Abstract
Very recently, side-channel attacks have threatened all traditional cryptographic schemes. Typically, in traditional cryptography, private/secret keys are assumed to be completely hidden to adversaries. However, by side-channel attacks, an adversary may extract fractional content of these private/secret keys. To resist side-channel attacks, leakage-resilient cryptography is a countermeasure. Identity-based public-key system (ID-PKS) is an attractive public-key setting. ID-PKS settings not only discard the certificate requirement, but also remove the construction of the public-key infrastructure. For solving the user revocation problem in ID-PKS settings, revocable ID-PKS (RID-PKS) setting has attracted significant attention. Numerous cryptographic schemes based on RID-PKS settings have been proposed. However, under RID-PKS settings, no leakage-resilient signature or encryption scheme is proposed. In this article, we present the first leakage-resilient revocable ID-based signature (LR-RIBS) scheme with cloud revocation authority (CRA) under the continual leakage model. Also, a new adversary model of LR-RIBS schemes with CRA is defined. Under this new adversary model, security analysis is made to demonstrate that our LR-RIBS scheme with CRA is provably secure in the generic bilinear group (GBG) model. Finally, performance analysis is made to demonstrate that our scheme is suitable for mobile devices.
Introduction
Identity-based public-key system (ID-PKS) (Shamir, 1984; Boneh and Franklin, 2001) not only discards the certificate requirement, but also removes the construction of the public-key infrastructure. In an ID-PKS setting, there are two roles, namely, users and a private key generator (PKG). A user’s identity information is regarded as the user’s public key. The PKG employs the user’s identity information to generate the user’s associated private key. For public-key settings, user revocation mechanisms are required to revoke the misbehaving or compromised users before the intended expiration date of their public keys. Typically, a conventional public-key setting adopts the certificate revocation list (CRL) (Housley et al., 2002) to manage the revoked users. In such a setting, each user has a public key and the associated certificate. Before employing a user’s public key, one must validate its associated certificate while looking up the CRL to ensure that the user’s certificate was not revoked. However, ID-PKS settings do not require the usage of certificates so that the CRL mechanism cannot be employed to the ID-PKS settings.
Recently, Tseng and Tsai (2012) proposed a revocable ID-PKS (RID-PKS) setting with a public channel. In the RID-PKS setting, a user’s private key includes two parts, namely, a secret key and a time update key. Initially, the PKG employs a user’s identity information to generate and send the associated secret key to the user using a secure channel. Also, the PKG generates the time update key by time period and the user’s identity information. Namely, for all non-revoked users, the PKG periodically generates and sends the associated time update keys to these users using a public channel. Subsequently, numerous cryptographic primitives based on RID-PKS settings were presented, such as revocable ID-based encryption (RIBE) (Tsai et al., 2012, 2013a) and revocable ID-based signature (RIBS) schemes (Tsai et al., 2013b; Hung et al., 2017). Furthermore, several RIBE and RIBS schemes (Li et al., 2015; Tseng et al., 2018; Jia et al., 2017) have been proposed to outsource the periodical generations of time update keys to a cloud revocation authority (CRA).
Quite recently, side-channel attacks have threatened all traditional cryptographic schemes because private/secret keys are assumed to be completely hidden to adversaries in traditional cryptography. By various kinds of side-channel attacks (Boneh et al., 1997; Kocher et al., 1999; Brumley and Boneh, 2005; Biham et al., 2008), an adversary can extract fractional content of private/secret keys participated in computation rounds. To resist side-channel attacks, leakage-resilient cryptography is a countermeasure while the design of leakage-resilient cryptographic schemes has attracted significant attention from researchers. For leakage-resilient cryptographic schemes, adversaries are allowed to extract fractional content of private/secret keys while these schemes still retain secure. However, no leakage-resilient RIBS scheme based on RID-PKS settings is proposed. In the article, our goal is to propose the first leakage-resilient RIBS (LR-RIBS) scheme.
Related Work
Here, let us briefly review some leakage-resilient encryption and signature schemes based on conventional and ID-PKS settings.
According to the amount of leaked content of private/secret keys during the life time, the leakage model has two kinds, namely, bounded leakage model (Alwen et al., 2009) and continual leakage model (Brakerski et al., 2010). In a leakage-resilient cryptographic scheme under the bounded leakage model, the overall amount of leaked content has to be limited to a ratio or a fixed bit-length of private/secret keys. On the contrary, a leakage-resilient cryptographic scheme under the continual leakage model allows adversaries to continuously extract fractional content of private/secret keys so that its overall amount of leaked content is unlimited. For security robustness, a cryptographic scheme under the continual leakage model is stronger than that under the bounded leakage model. The properties of continual leakage model have four properties as below:
Bounded leakage of single observation: A cryptographic scheme typically includes several computation rounds (i.e. observations). In each computation round, an adversary can extract fractional content of private/secret keys. Namely, adversaries can select a leakage function f for each computation round and then obtain the leakage information
Only computation leakage: Adversaries are only allowed to extract fractional content of private/secret keys involved in the current computation round.
Independent leakage: Any two leaked fractional contents of private/secret keys in various computation rounds are mutually independent. For achieving this property, a private/secret key must be updated before (or after) running each computation round.
Overall unbounded leakage: The total amount of leakage information is overall unbounded. Indeed, by the independent leakage property, the total leakage amount of private/secret keys is not strict.
Under the continual leakage model, there are several leakage-resilient encryption and signature schemes based on the conventional public-key settings. In the generic bilinear group (GBG) model (Boneh et al., 2005), Kiltz and Pietrzak (2010) presented a leakage-resilient encryption scheme that allows adversaries to continually extract fractional content of secret/private keys. In Kiltz and Pietrzak’s scheme, each user’s secret key is divided into two components. After/before performing the decryption procedure, a receiver (user) must refresh two components of her/his secret key. The key idea of refreshing employs the multiplicative blinding technique which appeared in Kiltz and Pietrzak (2010). Based on this key idea, Galindo et al. (2016) presented an efficient leakage-resilient ElGamal public-key encryption scheme. Also, Galindo and Virek (2013) proposed the first leakage-resilient signature scheme under the continual leakage model. To improve the performance of their scheme, Tang et al. (2014) presented a modified leakage-resilient signature scheme by employing Boneh et al.’s short signature (Boneh et al., 2001).
Based on an ID-PKS setting, Brakerski et al. (2010) presented the first leakage-resilient ID-based encryption (LR-IBE) scheme under the continual leakage model. Subsequently, Yuen et al. (2012) presented an improvement on Brakerski et al.’s scheme in terms of computational costs. under the continual leakage model, Wu et al. (2016) proposed the first leakage-resilient ID-based signature (LR-IBS) scheme.
Up to date, no work has been published on leakage-resilient revocable ID-based signature (LR-RIBS) scheme. In the article, we present a new adversary model of LR-RIBS schemes with a cloud revocation authority (CRA) under the continual leakage model. In the adversary model, there are two types of adversaries, namely, Type I adversary (a curious CRA or an outsider) and Type II adversary (a revoked user). As compared with the adversary models of RIBS schemes presented in Tsai et al. (2013b), Hung et al. (2017), Jia et al. (2017), three new key leakage queries, namely, the key extract leak query, time key update leak query and signing leak query are added to our new adversary model. These added leak queries allow an adversary to continuously extract fractional content of private/secret keys participated in the computation rounds.
The first LR-RIBS scheme with CRA is proposed while the revocation functionality is outsourced to the CRA. By employing Kiltz and Pietrzak’s key refreshing idea (Kiltz and Pietrzak, 2010), the proposed LR-RIBS scheme with CRA allows adversaries to continuously gain fractional content of private/secret keys so that its overall amount of leaked content is unbounded and it possesses overall unbounded leakage property. Under the new adversary model and generic bilinear group (GBG) model (Boneh et al., 2005), security analysis is given to show that our LR-RIBS scheme is existential unforgeability against adaptive chosen-message (UF-LR-RIBS-ACMA) attacks of both Types I and II adversaries. Finally, performance analysis and comparisons are made to demonstrate that the proposed LR-RIBS scheme requires some additional computation costs than the previously proposed RIBS schemes. The point is that the proposed LR-RIBS scheme with CRA can resist side-channel attacks. By the simulation experiences (Lynn, 2015) on a smartphone, the proposed LR-RIBS scheme with CRA is still suitable for mobile devices.
The rest of the paper is organized as follows. In Section 2, preliminaries are given. In Section 3, we define the framework and adversary model of LR-RIBS schemes with CRA. In Section 4, we propose a secure LR-RIBS scheme with CRA under the continual leakage model. Section 5 demonstrates the security analysis of the proposed LR-RIBS scheme. In Section 6, we present the performance analysis and comparisons with the previously proposed RIBS schemes. Finally, conclusions are given in Section 7.
Preliminaries
Several preliminaries are introduced in this section.
Bilinear groups
Let G and
Non-degeneracy:
Bilinearity: for all r,
Computability:
For the detailed properties and settings with regard to bilinear groups, please refer to Boneh and Franklin (2001), Tsai et al. (2013b), Lynn (2015), Scott (2011).
By extending the generic group model presented by Shoup (1997), Boneh et al. (2005) introduced the generic bilinear group (GBG) model. Their GBG model is an adversary model played by adversaries and a challenger. In the GBG model, to perform various kinds of group operations, adversaries have to request the associated group oracles/queries to the challenger. Also, the challenger uses bit strings to denote group elements of G and
Discrete logarithm problem: Let G and
In the GBG model, there are three group operations, namely, the multiplication
In information theory, entropy is usually employed to measure the uncertainty of unknown private/secret values. Assume that W is a discrete random variable (i.e. secret value) and Pr[
Min-entropy of W:
Average conditional min-entropy of W under the condition
To measure the entropy of a finite discrete random variable (secret value) with fractional leakage content, Dodis et al. (2008) derived the following consequence.
Assume that a leakage function
By Lemma 1, Galindo and Virek (2013) derived the following consequence to measure the probability distribution of a polynomial with multiple random variables and leakage content.
Let (See Galindo and Virek, 2013).
System Architecture, Framework and Adversary Model
Here, let us present the system architecture, framework and adversary model of LR-RIBS schemes with CRA. In an LR-RIBS scheme with CRA, there are three roles, namely, PKG, CRA and users. Several notations are defined as below:
SPK: the PKG’s system public key.
SSK: the PKG’s system secret key.
TPK: the CRA’s time public key.
TSK: the CRA’s time secret key.
ID: a user’s identity, where
msg: a message.
σ: a signature value.
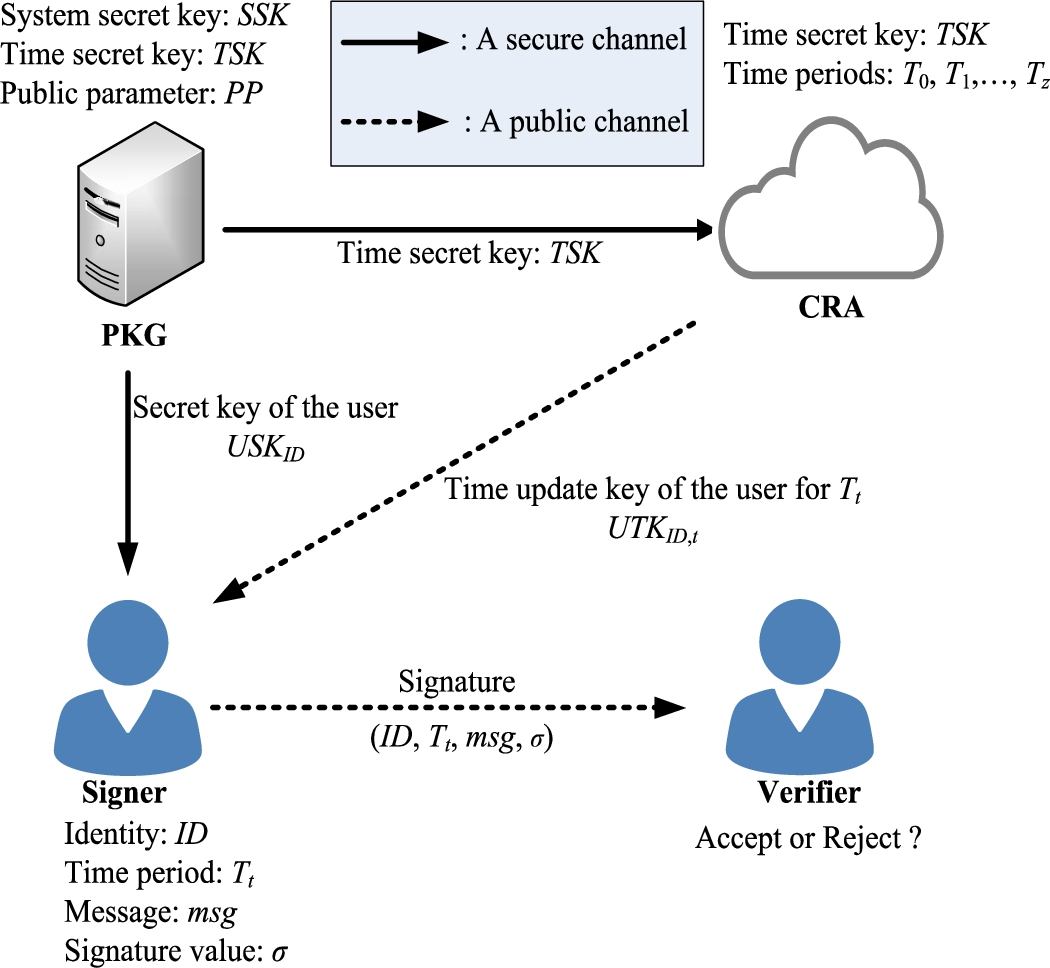
The system architecture of LR-RIBS schemes with CRA.
The system architecture of LR-RIBS schemes with CRA is depicted in Fig. 1. Firstly, the PKG sets the system secret key SSK, the time secret key TSK and a total number z of periods
Framework
To achieve overall unbounded leakage property (Galindo and Virek, 2013; Wu et al., 2016, 2018, 2019), a private/secret key must be split into two components. Additionally, each private/secret key participated in the associated algorithm is also refreshed before/after each algorithm invocation. In such a case, the PKG’s system secret key SSK, the CRA’s time secret key TSK and a user’s secret key An LR-RIBS scheme with CRA includes five algorithms as follows:
System setup: The PKG first sets the system secret key
Key extract: In the i-th invocation of the Key extract algorithm, the PKG refreshes
Time key update: In the j-th invocation of the Time key update algorithm, the CRA refreshes
Signing: In the k-th invocation of the Signing algorithm, the user ID refreshes
Verifying: Upon receiving
By extending the adversary model (security notions) presented in the RIBS schemes (Tsai et al., 2013b; Hung et al., 2017; Jia et al., 2017), we present an adversary model of LR-RIBS schemes with CRA, which allows an adversary to extract fractional content of the private/secret keys. According to our framework, an adversary can extract fractional content of the PKG’s system secret key
In the adversary model of LR-RIBS schemes with CRA, there are two types of adversaries:
Type I adversary
Type II adversary
The following security game For the LR-RIBS scheme with CRA, the game
Setup phase. The challenger C performs the System setup algorithm in Definition 1 to set a system secret key
Query phase. The adversary A can request the following queries to C adaptively.
Key extract query (ID): Upon receiving a user’s ID, C generates and sends the user’s corresponding secret key to A.
Key extract leak query
Time key update query
Time key update leak query
Signing query
Signing leak query (ID, k,
Forgery phase. The adversary A outputs a signature tuple If A is a Type I adversary (a curious CRA or an outsider), the Key extract query on If A is a Type II adversary (a revoked user), the Time key update query on ( The Signing query on ( The output of the Verifying algorithm on (
Here, let us present the first LR-RIBS scheme with CRA that consists of five algorithms as below:
Choose a random integer
Choose a random integer
Choose six random integers u, v, w, x, y,
Set
Finally, the PKG holds
Choose a random integer
Choose a random integer
Compute
Finally, by a secure channel, the PKG sends
Choose a random integer
Randomly select an integer
Compute
Finally, by a secure channel, the CRA sends
Choose a random integer
Choose a random integer
Set the signature tuple (
Here, let us discuss the correctness of the verifying equality. By the key refreshing procedures of those secret values employed in the proposed scheme, we have:
Hence, the equality is verified by
Let us analyse the security of our LR-RIBS scheme with CRA. By the adversary model (i.e. security game
In the GBG model, our LR-RIBS scheme with CRA possesses existential unforgeability under the UF-LR-RIBS-ACMA attack of Type I adversary (a curious CRA or an outsider).
Let
Setup phase: The challenger C carries out the System Setup algorithm of our scheme to generate SSK, TSK, a total number z of periods
When C receives When C receives
Query phase:
Group query Transform Compute the resulting polynomial Transform and return the bit string
Group query
Pairing query Transform Compute the resulting polynomial Transform and return the bit string
Key extract query (ID): Upon receiving the i-th Key extract query with a user’s ID, C looks for (ID, Choose a new variate Set the polynomial Compute the user’s secret key Transform and return two corresponding bit strings
Key extract leak query
Time key update query (ID, Choose a new variate Set the polynomial Set the user’s time update key Transform and return two corresponding bit strings
Singing query (ID, By ID, look for By ID and Set Choose a new variate Set Transform (
Signing leak query
Forgery phase: For evaluating the probability that The number of group elements in In the Setup phase, nine group elements are initially added in For each In the Key extract query for a new user, two new group elements are generated and added in In the Time key update query for a user at a period, two new group elements are generated and added in In each Signing query, six new group elements are added in The maximal degree of polynomials in In the Setup phase, since these polynomials In In the Key extract query, In the Time key update query, In the Signing query, The maximal degree of polynomials in In the Setup phase, both In In If one of the following two cases occurs, we say that
Let us evaluate ∙ The probability that Let us evaluate the probability that Let ∙
a, γ: In each Key extract query, a and γ are random values. Therefore, the leakage of a or γ is of no help to learn the system secret key SSK. (
(
Let
In our LR-RIBS scheme with CRA, the PKG employed SSK and a user’s information Therefore,
In the GBG model, our LR-RIBS scheme with CRA possesses existential unforgeability under the UF-LR-RIBS-ACMA attack of Type II adversary (a revoked user).
Let
Setup phase: The phase is the same with that of the proof in Theorem 1.
Query phase:
Time key update leak query Forgery phase: By the same arguments in Theorem 1, the total number of group elements in ∙ Hence, ∙
Let
In the Time key update phase of our scheme, the CRA employed the time secret key TSK and a user’s content Therefore,
Finally, C sends these public parameters
It is worth mentioning that C employs two rules to respond the transformation request as below:
Note that
The total number of
In the k-th Signing query of the user ID, by taking as input two leakage functions
Hence, the advantage
For the k-th Signing leak query of the user ID, by taking as input two leakage functions
Hence, the advantage
Here, we compare the performance between previously proposed RIBS schemes (Tsai et al., 2013b; Jia et al., 2017) and our LR-RIBS scheme with CRA. In the following, four notations are defined respectively to represent four time-consuming operation costs of bilinear groups:
Executing costs (in milliseconds) of several operations on a PC and a smartphone.
Performance comparisons between our LR-RIBS scheme with CRA and the previously proposed RIBS schemes.
Indeed, the cost of the operation (additive/multiplicative) on an (additive/multiplicative) cyclic group G is smaller than
Table 2 lists the performance comparisons between two previously proposed RIBS schemes (Tsai et al., 2013b; Jia et al., 2017) and our LR-RIBS scheme with CRA in terms of resisting side-channel attacks, overall unbounded leakage property, outsourced revocation authority and the computation costs of four phases. In Tsai et al. (2013b), the PKG is responsible to carry out both the Key extract and Time key update phases. On the other hand, the scheme in Jia et al. (2017) and our scheme employ a CRA to outsource the functionality of user revocation. Note that the executing costs of both the Key extract and Time key update phases are measured under a PC while the executing costs of both the Signing and Verifying phases are measured under a smartphone.
By Table 2, although performing worse than the other two schemes in the computation costs, our scheme is still well suited for a smartphone with limited computing capability. We should emphasize that our scheme can resist side-channel attacks with overall unbounded leakage property, but the other two cannot.
In the continual leakage model, we have defined a novel adversary model of LR-RIBS schemes with CRA. In the adversary model, Type I adversary (a curious CRA or an outsider) is allowed to extract fractional content of the target signer’s secret key and the PKG’s system secret key. Also, Type II adversary (a revoked user) is allowed to extract fractional content of the CRA’s time secret key. We have proposed the first LR-RIBS scheme with CRA and it possesses the overall unbounded leakage property. In the GBG model, security analysis demonstrated that the proposed LR-RIBS scheme with CRA is secure against Types I and II adversaries under the continual leakage model. Performance comparisons demonstrated that the proposed LR-RIBS scheme with CRA requires some additional computation costs than the previously proposed RIBS schemes. This point is that our scheme not only can resist side-channel attacks, but also is still suitable for mobile devices with limited computing capability.
