Abstract
With the development of cloud computing technology, cloud computing has been applied in various fields, but there is a lack of research in the Massive Machine Type Communication (mMTC) scenario. This article analyzed wireless communication reliability solutions in cloud computing mMTC scenarios to address this issue. Using the method of cloud computing, this article analyzed the reliability of wireless communication schemes and verified the effectiveness of the algorithm through credibility judgment and algorithm convergence characteristics under the guidance of wireless communication schemes. By analyzing the application of cloud computing in wireless communication solutions, this article analyzed the effectiveness of wireless communication solutions in the experimental section by comparing the error rate, success rate, and convergence of various algorithms. Through experimental analysis, it was found that the implementation success rate of chaotic particle swarm optimization algorithm was 5% higher than that of adaptive particle swarm optimization. The results indicated that cloud computing was well applied in wireless communication networks, thus providing reference significance for the application of cloud computing in other communication fields.
Introduction
Cloud computing is a vast and complex network that contains millions of cloud resources. In this context, how to effectively obtain trusted cloud resources and deploy them on trusted cloud resource nodes is an important guarantee for ensuring their efficient operation. In terms of wireless communication, cloud computing establishes a fault repair model for cloud nodes through cloud resources, as well as a data transmission model for cloud networks. It analyzes the credibility methods and applications in wireless communication networks for cloud computing.
As an internet technology, wireless communication networks have been analyzed by many experts and scholars. Emmanouil Skondras and others described a network slicing scheme for 5G-VCC systems aimed at improving the performance of modern vehicle services. They considered the QoS perceived by each user for its services and the energy consumption caused by each access network on user devices. Subsequently, it estimated the satisfaction level of user service by considering perceived QoS and energy consumption. If the estimated satisfaction level is higher than the predefined service threshold, allocate necessary resource blocks (RBs) from the current access point (PoA) to support the user’s service [1]. Emmanouil Skondras and others proposed a new VHO management scheme for 5G-VCC systems. Whenever user satisfaction falls below a predefined threshold, consider the vehicle’s speed, network characteristic standards (such as throughput, delay, jitter, and packet loss), and provider policy standards (such as service reliability, security, and price), initiate VHO and perform network selection. His proposed scheme uses the linguistic values of VHO criterion attributes represented by interval valued pentagonal fuzzy numbers (IVPFN) to express information using membership intervals [2]. The fifth generation (5G) in car network supports various services with strict Quality of Service (QoS) constraints. Network access technologies such as LTE Vehicle to Everything (LTE-V2X) and IEEE 802.11ac/ax provide users with network access, while Software Defined Networking (SDN) provides centralized control over heterogeneous network environments. In this environment, each vehicle can provide multiple services for multiple passengers. Emmanouil Skondras and others described a network slicing scheme for 5G systems aimed at optimizing the performance of modern in vehicle services. Specifically, the throughput obtained by each user for their service was considered. If the available connection throughput exceeds the predefined service threshold, allocate necessary telecommunications resources from the current access point (PoA) to support user services [3]. Shi Yanjun analyzed communication technology, conducted research on the integration of internet mobile communication and collaborative intelligent systems, and analyzed the main applications in internet networks, such as enhanced mobile networks and large-scale machine communication [4].
Qin Wei achieved collaborative manufacturing with wireless communication as the core through information processing technologies such as cloud computing, big data analysis, and intelligent sensing, thus providing enterprises with a brand new information service with independent intellectual property rights. He also made a comprehensive review of the current development from the aspects of reference architecture, key technologies, related applications, and challenges, and found that wireless communication was used to support various applications of Industrial Internet [5]. Tong Lili explored the architecture of wireless communication. Starting from four different types of business requirements, he focused on discussing how to improve user experience in a network environment [6]. Lin Mengting discussed the role of wireless communication technology in various fields and analyzed resource scheduling methods for mobile networks. In addition, the application of intelligent technology to the mobile internet put forward new requirements for the development of the mobile internet, thus providing new technological support for the development of the mobile internet [7]. Wireless communication had a wide range of applications in many fields, but there was a lack of application of cloud computing in wireless communication [8].
Some experts and scholars have analyzed cloud computing technology and believe that cloud computing brings convenience to data processing. Ma Zheng analyzed the Internet from the perspective of cloud computing technology. With the popularization of the Internet, many future Internet of Things technologies were widely applied in many fields. Research was conducted from three aspects: the physical layer, media access control layer, and network layer, all of which would have a significant impact on the latency and reliability of wireless Internet of Things [9]. Ali Hafiz Munsub utilized cloud computing for massive electronic medical record transmission and processing, and analyzed trusted health service systems and configuration computing communication systems [10]. Sengan Sudhakar analyzed the application of cloud computing in directional aspects and found that cloud computing could achieve information transmission through information transmission from sender to receiver. Therefore, it was necessary to integrate and improve intrusion prevention systems based on data mining technology [11]. Cloud computing provided new ideas for wireless communication. However, due to the previous lack of research on wireless communication, further analysis was needed.
Through the application of cloud computing in wireless communication reliability planning research, this article analyzed cloud computing and discusses wireless communication reliability planning in cloud computing mMTC scenarios, and studied wireless communication models. Through experimental research, it was found that cloud computing could more quickly regulate wireless communication reliability planning. Cloud computing could combine the convergence characteristics of algorithms to ensure the smooth implementation of wireless communication reliability solutions. The reliability analysis results of cloud computing in the field of wireless communication laid the foundation for future applications of cloud computing in other fields [12].
Evaluation of cloud computing technology
Cloud computing technology composition structure
With the continuous upgrading and development of cloud computing technology, in cloud networks, users’ data resources cannot be fully controlled by users, which brings security risks to information privacy. The security of user information has become a hot issue of concern. If more technology popularization is to be achieved, privacy security is a problem that needs to be addressed. It is necessary to proactively develop a set of measures that can ensure both the security of user data and user privacy, so as to promote the healthy development of cloud computing technology.
The high confidentiality and privacy of cloud computing technology would become an important feature of wireless communication networks, and it is also the most concerned issue in the current field of wireless network research. Many scholars have defined the main potential characteristics in wireless networks and explored the cloud computing technologies needed in wireless networks [13]. Due to the sharp increase in healthcare costs, resource imbalance, inadequate management of the healthcare system, and inconvenience caused by healthcare services, cloud computing methods can be used to solve these problems [14]. Cloud computing technology can process data transmission in wireless communication, thus bringing innovation, necessity, serviceability, and functional advantages to the Internet of Things technology [15].
Cloud computing has some unique features. Therefore, compared with traditional computing methods, it has a very obvious technical feature: The scale of data processing and services is huge, and such large-scale computing would continuously demonstrate its numerous resource advantages to the outside world. The cost setting of cloud computing varies with its economies of scale. When it generates positive benefits, its costs would significantly decrease; cloud computing mainly connects data to virtual platforms built on the network, and virtualizes all behaviors, thus packaging available functions with different programming commands to continuously provide users with more business. This type of business is not constrained by specific space and time, and users can obtain information from different locations and terminals but do not need to know the location of information providers in the cloud. Cloud computing is based on huge data storage space to store all information, while also providing virtualization services for cloud resources [16]. Therefore, each service needs to be dynamically configured and expanded in order to design specialized services for different users.
Cloud computing security issues
With the continuous popularity of cloud computing, its security has become increasingly important. The network structures at various levels such as system layer, network layer, transmission layer, and application layer all have potential security risks. Many experts have explored some special security issues in cloud computing. At present, cloud computing business is mostly achieved through cloud service providers to undertake customers’ information processing and data computing needs, which greatly reduces the burden of data computing and storage on customers. On the other hand, all data and information of users would also face significant security threats, and users cannot have complete control over their own data and information.
Cloud service providers would provide a large number of security, billing, and other systems based on cloud computing. The security of cloud services itself is also an important component of cloud platform security. Especially cloud computing systems developed by cloud computing service providers with three major features: identity authentication, access control, and behavior auditing, pay more attention to protecting user personal information from multiple perspectives and levels. If users want to use cloud security management software in their own enterprise with peace of mind, it must have a certain level of security. To achieve this security, it is necessary to resort to other effective ways or methods. Obviously, understanding the role of security management software in this process can better achieve data supervision.
Cloud computing, like many technologies, is designed to provide users with better services, but it also brings convenience to those with ulterior motives. For example, after network hackers invade the target host of cloud computing, they would use this as a stronghold to launch repeated attacks on merchants and enterprises specialized in providing cloud computing services. In this case, it is highly likely that the user would suffer an unknown cost loss and occupy network resources. After in-depth analysis of the characteristics of cloud computing, hackers can freely use high dynamic characteristics to establish some non-standard sites in cloud computing systems. Only by actively improving regulations in areas such as cloud services can a scientific, reasonable, and feasible cloud service security regulation system be constructed. From the above points of view, the security of cloud computing and the confidentiality of user data involve a wide range of fields and many levels. Therefore, it is urgent to study the issue of data confidentiality in cloud computing. The computing principle of cloud computing is shown in Fig. 1.
Computing principles of cloud computing.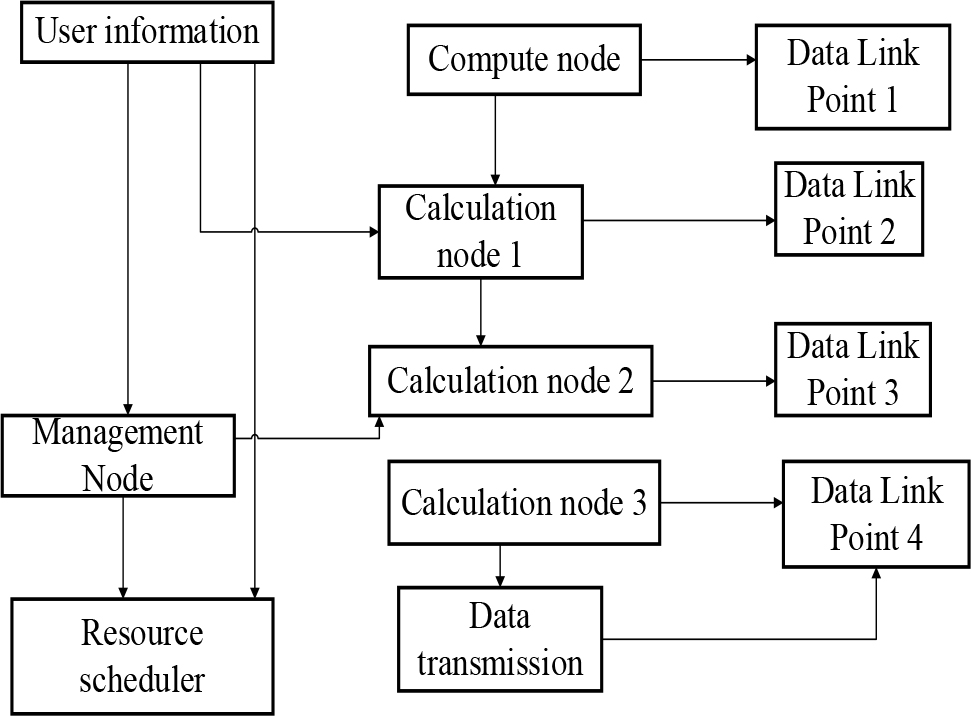
The mMTC scenario analyzes the insufficient support capacity of traditional mobile communication for the Internet of Things and industrial fields. Low power interconnected environment refers to perception and data collection, such as smart cities, environmental monitoring, smart homes, forest fires, etc. Its characteristics are small data packets, low power consumption, and large connection scale. The mMTC scenario has a wide distribution and a large number of nodes, which requires both support point access capacity and access density, as well as extremely low energy consumption and price.
As the main application scenario of cloud computing, smart cities have a wide range of accessible objects, including transportation facilities, water, electricity, etc. There are tens of millions of accessible objects, and a single access object requires very little information to be transmitted. Environmental monitoring has the characteristic of low energy consumption. It mainly utilizes various types of sensors to collect information, and has the characteristics of being insensitive to transmission delay, transmission rate, and can achieve extremely high connectivity density. mMTC is one of the three main application areas of the Internet, and wireless networks can carry millions of terminals, which is of great significance for the development of future Internet technology. The Internet has strong interconnectivity and can quickly promote the deep integration of multiple vertical industries such as smart cities, smart homes, and environmental monitoring [17].
The large-scale Internet of Things relies on the super strong connectivity of the network and promotes deep integration of multiple fields. In the context of the Internet of Things, utilizing various sensors and terminals can establish an intelligent lifestyle, which would overturn people’s way of life. mMTC has a higher data rate and is insensitive to latency. It has cheaper terminal costs for deployment, and has higher requirements for lifespan and reliability. Its connectivity covers every corner of people and reduces the price of the terminal, which extends the battery life of the phone and improves its stability.
The Internet of Things is the core content of the “Fourth Industrial Revolution” in recent years, which has been frequently mentioned by people. Now, the Internet of Things has become the most popular topic. In the future, the Internet of Things would completely change people’s lifestyles, work, entertainment, tourism, and even the interaction between government and business, thus achieving big data sharing. Among the three major applications of the Internet, the most critical issue is not the bandwidth performance of the network, but the reliability issue in the Internet of Things.
Internet technology is the core technology of networks for emerging applications such as intelligent driving and tactile networks. In the future, with the increasing demand for mobile internet applications and the Internet of Things, current wireless networks would not be able to meet this demand. The gap between supply and demand would drive the continuous upgrading of current wireless networks, thereby promoting the advent of the Internet era. From a demand perspective, it can utilize the network to transmit and share this information.
The mMTC concept is to interconnect billions of terminals, objects, and machines, even at long distances, such as sensors buried deep underground. To achieve this goal, it is not only necessary to provide more effective support for simple, low communication frequency devices, but also to improve energy efficiency. In the future, the Internet of Things industry would develop towards segmentation, differentiation, and customization, and its development speed would exceed people’s expectations. Internet technology is not just a change in speed. It would also bring tremendous changes to people’s thinking, business models, and future development.
Evaluation of the impact of cloud computing on wireless communication reliability
The security issue of wireless communication has always been a top concern for everyone. Especially some issues that arise in cloud computing environments require high attention and effective handling. Many experts have conducted in-depth analysis of the risks and challenges faced by computer networks in the cloud computing environment, and provided targeted improvement plans to address these issues. Nowadays, informatization has become an important factor, and all industries are developing based on computer networks. The vast amount of data and information on the Internet can bring companies the information they want, thereby promoting their sustainable development and accelerating the development of the entire society, thus making people’s lives more convenient. However, with the rapid development of big data, cloud computing, as a new form of internet development, has greatly affected the operation and security of computer networks.
Wireless communication technology can improve the reliability of drone driving ability. Cloud computing can analyze drones and enhance communication cooperation between drones, thus greatly reducing the constraints of drones in communication distance, network, volume, weight, power consumption, and other aspects [18]. Wireless communication technology can be applied to vehicle autonomous driving planning technology. Based on on-site research and the needs of end users, it proposes solutions for future development directions and problems faced. The research on wireless communication reliability in cloud computing provides a solution for vehicle autonomous driving [19].
Wireless communication has the characteristics of high speed and low latency, making it an ideal carrier for achieving multi terminal, high-speed, and highly reliable transmission. Although wireless communication technology has provided great convenience for mobile communication, research on mobile communication systems is still very scarce. Emerging wireless networks provide the foundation for future wireless communication technologies [20]. Wireless communication has also brought significant impacts to protection, control, operation, and planning, especially at the level of distribution networks [21]. In the future, how to use more technological means would be further explored in depth to better address the economic problems brought about by technology. Wireless communication technology is a decentralized and highly trusted method to maintain a trusted database. At present, cloud computing technology has been widely used in finance and other industries, and has broad potential value in production, education, scientific research, and other aspects [22].
Due to the large amount of data contained in cloud computing, in such a situation, if computer networks want to develop, corresponding changes need to be made. Therefore, cloud computing has also changed the control method of computer networks, resulting in computer networks being no longer a traditional network control method. Such changes would have a certain impact on the stability of computer networks.
With the development of cloud computing technology, its application scope is becoming increasingly broad. In such an environment, it is necessary to pay sufficient attention to network attacks and take effective preventive measures. The scale of network databases in the cloud computing environment is very large. For computer network systems, both storage and management are necessary. Only by effectively storing and managing them can the important role of building network databases be played. However, due to the massive amount of data, it poses a huge threat to computer networks, which has also become the biggest threat faced by computer networks in cloud computing environments. Therefore, improving the ability to prevent information security and taking relevant preventive measures is the key to ensuring information security in information systems.
Cloud computing has an extraordinary amount of data, which not only provides sufficient data support for the development of computers, but also brings new trends to the development of computers, and also brings new problems to database management. However, the current security performance of cloud computing systems is relatively poor, which poses significant risks to data processing in cloud computing systems. This is detrimental to the healthy development of data processing methods on the Internet.
Currently, in cloud computing environments, the security of stored data and information is relatively poor. Although there are many, the technologies used are roughly the same. Once breached, it would pose a great threat to the entire data. In addition, when a cloud system is breached, other cloud systems would also be attacked, thus posing a threat to the security of the entire computer network.
In the cloud computing environment, computer networks face significant challenges, and it is necessary to continuously carry out research and development of related technologies to address computer network security issues in the cloud computing environment, so as to improve the security of computer networks in the cloud computing environment. In addition, a corresponding data information management system should be established to make its management and use more organized, and corresponding classification management should be carried out for data to improve data security. At the same time, it is also necessary to encrypt the data in cloud computing to ensure its security. In this case, it is necessary to develop corresponding computer security related technologies based on the characteristics of cloud computing, and classify the database to make its management and use more standardized. In this way, the security threats of computer networks brought about by cloud computing can be effectively prevented, and the development of computer networks can also be further promoted [23].
Cloud computing is a necessary path for the development of the Internet. Therefore, in the process of controlling computer network systems, it is necessary to have a comprehensive understanding of cloud computing technology and effectively apply it to meet people’s needs to the maximum extent, and achieve the goals of convenient and fast computer networks.
In order to improve the security of computer networks in the cloud computing environment, it is necessary to have a deeper understanding of various threats and challenges in the cloud computing environment, and propose corresponding improvement measures accordingly, in order to improve the security of computer networks in the cloud computing environment. In order to ensure that the work in cloud computing is carried out on the target virtual machine, it is not only necessary to ensure the quality of work for each node in cloud computing, but also to ensure the communication quality between each node. In a cloud data center, it is assumed that there is a communication link between virtual machine resources S, and the transmission time
Among them,
It is assumed that the two maximum likelihood estimates of the parameters are
Starting from the random solution, and through fitness analysis and calculation, the fitness calculation formula is obtained:
Among them,
The start execution time in wireless communication should be greater than the latest execution completion time. Under the constraint conditions, the reliability of the scheme should be analyzed through fitness. The reliability planning of wireless communication solutions is as follows.
For wireless communication networks, fault problems can be divided into two types: accidental and abnormal. Under normal circumstances, fault problems can occur at any time, thus causing a significant impact on computer communication networks. Therefore, it is necessary to conduct research on the stability status of wireless communication networks and develop a complete reliability design plan, which should be combined with the current practical content situation to make it more sound and become a modern and advanced management model.
In the reliability management of wireless communication networks, the focus of monitoring and management can be placed on equipment and redundancy technology, which is linked to the current operational situation of the network system to determine the content and requirements of various aspects, thereby improving the operational level of the entire equipment. Advanced machines and technological methods must be adopted, and a large amount of experience must be accumulated on this basis to prevent computer communication network failures caused by machine aging. In the operation process of this system, it is necessary to manage costs reasonably and strictly manage and control equipment procurement, with the premise of reducing construction and maintenance costs, so as to maximize the optimization of the overall work mode. On this basis, combined with the current status of communication systems, a monitoring and protection system for modern communication systems should be established.
Wireless communication reliability planning experiment
This article analyzed the cloud computing simulation experimental platform through cloud computing simulation software, and tested and evaluated the designed simulation results. This article utilized discrete event simulation software to simulate physical hosts, virtual machine resources, virtualized data centers, various resource management strategies, and coordination strategies. In view of the lack of strong support for the reliability and failure recovery methods of the current cloud system, this experiment analyzed a data center based on multiple physical machines by analyzing the interruption of running tasks and data loss after the failure of the virtual machine cloud system, and predetermined the number of routers and transmission delay in the access layer, convergence layer, and core layer.
In order to test the performance of cloud computing in the mMTC scenario, this experiment integrated cloud computing and wireless communication technology for analysis, and conducted experimental data analysis. By analyzing various algorithms, the reliability of wireless communication network technology was compared. The wireless communication network speed and error rate are shown in Fig. 2.
Wireless communication network speed and error rate.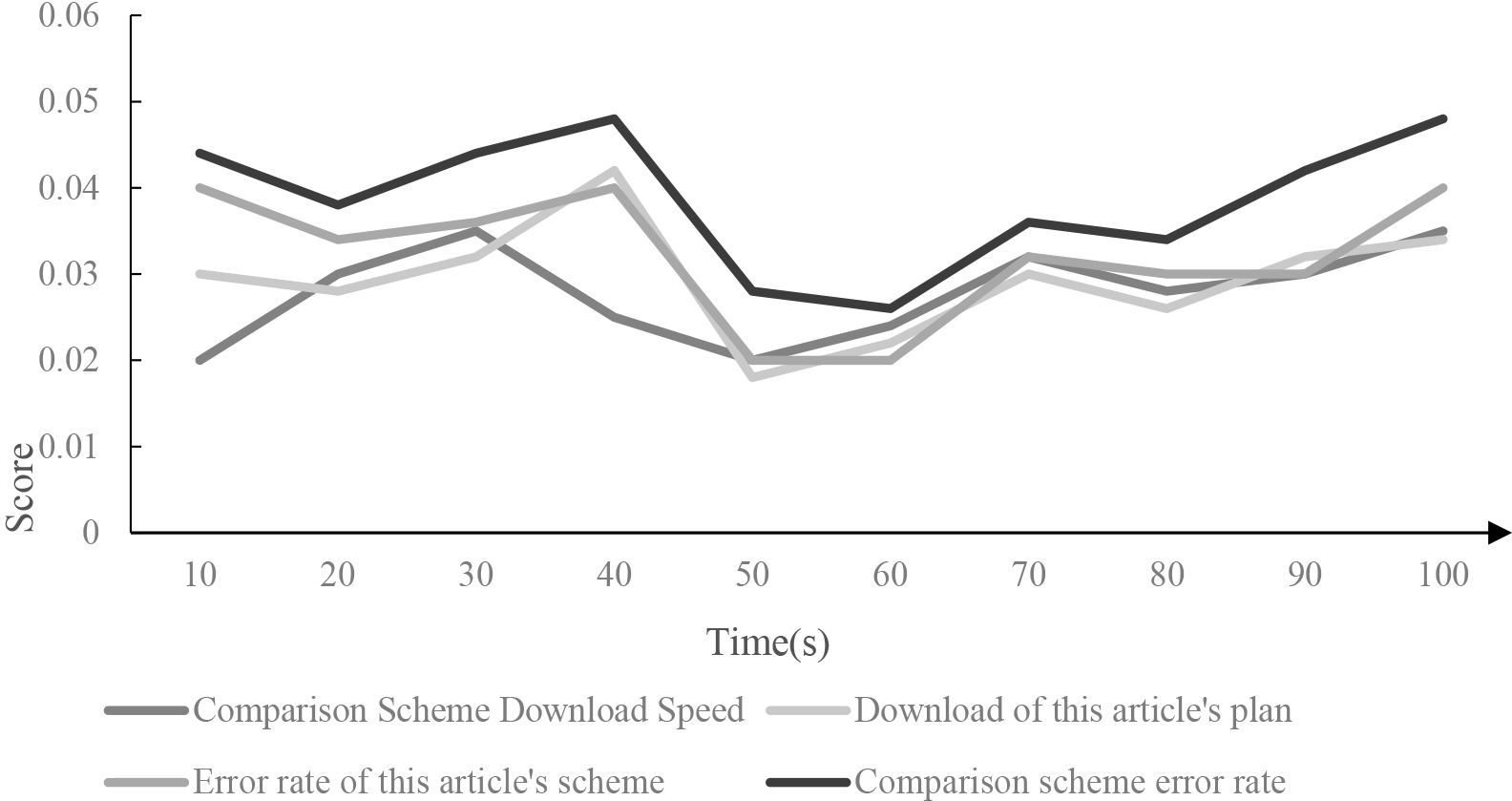
From Fig. 2, it could be seen that compared to the download speed of the comparative scheme, the download speed of this scheme was faster. From the analysis of data from each group, the average download speed of this scheme was larger, and it was slightly faster than the download speed of the comparative scheme. This was mainly because the wireless communication reliability scheme in this article combined the processing of communication data by cloud computing, and the data was processed using algorithms during the wireless communication data transmission process. Therefore, the overall wireless communication data transmission was faster, thus improving the operational efficiency of the wireless communication scheme. Due to the varying data transmission error rates under different operating speeds, schemes with relatively low error rates could be compared. After comparative analysis, it was found that the data transmission error rate of the proposed scheme was lower than that of the compared schemes, indicating that the proposed scheme could achieve more reliable wireless communication performance.
Due to the fact that wireless communication schemes could be processed through the use of algorithms, a comparative analysis was conducted based on the characteristics of the algorithms, including the task points and convergence points of the four sets of algorithms. The four groups of algorithms were Adaptive Particle Swarm Optimization (APSO), Chaos Particle Swarm Optimization (CPSO), Immune Particle Swarm Optimization (IPSO), and Ladder Particle Swarm Optimization (LPSO). The number of convergence points for each algorithm under different task counts, as well as the convergence performance of the four algorithms, were compared. The comparative analysis of the convergence of the four algorithms is shown in Table 1.
Comparison and analysis of the convergence of four algorithms
From Table 1, it could be seen that the number of tasks processed by the four algorithms was different, and the number of convergence points was also different. By observing the data in the table, it could be observed that IPSO had a higher number of tasks but fewer convergence points compared to CPSO. Therefore, in practical analysis, it was necessary to apply specific wireless communication schemes in order to maximize the effectiveness of algorithm optimization.
The experimental parameters were set as follows: 6 sets of tasks were randomly assigned, and the success rates of APSO, IPSO, and CPSO algorithms were compared to compare the convergence of these three algorithms. The comparison of algorithm success rates is shown in Fig. 3.
Comparison of algorithm success rates.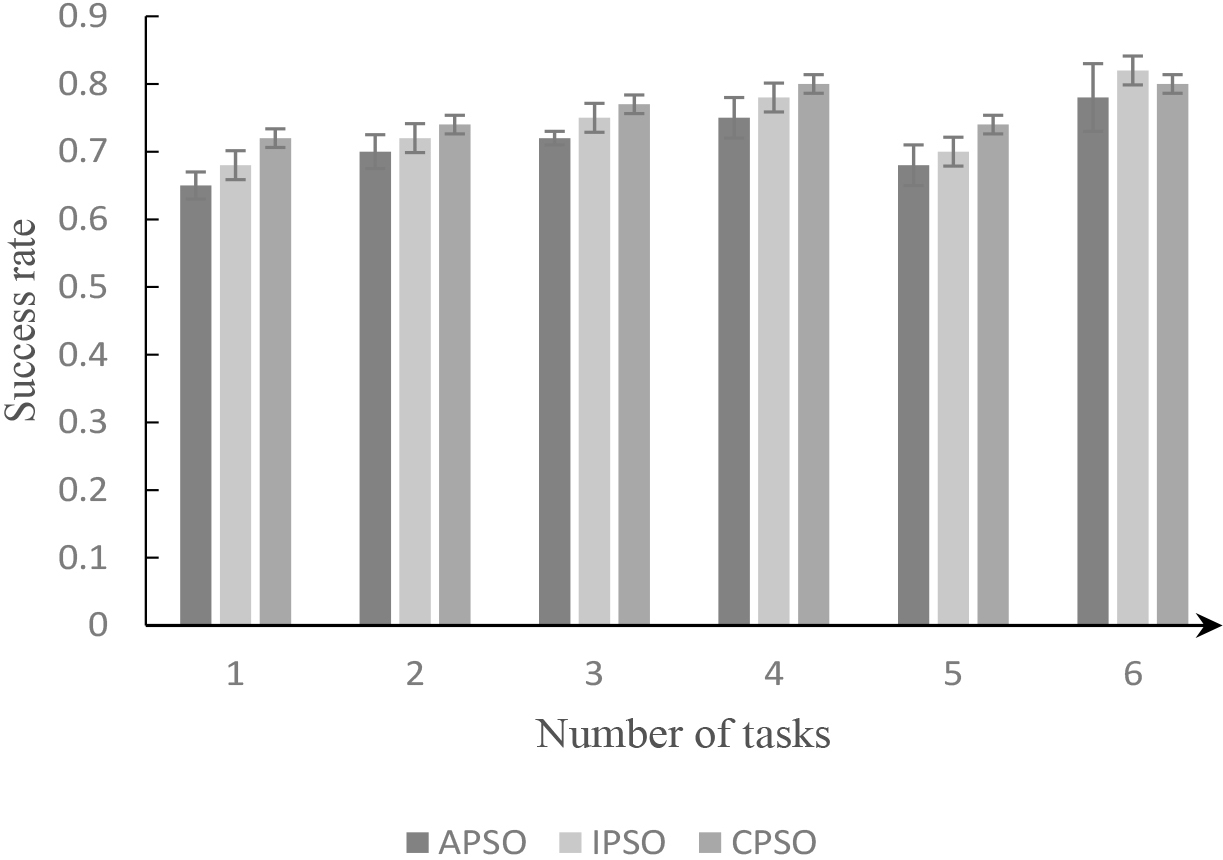
From Fig. 3, it could be seen that as the number of executing tasks increases, the success rates of the three algorithms exhibited different development trends. Among them, the execution success rate of the CPSO algorithm was relatively high, while the APSO algorithm had the lowest execution success rate. It could be seen that in the research of wireless communication schemes, the CPSO algorithm could be chosen as much as possible for data analysis and processing. The average execution success rate of the CPSO algorithm was 5% higher than that of the APSO algorithm.
Due to the consideration of time factors, the running times of the three algorithms were compared here, as shown in Fig. 4.
Comparison of algorithm runtime.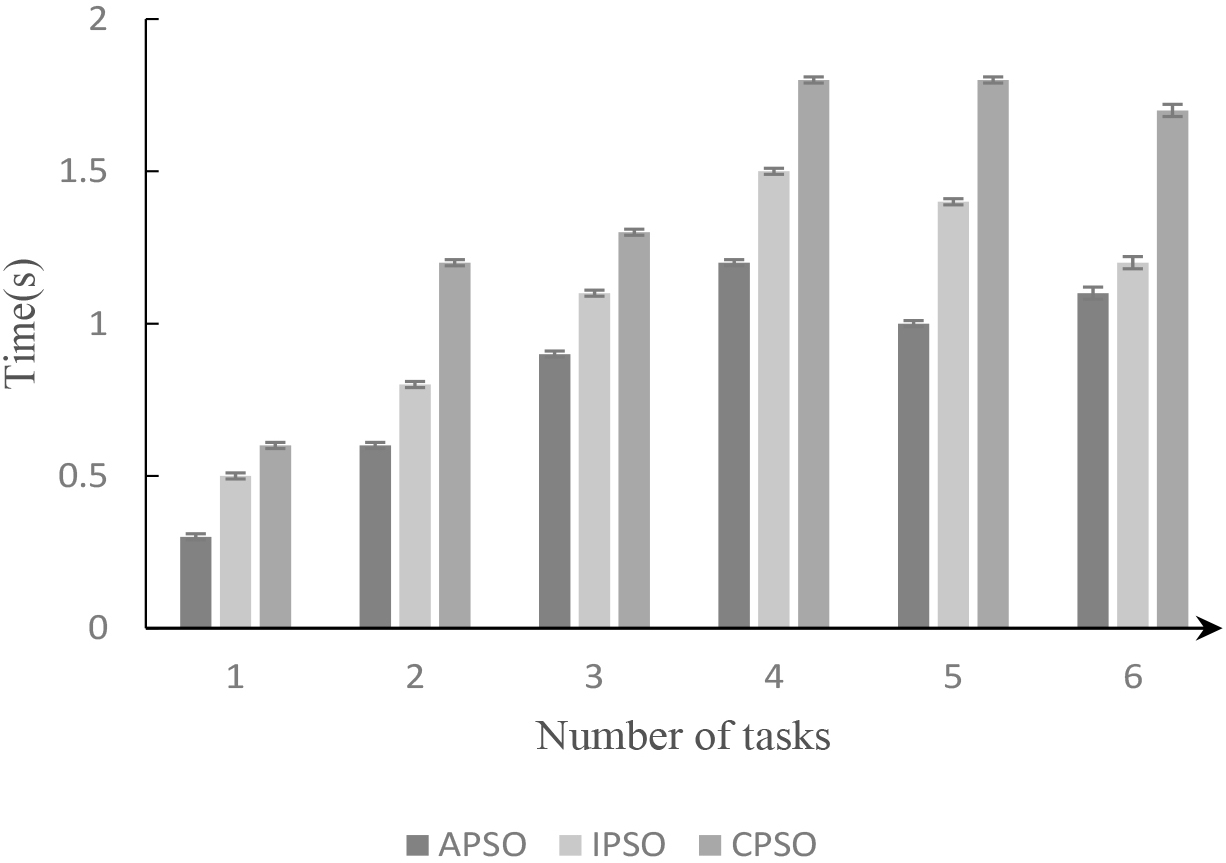
As shown in Fig. 4, the running time of the three algorithms showed an increasing trend as the number of tasks increases. By analyzing time data, it was possible to effectively avoid time resource failures during the operation of wireless communication networks, which improved the time reliability of cloud computing in mMTC scenarios and the accuracy of other parameters. All three algorithms could achieve good results in resource scheduling. However, through data analysis, it was found that CPSO had the highest running time. Therefore, when scheduling resources, appropriate algorithms should be selected to improve the performance of wireless communication schemes.
In order to verify the execution efficiency of cloud computing in the mMTC scenario, the running speed of wireless communication was set. Data transmission in cloud computing was determined by the Communication Calculation Ratio (CCR), which served as the ratio of communication volume to task computing volume. When CCR
The impact of different task communication ratios.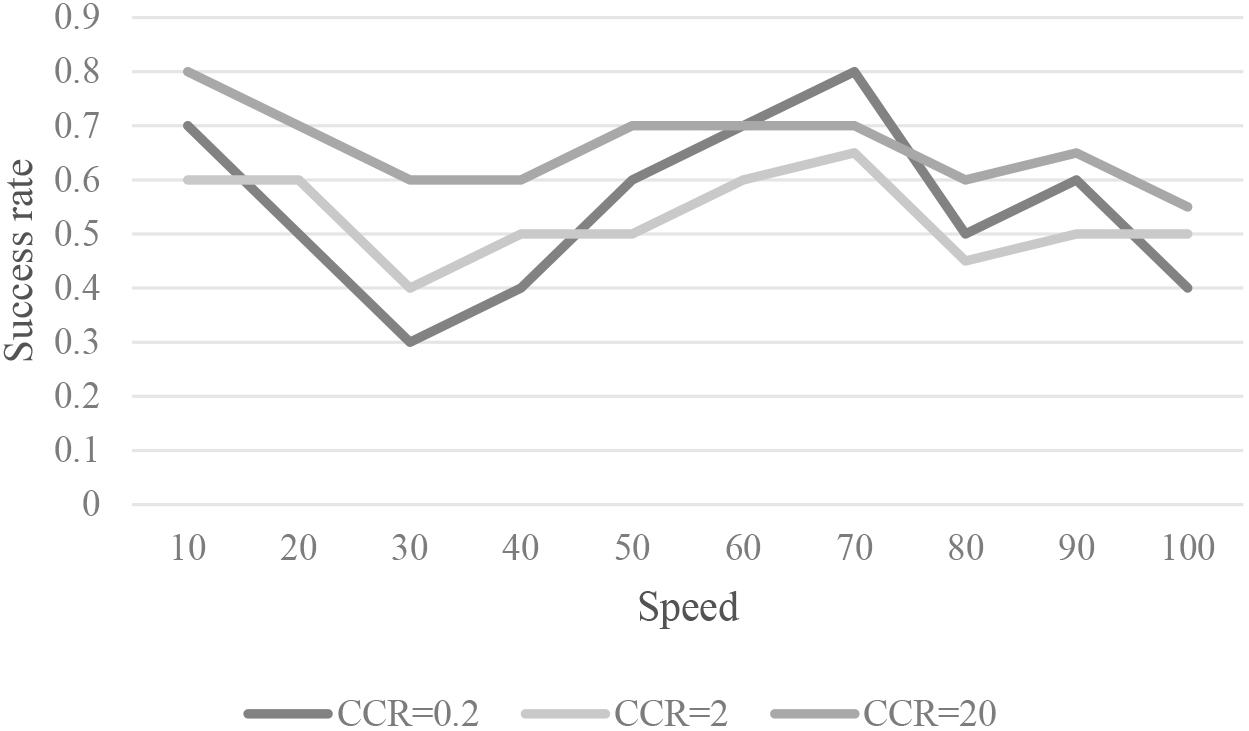
As shown in Fig. 5, when CCR
The wireless communication scheme was analyzed. The running time of the CPSO algorithm was compared when CCR
The running time of the algorithm under different communication calculation ratios
From the data in Table 2, it could be seen that under different values of CCR, the algorithm running time also varied. The impact of CCR on the reliability of wireless communication varied under different values. Due to the influence of the selection of experimental environment parameters on the experimental results, and as the number of executions increased, the task communication ratio varied in efficiency for different types of tasks under the maximum number of failures limit.
By analyzing the differences in the number of convergence points, the differences between the average processing rate and the relative processing rate were compared. The relationship between the specific number of convergence points and processing speed is shown in Table 3.
The relationship between the number of specific convergence points and processing speed
From the data in Table 3, it could be seen that the wireless communication reliability scheme after using the algorithm had stronger reliability. As the number of convergence points increases, the average processing rate of the algorithm first increased and then decreased, and the relative processing rate of the algorithm also increased and then decreased. The average processing rate range of wireless communication solutions in cloud computing mMTC scenarios was between 0.25 and 0.45, and the relative processing rate range was between 0.4 and 0.6. Therefore, the overall relative processing rate was relatively high.
This article analyzed cloud computing technology, studied wireless communication solutions, and tested and analyzed the effectiveness of wireless communication to achieve data transmission and processing of cloud resources. This article analyzed the success rate and transmission performance of APSO, IPSO, and CPSO algorithms to analyze wireless communication solutions. By analyzing wireless communication schemes and studying cloud computing data transmission methods, and through experimental data processing, it was found that the average rate of wireless communication reliability schemes increased first and then decreased, and the reliability of wireless communication schemes was stronger. Of course, there are still limitations to the experiment in this article: in the process of reliability management in computer communication networks, it is necessary to summarize rich experience, develop comprehensive control plans, innovate overall management methods and approaches under scientific management and control, comprehensively improve the reliability and effectiveness of communication systems, and meet current development needs. During the reliability management period of computer communication networks, it is necessary to summarize specific work experience, follow the design principles of reliability to carry out work, improve management efficiency and level, and achieve the expected management objectives.
The study of wireless communication reliability is one of the most important areas in the field of wireless communication. In response to issues such as wireless signal interference and weak signals, people adopt various technical measures such as information encoding methods, frequency tuning methods, and antenna design optimization to improve the reliability of wireless communication systems. This article analyzed the success rate and transmission performance of APSO, IPSO, and CPSO algorithms to analyze wireless communication solutions. The application of these technological measures helps to ensure the smooth operation of a large number of wireless communication systems, promoting social technological progress and economic development.
Research involving Human Participants and/or Animals
This article does not contain any studies with human participants or animals performed by any of the authors.
Informed consent
Not applicable.
Funding
No funding was received for conducting this study.
Footnotes
Conflict of interest
The authors declare that there are no conflicts of interest regarding the publication of this article.
