Abstract
This study examined how internet-based communication channels impact on national security in Nigeria. The study was conducted in Enugu State, South East Nigeria. Three research questions guided the study and three null hypotheses were tested at .05 level of significance. A total of 385 internet users were selected using a combination of purposive and snow ball sampling techniques. In the analysis of data for the study, correlation analysis and multiple regression were used. The result of the analysis showed that internet-based media of communication like the Facebook, Gmail, YouTube, Yahoo mail, and Twitter significantly correlate national security. It was also found that there are specific ways through which negative use of the internet could impact negatively on national security. Such predictors include using internet-based media to recruit agents of national security challenges, to finance such efforts, to radicalize such agents, to train such agents, and to spread incitement that may be inimical to national security. It was also found that internet-based media could be useful for creating awareness on national security threats, raising alarm on national security issues, and making people alert on national security issues. Base on the result of this study, the researcher recommends, among others, that the traditional media like radio, TV, newspapers, and magazines should form a synergy with security agencies on how to create awareness to Nigerians regarding how security alertness for the overall benefit of national security.
Introduction
The internet has brought about many changes in communication. It has widened communication scope and created new opportunities. It has made the voices of the voiceless to be heard and broken the boundaries hitherto created by the traditional media. Before the emergence of the internet, people who could not afford the cost of obituary announcement through the traditional media simply kept mute. In fact, radio or TV obituary announcements were an exclusive preserve of the rich. However, with the emergence of the internet-based communication channels, all those have changed. People could take to social media like the Facebook and Twitter to announce their bereavements at little or no cost. Asogwa (2017) found that internet-based media are a critical part of media preference and consumption of people in the 21st century. The internet has also expanded the scope of advertising. Small- and medium-scale enterprises who cannot afford the financial burden of placing adverts in traditional media can now do so at just a click of the button. The internet has also brought the world closer than ever before. With the internet, a person from Nigeria can freely interact with his counterpart from the United States. They could have video calls and send text messages, and all these could happen in minutes. People from different countries of the world like Nigeria, Canada, the United Kingdom, and Turkey could hold a meeting through teleconferencing. Academics do not need to travel far to attend conferences as this could be done through video presentation. The Skype is one of the channels for this purpose. The global village envisage by Marshall McLuhan as far back as 1962 is a reality. In projecting the global village, McLuhan and Fiore (1967) notes, Ours is a brand-new world of allatonceness [sic]. “Time” has ceased, “space” has vanished. We now live in a global village . . . a simultaneous happening. We are back in acoustic space. We have began again to structure the primordial feeling, the tribal emotions from which a few centuries of literacy divorced us. (p. 63)
Gever (2016) in corroborating McLuhan argues that because information is being disseminated immediately, thus closing the globe in time, different transactions are now like those that were regarded within a village instead of the wide world we have known until now. People can interact with others instantly, in a manner typical of a village.
Things that were once purchased only in the village market can now be purchased anywhere in the world, instantly. Things that we could only see if they occurred in our village can now be brought into our home, before our eyes instantly. That makes the globe in effect our village (Gever, 2016).
Much as the internet-based communication channels have expanded the scope of communication and brought about many positives things, some people have expressed concerns on how such new communication platforms impact on the national security. This partly explains why some countries of the world attempt to restrict their citizens’ access to internet-base communication channels. Examples of such countries with high internet restriction include Myanmar (Burma), Vietnam, Tunisia, Syria, Iran, Saudi Arabia, Ethiopia, Eritrea, China, and North Korea (Le VPN, 2018). Also, during the 2018 general elections in Democratic Republic of Congo, internet restrictions were put in place in a bid to protect national security.
Nigeria’s constitution also recognizes the place of national security which is the provision of Section 14.-(1b) of the 1999 Constitution (as amended) states that the security and welfare of the people shall be the primary purpose of government. The United Nations (1948) Universal Declaration of Human Rights also recognizes the importance of security as a basic right that must not be taken away from all human beings. This is contained in articles 3, 22, and 25(1), respectively. While article 3 posits that everyone is entitled to right to life, liberty, and security, article 22 notes that every member of society is entitled to social security and has the right to achieve this via national effort and international co-operation and based on the organization and resources of each State. Article 25 (1) states that everyone has the right to a standard of living that is good enough for the health and well-being of himself and of his family, which also covers food, clothing, housing, and medical care and necessary social services, and the right to security in case of unemployment, sickness, disability, widowhood, old age, or other lack of livelihood that he or she may not be able to handle unassisted. Therefore, in this study, the researcher attempted to provide empirical data on public reviews regarding the contribution of the internet to Nigeria’s national security.
Statement of the Problem
The emergence of internet-based communication channels such as the Facebook, Twitter, and YouTube has been regarded as significant milestones that have completely changed the communication landscape. They have made communication easy, flexing, and faster. They have also broken the barriers of time and space. However, stakeholders have expressed concerns that such advancements in technology may have negative implications on national security. Such concerns have also been affirmed by some empirical evidence (see Chukwuere & Onyebukwa, 2018; Fomenko, 2014). However, there appears not to be a consensus as Benson (2014) also reported that internet-based media do not pose a threat to security; rather, they are helpful tools for combating the challenge. This conflict in literature is problematic as it calls for the need to examine the impact of internet-based media on national security from two perspectives of both negative and positive, hence the need for this study.
Research Objectives
The general objective of this study was to ascertain how internet-based media correlate with national security. Specifically, the study sought to
Ascertain relationship between internet-based communication channels and national security,
Examine the negative internet-based media use that negatively impact on national security, and
Determine the positive internet-based communication channels that positively impact national security.
Research Questions
This study sought answers to the following questions:
Research Hypotheses
This study tested the following hypotheses at .05 level of significance:
From Yesteryears to Today: Internet-Based Communication Channels
Communication has undergone several changes. Communication describes the exchange of information or the sharing of meaning from a source who is also called the sender through a channel to a receiver. This definition falls within the context of Berlo’s (1960) linear model of communication (Sender-Message-Channel-Receiver). During the days of carving on walls to pass meanings, communication was not immediate because receivers had to take longer time in interpreting the meaning of carved messages. Georgiadou (1995) notes that communication that is not immediate depends on systems/means in which case information, ideas, and attitudes can be preserved in an intermediate point between the transmission and the receiving end. The researcher notes further that during the oral culture, communication was immediate as such people largely relied on the spoken word so as to pass messages to others and interact. During that time, memory was very important because it was the sole “system” that allowed people to preserve information. During the oral culture also, transmission of information through long distances relied significantly on sound or light. Nonetheless, the voice of human beings was applied using different attachments like animals’ horns or other such devices, conveyed over only 1 or 2 km at the most (Clarke, 1993, p. 19). As a result of such limitations, people attempted to find a way to store what they had in their minds so that they would not have to rely only on their memory to recall them, and also to make communication possible over long distances without depending only on ephemeral phenomena like sound and light (Georgiadou, 1995). Such attempts to search for ways to storing meaning for future references led to the emergence of written communication. Jean (1987, pp. 11–14) says that the first written signs were deployed for agricultural messages during the latter part 4th millennium BC in Mesopotamia. As time progressed, written communication became an alternative medium of meaning sharing. This was made possible only with the Phoenician alphabet as writing really became a flexible medium of communication. It is essential to add here that even after the emergence of written communication, oral communication was still playing a critical role in meaning sharing because most people were illiterate. So written communication served the purpose of preserving meaning.
The emergence of electric telegraph brought about a new phase in human communications. In 1840, the electric telegraph emerged as a commercial tool of substantial possibilities. “Within ten years it had covered most of Europe and the settled portions of North America—but it still stopped at the edge of the sea” This problem, “wiring the sea,” was addressed only a very few decades afterwards. In 1858, a telegraph cable was smoothly laid across the North Atlantic, and “at the closing of a switch the gap between Europe and America collapsed suddenly from a month to a second” (Clarke, 1993, p. 20). This particular project lasted only for a few days as the cable broke, “but after an eight-year saga of almost unbelievable courage and persistence, a successful Atlantic telegraph that was finally laid is one of the great engineering epics of all time, and has many lessons for us even today” (Clarke, 1993). Innovations in technology continued and led to different communication channels like television, newspaper, and magazine and eventually the internet which has led to the emergence of internet-based media of communication like Facebook, Twitter, Instagram, Gmail, and yahoo mail. These media are internet based because without internet connection, it will be impossible to use them. Therefore, in this study, internet-based communication channels describe those communication media that are powered by the internet, without which they cannot share messages.
The increasing internet penetration in Nigeria has raised security concerns. According to WOW Effect (2010), most of Nigeria internet users are concentrated in the big cities. WOW maintained that though all the 36 state capitals including the FCT have one degree internet connectivity or the other, only a handful of them (the main commercial cities of Lagos, Ibadan, Abuja, Kano, Kaduna, Jos, Benin, Port Harcourt and Enugu) have real broadband internet facilities. The second concentrations of internet users are found in the university/polytechnic areas. In the area of age distribution, internet users in Nigeria are said to have been 40 years and below. WOW divides the age distribution into four as 10 to 17 years, 18 to 24 years, 24 to 40 years, and 40 years and above.
In the area of economic/social status, students between 10 to 17 years and 18 to 24 years old were found to be users of the internet. This set of people depends on their parents and guardian for financial assistance. Job seekers were also documented to use the internet in search of jobs, mostly within the ages of 20 to 30. This increasing internet use makes a study of the implications of internet-based communication channels necessary so as to such ways of controlling its impact on Nigeria’s security as Olijo (2016) says that there is a strong relation between communication and peace building.
Internet-Based Communication Channels and National Security
The internet describes the interconnection of network. On October 24, 1995, The Federal Networking Council (FNC) agreed that the following language reflects the definition of the term “internet.” “Internet” refers to the global information system that (a) is logically linked together by a globally unique address space based on the Internet Protocol (IP) or its subsequent extensions/follow-ons; (b) is able to support communications using the Transmission Control Protocol (TCP)/IP suite or its subsequent extensions/follow-ons, and/or other IP-compatible protocols; and (c) provides, uses, or makes accessible, either publicly or privately, high-level services layered on the communications and related infrastructure described herein (The Internet, n.d.). Table 1 provides a brief insight into the historical evolution of the internet.
History of the internet.

Source. The internet (n.d.).
The internet could be used for different purposes. The traditional core applications include email news, remote login, and file transfer. On the other hand, the new applications are videoconferencing, telephony, P2P applications, and internet Broadcast (The Internet, n.d.). Since the emergence of the Internet, especially its full commercialization in 1995 which allows everybody in any part of the world access, scholars have expressed concerns over its impact on national security.
National security is used in reference to all the issues relating to the security of lives and property of a country (see also Asad, 2007; Oshio, 2009). One of the famous scholars in the area of national security is Arnold Wolfers. In the views of Wolfers (1960), cited in Paleri (2008), national security entails lack of threats that could limit the acquisition of cherished values. He adds that it also entails an atmosphere free from attack or any scenario that could lead to the outbreak of law and order. In the views of Maier (1990), national security refers to the capacity of a nation to fully control foreign and domestic situations that may compromise the security of lives and properties.
For some time now, Nigeria has faced many national security issues that border on defense and survival of the state. These national security threats range from conflict agitations, to religious conflicts, to politically motivated threats, the farmers–herdsmen conflict, insurgency, among others. The Institute for Economic & Peace (2014) in a global survey notes that in 2013 alone, Nigeria recorded 303 bomb blasts, with 1,826 fatalities and 457 injuries. The economic cost of insurgency in Nigeria was estimated at $28.48 billion. Apart from the Boko Haram, whose attacking powers have been reasonably reduced, the Niger Delta Avengers have renewed attacks in the oil rich region with corresponding consequences. Onuoha (2016) chronicles some of the NDA attacks to include February 10 attack on Bonny Soku Gas Line, and February 13th launch of attack that gave the Federal Government a 14-day ultimatum to respond to its demands. Also, On May 4, 2016, NDA militants blew up the Chevron Valve Platform located in Warri, the Delta State.
The activities of the NDA have led to many economic losses for Nigeria. In this regard, the Agence France-Presse (AFP, 2016) observed that Nigeria’s oil production has reduced from 2.2 million bpd to about 1.4 million bpd. The AFP adds that militant attacks have also caused water supplies to be turned off in the country’s commercial hub and biggest city of Lagos. Apart from having negative effects on crude oil production, these attacks have made the supply of gas to local power plants difficult, thereby hobbling Nigeria’s power grid. Electricity generation in Nigeria has also dropped from about 4,800 megawatts in August 2015 to 1,000 megawatts in May 2016 (AFP, 2016), thereby affecting the economy of Nigeria. The Maritime sector is not immune to these attacks either. Zerihoun (2016) reported that an estimated 70% of all piracy-related incidents in the Gulf of Guinea are directly related to Nigerian criminal gangs, mostly emanating from the Niger Delta. The interest of the current study here is that this situation has affected national security in Nigeria in its general scope. For example, it has led to fear, destruction of lives and property, job losses in the oil sector, hardship, and so on. Gever (2016) notes that security challenges have occurred in all areas of Nigeria’s existence such as social security and security of lives and property. Gever regretted that the prevailing mindless killings of innocent citizens orchestrated by the Boko Haram sect have become locally and internationally pronounced. It is important to add here that Boko Haram has caused untold hardship to the Nigerian people. This is evident in the burning of schools, abduction of women and school children, attacking of public places like schools, mosques, churches, markets, and so on.
Another security threat in Nigeria today is the conflict between farmers and Fulani herdsmen. Gever (2014) regretted that conflicts of varying degrees between farmers and herdsmen have become too perennial in Nigeria. And that these conflicts sometimes end fatally for both parties, properties worth billions are destroyed, people are displaced from their homes, and cattle are killed, among others. Tenuche and Olarewaju (2009) in a study on “Resource Conflict among Farmers and Fulani herdsmen: Implications for resource sustainability” with evidence from Kogi State noted that the conflict has caused untold hardship to the victims and their relatives. The scholars list the consequences of the conflict to include loss of crop yields, loss of economic plants, pollution of drinking water, increased labor in pre-farming activities, loss of soil fertility, and loss of fish resource. Also, the conflict agitations orchestrated by Indigenous people of Biafra has also threatened the national security of Nigeria. The situation reached a point where quit notices and counter quit notices were issued to some ethnic groups in Nigeria. See also Gever et al. (2019) and Gever (2016) for more on national security issues in Nigeria.
In the midst of these national security threats, the internet-based communication channels have been regarded as playing critical role in disseminating information on these security issues. This could be negative and positive. There is no consensus on the actual impact of internet-based communication channels on national security. For example, the United Nations Office on Drugs and Crimes (2012) notes that internet-based communication channels could be used for terrorism in the area of recruitment, incitement, radicalization, financing, training, planning, preparatory secret communication, and so on. Fomenko (2014), Nsudu and Onwe, (2017), and Chukwuere and Onyebukwa (2018) also found that internet-based communication channels negatively affect national security. However, Benson (2014) in an article entitled “Why the Internet Is Not Increasing Terrorism” argues that the internet poses not national security threats. Benson argues that far from being a threat to national security, the internet-based communication could be useful for combating national security challenges. One gap in literature that is worth pointing out here is that scholars such as Fomenko (2014), Nsudu and Onwe (2017), and Chukwuere and Onyebukwa (2018) have examined issues related to the impact of internet-based media such researchers did not look at it from the broad point of view of positive and negative associations. This makes this study important, not just to add to the body of literature on the subject matter but to provide empirical evidence that could serve as a guide on how to deploy internet-based media for enhancing national security.
Theoretical Framework
The Technological Determinism Theory was used for this study. The theory was suggested by Thorstein Veblen (1857–1929), an American sociologist. However, it was developed by McLuhan in 1960 (McQuail, 2005). The Technological Determinism (TD), simply put, is the idea that technology has important effects on our lives (McQuail, 2005). McLuhan argues that changes in technology will also affect the generality of the society. This idea features prominently in the popular imagination and political rhetoric, for example, in the idea that the internet is revolutionizing economy and society (McLuhan & Fiore, 1967). Technological determinism has also had a long and controversial history in the social sciences in general and in organization studies in particular (Asemah, 2011). Critics of technological determinism argue variously that technology itself is socially determined, that technology and social structures co-evolve in a non-deterministic, emergent process, or that the effects of any given technology depend mainly on how it is implemented which is in turn socially determined. This theory is relevant to the current study because it provides the basis for understanding the changes that have led to the emergency of internet and new communication channels that have also changed the approaches in addressing issues related to national security. This is because the theory makes a case regarding the impact of new technologies on the society. Before the emergence of new technologies, security issues were easier to handle; at least, the issue of cyber security was not part of the problems that security experts were facing. However, with the current situation, it is easier for security architecture of a country to be compromised. It is also easier in the current era for people to revolt against constituted authorities. The Arab spring is a good example of how easier it is for citizens to rise against constituted authorities. It is also now easier for people to mobilize themselves for mass action. In addition, crimes can also be coordinated with the use of new technologies. On the other hand, new technologies have also provided potentials for combating national security threats. New technologies can be deployed to monitory security threat as well as carry out investigation. For example, there are now Closed Circuit TV that are used to monitor potential security threat. There are also devices that are useful for investigating and spying. This means that the issue of new technologies presents a dilemma, the need for the current study.
Materials and Methods
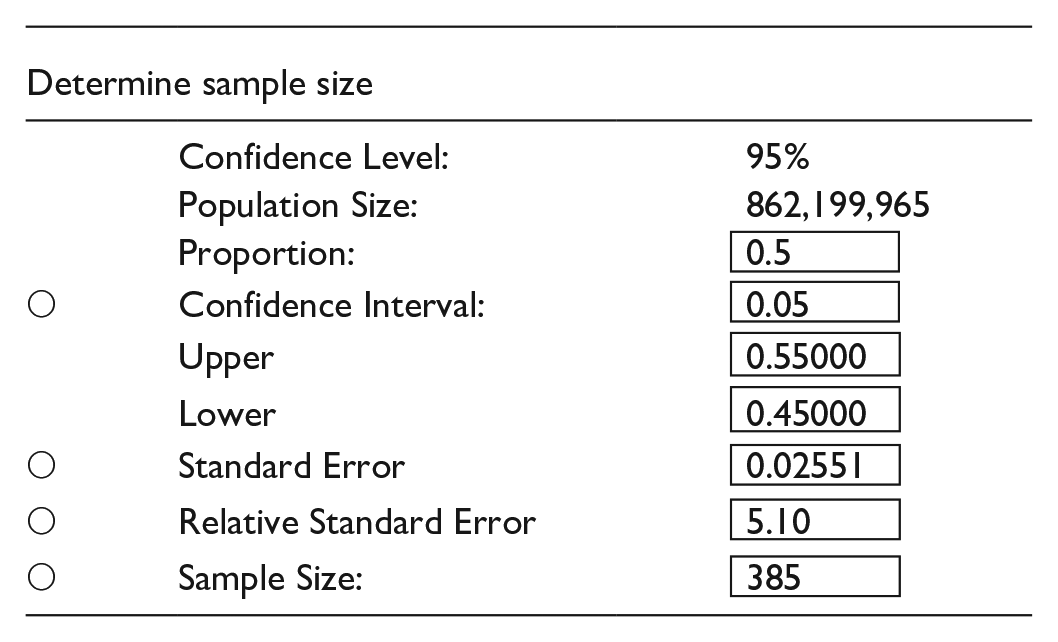
The descriptive survey method was used for this study. This study was conducted in Enugu State. The population of this study was all the internet users in Nigeria. The total population of internet subscribers in Nigeria, according to the internet Live Stats (2016) is 862,199,965. It was decided that internet users were best for the study because they will better understand how internet-based communication channels impact on national security. The researcher determined the sample size for this study through the Australian Calculator as provided by the National Statistical Service (NNS) was used. The confidence level was 95% precision level of .05 and estimated variance of 5% will be used. The calculation yielded the following:
This study adopted purposive sampling technique to achieve its aim. This was to enable the researcher sample only internet users. Therefore, the researcher purposively selected Enugu State as the area of the study. In Enugu State, Enugu capital city was selected. The choice of Enugu capital city was based on the result of WOW Effect (2010) that reported that there are more internet users in capital cities than other areas in Nigeria. To sample the individual respondents, the researcher adopted snow ball sampling. To implement this technique, initial internet users were contacted and requested to recommend other internet users. The process continued until all the 385 respondents were sampled. A self-developed questionnaire was used to collect data for this study. The questionnaire was developed after a review of literature. The questionnaire had two parts. The first part sought the demographics of the respondents while the second part sought data for the hypotheses testing. The response format was closed-ended. The instrument was administered to the respondents with the help of three research assistants who were briefed on the modalities for administration. The instrument was validated by three communication experts at the University of Nigeria, Nsukka. The reliability of the instrument was ascertained through a test–retest approach and the correlation coefficient was 0.78, an indication of high reliability.
In the analysis of data for this study, the researcher used the Statistical Package for Social Sciences (SPSS 16.0). In terms of statistical tool, the mean and standard deviation were used in the study. Multiple regression and correlation analysis were used to test the hypotheses at .05. The results were presented in tables.
Results
A total of 385 copies of the questionnaire were administered to respondents; 355 copies were filled and returned and found useful. This represents a returned rate of 92%. Therefore, the attrition rate was low.
Sample Characteristics
The characteristics of the sample show that 56% were male, while 167 (44%) were female. The result also showed that the mean age of the respondents was 28 (range = 23–33). Most (87%) of the respondents have been internet users for over 5 years.
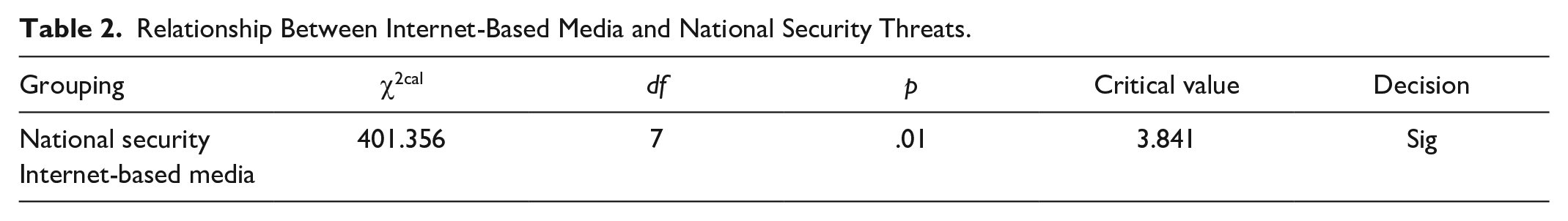
Table 2 sought to ascertain the association between internet-based communication channels and national security threats. The result showed that internet-based communication media significantly correlate national security. Although the table reveals the correlation between internet-based communication on national security threats, it did not reveal the negative indicators that impact the national security through internet-based media communications. To address this, Table 3 was computed.
Relationship Between Internet-Based Media and National Security Threats.
Negative Associations of Impact of Internet-Based Communication Channels on National Security.

Correlation is significant at .05 level of significant.
In Table 3, a correlation analysis carried out to ascertain the negative association between internet-based media and national security. The result of the analysis showed that all the variables are significantly associated with the impact of the internet on national security. The result showed that radicalization had the highest value (r = .869), an indication that there is 86.9% chance that internet could lead to radicalization. To examine the predictors of positive impact of the internet-based media on national security, Table 4 was computed.
In Table 4, the researcher examined the positive association indices on impact of internet-based communication channels on national security based on specific indications like awareness creation, alertness about security threats, raising alarm about security threats, and tracking actors that instigate national security threat as well as information on actors of national security. The result of the analysis showed that all the variables are significantly associated with positive impact of the internet on national security. The result also reveals that awareness had the highest correlation value (r = .903), an indication that there is 90% chance internet-based media can be used for awareness creation on national security.
Positive Associations Between Internet-Based Media and National Security.

Correlation is significant at .05 level of significant.
Test of Hypotheses
Three hypotheses were tested in this study. The first hypothesis sought to ascertain the relationship between internet-based communication channels and national security. The result of the correlation matrix as presented in Table 2 showed that internet-based communication channels significantly correlate national security (p < .05). Therefore, the first null hypothesis was rejected and the researcher concludes with 95% confidence that internet-based communication media significantly correlate national security. The second hypothesis sought to ascertain negative associative impact of internet-based media on national security. The result of the correlation analysis reveals that negative internet use is significantly associated with national security (see Table 3). Therefore, the second null hypothesis was rejected and the researcher concludes that negative internet-based media use is associated with national security. The third research hypothesis sought to ascertain the positive internet-based media use that could help in promoting national security. The result of the hypothesis testing showed that the p value was less than .05. Therefore, the third null hypothesis was rejected and the researcher concludes that positive internet-based media use could help in combating national security (see Table 4).
Discussion of Findings
This study examined how internet-based communication channels impact on national security in Nigeria. The study was conducted in Enugu State, South East Nigeria. Three research questions guided the study and three null hypotheses were tested at .05 level of significance. The result of the analysis showed that internet-based media of communication like the Facebook, Gmail, YouTube, Yahoo mail, and Twitter significantly correlate national security. Such internet-powered media are like two edged sword; they could be used to fight national security and to instigate national security. This result is consistent with that of Nsudu and Onwe (2017) and Chukwuere and Onyebukwa (2018) who reported that internet-based media are inimical to national security. The result of this study also has implications on the technological determinism theory of Thorstein Veblen (1857–1929), suggesting that advancements in technologies have led to corresponding changes in approaches for addressing national security issues. The result of this study has, therefore, provided a fresh perspective in the understanding of technological determinism theory by suggesting that it could also serve as a framework for studying the impact of new technologies on national security. It was also found that there are specific ways through which negative use of the internet could impact negatively on national security. Such predictors include using internet-based media to recruit agents of national security challenges, to finance such efforts, to radicalize such agents, to train such agents, and to spread incitement that may be inimical to national security. This result is consistent with that of the United Nations Office on Drugs and Crimes (2012) who reported that internet-based media pose serious threat to security. The result is, however, contrary to that of Benson (2014) who reported that internet-based media do not have negative impact on national security; rather, they could be used to addressing security challenges. Benson used the example of Al-Quida by revealing that the terror group was more deadly in pre-internet era than in the current internet-dominated society. The result of the current study revealing that positive use of internet-based media could be useful for combating national security is, however, consistent with that of Benson. It was found that internet-based media could be useful for creating awareness on national security threats, raining alarm on national security issues and making people alert on national security issues.
Conclusion/Recommendations
This study concludes that internet-based media such as the Facebook, Twitter, YouTube, Gmail, and Yahoo mail play critical role in matters relating to national security. Such communication channels are like guns in the hands of users. They could be used for good or for bad. They have both positive and negative impact on national security. The basic contribution of this study is that it has been able to harmonize diverging results on the impact of the internet on national security. The study has provided empirical evidence showing that the internet has both positive and negative use with corresponding impact on national security. The study has also contributed to our understanding of how to precisely use the internet to address national security issues in Nigeria. Theoretically, the study has also helped us in the understanding of the technological determinism theory by showing that it could be a relevant framework for studying issues related to national security. The researcher makes the following recommendations:
There is the need for the Federal Government of Nigeria to develop an application that will help in creating awareness on national security challenges in Nigeria.
Security agencies in Nigeria should significantly use internet-based media for tracking criminal elements in Nigeria whose activities pose a serious threat to national security.
There is the need for the traditional media like radio, TV, newspaper, and magazines to form a synergy with security agencies on how to better raise alertness on national security issues in Nigeria.
Further researchers should expand the scope of the study to cover more states in Nigeria so as to give room for generalization.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
