Abstract
Replications are especially useful to test the generalizability of managerial knowledge across diverse situations and contexts. In this study, we conduct a quasi-replication of Zavyalova and colleagues’ (2012) influential product harm paper, which explored how firm impression management strategies shaped media tenor following misconduct. Extending their approach to a new context, we seek to understand how firm impression management strategies impact media tenor following data breaches, representing a case of firm misfortune. Drawing on a sample of 287 U.S. data breach events, we find that media evaluations are shaped by firm impression management responses and industry features following a breach. Our findings also suggest that firms should respond differently in cases of misfortune than in instances of misconduct, adding important nuance to the literature. Taken together, our study tests the theory of Zavyalova et al. in a different context, finds contextual differences that resulted in dissimilar empirical results, and contributes new knowledge by showing how firm impression management strategies and industry context affect media tenor differently after data breaches than after toy recalls.
Keywords
A growing literature investigates how the media evaluate firms following instances of misconduct or misfortune (see Hersel, Helmuth, Zorn, Shropshire & Ridge, 2019 for review). Organizational misconduct occurs when firms engage in illegal, unethical, or irresponsible behavior that directly harms its stakeholders (Greven, Palmer & Pozner, 2010; Han, Pollock & Graffin, 2023), while misfortune occurs when organizational stakeholders are harmed despite an organization's efforts to safeguard them.
Over a decade ago, Zavyalova, Pfarrer, Reger and Shapiro (2012) investigated how organizational impression management strategies shaped media evaluations of firms following product harm events. Their paper found that firm impression management strategies differentiated media tenor after toy recalls, providing important guidance for firms seeking to navigate instances of misconduct. According to Google Scholar, this article has now attracted over 600 citations, and its findings are assumed to apply across a wide array of events. Building on the Journal of Management Scientific Reports’ mission to publish studies that test the generalizability of existing evidence, we conduct a quasi-replication of Zavyalova et al.'s (2012) influential work to reexamine an array of its relationships and provide further evidence of its generalizability in the context of data breaches, which represent cases of firm misfortune.
Data breaches (hereafter: breaches) are increasingly consequential negative events that are not well understood. For example, the IBM 2016 Cost of Data Breach Study found that the average cost of a breach was four million U.S. dollars. The strategic consequences of breaches also affect firms long after a breach, including heightened regulatory scrutiny, operational disruptions, damage to supplier relationships, and reputational loss. Considering these deleterious consequences, many firms have rated breaches as a critical threat to their core business and survival (Ulsch, 2014). Moreover, the prevalence of breaches raises questions about how the firm should respond after a breach (Kamiya, Kim, Milidonis & Stulz, 2021), including the actions and learning processes needed to mitigate its negative consequences (Madsen & Desai, 2010).
Although firm actions can shape stakeholder evaluations after a negative event (Munyon, Jenkins, Crook, Edwards & Harvey, 2019), existing studies do not distinguish the impacts of breaches compared to other types of negative events, such as product quality issues and recalls (e.g., Zavyalova et al., 2012). As a result, it remains uncertain whether the firm actions—and especially impression management approaches—for instances of misfortune vary from those employed in cases of misconduct. Ultimately, without further evidence, important questions remain about the generalizability of findings from prior studies examining other types of negative events, including optimal corrective actions for firms (e.g., Diestre, Montauti & Pinto de Sousa, 2023; Graf-Vlachy, Oliver, Banfield, König & Bundy, 2020; Hersel et al. 2019; Kibler, Mandl, Farny & Salmivaara, 2021).
This knowledge deficiency is magnified in importance because breaches possess unique characteristics compared to other types of negative events. Breaches are sometimes perceived as unfortunate incidents beyond the firm's control, representing cases of “misfortune” (Barona & Anita, 2017; Butt et al., 2023), whereas other negative events can be deliberate actions (i.e., wrongdoing) taken by the firm, representing cases of “misconduct” (cf. Roulet & Pichler, 2020). Considering the potential distinctions between instances of misfortune and misconduct, replication (i.e., a quasi-replication – Bettis, Helfat and Shaver, 2016) represents a valuable mechanism to determine whether prior evidence applies across these divergent situations. Therefore, a more nuanced quasi-replication that extends and generalizes the original theory to new empirical contexts appears needed (Bettis et al., 2016; Köhler & Cortina, 2021). Specifically, a quasi-replication is needed to examine both the effects of breaches as well as the efficacy of firm response strategies and media reactions following such events, and the purpose of this paper is to quasi-replicate Zavyalova et al.'s (2012) study in a multi-industry data breach context.
Three contributions are intended in this investigation. First, our empirical generalization and quasi-replication of Zavyalova et al. (2012)—using a different context—contributes to the growing call for replications within strategic management research (Bettis et al., 2016; Köhler & Cortina, 2021). Such studies (e.g., Berry & Kaul, 2016; Gong et al., 2021; Howard et al., 2016; Mezias & Regnier, 2007) are increasingly important within the field, in part, because they “assess robustness and/or generalizability” of prior research by considering how the findings from one study apply in new contexts, settings, data sources, and even periods (Bettis et al., 2016: 2195). Second, we contribute to the literature on negative social evaluation/deviation (e.g., Roulet, 2020) and impression management (e.g., Diestre et al., 2023) by highlighting how different firm responses shape social evaluations following a case of firm misfortune. Finally, we contribute to research on media evaluation (Graf-Vlachy et al., 2020; Zavyalova et al., 2012) by examining the media responses following a major negative event. Below, we describe Zavyalova et al.'s (2012) theory and replicate their hypotheses in a new context.
Data breaches versus toy recall: a quasi-replication study
Theory can be refined, tested, and extended by generalizing the empirical findings from one context to another (Tsang & Kwan, 1999). Although breaches and toy recalls both negatively affect stakeholders, including consumers (Culnan & Williams, 2009; Tang, 2008), there are notable differences between these two types of negative events. Data breaches indirectly reveal a firm's liability when breached data are maliciously used, whereas toy quality issues result in direct harm through interactions with defective products (Malhotra & Malhotra, 2011). Furthermore, toy recalls can result from the firm or its suppliers (Cleeren, Dekimpe & van Heerde, 2017), while breaches generally originate from outside forces. Thus, although the findings of Zavyalova et al. (2012) inform how firms can respond to direct product failure incidents, or instances of “misconduct,” contextual differences in breaches suggest that further inquiry is warranted and important to inform how firms should react in situations of “misfortune.”
Media tenor of a firm
As a key stakeholder group, the media assess firm events and activities and generate subsequent coverage about these events and activities (Deephouse & Suchman, 2008). Media tenor reflects the overall positive or negative sentiment that the media expresses concerning a firm and shapes others’ perceptions and behaviors towards the firm (Kellner, 2004; Zavyalova et al., 2012). Theory suggests that tenor becomes negative toward a focal firm when that firm experiences a negative event or violates stakeholder expectations (Deephouse & Suchman, 2008). These effects also compound with repeated failures, such that firms that re-offend or fail to meet stakeholder expectations increase media skepticism regarding the firm's capability to handle such events (Pfarrer et al., 2008a). This effect also reflects observer assessments found in attribution theory, where repeated violations of expectations or norms heighten judgments of responsibility and blame toward a focal firm (Weiner, 1995; 2006). Thus, repeated failures focus attention on the lack of firm capabilities, which should modify how the media assesses firms. In sum, we expect the magnitude or frequency of breaches to shape the firm's media image (Bansal & Clelland, 2004; Deephouse, 1996; Lamin & Zaheer, 2012; Pollock & Rindova, 2003). Stated formally:
Hypothesis 1: The greater the magnitude of a firm's negative event (i.e., data breach), the less positive the tenor of media coverage about the firm.
Media tenor of industries
Although breaches theoretically impact a firm's media tenor, such negative events can spillover and impact the industry in which a firm competes (Zavyalova et al., 2012). This industry spillover effect occurs because stakeholders often believe firms from the same industry may experience similar problems (Barnett & King, 2008; Naumovska & Zajac, 2022), thus reconsidering how they view other industry participants. Breaches can also reveal capability gaps in industries that share the same information security protocols, negatively impacting others within the same industry. For example, since breaches were prevalent in the retailing industry, breaches at Target, Home Depot, and T.J. Maxx might have impacted media stakeholder perceptions and expectations toward other retailers. Thus:
Hypothesis 2: The greater the magnitude of negative breach events in a firm's industry, the less positive the tenor of media coverage about the firm.
By contrast, the magnitude of negative events in an industry may also have the “safety-in-numbers” effect. Specifically, when several firms in an industry experience breaches, a single firm's breach might lose its novelty, convey information that is expected by audiences (Diestre et al., 2023), or highlight causes in the external environment beyond a firm's control (Roulet & Pichler, 2020). The cumulative effect is that repeated negative breaches in a single industry may attract less media attention and, thus, weaker effects on media tenor, given that the media often see novel events in an industry as newsworthy (Pfarrer et al., 2008b). The frequency of breaches in an industry allows media stakeholders to attribute the breaches to industry factors rather than idiosyncratic firm problems (Bundy & Pfarrer, 2015; Pfarrer et al., 2008a), reducing the blame of the firm and shifting it partly to the industry. As a result, the media may blame the firm less when breaches occur within a focal industry prone to breaches. Hence:
Hypothesis 3: The magnitude of negative breach events in a firm's industry attenuates the negative effect of a firm's event on the tenor of media coverage about the firm.
Firm responses
Beyond understanding how media stakeholders react to breaches, firms are interested in knowing how to minimize negative consequences following a breach (Martin, Borah & Palmatier, 2017). Most firms and managers engage in impression management to repair their reputations (Kibler, Mandl, Farny & Salmivaara, 2021). Zavyalova et al. (2012) theoretically categorized two key types of firm responses following major product recalls in the toy industry: technical and ceremonial responses. The primary difference between these two responses is that technical responses attempt to address the causes of a negative event, while ceremonial responses attempt to deflect media attention toward other issues. Following Zavyalova et al. (2012), we argue that these response actions impact media tenor differently following breaches.
Technical responses
Technical responses attempt to address the cause of an issue, offer solutions, and attract media and stakeholder attention to the focal issue (Zavyalova et al., 2012). The negative consequences of breaches might demand that firms be more responsive and effective in terms of offering solutions and providing plans to address the source of the problem (Martin et al., 2017). For example, following Target's payment system hack in 2014, the firm released detailed statements about its investigation on the cause of a breach, informing potentially affected customers to prevent further payment fraud and offering comprehensive credit monitoring services (e.g., LifeLock) (Morad, 2014).
The crisis management literature argues that firms may effectively rebuild media evaluations by taking actions that signal they are in control and are effectively addressing the problem (Benoit, 1997; Coombs, 2007). This argument is especially valid when stakeholders perceive events (e.g., data breaches) as violations of their expectations and thus expect firms to resolve the incident directly; that is, presenting a technical response (Bundy et al., 2017; Durand & Vergne, 2015; Mishina, Block & Mannor, 2012). Therefore, firms appear more likely to restore positive media tenor following a breach by responding technically. Thus:
Hypothesis 4a: A firm's announcements of technical actions attenuate the negative effect of the firm's event (i.e., data breach) on the tenor of media coverage about the firm.
Ceremonial responses
In other cases, focal firms might respond to breaches in a ceremonial manner, meaning that they do not directly address an event's cause but instead focus on the positive characteristics of the firm to deflect stakeholder attention away from the focal event (Kim et al., 2004; Zavyalova et al., 2012). Notably, following negative events, the media are more likely to perceive ceremonial responses that indirectly address the cause of the incident as inconsistent with their expectations of the focal firm and inadequate to remedy perceived deficiencies that enabled a breach (Ashforth & Gibbs, 1990; Fiss & Zajac, 2006). In short, the media might doubt the trustworthiness of a firm if it fails to take action to remedy harm and prevent future breaches (Fiske & Taylor, 2013; Greenwald & Banaji, 1995; Lingle et al., 1979; Zavyalova et al., 2017). Therefore, when breaches occur, we anticipate that ceremonial responses will magnify the negative media sentiments toward this firm:
Hypothesis 4b: A firm's announcements of ceremonial actions amplify the negative effect of the firm's event (i.e., data breach) on the tenor of media coverage about the firm.
Firm responses and industry effects
Firm reactions following a breach might also be impacted by the firm's industry context, and the relationship between firm responses and media tenor might depend on the magnitude of breaches within an industry. Specifically, attribution theory proposes that actor (i.e., firm) behavior is evaluated in comparison to others in a similar situation (Kelley, 1973). When many firms in an industry are affected by breaches, media evaluations of breached firms should be altered compared to when few firms experience breaches (cf. Harvey et al., 2014).
Technical responses
When multiple data breaches occur in an industry, the media are more likely to attribute a focal firm's breach to industry characteristics rather than causes idiosyncratic to the firm. As a result, the lack of direct responsibility for a breach should attenuate the expectations of others on the firm to rectify the situation via a technical response (Bundy & Pfarrer, 2015; Zavyalova et al., 2012). In contrast, when the magnitude or frequency of breaches in an industry is low, a breached firm may lose its “industry shield,” which otherwise reduces stakeholder blame toward a focal firm. In this instance, failure by the breached firm to directly address stakeholder concerns may generate negative media tenor. For example, insurance companies are seldom targeted in breaches, but AFLAC experienced an isolated breach (DataBreaches.net, 2013). When the firm did not announce a timely technical response, negative media tenor increased about the firm. Hence, we propose:
Hypothesis 5a: A firm's announcements of technical actions amplify the negative effect of the industry's breach events on the tenor of media coverage about the firm.
Ceremonial responses
The strategic categorization literature suggests that the media categorize various strategic issues as either opportunities or threats based on issue novelty. When the magnitude of breaches is high in an industry, an individual firm's breach will become less unique. As a result, the media are more likely to attribute the cause of an event to uncontrollable industry factors than to an individual firm (Ford, 1985; Sjovall & Talk, 2004) and express more tolerance toward the breached firm (cf. LePine & Van Dyne, 2001). Thus, when breaches become a common problem in an industry, ceremonial actions might help a breached firm restore its legitimacy by deflecting media attention from the firm to its industry context (Försterling, 2001; Weiner, 1985). For example, 60% of breaches have occurred in high-tech industries, compared to 20% in the manufacturing sectors (Cisco, 2015). In the case of high-tech industries, stakeholders might be more likely to attribute the breach to factors outside the firm (e.g., industry). Thus, a ceremonial response may weaken negative media tenor. Hence:
Hypothesis 5b: A firm's announcements of ceremonial actions attenuate the negative effect of the industry's breach events on the tenor of media coverage about the firm.
Methods
Sample
We followed the original work of Zavyalova et al. (2012) as closely as possible in terms of their assumptions and data collection. To capture breach events, we used reports from the Privacy Rights Clearing House (PRCH) (Kamiya et al., 2021) and the RavenPack News Analytics (RavenPack) databases. The PRCH database captures all major breaches in U.S. organizations reported by government agencies and verified by media sources from 2005 forward. RavenPack captures breaches reported by traditional media (i.e., newspapers, magazines, and broadcasts), social media (i.e., blogs), or firm press releases. To remove “potentially noisy news” that was less salient, we collected reports from RavenPack with relevance scores equal to 100 (Dang, Moshirian & Zhang, 2015: 86). 1 If a breach was recorded in both databases, we cleaned the duplicate record(s). Our final sample involves 287 breaches that occurred in 95 U.S. publicly traded firms during the period 2001–2015. The data were collected in 2016.
Measures
Dependent variable
The main dependent variable in Zavyalova et al.'s (2012) study is media tenor. Thus, our dependent variable is constructed and measured in the same manner.
We measured media tenor exactly following Zavyalova et al.'s (2012) LIWC approach. In particular, we used the Factiva database to identify traditional news and online blog articles published in media newswires. We then calculated the percentage of positive and negative content in each article and coded it as positive if its total affective content was at least 66 percent positive and as negative if its total content was at least 66 percent negative. In this way, we coded each article as a positive or negative article. Following the original study, we measured the tenor of media coverage about a focal firm as the difference between the number of positive and the number of negative articles published about a firm during the present and following quarters of the data breach. To be consistent with the original study, we standardized the dependent variable.
Independent variables
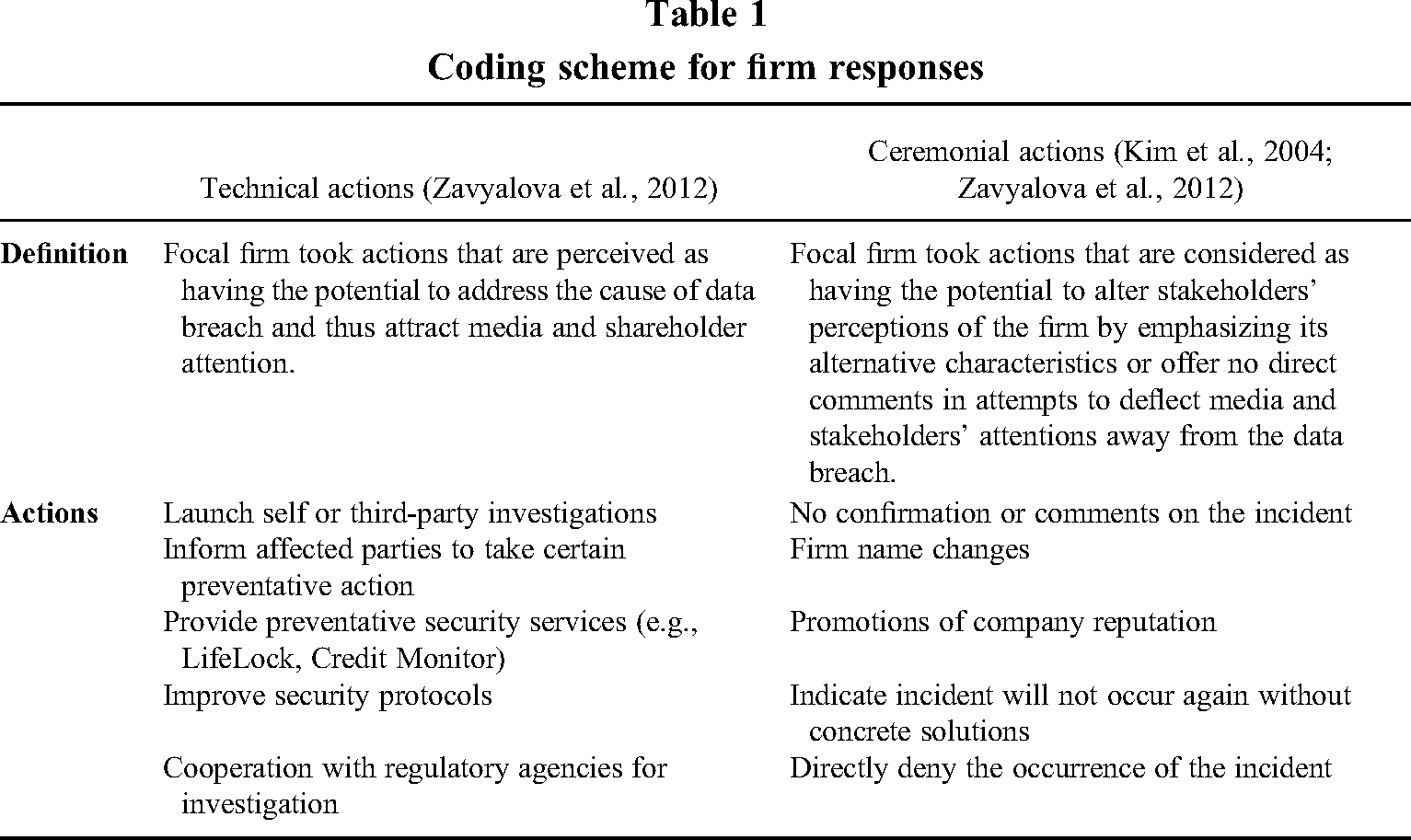
Consistent with Zavyalova et al.'s (2012) conceptualization of wrongdoing, we measured firm data breaches as the total number of breaches that occurred to the focal firm in a given quarter and industry data breaches as the sum of all breaches in the industry in the same quarter. Data were collected from the PRCH. Also, consistent with Zavyalova et al.'s approach (2012), we conducted a structured content analysis of media coverage, firm self-announcements, court and attorney general disclosures, and third-party investigation reports of breaches to create two categories of responses—technical and ceremonial actions. Table 1 reports our coding scheme in line with Zavyalova et al.'s (2012) coding. Technical responses capture: (1) launching self or third-party investigations, (2) informing affected parties to take preventative and remedy actions, (3) offering direct financial compensation, (4) providing preventative security services (e.g., Life Lock, Credit Monitoring), (5) improving security protocols, and (6) cooperating with regulatory agencies for the investigation (cf. Zavyalova et al., 2012). Ceremonial responses capture (1) no direct confirmation, announcement, or comments on the breach, (2) denial of the occurrence of a breach, (3) firm name changes, (4) announcement of company award, (5) promotion of company reputation, and (6) stating the incident will not occur again but without concrete solutions (Zavyalova et al., 2012). We counted the announcements of the actions taken by a firm following a breach to capture the extent to which firms engaged in technical or ceremonial responses. To be consistent with the original study, we standardized all the above independent variables.
Coding scheme for firm responses
Control variables
We controlled for firm-level factors consistent with Zavyalova et al. (2012)'s variable selection, including firm age, size, firm performance, and the total amount of media coverage. Past research has found that firm age is highly associated with stock market returns (Zhang, 2006). Thus, we captured firm age by measuring the number of years starting from a firm's IPO year (Linck, Netter & Yang, 2008). If the IPO year was not available, we alternatively used the year when a firm was first covered by COMPUSTAT (Flammer, 2013). Small firms often display higher stock price volatility because they are strongly affected by the credit market and environmental risks (Perez-Quiros & Timmermann, 2000). However, large firms are more likely to be the targets of breaches because they use more Internet and cloud infrastructures (Baker et al., 2011). Thus, we controlled for firm size using the natural logarithm of total assets (Flammer, 2013; Leland, 2007). Prior firm performance is the return on assets (ROA), defined as the ratio of net income to total assets lagged by one year. Firm age, size, and prior financial performance are measured using COMPUSTAT data. The total amount of media coverage is measured by the number of articles published about a firm in a given quarter (Zavyalova et al., 2012).
Consistent with Zavyalova et al. (2012), we also controlled for the social memory of the firm data breach and the social memory of the industry data breach. These two variables capture the effect of a firm's and industry's data breaches on subsequent levels of social evaluation (Zavyalova et al., 2012). The social memory of the firm is measured by the sum of the number of breaches by a firm and a decay measure that assigns a weight of 1/n for each quarter before the quarter of the breach. Likewise, we measured the social memory of the industry data breach as the decay measure of the firm competitors’ breaches and their decayed influence in the same industry. Similar to Zavyalova et al., we also controlled for the media tenor of the industry, which is measured as the difference between the number of positive and negative articles published about a firm's competitors in the quarter of a data breach and the following quarter.
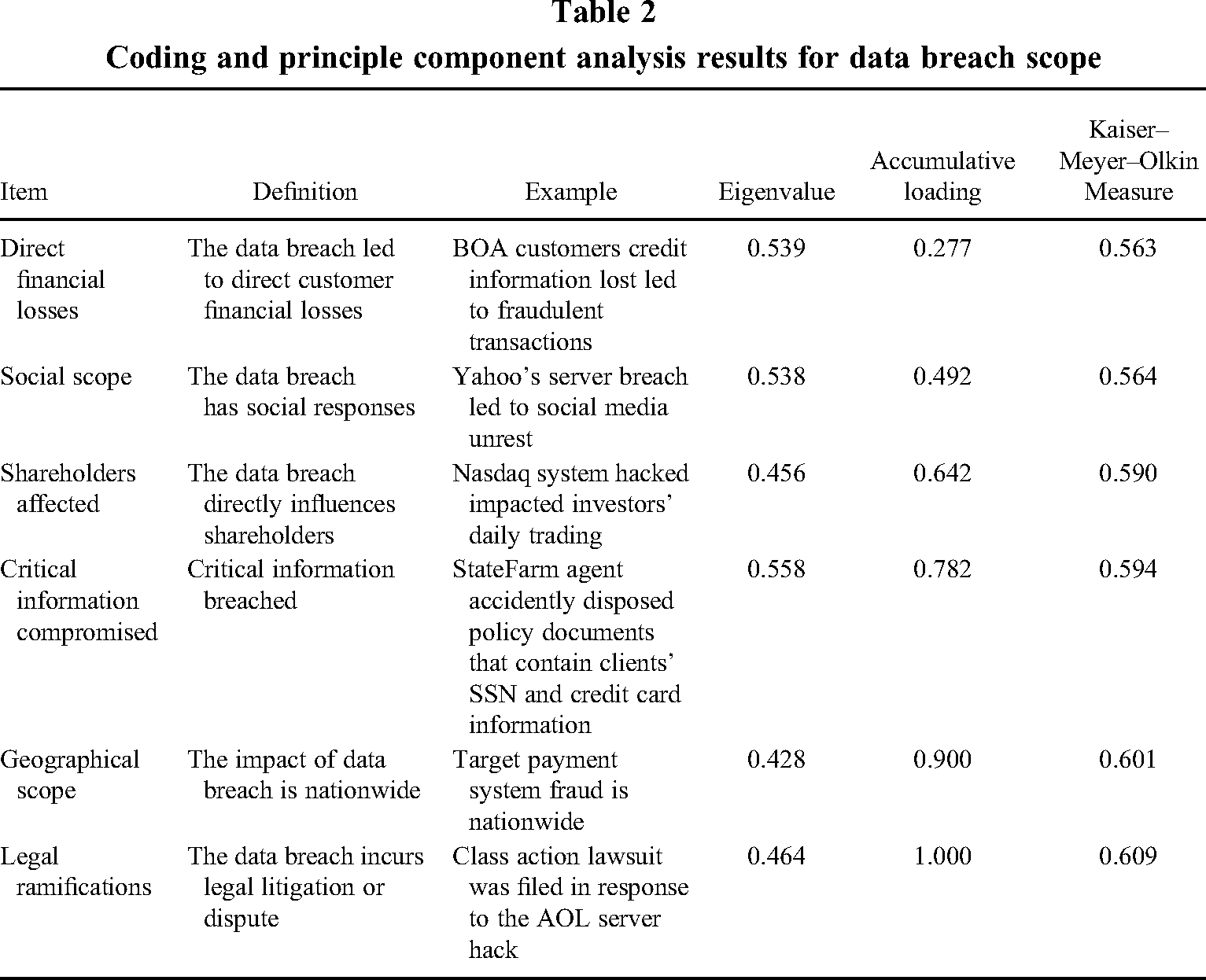
As Zavyalova et al.'s context of toy recalls, breaches that are larger in scope can cause stakeholders to pay closer attention due to their greater potential implications (see Weiner, 2006). Thus, to the extent possible, we captured scope via close proxies to the original study's three control variables: numbers of injuries, scope of incidents, and the average price of toys recalled in a given quarter. Specifically, we coded six dummy variables representing breach scope, including the number of stakeholders affected, social scope, geographic scope, direct financial loss, critical information loss, and legal ramifications (Martin et al., 2017). After conducting a principal components analysis for the six items, we selected five main items that load on the common components and together account for more than 90% of the variance in the data (Xia, 2011). Specifically, we excluded legal ramifications and constructed a single variable measure using weighted items. This method of variable construction is recommended for strategic management research (Boyd, Gove & Hitt, 2005). Table 2 indicates the items, definitions, examples in our sample, eigenvalues, accumulative loading, and Kaiser-Meyer-Olkin estimation for our principal components analysis.
Coding and principle component analysis results for data breach scope
Finally, following Zavyalova et al.'s (2012) caution about potential timing effects, we controlled for the potential variance in breach timing, such as when the Personal Data Privacy and Security Act was introduced (Stevens, 2010) and when the social media era emerged (Kaplan & Haenlein, 2010). All time-variant controls were lagged by one year to help rule out reverse causality (Kenny, 1979).
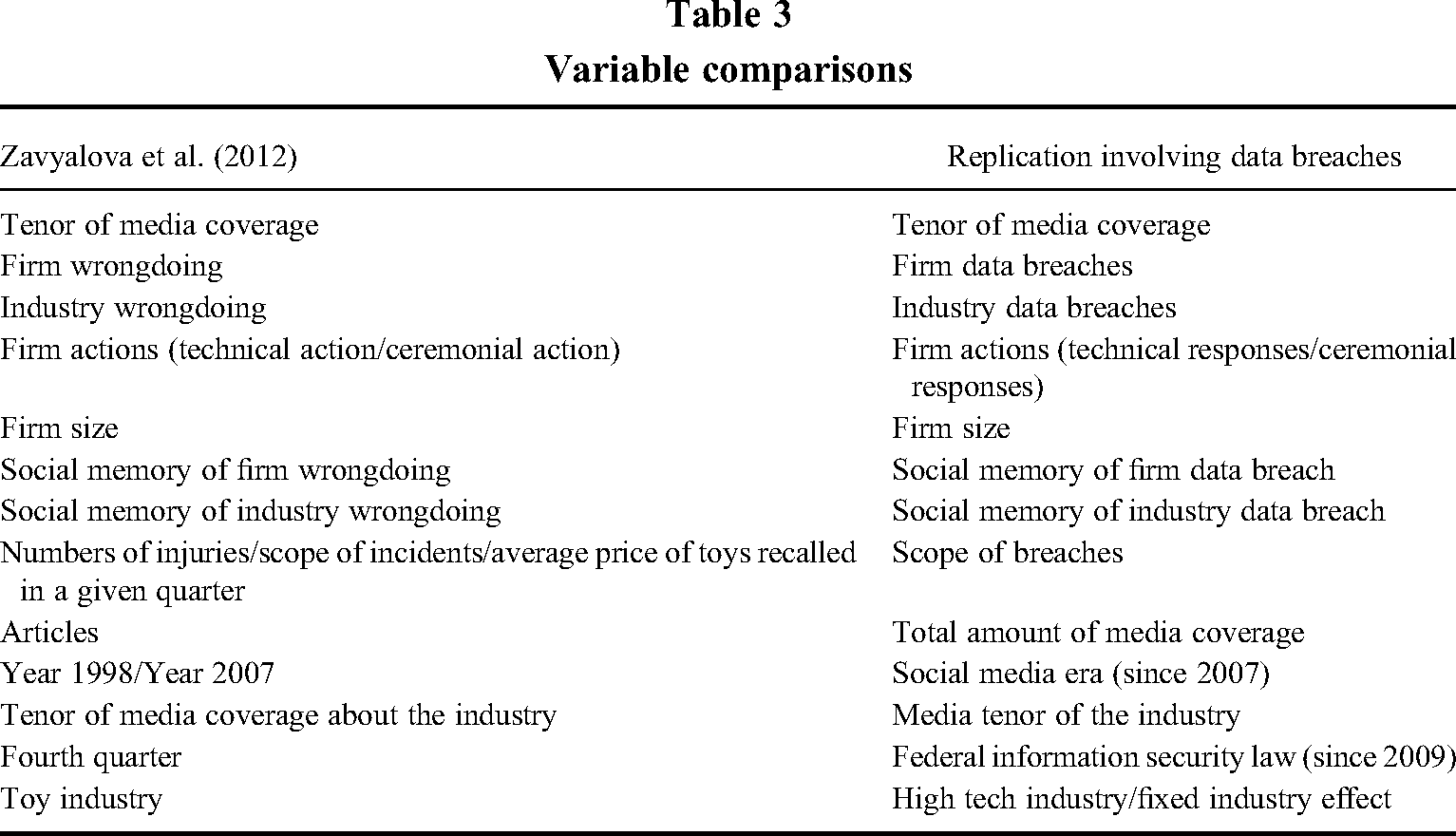
Zavyalova et al. (2012) focused on the toy manufacturing industry. Therefore, we controlled for the high-tech industry and fixed the industry effect. Because high-tech firms are more vulnerable to data breaches due to their relatively extensive cloud computing (Baker et al., 2011), we modeled these effects. Specifically, the American Electronics Association (AEA) identified 45 SIC codes representing a high-technology industry. If a firm belongs to AEA industries, we coded a 1 and a 0 otherwise (Bracker, Keats & Pearson, 1988). Following Mauri and Michaels (1998), we fixed the industry effects using a two-digit SIC. The summary of the variable comparison between the original study and our replication is shown in Table 3.
Variable comparisons
Analytical techniques
We first performed our quasi-replication. The main difference from the original study's analytical method is that we use two a two-stage least squares (2SLS) model with instruments to control potential endogeneity. This is because, after performing an endogeneity test, we found that, in our sample, firms’ data breaches are highly endogenous in the model. In particular, the results (i.e., Durbin test Χ2(1) = 10.86 (p = 0.0010); Wu–Hausman test F(1, 281) = 11.06 (p = 0.0010) reject the Ho: variables are exogenous. We choose firm reputation as an instrument variable in our 2SLS estimation. We measured firm reputation by collecting and coding rankings of the World's Most Admired Companies (Pfarrer et al., 2010). If a firm was listed in the ranking in a certain year, meaning the firm had high media reputation in that year, we coded it a 1 and 0 otherwise (Pfarrer et al., 2010). The main distinction between media reputation and media tenor is that the former emphasizes stakeholders’ assessments of firm actions over a relatively long period (Mishina et al., 2012; Rindova et al., 2005), while media tenor emphasizes the sentiments of media coverage involving a specific event or firm action over a relatively short period (Zavyalova et al., 2012, 2017).
In particular, for an excluded exogenous variable to be a valid instrument, it must meet two conditions: (1) it must be sufficiently correlated with the included endogenous regressors but (2) uncorrelated with the error term (Wooldridge, 2010). Thus, we performed a regression test: F(1, 282) = 21.37 Prob > F = 0.0000 which indicates strong relevance of the instrument variable (i.e., condition 1 is met), and over-identification test: Sargan statistic: 8.0, χ2(12) p-value = 0.125 which failed to reject the Ho that instruments are uncorrelated with the error term, indicating that the over-identifying restrictions are not violated (i.e., condition 2 is met). We reported the first state regression results in Table 5. It shows that firm reputation predicts the firm data breach (β = 1.44, p = 0.000), which indicates the validity of the instrument. We also utilized a recently developed instrument approach (Baum & Lewbel, 2019; Lewbel, 2012, 2018) to further validate our instrument variable, which provided evidence that the instrument variable is exogenous. In particular, we used certain elements of covariates (vector X), such as breach scope, social memory of the firm, and social memory of the industry, to compose vector Z to generate the Lewbel estimator (i.e., constructed instruments). We ensured that the two underlying assumptions (i.e., A1 and A2 assumptions) of Baum and Lewbel's (2019) model were met. We also used the Sargan–Hansen test to examine the validity of both the internally constructed instruments and the external instrument (i.e., firm reputation). Overall, these test results provide evidence that our variables are valid and robust.
Results
Table 4 presents descriptive statistics of unstandardized variables and correlations for the standardized variables of interest. We also examined the variance inflation factor (VIF) to identify potential multicollinearity problems. Guidelines provided by Kutner, Nachtsheim and Neter (2004) suggest multicollinearity is not a problem in our data. Notably, our media tenor variable has a relatively larger standard deviation and a wider range than Zavyalova et al.'s (2012) sample. We believe this is due to several factors. First, our sample covers various industries instead of only focusing on toy manufacturing. This means that a typical negative event, such as a data breach, will attract a wider range of media exposure. Second, the event of a data breach is more salient than the event of toy recall, especially in high-tech industries where a single data breach might invite greater public attention and media scrutiny (Han et al., 2023; Rosati et al., 2017; Schatz & Bashroush, 2016). Table 6 shows our replication results involving breaches. Model 1 in Table 6 includes control variables plus the magnitude of firm and industry data breaches; Models 2 and 3 introduce technical and ceremonial actions, respectively. Model 4 consists of both firm actions, and Model 5 is the full model with interactions. We report a comparison and interpretation between our results involving breaches and the original study's results in Table 7.
Descriptive statistics and intercorrelations
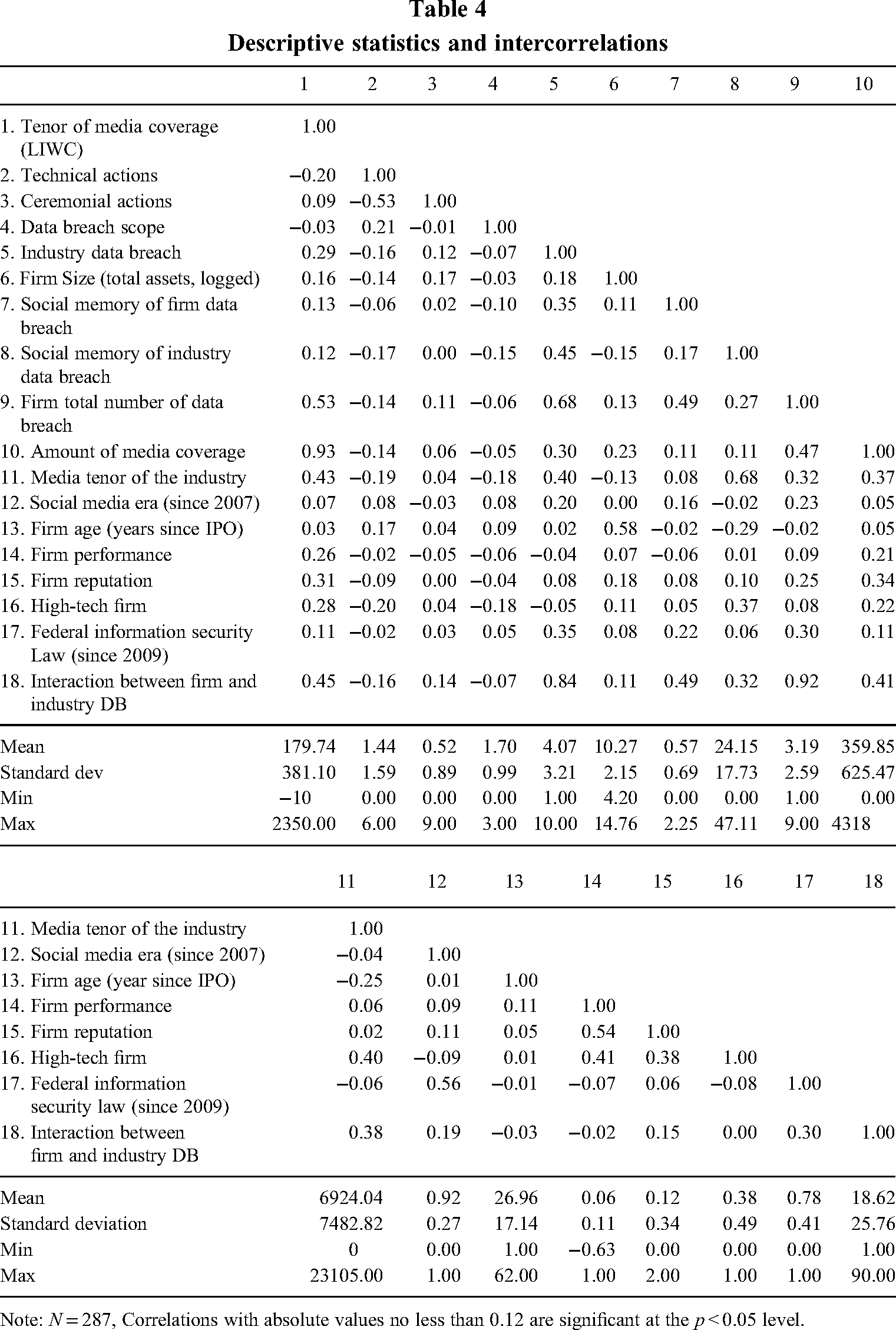
Note: N = 287, Correlations with absolute values no less than 0.12 are significant at the p < 0.05 level.
First stage regression predicting firm data breach
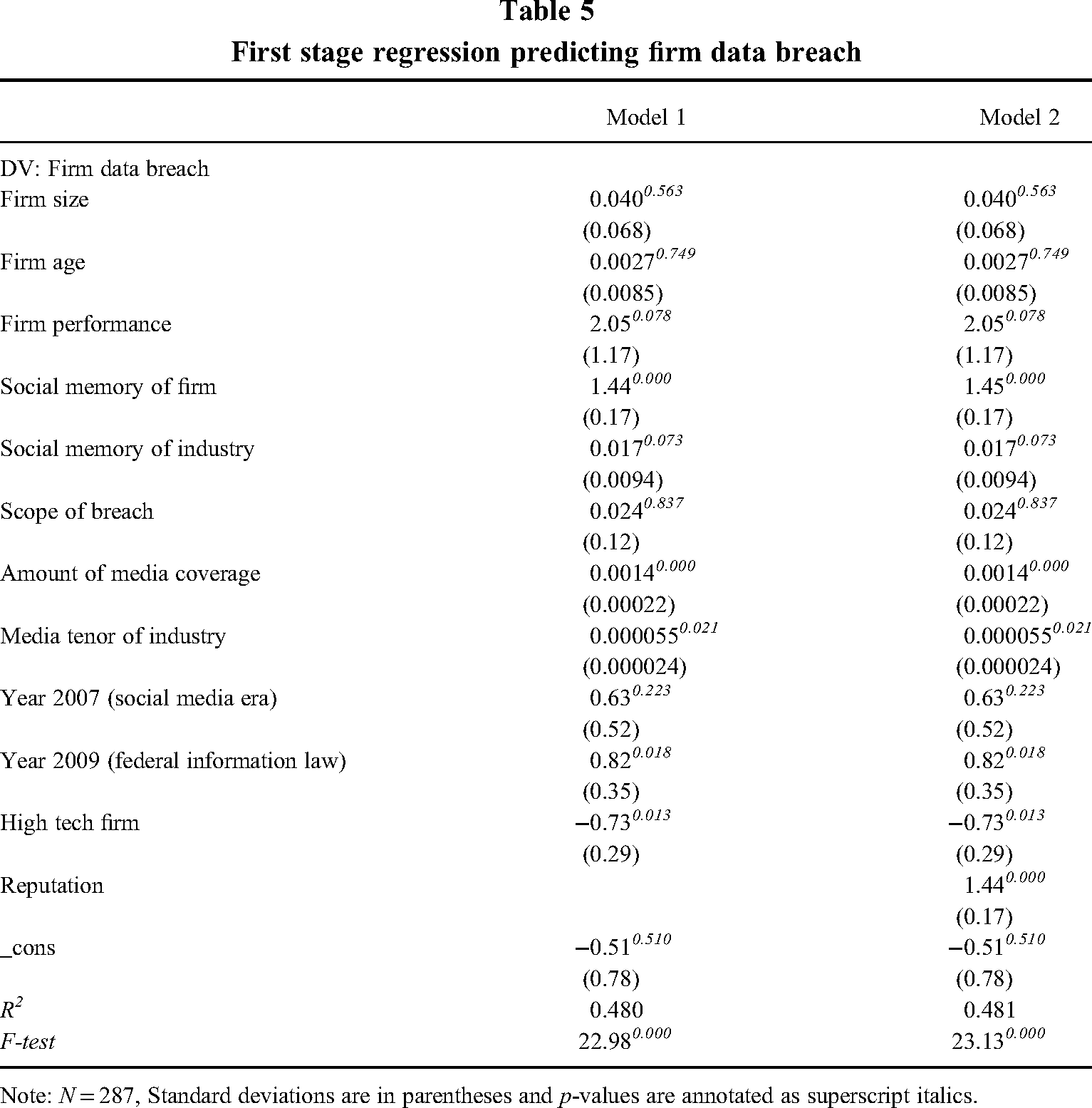
Note: N = 287, Standard deviations are in parentheses and p-values are annotated as superscript italics.
Results of 2SLS regression predicting tenor of media coverage using LIWC approach
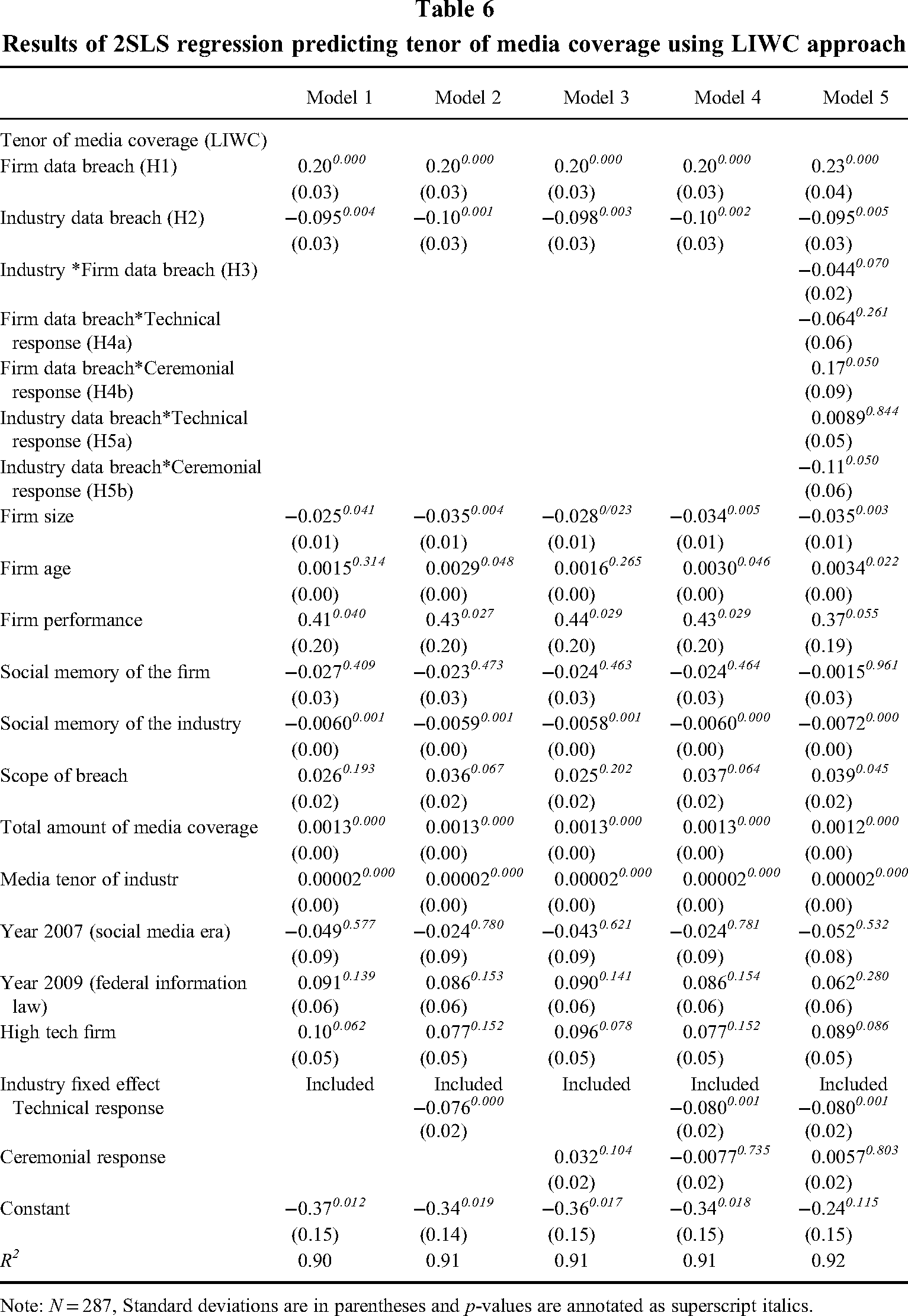
Note: N = 287, Standard deviations are in parentheses and p-values are annotated as superscript italics.
Hypothesis test comparison
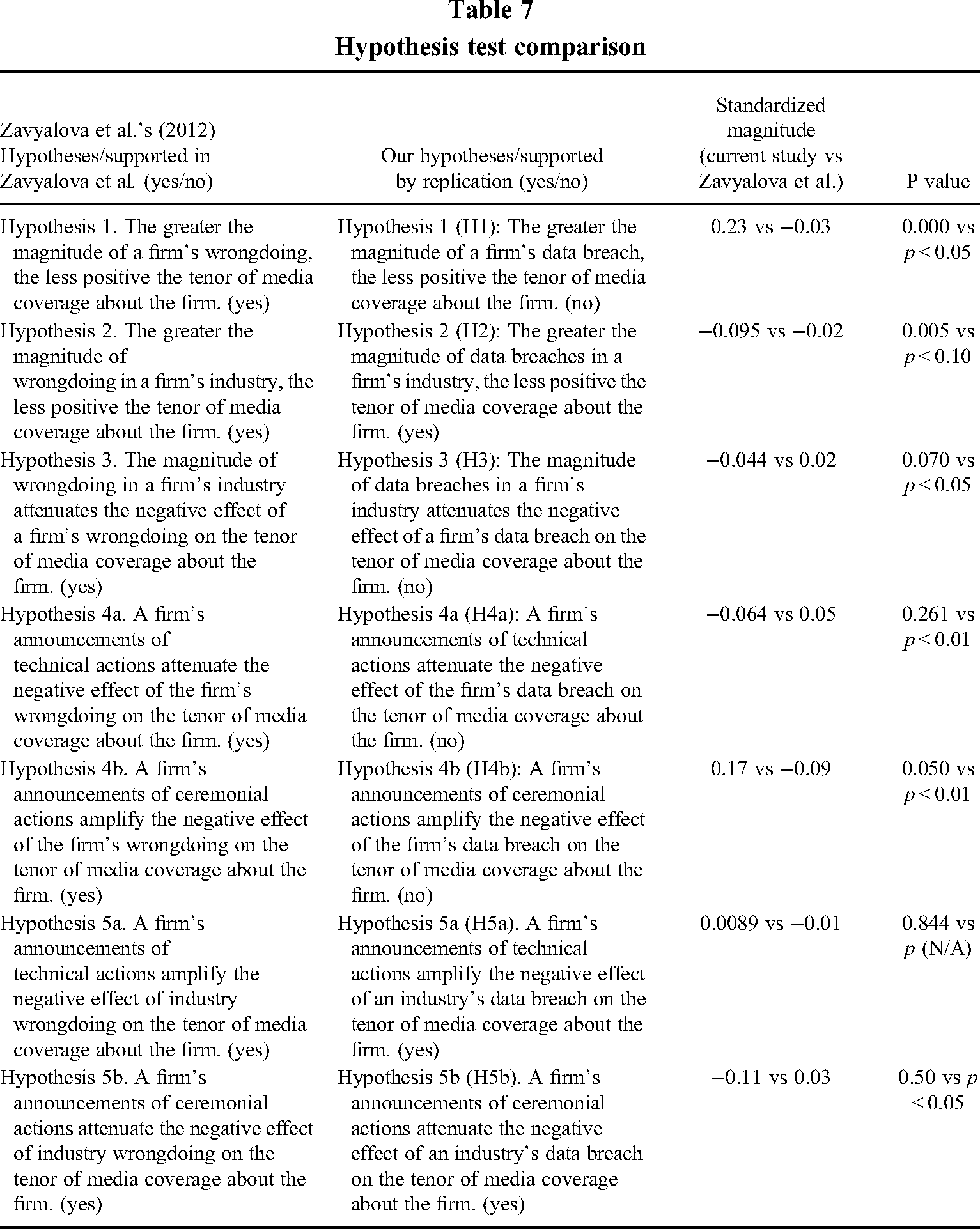
In Hypothesis 1, we predicted that the magnitude of a firm's negative events is less positively related to media tenor about the firm; the results of coefficient and exact p-value in full model 5 are β = 0.23 and p = 0.000. For H1, our results are in the opposite direction of that of Zavyalova et al. In terms of economic/practical magnitude, if one additional data breach occurred to the firm, the number of net positive articles (the number of positive articles – the number of negative articles) published about it would increase by about 88 articles (0.23*381). By contrast, Zavyalova et al. showed a 2-article decrease.
In Hypothesis 2, we predicted that the number of industry events would result in a less positive (i.e., more negative) tenor of the media coverage; the results shown in the full model 5: β = −0.095, p = 0.005. If we interpret the economic magnitude using our full model, when one extra data breach occurred in the industry, the number of net positive articles (the number of positive articles – the number of negative articles) published about it would decrease by about 36 articles (−0.095*381). This is significantly larger than the decrease of 1.5 articles found by Zavyalova et al., but nevertheless provides support for H2.
In Hypothesis 3, we predicted that industry breaches would attenuate the effects of a firm's breaches on the tenor of its media coverage. The results are shown in model 5: β = −0.044, p = 0.070. We followed recent work on interpreting this moderating effect (Busenbark et al., 2022) to include an interaction term in the correlation table and provide an interaction plot. In order to make a more complete comparison with the original study, we report interaction plots for all interaction effects (From H3 to H5b). First, the interaction plot in Figure 1 shows that in an industry with high data breach levels, firms with more data breaches tend to receive less positive media tenor compared to firms in an industry with low data breach levels. For the finding of H3, our results are in the opposite direction of that of Zavyalova et al. By comparing our figure with the original study's figure 1, we discovered that the line of low industry wrongdoing presents an opposite slope than the original study's line.
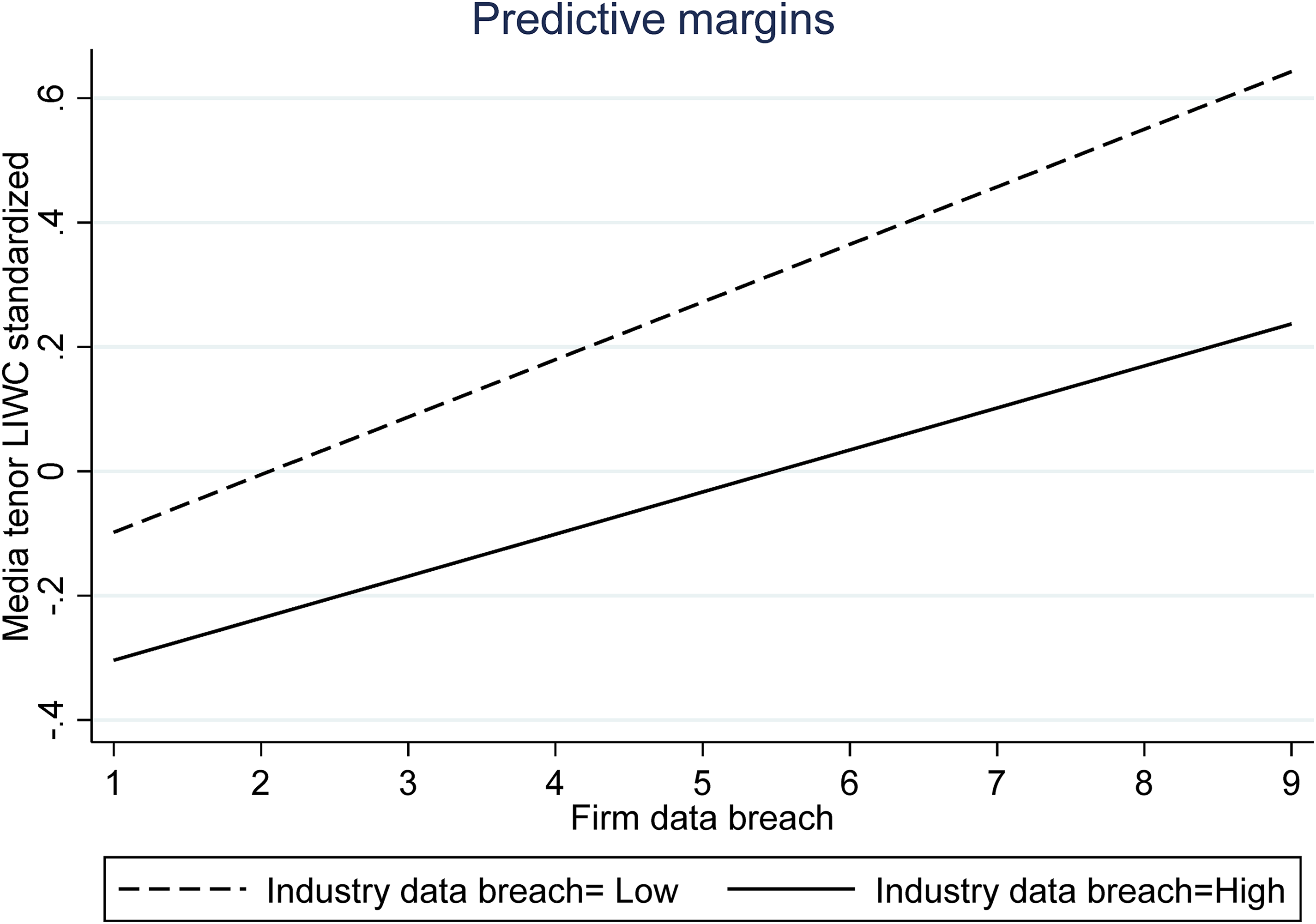
Moderating effect of industry data breach on the relationship between firm data breach and media tenor
In Hypotheses 4a and 4b, we predicted that technical actions (H4a) and ceremonial actions (H4b) interact with firm events to affect media tenor. Specifically, we proposed that a firm's announcement of technical actions attenuates the negative effect of the firm breaches on the firm's media tenor, whereas a firm's announcements of ceremonial actions amplify the negative effect of the firm breaches. The results in the full model 5 for H4a is: β = −0.064, p = 0.261, and for H4b is: β = 0.17, p = 0.050. The interaction plot in Figure 2 shows that when a firm announces a high level of technical actions, firms with more data breaches tend to receive less positive media tenor compared to firms that announce a low level of technical actions. For the finding of H4a, our results are in the opposite direction of that of Zavyalova et al. Similarly, compared with the original study's Figure 2, our slope of high technical actions is opposite to that identified by Zavyalova et al. (2012).
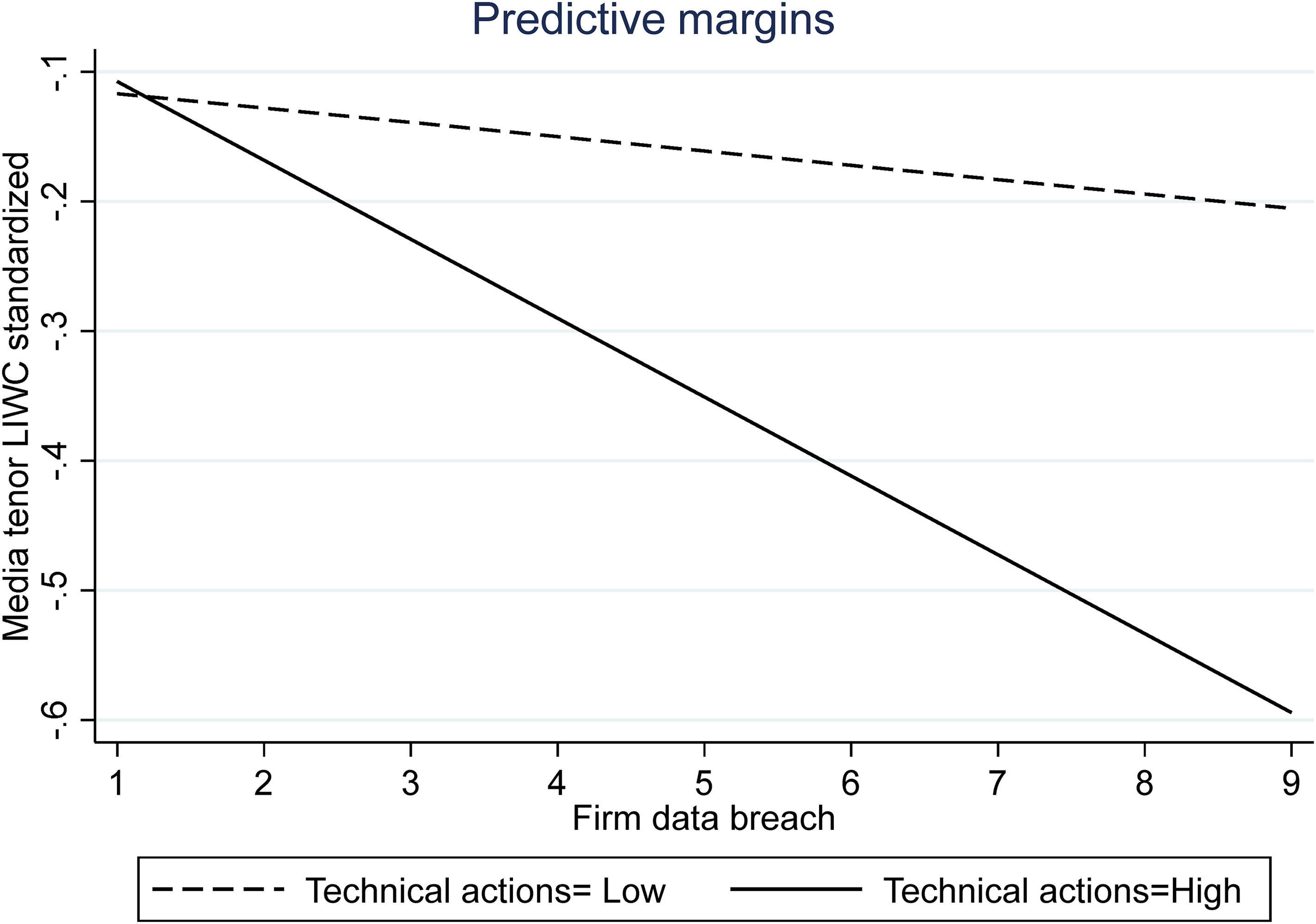
Moderating effect of technical actions on the relationship between firm data breach and media tenor
The interaction plot in Figure 3 suggests that when firms announced a high level of ceremonial actions, those with more data breaches tended to receive more positive media tenor compared to firms that announced a low level of ceremonial actions. For H4b, our results are in the opposite direction of that of Zavyalova et al. Compared with the original study's Figure 3, our slope of high ceremonial actions is opposite to that of the original study.
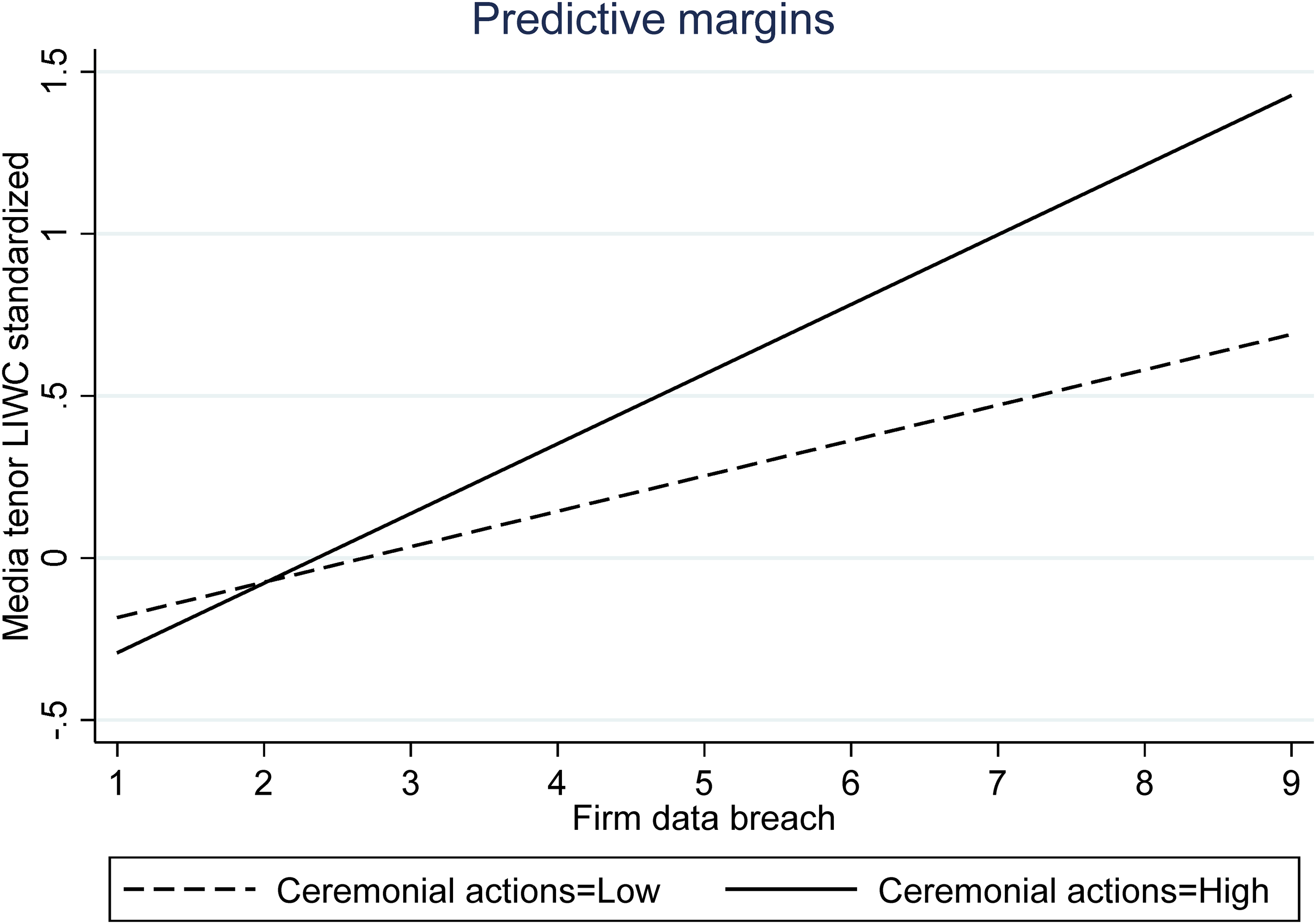
Moderating effect of ceremonial actions on the relationship between firm data breach and media tenor
In Hypotheses 5a and 5b, we predicted that firm announcements of technical actions amplify the negative effect of the industry breaches (H5a) on the tenor of media coverage, but firm announcements of ceremonial actions attenuate the negative effects of industry breaches (H5b) on the tenor of media coverage. The results in the full model 5 showed for H5a: β = 0.0089, p = 0.844 and for H5b: β = −0.11, p = 0.050. The overall effect sizes we found are generally stronger than that of the original study, suggesting that the effect of data breaches on media tenor tends to be greater than the toy recalls studied by Zavyalova et al. (2012). 2
The interaction plot in Figure 4 shows that when a firm announces a high level of technical actions, firms in an industry with high data breach levels tend to receive less positive media tenor compared to firms that announce a low level of technical actions. The results are consistent with the H5a.
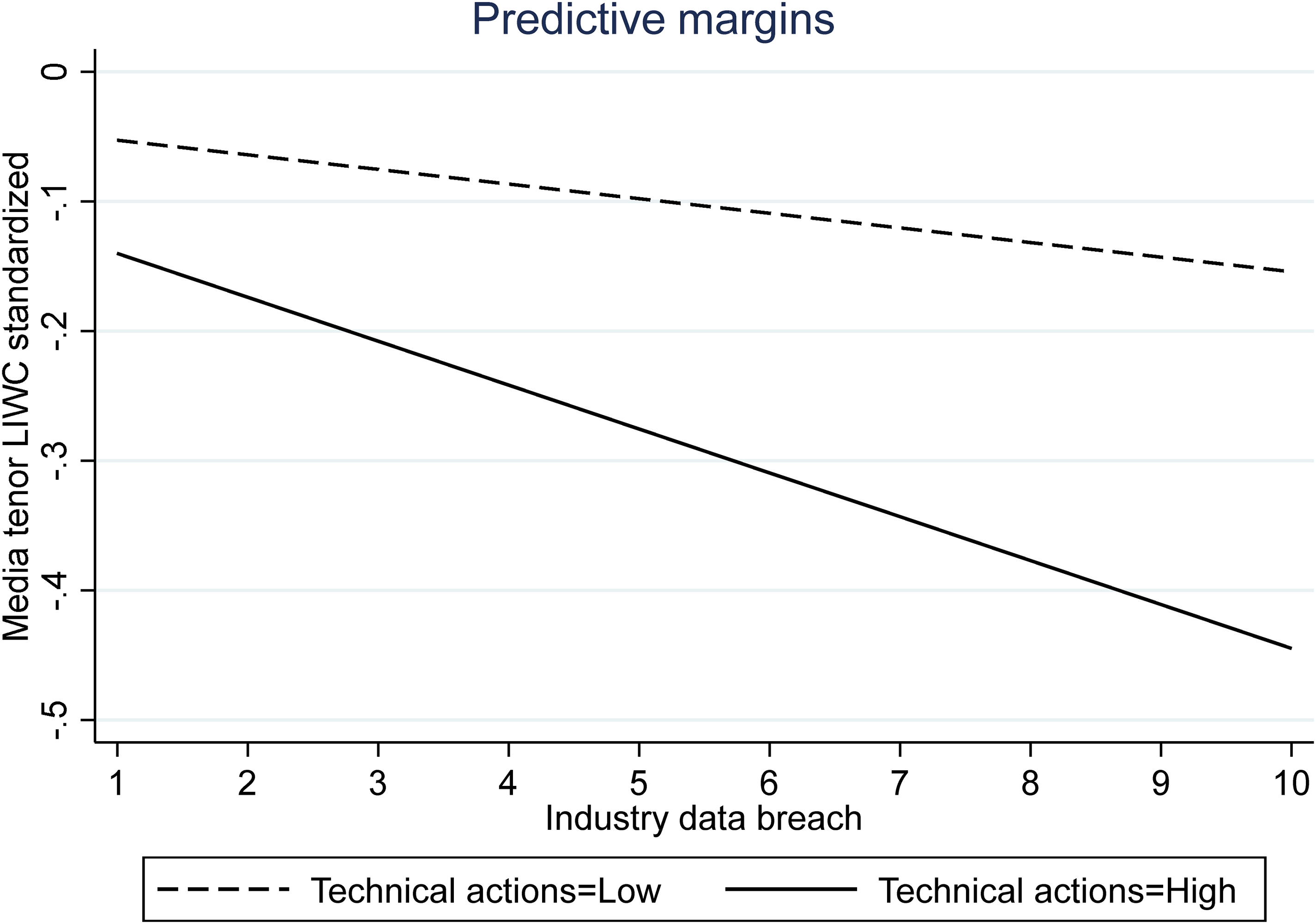
Moderating effect of technical actions on the relationship between industry data breach and media tenor
The interaction plot in Figure 5 shows that when breached firms announced a high level of ceremonial actions, firms in an industry with a high level of data breaches tend to receive more positive media tenor compared with firms that announced a low level of ceremonial actions. The results thus support H5b. Compared with the original study's Figure 4, our line of low ceremonial action slope is in the opposite direction of the original study slope.
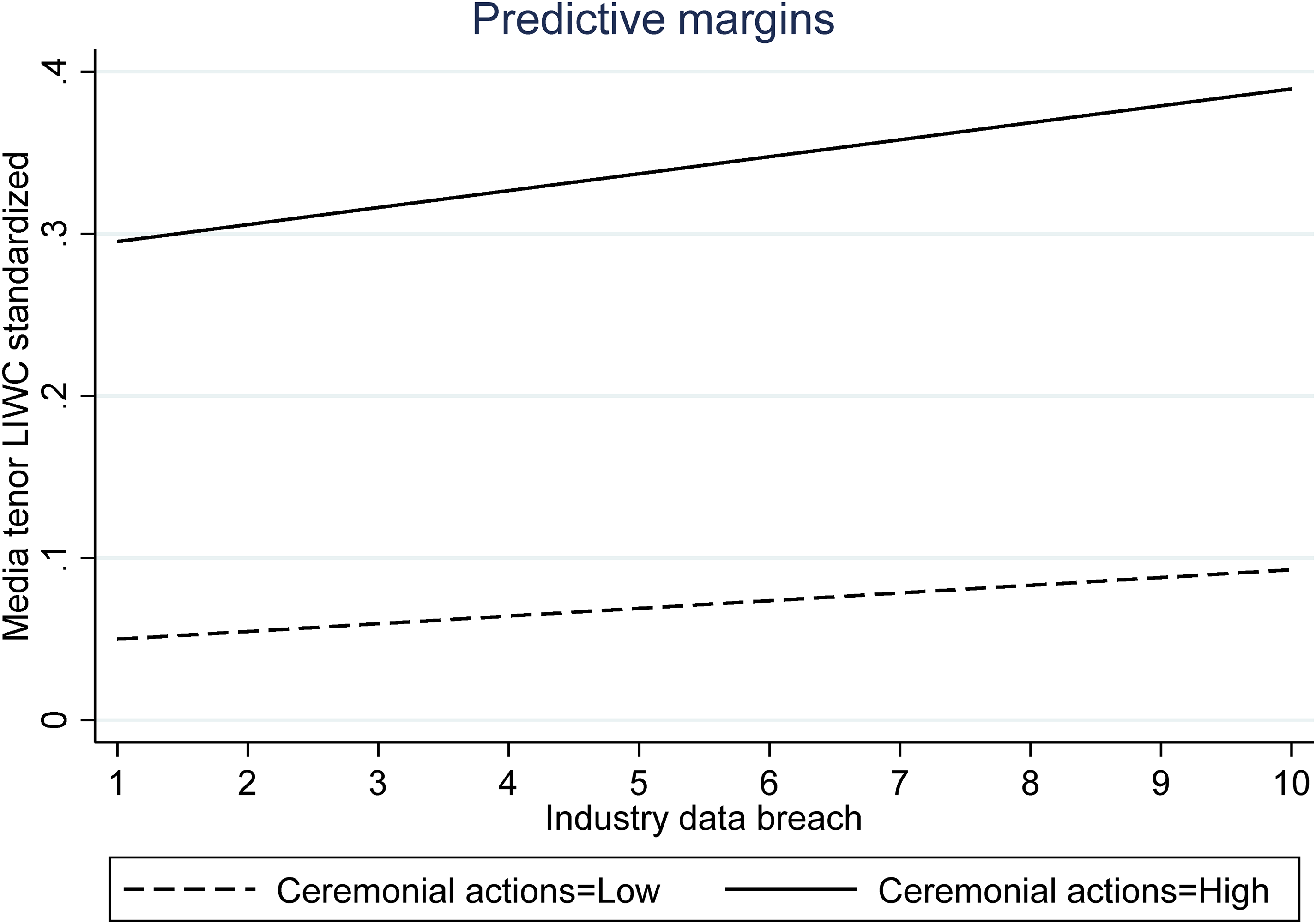
Moderating effect of ceremonial actions on the relationship between industry data breach and media tenor
Robustness analyses
We conducted a series of robustness analyses by altering the data source (RavenPack), analytical approach (non-2SlS estimation), and industry context (only looking at B2C industries). The detailed results and interpretations are included in the appendix. The results of our robustness analyses demonstrated that using different data sources in a replication study can provide further validation for the original study. The robustness check comparison between LIWC and RavenPack approaches reveals that although the magnitude and statistical significance are in general consistent, there are some notable inconsistencies in terms of the direction of estimates; for example, the results of H2, H4b, and H5b show opposite signs of coefficients between the two approaches. In particular, by comparing all three versions of results, LIWC, RavenPack, and the original study, we noticed three key differences. (1) For H2, our RavenPack results are the opposite of that of the original study, whereas our LIWC results are consistent with that of the original study. (2) For H4b, our RavenpPack results are consistent with that of the original study, yet our LIWC results are the opposite of that of the original study. (3) For H5b, our RavenPack results are consistent with that of the original study.
Collectively, these robustness tests reveal important nuanced relationships depending on empirical contexts and data sources. In terms of practical magnitude, RavenPack results indicate that for H1, if one additional data breach occurred to the firm, the number of net positive articles (the number of positive articles – the number of negative articles) published about it would increase by about 2291 articles (0.28* 8183). This is compared with that of the original study, which shows a 2-article decrease. Using an LIWC approach, we found an 88-article increase. Moreover, RavenPack results indicate that for H2, when one extra data breach occurred in the industry, the number of net positive articles (the number of positive articles – the number of negative articles) published about it would increase by about 982 articles (0.12*8183), compared with a decrease of 1.5 articles in the original Zavyalova et al. (2012) study or a decrease of 36 articles using the LIWC approach. Given these practical and statistically significant differences, we advise future researchers to be aware of data source differences that may alter hypothesis tests and practical implications. Ideally, media tenor research should include RavenPack and LIWC approaches, along with comparisons of findings between these two data sources.
In terms of industry context, we replicated the results in both general industries and B2C industries only. By looking at the B2C industries only in our robustness analysis, we attempted to replicate the industry context of the original study closely, and a comparison of general industry and B2C industries shows fairly consistent results (see Appendix Table C). This suggests that our replication study's results can be further generalized to other industry contexts, and further validate the original study's findings that firm actions following a negative event influence media tenor.
Discussion
Organizations are often faced with negative events that jeopardize stakeholders’ well-being, yet it is often unclear how firms should respond. In this study, we replicated many aspects of Zavyalova et al.'s product harm study (2012) to examine how firm responses shape media evaluations following a data breach. In doing so, we explored how theory and findings from prior firm misconduct events generalize to events of firm misfortune (Han et al., 2023; Hersel et al., 2019), including breaches. Data breaches represent an ideal generalizability test because they are pervasive negative events that threaten firms and their stakeholders (Martin et al., 2017), are generally externally initiated, and result in indirect latent harm in contrast to the direct harm of product harm events (e.g., Han et al., 2023; Zavyalova et al., 2012).
Our quasi-replication study showed some key similarities with Zavyalova et al. (2012). First, negative events that happened in the industry can reduce a firm's media tenor (H2), suggesting that firm media evaluations could be sensitive to negative events that occurred in the industry (i.e., spillover effects). Also consistent with Zavyalova et al. (2012), technical actions following a breach amplify (i.e., moderate) the effect of industry data breaches on subsequent media evaluations (H5a). Ceremonial actions attenuate the effect of industry data breaches on media evaluations (H5b).
Yet, in contrast to Zavyalova et al. (2012), our results also shed new light on the contextual differences between product harm and breach events. First, Zavyalova et al. (2012) found firms’ toy recalls are negatively related to media tenor, yet we found a positive relationship for data breaches (H1), which may have resulted from at least two reasons. First, the impact of data breaches may exhibit a short-term nature, given that firms typically initiate responses to address data breaches within a few weeks. Consequently, the negative influence of data breach magnitude on media tenor over the 180-day period might gradually diminish, potentially replaced by a positive tone from the media towards firms’ responses. Second, the existing literature suggests that journalists tend to concentrate on trending topics rather than consistently scrutinizing an event over two quarters (Wang, Reger and Pfarrer, 2021). To investigate the short-term impact of data breach magnitude versus the long-term impact, we conducted a regression of the data breach magnitude on CAR (Cumulative Abnormal Returns) within various windows, particularly within one or two weeks. We found a significant negative effect in the short term, adding credence to this logic.
Second, although Zavyalova et al. predicted the moderating effect of technical action and ceremonial actions on firms’ data breach consequences (H4a and H4b), we found contrasting evidence in our results. These findings might be explained by considering the different attributes of toy recalls and breaches, including the source of the negative event and its direct or indirect harm to stakeholders. Specifically, regarding Hypothesis 4b, negative events caused by internal misconduct are perceived by stakeholders as more salient (Vergin & Qoronfleh, 1998). Thus, when firms respond to product harm incidents, such as toy recalls, via ceremonial actions, stakeholders may view the response as less genuine and less instrumental in addressing harmful causes (Elsbach, Sutton & Principe, 1998; Lyon & Maxwell, 2011). Conversely, the harm to stakeholders caused by data breaches is less direct and may unfold over longer time windows (Han et al., 2023; Rosati et al., 2017; Schatz & Bashroush, 2016). The complex causality associated with data breaches may also obscure the utility of technical responses. In such instances, a firm's ceremonial actions might be perceived by stakeholders as adequate actions that highlight other positive aspects of the firm, or only tangentially related to data breaches.
Last, our series of robustness tests revealed that researchers should be aware of data source heterogeneity, which can affect the convergent validity and practical substitutability of empirical measures. For example, results from using the LIWC approach and RavenPack approach indicate inconsistencies compared with those of the original study. In terms of practical magnitude, RavenPack results show a much larger magnitude than that of either the LIWC approach or the original study and some inconsistencies in terms of the directions of the effect. For example, regarding the relationship between number of breaches and number of positive articles, Ravenpack results suggest a 2291-article increase for each additional breach, compared with an 88-article increase using LIWC and a 2-article decrease in the original study. These robustness tests suggest that scope differences between data sources resulted in these consistencies. In particular, the LIWC includes traditional media coverage such as WSJ and Financial Times, which appeared in only traditional newswires. Yet, RavenPack's methodology includes additional news articles, blogs, and social media coverage of the firm, which is much more comprehensive than LIWC. However, RavenPack's news sentiment score rating technique follows the same principle of calculating positive and negative sentiments as LIWC.
As another point of contrast, RavenPack's rating is less constrained when multiple firms are mentioned in the text because of its independent rating technique. It also covers a broader spectrum of media coverage than Lexis-Nexis. In recent years, RavenPack data have been widely accepted in finance, economics, and accounting literature to measure news coverage and sentiment regarding public firms (Drake, Guest and Twedt, 2014; Ho, Shi and Zhang, 2013; Smales, 2014; Twedt, 2016). Due to these differences, the RavenPack scale of media tenor is bigger and less positive than the LIWC measure, which ultimately bears on the nature of results found leveraging these data sources.
Practical implications
Beyond our theoretical contributions, this paper also offers practical insights for firms and stakeholders. First, industry context is a critically important consideration, and firms should adapt their post-breach responses to accommodate the industry conditions in which they operate. Specifically, our results suggest that negative media tenor is increased for “strays” or companies experiencing a breach in an industry where breaches do not normally occur. Thus, it appears important for firms to maintain “best in class” solutions to reduce exposure to breaches. Such actions may necessitate ongoing communication with internal stakeholders and training to increase awareness of breach risks. Yet, for firms experiencing a breach in industries where they are common, silence may be the best option, lest they make themselves salient and open to critiques by the media. Pragmatically speaking, our results also highlight useful response strategies for companies experiencing a breach or planning communication strategies in response to a breach.
Limitations and directions for future research
There are several potential limitations of this research. First, although a range of stakeholders beyond the media and stakeholders are important (Donaldson & Preston, 1995), we were unable to examine whether breaches affect other stakeholders, including managers and employees. Yet, because breaches may compromise important data that jeopardizes employee or customer privacy and instigate legal actions against the firm (Munyon & Kane-Frieder, 2015), each of these effects may threaten stakeholders as well as the operations and positioning of the firm.
Second, as outsourcing has become increasingly important for firms (Williamson, 1999), another potential limitation is that we were unable to observe whether the breach occurred through systems developed and maintained by the focal firm or via an outsourcing relationship (e.g., enterprise resource software). Also, because so many firms are involved in developing hardware and software (i.e., constellations of partners), it is typically challenging for the media and other stakeholders to pinpoint the direct causes of such negative events. Building on our earlier discussion of attribution theory, more research is needed that integrates theories involving trust and inter-organizational relationships (Connelly et al., 2018).
Third, although our research model is consistent with impression management and attribution theories, we recognize the possibility that other theoretical lenses might also explain media or stakeholder reactions to breaches. For example, upper echelons theory (Hambrick & Mason, 1984) proposes that managerial characteristics and experiences impact firm decisions and responses. Thus, executives with prior experience managing breaches may respond more effectively than those lacking experience, helping the organization learn from and adapt to mitigate future breaches. Similarly, our study primarily focused on general media coverage of breaches without differentiating between traditional and social media sources. Although we controlled for the emergence of social media, studies have found different effects of traditional and social media on speed, emotion, and network diffusion about negative events (Leonardi & Vaast, 2017). Consequently, future research is needed to explore how stakeholders weigh different media forms, including those that originate from company press, social media, and traditional media. Recent research also suggests that firm status impacts the depth of media coverage and how negative events become scandals (Han et al., 2023). Although our purpose was to quasi-replicate Zavyalova et al.'s product harm study, these insights may also shed new light on how data breaches become larger scandals in the media over time. Finally, our replication is not without empirical limitations. For example, due to the differences in model specifications and empirical context, we cannot fully replicate Zavyalova et al.'s (2012) original estimation procedure using the Heckman approach to account for the endogeneity of recalls and actions.
Conclusion
Given the recent growth in breaches alongside their potential negative consequences, we examined how firm responses following a data breach shaped media sentiment of that firm. In doing so, we quasi-replicated Zavyalova et al.'s (2012) toy recall study, finding that breaches do not negatively impact the media tenor of firms. However, industry characteristics and firms’ certain responses can alter the media effects of breaches. We hope that this investigation will stimulate further inquiry into the firm-level implications of breaches and other crisis events.
Footnotes
Acknowledgments
We wish to thank JOMSR Senior Associate Editor Dr. Xavier Martin and anonymous reviewers for their constructive feedback. We also wish to thank anonymous reviewers of SMS annual conference and participants in the University of Tennessee Pathways paper-development workshops.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
