Abstract
The expeditious advancement and widespread implementation of intelligent urban infrastructure have yielded manifold advantages, albeit concurrently engendering novel security predicaments. Examining current patterns in the security of smart cities is paramount in comprehending nascent risks and formulating efficacious preventative measures. The present study suggests the utilization of Latent Semantic Analysis (LSA) as a means to scrutinize and reveal implicit semantic associations within a collection of textual materials pertaining to the security of smart cities. Through the process of gathering and pre-processing pertinent textual data, constructing a matrix that represents the frequency of terms within documents, and utilizing techniques that reduce the number of dimensions, Latent Semantic Analysis (LSA) has the ability to uncover concealed patterns and associations among concepts related to security. This study proposes five recommendations for future research that employ a topic modeling technique to investigate the often-explored subjects related to smart city security. This discovery provides additional evidence in favor of the proposition that a robust blockchain-driven framework is vital for the advancement of smart cities. Latent Semantic Analysis (LSA) offers important insights into the dynamic landscape of smart city security by employing several techniques such as pattern recognition, document or phrase clustering, and result visualization. Through the examination of patterns and developments, individuals in positions of political authority, urban planning, and security knowledge possess the ability to uphold their proficiency, render judicious choices substantiated by empirical data, and establish proactive strategies aimed at preserving the security, privacy, and sustainability of intelligent urban environments.
Keywords
Introduction
The safeguarding of smart cities is of paramount importance in guaranteeing the security, confidentiality, and durability of metropolitan settings that are progressively linked and reliant on digital innovations [1]. The security of smart cities is contingent upon several critical factors, such as conducting a thorough risk assessment, implementing strong cybersecurity measures, establishing policies for data privacy and governance, monitoring and segmenting networks, fostering partnerships and collaboration, developing resilience and disaster management strategies, educating users on security best practices, securing IoT devices, establishing effective incident response and management protocols, and conducting routine audits and compliance checks [2]. Through the implementation of a comprehensive security strategy, smart cities have the potential to effectively manage potential threats, safeguard critical infrastructure and inhabitants, and establish a dependable and robust urban ecosystem. The attainment of these objectives necessitates regular assessment, modification, and cooperation among all parties involved. Contemporary developments in the realm of smart city security encompass a range of areas, such as cybersecurity, privacy preservation, artificial intelligence and machine learning technologies, blockchain technology, physical security measures, resilience, and disaster management, and collaborations between public and private entities [3]. The issue of cybersecurity is of paramount import protocols particular emphasis on safeguarding Internet of Things (IoT) devices, implementing strong authentication and encryption protocols, and adopting sophisticated threat detection and response mechanisms. This approach involves the detection of anomalies, identification of patterns, and prediction of potential security threats. The safeguarding of privacy encompasses various measures such as the anonymization of data, secure storage and transmission of data, and the implementation of transparent data governance frameworks. The utilization of artificial intelligence (AI) and machine learning (ML) techniques has been implemented to augment security measures through the analysis of voluminous datasets in real-time technology of blockchain provides a decentralized and tamper-proof means of storage, secure transactional processes, identity management, and peer-to-peer communication [4]. Physical security measures encompass a range of strategies, such as the utilization of surveillance cameras, sensor-based systems for crowd management and emergency response, and intelligent access control systems [4]. The topics of resilience and disaster management have garnered increasing attention in recent times. There is a concerted effort to devise resilient disaster management strategies that incorporate real-time monitoring, early warning systems, adaptive infrastructure, and communication networks [5]. The establishment of public-private partnerships is a crucial factor in effectively addressing security challenges in smart cities. This approach facilitates innovation and promotes the seamless integration of security measures within initiatives. The most important concern in smart cities is the privacy and security of healthcare data. Researchers have initiated many research projects in the direction of data privacy and security, one of the research presents a unique paradigm for the privacy of healthcare data which is called the Self-diagnosis Platform (SDP) to effectively mitigate security problems in the context of Internet of Things (IoT) in healthcare [6]. The approach employs EdDSA encryption to augment privacy and guarantee confidentiality in the interactions between patients and third parties. Securing the data using one time password can also add new dimension in the field of privacy and authentication of the data, a recent research developed a system that ensures the security using OTP [6].
Addressing the diverse cybersecurity challenges in smart city environments
Researchers and cybersecurity specialists are actively engaged in the exploration of techniques aimed at mitigating cybersecurity concerns in smart city environments. The aforementioned elements encompass various aspects of cybersecurity, such as risk assessments, secure-by-design principles, encryption, access control, network segmentation, intrusion detection and prevention systems, incident response plans, public awareness, privacy-preserving technologies, regulatory frameworks, collaboration, resilience planning, blockchain and distributed ledger technology, cybersecurity training and workforce development, cross-disciplinary research, ethical considerations, and international cooperation. Ensuring the security of smart cities necessitates the implementation of various crucial elements, including incident response plans, public awareness initiatives, privacy-preserving technologies, legislative frameworks, collaborative efforts, resilience planning, blockchain and distributed ledger technology, as well as cybersecurity training and workforce development.
Smart cities need data anonymization, secure data sharing, and analytics to protect personal data and enable data-driven decision-making. Data anonymization removes or replaces personally identifiable information (PII) to prevent identification. Secure data sharing involves government agencies, private corporations, and research organisations sharing data securely. Data encryption, masking, transfer protocols, access controls, and sharing agreements are essential to safe data sharing. Smart city analytics uses privacy-preserving data analysis, anomaly detection, and real-time data access and usage monitoring to protect personal data. These methods prioritize privacy-aware data analysis to protect individual anonymity. Smart cities can use data to improve services and decision-making while safeguarding inhabitants’ and stakeholders’ privacy and security.
Social and ethical implications in smart city implementation
Despite the positive effects that smart city technology has had on metropolitan areas; it has also raised a number of social and ethical concerns. Concerns about privacy arise because the collection of massive volumes of data can make it easier to spy on people and invade their personal space [7]. Implementing privacy safeguards and adopting appropriate cybersecurity measures are taken to address these worries. By expanding access to technology and introducing initiatives to improve digital literacy, the digital divide can be narrowed [8]. The goal of establishing data governance is to reduce the likelihood of misuse and breaches while ensuring that ethical standards are met in the deployment of AI and robotic process automation. Energy-efficient technologies and trash reduction strategies help lessen the negative effects on the environment [9]. Unrestricted access to data and information is provided to enhance community involvement while also upholding the ideals of transparency and accountability. Respect for local customs and norms is considered while adapting technology to meet the needs of the area. The social and ethical concerns that arise from implementing smart city technologies are actively sought out. The ultimate objective is to promote humane, sustainable, and equitable urban environments for the benefit of all residents. Meanwhile, smart cities work to lessen the blow of any unintended consequences.
The utilization of Latent Semantic Analysis (LSA) is prevalent in the fields of natural language processing and text analysis due to its various advantages and applications [10]. The process of reducing the dimensionality of text data enables more effective computing management. Latent Semantic Analysis (LSA) is a computational technique that aims to uncover the underlying semantic structure of textual data. By analyzing the correlations and similarities between words and documents, LSA provides insights into the hidden meaning and associations inside the text [11]. Topic modelling, information retrieval, document clustering, text summarization, sentiment analysis, recommendation systems, automatic tagging, cross-domain analysis, uncovering hidden patterns, and language independence are among the several applications in which it is frequently employed. The current research contributes to the following areas:
The utilization of Latent Semantic Analysis (LSA) facilitates the identification and extraction of pivotal issues or themes from an extensive collection of scholarly papers, reports, or documents. The identification of new trends and shifts in focus within the subject of smart city security can be facilitated by the analysis of the temporal evolution of topics using Latent Semantic Analysis (LSA). Cross-disciplinary insights can be obtained using Latent Semantic Analysis (LSA) to identify linkages between smart city security and other fields, including urban planning, information technology, and data science. In light of the dynamic nature of security threats in smart cities, the utilization of LSA enables the continuous monitoring and analysis of emerging risks and vulnerabilities. This capability facilitates the implementation of proactive security solutions.
The application of latent semantic analysis in academic research that is essential to modern breakthroughs in the safety of smart cities has the potential to deliver significant and valuable insights into the ever-changing and dynamic character of this subject.
Literature review
The application of Latent Semantic Analysis (LSA) has been extensively employed across diverse fields to reveal implicit semantic associations within textual information. The utilization of Latent Semantic Analysis (LSA) in the examination of security trends in smart cities can offer valuable perspectives on the dynamic smart city security environment, and bring to research has exhibited the efficacy of Latent Semantic Analysis (LSA) in evaluating security-related facets of intelligent urban environments. Scholars have amassed a varied corpus of written material, encompassing academic papers, official documents, journalistic pieces, and online content, particularly emphasizing themes such as information security, data protection, safeguarding of assets, and novel technological advancements [12]. Through the preprocessing of textual data, the construction of a document-term matrix, and the implementation of dimensionality reduction methods such as Singular Value Decomposition (SVD), Latent Semantic Analysis (LSA) is able to extract the underlying semantic relationships between various security concepts [13]. The utilization of Latent Semantic Analysis (LSA) in scrutinizing these associations has facilitated scholars in detecting patterns and variations across temporal dimensions. Through the examination of alterations in the resemblance of terms or documents, scholars have identified nascent security hazards, developing technologies, and shifting priorities in the realm of smart city security [14]. The aforementioned insights have demonstrated their usefulness in providing guidance to policymakers, urban planners, and security experts in making well-informed decisions and executing suitable security protocols. It is noteworthy that although LSA constitutes a potent instrument for semantic analysis, supplementary methodologies such as topic modeling, natural language processing, or deep learning models can be utilized to augment the scrutiny of smart city security patterns [15]. Furthermore, owing to the ever-evolving nature of the discipline, contemporary studies may have introduced novel approaches or modifications to LSA that are specifically customized for the analysis of security in smart cities. In order to obtain a comprehensive comprehension of the literature and the most recent developments in utilizing LSA for the purpose of analyzing security trends in smart cities, it is suggested that a meticulous literature search be conducted utilizing academic databases, research repositories, and pertinent conference proceedings within the realm of smart cities, cybersecurity, and data analytics. As the Internet of Things (IoT) grows, security vulnerabilities like unsecured firmware, data protection, identity theft, and DoS/DDoS assaults make its adoption and deployment difficult. To overcome these concerns, IoT frameworks should assess physical, remote, and secured data access. Proactive security strategies are examined in this research on assaults and mitigation methods. One of the research studies conducted in 2019 presented the vulnerabilities associated with IoT Devices in smart city framework [16].
The existing body of research on the security of smart cities reveals several areas that require further investigation. These research gaps encompass fo the followings:
There exists a necessity for doing research that assesses the effectiveness of security measures and technologies implemented in smart cities in order to prevent and alleviate security threats. The widespread implementation of emerging technologies such as 5G, the Internet of Things (IoT), and Artificial Intelligence (AI) is observed in smart cities. Emphasis should be placed on conducting investigations into the potential risks and hazards that may arise from the integration of diverse technologies, particularly in relation to vulnerabilities and security concerns. The examination of how smart cities strategize and address security events and interruptions holds significant importance. There are gaps in the existing research pertaining to the evaluation of resilience and recovery measures, as well as their efficacy in guaranteeing the continuous provision of urban services. The increasing prevalence of autonomous vehicles in smart cities has given rise to research gaps pertaining to the comprehension of the distinct security concerns they pose. These challenges encompass weaknesses within communication networks as well as the potential for cyberattacks.
The existence of these gaps in knowledge might facilitate the formulation of more efficient approaches to ensuring the safety of urban areas in the digital age, as well as enhance comprehension of the security obstacles encountered by smart cities. The prioritization of these areas can facilitate the advancement of secure and resilient smart cities. By acknowledging and investigating these areas of insufficient research, scholars and policymakers will enhance their understanding and ability to effectively analyse and tackle the security complexities presented by smart cities. The current body of literature is disorganized and fails to provide clear guidance for researchers on where to begin and which sources to consult, as shown by an analysis of completed academic investigations. The current state of knowledge in this area suggests directions for further research. It also argues for the importance of research into Security Matters. In the context of smart cities and the problems that can be solved by employing blockchain technology. It also presents the latest trends in research on the most interesting topics related to the safety of smart cities.
Methodology
Natural Language Processing is a subfield of artificial intelligence and linguistics focusing on interactions between computers and human language. It involves the development of algorithms and techniques to enable computers to understand, interpret, and generate natural language text or speech [17]. NLP encompasses many tasks, including text classification, information retrieval, sentiment analysis, machine translation, question answering, etc [18]. In addition, it involves tokenization, part-of-speech tagging, syntactic parsing, semantic analysis, and discourse processing. NLP systems are designed to process and understand human language in a meaningful and valuable way for various applications. On the other hand, latent Semantic Analysis is a mathematical method used in natural language processing and information retrieval to analyze relationships between a set of documents and the terms they contain [19]. It is based on the idea that words used in similar contexts tend to have similar meanings. LSA represents words and documents as vectors in a high-dimensional space and uses linear algebra techniques, such as singular value decomposition (SVD), to uncover latent semantic relationships. LSA can be used for document classification, information retrieval, and automated essay grading tasks [20]. It can help identify similar documents, find relevant information, and measure the similarity between words or documents based on their semantic content. In addition, using LSA can overcome some of the limitations of traditional keyword-based approaches, as it captures the meaning of words and their context rather than relying solely on exact word matching. In summary, Natural Language Processing is a broader field that encompasses the development of algorithms and techniques to process human language. At the same time, Latent Semantic Analysis is a mathematical method used within NLP to uncover latent semantic relationships between words and documents.
Data collection
In this study, various strings are formulated to experiment. The first step is to gather data to conduct the research and collect the string data formulation developed following Kitchenham & Charters (2007) guideline [21]. As shown in Fig. 1, six various strings are formulated, and the Scopus database is considered to extract the results. Figures 1 to 6 is labeled for String I to String VI. Scopus database, which is considered the world’s most comprehensive research database. The Scopus database contains articles from various sources, including academic journals, conferences, and books.
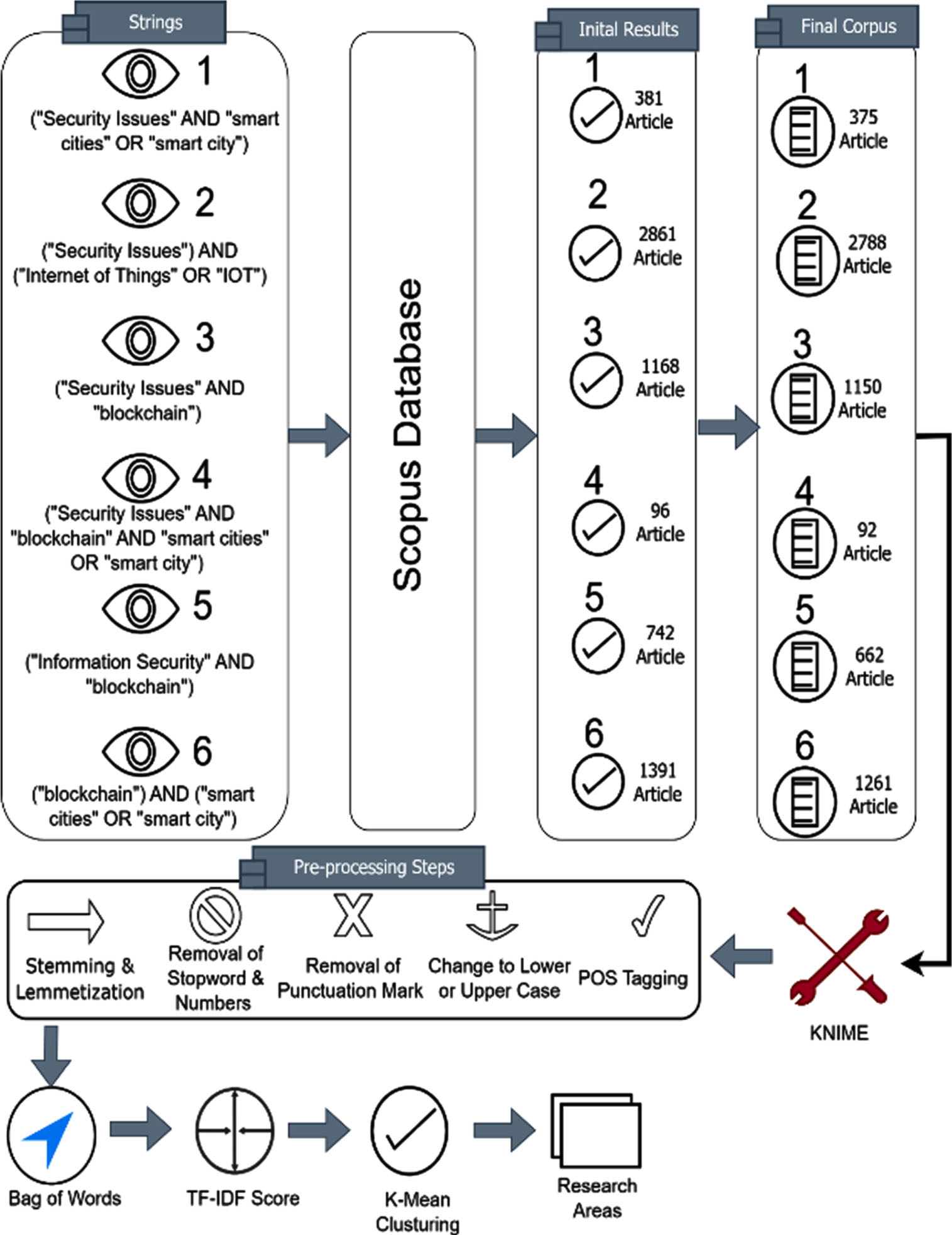
Methodology used for conducting the research.
It includes well-known databases such as Elsevier, Springer, Emerald, Inderscience, SAGE, Wiley, and Taylor & Francis. Once the string is passed to Scopus, each string provides some articles, which are shown Table 1.
Sting formation and corpus fetched from Scopus
KNIME (Konstanz Information Miner) is a popular open-source data analytics platform with a graphical interface for designing data processing workflows [22]. It offers many preprocessing steps to prepare and clean data before analysis. Here are some common preprocessing steps in KNIME:
Once all the preprocessing steps are done, all words are stored in one bag, a bag of words (BOW). These words are further used for sentiment analysis using the TF-IDF score.
Data collection
TF-IDF (Term Frequency-Inverse Document Frequency) is a numerical statistic used in natural language processing and information retrieval to measure the importance of a term in a document within a collection of documents [23]. It provides a way to quantify the relative significance of terms based on their frequency in a document and their rarity across the entire document collection. The TF-IDF score for a term in a document is calculated as the product of two components:
The TF-IDF score is obtained by multiplying the TF and IDF values for a term in a document. A higher TF-IDF score suggests that a term is both frequent in the document and rare in the document collection, making it potentially more critical in distinguishing that document from others. TF-IDF scores are commonly used in information retrieval tasks, such as document ranking, text classification, and similarity calculations. The higher the TF-IDF score for a term in a document, the more relevant that term is to the document and the document collection as a whole.
Result and discussions
This section represents the authors’ result analysis of the string selected for this study.
String-I
(“Security Issues” AND “smart cities” OR “smart city”)
Year-wise analysis
Figure 2 represents the year-wise growth of publication. According to the Figure, the first article was published in 2012, and after that, there was a gradual increase in the publication of articles. Maximum articles were encountered in 2021, approximately 24% of the total articles considered for the experiment. Data is considered till April 2023, so there may be an increase in the total number of publications at the end of year 2023.
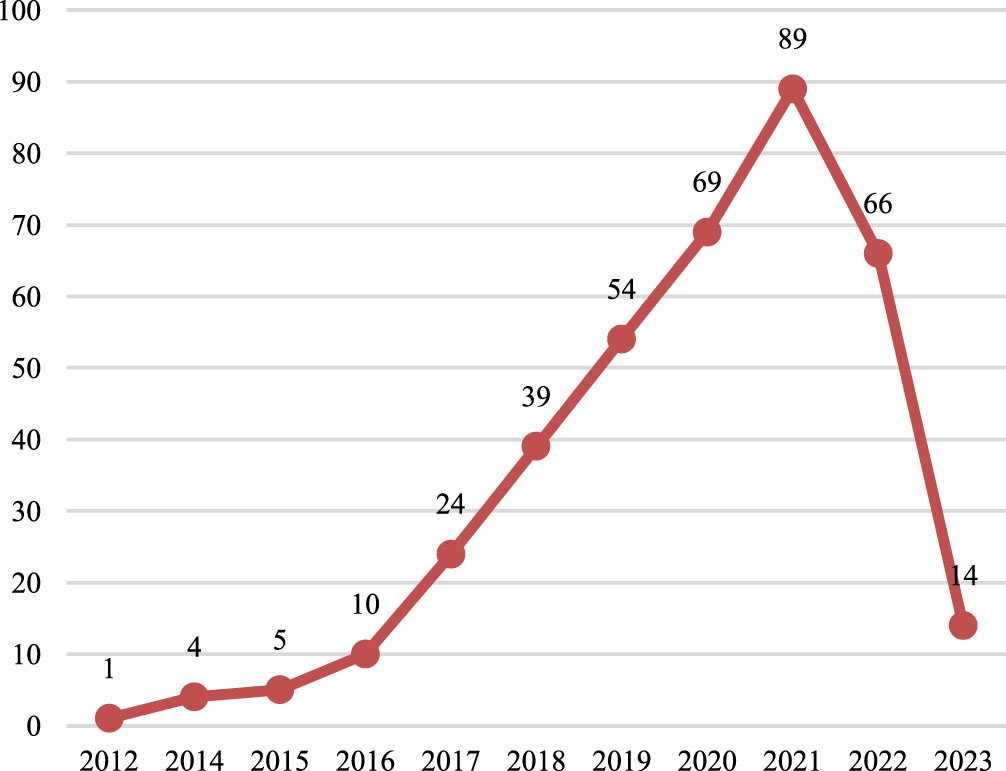
Year wise analysis for string I.
Figure 3 represents the top journal and conferences where the articles were published. The Figure shows the maximum article published in Lecture notes in Springer’s Networks and System conference series. This has come under the book series having an H-Index of 27. Regarding Journal, Advances in Intelligent Systems and Computing led the board with 12 publications which are 3.2% of publications. Journal has an H-Index of 58.
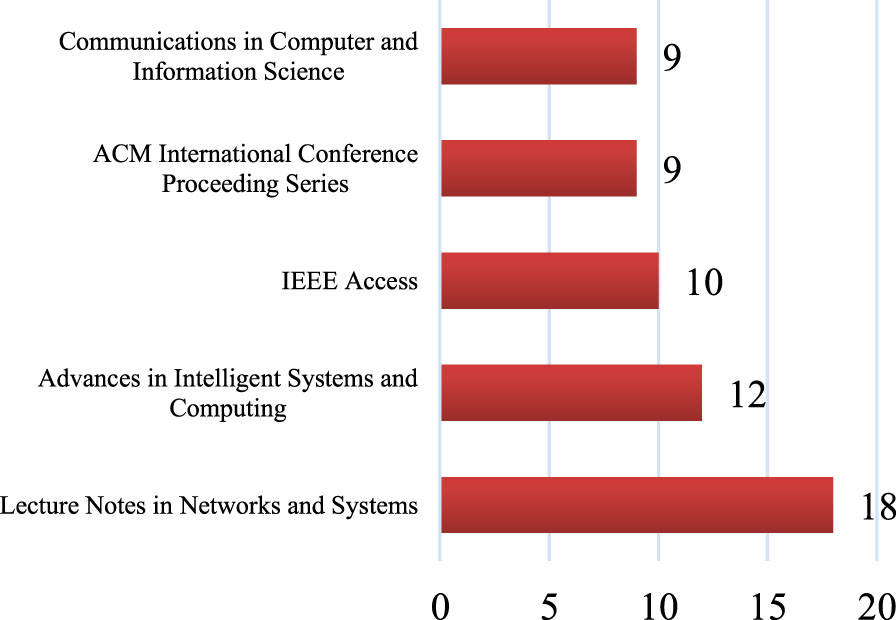
Journal wise analysis of string I.
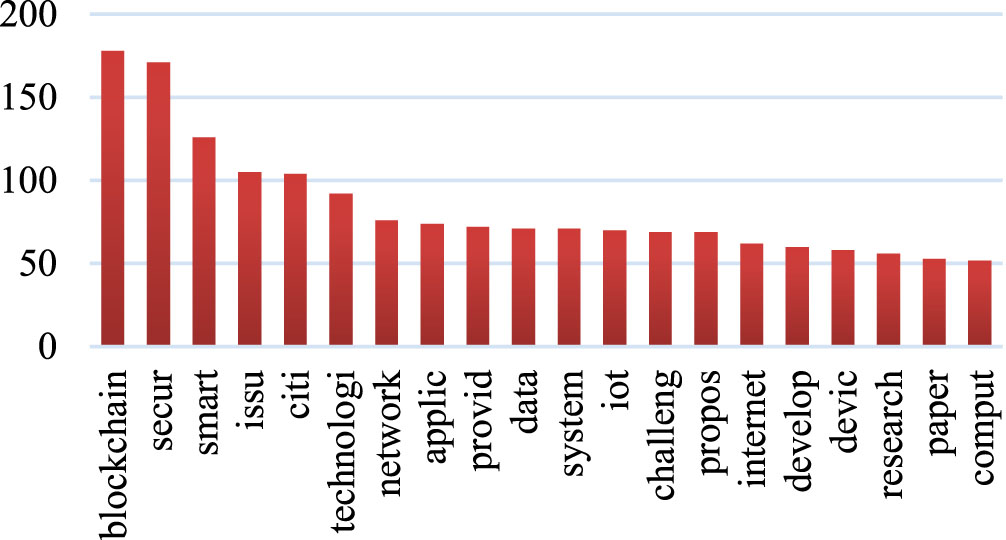
The corpus includes 375 articles scraped from Scopus, and 3824 tokens were used to construct BOW’s vocabulary. The Fig. 4 displays the top 20 most frequent words from BOW with their corresponding occurrence from these 3824 tokens in a visual format.
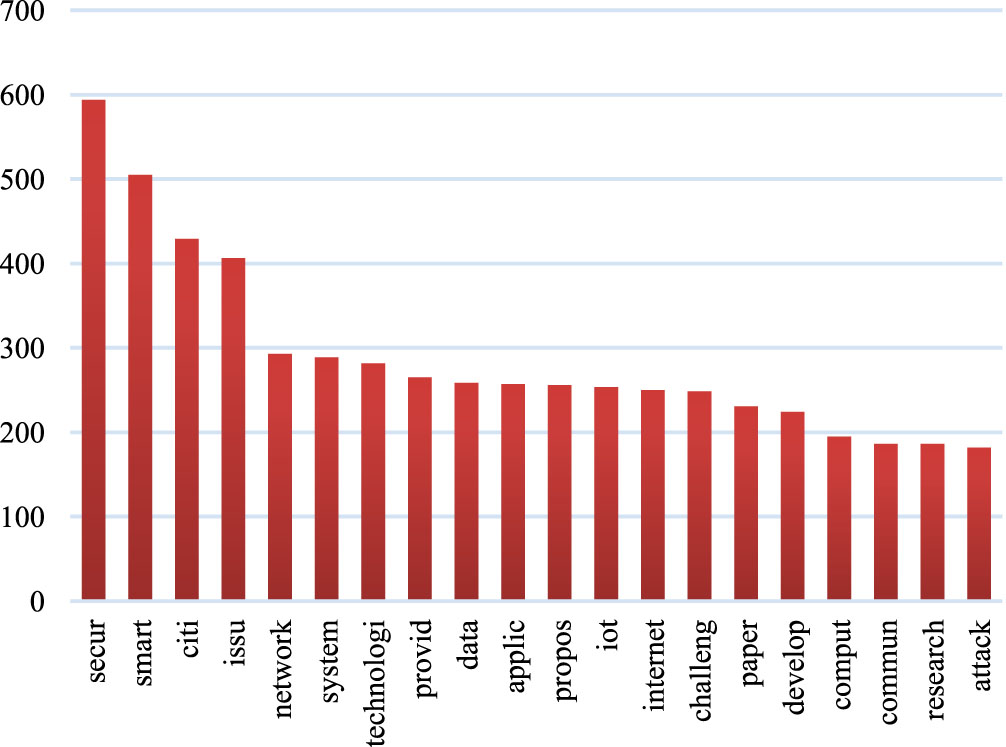
High loading terms fetched from the corpus of string I.
Table 2 represents the cluster labeling created from the high loading terms from the corpus. The clusters show the topics created through the high loading terms along with the relevant articles related to that topic.
High loading terms and cluster formation for String I
High loading terms and cluster formation for String I
(“Security Issues”) AND ("Internet of Things” OR “IOT”)
Year-wise analysis
Figure 5 represents the year-wise growth of publication. According to the Figure, the first article was published in 2010, and after that, there was a gradual increase in the publication of articles. Maximum articles were encountered in 2022, approximately 22.34% of total articles considered for the experiment. Data is considered till April 2023, so there may be an increase in the total number of publications at the end of year 2023.
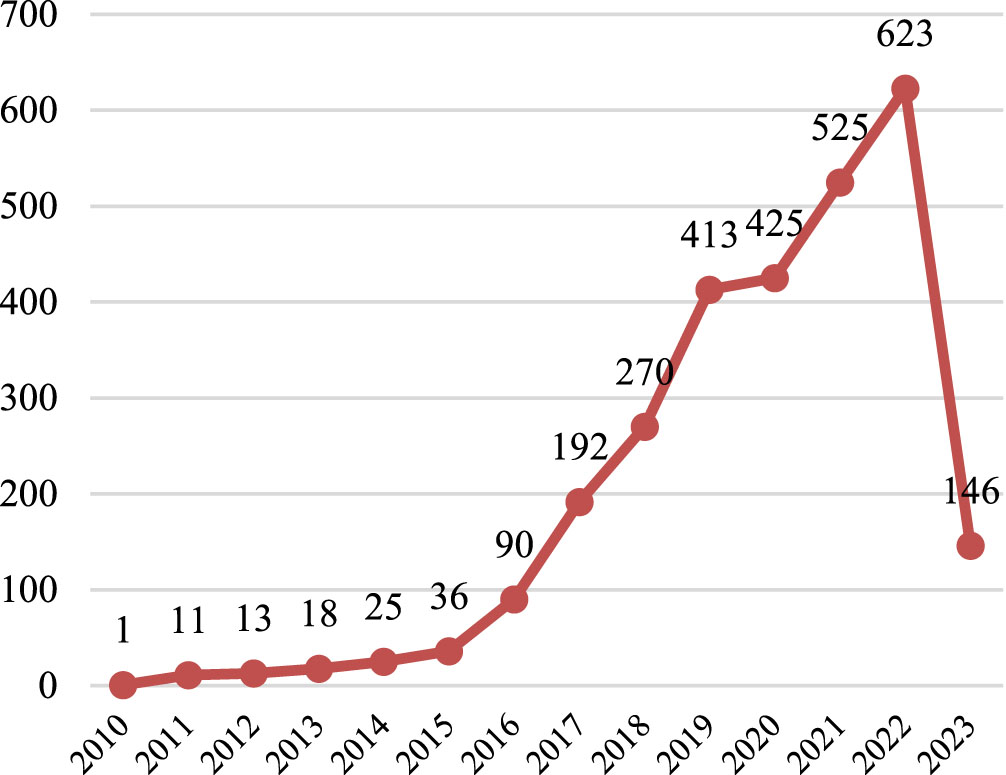
Year wise analysis for string II.
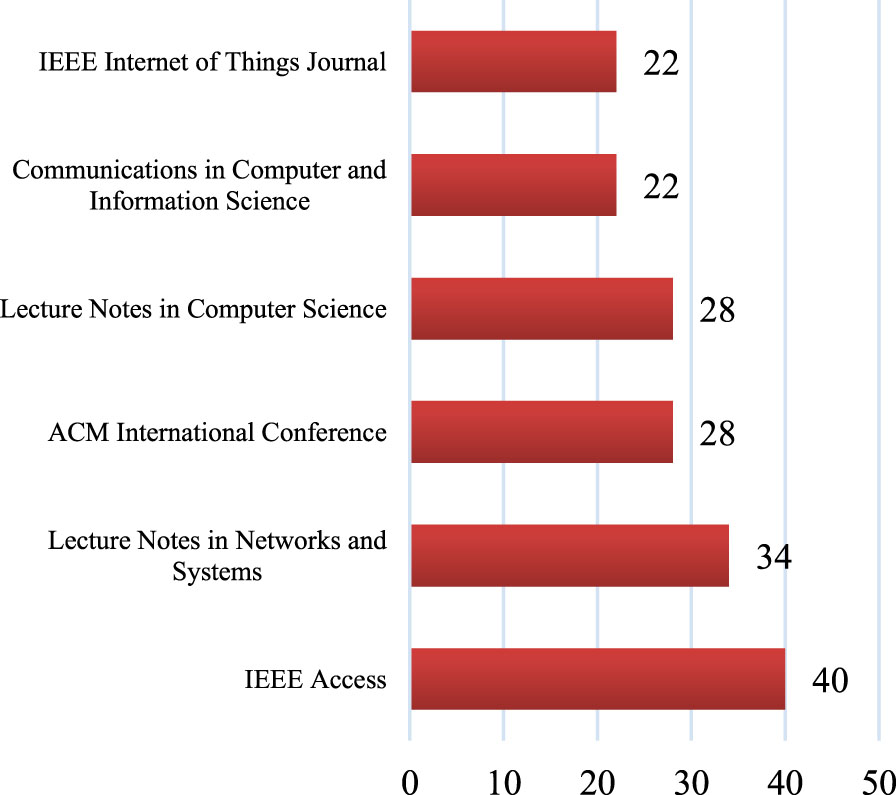
Figure 6 represents the top journal and conferences where the articles were published.
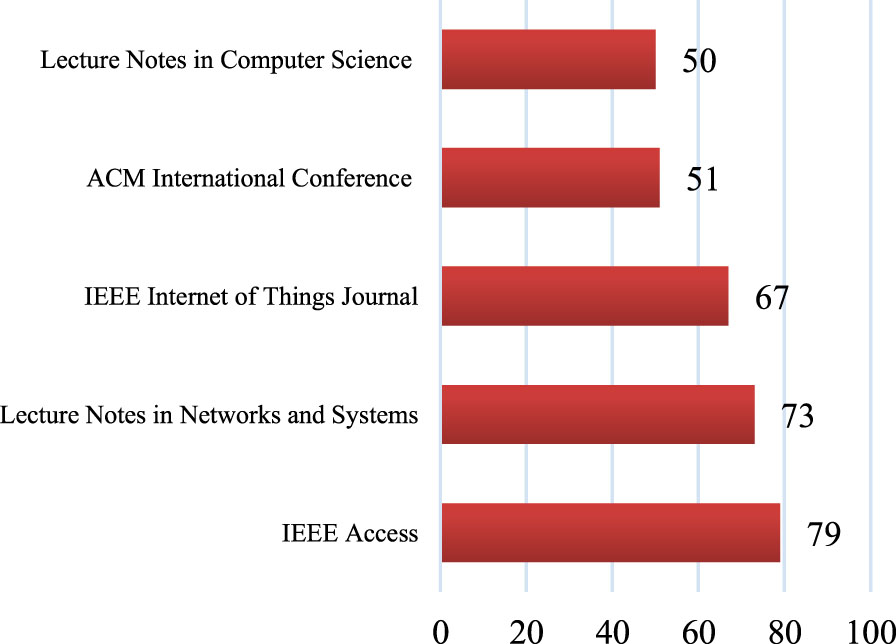
Journal wise analysis of string II.
The Figure shows that the maximum article published in IEEE Access is an open access journal published by IEEE, having an H-Index of 158. Lecture Notes in Networks and Systems is leading the board in conferences, and this is a conference series published by Springer. This has come under the book series having an H-Index of 27.
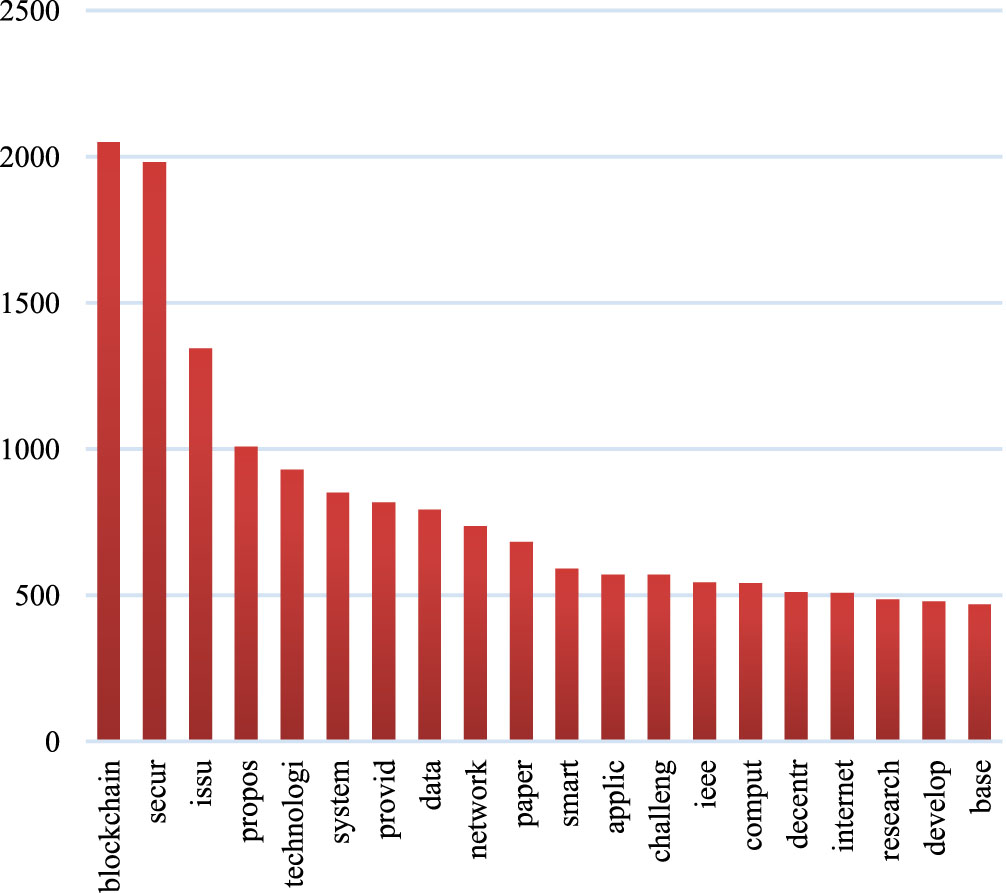
The corpus includes 2788 articles scraped from Scopus, and 11,458 tokens were used to construct BOW’s vocabulary. The Fig. 7 displays the top 20 most frequent words from BOW with their corresponding occurrence from these 11,458 tokens in a visual format.
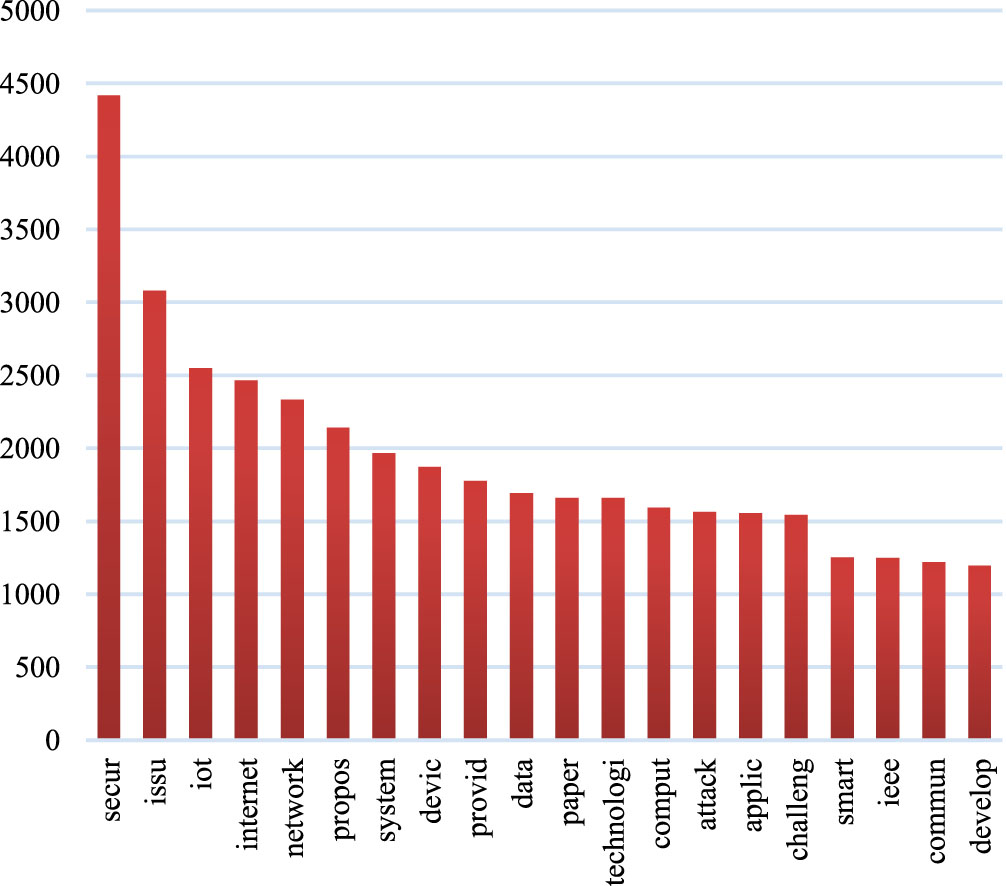
High loading terms fetched from the corpus of string II.
The cluster labels generated from the high-loading phrases in the corpus are shown in Table 3. The clusters display the themes generated by the high-loading phrases together with the associated articles.
High loading terms and cluster formation for String II
High loading terms and cluster formation for String II
(“Security Issues” AND “blockchain”)
Year-wise analysis
Figure 8 represents the year-wise growth of publication. According to the Figure, the first article was published in 2014, and after that, there was a gradual increase in the publication of articles. Maximum articles were encountered in 2022, approximately 33.56% of the total articles considered for the experiment. Data is considered till April 2023, so there may be an increase in the total number of publications at the end of year 2023.
Year wise analysis for string III.
Figure 9 represents the top journal and conferences where the articles were published. The Figure shows that the maximum article published in IEEE Access is an open access journal published by IEEE, having an H-Index of 158. Lecture Notes in Networks and Systems is leading the board in conferences, and this is a conference series published by Springer. This comes under the book series having an H-Index of 27.
Journal wise analysis of string III.
The corpus includes 2788 articles scraped from Scopus, and 11,458 tokens were used to construct BOW’s vocabulary. Figure 10 displays the top 20 most frequent words from BOW with their corresponding occurrence from these 11,458 tokens in a visual format.
High loading terms fetched from the corpus of String III.
Table 4 displays the cluster labelling that was generated based on the high-loading terms extracted from the corpus. The clusters exhibit the topics that have been formed based on the high-loading terms, accompanied by the pertinent articles that are associated with each respective topic.
High loading terms and cluster formation for String III
High loading terms and cluster formation for String III
(“Security Issues” AND “blockchain” AND “smart cities” OR “smart city”)
Year-wise analysis
Figure 11 represents the year-wise growth of publication. The Figure shows that the first article was published in 2018, and after that, there was a gradual increase in the publication of articles.
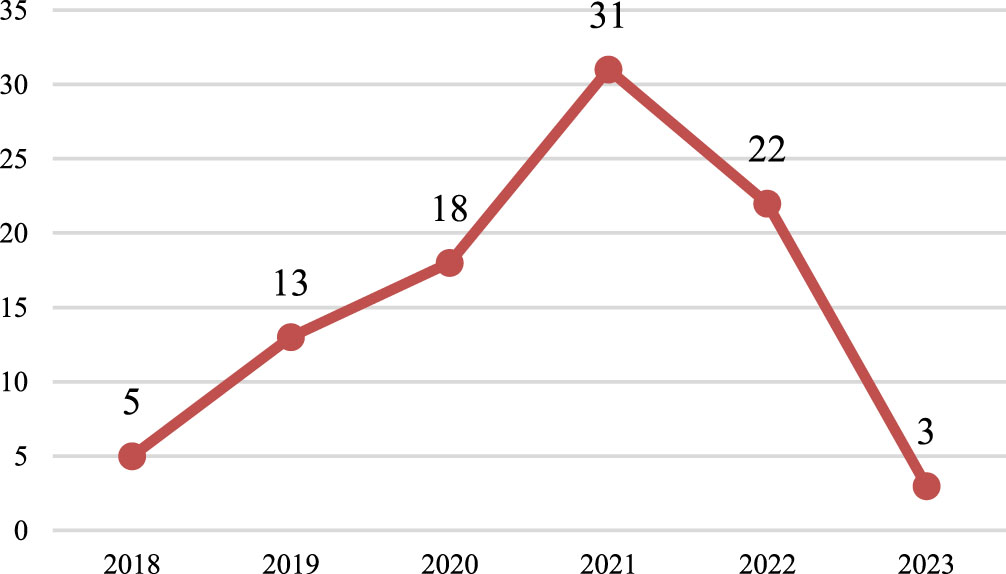
Year wise analysis for string IV.
Maximum articles were encountered in 2021, approximately 33.69% of total articles considered for an experiment. Data is considered till April 2023, so there may be an increase in the total number of publications at the end of year 2023.
Figure 12 represents the top journal and conferences where the articles were published. The Figure shows that the maximum article published in Communications in Computer and Information Science is a conference series published by Springer. This comes under the book series having an H-Index of 62. Five articles are published in Lecture Notes in Networks and Systems under the conference umbrella and part of Springer. In journals, Electronics has the leading publication published by MDPI with an H-index of 62.
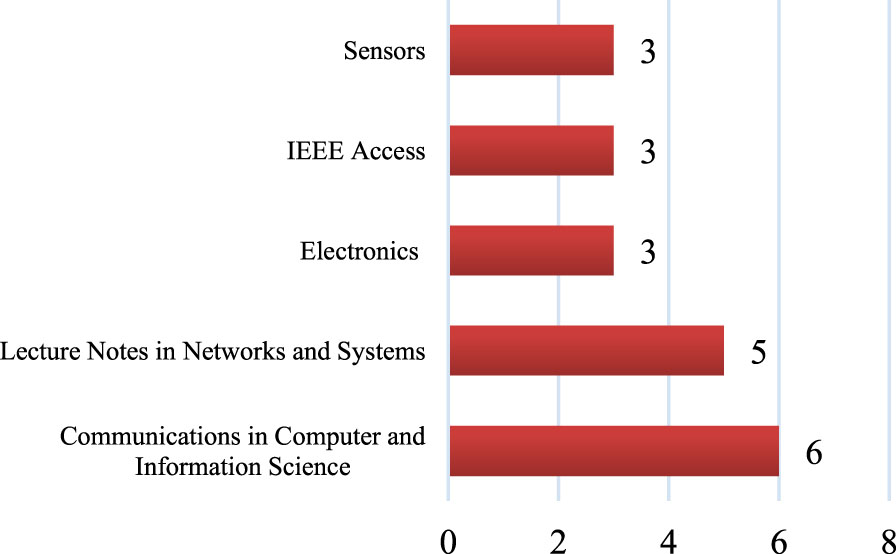
Journal wise analysis of string IV.s
The corpus includes 92 articles scraped from Scopus, and 1789 tokens were used to construct BOW’s vocabulary. Figure 13 displays the top 20 most frequent words from BOW with their corresponding occurrence from these 1789 tokens in a visual format.
High loading terms fetched from the corpus of String IV.
The labeling for the clusters that were generated from the high-loading terms in the corpus is presented in Table 5. The clusters present the subjects that were produced because of the high-loading phrases together with the relevant articles that are associated with that topic.
High loading terms and cluster formation for String IV
High loading terms and cluster formation for String IV
(“Information Security” AND “blockchain”)
Year-wise analysis
Figure 14 illustrates the progression of the number of publications over time. According to the figure, the first article was not published until the year 2003; nonetheless, there is a significant publication void after that year. In 2017, nine articles were published, and in the years that followed, there was a slow but steady growth in the number of articles that were published. The greatest number of articles, or about 28.54 percent of the total articles that were taken into account for the experiment, were found in 2021. Since data are evaluated up until April 2023, it is possible that there will be a rise in the overall number of publications by the time the year 2023 comes to a close.
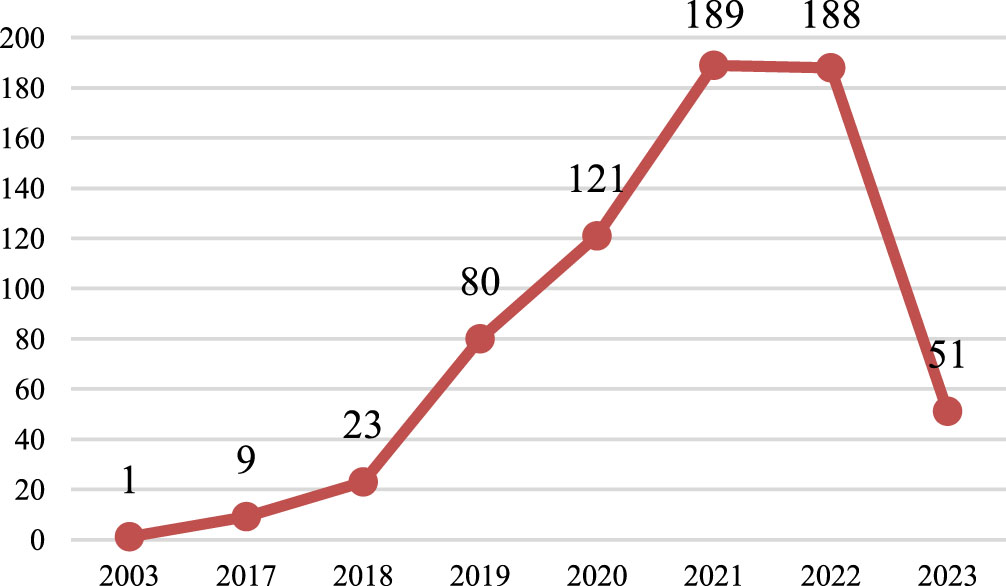
Year wise analysis for string V.
Figure 15 represents the top journal and conferences where the articles were published. For example, the Figure shows that the maximum article published in Lecture Notes in Computer Science is a conference series published by Springer. This comes under the book series having an H-Index of 446. Twenty-five articles are published in ACM conference proceedings, which also come under the conference umbrella and are part of ACM publisher having an H-Index of 137. In journals, IEEE Access has the leading publication published by IEEE, having an H-index of 158.
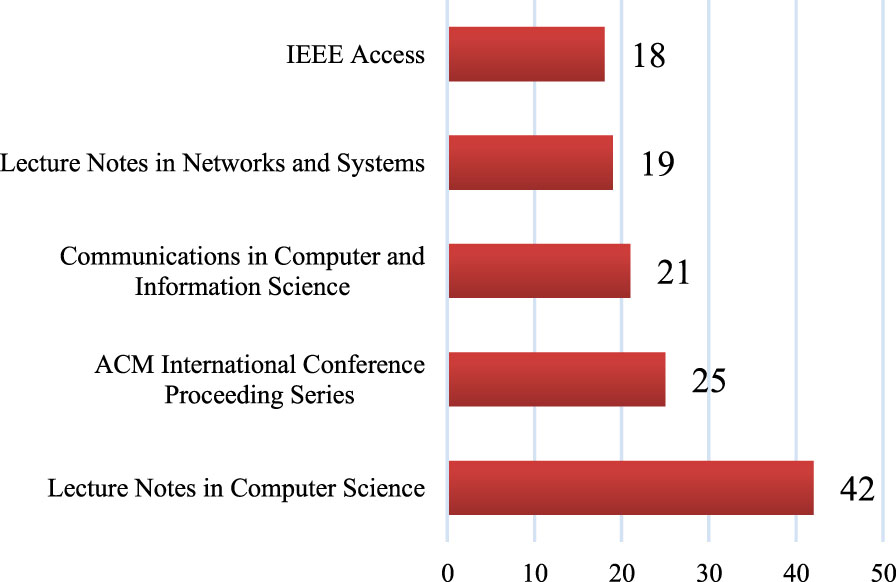
Journal wise analysis of string V.
The corpus contains 662 articles that were harvested from Scopus, and the vocabulary of BOW was built using a total of 5112 tokens. A visual representation of the top 20 most frequent terms in BOW, together with the number of times each word appears in the 5112 tokens that make up Fig. 16, can be found in Fig. 16.
High loading terms fetched from the corpus of String V.
Table 6 presents the labelling that was obtained for the clusters that were generated from the high-loading phrases that were present in the corpus. The clusters provide not only the subjects that were generated as a result of the high-loading phrases but also the relevant articles that are related to those topics.
High loading terms and cluster formation for String V
High loading terms and cluster formation for String V
(“blockchain”) AND (“smart cities” OR “smart city”)
Year-wise analysis
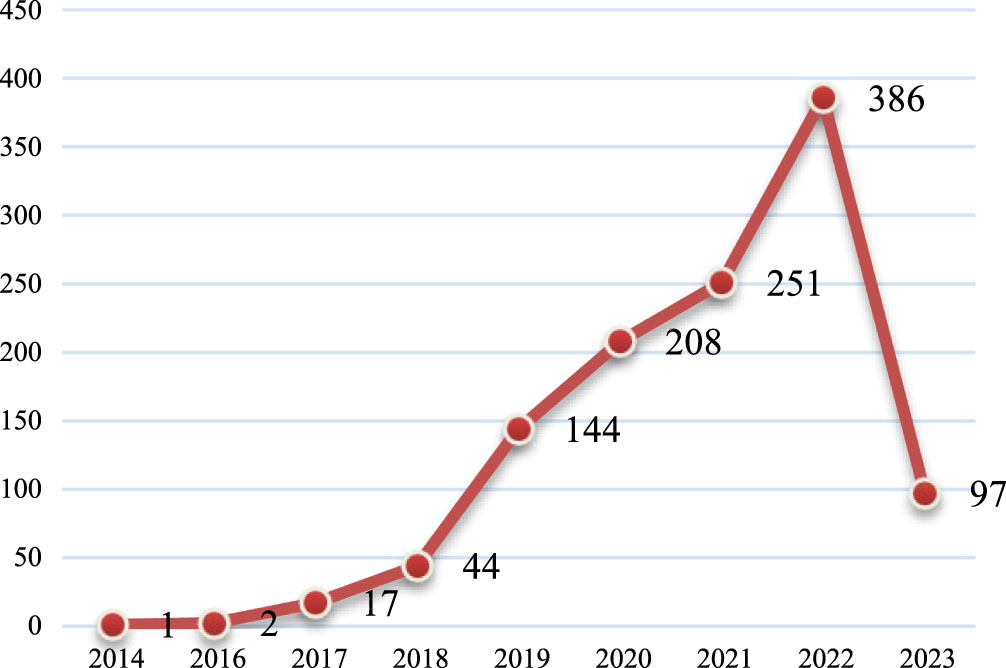
Figure 17 illustrates the progression of the number of publications over time. The Figure indicates that the first article was published in 2016, and that there was a subsequent progressive increase in the number of articles published after that point. In the year 2022, the most articles were found, accounting for around 24.48% of the total articles that were considered for the experiment. Since data are evaluated up until April 2023, it is possible that there will be a rise in the overall number of publications by the time the year 2023 ends.
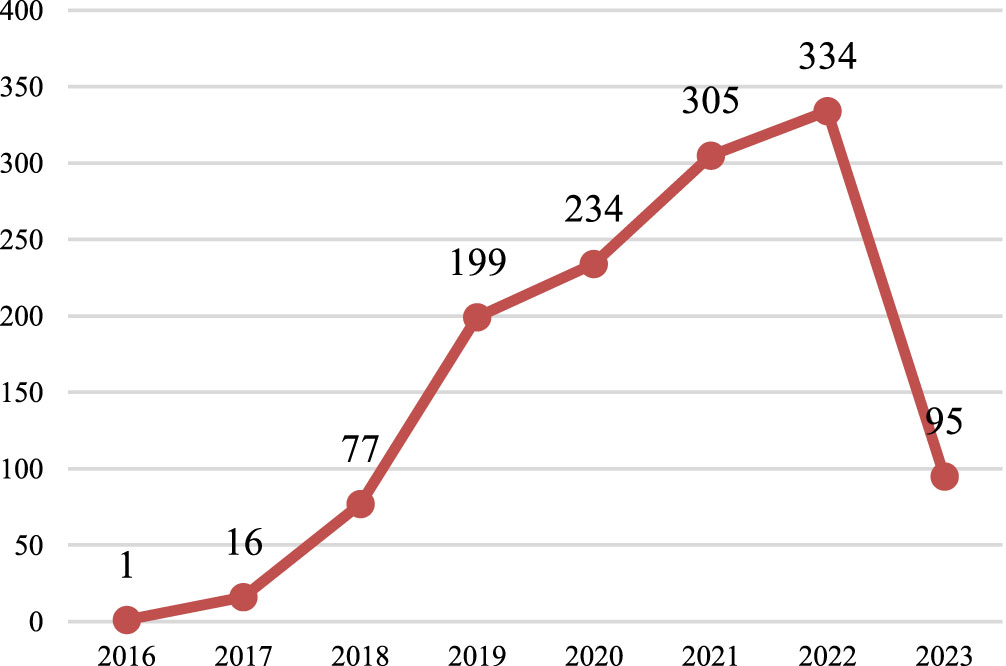
Year wise analysis for string VI.
The most influential journals and conferences are shown in Fig. 18. These are the places where the articles were published. The majority of the publications that are included in the Lecture Notes in Networks and Systems journal can be found within Springer’s conference series. This is part of the book series that has an H-Index of 27, which you can find here. After this meeting, the publication with the highest H-Index was Lecture Notes in Computer Science, which was also issued by Springer and has the same number.
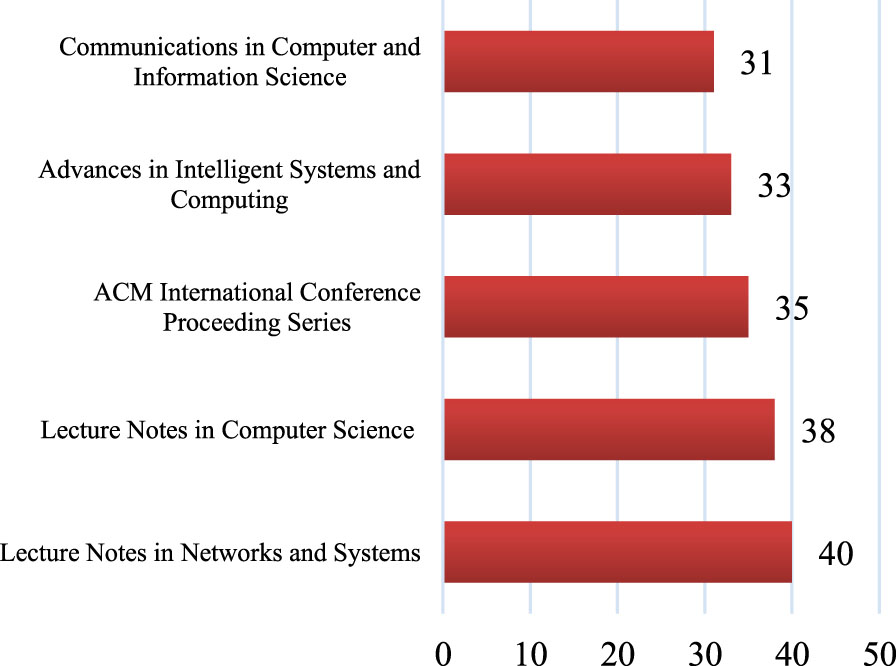
Journal wise analysis of string VI.
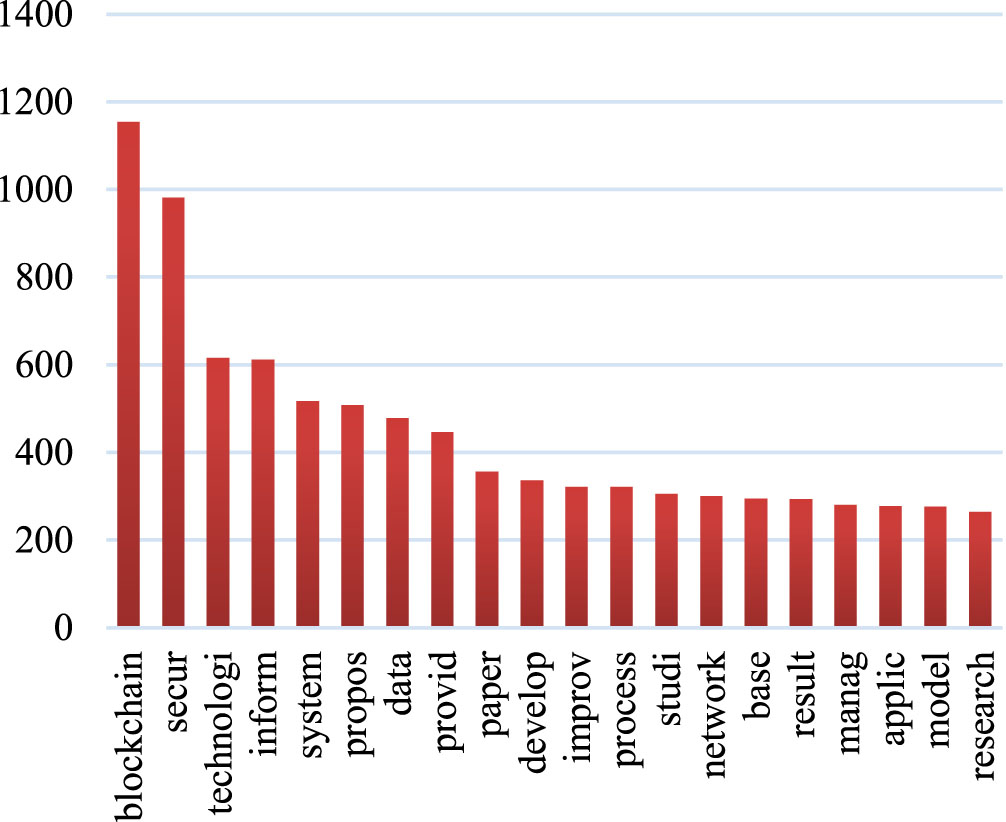
The BOW vocabulary was built out of 7252 tokens, while the corpus itself contains 1261 articles that were harvested from the Scopus database. Figure 19 shows a graphical representation of the top 20 most frequent terms found in BOW, together with the number of times each word appears in the set of 7252 tokens.
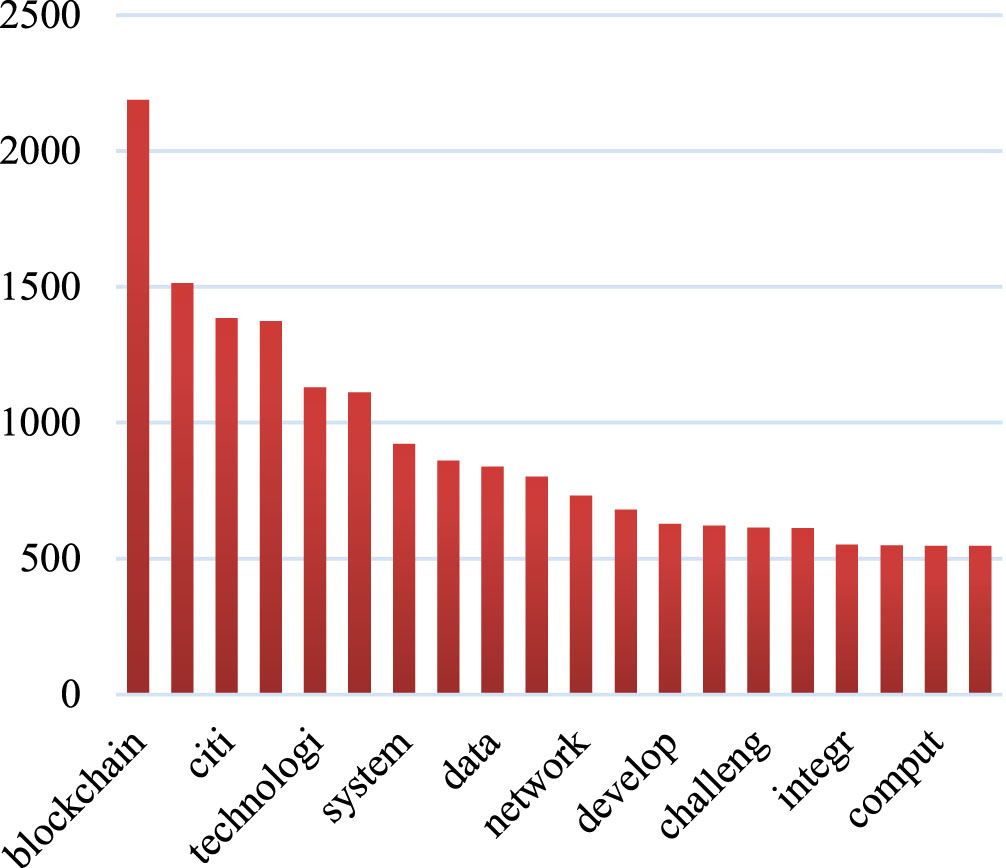
High loading terms fetched from the corpus of string VI.
The labelling of the clusters that resulted from the high-loading phrases in the corpus is presented in Table 7. The clusters include both high-loading phrase-generated themes as well as articles that are pertinent to those subjects.
High loading terms and cluster formation for String VI
High loading terms and cluster formation for String VI
Blockchain technology is employed in smart cities to enhance several aspects such as identity management, supply chain security, public safety, and cybersecurity. The system provides decentralized identity creation, tamper-resistant recordkeeping, selective disclosure, and interoperability. Blockchain technology enhances supply chain visibility by ensuring the integrity and dependability of data. Furthermore, it streamlines the processes of payment and delivery, enabling efficient and convenient transactions. Additionally, it facilitates real-time monitoring, enhancing the ability to monitor the progress of orders in a timely manner. Smart contracts have the capability to automate the processes of payment and delivery, hence mitigating disagreements, and instances of fraudulent activities. The utilization of blockchain technology facilitates secure communication and efficient data sharing among emergency services, hence enhancing public safety. The implementation of decentralization mitigates the risk of emergency situations by eliminating single points of failure, hence enhancing overall resilience. The use of measures such as data integrity, access control, threat detection, and zero trust security is crucial in safeguarding against cybersecurity threats. Blockchain technology provides a range of valuable features, including data immutability, decentralization, privacy, trust, transparency, smart contracts, and interoperability. These factors enhance the security and resilience of smart cities. The implementation of blockchain technology has been found to enhance the efficiency and effectiveness of several smart city operations.
The incorporation of blockchain technology within the context of a smart city environment presents notable benefits for data management, owing to its inherent attributes of immutability, transparency, and decentralized identity verification. The protection of data is achieved by the implementation of cryptographic algorithms, the transparent maintenance of records, consensus procedures, and immutable storage. The fortification of safeguards against unauthorized alterations is strengthened within decentralized blockchains with the participation of several nodes in the consensus mechanism. Within a blockchain network, each transaction or data input is allocated a timestamp, functioning as an unalterable documentation of the data’s incorporation. Decentralized identity verification systems, also known as self-sovereign identity systems, enable individuals to independently manage and control their digital identities. These systems facilitate the acquisition of credentials from reputable issuers, the controlled disclosure of credentials and personal information, and the authentication of individuals without dependence on a centralized controlling authority. Blockchain-based identification solutions offer users the ability to verify their identity across multiple services and applications without the necessity of creating new accounts or revealing personal information. The utilization of blockchain technology in a smart city’s digital ecosystem serves to augment the integrity, immutability, and trustworthiness of data.
Blockchain technology enhances cybersecurity protocols in smart cities by offering a robust and immutable storage system for threat intelligence data. It facilitates prompt retrieval and modification of security systems through the utilization of smart contracts. Additionally, it fosters transparency and trust in the sharing of data and tracking of incidents. The use of an immutable ledger guarantees that data cannot be modified or erased without the agreement of the network, hence strengthening confidence among the various parties involved. Blockchain networks function through a decentralized arrangement of nodes, so mitigating the potential vulnerabilities associated with a singular point of failure or compromise. The system incorporates a timestamp for each data entry, so facilitating the accurate tracking of the chronological sequence of threats. The facilitation of private and safe data sharing across authorized bodies serves to augment the levels of data privacy and security. Smart contracts provide the automated execution of security responses in real-time, in accordance with predetermined circumstances. Additionally, a distributed ledger designed for incident recording aids authorities in monitoring and documenting security incidents. The decentralized nature and resistance to tampering of blockchain technology contribute to its ability to maintain secure networks, even in the presence of cyberattacks.
Conclusion
The primary conclusions of this investigation encompass the six prevalent domains that pertain to the security of Smart cities, as well as the present patterns observed within them. These trends have been derived through the application of topic modelling on a corpus of various strings obtained from the Scopus database. This study also suggests that vulnerabilities exist inside the Internet of Things (IoT) framework for smart cities, which can be addressed by implementing a comprehensive security framework. Current research trends in the field of smart city security focus primarily on the investigation and resolution of diverse cybersecurity challenges, as well as the development of strategies to protect privacy, improve resilience, and effectively manage potential disasters. Currently, academic researchers are investigating the concepts of data anonymization, secure data sharing, and analytics as means to safeguard personal information and facilitate data-driven decision-making. The Internet of Things (IoT) plays a crucial role in the implementation of smart city initiatives, but it also introduces novel security challenges. Researchers are investigating vulnerabilities in Internet of Things (IoT) devices by evaluating aspects such as device authentication, access control, and secure firmware updates. The use of blockchain technology is presently under investigation for the purposes of ensuring secure data management, facilitating transparent transaction verification, and preserving temper-proof records. Incorporating smart city technologies into urban environments has prompted the consideration of social and ethical implications. The primary purpose of these initiatives is to facilitate the development of smart cities in a manner that prioritizes safety and security, while also promoting trust, privacy, and sustainability. Through its capacity to facilitate secure data management, identity management, supply chain security, public safety, cybersecurity, and energy infrastructure security, the implementation of blockchain technology has the potential to improve the security of smart cities. The implementation of this system ensures the preservation of data integrity, immutability, and decentralized identity verification, thereby mitigating the risks associated with identity theft and unauthorized access. Through the storage of threat intelligence data on the blockchain, blockchain technology has the capacity to bolster cybersecurity protocols. This allows for the seamless retrieval and modification of security systems in real-time. The significance of blockchain technology in the security frameworks of smart cities is the conclusion of the current study. Using LSA on a variety of strings, it has been determined that most of the clusters generated by NLP revolve around the use of blockchain in smart cities to improve security.
Future research directions
Blockchain technology can enhance the security of smart cities by providing a secure and transparent framework for data integrity, identity management, supply chain security, public safety, cybersecurity, and energy infrastructure management. Secure data management, identity management, supply chain security, smart contracts for security policies, public safety and emergency response, cybersecurity and threat intelligence, and energy grid security are among the most essential applications. Future research should emphasize scalability and performance, interoperability and standardization, privacy and confidentiality, governance and legal frameworks, security and resilience, energy efficiency, user experience, and adoption. By resolving these issues, researchers can contribute to the creation of robust and resilient blockchain solutions that enhance the security and resilience of smart cities. There is a need to implement a trustworthy information security framework using latest technologies like Blockchain Technology, AI for malware detection, Machine Learning for Security threat monitoring and many more.
Footnotes
Acknowledgments
We would like to extend my utmost gratitude and appreciation to all individuals who have made significant contributions towards the successful culmination of this research paper. This achievement would not have been attainable without the invaluable support, guidance, and assistance provided by others.
Conflicts of interest
The authors have no conflicts of interest to declare.
