked and it is sent for further verification for classifying the types of attacks. The effectiveness of the proposed strategy is examined using several parameters, such as computational complexity, scalability, accuracy, and Execution time. The proposed technique improves the overall computational overhead of 31.77, 9.34, and 4.67 better than AKA protocol, lightweight cipher, and FHEEP respectively.
Introduction
With the explosive growth of Internet-connected devices, user demands for broadband are undergoing an unprecedented rise [1]. According to Cisco, the global mobile data traffic had increased sevenfold between 2016 and 2021, reaching 49 exabytes per month by 2021. To resolve this issue, traditional solutions have been proposed, including the use of small cell sizes and pico- and femtocells, but their high deployment costs have prevented their widespread deployment. A device-to-device communication method boosts network speed and functionality by moving data between devices [2]. To meet this ever-increasing demand D2D communication has been suggested as a way to improve network performance and user experience [3]. In a recent report, D2D communications have been considered a promising technique since Release 9 of the Long-Term Evolution Advanced (LTE-Advanced) standard by the Third-Generation Partnership Project (3GPP) [4].
D2D communication protocols enable devices to communicate directly with one another without the use of an access point or base station [5]. In LTE-Direct, devices capable of D2D communication communicate with each other using a secure transmission protocol [6]. D2D communication allows devices to communicate directly with each other, which helps to sort out issues like congestion, interference, scarce spectrum, and coverage issues [7]. Moreover, it is capable of supporting local data communication services via unicast, group cast, and broadcast communication [8]. Figure 1 illustrates the D2D application.
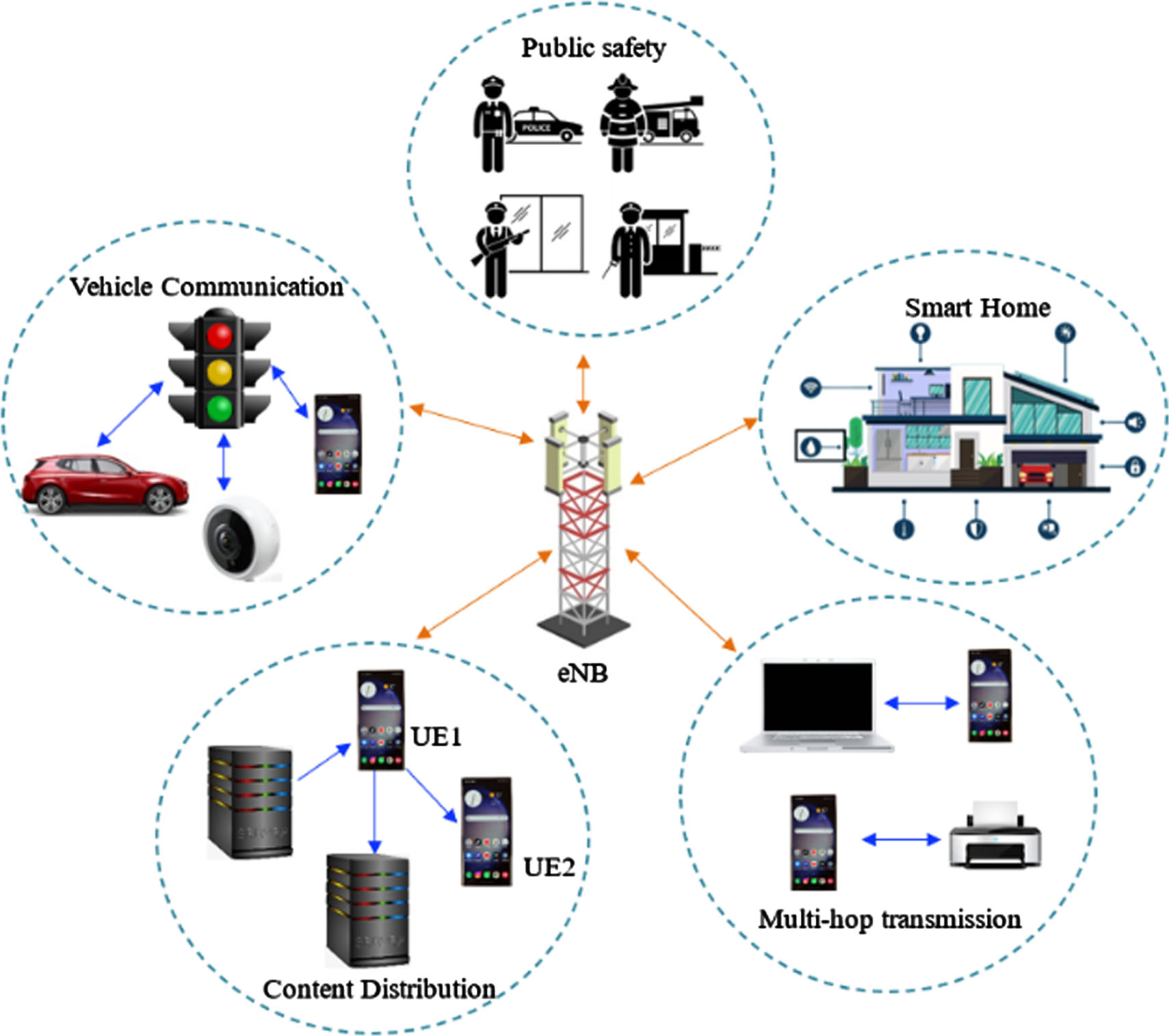
D2D applications.
Figure 1 illustrates some samples of D2D applications. Sometimes it can act as the base station and may help transmit data between two devices. It will be more helpful in multimedia data transitions because, due to the high fast transmission between two devices with higher bandwidth, low latency, better efficiency, and high spectral efficiency [9]. To enable D2D communication, short-range technologies are utilized such as Long-Term Evolution (LTE) Wi-Fi, and Bluetooth [10].
Despite this, traditional D2D communication technology is vulnerable to several attacks, leading to critical security challenges [11]. As a result of the lack of trusted infrastructure, it is the users’ responsibility to protect their sensitive data from a variety of attacks and to ensure their communication is secure [12]. Multiple cyberattacks, including Man in the Middle (MITM), Zeroday, Phishing, Distributed Denial of Service (DDoS), and XXS attacks, can cause rapid battery drain and make D2D devices more vulnerable to hardware failures which will affect the mobile network performance and operations [13]. Therefore, it is important to tackle the security challenges involved in D2D communication.
Sensitive data during transmission should be protected from unauthorized access to improve its security. Therefore, a wide variety of key generation, encryption, and decryption mechanisms are developed to ensure cloud authentication. However, it still faces issues like increased computational complexity, time consumption, and security vulnerabilities.
D2D communication is a peer-to-peer form of communication that eliminates the need for intermediate nodes. There are many advantages to D2D communication, such as: (i) extending the coverage of each cell in a cellular network, and (ii) transmitting multiple data over the same radio frequency. These advantages have led to the inclusion of D2D communication in the 5G network, such as the LTE-advanced network (4G). However, D2D communication through mobile phone networks involves considerable security problems.D2D communication involves device discovery, link setup, and data transmission. There is no authentication process for confirming the device’s identity in this process.
Furthermore, existing technologies for D2D communication do not use encryption to ensure confidentiality and message authentication to ensure integrity in the communication process. Also, the existing method does not detect and classify the types of attacks during transmission. To overcome these issues this paper proposed a novel Deep-MAD model to preserve data privacy along with its access control in the D2D network and multiple attack detection in a fog environment.
The following are the key contributions of this work. The primary purpose of this work is to present a novel Deep-MAD model to preserve data privacy along with its access control in the D2D network and multiple attack detection in a fog environment. A Fully Homomorphic Elliptic Curve Cryptography (FHECC) is introduced to transmit data securely in a D2D network. The deep learning-based Bi-LSTM is used to differentiate the device as an authorized or unauthorized user and detect the types of attack. The performance evaluation of the proposed Deep-MAD model is done against the existing algorithms to claim its superiority based on computational complexity, scalability accuracy, and Execution time.
The remainder of the research paper was structured as follows: the related works are summarized in Section 2. Section 3 discusses the proposed methodology. Section 4 includes the result and discussion of the proposed model. Section 5 holds the conclusion and future work.
D2D communications have many benefits, but security is the primary issue that is essential to address before the technology becomes widely used and accepted. In D2D communications, an increasing number of studies have concentrated on authentication and key management techniques. This section presents a summary of some of the most recentstudies.
In 2023 Rani, S.J., et al., [14] developed an ML-based DDoS attacks detection and prevention in D2D communication. To validate the test CICDDoS2019 and D2D Network-specific Slowloris datasets are utilized. The ML techniques such as Light GBM, Ada Boost, XGBoost, and Random Forest, are used for attack detection. The Random Forest achieves better accuracy, where the D2D device’s resources are mostly linked to the object’s lifespan andcapabilities.
In 2023 Tayade, P. and Vijaya Kumar, P., [15] developed a D2D-based secure authentication protocol. In the authentication stage, public and private secret keys are generated using the ECC and Elliptic Curve Diffie-Hellman (ECDH) algorithm. For the creation of associated keys, a hash-based message authentication code (HMAC) is utilized. A quantum channel is used to ensure the security of this transmission.
In 2022 Nyangaresi, V.O et al., [16] presented a session authentication and secure key agreement mechanism for IoT devices. The suggested model utilized a lightweight asymmetric Elliptic curve cryptography (ECC). This model provides lower computation, high stability, turnaround time, and moderate communication costs Yet this technique does not implement in a real IoT communication environment.
In 2022 Hajian, R., et al., [17] presented an Authentication and Key Agreement in secure anonymous D2D for IoT. In the registration step, a D2D mutual AKA protocol was created that did not require a secure channel to generate paired private and public keys. The suggested protocol utilizes the Scyther tool and BAN logic to accomplish strict formal security verification. This model provides better performances for communication, computation costs, and energy consumption.
In 2022 Kishore et al., [18] presented an ECC-based security mechanism for D2D communications in 5G networks. The mobile phone’s hardware, the SIM card provided by the mobile operator, and the SIM storage, which is used to store signature data or private keys. This method offers an accurate representation of secure D2D communication on 5G networks.
In 2022 Khoshafa, M.H., et al., [19] developed a Relay selection for physical layer security in D2D underlay communications. To secure the D2D transmission, both optimum and poor relay selections are used. The eavesdropper amplifies the wiretapped signals using either maximal-ratio combining or selective combining. The system parameter on the SOP is better understood due to the asymptotic results.
In 2021 Suraci, C. et al., [20] presented a secured and Trusted D2D communications to assist a trusted multicast service delivery in 5G-oriented networks through an improved Conventional Multicast Scheme. The best relay node is selected based on the selection of trustworthy and effective D2D transmitters. Furthermore, the Diffie-Hellman Key Exchange (DHKE) algorithm is used to secure data delivered via D2D interactions. The suggested strategy efficiently chooses relay nodes, improving network performance.
In 2021 Pothumarti, R., et al., [21] developed a lightweight cipher technique that improves the security, access control, and authentication that is implemented on a multi-layer communication to resolve heterogeneity and scalability problems. The suggested framework also included a dynamic key generation mechanism that uses a set of distinct keys and entropy. This method lowers the cost of computation and communication without compromising security. Yet this model requires a high-speed and reliable environment.
In 2021 Noura, H.N., et al., [22] developed a D2D MIMO technique for PLS cipher solution which is based on the dynamic key structure and includes various parameters such as a private key and a physical channel. Input frames are updated with cipher primitives, and frame symbols are updated with selection cipher primitives. The updating procedure aims to increase security and guarantee the avalanche effect. The suggested model attains high efficiency and high immunity.
In 2021 Gaba, G.S., et al., [23] developed an efficient mutual authentication and key exchange scheme for WiFi Direct. A commit/open pair and the Diffie Hellman key exchange method form the foundation of the suggested approach. The suggested protocol prevents DoS and MITM attacks from happening during the important agreement and discovery phases. This model may provide a comprehensive security package and is readily integrated into WiFi Direct-enabled devices.
In 2020 Zheng, W et al., [24] developed a task allocation and node classification based on a Cooperative-routing approach for social networks. It allows the message carrier to find the next hop by rationally utilizing the idle resources of other nodes in its online community to find the next hop. This model enhances the network communication, yet does not provide secure information transmission.
In 2020 Li, Z., et al., [25] presented a social network routing technique based on triangular fuzzy layers and multi-layer clustering. The best message transmission node is chosen using the fuzzy analytic hierarchy process model, which analyses social similarity and trajectory similarity. The trajectory of each node is calculated using the multi-level clustering model based on time. Yet this model computes more power and cache space.
In 2019 Abro, A., et al., [26] presented a lightweight elliptic-ElGamal-based authentication technique employing PKI in D2D communication for lowering M-I-T-M and decreasing communication expenses. Herein The secret key is exchanged via Elgamal once the key pair is chosen using ECC. To assess the veracity and secrecy of the suggested model, Pollard’s rho and Baby Step, Giant Step (BSGS) techniques are utilized. The suggested model performs better while improving security.
Differences between the proposed and existing techniques
The important findings from their research as well as the differences between the existing and proposed technique are given below. Unlike the proposed Deep-MAD model many of the algorithms did not consider confidentiality and message authentication for integrity during communication The proposed method not only uses security while transmission but also detects and classifies the types of attacks. Computational complexity is another aspect that makes existing techniques unsuitable for various real-time applications. However, the proposed model was found to be computationally efficient.
From the above literature survey, various encryption-based security techniques are used in D2D communication. There have been many previous studies showing the benefits of D2D for security protection, but few have explored how this protection can be maximized by selecting and controlling the access of the D2D pairs. Due to the lack of secure and privacy-preserving solutions, D2D group communication could be used for a limited number of applications. The overall literature survey highlights several promising avenues for future research on D2D communication in 5G networks.
Proposed Deep-MAD model
In this work, a novel Deep-MAD model to preserve data privacy along with its access control in the D2D network and multiple attack detection in a fog environment. Initially, a security protocol based on Fully Homomorphic Elliptic Curve Cryptography (FHECC) is introduced to transmit data securely in a D2D network.
The data owner uses FHECC algorithm to encrypt the plain text into cipher text before storing it on the fog. Whenever the user requests data from the fog, the fog service provider confirm the user’s access control. When a user requests data from the fog, the fog service provider confirms the user’s access control policy to enable the data’s restricted access. Furthermore, the deep learning-based Bi-LSTM is used to differentiate the device as authorized or hacker. If the IP address is genuine then the inverse FHECC is used to decrypt the decrypted data and provide it to the authorized users. Otherwise, the particular device is blocked and it is sent for further verification for classifying the types of attacks. The overfall workflow is shown in Fig. 2
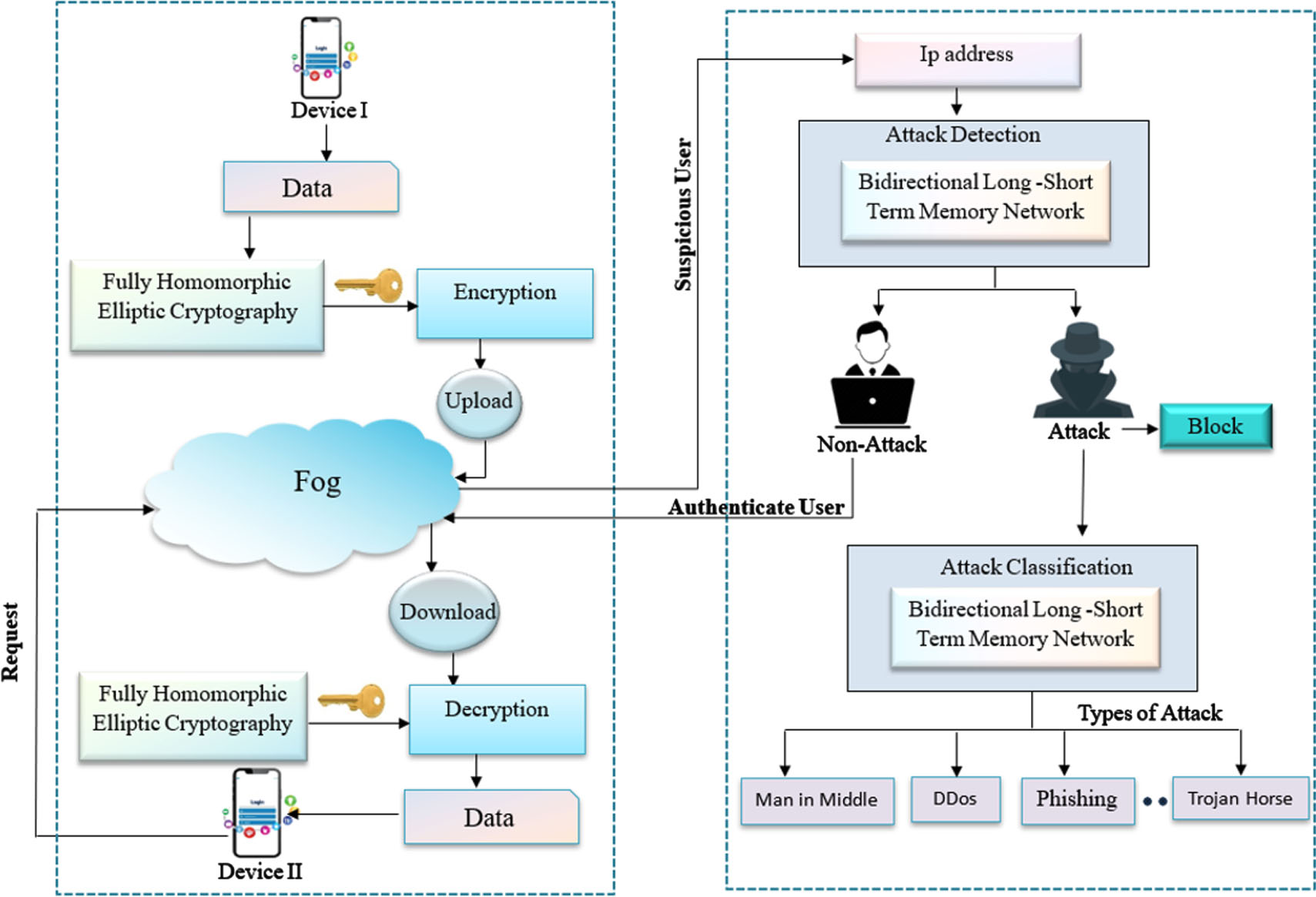
The schematic representation of the proposed Deep MAD model.
In this research, fog nodes act as relay nodes to facilitate communications between devices, particularly if the devices are not in direct radio range of one another. The fog nodes are typically located between and closer to the devices, and they have the advantage of processing and forwarding data with low latency. In this scenario, a fog node positioned strategically could act as a relay, transferring data from one device to another despite obstacles, interference, or signal attenuation, and improving the quality of communication. A fog node can also provide data caching, security, and computation offloading, making it a versatile D2D communication component. The ability of these devices to act as relays enhances network performance and allows seamless communication among devices without compromising networksecurity.
In a D2D network, devices frequently need to find network resources throughout the entire network, and these resources normally contain sensitive information. Direct transmission of the necessary data to the requesting device increases the risk of privacy disclosure and creates an unsecured D2D network. Firstly, private data must be encrypted in the D2D network before it can be sent to the device that requested it. FH-ECC is added to the D2D network to meet the aforementioned requirements.
The FH-ECC is used to transmit data securely between nodes. For encryption in a fully homomorphic model, single symmetric keys are commonly used. The proposed approach makes use of an asymmetric Fully Homomorphic algorithm, in which the ECC varies proportionally to the Fully Homomorphic functions. The key size of the proposed model is 512 bits. The proposed FH-ECC flowchart is illustrated in Fig. 3.
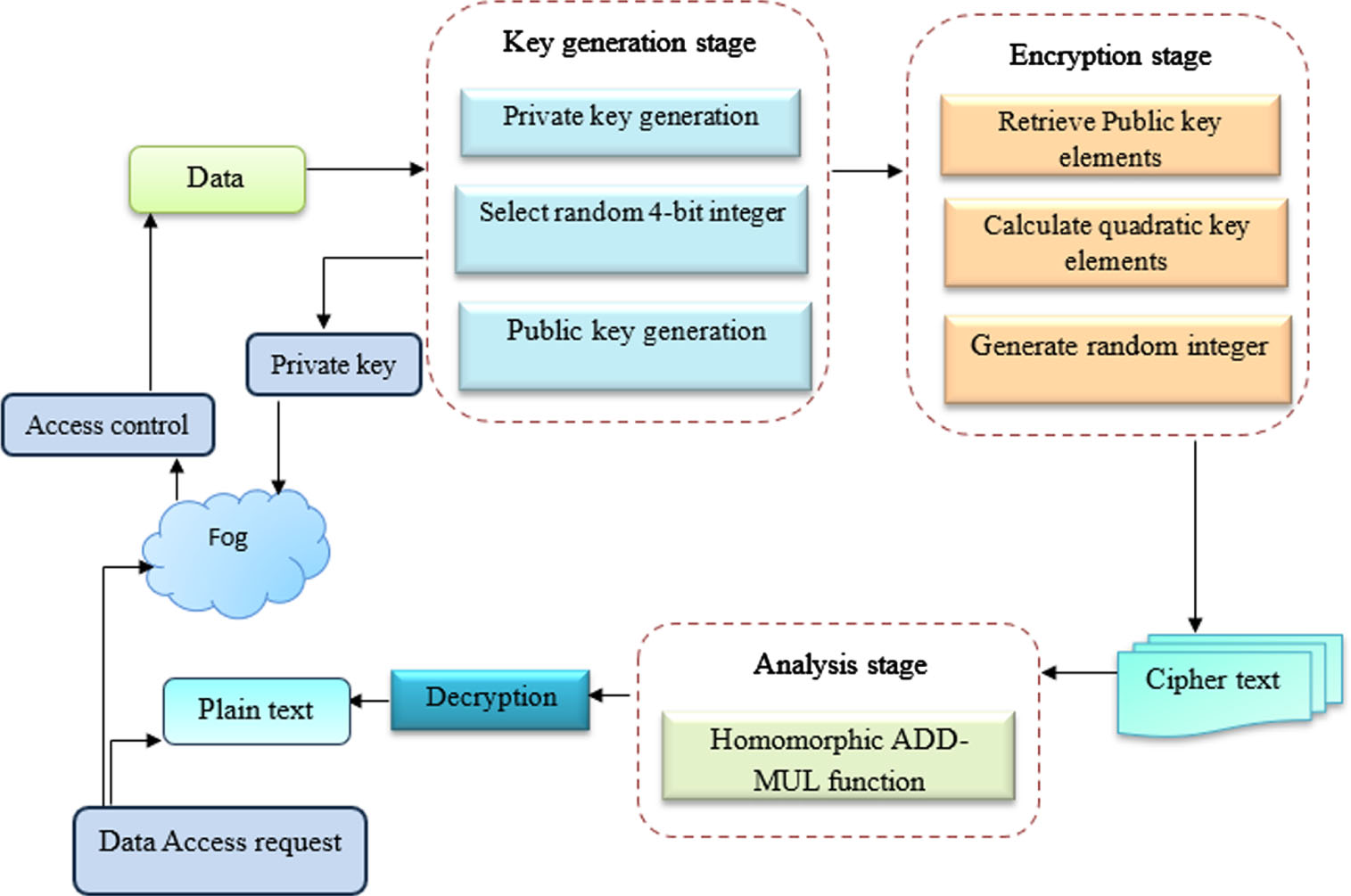
Architecture of the proposed FH-ECC.
Data requests are initially made by the user to fog, and then access policies are verified by the service provider to restrict data access. The public and private key pairs are created using random bits once access to the system has been restricted. The data is then encrypted using the key to create ciphertext, which is converted to ciphertext by applying the ECC algorithm. The cipher data is then processed by FH operations before being stored in the Fog. Decryption is performed after the encrypted data has been forwarded to the requested user.
Encryption is a technique for encrypting plain text to offer a higher level of security. Security issues are classified based on their complexity using the ECC. This method has the advantage of only requiring an alphabetical table and key. Additionally, it enhances the data solution and permits secure key transmission for communications between the source and destination nodes.
A FH operation can be used to perform computations on both encrypted data and random data. To boost the security of data transmission, FH-ECC increases data packet security while lowering packet loss. This method’s improved security and quicker processing are its two main benefits.
A private key pr k and input data (I d ) is given as an input, then a generator function is used to generate the public key pu k . Consequently, a random bit is used to generate a cipher, and the input data (I d ) is encrypted using a random number, which is created according to a point of the curve. A homomorphic operation is then applied to the set of encrypted data using its multiplicative property. Finally, the encrypted data is uploaded on Fog.
Decryption
The original data can be retrieved from the data when it reaches the receiver after it is decrypted. Herein, FH is used to separate the cipher data from the encrypted data, followed by ECC decryption to recover the plain text. The encrypted data E d and the private key pr k are the inputs for the ECC decryption method. Using the private key, this technique decodes the cipher text from encrypted text. The generator function gn f random number df n is then fetched using pr k . A homomorphic method creates the original text from the decrypted data after the point-on-curve method has been used to decrypt the data. The delivery ratio increases and packet drops are reduced as a result.
Classification and detection of multiple attacks using Bi-LSTM
In this section, the deep learning-based Bi-LSTM is used to differentiate the device as an attack or non-attack. If the IP address is genuine then the inverse FHECC is used to decrypt the decrypted data and provide it to the authorized users. Otherwise, the particular device is blocked and it is sent for further verification for classifying the types of attacks based on Bi-LSTM. The LSTM model can be used as a building block for large-scale neural networks. In contrast to RNN, LSTM avoids gradient problems by efficiently using memory. Yet, a bi-directional LSTM accepts input in both directions, either forward or backward which makes it different from a consistent LSTM. LSTM models can only be determined by using inputs that have already been processed, as information propagates forward. Meanwhile, Bi-LSTM is capable of handling contextual data efficiently since it considers both past and future data.
The LSTM classifier is composed of the memory cell, output gate, input gate, and forget gate as illustrated in Fig. 4.
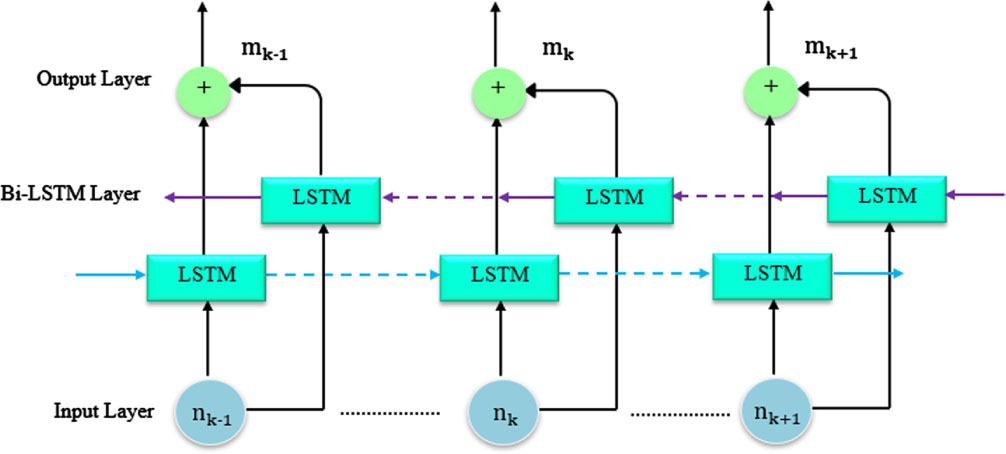
Bi LSTM architecture.
The input data is either temporarily or permanently retained in the memory cell. While the Forget Gate maintains data holding in the LSTM cell, the Input Gate controls data volume. The output activation for the gate can be evaluated and prepared by managing the data in the LSTM layer cell. Equations can be used to determine how input, hidden states, and various gates relate to one another.
Where, o
n
, f
n
, i
n
, and T
n
denotes the output gate, forget gate, input gate, and the cell at time t;
The second LSTM receives the first LSTM’s output series as input, and the final units of the forward and backward layers are concatenated with the second LSTM’s output series as shown below:
A major goal of the global max pooling layer is to obtain as many features from the temporal data as possible. The final feature maps are frequently transformed into one-dimensional arrays using the flatten layer. Full-connected layers receive the input from the one-dimensional array. All neurons between layers in a feed-forward neural network are connected via the FC layer. The output layer calculates the likelihood of identifying and classifying multiple attacks by adding the bias vectors, weight matrices are multiplied by the inputs, and multiplying the result by the inputs
In this section, the results of the proposed Deep MAD model are discussed. The implementation was carried out with the Network Simulator (NS2), which had a 4-GB RAM and an Intel Core processor. This section also describes the results of the proposed and existing model and their performance under several efficiency measures, such as security mechanisms and network analysis. Table 1 provides the default simulation parameters. In the simulation 500 nodes are placed in 300 m×300 m. Nodes move randomly in the network at different speeds.
Simulation parameters
Simulation parameters
Figure 5(a) illustrates the unreliable D2D connection as the UEs (e.g., UEx, UEy) are separated by quite a distance and are not within each other’s communication range. Figure 5(b) depicts the reliable d2d connection that meets the aforesaid requirements, the UEs connect jointly via device discovery and link setup. Figure 5(c) shows the attack in a d2d connection. The red symbol denotes the attack in the d2d connection.
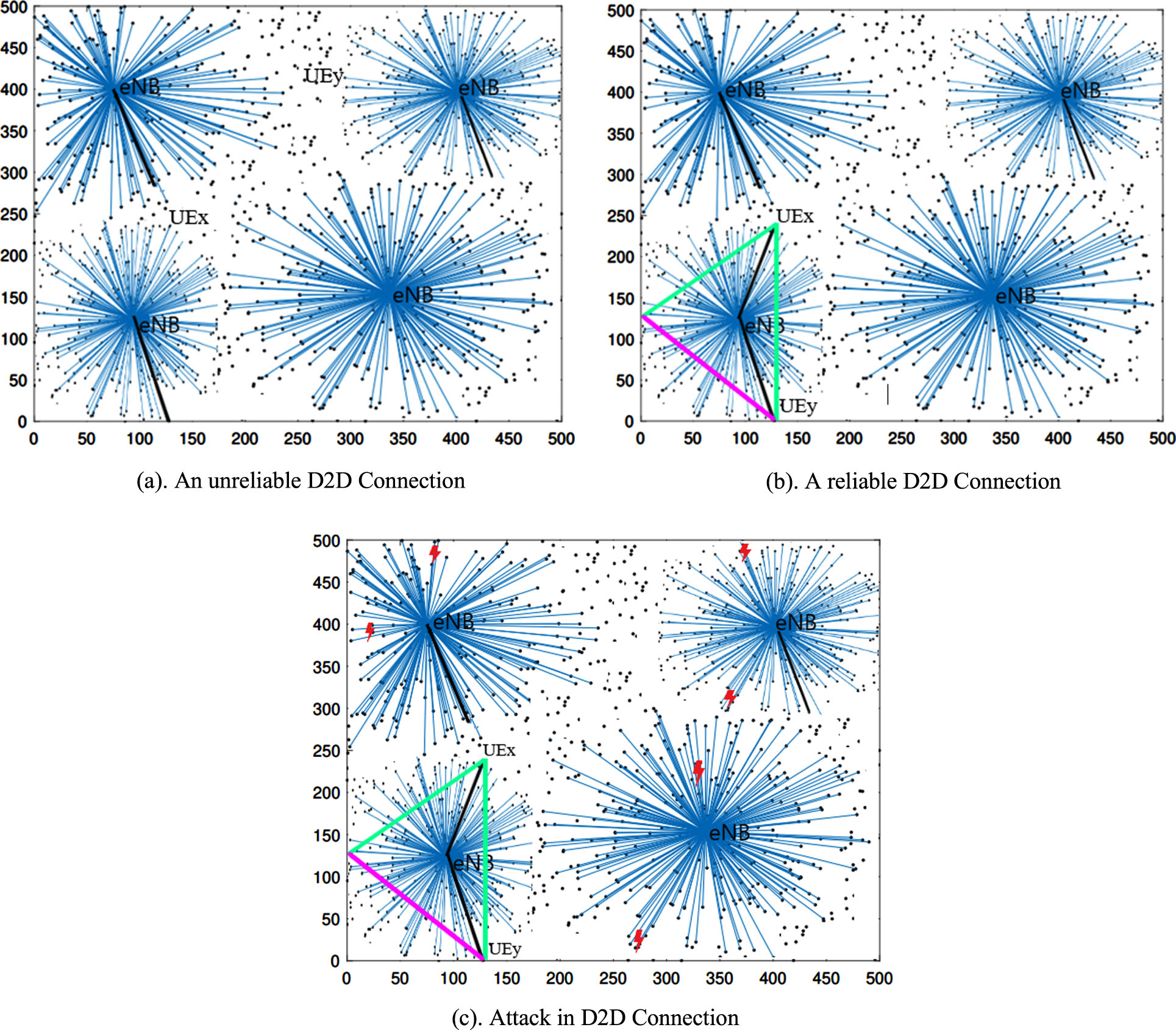
(a) An unreliable D2D Connection. (b) A reliable D2D Connection. (c) Attack in D2D Connection.
Exe time can be defined as the time required to compute data storage access. It also defines how long the system takes to store the encrypted data and access it from a server.
Figure 6 shows the execution time of the existing ECC [18], MIMO [22], FHEEP [26], and proposed technique based on varying points. As shown in the analysis, the proposed model effectively reduces the overall execution time in seconds when compared to the existing method.
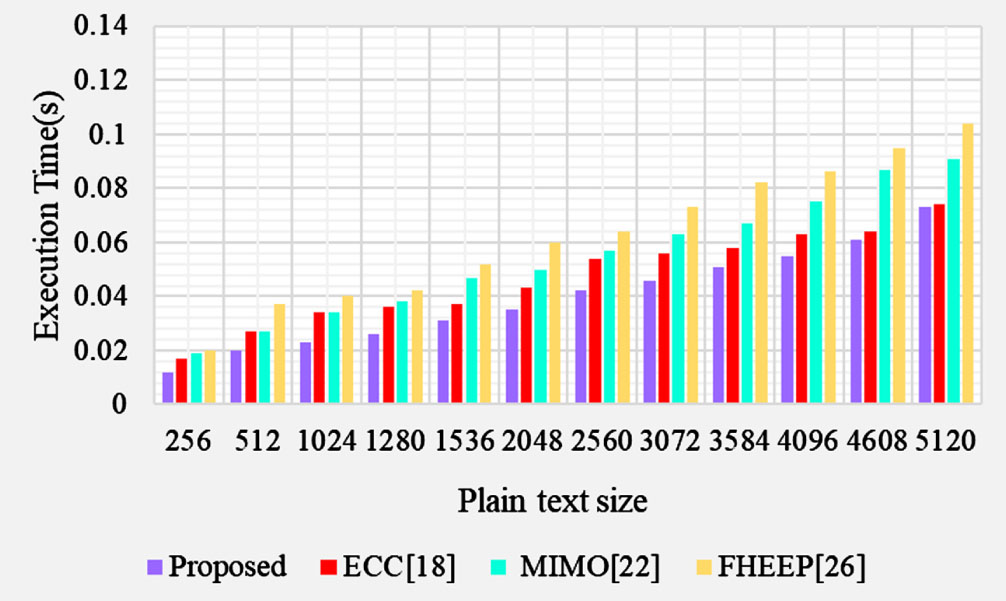
Performance of Execution time.
E
time
is the measure of time required to encrypt the given data, which is represented in milliseconds, and computed as shown in Equation (7)
Figure 7 shows the encryption time of the proposed and existing mechanisms. This technique analyzes how encryption time can increase with a linear increase in key size (bits). The proposed method requires less encryption time compared to other methods, as determined by the analysis.
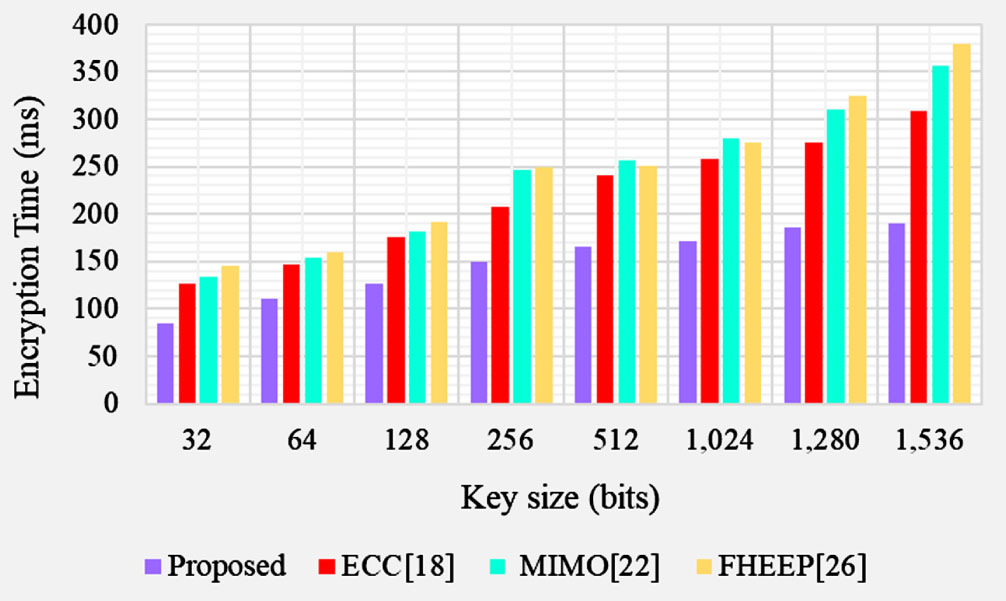
Performance of Encryption time.
D time is the measure of time required to decrypt the encrypted data that is represented in milliseconds, and computed as shown in Equation (8)
Figure 8 illustrates the decryption time of the proposed and existing technique concerning varying key sizes (bits). Thus, the decryption time can increase linearly with the key size.
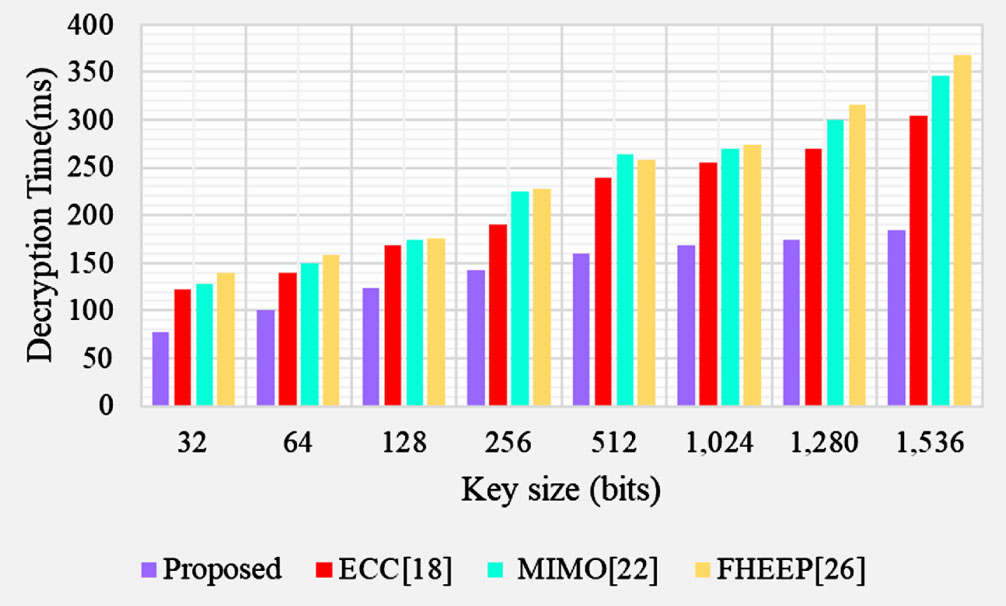
Performance of decryption time.
Efficiency evaluation
The efficiency of the proposed protocol can be measured using performance metrics such as false alarm rate, accuracy, F1 score, recall or detection rate, and precision,
Table 2 illustrates the detection of attacks with specific parameters. This model detects attackers and non-attackers, which helps the system while preserving security. The average accuracy, detection rate/recall, precision, and F1 score of the proposed technique are 98.15%, 98.25, 97.55, and 97% respectively.
Efficiency metrics of the detection of attacks
Table 3 illustrates some sample classifications of attack with specific parameters. The average accuracy, precision, detection rate/recall, and F1 score of the proposed model are 98.15%, 96.56, 97.48, and 96.58%.
Performance metrics of the classification of attacks
The accuracy curve is presented in Fig. 9 as the range of accuracy is shown in the vertical axis and the number of epochs is shown in the horizontal axis. When epochs are increased, accuracy improves. The epoch and loss range in Fig. 6 indicates that when the epochs are raised, the loss of the proposed model is reduced. So, the detected accuracy of 98. 15% of the proposed models are highly reliable for the detection and classification of attacks.
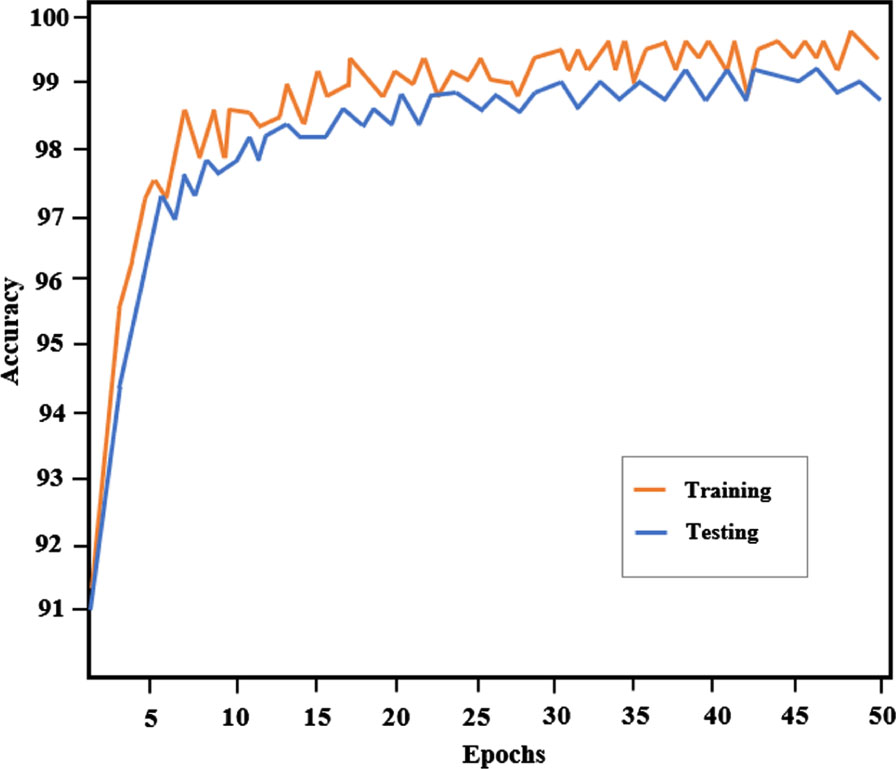
Performance curve of the proposed model.
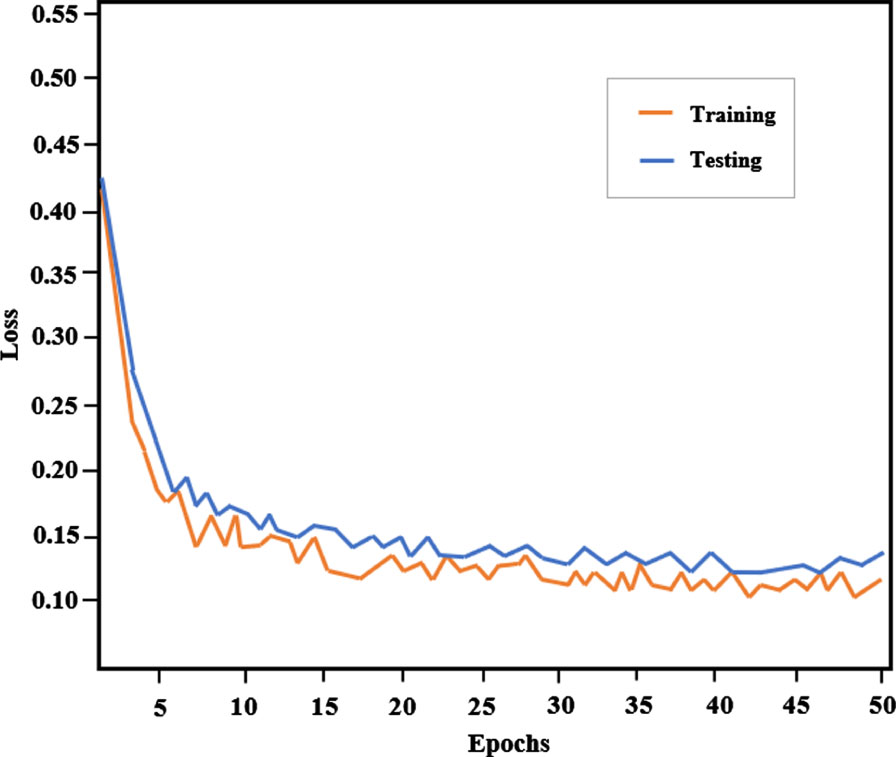
Loss curve of the proposed model.
The proposed deep neural network model is compared with existing deep learning methods namely ANN, RNN, and LSTM based on some samples of different types of attacks such as DDOS, Man in Middle, Zeroday attack, Phishing attack, and XXS attack. The proposed deep learning approach achieves the highest recognition accuracy compared to the standard deep learning algorithms.
Table 4 display the comparison result of the proposed model to other traditional deep learning techniques based on Man in the Middle, DDOS, Phishing attacks, Zeroday attacks, and XXS attacks. It is clear from the tables that the proposed technique attains better accuracy than the other traditional deep learning models.
Comparison analysis of traditional models based on different types of attacks
Comparison analysis of traditional models based on different types of attacks
The effectiveness of the proposed model was compared to the classic DL models based on the classification results shown in Fig. 11, in which the proposed model achieves a better accuracy rate of 98.15%. It is evident from the findings that the proposed technique produces higher accuracy on both training and testing datasets while having a reduced false alarm rate.
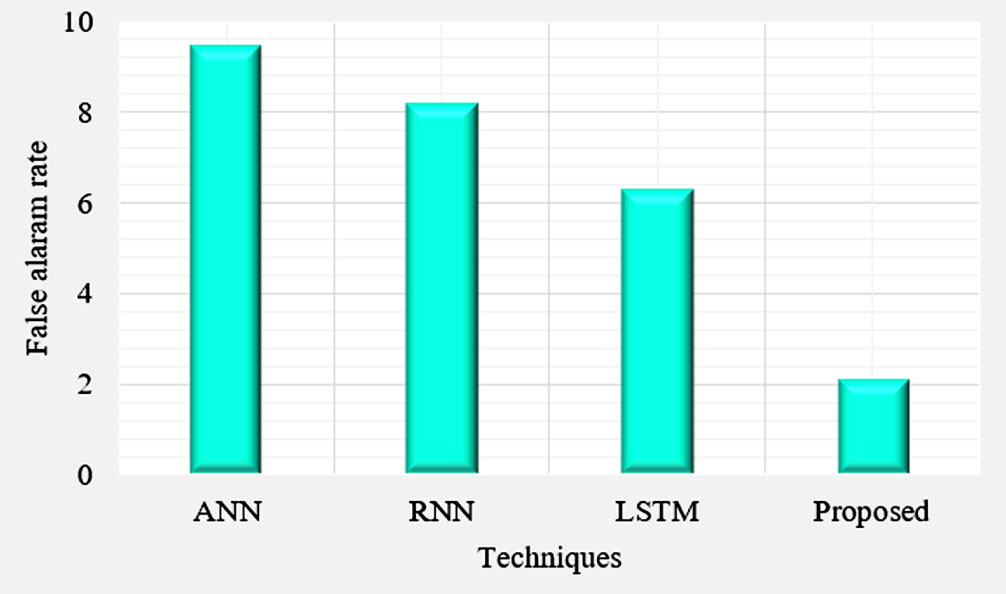
FAR comparison of proposed with traditional techniques.
Figure 12 shows the Computational overhead comparison with existing and proposed techniques. The proposed Deep MAD technique attains a lower computational overhead than the existing techniques. The proposed technique improves the overall computational overhead of 31.77, 9.34, and 4.67 better than AKA protocol, lightweight cipher, and FHEEP respectively.
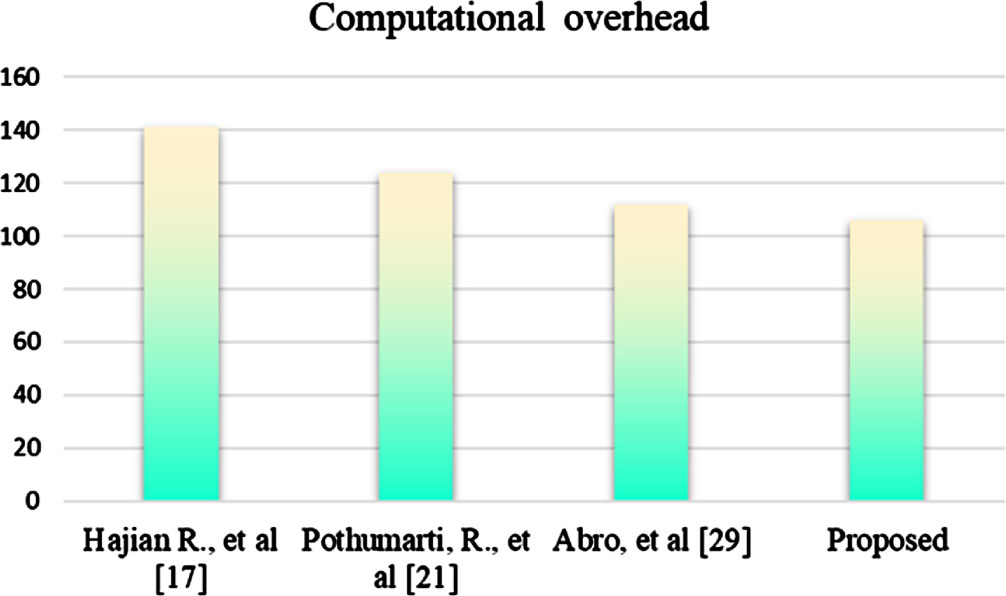
Computational overhead comparison with existing and proposed techniques.
The time complexity of the proposed Deep-MAD model is o (n3). The values are transformed into global values if there are more than three or four relay nodes. Herein n represents the number of devices. This process is o (n) in terms of complexity and o (nlogn) in terms of overall communication expense.
Conclusion
In this work, a novel Deep-MAD model to preserve data privacy along with its access control in the D2D network and multiple attack detection in a fog environment. A Fully Homomorphic Elliptic Curve Cryptography (FHECC) is introduced to transmit data securely in a D2D network. The data owner uses FHECC algorithm to encrypt the plain text into cipher text before storing it on the fog. Whenever the user requests data from the fog, the fog service provider confirm the user’s access control. Furthermore, the deep learning-based Bi-LSTM is used to differentiate the device as an authorized or unauthorized user. If the IP address is genuine then the inverse FHECC is used to decrypt the data for authorized users. Otherwise, the particular device is blocked and it is sent for further verification for classifying the types of attacks. The limitation of the proposed Deep-MAD model does not handle the multi-owner nature. This limitation will be considered as a future work for extending our proposed system.
