Abstract
IT infrastructures are indispensable parts of today’s organizations, and keeping them secure is very important for successfully running the business. Due to the complexity of information infrastructure and network topology, traditional security measures no longer meet the security needs of current enterprises. Therefore, the holistic information security management analysis method has received extensive attention. An important task of these holistic security analysis methods is to analyze the value of assets so that IT managers can effectively allocate resources to protect the information infrastructure. Most of the current asset valuation methods are based on analyzing the dependencies between assets. In some cases, the dependencies are not easy to find, which makes the evaluation results inaccurate. Therefore, we propose model with analytic network process network (ANP) to evaluate the value of assets. This method not only considers the security factors and considers the importance of the assets to the business as well. It can evaluate the value of the assets and prioritize them, which can help the system administrator in making the decision for security enhancement.
Introduction
Today, information technology (IT) has brought great convenience to people’s lives. The rapid development of the IT sector leads to accelerated application and introduction of digital innovations [1]. However, information systems are frequently exposed to various types threats which can cause different types of damages [2]. Security countermeasures such as firewalls, antivirus software, data encryption, etc., aim to address specific security problems. As technologies evolve, threats are more sophisticated to detect [3]. These point solutions no longer meet the security requirements of applying in large-scale networks. In order to locate the security loopholes proactively, holistic approaches are needed in information security management [4]. Under such demands, technologies such as information security risk assessment (ISRA) and network security situational awareness (NSSA) arise and have been widely used. These methods analyze the information infrastructure or networks integrally to provide the decision-makers of the firms with a comprehensive security status. One of the main tasks of these holistic approaches is prioritizing the information asset, which can give the system administrators an indicator of how to distribute the limited resource to defend the information asset more suitably. A standard way of asset value analysis is examining the dependencies between assets, and assets with a high degree of dependence have relatively higher values. The methodology of this type of approach is very efficient and intuitive. However, due to the complexity of the network topology, the dependencies between assets become challenging to analyze. Some potential dependencies between assets are challenging to discover and may lead to inaccurate evaluation results. Besides, we also noticed that an asset may have different values in the context of different business processes [5]. Therefore, considering the business factor is necessary in the asset valuation process. For the above reasons, we design a method for prioritizing the asset value based on analytic process network (ANP). The method considers the firm’s security requirements for the assets on the one side and take account into the asset’s importance to the firm’s business as well. Through such an evaluation method, IT managers can get rid of the tedious work of analyzing the dependencies between assets and evaluate the value of assets more reasonably from two aspects of security and business. System administrators can also design resource allocation plans more effectively to protect information infrastructure based on the assessment results. The rest of the work is organized as follows. Section 2 reviews the related works and explain the initiative of using ANP to evaluate the asset value. Section 3 elaborates on how to build the model with security and business criteria and assesses the importance of assets for each sub-criterion. Section 4 discusses the generation method of the supermatrix and analyzes the evaluation process of the asset value with the example. Section 5 concludes this work.
Related works
Resources are not limitless when it comes to cyber defence. Making decisions on where to focus one’s cyber defence resources can be difficult if there are no clear priorities [6]. Therefore, in the field of information security and network security, appropriately evaluating the asset value is a critical issue and has received continuous attention. In [7], Since routers connect the corporate network with multiple simple networks, the method proposed by the authors is to check the function dependencies of each asset based on their network connection. The degree of dependence is expressed as a real number between 0 and 1, and the asset value is accumulated from the source asset to the final supporting asset. Kim and Kang propose a method to determining the criticality of assets in cyber defense, because it is mainly used in the military area, it first decomposes the commands hierarchically and considers the degree of dependency of the assets and finally uses TOPSIS to calculate the value of the assets [8]. Loloei et al. propose a model to analyze asset value from two aspects. One is an independent value, and the other is a dependent value. The independent value is determined by the cost of the asset and its importance to the business. The dependent value is calculated by the two parameters: the asset being depended on and the corresponding degree of dependency [9]. Leung defines a fuzzy inference system to analyze an asset’s static and dependent value according to its type, service, and support operations. The sum of the static value and dependent values is the asset’s final value [6]. Su et al. construct an information network risk assessment model based on a neural network. In order to apply the model, since the asset value is the important input of the neural network, the authors use the analytic hierarchy process (AHP) to evaluate the value of the assets [10]. The authors also apply AHP to rank the importance of assets. First, the model evaluates the weight of the security criteria based on expert opinion and then computes the information system’s value with these weights [11]. The above methods can be divided into two categories. One is based on the analysis of dependencies between assets. This kind of method needs to find the complete dependency chain of each asset, so the evaluation process is cumbersome for the security practitioner. The other is to use the pairwise comparison of the importance of assets to determine the value, but the evaluation criteria of these methods do not address both security and business aspects. Therefore, we propose a evaluation model with ANP to evaluate the value of assets according to the firm’s security and business requirements.
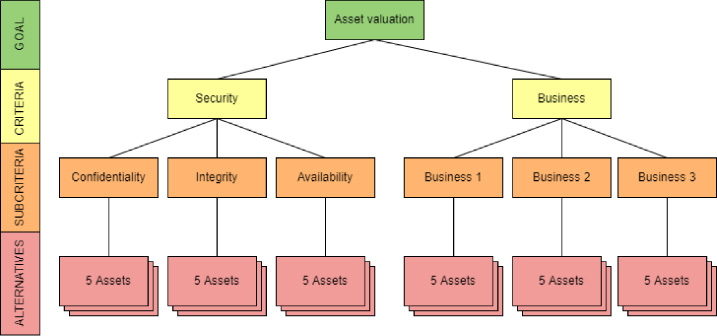
Example of the evaluation criteria of the information infrastructure with 5 assets and 3 business.
ANP is a very efficient multi-criteria decision making method and is one of the most applied decision approaches in many research fields. ANP is derived from AHP. Similar to AHP, before the evaluation with ANP approach, appropriate decision criteria must be selected for constructing the evaluation model. For today’s enterprises and organizations, the role of their information infrastructure is to accomplish the exchange of information securely and achieve the business goal. Therefore, besides the security requirements, business factors need to be considered when analyzing the state of asset value. Our evaluation model also forms assessment criteria from security and business perspectives. We choose confidentiality, integrity, and availability as security criteria. These security metrics are called the CIA triad, which is commonly used in information security analysis. For example, Yang et al. apply deep learning method to assess the network’s security risk and use the CIA triad to evaluate the impact for each type of attack packet [12]. As we mentioned before, an asset has different values for different businesses. Accordingly, to emphasize the assets in the network for different businesses, our model should have the ability to distinguish the importance of the node for every business. Thus, we use each business as a sub-criterion for evaluating the importance of nodes for business criteria. For instance, If the target information infrastructure has five assets and supports three businesses, the structure of the evaluation model is as shown in Fig. 1. According to the evaluation model, the system administrator first analyzes the business and identifies the assets, and then compares the alternatives under each criterion. For the security sub-criteria, the assessor must determine the importance of each asset to the corresponding security requirements of the enterprise. For example, a server storing customer order information has a higher confidentiality requirement than a personal computer used by an ordinary employee. Thus, the server is more important than the computer under the sub-criterion Confidentiality. For the business sub-criteria, each business is a sub-criterion, and the assessor must analyze the importance of each asset to the business.
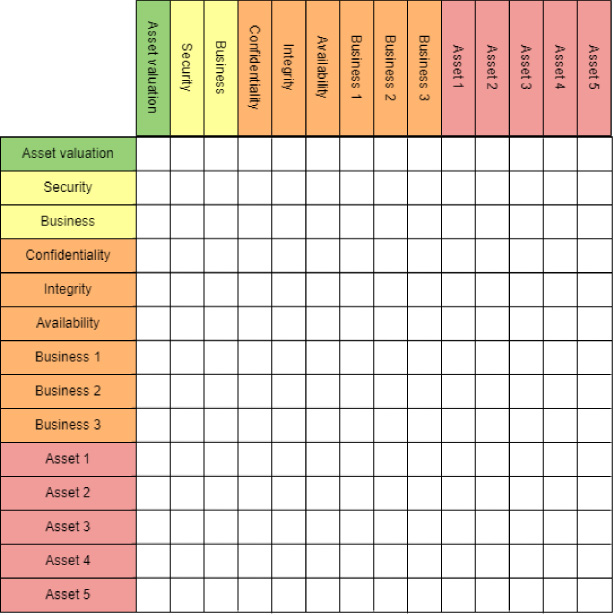
Supermatrix for evaluation of the example information infrastructure.
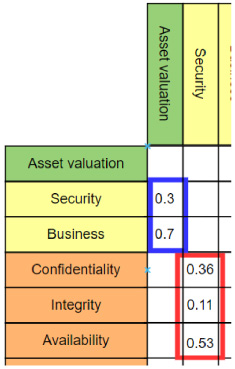
Security and Business weights assignment of the example information infrastructure.
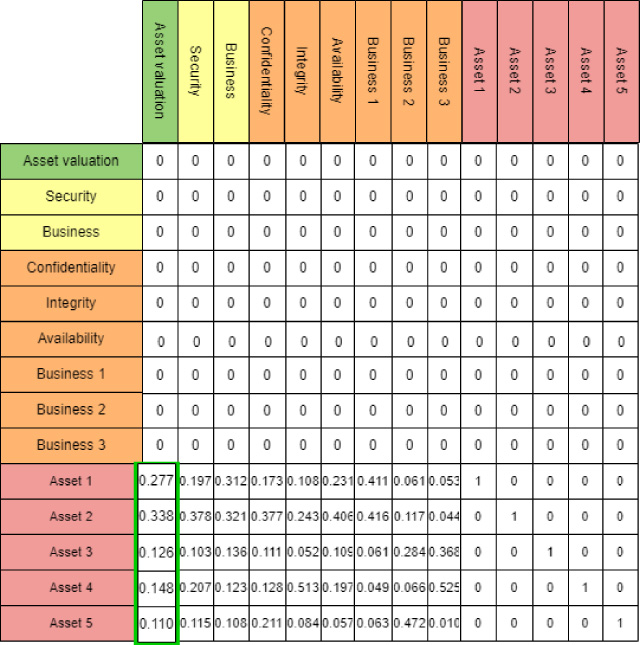
Asset valuation result for the example information infrastructure.
The essential part of applying ANP for evaluation is to construct a supermatrix, which contains the weight assignment of each criterion to its alternatives. For our example in the previous section, the supermatrix we want to construct is shown in Fig. 2. For each column, we need to compare each alternative under the criterion corresponding to the column and then fill the weights for all the alternatives. For example, suppose we believe that for the enterprise, the importance of business operation is 0.7, and the importance of ensuring information security is 0.3. Therefore, in the supermatrix, the entry corresponding to Business criterion in column Asset valuation is 0.7, and the entry corresponding to Security criterion is 0.3. The weights assignment of security and business is shown in the blue rectangle in Fig. 3. Similarly, under the criterion Security, if availability is the most important security requirement to the enterprise and its weight is 0.53, next is confidentiality, its weight is 0.36, and at last is integrity, its weight is 0.11. The weights assignment of sub-criteria Confidentiality, Integrity and Availability is show in the red rectangle in the Fig. 4. When there is no direct relationship between the criteria represented by the column of the supermatrix and the alternatives represented by the row, the value of this entry is 0. In addition, the value of the entry corresponding to the same asset is 1. Following the rule of above operation, suppose we can get the supermatrix W of the example information infrastructure as shown in Eq. (1).
In this paper, we proposed an asset valuation model based on ANP decision method. It can prioritize the assets in the information infrastructure. The model can evaluate the value of assets from both security and business perspectives. The evaluation criteria of the model are mainly divided into two parts: security and business. Security criteria are evaluated from three aspects: confidentiality, integrity, and availability. The sub-criteria of the business criterion are all businesses supported by the target information infrastructure. The system administrator analyzes the importance of the related alternatives according to each criterion and fills the supermatrix. Finally, the limited supermatrix can be computed with the supermatrix, and the asset value is obtained as well. The method does not need to consider the complex dependencies between assets and can obtain comprehensive evaluation results of asset value. This method provides a basis for system administrators to evaluate the risk of information infrastructure and allocate protection resources.
