Abstract
To resolve both certificate management and key escrow problems, a certificateless public-key system (CLPKS) has been proposed. However, a CLPKS setting must provide a revocation mechanism to revoke compromised users. Thus, a revocable certificateless public-key system (RCLPKS) was presented to address the revocation issue and, in such a system, the key generation centre (KGC) is responsible to run this revocation functionality. Furthermore, a RCLPKS setting with an outsourced revocation authority (ORA), named RCLPKS-ORA setting, was proposed to employ the ORA to alleviate the KGC’s computational burden. Very recently it was noticed that adversaries may adopt side-channel attacks to threaten these existing conventional public-key systems (including CLPKS, RCLPKS and RCLPKS-ORA). Fortunately, leakage-resilient cryptography offers a solution to resist such attacks. In this article, the first leakage-resilient revocable certificateless encryption scheme with an ORA, termed LR-RCLE-ORA scheme, is proposed. The proposed scheme is formally shown to be semantically secure against three types of adversaries in the RCLPKS and RCLPKS-ORA settings while resisting side-channel attacks. In the proposed scheme, adversaries are allowed to continually extract partial ingredients of secret keys participated in various computational algorithms of the proposed scheme while retaining its security.
Introduction
To eliminate the management of both public keys and their associated certificates in the traditional public-key systems (PKS), an identity (ID)-based public-key system (IDPKS) was proposed (Boneh and Franklin, 2001). In an IDPKS setting, a private key generator (PKG) is responsible to generate all participants’ secret keys. Hence, the IDPKS setting has an inborn disadvantage, namely, the key escrow problem in the sense that the PKG can decrypt any ciphertexts of all participants and sign any messages on behalf of all participants. To resolve both certificate management and key escrow problems, Al-Riyami and Paterson (2003) proposed the certificateless public-key system (CLPKS). In which, there are two kinds of participants, namely, a key generation center (KGC) and users. The KGC is responsible to generate all users’ identity secret keys. In the meantime, each user chooses a personal secret key and sets the associated public key. Therefore, each user has two secret keys, namely, identity secret key and personal secret key. Obviously, the CLPKS setting can solve both the key escrow and certificate management problems.
Under some situations, a user’s ID or public key has to be revoked before expiration. Although the certificate revocation list (CRL) (Housley et al., 2002) is a well-known revocation method, it is unsuitable for IDPKS and CLPKS settings because no certificate is required. Therefore, an IDPKS or CLPKS setting must provide a revocation mechanism to revoke compromised users. Tseng and Tsai (2012) has presented a revocable IDPKS setting. By this revocable concept of Tseng and Tsai, revocable CLPKS (RCLPKS) settings (Shen et al., 2014; Tsai and Tseng, 2015; Hung et al., 2016) were presented to address the revocation issue and the key generation center (KGC) is also responsible to run this revocation functionality. Furthermore, a RCLPKS setting with an outsourced revocation authority (ORA), named RCLPKS-ORA setting (Tsai et al., 2015; Du et al., 2018), was presented to employ the ORA to alleviate the KGC’s computational burden.
Typically, all public-key systems mentioned above have a nature assumption that secret (or private) keys are completely hidden to adversaries. However, a new type of attacks, called “side-channel attacks”, has threatened these existing public-key systems. An adversary may employ side-channel attacks, such as power analysis (Kocher et al., 1999) and timing attack (Kocher, 1996; Brumley and Boneh, 2005) to continually obtain partial ingredients of a participant’s secret (or private) keys so that the associated cryptographic schemes/protocols could be broken. Ways to withstand side-channel attacks on cryptographic schemes/protocols have received significant attention of researchers. Fortunately, leakage-resilient cryptography offers a solution to resist such attacks. Up to date, little research addresses leakage-resilient certificateless public-key systems. In this paper, our aim is to propose the first leakage-resilient revocable certificateless encryption (LR-RCLE) scheme with an outsourced revocation authority (ORA), termed LR-RCLE-ORA scheme.
Related Work
In leakage-resilient cryptography, a cryptographic scheme/protocol remains secure even though partial ingredients of a participant’s secret (or private) keys in this scheme/protocol is leaked to adversaries. For leakage property, there are two leakage models, namely, bounded and continual. In the bounded leakage model (Katz and Vaikuntanathan, 2009; Alwen et al., 2009), total leaked bit sizes of secret keys for a cryptographic scheme/protocol are limited during its life cycle. Obviously, this limitation is impractical. In contrast, in the continual leakage model, adversaries may continually get leaked information of secret keys for each invocation of cryptographic scheme/protocol. Indeed, the continual leakage model is more accredited (Galindo and Virek, 2013; Wu et al., 2019, 2020; Tseng et al., 2020; Hsieh et al., 2020; Tsai et al., 2021) and it consists of four properties as follows:
Only computation leakage: An adversary can extract partial ingredients of secret keys involved in the current computation round.
Bounded leakage of single computational algorithm: A cryptographic scheme/protocol typically includes several computation rounds. In each computation round, an adversary can extract partial ingredients of secret keys. Namely, an adversary can select a leakage function f for each computation round and obtain the leaked information
Independent leakage: Any two leaked partial ingredients of secret keys in various computation rounds are mutually independent. For achieving this property, a secret key must be updated before (or after) running each computation round.
Overall unbounded leakage: The total amount of leaked information is overall unbounded. Indeed, by the independent leakage property, the total leakage amount of secret keys is unlimited.
According to the usage of secret key or public key, there are two kinds of encryption schemes, namely, symmetric encryption and asymmetric encryption based on various public-key systems. For a symmetric encryption scheme, a pre-shared secret key between a sender and a receiver is used to encrypt and decrypt procedures. A symmetric encryption scheme is typically employed to encrypt a large size of message and have high-throughput efficiency. On the contrary, for an asymmetric encryption scheme, a sender uses a designated receiver’s public key to encrypt message while the receiver uses her/his private key to decrypt it. Generally, an asymmetric encryption scheme is employed to encrypt a short size of message (e.g. a session key) or authenticate identity/message so that the throughput of encryption/decryption procedure is not their priority. Also, for considering leakage-resilient property, there are two kinds of leakage-resilient encryption schemes, namely, leakage-resilient symmetric encryption and leakage-resilient asymmetric encryption based on various public-key systems.
Here, let’s introduce the evolution of leakage-resilient symmetric encryption schemes. The first generic construction of leakage-resilient symmetric encryption based on minimal assumptions has been proposed by Hazay et al. (2013). However, the efficiency of Hazay et al.’s scheme is not good so that Abdalla et al. (2013) improved their scheme to propose an efficient leakage-resilient symmetric encryption scheme using the AES block cipher without constructing a leakage resilient block cipher. Recently, for enhancing the efficiency, several leakage-resilient authenticated symmetric encryption schemes based on hardware AES coprocessors (Unterstein et al., 2020; Bronchain et al., 2021) have been proposed.
In the following, several leakage-resilient asymmetric encryption (or key encapsulation) schemes based on traditional PKS, IDPKS and CLPKS settings are reviewed. Based on a traditional PKS setting, the first leakage-resilient encryption (LRE) scheme was presented by Akavia et al. (2009). Subsequently, several LRE schemes (Naor and Segev, 2009, 2012; Liu et al., 2013; Li et al., 2013) were proposed to improve security and performance of Akavia et al.’s scheme. However, all these LRE schemes above are secure only in the bounded leakage model. Moreover, Kiltz and Pietrzak (2010) presented the first LRE scheme under the continual leakage model. Furthermore, Galindo et al. (2016) presented an efficient ElGamal-like LRE scheme under the continual leakage model. Based on an IDPKS setting, Brakerski et al. (2010) proposed the first leakage-resilient ID-based encryption (LR-IBE) scheme under the continual leakage model. Subsequently, several LR-IBE schemes (Yuen et al., 2012; Li et al., 2016) were also proposed to improve security and performance of Brakerski et al.’s scheme.
Up to date, little research addresses leakage-resilient certificateless public-key systems. In 2013, the first leakage-resilient certificateless encryption (LR-CLE) scheme was presented by Xiong et al. (2013). To improve the security and performance of Xiong et al.’s scheme, Zhou et al. (2016) proposed a new leakage-resilient certificateless signcryption scheme. However, both Zhou et al.’s and Xiong et al.’s schemes are secure only under the bounded leakage model. In 2018, Wu et al. (2018) proposed the first LR-CLE scheme under the continual leakage model. In the generic bilinear group (GBG) model (Boneh et al.), Wu et al.’s LR-CLE scheme is semantically secure against chosen ciphertext attacks for two adversaries, namely, outsider and honest-but-curious KGC.
As mentioned earlier, a RCLPKS setting with an outsourced revocation authority (ORA), named RCLPKS-ORA setting, can revoke compromised users and alleviate the KGC’s revocation computation burden. However, up to date, there are no leakage-resilient revocable certificateless encryption (LR-RCLE) or leakage-resilient revocable certificateless key encapsulation scheme. In this article, the first leakage-resilient revocable certificateless encryption scheme with an ORA, termed LR-RCLE-ORA scheme, is proposed. By extending the adversary models of the revocable certificateless encryption (RCLE) (Tsai and Tseng, 2015) and leakage resilience certificateless encryption (LR-CLE) schemes (Xiong et al., 2013; Wu et al., 2018), a new adversary model of LR-RCLE-ORA schemes is presented. Under this new adversary model, the proposed scheme is formally shown to be semantically secure against three types of adversaries, namely, outsider, revoked user and honest-but-curious KGC. Finally, comparisons with previously proposed schemes (Tsai and Tseng, 2015; Xiong et al., 2013; Wu et al., 2018), the proposed scheme has the following merits. (1) It can resist side-channel attacks and has leakage resilience properties. (2) The revocation functionality is outsourced to an ORA to alleviate the computational load of the KGC. (3) It permits adversaries to continually extract partial ingredient of secret keys and offers the overall unbounded leakage property.
The remaining paper is organized as below. Several preliminaries are presented in Section 2. In Section 3, the syntax (framework) and adversary model (security notions) of LR-RCLE-ORA schemes are defined. The proposed LR-RCLE-ORA scheme is presented in Section 4. In Section 5, the security of the proposed scheme is formally established. The comparisons of the proposed scheme with some RCLE and LR-CLE schemes are given in Section 6. Conclusions are drawn in Section 7.
Preliminaries
Bilinear Groups
Let
Bilinear: for
Non-degenerate:
Efficiently computable: for
We say that
In 2005, Boneh et al. (2005) defined the generic bilinear group (GBG) model, which is a technique of proving the security of some cryptographic schemes. In the GBG model, the discrete logarithm problems on groups of a large order would be solved if collisions of the groups were found by adversaries after finishing the security games of the cryptographic scheme.
In the GBG model, as mentioned in Section 2.1, let
Note that
After finishing the security games in the GBG model of a cryptographic scheme, the discrete logarithm problem on
To measure the security influence incurred by leaked information of secret keys (finite random variables) involved in a cryptographic scheme, we first introduce the concept of entropy. The entropy of a random variable is employed to denote its uncertainty for guessing this random variable. Let R be a finite random variable and let
Min-entropy of R:
Average conditional min-entropy of R under the condition
In 2008, Dodis et al. (2008) inferred the following consequence related to the security influence incurred by leaked information of a secret key (finite random variable).
Let λ denote the maximal bit-length of leaked information of a secret key (a finite random variable) R. Let
Galindo and Virek (2013) further presented the following consequences related to multiple secret keys (finite random variables).
Let
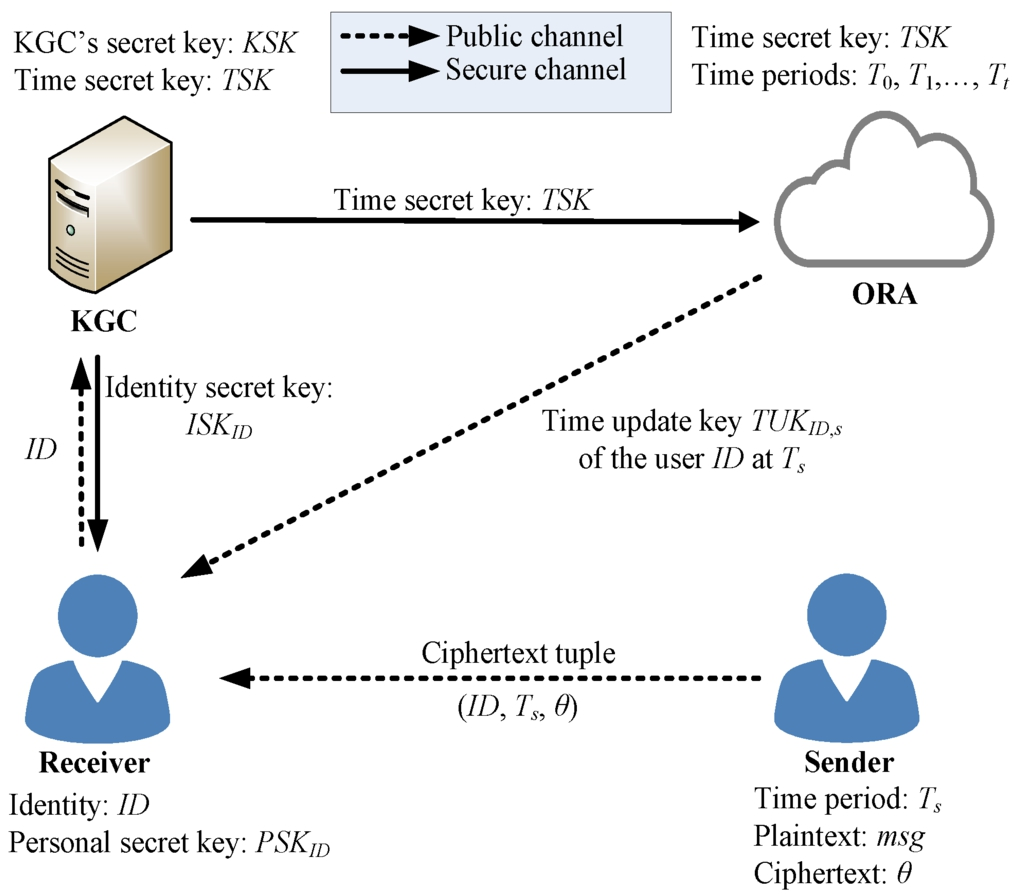
The system architecture of a LR-RCLE-ORA scheme.
The syntax (framework) and adversary model (security notions) of LR-RCLE-ORA schemes are presented as follows.
Here, let us present the system architecture of an LR-RCLE-ORA scheme as depicted in Fig. 1. An LR-RCLE-ORA scheme consists of three roles, namely, a key generation centre (KGC), an outsourced revocation authority (ORA) and users (senders and receivers). Each user with an identity
In the following, we summarize some notations used in the whole paper:
θ: a ciphertext.
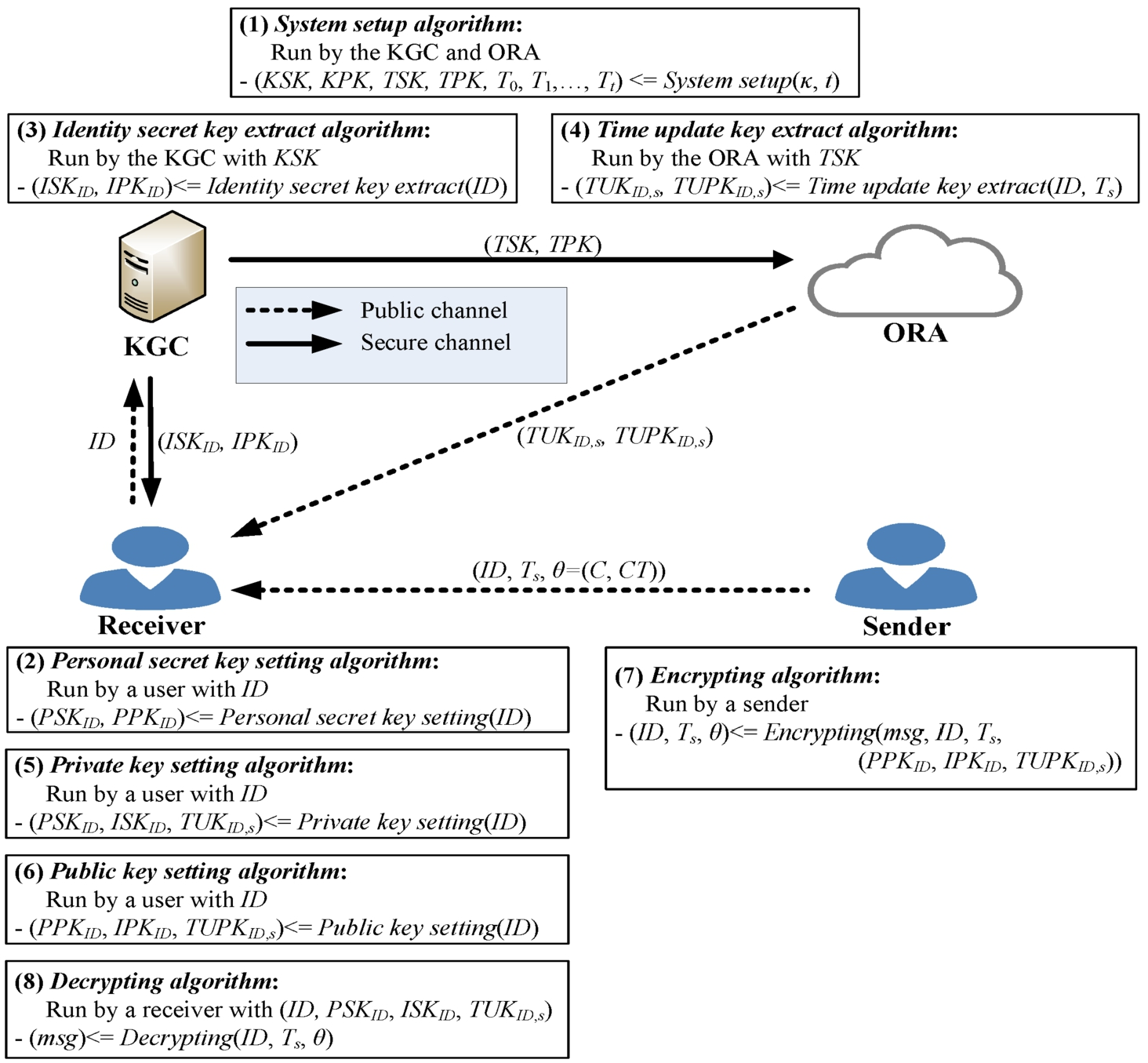
The algorithm architecture of the proposed LR-RCLE-ORA scheme.
Based on the syntax (framework) in (Tsai and Tseng, 2015; Xiong et al., 2013; Wu et al., 2018), the syntax of LR-RCLE-ORA schemes is defined as follows. An LR-RCLE-ORA scheme consists of three roles, namely, a key generation centre (KGC), an outsourced revocation authority (ORA) and users (senders and receivers) while including eight algorithms: (1) System setup; (2) Personal secret key setting; (3) Identity secret key extract; (4) Time update key extract; (5) Private key setting; (6) Public key setting; (7) Encrypting; (8) Decrypting. Fig. 2 depicts the algorithm architecture, interactions and their inputs/outputs of the proposed LR-RCLE-ORA scheme. Eight algorithms of the LR-RCLE-ORA scheme are presented in Definition 1 as below:
An LR-RCLE-ORA scheme consists of three roles, namely, a key generation centre (KGC), an outsourced revocation authority (ORA) and users (senders and receivers). Eight algorithms of the LR-RCLE-ORA scheme are presented as below:
System setup: By taking as input a security parameter κ and a period number t, the KGC generates the KGC’s secret key
Personal secret key setting: Each user with an identity ID randomly selects a personal secret key
Identity secret key extract: In this algorithm’s i-th round, by taking as input a user ID and
Time update key extract: In this algorithm’s j-th round, by taking as input a user ID, a period
Private key setting: At period
Public key setting: At period
Encrypting: At period
Decrypting: In this algorithm’s k-th round, by taking as input
By the entropy concept of secret keys mentioned in Section 2.3, six leakage functions
By extending the adversary model (security notions) in Tsai and Tseng (2015), Xiong et al. (2013), Wu et al. (2018), the adversary model of LR-RCLE-ORA schemes consists of three types of adversaries, namely, outsider (Type I,
Outsider (
Revoked user
Honest-but-curious KGC
In the continual model of leakage resilient property, the adversary model of LR-RCLE-ORA schemes is defined by the following security game In the continual leakage model, an LR-RCLE-ORA scheme is semantically secure against chosen cipher-text attacks if no adversary
Setup phase: By taking as input a security parameter κ and a period number t, a challenger B carries out the System setup algorithm of the LR-RCLE-ORA scheme to generate the KGC’s secret key If the adversary is of If the adversary is of If the adversary is of
Query phase: In the phase, the adversary may request the following queries to B adaptively.
Identity secret key query
Identity secret key leak query
Time update key query
Time update key leak query
Public key retrieve query
Public key replace query
Personal secret key corrupt query
Decrypting query
Decrypting leak query
Challenge phase. The adversary sends a target identity If the adversary is of If the adversary is of If the adversary is of
Guess phase. In this phase, the adversary must output a bit
The proposed LR-RCLE-ORA scheme consists of eight algorithms as follows:
System setup: By taking as input a security parameter κ and a period number t, the KGC chooses the bilinear group parameters
Randomly select an integer
Randomly select an integer
Randomly select four integers
Publish public system parameters
Personal secret key setting: Each user with an identity
Identity secret key extract: In this algorithm’s i-th round, by taking as input a user’s
Randomly select an integer
Randomly select an integer
Compute
Send the user’s identity secret key
Time update key extract: In this algorithm’s j-th round, by taking as input a user’s
Randomly select an integer
Randomly select an integer
Compute
Send the user’s time update key
Private key setting: At period
Randomly select an integer
Randomly select an integer
Set the user’s private key tuple
Public key setting: At period
Encrypting: At period
Randomly select an integer
Compute
Set the encryption key
Compute
Decrypting: In this algorithm’s k-th round, by taking as input
Randomly select an integer
Randomly select an integer
Compute two temporary values
Compute Compute Compute the encryption key Decrypt the plaintext
In the following, by the key refreshing technique, we have
In the following, we show the correctness of
As the security game
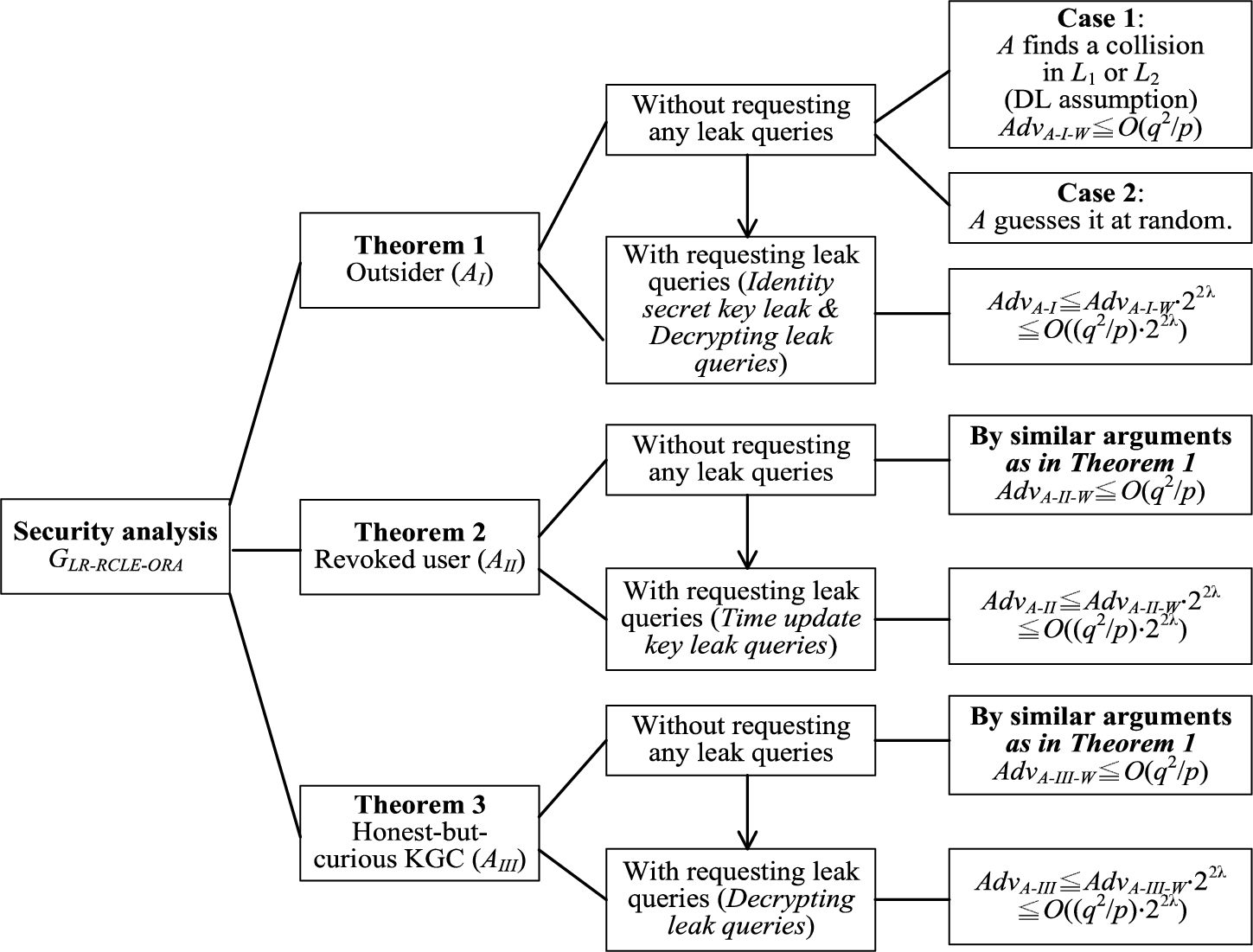
The relationship and robustness of security analysis for the proposed scheme.
In the GBG model, the proposed LR-RCLE-ORA scheme is semantically secure against chosen cipher-text attacks against an outsider
Let
Setup phase: By taking as input a security parameter κ and a period number t, B carries out the System setup algorithm of the LR-RCLE-ORA scheme to generate the KGC’s secret key
By taking as input a polynomial By taking as input an encoded bit-string
Query phase:
Get a pair of polynomials Compute the polynomial Return the encoded bit-string
Get a pair of polynomials Compute the polynomial Return the encoded bit-string
Get a pair of polynomials Compute the polynomial Return the encoded bit-string
Identity secret key query Choose a new variate Set two polynomials Set the user’s identity secret key Transform
Identity secret key leak query (
Time update key query Choose a new variate Set a polynomial Set the user’s time update key Transform
Time update key leak query
Public key retrieve query
Public key replace query
Personal secret key corrupt query Choose a new variate Set two polynomials Transform
Decrypting query By
B transforms the ciphertext C to the polynomial
Decrypting leak query
Challenge phase.
Guess phase. In this phase,
Finally, these public system parameters
It is worth mentioning the two transforming rules defined below.
To evaluate the advantage that
7 and 2 elements are increased in For each For each Identity secret key query, at most 3 elements are increased in For each Time update key query, at most 3 elements are increased in For each Decrypting query, at most 4 elements are increased in
The maximal degree of polynomials in In the Setup phase, 7 new variates (polynomials) For the For the Identity secret key query, For the Time update key query, The maximal degree of polynomials in In the Setup phase, For the For the For the Decrypting query, all
Let
In the following, let us first evaluate the advantage that
If Case 1 does not occur and
Identity secret key leak query
Decrypting leak query
Let Let Let
Because
Let
Let
Hence, the advantage
In the GBG model, the proposed LR-RCLE-ORA scheme is semantically secure against chosen cipher-text attacks against a revoked user
Let
Setup phase: The phase is the same as that in the proof in Theorem 1. Additionally, B sends the time secret key
Query phase: In this phase,
Challenge phase:
Guess phase: In this phase,
In the following, let us first evaluate the advantage that
Let Let Let
Because
Hence, the advantage
In the GBG model, the proposed LR-RCLE-ORA scheme is semantically secure against chosen cipher-text attacks against an honest-but-curious KGC
Let
Setup phase: The phase is the same as that in the proof in Theorem 1. Additionally, B sends the KGC’s secret key
Query phase: In this phase,
Challenge phase:
Guess phase: In this phase,
Let Let Let
In the following, let us first evaluate the advantage that
Because
Hence, the advantage
Here, let’s first present the computation notations of several operations in bilinear groups. By employing the simulation experiences in Li et al. (2021), Table 1 lists two kinds of time-consuming operations and their computational time (in milliseconds). The environment of simulation experiences is a platform with the Intel Core i7-8550U CPU 1.80 GHz processor. The selection of security parameters are
Computational time (in millisecond) of two time-consuming operations.
Computational time (in millisecond) of two time-consuming operations.
Table 2 lists the comparisons of our LR-RCLE-ORA scheme with several RCLE and LR-CLE schemes (Tsai and Tseng, 2015; Xiong et al., 2013; Wu et al., 2018) in terms of encryption cost (time), decryption cost (time), security proof model, revocation property, outsourced revocation, resisting side-channel attacks and leakage resilience model. Note that a user’s private key in Xiong et al.’s LR-CLE scheme (2013) is a vector with
Comparisons between our scheme and the previously proposed schemes.
In this paper, the first leakage-resilient revocable certificateless encryption scheme with an outsourced revocation authority (LR-RCLE-ORA) was proposed. As compared to previous RCLE and LR-CLE schemes, our scheme possesses several merits. (1) It can resist side-channel attacks and has leakage resilience properties. (2) The revocation functionality is outsourced to the ORA to alleviate the computational load of the KGC. (3) It permits adversaries to continually extract partial ingredients of secret keys and offers the overall unbounded leakage property. By extending the adversary models of RCLE and LR-CLE schemes, a new adversary model was defined while three kinds of leak queries are added, namely, Identity secret key leak query, Time update key leak query and decrypting leak query. In the GBG model, the security of the proposed scheme is shown to be semantically secure against chosen cipher-text attacks for three kinds of adversaries, namely, outsider, revoked user and honest-but-curious KGC.
