Abstract
In order to solve the problems of tedious, insufficient manpower, low efficiency, and easy to cause human errors in the verification of relay protection equipment settings with the development of the power grid, an automatic verification method of relay protection equipment settings combining cell image gray enhancement and AI recognition is studied. In this method, Gaussian mixture and particle swarm algorithm are used to enhance the gray level of the original image captured, and the binary method is used to further denoise the image; The histogram is used to segment the cells in the denoised constant value image one by one; The OCR technology in AI technology uses the maximum width backtracking segmentation algorithm to segment a coherent text in a cell into multiple single words, and collects the 13 dimensional characteristics of the text to be detected to compare with the text in the database. The text with the smallest error is the detected text, which completes the text extraction in the cell; Store the extracted text data in the database, check the data in the notification constant value sheet and the device constant value sheet, and give an abnormal prompt of different data. The experimental results show that the image pre processed by this method is clear, the fixed value single cell segmentation is accurate, and the OCR text extraction efficiency is high. Through a large number of data experiments, the final verification accuracy can reach 99.8%.
Keywords
Introduction
Relay is an electrical control device [1]. It is an electrical appliance that makes the controlled quantity have a predetermined step change in the electrical output circuit when the change of input quantity (excitation quantity) meets the specified requirements.It has the interaction between the control system (also called the input circuit) and the controlled system (also called the output circuit) [2]. Usually used in automatic control circuit [3], it is actually an “automatic switch” that uses small current to control large current operation. It plays the role of automatic adjustment, safety protection and conversion circuit in the circuit. Since the correctness of the relay protection device setting data will directly affect the operation mode of the power grid system [4], which is of great significance to the safe and stable operation of the power grid [5], in the setting management, field staff are required to check the operation setting of the relay protection device on a regular basis every year or when the operation setting changes (when the setting is implemented). At present, the substation setting value verification is conducted manually, that is, the relay protection personnel print the protection device setting value list on site, and read, repeat and check whether the protection setting value list printed by the device is consistent with the setting value list issued by the dispatcher. However, the current constant value verification work has the following shortcomings: (1) The constant value verification work needs to use an external needle printer to print a paper constant value list. The needle printer is slow in printing, which is prone to paper jams, no paper and other problems. Workers often spend time checking the status of the printer and making it have printing conditions [6], so it is easy to cause low verification efficiency. (2) The process of setting value verification is manual verification, so there is a human error [7]. Once this happens, the relay protection device will operate for a long time with incorrect setting value and cannot be found out [8], which is very likely to cause the relay protection device to misoperate or refuse to operate, leading to the expansion of power grid accidents [9]. (3) With the continuous development of the power grid, the number of substations is increasing year by year, and the number of relay protection devices is increasing day by day, the verification of setting values inevitably faces problems such as large quantity, complexity, and insufficient human resources [10]. Integral based holographic image registration is a method to align multiple holographic images to obtain higher quality and clearer reconstructed images. This registration technique can be applied to a variety of fields, including medical imaging, light microscopy, etc. In the real scene, due to environmental factors or the damage of the object itself, the Angle of view of the image may be distorted or deformed. When it comes to the recognition of QR codes, this distortion can have a negative impact on the readability of QR codes.To solve this problem, you can try to use image correction and correction techniques to correct Angle distortion in the image. These techniques are often based on computer vision and image processing algorithms such as perspective transformation, distortion correction, edge detection, etc. By geometrically correcting the image and removing the distortion, the QR code in the image can be restored to the normal shape and positioning, thus improving the accuracy of recognition.The traditional setting of relay protection equipment often needs to be completed by manually adjusting parameters. This method depends on the experience and skill level of the engineer, is easily affected by subjective factors, and the tuning process is cumbersome and time-consuming. The lack of automation and intelligent functions can not be adjusted according to the actual state and operation of the system. This may result in unreasonable, over - or under-setting.
With the progress of science and technology, many scholars have also carried out research on the verification technology of relay equipment settings, such as Lin S et al.’s research on condition based maintenance of traction power supply equipment based on partial observable Markov decision process [11]. In order to optimize the value verification of relay protection equipment, a four state Markov process is used to describe the degradation process of setting value calculation. The state dwell time and transition probability of the equipment can be obtained by the equal number of failures in the statistical cycle; Then, the problem of incomplete maintenance is considered, and the failure risk after the abnormal value verification is quantified to optimize the economic cost and reliability of the verification strategy. A W L et al. studied the rotation pressure correction method of stokes/darcy model based on modular gradient stability [12], adopted the check method with modular gradient stabilization, optimized the non-stationary Stokes/Darcy model, improved the stability of the model, accelerated the speed of the check and improved the accuracy of the check in the process of constant value check. Tamo I et al. proposed a fixed value verification method based on error correction of partial information [13], which uses Reed Solomon rule and another kind of folded Reed Solomon code. When the information in the equipment fixed value sheet is insufficient, the algorithm is used to deduce the exact part and check with the original fixed value information in the database to complete the work. Komathi C et al. proposed the design of SMPS power factor correction fractional order pi controller based on the gray wolf optimization algorithm [14], carried out a detailed analysis of the proposed relay settings, obtained the optimal parameters of relay settings using the GWO algorithm, improved the speed of verification, and used the system to check the settings of relay protection equipment when inputting the equipment settings into the system. The above methods can complete the verification of relay protection equipment settings, but there are also problems such as low verification efficiency, easy to generate verification errors, and unable to check a large amount of data.Bandini et al. [15] proposed a multi-component structure multivariate probabilistic seismic demand model (PSDMs) based on multi-fringe analysis and Gaussian mixture model coupling. The proposed method is very flexible in terms of the assumptions adopted and uses a classic highway bridge in eastern Canada to demonstrate the application of the new method and investigate its implications for seismic vulnerability analysis. Mlyahilu et al. [16] proposed the use of morphological geodesic active contours and image processing techniques to perform segmentation and evaluate the performance of robots used to manufacture solder beads. The algorithm has four parameters: pre-processing image, balloon force, smoothing parameter and iteration number. In order to preprocess the image, the algorithm uses the anti-Gaussian gradient operator to detect the edge and the histogram equalization method to horizontally process the distribution.
The image gray enhancement can reduce the noise of the image and make the image clearer. The efficiency of AI recognition after training is much higher than that of manual work. Therefore, the automatic verification method of relay protection equipment setting value combining the gray enhancement of cell image and AI recognition is studied. This method uses gray enhancement and binary method to preprocess the single image of relay protection equipment setting value taken to reduce the noise of the single image of setting value. Then, the table in the setting sheet is divided, and the text of the divided table is extracted using OCR (optical character recognition) in AI technology. The extracted data is stored in the database, and compared with the setting data stored in the database, the error data will be prompted, and the customized automatic verification of relay protection equipment will be completed.
Automatic verification of relay protection equipment setting
Image pre-processing of relay protection equipment setting sheet
After obtaining the paper setting value sheet and device setting value sheet of the relay protection equipment, use the mobile phone or other photographing equipment to collect the image information of the setting value sheet of the relay protection equipment and upload it to the computer, and use the computer to complete the follow-up work.
Gray enhancement of relay protection equipment setting single image based on particle swarm optimization Gaussian mixture
After uploading the captured image of relay protection equipment setting sheet to the computer, it is necessary to process the setting sheet image first to reduce the difficulty of the subsequent work.
(1) Determination of the number of gaussian functions in mixture model
If Gaussian mixing is required, the number of quasi functions shall be determined first i is the gray level of the setting value single image, 0 ≤ i ≤ L, n
i
is grayscale i the number of pixels, MN is the total number of pixels in I
in
, K is the number of Gaussian functions required for modeling the input constant value single image, 2 ≤ K ≤ L. The primary objective of GMM (Gaussian mixture model) is to obtain K and divide the image histogram into K subgraph. Then use the following formula (1) to calculate the cumulative probability density of each sub histogram cdf
j
, where 1 ≤ j ≤ K.
Where,
The quality of histogram segmentation scheme is determined by the standard deviation of the scheme σ
w
and the number of sub histograms K decision. The cost function is:
Where:
(2) GMM parameter estimation
Gray level distribution of input constant value single image p (x
i
) (x ∈ I
in
) the available GMM is expressed as K linear combination of Gaussian functions:
Where: g (x
i
|μ
j
, σ
j
) is the first j Gaussian components; a
j
is the first j of the weight value of Gaussian components; a1 + a2 + a3 + ⋯ + a
k
= 1. The Gaussian distribution density function is defined as:
Where: μ
j
and
(3) Histogram segmentation
The histogram is segmented according to the intersection of adjacent Gaussian functions. In order to get the intersection points, the Gaussian functions are arranged in ascending order of average value j and j + 1 the intersection points of Gaussian functions can be expressed as follows:
To cover the whole dynamic range of the input constant value single image, select the leftmost and rightmost important intersection points
Weight value of each subinterval w and variance σ w the parameters of the main Gaussian function in this subinterval are the same.
(4) Subinterval mapping
In the map, each sub histogram interval
Where: w
i
and variance σ
wi
are the first i the weight and variance of the subinterval. nl is the brightness level that less than or equal to the total number of pixels for
The above mapping formula maps the interval in the input dynamic range to the output dynamic range
The process of constant value single image enhancement based on particle swarm optimization Gaussian mixture algorithm is as follows:
Step 1: Determine the number of Gaussian functions of the input constant value single image Gaussian mixture model;
Step 2: Estimate GMM parameters and obtain the intersection point of adjacent Gaussian functions [17];
Step 3: Segment the histogram of the image according to the important intersection points;
Step 4: Use n random locations {ξ i , υ i , ι i } and velocity value to initialize particle swarm, this paper takes n = 20 and calculates the fitness function of each particle;
Step 5: Assign the particle parameters with the best fitness to p bestiter (local optimum value) g best (global optimal value);
Step 6: Cycle until the maximum number of iterations is reached
(1) Cycle until all particles are exhausted (i = 1, 2, ⋯ , n);
a. Use the current p bestiter and g best value update page i velocity and position of particles;
b. Generate the enhanced fixed value single image according to the updated ith particle, and calculate its fitness;
c. If the i particle fitness is better than p best , then p bestiter =section i particles, return (1);
(2) If the fitness value of p bestiter is better than g best , then g best = p bestiter , return to step 6;
Step 7: Output g best , that is, the global optimal solution ξ, υ, ι; The image of the setting sheet of the enhanced relay protection equipment is obtained from Formula (11) and Formula (13).
On the basis of the gray enhancement of the setting value single image of the relay protection equipment, the binary processing of the setting value single image is performed [18]. For binary processing of fixed value single image, probability density model and subspace model are mainly used. In the probability statistical model, assuming that the summary of any fixed value single image contains m words, the formula for calculating the probability mixing degree of any spectrum is given below:
Where, g
i
represents the probability of the existence of a text, f
i
(x) is spectrum i before mixing, the probability needs to meet the following constraints:
In the process of binary processing of fixed value single image, the following assumptions are set:
Where, H is the grayscale of the pixel block (0 and 1 represent black and white),
The Niemann Pearson decision rule is introduced to reduce the probability of errors in the binary process of fixed value single image. Niemann Pearson decision rule is a decision rule that minimizes the error rate under set conditions. The specific calculation formula is given below:
By introducing Lagrange multipliers, the probability density function can be expressed as:
Where, R0 represents category H0 decision domain; R1 represents the decision domain of category H1
When Q2 = α, the value of J is the smallest, then there is
Generally, the cost function of wrong decision is larger than that of correct decision.For observation samples, the likelihood ratio function can be set as:
When the value of Δ (x) exceeds the set threshold, it indicates that the target really exists; otherwise, it indicates that the target does not exist. The specific calculation process of the maximum likelihood estimation method is given below:
Where, q (x|θ1 ; H1) represents the probability density function of unknown parameter θ1. Similarly, the generalized likelihood ratio test can be expressed as
The constrained energy minimization method is a binary image processing method, which can effectively suppress external interference, but
It can only extract signals in one direction, and set the target as o, the minimum conditional filtering output is:
Where, v is the filter parameter v = (v1, v2, ⋯ v L ) T .
Acquire the edge information of the fixed value single image, and conduct binary processing for the adaptive image. The formula is:
Thus, the binary image processing of relay protection equipment setting sheet is completed.
Fixed value single cell segmentation and character AI recognition
After the above preprocessing of the fixed value sheet photo is completed, the following table is divided to separate each customized single cell image. The key is to obtain the horizontal and vertical lines in the table, and then obtain the table intersection diagram and the outline of the cell.In this paper, based on binary processing, gray image enhancement method, according to the gray histogram, the horizontal or vertical lines are retained. The horizontal and vertical line graph of the table obtained from the local image processing of the fixed value sheet is then processed with “AND” and “Overlay” to obtain the intersection point graph of the table and the outline graph of the cell.
After scanning the intersection point graph of each row and column of the table to get the coordinate set of the intersection point, the cells are reconstructed according to the original graph according to the obtained intersection point coordinates, so that the cells are divided from top to bottom and from left to right. The accurate segmentation of complex cells can be completed by processing the fixed value sheet image according to the above steps.
Character recognition of relay protection equipment setting sheet based on OCR in AI technology
OCR (Optical Character Recognition) is a technology based on AI (Artificial Intelligence). OCR involves the use of computer algorithms to recognize and extract text from images. OCR technology usually involves the combination of computer vision technologies, such as image processing and machine learning algorithms, which are trained on large data sets of text and image data.These algorithms can learn to recognize various fonts, styles and sizes of text, and distinguish between text and non text elements in images.
(1) Text Cut
After the fixed value single cell segmentation, the fixed value single image is a whole, which contains the space between words. Therefore, to detect the text in the image extracted from the fixed value single cell image [19], first separate the single Chinese characters in the relay protection equipment fixed value list from the whole, which is the task of character segmentation.
In word segmentation, search the left and right boundaries of a single word in each line of text from left to right, and cut out the single word or punctuation marks. For Chinese character text lines, because there are left and right separated characters, wide and narrow characters, and the upper line is often mixed with English, numbers, symbols and inter character stains, which makes character segmentation much more difficult, so character segmentation can be roughly divided into two passes: First, find the left and right boundaries of fixed value single characters, symbols or radicals; The second is to merge radicals into complete text Chinese characters.
Maximum width backtracking segmentation algorithm is adopted. This algorithm is relatively simple and has certain adaptability. First, according to the characteristics that Chinese characters in the relay protection equipment setting sheet are square characters, the average line width is taken as the word width reference value of k:
The algorithm steps are as follows:
Step 1: In j
a
≤ j ≤ j
a
+ k
m
calculate the first in the range
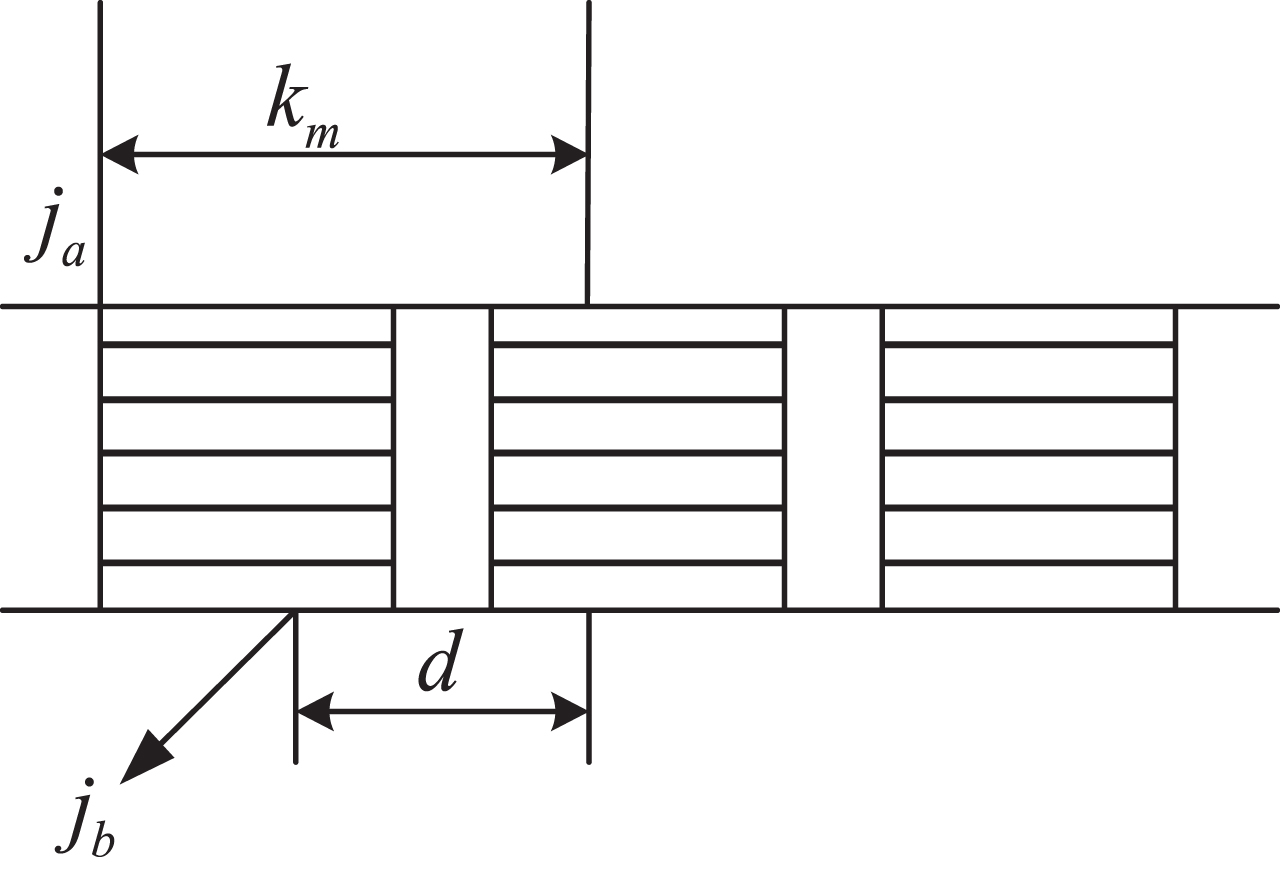
Maximum width retrospective segmentation algorithm.
Step 2: If j a - j b < δ (δ is determined by experience), that is, if it is less than a minimum character width, it is noise interference, not counting, and then go to the third step. Otherwise, go to the fourth step;
Step 3: In the j
a
≤ j ≤ j
a
+ k
m
calculate the first in the range
Step 4: Use the dictionary to match the above cut image. If the matching is successful, write down j b , turn to the sixth step, otherwise turn to the third step;
Step 5: In the j
a
≤ j ≤ j
a
+ k
m
get the result within the range
Step 6: From j b the vertical line is the dividing line (right boundary) of the text j width of the word j a ∼ j b .
Step 7: Start from j
b
, calculate
This completes word segmentation.
(2) Text extraction
The current OCR text extraction system adopts a grid based feature extraction method combining two methods [20]. The specific method is to extract two statistical features. One is the grid feature, which converts the outer border of the character to 32 * 16 pixels through normalization processing (the experiment shows that this size is the optimal value in terms of both character recognition speed and correct recognition rate). Then divide the relay protection equipment setting sheet image into 3 * 3 = 9 cells, and count the number of black pixels in each cell to form a 9-dimensional vector; The other feature is the intersection feature. At the place where the horizontal and vertical directions are divided into three equal parts, make horizontal and vertical lines to pass through the character, and see the number of times it intersects with the edge of the character. In this way, four more values can be obtained, and a total of 13 dimensional characteristics can be obtained [21, 22].
The 13 dimensional feature is extracted and saved. When a new character is encountered, the feature vector of the character is compared with the saved standard feature vector. The character with the smallest difference is the character.
After the information on the relay protection equipment setting value sheet and device setting value sheet is stored in the database, the setting value data can be read for automatic verification. It should be noted that for the setting sheet, the setting value includes the original setting value and the new setting value; For the device setting sheet, the setting values usually include the setting values of different groups such as Group 1 and Group 2. In addition, even if it points to the same fixed value, the fixed value names on the two kinds of fixed value sheets are not identical. Therefore, according to these characteristics, the automatic check steps are adjusted as follows:
Step 1: For the setting sheet, the new setting value is preferred. If no new setting value is given, the original setting value is selected;
Step 2: For the device setting sheet, select the current group setting according to the control word;
Step 3: Match the fixed value names in the two fixed value sheets according to the established key vocabulary;
Step 4: Compare the setting values successfully paired. If the setting values are the same, “normal” will be displayed; if the setting values are different, “warning” will be displayed. Otherwise, it is deemed that the “abnormal” signal cannot be recognized [23].
The overall process of automatic verification method for relay protection equipment settings is shown in Fig. 2.
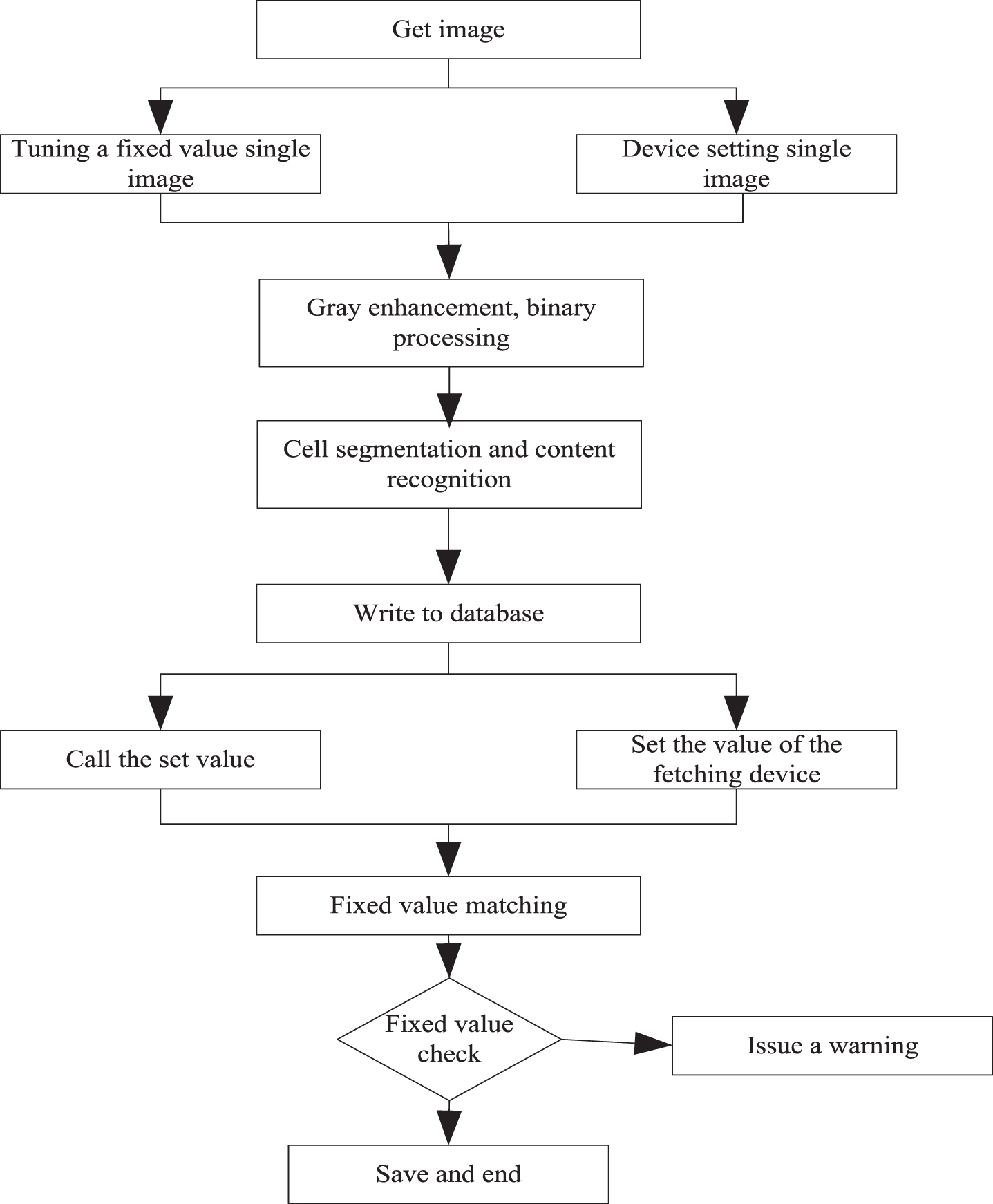
Overall flow of automatic check method for setting values of relay protection equipment.
Experimental objects
The data of the electric power bureau located in southern J city were used to carry out the automatic verification experiment of relay protection equipment settings. The power supply area of the electric power bureau in this city was 16535 square kilometers. In 2010, 3.32 million power users were found. By the end of December 2010, the power grid had 330 public substations of 35 kV and above (including 5 500 kV, 44 220 kV and 186 110 kV); The transformation capacity of 35 kV and above is 44.8694 million KVA, and the line is 7260 km. In 2010, 48.393 billion kWh was sold; The maximum load of the whole society is 8.526 million kilowatts, and the maximum load of the power supply network is 7.977 million kilowatts. Due to the wide coverage of the city’s power grid and the large installed capacity, the city also pays more attention to relay protection. The relay protection equipment used by the largest power station in the city is all equipment produced in three years, which has a good ability in relay protection.
Experimental data
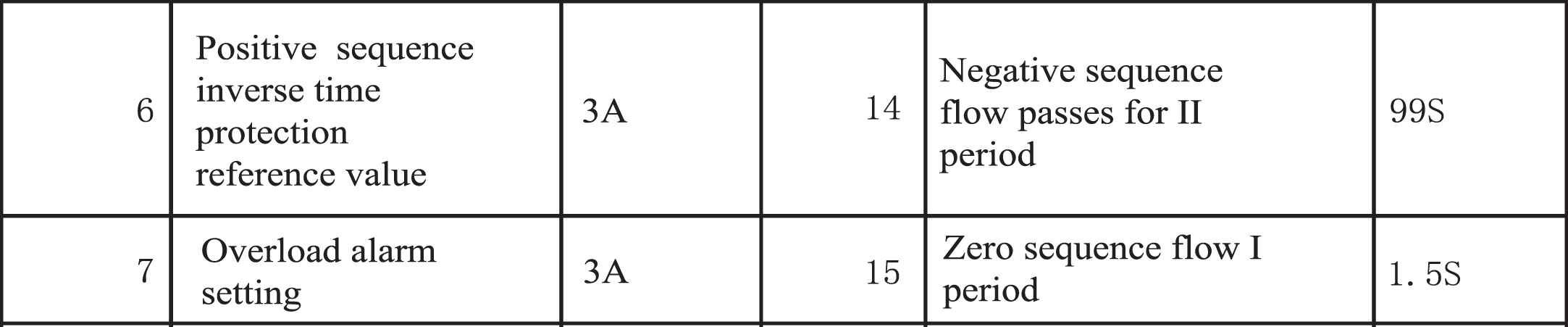
The collected setting value sheet information of a relay protection equipment is shown in Fig. 3.
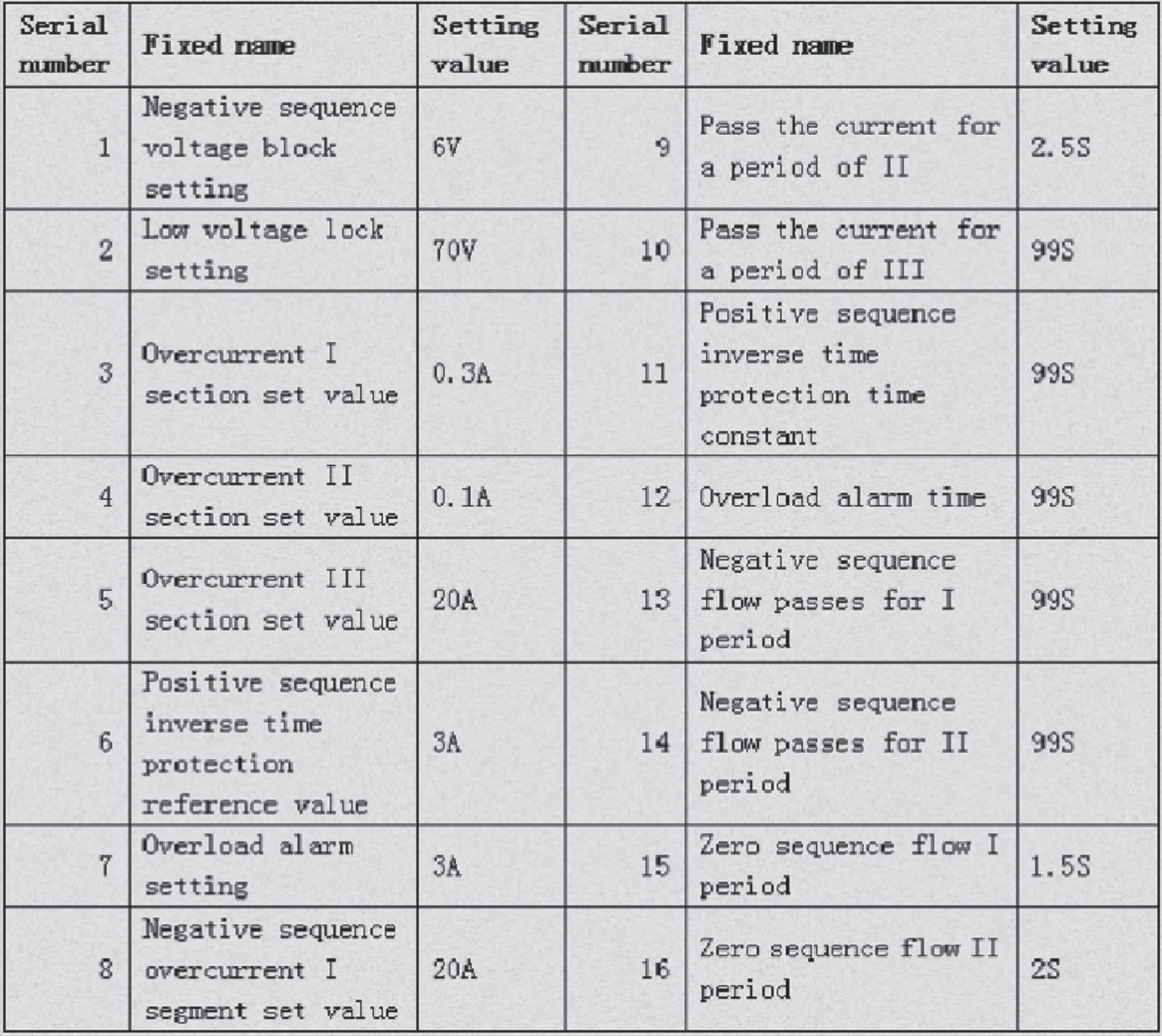
Set the fixed value single photo.
In order to verify the actual effect of the pre-processing in this paper, partial processing is carried out on the images captured by the setting value sheet. The results before and after processing are shown in Figs. 4 and 5.
Partial fixed single image before processing.
Partially fixed single image after preprocessing.
It can be clearly seen from Figs. 4 and 5 that the text before preprocessing is fuzzy and difficult to recognize. If the text is extracted directly, a large number of wrong words will be generated. However, the result of the preprocessing method in this paper is clear in Chinese characters, with obvious differences between the background and the text, which can reduce the difficulty of subsequent text extraction and thus improve the efficiency.
Because the method in this paper divides cells and extracts the text of each block after cell segmentation, the cell segmentation result is shown in Fig. 6.
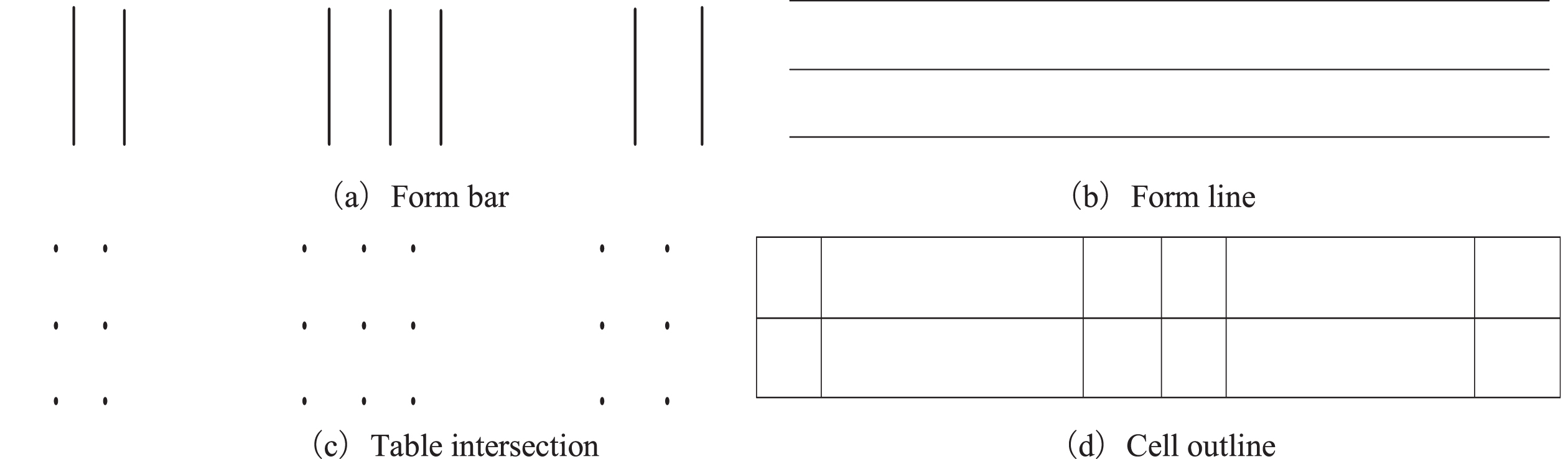
Cell segmentation results.
It can be seen from Fig. 6 that the segmentation result of the fixed value single cell using this method is obvious, and the horizontal and vertical lines of the cell can be clearly and accurately segmented. After the horizontal and vertical lines of the table are segmented, the intersection point of the table obtained by “and” and “superposition” operation is accurate. The seventh row is used for table segmentation, and the result is shown in Fig. 7.
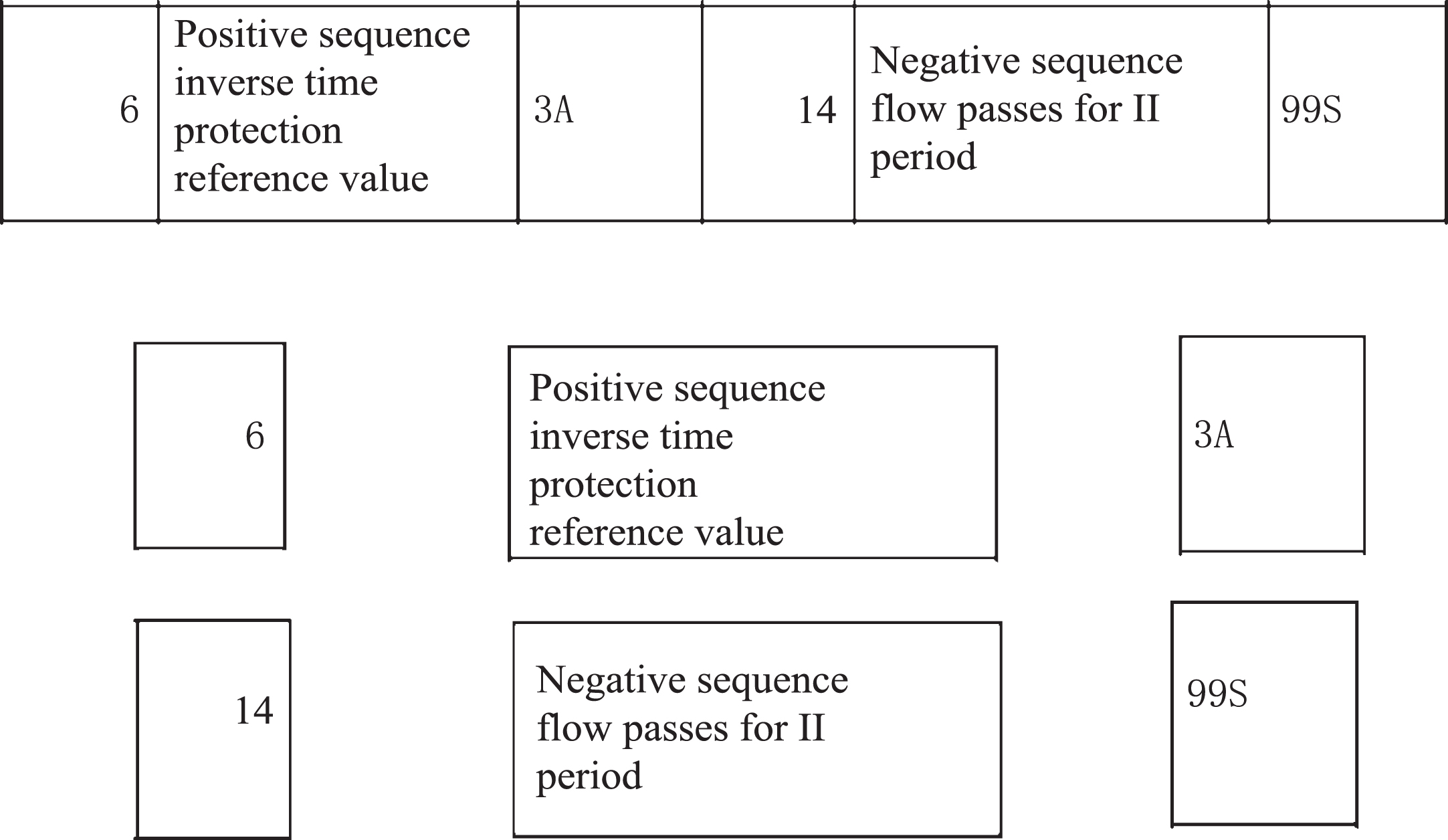
Table row 7 split results.
It can be seen from Fig. 7 that the method in this paper is accurate in the table segmentation, instead of segmenting the characters that do not belong to the cell. After the fixed value sheet table is segmented, the next step is to extract the text from the segmented fixed value sheet table. The fixed value sheet table segmentation can effectively reduce the amount of text extraction from a single fixed value sheet, reduce the time of text extraction from each fixed value sheet, and improve the accuracy. Taking Fig. 5 as an example, the method in this paper is used for text extraction, and the text extraction results are shown in Fig. 8.
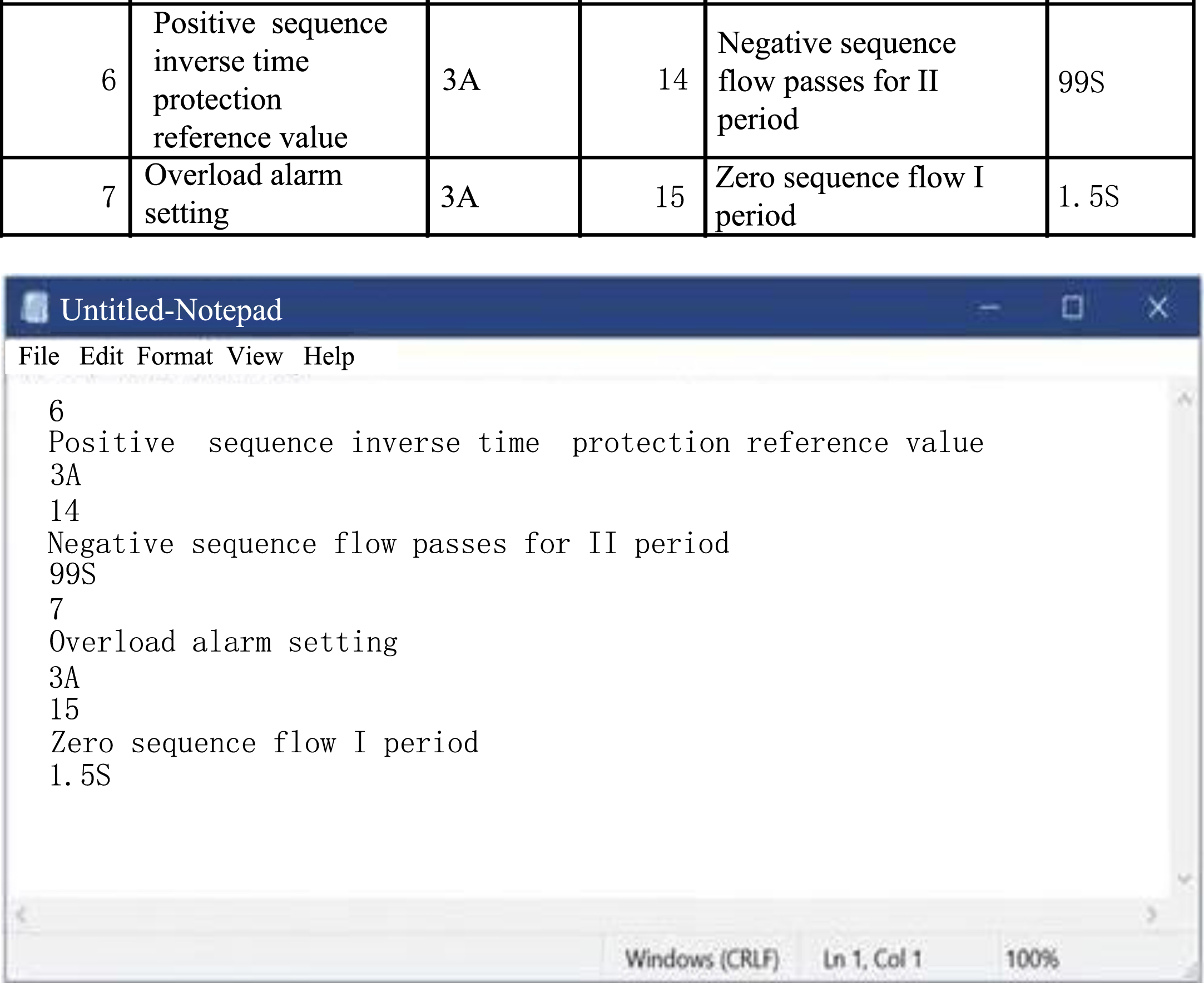
Text extraction results are shown in the figure.
As can be seen from Fig. 8, this method can be used to extract characters efficiently, quickly and accurately. After statistics, the recognition rate of 3000 Chinese characters in daily use can be more than 99% after preprocessing with this method, and the errors are mainly part of similar characters.
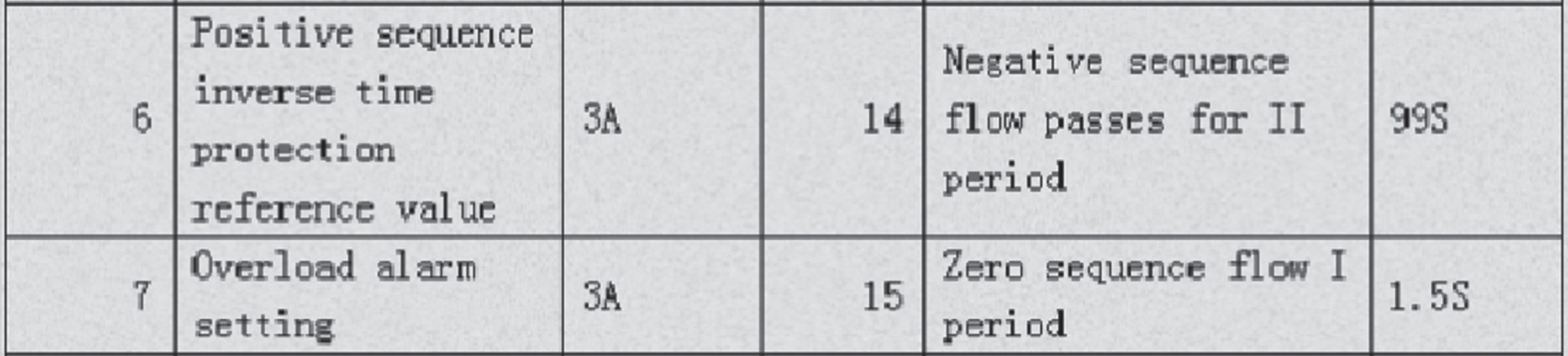
It can be seen from Fig. 3 that for the setting value sheet, the setting value in one line includes the information such as serial number, name, unit, setting value, etc. Therefore, according to these characteristics, the recognition results are scanned line by line to determine the location of the fixed value information (row and column) and stored in the database. For Fig. 4, the storage results of the row setting values in the database are shown in Table 1.
Sets the store results
This completes the storage of relay protection equipment settings. Since the settings of different protection equipment are different, it is necessary to store the settings of various relay protection equipment. The storage method is the same as the above example.
Store all the settings of a relay protection equipment in the database for automatic verification of settings. The results after automatic verification are shown in Table 2.
Results of automatic check of fixed values
It can be seen from Table 2 that the results of the comparison notice setting sheet and the device setting sheet are basically normal, and errors in the zero sequence voltage of the failure protection are also detected during automatic verification.
During the pressure test on our party, 307 sets of setting sheets were checked, with a total of 7024 items, including 20 main relay protection equipment. The check results are shown in Table 3.
Check result of setting value of relay protection equipment
It can be seen from Table 3 that the method in this paper can still maintain a very high accuracy rate when checking the setting values of a large number of relay protection equipment. The reason for the check error is that the text is still unrecognizable after the setting sheet condition is too poor, which leads to problems with text extraction.
In order to further verify the effectiveness of the proposed method, the non-fragile consistency of the proposed method is compared with the adaptive event-triggered fuzzy positioning control based on actuator saturation hybrid attack and the nonfragile consistency of the nonlinear multi-agent system based on aperiod memory sampled data control. The test index is check accuracy, and the specific comparison results are shown in Table 4.
Comparison of check accuracy of different methods /%
As can be seen from Table 4, the verification accuracy of the proposed method is the highest of 98.15%, and the non-fragile consistency of the adaptive event triggered fuzzy positioning control method based on actuator saturation hybrid attack and the nonlinear multi-agent system based on non-periodic memory sampled data control is the highest of 89.36% and 87.46%. Compared with the two literature methods, The verification accuracy of this method is higher.
It can be seen from the experiment that the method in this paper uses gray enhancement and binary method to preprocess the captured relay protection equipment setting sheet, so that the image clarity, contrast and other aspects are greatly improved. Secondly, for the cell segmentation of the setting sheet, using the method in this paper to segment the cell, the segmentation result is accurate, and there will be no data segmentation error resulting in data loss and other problems. And the OCR text extraction technology in AI technology is used to train it locally with the constant value sheet. It can be seen that the image of the constant value sheet after pretreatment in this paper can basically achieve 100% text extraction accuracy unless the document itself is too poor. Store the extracted text in the database, check the results of the notification setting sheet and the device setting sheet in the database, and give the results.In the future development, the algorithm of image gray enhancement and AI recognition will be further improved and optimized to improve accuracy and robustness. More advanced image processing techniques can be studied, including denoising, contrast enhancement, edge enhancement and other methods, as well as deep learning models and training methods to improve AI recognition algorithms. Build larger and more diverse training datasets covering image data from different scenes, angles and device types. At the same time, specific difficult situations (such as blur, illumination changes, etc.) are processed and learned.By introducing AI recognition technology, the method can realize the automatic check of the fixed value of the relay protection equipment, greatly improve the efficiency and accuracy of the check, and reduce the manual operation and error. Using image gray enhancement technology can improve the quality and clarity of the image, and is conducive to accurately identify the information in the setting table of the relay protection equipment, and then compare and check. However, this method depends on the consistency and standardization of the setting table of the relay protection equipment. If the format of the table of different models or specifications is different, it may lead to identification and verification errors.
Footnotes
Acknowledgments
This study did not receive any funding in any form.
Conflicts of interest
The authors declare that they have no competing interests, and no financial or other conflict of interest between the work and that of the authors.
Data availability statement
The datasets generated during and/or analyzed during the current study are available from the corresponding author on reasonable request.
