Abstract
To address climatic risks to human security, various climate security risk assessment (CSRA) tools have been developed. We have systematically reviewed 28 such tools against state-of-the-art research to (i) define best practices in CSRAs, (ii) identify related gaps in these tools and derive recommendations on how to address them, and (iii) outline a policy-relevant research agenda. We suggest the following measures to improve CSRA tools: Global South actors need to be more strongly involved in priority setting, conceptualization, risk analysis, and intervention design. CSRA tools should offer geographically disaggregated analyses, transparently explain choices regarding tools’ temporal and geographical foci, and assess their implications for the evidence. In this regard, any type of sampling bias should be avoided. Mixed methods can offer clear advantages to study the context-specific climate security dynamics across different time scales. The main gaps in the tools’ conceptualizations evolve around comprehensive consideration of risk determinants (climatic hazards, exposure, and vulnerability) and complex climate–security linkages, communication of uncertainty, and implementation of validation routines. These factors need to be better accounted for. To advance CSRAs, future research should, for example, develop methodologies to systematically integrate quantitative and qualitative approaches, improve the performance of risk predictions, and develop conflict projections.
1. Introduction
Climate hazards pose serious risks to human security, 1 by, among other things, reducing food availability (Frieler, Schauberger, et al., 2017; Lobell et al., 2011; Ray et al., 2015), threatening physical and mental health (Adger et al., 2022; Obradovich et al., 2018), driving involuntary migration (Petrova, 2021; Sedova & Kalkuhl, 2020), and increasing risk of violence in specific contexts (Koubi, 2019; Mach et al., 2019; O’Neill et al., 2022). At the same time, insecurity reduces people’s ability to address the impacts of climatic hazards, with the potential to trap affected populations in a vicious cycle of vulnerability, climate hazards and insecurity (Buhaug & Von Uexkull, 2021; Flamm & Kroll, 2024; Pereira et al., 2022; Rawtani et al., 2022). Climate change is reinforcing these dynamics. For example, the Sixth Assessment Report (AR6) of the Intergovernmental Panel on Climate Change (IPCC) concludes that global warming will progressively drive involuntary migration and affect conflicts by increasing vulnerability (O’Neill et al., 2022). Therefore, climate change mitigation and adaptation efforts are critical. However, if designed poorly, these efforts can have unintended consequences (e.g., maladaptation, more inequality), further exacerbating insecurity (Adger et al., 2022; Dorband et al., 2019; Schipper, 2020; Steckel et al., 2021).
Sustaining human security in a changing climate is a highly complex and uncertain policy issue with numerous interdependencies, affecting multiple temporal and spatial scales, governance levels, policy fields, and socio-economic contexts. Due to the numerous synergies and trade-offs, appropriate policy and programming choices to achieve the objective are not straightforward, requiring comprehensive assessments (Beaumont & de Coning, 2022; Hoffmann et al., 2023; Kowarsch et al., 2016). Over the past years, academia, think tanks, NGOs, international organizations, and government bodies have produced a wide variety of knowledge about the security challenges posed by climatic hazards. We call this somewhat diverse group of knowledge products 2 climate security risk assessments (CSRAs) (see Section 2). Some of these CSRAs offer concrete tools (e.g., online dashboards, guiding frameworks) to directly support decision-makers with risk analysis. While pursuing the same goal, these tools are conceptualized in different ways. Thus far, little scholarly work focuses on systematically analyzing these efforts. This article offers a systematic review of the existing CSRA tools against the backdrop of the continuously improving scientific understanding showcasing how to assess the complex climate–security dynamics.
Based on expert recommendations and desk research, we identified 28 such tools that were accessible. We reviewed tools focusing on various security risk outcomes (e.g., hunger, conflict), which simultaneously consider climate as a risk factor, and conflict either as an outcome and/or a driver of climate vulnerability. The tools were compared along the following six key dimensions: (1) by and for whom they are produced, (2) their geographical and temporal scopes, (3) applied methodology, (4) choice of variables, (5) considered complex climate–security dynamics, and (6) implementation of validation routines. The goals of this analysis are to (i) distill best practices in assessing climate security risks based on the state-of-the-art scientific knowledge from across disciplines, (ii) identify related gaps of the CSRA tools and derive recommendations on how to address them, and (iii) outline a policy-relevant research agenda. Our paper aims to inform academics interested in policy-relevant knowledge production but also the larger community of academics, policymakers, and practitioners interested in developing credible and effective CSRA tools.
Prior work shows that climate–security links are characterized by complex interactions. They are mediated through various pathways and operate in specific contexts, often in a nonlinear manner (Beaumont & de Coning, 2022; O’Neill et al., 2022). Climatic and other risks can compound and cascade, triggering new, emergent risks (Kemp et al., 2022; Simpson et al., 2021; Zscheischler et al., 2018). Significant progress has been made in understanding the pathways between climate-related events and various insecurity outcomes and the scope conditions under which such risks materialize (Mach et al., 2019; O’Neill et al., 2022; von Uexkull & Buhaug, 2021). For instance, the evidence suggests some climate impacts on social unrest in urban areas (Adger et al., 2021; Ide, Kristensen, et al., 2021; Spilker et al., 2020), high complexity of the climate–migration–unrest association (Ash & Obradovich, 2020; Koubi et al., 2018; Petrova, 2021; Selby et al., 2017), and a significant role of institutional (Detges, 2017; Eastin, 2018; Linke et al., 2018), demographic, economic (Ide et al., 2020), and agricultural production conditions (Ide et al., 2020; McGuirk & Burke, 2020; von Uexkull et al., 2016) in moderating the climate–security linkages. Nevertheless, many gaps in our understanding of these dynamics prevail, concerning, for example, the mechanisms and conditional factors, cascading and compounding risks, long-term climate change impacts on conflict, and conflict potential of various interventions (Buhaug & Von Uexkull, 2021; de Bruin et al., 2022; Kemp et al., 2022; Mach et al., 2020; von Uexkull & Buhaug, 2021).
Our study builds on this knowledge to evaluate CSRA tools and adds primarily to two literature streams. First, we complement other reviews of risk assessment tools. Mostly, these reviews focus on comparing the tools’ performance, by validating them (Bakkensen et al., 2017; Birkmann et al., 2022; Rød et al., 2023; Visser et al., 2020). 3 Given the different tool types (e.g., risk indices, frameworks, early warning systems) in our sample, we cannot directly compare their performance. Instead, we compare the tools conceptually, along the above-stated six dimensions, where science provides clear recommendations for more effectively assessing climate-related security risks. Our study is most closely related to Rod et al. (2023), who review conflict early warning systems (CEWS), which provide quantitative forecasts of large-scale political violence. They review the CEWS along the dimensions: (i) transparency and accessibility in terms of documentation, data, and code availability, (ii) key parameters (e.g., data and methods), and (iii) forecast performance. 4 We complement their work with a review of risk assessment tools with a focus on climate-related security risks, yet we do not impose any methodological restrictions on the tools. We analyze the CSRA tools along different, yet partially overlapping, dimensions more suited to our endeavor. Second, we identify policy-relevant knowledge gaps based on a review of tools developed for decision-making. Thus, we complement various academic papers (e.g., Buhaug (2015), Gilmore & Buhaug (2021), Mach et al. (2020)) setting the research agenda in the field of climate security mainly based on academic research.
The remainder of this paper is structured as follows. In the next section, we detail the systematic identification and evaluation of relevant CSRA tools. In Section 3, we describe the key dimensions, along which the CSRA tools are compared. Section 4 presents the emerging evidence. We conclude in Section 5 by summarizing the main findings and outlining recommendations.
2. Assembling the sample of CSRA tools
Risk assessment is a process, where risk analysis and risk evaluation are jointly carried out. The former refers to a systematic use of information to recognize hazards and related risks, the latter involves judgments about the risk tolerability conditioned upon contextual factors (Rausand, 2011). Following the AR5 of the IPCC, we define climate risk as a function of climatic hazards, and vulnerability and exposure to them (Oppenheimer et al., 2014) and review tools that allow for assessing risks to human security.
To be included in our review, CSRAs have to fulfill the following three criteria: First, they provide tools and materials (e.g., risk score dashboards, guiding frameworks) to support decision-makers in analyzing climate-related security risks independently. Second, while the tools may focus on a variety of security risk outcomes (e.g., hunger, conflict), they simultaneously consider climate as a risk factor, and conflict either as an outcome and/or a driver of climate vulnerability. We included tools, with a broad range of conceptualizations along this dimension. For instance, in some tools, climate is one among many analyzed risk factors (e.g., ViEWS, Global Conflict Risk Index [GCRI]), while in others (e.g., Strata, Weathering Risk (WR)), it is the central element. Third, the tools have to be accessible. We consider tools to be accessible if at least the conceptual documentation along the dimensions relevant for this review (Section 3) is available on the tool website or via a (peer-reviewed and/or non-peer-reviewed) publication. We included several work-in-progress tools (e.g., Strata, Climate Conflict Vulnerability Index (CCVI), Climate Security Observatory [CSO]), only providing detailed tool documentation, along with others offering ready-made products (e.g., ViEWS, Water Peace Security [WPS]). While we did not impose any geographical or temporal inclusion criteria, we searched for tools in English. Moreover, we consider different types of tools (guiding frameworks, risk scores). Despite the large tool heterogeneity (e.g., methodology, importance of climate, type), conceptual insights from the relevant scientific debates can be applied to each of them as they all consider climate hazards as security risks and pursue the larger goal, that is, to foster human security. This allows us to conceptually compare a broad range of available tools affecting decision-making.
To construct the initial sample of potentially relevant risk assessments, we drew on the 10 CEWS reviewed by Rød et al. (2023). We complement this list with 39 assessments identified via an exchange with established climate security experts. Finally, we identified an additional 48 assessments via desk research. The desk research entailed: (i) reviewing the first 50 Google search results applying the query climate security risk assessment tool 5 (the last search was conducted on the 1st of August 2023) and (ii) snowballing, that is, reviewing tools referenced in relevant documents (e.g., Crawford et al. (2015), New America (2023), UNDP (2020),Vision of Humanity (2023)). We evaluate these assessments on their relevance along the outlined inclusion criteria by reviewing the tool documentation on the website and/or in (peer-reviewed and/or non-peer-reviewed) publications.
From the total 97 potentially relevant risk assessments, we dropped 69 based on one or more of the above-mentioned three inclusion criteria. What follows are a few examples illustrating our selection process: For example, based on the first inclusion criterion, we considered but did not include Cascades (Cascades, 2024). While it comprehensively assesses climate security risks, it does not provide any concrete tool. As for the second inclusion criteria, while we included ViEWS, which predicts conflicts using, among other things, climatic variables (Hegre et al., 2019); we did not include the Conflict Forecast as it does not consider climatic variables in its predictive analyses (Mueller & Rauh, 2022). Other examples of excluded tools are Isipedia (Isipedia, 2024), which does not consider conflict in any way, as well as platforms that exclusively monitor conflicts (e.g., ACLED (Raleigh et al., 2010) and UCDP (Sundberg & Melander, 2013)) but do not link them to climate vulnerability. We also excluded data platforms, such as MapX (UNEP and Grid-Geneva, 2024) and Humanitarian Data Exchange (UN OCHA, 2024), which facilitate sharing and visualizing geospatial information. While such platforms might simultaneously include climate- and conflict-related data layers, these are not conceptually connected (e.g., via an index). 6
Our final sample contains 28 CSRA tools, that is, 13 analytical frameworks, 12 risk scores, and 3 tools that provide both (Table 1). Using descriptive analysis, we review the tools along six key dimensions described in the next section.
Systematically reviewed CSRA tools.
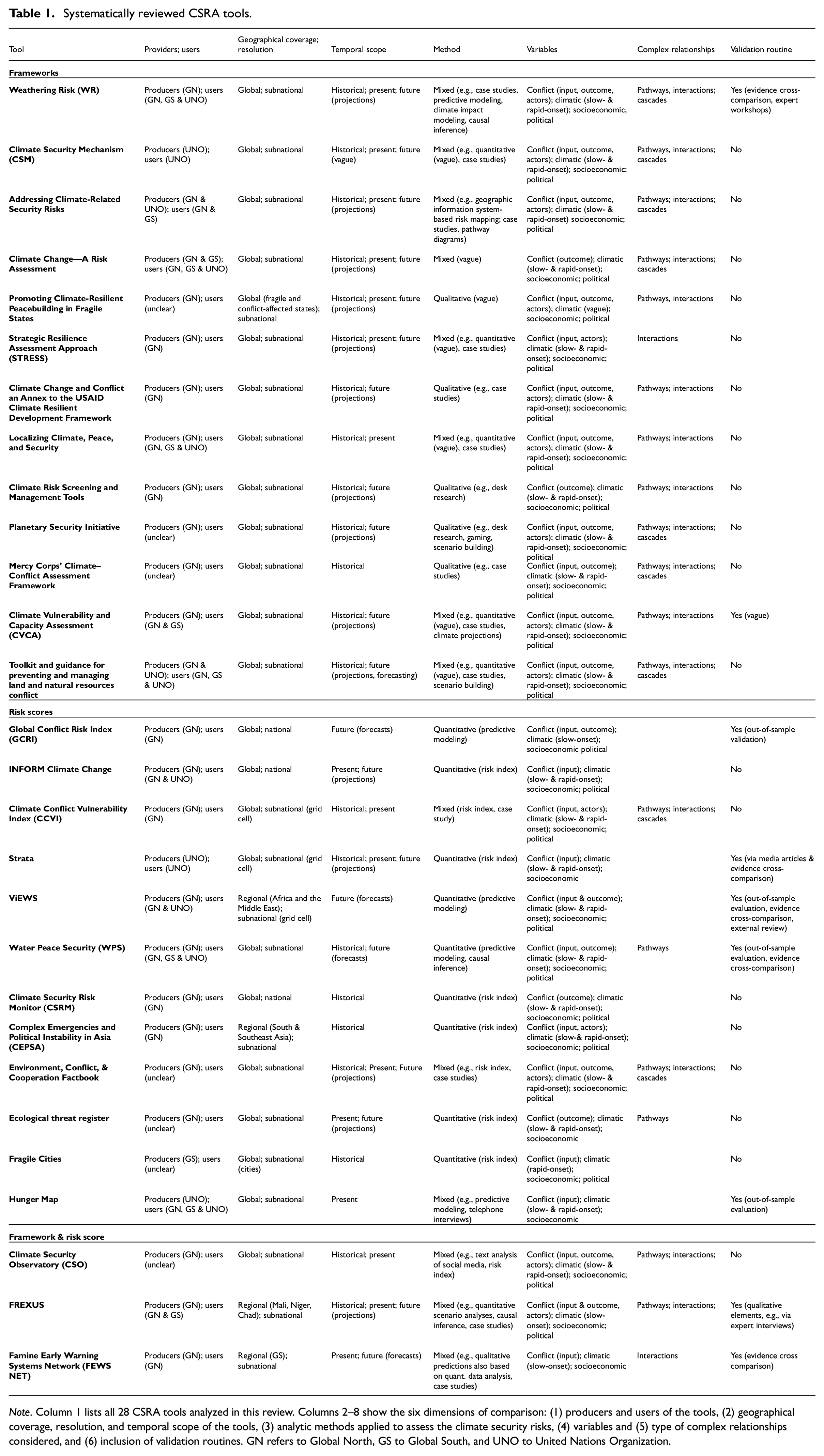
Note. Column 1 lists all 28 CSRA tools analyzed in this review. Columns 2–8 show the six dimensions of comparison: (1) producers and users of the tools, (2) geographical coverage, resolution, and temporal scope of the tools, (3) analytic methods applied to assess the climate security risks, (4) variables and (5) type of complex relationships considered, and (6) inclusion of validation routines. GN refers to Global North, GS to Global South, and UNO to United Nations Organization.
3. Review approach
We code and compare the CSRA tools along the following six dimensions to monitor the gaps between science and policy debates: CSRA producers and users (Section 3.1), geographical and temporal scopes (Section 3.2), applied methods (Section 3.3), considered variables (Section 3.4), complex relationships (Section 3.5), and inclusion of validation routines (Section 3.6).
3.1. CSRA producers and users
CSRAs are a form of knowledge production, and knowledge is ultimately for “someone and for some purpose” (Cox, 1996). By understanding for whom CSRAs are produced and how, we can analyze to what extent the tools are suitable to effectively address risks, and make recommendations for improving them. To this end, we broadly code, whether the producing institutions and target audiences come from the Global North (GN) or South (GS). 7 For conceptual clarity, we code tools (co-)produced or used by a United Nations Organization (UNO) separately, as its member states come both from the GS and GN. These institutions afford a political voice to each member state and nearly all countries make meaningful use of that (Iida, 1988). However, both formal and informal inequalities within the system often allow GN countries to have a disproportionate influence on the workings of the organization and the operationalization of its goals (Blicharska et al., 2021; Novosad & Werker, 2019).
3.2. Geographical and temporal scopes
3.2.1. Geographical scope
To capture the geographical scope of CSRA tools, we code two variables: geographical resolution and coverage. Geographical resolution distinguishes between CSRA tools at the national and subnational (including grid-cell) level. While the more localized analyses allow us to more effectively understand and manage the contextual climate-related security risks (Mach et al., 2019), coarser assessments offer some advantages, especially if the capacities (e.g., technical, financial) are limited. Coarser data are often more easily available and comparable, requiring less manipulation and offering an easily feasible analysis. More granular information, on the contrary, is often much more limited and requires a lot of data manipulation to obtain comparable information over geographies and time. This can lead to higher processing power and time requirements (Ide, 2017). Geographical coverage informs about regional foci of the CSRAs tools, for instance, whether they assess risks globally or look at a specific continent or country. Among other things, the geographical context determines whether and what type of relationship between climate and security risks is revealed, as some regions are more exposed and vulnerable to climate hazards than others (Adams et al., 2018; Hendrix, 2017; O’Neill et al., 2022).
3.2.2. Temporal scope
We further code the temporal scopes of CSRA tools, distinguishing their focus on historical, present, and/or future risks. At different temporal resolutions, CSRAs reveal different dynamics, providing complementary information for policy interventions (Hoch et al., 2021). Contextual analyses of historical and present risks inform entry points for action to reduce them in the future (Mach et al., 2020). To improve the effectiveness of such (preventive) measures and predict the place and time of the uncertain risks, forecasting is typically applied (Rød et al., 2023). It informs current and short-term anticipatory decisions as it aims to produce plausible estimates of risks now and in the near future. To support long-term decision-making, quantitative risk projections are typically applied. They evaluate long-term risks under different assumptions about climate and societal change (Frieler, Lange, et al., 2017; Hoch et al., 2021; Warszawski et al., 2014). To assess (near- to long-term) future risks, one can also draw on the (non-academic) foresight elements such as qualitative projections via scenario building or gaming. Scenario building involves describing different plausible futures and exploring strategies to address the outlined developments. Gaming encompasses the development and testing of scenarios by including human decision-making, where players can observe the implications of their decisions within the game framework (de Bruin et al., 2022; Fetzek et al., 2017; Rüttinger et al., 2021).
3.3. Methods used by CSRA tools
We broadly distinguish between the following methodological approaches typically used to study climate-related security risks: qualitative, quantitative, and mixed methods. Qualitative assessments, typically using case study analysis, help to understand local complexities in the highly contextual climate–security dynamics (Ide, 2017; Nagarajan et al., 2022). Quantitative assessments allow for data-intensive analyses, can detect large-scale trends across geographies and time, and ensure external validity and replicability of the evidence (Ide, 2017).
We distinguish three types of commonly used quantitative approaches, all of which apply some form of statistical learning (James et al., 2013; Shmueli, 2010). First, causal inference is mostly, but not exclusively, implemented via regression analysis and typically characterizes a (causal) relationship between input and output variables, for example, between climatic hazards and potential security risks (e.g., conflict (Burke et al., 2009; McGuirk & Burke, 2020), and migration (Sedova & Kalkuhl, 2020)). Its primary intention is to explain past events. Second, predictive modeling, commonly, yet not solely, implemented via machine learning, is used to predict the likelihood of event occurrences (e.g., conflicts), that is, observations not used to fit the model in the first place (Michelini et al., 2023; Schutte et al., 2021; Shmueli, 2010). It allows accounting for complex relationships and a large number of predictors to produce a risk probability score (Cederman & Weidmann, 2017). Third, geographic information system (GIS)-based risk indices also produce a risk score, yet in a descriptive rather than predictive manner. They assess the spatial distribution of factors shaping the likelihood of climate security risks by mapping quantitative data on risk drivers and integrating them via various, rather simplistic, statistical approaches (e.g., principal component analysis) to a composite index (Bocchi et al., 2006; Ide, 2017; Zhijun et al., 2009).
Finally, combining the diversity in knowledge production techniques via mixed methods could be highly valuable for assessing complex phenomena such as the climate–security links (Beaumont & de Coning, 2022; de Bruin et al., 2022; Ide, 2017). They combine different qualitative (e.g., case studies, literature review, scenario development) and quantitative (e.g., climate impact modeling, statistical learning) elements, which jointly help us to understand the dynamics (Ide, 2017).
3.4. Considered variables
We further assess to what extent CSRA tools consider variables to comprehensively monitor climatic risks to human security, drawing on our definition of risk (Section 2). Specifically, we code whether the tools account for variables capturing climatic hazards (slow- and rapid-onset), socio-economic and political (i.e., governance indicators) vulnerability, and conflicts (as an input, output, or both, conflict actors). Due to this review’s focus on CSRA tools, where conflict is treated either as an outcome and/or a driver of climate vulnerability (Section 2), we code conflict-related variables separately.
Climatic hazards have been shown to increase the risk to human security (Mach et al., 2019; O’Neill et al., 2022). They capture the physical triggers from the climate system, ranging from slow- (e.g., sea-level rise, increasing temperatures) to rapid-onset (e.g., floods, storms) climatic events. We treat them as exogenous events whose consequences are determined by the level of exposure and vulnerability of affected populations (Buhaug & Von Uexkull, 2021; McLeman et al., 2021; Oppenheimer et al., 2014).
The level of exposure and vulnerability to climatic hazards jointly determine the extent to which climatic hazards pose risks to human security. Exposure refers to the presence of a certain system in locations prone to hazards, such as the size of the affected area and the number of people located there. It could also entail, for example, affected ecosystems, agricultural systems, or critical societal infrastructure (e.g., schools, hospitals). Exposure is shaped by demographic factors (e.g., population size, density, settlement patterns) and their dynamic changes (e.g., population growth, urbanization, migration). Vulnerability captures the susceptibility to be negatively affected by climatic hazards and entails aspects of socio-economic and political conditions. While vulnerability increases the climate-related security risks, these again increase vulnerability, potentially trapping populations in a vicious cycle. It is possible to be exposed to climatic hazards but to still have the capacity to withstand their effects; or to be highly vulnerable but have very little exposure to climatic hazards. If either vulnerability or exposure is close to zero, the risk from climatic hazards is also minuscule. In the coding, we focus on the determinants of vulnerability, assuming that in a risk context, exposure is given. Scientists made progress in understanding the structural conditions under which climate security risks exist (Buhaug & Von Uexkull, 2021; Ide, 2020; McLeman et al., 2021; Oppenheimer et al., 2014):
Socio-economic variables of vulnerability: Socio-economic marginalization is the most prominent vulnerability condition (Buhaug & Von Uexkull, 2021). For individuals and households, it manifests via poor resource access, mobility barriers, poverty, and hunger (Erman et al., 2020; Hallegatte & Rozenberg, 2017; Sedova et al., 2020; Thalheimer et al., 2023; Warner & Afifi, 2014). Urban poor typically live on land more exposed to climatic hazards and are disproportionately sensitive to them as well as to the housing and food cost spikes. Insecure land tenure and climate-sensitive livelihoods, on the other hand, drive the vulnerability of rural populations (Buhaug & Von Uexkull, 2021; Chakraborty et al., 2019; Douglas et al., 2008; Hardoy & Pandiella, 2009; Linke & Ruether, 2021; Sietz et al., 2012). At higher aggregation levels, indications of vulnerability are, for instance, (gendered) inequality, dependence on rainfed agriculture and imports of food staples, corrupt and inefficient markets, and poor infrastructure (Bren d’Amour & Anderson, 2020; Detges, 2016; Ide, Ensor, et al., 2021; Mach et al., 2019; Vesco et al., 2021; von Uexkull et al., 2016).
Political variables of vulnerability: While good governance has been shown to enable communities to prepare for and adapt to climatic hazards, poor governance constitutes a driver of vulnerability (Busby, 2022; Gilmore & Buhaug, 2021; Witmer et al., 2017). For example, governments with stronger capacities to deliver services and security, more inclusive political systems, and better access to international assistance are better able to peacefully navigate climatic hazards (Busby, 2022). This also applies explicitly to climate governance, where adaptation and mitigation can reduce security risks and build peace but unintended side effects of such measures can drive insecurity (Doelman et al., 2020; Dorband et al., 2019; Hegazi & Seyuba, 2022; Hunsberger et al., 2017; Steckel et al., 2021).
While climatic hazards can increase the risk of conflict, the association works also in the opposite way. Conflicts make affected societies more vulnerable to climatic events; for example, through adverse health impacts, food insecurity, loss of livelihoods, or by reducing states’ ability to uphold the rule of law. These dynamics can trap societies in a vicious cycle, where climate and conflict vulnerability are mutually reinforcing. Thus, conflicts should serve as input variables (e.g., history of conflict, ongoing conflict) and, depending on the focus, can also be outcomes in CSRAs. Identifying different conflict actors helps to account for different vulnerabilities and understand the associated incentives driving violence (Seter, 2016; von Uexkull & Buhaug, 2021).
3.5. Complex relationships
Climate security risks are characterized by complex interactions via different sectors and systems. They can amplify each other, increasing the overall risk. For example, the climate–conflict association is mediated through various pathways and thus the relationship is highly context-dependent (O’Neill et al., 2022). By interacting and coinciding, climatic and other hazards can compound and the risks can even cascade, e.g., across space and time (Kemp et al., 2022; Simpson et al., 2021; Zscheischler et al., 2018). In this review, we code to what extent CSRA tools consider these complex relationships, focusing on causal pathways, conditional effects, and risk cascades.
Climate–security risk pathways help to understand the mechanisms, that is, how and why these risks emerge. This further informs about the conditional effects, that is, about when these risks emerge and interact with/are compounded by their scope conditions. Within the last decade, there has been some progress in understanding the complex climate–security linkages (Busby, 2018; von Uexkull & Buhaug, 2021). For instance, prominent pathways between climate and conflicts lead through climate-related economic shocks (Mach et al., 2019), which reduce opportunity costs of insurrection (Burke et al., 2009; McGuirk & Burke, 2020) and increase inequality (von Uexkull et al., 2016), leading to higher risk of conflict. However, several knowledge gaps prevail. In addition to scope conditions, indirect pathways (e.g., the climate–migration–conflict links), under which climate security risks emerge, are among the most frequently mentioned research gaps (von Uexkull & Buhaug, 2021).
In our increasingly interconnected world, hazards can also spread across sectors, space, and time in a domino-like cascade (Kemp et al., 2022; Simpson et al., 2021). For example, climatic events drive migration (Petrova, 2021; Šedová et al., 2021). Migration can increase social unrest in the host (He et al., 2024; Petrova, 2021) and peri-urban areas (Gizelis et al., 2021) and contribute to perceived insecurity among migrant populations. Adverse climate impacts in major food-producing regions can affect global food prices (Bren d’Amour et al., 2016; Gaupp et al., 2020; Kalkuhl, 2016), and climate impacts on the spread of infectious diseases could lead to the outbreak of epidemics (Gibb et al., 2020; Shuman, 2010). To comprehensively assess climate-related security risks, the complex linkages should be accounted for.
3.6. Validation routine
Due to their broad use in decision-making, the reliability of the CSRA tools is essential. If assessments are poor, they will lead to inefficient interventions (Visser et al., 2020). We cannot directly compare the performance of the reviewed tools, due to the heterogeneity of the tool types, some of which do not directly allow us to observe the assessment outcomes. However, we code whether they have routines for assessment validation, which helps to improve the tools’ accuracy. Such routines contribute to build legitimacy and trust among the potential users.
There are various approaches to validation. For example, evidence from the assessments (e.g., narratives, risk hotspots) could be compared against the ground truth as a benchmark, which is the validation gold standard (Backer & Billing, 2021). The ground truth can be retrieved via interviews with regional experts, media posts, and impacts of climatic events observed in quantitative data, to name a few examples (Bakkensen et al., 2017; Busby et al., 2018; Mach & Kraan, 2021; Visser et al., 2020). In this sense, the quantitative predictive tools can draw on out-of-sample heuristics, to evaluate the model performance on a test set not used for the model construction (Busby, 2018; Colaresi & Mahmood, 2017; Hegre et al., 2021). This could be advanced by feeding the model with new observations over time and validating against these new data points. Another approach to validation is cross-comparison of the evidence from different assessments and benchmarking against the best practice (Rød et al., 2023; Visser et al., 2020). This could be done even within one tool, where applying different methods (e.g., quantitative and qualitative) could help to cross-verify the findings (Ide, 2017). Transparent and replicable assessments could further enable an external review as another form of validation. Rigorous documentation of the research process and, in the case of quantitative tools, data and code availability facilitate such reviews (Rød et al., 2023). To conclude, these are merely some examples of validation approaches. Given their broad range, we simply code whether the tools have such a routine or not and describe some illustrative cases in Section 4.6.
4. Review findings
In this section, we review the 28 CSRAs tools (see Table 1) against the backdrop of the state-of-the-art research along the outlined six key dimensions: producers and users (Section 4.1), geographical and temporal scopes (Section 4.2), methods (Section 4.3), considered variables (Section 4.4), complex relationships (Section 4.5), and validation routine (Section 4.6). In addition, in the Supplemental Appendix, we offer an in-depth comparative analysis of two tools, WR and Strata, which currently offer state-of-the-art CSRAs to better illustrate trade-offs of different approaches.
4.1. Producers and users
CSRA tools are mainly made by and for the GN. Out of 28 tools, 24 are produced by the GN, with two of these conducted in cooperation with the UNOs and one with the GS. Three tools are produced solely by the UNOs and one by the GS alone. Overall, the tools production is concentrated in the GN and, when “Global South actors take part in knowledge production, it is often through commissioned research for pre-designed projects, or via the hiring of ‘Northern’ expats located in the Global South” (Abdenur, 2021). Strata goes further toward involving the GS actors in the development than most other tools, as it has been co-designed with international and local stakeholders, such as the UN country offices and their partners in Somalia, Colombia, and Haiti (see Supplemental Appendix). While our English query (Section 2) creates a bias toward identifying tools in the English language, such a North-South divide in knowledge production in climate-related (Blicharska et al., 2017; Hoffmann et al., 2021; Pasgaard et al., 2015; Piguet et al., 2018; Siddiqi, 2022) 8 and other disciplines (e.g., global health (Yegros-Yegros et al., 2020)) has been identified before. There are some indications of the underlying causes, such as the disproportionately higher wealth and research spending in the North compared to the South (Trisos et al., 2022).
As a next step, we assessed who the tools are made for. The target audience of the CSRA tools can be somewhat ambiguous, as 7 of the 28 tools list no clearly defined target audience (e.g., “policy/decision-makers/practitioners”). Of the remaining 21 tools, 19 list GN institutions as the target audience, 10 list international organizations such as the UN World Food Programme, and only nine tools mention GS users. While WR lists the African Union among its potential users (see Supplemental Appendix), most CSRA tools only refer to GS institutions in abstract terms (e.g., local communities or national governments) or as the country branches of UN organizations and GN-based NGOs. Again, we see actors from the GS are underrepresented among the intended users of these tools.
The underrepresentation of GS actors in all steps of the development and implementation of the CSRA tools partially reflects the criticism that CSRA tools work toward the developmental, humanitarian, and security agendas of donor countries in the GN (Abdenur, 2021; Maertens, 2018; McDonald, 2013). When actors from the GS participate, it is largely not in agenda-setting roles. This creates important gaps. For example, none of the tools offer specific recommendations on how to interact and engage with the goals of local actors or discuss how international organizations should navigate domestic political challenges (e.g., How does a recent military coup change the necessary strategies?). This is limiting the types of questions asked, solutions proposed, and ultimately the effectiveness of the tools (Daoust & Selby, 2022). Without meaningful participation from the GS, GN might define climate security in a way that has little relevance or salience in the most affected countries, risking not including the perspectives of the most vulnerable ones and side-lining calls for justice (Amador-Jimenez et al., 2024; Blicharska et al., 2017; Karlsson et al., 2007; Nalbo, 2024; Pasgaard & Strange, 2013).
4.2. Geographical and temporal scopes
4.2.1. Geographical scopes
As for geographical coverage, the CSRA tools demonstrate a strong focus on Africa and Asia. While 24 of the 28 tools have a global scope (see Figure 1a), this disguises the fact that all case studies assess risks in low- and middle-income countries in Africa, the Middle East, Southeast Asia, and/or Pacific island states. The four remaining tools have a similar regional focus. For example, ViEWS assesses risks in Africa and the Middle East, FREXUS in Mali, Niger, and Chad, and Complex Emergencies and Political Instability in Asia (CEPSA) in 11 countries in South and Southeast Asia. Our findings reflect the streetlight effect on Africa and Asia in climate and conflict research, caused by factors related to research convenience, including conflict data availability or country accessibility. As a consequence, the research field has produced evidence of some climate and conflict association. While such biases do not affect the validity of a particular study, they produce an imbalanced state of knowledge in a given field, which can lead to overlooking of policy-relevant cases (e.g., where climatic stress has led to peaceful cooperation) and contribute to resource misallocation (Adams et al., 2018; Hendrix, 2017). 9 Whether the CSRA tools are similarly biased depends on why their geographical foci were picked in the first place. Often, the assessment of specific regions is a consequence of pragmatic considerations, including strategic interests of the providers or limited funding, rather than convenience. For example, the particular attention to the Sahel among the tools is a product of its high rates of violence and potential migration flows toward Europe, which is strategically important to European decision-makers (Charbonneau, 2022; Daoust & Selby, 2022).
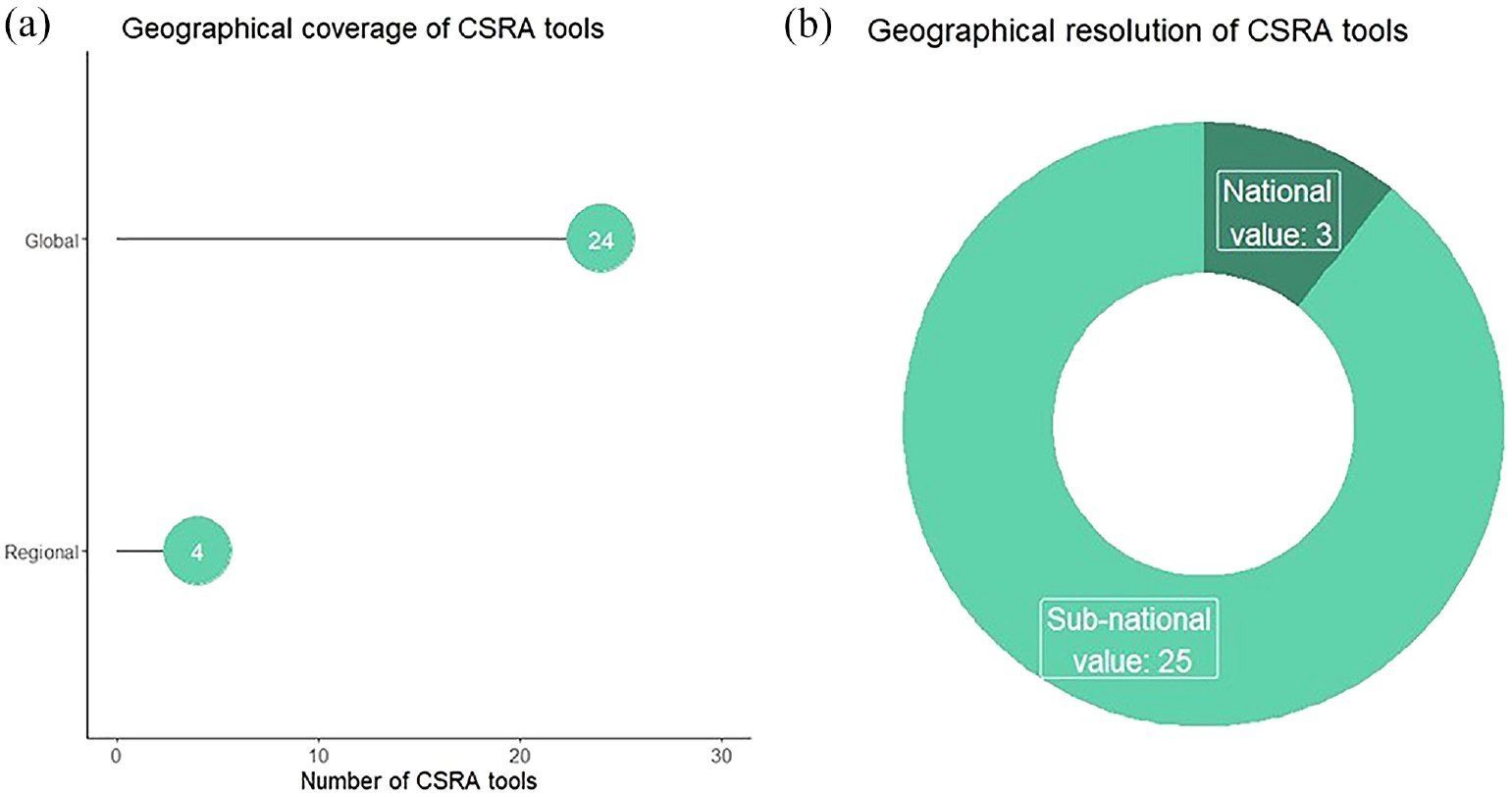
Geographical scopes (coverage (a), resolution (b)) of 28 CSRA tools.
As for the level of granularity, three risk score tools (GCRI, INFORM, and Climate Change and Climate Security Risk Monitor [CSRM]) are conducted at the national level, which can be useful for detecting countries at risk. Yet, most of the tools (25 out of 28) allow for a subnational analysis, including tools at the grid-cell level (e.g., ViEWS) and one (Fragile Cities) focusing on urban fragility (see Figure 1b). This reflects the scientific aspirations toward a localized understanding of the climate–security dynamics (Beaumont & de Coning, 2022; Ide, 2017). This might be easier to implement via approaches with qualitative components (see Section 4.3) as they are less restricted by the availability of quantitative data. However, thanks to the increasing availability of better quantitative information (Ide, 2017), also most of the quantitative risk score tools allow for subnational analysis.
4.2.2. Temporal scopes
Most of the tools (22 out of 28) assess historical climate security dynamics (Figure 2). For example, analytics of CCVI and CSRM are based on historical information only. There are also tools that, in addition, assess present (e.g., Climate Security Dialogues, part of the CSO, collects social media content related to climate security since January 2014) and even future (e.g., WR and Strata) risks. Out of the six tools that do not assess historical risks, some use historical information indirectly. For example, ViEWS and GCRI forecast the risk of conflict ahead of time while drawing on historical data to train the models. In all, 16 tools assess present risks. For example, one of the objectives of Strata is to track environment and climate stress hotspots in near-real time. Similarly, HungerMap aims to monitor food security trends in near real time.
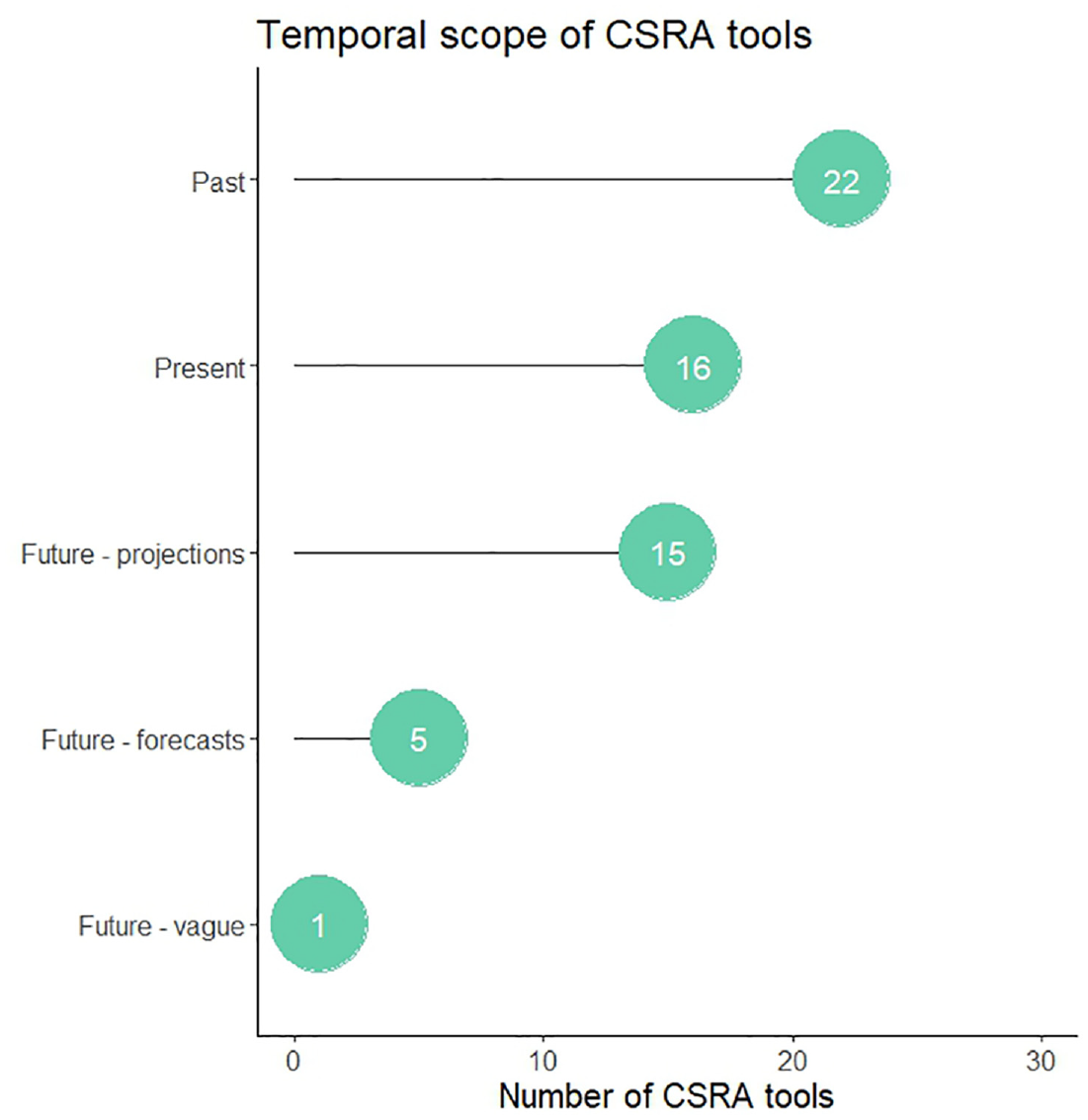
Temporal scopes of 28 CSRA tools.
Lastly, 20 tools assess future risks: 14 use only projections, four use only forecasting, one tool draws on both forecasting and projections, and the remaining one (CSM) remains vague about how their forward-looking assessment is implemented. Forecasting tools analyze what will happen in the foreseeable future (de Bruin et al., 2022) and mostly focus on a measure of conflict as an outcome. For example, ViEWS produces monthly conflict forecasts in a 3-year window, and WPS forecasts conflicts over the next 2 months and a 12-month period. FEWS NET tool is an exception in terms of predicted outcome, providing forecasts of current, near- (the first 4 months ahead), and medium-term (the second 4 months ahead) food insecurity. While advances in data and modeling enable higher out-of-sample accuracy of machine learning-based forecasting (Cederman & Weidmann, 2017), the models still perform much better at predicting the locations rather than the timing of conflict escalations and their onset (Hegre et al., 2019; Mach et al., 2020; Mueller & Rauh, 2022; Rød et al., 2023). Such forecasting seems to be especially relevant for predictions with a limited spatio-temporal scope, such as violence forecasts in a given city with an ongoing war (Cederman & Weidmann, 2017; Rød et al., 2023).
Quantitative future projections typically consider much longer time horizons under different Representative Concentration Pathways (RCPs) 10 (IPCC, 2014), possibly combined with the Shared Socio-economic Pathways (SSPs) 11 (Riahi et al., 2017). They entail projections of various security risks. For example, INFORM Climate Change projects risk of humanitarian crises and disasters globally under RCP4.5 and RCP8.5 combined with SSP1 and SSP2 by 2050 and 2080. WR provides projections of climate change and sectoral climate impacts under RCP2.6, RCP6.0, and SSP2 by 2080 in regions of interest. FREXUS shows projections of conflict until 2050 under RCP8.5 and under a medium and high population scenario based on SSPs. Other tools only vaguely recommend to include projections of security risks under different climate change scenarios.
In academic research, quantitative projections of climatic indicators (e.g., sea-level rise (Mengel et al., 2018) water availability (Schewe et al., 2014)) and related sectoral impacts (e.g., migration (Rikani et al., 2022)) have been widely applied. Rigorous long-term projections of conflicts are, however, mostly absent (von Uexkull & Buhaug, 2021). This is largely due to methodological challenges to specify causal mechanisms and processes explaining conflicts (Mach et al., 2019; von Uexkull & Buhaug, 2021), and their perceived limited usability in decision-making (de Bruin et al., 2022). Conflict projections can be useful, for example, to better assess climate change impacts or as an input to projections of other sectoral impacts sensitive to conflict (de Bruin et al., 2022; Hoch et al., 2021), such as food security (Anderson et al., 2021) and displacement (Bohnet et al., 2018). However, projections have generally been criticized as the future might look very different than the past due to the complex ways in which climate and societal change operate (de Bruin et al., 2022; Tubi et al., 2022). This is particularly relevant for the climate–conflict relationships, where the multifaceted nature of climate change is combined with the dynamic and continuously evolving nature of affected societies and their ability to adapt, which often adds to compounding and cascading effects on security (Beaumont & de Coning, 2022).
The complementary role of expert elicitation and qualitative scenario development has been advocated for as it can help address methodological challenges of quantitative projections and forecasting (Hoch et al., 2021). For instance, qualitative approaches could account for highly disruptive events currently not part of the SSPs, plausibly interpret the quantitative scenarios, address the fact that conflict risks are dynamic and unstable over time, or incorporate on-the-ground experiences (de Bruin et al., 2022). There are four tools, WR, Planetary Security Initiative, Climate Change and Conflict an Annex to the USAID Climate Resilient Development Framework, and FEWS NET which apply this approach.
4.3. Methods used by CSRA tools
First, Figure 3 shows that 19 tools have some qualitative methodological components. Mostly, it is localized context analysis via case studies (e.g., WR, CCVI, and Environment, Conflict, & Cooperation Factbook, and Localizing Climate, Peace and Security) but some tools also apply other approaches, such as telephone interviews (HungerMap), scenario development (e.g., WR, Climate Change and Conflict an Annex to the USAID Climate Resilient Development Framework), or analysis of social media debates (CSO). Out of these 19 tools, 14 combine the qualitative with quantitative approaches in a mixed-methods framework (see below). Qualitative research is suited to assess localized factors (e.g., power relations, institutions to cope with intergroup tensions) that vary considerably on the microlevel and for which quantitative data are often unavailable (Ide, 2017; von Uexkull & Buhaug, 2021). It can identify new dynamics and variables shaping the climate–security association in ways quantitative methods cannot (Ide, 2017).
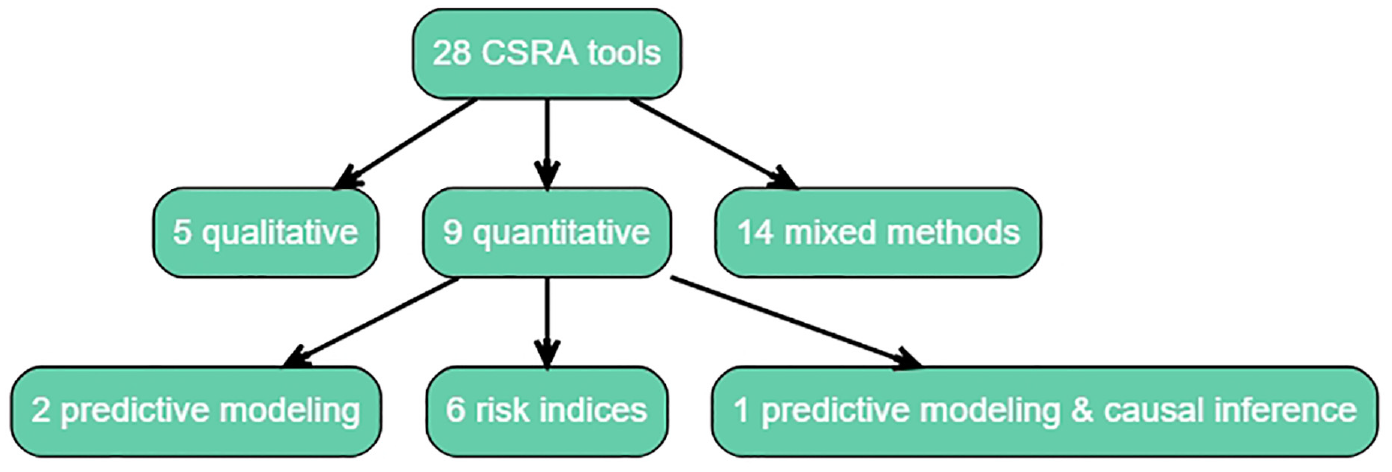
Methods of 28 CSRA tools.
Second, 23 tools have quantitative methodological components. Six of them use predictive modeling, to predict either conflict (GCRI, ViEWS, WR, and WPS) or food insecurity (HungerMap, FEWS NET) in the near-real time and/or future. WR and WPS additionally apply causal inference techniques from statistical learning to test pathways between climate and conflict. Nine tools provide risk indices to map climate security risks (e.g., CCVI, Ecological Threat Register, Strata), humanitarian crises (INFORM Climate Change), or climate vulnerability (CEPSA). Furthermore, FREXUS draws on several quantitative elements such as causal models and climate and conflict projections. Finally, the remaining tools emphasize the use of quantitative methods and also partially provide an overview of relevant quantitative data sources to be used but they do not specify the approaches to evaluate these data. All of the tools that are rather vague about the quantitative methods are frameworks.
Quantitative assessments allow for data-intensive analyses, help to detect large-scale trends across geographies and time, and ensure external validity and replicability of the evidence. Their challenges are different compared to those of qualitative analyses, which often require fieldwork with substantial organizational arrangements, language, and financial requirements and involve risks to personal safety. Quantitative assessments remain restricted by data availability and construct validity. 12 Yet, some progress in data quality can be observed, enabling more detailed and better analyses (Ide, 2017).
Moreover, different quantitative methods are associated with different trade-offs. Statistical causal inference helps to detect (causal) relationships between climatic hazards and various security outcomes. The trend toward, for example, inclusion of interaction terms or subsample analyses has improved the understanding of the indirect effects (Hoffmann et al., 2021; Ide, 2017). Yet, while causally related, these variables might be weak predictors of security risks (Michelini et al., 2023; Schutte et al., 2021). Predictive modeling can account for a large number of parameters and complex linkages, such as those between climate and security. Yet, predictions also come at the price of reduced interpretability as tracing back the most important predictors and thus generating entry points for interventions is often difficult (Hegre et al., 2017; Mach et al., 2019; von Uexkull & Buhaug, 2021). Moreover, these models have only limited explanatory power (Section 4.2.2). Risk indices are used to map the spatial distribution of factors, shaping the likelihood of climate security risks. Compared to predictive modeling, they are methodologically simpler, generating scores based on overlapping risks using GIS techniques. They facilitate the integration of diverse data, which helps understand the scope conditions and thanks to their simplicity, they are also accessible to non-scientific audiences. However, such simplified indices often fail to correctly account for complex relationships and collinearity among variables so that one hazard might be mapped multiple times, misestimating the risk (Halkia et al., 2020; Ide, 2017).
Third, 14 tools apply mixed methods, yet their methodological components differ. Three are risk score tools. CCVI offers a risk index to monitor climate and conflict vulnerability. It is informed by one qualitative study focusing on farmer–herder conflicts in the Sahel. HungerMap uses telephone interviews to monitor food insecurity. The missing information is complemented with a quantitative predictive model. Environment, Conflict, & Cooperation Factbook provides a hotspot map of environmental conflicts and cooperation globally and assesses selected occurrences via case studies. Furthermore, three mixed-methods tools offer a combination of a risk score and a framework. Applying quantitative and qualitative approaches, CSO evaluates textual information from social media to monitor climate security risks. The evidence can be retrieved via an interactive dashboard. The tool also offers guiding documents, such as conceptual diagrams illustrating climate security pathways. FEWS NET offers an early warning of acute food insecurity via a forecasting tool and supports stakeholders by offering guiding documents. FREXUS guides practitioners on how to assess climate security risks to develop and implement projects, which strengthen societal resilience. It also offers a tool with quantitative evaluation of causal and future climate and conflict links. The remaining eight tools provide pure frameworks with guiding documents (e.g., conceptual guides, overviews of quantitative data, checklists with interview questions, supporting assessment reports) emphasizing the necessity of combining qualitative and quantitative methods. As mentioned above, often these frameworks remain vague about specific methodological choices to address the guiding questions, analyze suggested data, or combine different methodological steps, which jeopardizes their credibility.
Integrating the diverse knowledge production techniques via mixed methods can be valuable for assessing the complex climate–security relationship (Beaumont & de Coning, 2022; de Bruin et al., 2022; Ide, 2017; O’Neill et al., 2022). Qualitative research can be fruitfully combined with quantitative assessments in several ways. For example, quantitative assessments (e.g., predictive modeling or risk indices) could first detect areas at risk and thus determine cases for qualitative analysis, which could then reveal insights for policy interventions. Alternatively, field research could reveal new mechanisms linking climate and insecurity and their external validity could be tested via statistical causal inference methods (Ide, 2017). Mixed methods have also been emphasized for assessing the long-term climate–security risks as discussed in Section 4.2.2.
4.4. Considered variables
There are significant differences in the number and type of variables considered by the CSRA tools to evaluate the risk landscape. Drawing on our definition of risk (Section 2), we assess to what extent CSRA tools draw on climatic, conflict, and vulnerability variables (Figure 4) and thus can account for climate risk comprehensively.
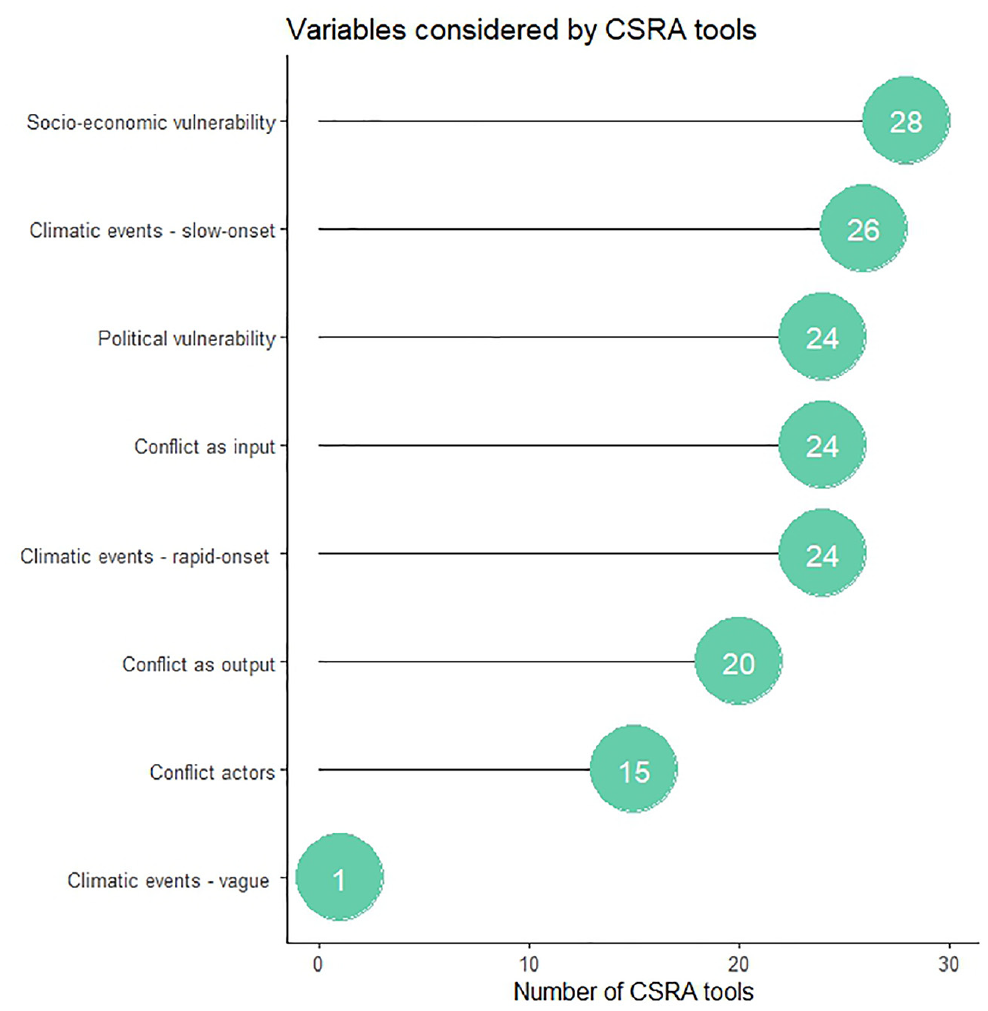
Variables considered by the 28 CSRA.
Climatic hazards: Given our focus on CSRAs, all tools account for climatic hazards to some extent. Slow-onset events are considered in 26 tools, most prominently droughts, long-term temperature changes, and temperature and precipitation variability. Other slow-onset events (e.g., sea-level rise, ocean acidification, and salinization) are considered less frequently and if so then via mixed methods or qualitative tools, presumably because they change more slowly over time and thus do not offer sufficient variation necessary for quantitative attribution to security-related outcomes (von Uexkull & Buhaug, 2021). Rapid-onset events are considered in 24 tools. Some of the tools (e.g., CSO and ViEWS) do not specify their choice of rapid-onset variables. In the other tools, rapid-onset variables differ and include, for example, extreme precipitation, floods, heatwaves, tropical storms, and cyclones. The variable diversity can partially be explained by the different foci of the tools. For example, WPS and FREXUS focus on hydrology-related risks and therefore account for variables such as river inundation and water availability. 13 Finally, one framework tool, Promoting Climate-Resilient Peacebuilding in the Fragile States, only emphasizes the necessity to integrate climate risks into the analysis but remains vague about whether to consider slow- or rapid-onset events.
Socio-economic variables of vulnerability: All reviewed CSRA tools cover a wide range of socio-economic drivers. Mostly, quantitative risk score tools capture economic variables, incorporating indicators such as GDP growth, development aid, remittances, trade, inflation, and exchange rates. Fewer of them consider agricultural dependence (e.g., share of agricultural land, agricultural GDP, yields), aspects of food security as well as indicators related to water, sanitation and hygiene, healthcare, and education. GCRI and CCVI, for example, also incorporate variables related to ethnic marginalization. The framework tools, all of which have a qualitative component, emphasize the need to consider different socio-economic factors in a context-specific manner. Largely, they account for a broader range of socio-economic variables than the tools offering quantitative risk scores, clearly demonstrating the restrictions imposed by the availability of quantitative data. For instance, while only a few risk score tools assess aspects of gender and ethnicity, WR, CSM, and Addressing Climate-Related Security Risks account for different types of vulnerability and inequalities.
Political variables of vulnerability: In all, 24 tools include variables of political vulnerability. Risk score tools typically consider regime type (e.g., democracy indices) and performance (e.g., government effectiveness, corruption, rule of law). The underlying databases and applied variables differ. For example, the GCRI and ViEWS rely entirely on the VDEM Dataset (Coppedge et al., 2022). INFORM Climate Change, CCVI, and CSRM measure corruption via the Corruption Perception Index (Transparency International, 2023). CCVI and CEPSA draw on the Worldwide Governance Indicators (The World Bank, 2023). CEPSA additionally derives data from the Polity IV Project (Marshall, 2023). Framework tools typically suggest which aspects of governance to assess. For example, Addressing Climate-Related Security Risks emphasizes analyzing marginalization, identity politics, rule of law, and service delivery. WR proposes a context-specific selection of variables and provides guiding questions, addressing aspects of basic service delivery, natural resources management, and government effectiveness and legitimacy, among others (see Supplemental Appendix). However, only a few framework tools (e.g., WR, CSM, Addressing Climate-Related Security Risks, Climate Change - A Risk Assessment) consider climate governance as a potential driver of conflict.
Conflict variables: In all, 16 tools consider conflict as both input and outcome variables. Eight tools use conflict mainly as an input and the remaining four as an outcome. Tools with quantitative elements typically draw on the ACLED (Raleigh et al., 2010) and UCDP (Sundberg & Melander, 2013) databases, which capture smaller and larger scale violence, respectively. Thus, their conflict definition is typically limited to violent conflicts. 14 Tools with qualitative methodological elements keep the conflict and insecurity definitions broader, presumably since qualitative approaches can capture types of conflicts for which quantitative data are unavailable. For example, CSM notes that the types of insecurity extend beyond violent conflict to include “other types of insecurity, including organized crime, armed group activity, and sexual and gender-based violence” (UNDPPA et al., 2020). Only 15 tools, mostly with a qualitative methodological element, provide information on conflict actors, with different levels of detail. For example, CCVI features a qualitative case study of farmer–herder conflicts in the Sahel, though its quantitative tool does not account for conflict actors. FREXUS incorporates a conflict actor analysis in their case studies (e.g. Oyamta & Kabdana, 2022), and Addressing Climate-Related Security Risks provides comprehensive guidance for a detailed actor mapping that considers actors’ relative power in the conflict, their relationships, and the conflict issues between them. CEPSA is the only quantitative tool, which allows for distinguishing between actor types.
Overall, while it is crucial for CSRAs to comprehensively account for all relevant determinants (i.e., climatic hazards, conflict, and exposure and vulnerability) of climate security risks, the list of specific indicators should be chosen depending on the contextual focus of the CSRA.
4.5. Complex relationships
In all, 18 tools, mostly applying mixed methods, incorporate some analysis of climate-security pathways, evolving mostly around water and food security, and migration. Primarily, they are assessed qualitatively, via case studies. There are only three tools (WR, FREXUS, and WPS), which conduct pathway analysis quantitatively, via different causal inference techniques. While all tools incorporate variables of scope conditions, primarily those with a qualitative element consider their interactions with climatic hazards. For instance, CGIAR’s CSO provides a visualization tool of a network of first- and second-order interactions of environmental, institutional/political, social, agronomic, and economic drivers. FREXUS analyzes the linkages between resource use, climatic hazards, and conflict by focusing on water, energy, and food security. The lower ability of the reviewed quantitative tools to account for pathways and conditional effects strongly correlates with the two dominant approaches applied: predictive modeling and risk indices (Section 4.3). While predictive modeling can account for complex relationships analytically, it often fails to reveal explicit linkages between the input variables and the predicted variable, being often criticized for operating in a black box-like setup (Mach et al., 2020). Risk indices, on the contrary, are methodologically often too simplistic to deliver an in-depth understanding of these complexities (Ide, 2017). This implies, yet again, that there is a lot of potential in the mixed-methods approaches.
Finally, only nine CSRA tools explicitly incorporate cascading hazards into their approaches, most of them applying mixed methods. For example, Climate Change—A Risk Assessment concludes that risks to global food security, and national and international security are among the greatest systemic risks in the future. Not accounting for these complexities and interactions in CSRAs can lead to misestimation of risks. While the awareness of risk cascades in CSRAs is increasing, thus far they have been only considered to a limited extent (Kemp et al., 2022; Simpson et al., 2021; Zscheischler et al., 2018), as reflected by the CSRA tools.
4.6. Validation routine
We find that only nine tools contain a validation routine. Two out of the 13 framework tools stress the role of validation. As a mixed-methods tool, WR emphasizes an ongoing exchange between quantitative and qualitative analyses to validate the emerging evidence (see Supplemental Appendix). For its analyses, WR also conducts expert workshops to verify emerging narratives (Rüttinger et al., 2021; UNDP & PIFS, 2023). While CVCA also stresses validation of the emerging evidence, they remain vague about its implementation. Overall, framework tools rarely offer guidance to validate the risk assessment. Yet, most of them emphasize monitoring and evaluation of the risk management carried out based on the assessment.
Less than half (five) of the 12 risk score tools perform some form of validation. All predictive tools conduct some out-of-sample predictions to validate the model performance (Ward & Beger, 2017). In this regard, ViEWS explicitly follows the guidelines by Colaresi and Mahmood (2017). WPS further benchmarks its model against others, including ViEWS (Kuzma et al., 2020). Out of all predictive tools, ViEWS has the most elaborate validation routine, as in addition to the annually conducted state-of-the-art out-of-sample heuristics, it benchmarks the model against other assessments and as an only predictive tool, it facilitates external review by publicly providing all source code and data (Hegre et al., 2019, 2021). Strata is the only risk index with a validation routine, in line with Bakkensen et al. (2017), who conclude that only a few risk indices are empirically validated. It focuses on a pilot study on Somalia and evaluates the accuracy of the assessment by comparing the emerging evidence with historical events described by media and with other data-driven assessments of climate security in Somalia. Its narrow geographical focus might put the external validity of the validation exercise in question. On its website, Strata further published parts of its code, yet only a full disclosure of applied data and codes would enable external reviews of the tool. Beyond this, Strata also evaluates the tools’ uptake, relevance, usability, and ethics (see Supplemental Appendix).
Finally, two out of the three tools combining risk scores and frameworks, have a validation routine. FREXUS emphasizes the validation of the analysis via expert workshops and provides various guiding questions to be addressed in this regard. Using quantitative analyses, the predictions of food security by FEWS NET have been validated, for instance, ex-post against the assessment of the current situation for Ethiopia (Choularton & Krishnamurthy, 2019), the Greater Horn of Africa (Krishnamurthy et al., 2020), and 25 African countries (Backer & Billing, 2021).
5. Concluding remarks
We reviewed 28 CSRA tools developed for decision-making against the backdrop of state-of-the-art research. In what follows, we summarize our findings (Section 5.1) and derive recommendations on how to better embed CSRAs tools in science and outline entry points for future research (Section 5.2).
5.1. Review findings
Most of the CSRA tools are provided by and for the GN. Yet, the tools largely focus on risks in the GS, involving Southern actors primarily to consult on their local expertise on aspects of interest to the Northern actors. This might reinforce the skepticism among many GS foreign policymakers that the climate security agendas are dominated by the GN and lead to unintended consequences, distracting from policy agendas in the GS (Abdenur, 2021). Overall, the insufficient participation of the GS actors could lead to the production of extractive CSRA tools and jeopardize their relevance.
Largely, the CSRA tools have global coverage and look at risks at the granular level. We did, however, detect an exclusive focus on Africa and Asia in the regional case studies. We also find that the tools mostly assess historical risks, followed by near-real-time analytics and future projections. Only a few tools are anticipatory, assessing short-term future risks. Qualitative scenario developments to assess (near- to long-term) future risks are applied only rarely. Also, assessing the uncertainty of future projections remains an exception.
Most of the tools have a quantitative and slightly fewer qualitative methodological component. Only half of the tools combine these via mixed methods, which serve as the best practice in assessing climate security risks (Ide, 2017). Those mixed-methods tools often fail to transparently outline an approach on how to execute and combine the different methodological steps, likely because scientifically robust ways illustrating how to integrate these different approaches are largely missing. In fact, methodological transparency is particularly an issue in the tools providing guiding frameworks.
CSRAs do not comprehensively map all dimensions of climate security risks (climatic hazards, exposure, and vulnerability). While all tools consider climatic hazards to some extent, some remain vague about which ones. To account for sources of vulnerability, all tools consider some socio-economic variables but several do not account for political factors. Main gaps include, for example, consideration of conflict as a source of vulnerability, conflict actors, governance (e.g., climate action and peacebuilding), and gender and ethnic relations. Overall, tools applying qualitative approaches typically account for a broader range of variables, while quantitative assessments remain restricted by existing data. Especially, governance data on a subnational level are largely missing.
CSRAs insufficiently account for complexity: Climate-related risk drivers are characterized by complex interactions, for example, over space, time, and sectors (O’Neill et al., 2022; Simpson et al., 2021). These complexities have been considered only to a limited extent within the reviewed CSRA tools. For example, approximately two-thirds of the tools focus on explaining the pathways, while only approximately a third assesses cascading risks.
Finally, a large share of CSRAs are not empirically validated. While all tools with a predictive component are validated, this is true only for a very few risk indices and frameworks. A likely explanation is that there are robust scientific approaches to validate predictions, such as out-of-sample heuristics (Colaresi & Mahmood, 2017). Yet, we did not identify a clear best practice when it comes to the validation of other methods. Moreover, while transparency and replicability are common practice in academic research (Rød et al., 2023), ViEWS is the sole predictive tool that makes its data and analyses fully transparent and available for replication.
5.2. Recommendations for CSRA tools and future research
Since the GS is more affected by climate and security risks and related interventions (O’Neill et al., 2022), CSRAs tools should more strongly involve local GS actors in all steps, ranging from the priorities setting, tool conceptualization, and risk analysis, to the identification of interventions. This would increase their relevance and effectiveness. Environmental assessments fostering representation and empowerment of underrepresented groups enhance the legitimacy and effectiveness of decision-making (Barnett, 2022; Busby, 2018; Kowarsch, 2016; Kowarsch et al., 2016; Medina et al., 2024; Sitati et al., 2021). In particular, consideration of local and/or indigenous perspective of the natural environment improves the climate security outcomes (Amador-Jimenez et al.,2024; Nalbo, 2024). Thus, funders of CSRAs and related tools should prioritize diverse research partnerships, particularly including GS actors (Hoffmann et al., 2023).
Given the contextual character of the climate security risks, CSRA tools would ideally foster geographic granularity (Buhaug, 2015; O’Neill et al., 2022). Any choices regarding tools’ geographical and temporal coverage should be made transparent and accompanied by a critical reflection on the implications for the evidence. In this regard, any sampling bias should be avoided (Adams et al., 2018; Barnett, 2019). Analyzing risks across different time scales provides complementary information and is thus highly policy relevant. Yet, historical inference to learn about the future should be applied critically (Tubi et al., 2022). Here, quantitative and qualitative developments of future scenarios create synergies (Hoch et al., 2021). Risk projections further require thorough communication of uncertainties. Future research should continuously advance quantitative forecasts to improve predicting the timing of violence escalations or conflict onset (Cederman & Weidmann, 2017; Rød et al., 2023). Furthermore, scientifically sound projections of conflicts and the necessary methodological approaches should be developed particularly by combining quantitative and qualitative approaches (de Bruin et al., 2022).
Mixed methods enhance the understanding of climate-related security risks, as qualitative and quantitative approaches can complement each other (Beaumont & de Coning, 2022; de Bruin et al., 2022; Ide, 2017). There are various opportunities to combine these different methodological components and their concrete choice depends on the objectives of a given tool. Future research should develop scientifically robust approaches to systematically integrate various quantitative and qualitative methodological parts, as these are largely missing.
To thoroughly assess climate security risks, all context-relevant climate risk determinants should be accounted for. Notably, the gaps mentioned in Section 5.1 should be addressed, since existing power inequalities, such as gender roles, significantly affect the climate risk outcomes and are thus central to a human-centered approach to security in a changing climate (Francis, 2024). Data advancements increasingly enable considering a broader range of relevant variables in quantitative assessments (Auffhammer et al., 2013; Donaldson & Storeygard, 2016; Helbling et al., 2023; Leyk et al., 2019; Yeh et al., 2020). Also, qualitative research can complement the quantitative analyses (de Bruin et al., 2022; Ide, 2017). In this context, a common understanding of climate risk and its determinants among researchers and analysts would be beneficial. To this end, we propose the established definition by the IPCC, where climate risks are determined by an interaction of climatic hazards, vulnerability, and exposure to them (Oppenheimer et al., 2014)
The consideration of the complex climate security interactions should be enhanced within CSRA tools. Depending on the capacities and conceptual foci, the tools may start at lower levels of assessment complexity but should clearly acknowledge the need for an update (Simpson et al., 2021). Future research could improve the thus far limited abilities to analyze these complex dynamics.
Even if the CSRA tools follow our above-mentioned recommendations, it is not for granted that they succeed in correctly identifying risks. Establishing validation routines to test and advance the tools’ reliability is therefore essential. Especially, since more reliable CSRAs lead to more efficient decision-making (Busby, 2018; Mach & Kraan, 2021; Visser et al., 2020). Tools with a predictive component should continue to follow state-of-the-art scientific advice on validation implementation (Colaresi & Mahmood, 2017). However, best practice in the validation of other methods, such as indices or case studies, is still needed. This should be addressed by future research. Finally, all tools should foster research transparency and replicability, which are essential for them to be taken seriously and for their further development (Rød et al., 2023).
To conclude, if climate security risks are poorly understood, solutions remain flawed (Autesserre, 2012, 2017). Following our recommendations would make CSRAs and related tools better embedded in state-of-the-art research and advance their overall performance. There might be factors, such as funding, inhibiting the implementation of (some of) our recommendations. In such cases, it is better to conduct a more focused, yet rigorous assessment with transparently and clearly defined goals. In our analytic process, we have indeed noticed that tools whose goals were confined to concrete, clearly defined, and limited objectives were more likely to succeed in meeting these goals and delivering actionable rather than generic evidence. 15 What remains crucial is that CSRAs and related tools continuously follow and integrate research across relevant fields, including climate and conflict, environmental peacebuilding, and climate security assessments. Finally, following the fundamental principles of ethical research remains imperative. A broad range of aspects could raise concerns in this regard. For example, the use of emerging technologies to collect information has been widely debated due to possible violations of security and privacy (Sloan et al., 2020). Another example is the analysis of conflict actors, where assigning the potential for conflict to certain groups could feed systematic antagonism toward these groups (e.g., affect the provision of resources from governments and intergovernmental organizations). While in-depth discussion of ethical issues in CSRAs is beyond the scope of this review, these need thorough considerations already in the research design phase.
Supplemental Material
sj-docx-1-eas-10.1177_27538796241226996 – Supplemental material for A review of climate security risk assessment tools
Supplemental material, sj-docx-1-eas-10.1177_27538796241226996 for A review of climate security risk assessment tools by Barbora Šedová, Lisa Binder, Sidney Michelini, Marie Schellens and Lukas Rüttinger in Environment and Security
Footnotes
Acknowledgements
The authors would like to thank the reviewers and the editors of this special issue as well as to Halvard Buhaug and Silja Halle for their helpful comments.
Author contributions
BŠ wrote the main parts of the paper. SM wrote mainly Sections 3.1 and 4.1, LB wrote mainly Sections 3.5 and 4.5 and Sections 3.4 and 4.4. LR and MS contributed mainly to parts describing Strata and Weathering Risk and overall text editing. BŠ, SM, and LB coded the tools and evaluated the data.
Declaration of conflicting interests
The author(s) declared the following potential conflicts of interest with respect to the research, authorship, and/or publication of this article: The author team acknowledges their involvement with the initiatives Weathering Risk and Climate Conflict Vulnerability Index by the German Federal Foreign Office and with Strata by the United Nations Environment Programme.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: BŠ, LB, and SM acknowledge funding from the German Federal Foreign Office (GFFO). MS acknowledges funding from the European Union, grant number IFS/2016/380-502. LR acknowledges funding from the Organization for Security and Co-operation in Europe (OSCE), UNEP, and GFFO.
Research data availability
Upon request.
Supplemental material
Supplemental material for this article is available online.
Notes
Author biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
