Abstract
This article offers some remarks on a few critical issues related to explanation in criminal network research. It first discusses two distinct perspectives on networks, namely a substantive approach that views networks as a distinct form of organisation, and an instrumental one that interprets networks as a collection of nodes and attributes. The latter stands at the basis of Social Network Analysis. This work contends that the instrumental approach is better suited to test hypotheses, as it does not assume any structure a priori, but derives it from the data. Moreover, social network techniques can be applied to investigate criminal networks while rejecting the notion of networks as a distinct form of organisation. Next, the article discusses some potential pitfalls associated with the instrumental approach and cautions against an over-reliance on structural measures alone when interpreting real-world networks. It then stresses the need to complement these measures with additional qualitative evidence. Finally, the article discusses the use of Quadratic Assignment Procedure regression models as a viable strategy to test hypotheses based on criminal network data.
Introduction
Scholars and practitioners alike are increasingly adopting a network perspective to explore criminal phenomena. Varese (2010) has noted that, since the 1990s, an increasing number of definitions of organised crime have started to include the term ‘network’ (p. 7). At the same time, formal network analysis techniques are being used more and more to study interactions among offenders. Social network analysis (SNA), as maintained by Bouchard and Amirault (2013), has finally ‘taken root in the field of criminology’ (p. 199; see also Bruinsma and Bernasco, 2004: 79). Moreover, Papachristos (2011) has pointed out that we may be witnessing the ‘coming of a networked criminology’ (p. 101).
However, some ambiguity around key concepts still remains, starting from the very same notion of ‘network’: is it a specific form of organisation or just a collection of actors and ties? Are these two perspectives on networks invariably intertwined or can we apply social network techniques while rejecting the notion of networks as a distinct form of organisation? To shore up the foundations of criminal network research, it is vital to fully address this ambiguity. In addition, while the number of articles devoted to the study of criminal networks has undoubtedly increased in the recent past, a large proportion of them still remains descriptive in nature (Carrington, 2011: 248; Papachristos, 2011: 112; Papachristos, 2014: 350). The aim of this article is to foster explanatory research in the field by offering some remarks on selected critical issues related to the study of criminal networks.
This work starts by discussing two different perspectives on networks while examining the implications for criminologists (Section ‘Conceptualising social (and criminal) networks’). Ultimately, this article favours an instrumental approach to networks, interpreted as a collection of actors and ties, and regards it as the most fruitful strategy to foster explanation in criminal network research. This approach, however, is not without its pitfalls: the section, ‘Potential pitfalls in criminal network research’, will explore the dangers of an over-reliance on structural measures. Finally, the section, ‘Explanation in criminal network research: The use of QAP regression models’, will discuss a viable strategy to assess the determinants of criminal networks, and explaining why a given network is structured in the way we have observed. This strategy is based on the use of a Quadratic Assignment Procedure (QAP) regression method.
Finally, two caveats: first, this article mainly focuses on the study of criminal networks defined as ‘the organisation of criminal groups and activities’ (Carrington, 2011: 236), thus leaving aside other possible applications of network analysis relevant to criminologist, for instance the study of how personal networks may influence crime and delinquency (for an insightful review of the latter, see Carrington, 2011: 236–243). Second, the aim of this article is not to present an up-to-date review of literature: Morselli (2009, 2014), Carrington (2011) and Bichler and Malm (2015) offer a compelling and comprehensive overview of the state-of-the-art research in the field.
Conceptualising social (and criminal) networks
On the face of it, one might be tempted to regard the question of what a network is as a trivial one. However, at least for researchers interested in explaining the organisation of criminal activities, the answer is far from unambiguous. Broadly speaking, there are two distinct ways of conceptualising networks. One perspective, which can be defined as ‘substantive’, interprets networks as a specific form of organisation. The second perspective, which can be regarded as ‘instrumental’, defines networks as based on the presence of two constitutive sets of elements: actors (nodes) and relationships (ties). This dualism is a long-standing source of ambiguity and misunderstanding among scholars and practitioners alike. Morselli (2009: 10), Von Lampe (2009: 96) and Varese (2010: 8) have highlighted the tension between the substantive perspective and the instrumental one in the context of criminal networks. Given the increasing popularity of networks in criminological research, it is vital to discuss this dualism at some length. In addition, the adoption of a substantive rather than an instrumental approach has a direct impact on the extent to which we can perform explanatory research in the context of criminal networks. I will now examine the defining characteristics of both perspectives.
Networks as a form of organisation
The idea of conceptualising networks as a distinct form of organisation arose in opposition to the ‘conventional’ view that identifies only two possible forms of coordination among economic actors: market and hierarchy (Podolny and Page, 1998; Powell, 1990). The latter view can be traced back to the seminal work of Ronald Coase, The Nature of the Firm, published in 1937. In this work, Coase (1937: 388) puts forward the idea that production, and by extension economic exchange, can be coordinated in two alternative ways: (1) through the price mechanism that underpins transactions in the market or (2) through the decisions of an entrepreneur who directs production within a firm (hierarchy). Coase’s ideas gained prominence in the Seventies when Oliver Williamson put them at the basis of the new transaction cost economics to explain coordination and governance of economic activities (Williamson, 1973; also 2005). Over the years, the original dichotomy has been reinterpreted as a continuum to capture hybrid forms of governance, for instance long-term contracting (see, for example, Williamson, 2005: 7). However, this continuum remains firmly anchored in the market vs. hierarchy framework.
Organisational scholars and sociologists have challenged the premises of the Coase-Williamson framework by suggesting the presence of a third, separate, mode of exchange: the network. According to Powell (1990), the continuum suggested by Williamson is still ‘too quiescent and mechanical’ (p. 299); by ‘sticking to the twin pillars of markets and hierarchies, our attention is deflected from a diversity of organizational designs that are neither fish nor fowl, nor some mongrel hybrid, but a distinctly different form’ (p. 299). He then suggested a third form of organisation, namely the network, defined in the following way: Networks are ‘lighter on their feet’ than hierarchies. In network modes of resource allocation, transactions occur neither through discrete exchanges nor by administrative fiat, but through networks of individuals engaged in reciprocal, preferential, mutually supportive actions. Networks can be complex: they involve neither the explicit criteria of the market, nor the familiar paternalism of the hierarchy. (Powell, 1990: 303)
Podolny and Page (1998) offer a more formal definition of ‘network’ as a distinct form of organisation: We define a network form of organization as any collection of actors (N ⩾2) that pursue repeated, enduring exchange relations with one another and, at the same time, lack a legitimate organizational authority to arbitrate and resolve dispute that may arise during the exchange. (p. 59)
One of the defining characteristics of the network form of organisation is trust. According to Podolny and Page (1998), a ‘more trusting ethic’ makes the network ‘not reducible to a hybridization of market and hierarchical forms, which, in contrast, are premised on a more adversarial posture’ (p. 61).
Scholars in criminology have also embraced the concept of network to describe a (supposedly) new mode of operation adopted by criminals as well as terrorists. This ‘emerging’ organisational form is believed to pose a ‘new’ threat to the security of states (Arquilla and Ronfeldt, 2001). For example, Williams (2001) maintains that ‘there is a growing recognition that organized crime is increasingly operating through fluid network structures rather than more formal hierarchies’ (p. 62). He points out that ‘networks are one of the most common forms of social organization. They are simultaneously pervasive and intangible, ubiquitous and invisible, everywhere and nowhere’ (Williams, 2001: 64). According to Williams (2001), networks are ‘an ideal form for organizing criminal activities’ (p. 64) as they possess a number of characteristics that makes them particularly appealing to criminals: they are flexible and dynamic (p. 67); they are able to limit the exposure to risks as networks possess limited fixed assets and higher adaptation than hierarchies (p. 74); and they allow the formation of flexible alliances among criminals as well as between criminals and corrupt individuals (p. 77–80). Practitioners too have embraced the ‘new’ network paradigm and have started to adopt the network form of organisation in their description of the underworld. For instance, the latest Serious and Organised Crime Threat Assessment compiled by Europol (2013), explicitly states that ‘it appears that criminal groups increasingly employ network forms of organisation and behaviour’ (Europol, 2013: 33). Yet, the popularity of a substantive network perspective in the study of the organisation of criminal activities has not always been matched with a thorough reflection on the limits of such an approach. While, according to a number of scholars, the network form of organisation appears to be able to capture the essence of contemporary criminal endeavours (see, among others, Castells, 2000: ch. 3; Williams, 2001), a closer scrutiny of real-world evidence reveals a different picture.
Interpreting networks as a form of organisation rules out the possibility of looking at hierarchies through the network lens. This is indeed very limiting. As pointed out by Varese (2010), ‘hierarchies too are networks’ and ultimately ‘any organization can be thought of as a network-based social system’ (p. 13). Varese (2013) compellingly shows the potential of analysing the connections between members of a hierarchical organisation through a network approach (in this case it was a Russian Mafia group). By reconstructing the informal patterns of interaction, one can derive the structure of hierarchical organisations from the ground (Varese 2010, 2013; Campana and Varese 2012). This opens up the possibility to develop formal models to assess the determinants of these interactions as well as their change over time; crucially, this can also be carried out in relation to hierarchies (Campana and Varese, 2012; Varese, 2013; see also the section, ‘Explanation in criminal network research: The use of QAP regression models’).
Furthermore, not only organisations with an established hierarchy will be out of our reach, but the very same forms of organisation that are neither market nor hierarchy may, indeed, fall outside the conceptual domain of a substantive approach to networks. For instance, Campana (2015) presents a study of a transnational Nigerian human trafficking ring. The study shows that the ring under scrutiny does not possess an established hierarchy that is in control of all the activities, while being neither completely flat nor ‘fluid’. In other words, this ring is neither a classic example of hierarchy nor just a host of market-based transactions. However, the formal definition of the network form of organisation given by Podolny and Page (1998), or the one given by Powell (1990), seems unable to capture the dynamics observed in this ring. For instance, the majority of the key actors did not pursue repeated and enduring exchange relations with one another, that is, a defining property of the network form of organisation as interpreted by Podolny and Page (1998). Yet, this was not a completely flat ring as some degree of centralised coordination was indeed detected. In other words, a substantive approach to networks offers very limited analytical help; on the contrary, a continuum between market and hierarchy seems to capture reality much better.
Finally, the stress on trust as a constitutive element of the network mode of organisation (Podolny and Page, 1998: 61) is hard to reconcile with the reality of the Nigerian trafficking ring or, indeed, the underworld more generally. As documented by Campana and Varese (2013), trust is often in scarce supply among law-breakers (see also McCarthy et al., 1998).
Contrary to the received wisdom that sees the network form of organisation as ‘pervasive’ and ‘ubiquitous’ (Williams, 2001: 64, also Castells, 2000), the reality is that such an approach is indeed very limiting and often hard to reconcile with real-world manifestations of criminal endeavours. It is precisely because our object of study is situated on an extended continuum ranging, as noted by Morselli (2009: 1), from ‘a one-time partnership to execute a criminal venture’ to a ‘bureaucratic-like infrastructure that demands and enforces exclusivity on the actions and productivity of members’ that we need a radically different approach to the study of criminal networks. This article argues that the alternative approach discussed below is better-suited to fully grasp the mechanisms underpinning the organisation of criminal activities, and places us in a better position to test hypotheses on the formation of ties in criminal networks. Ultimately, as argued by Varese (2010: 13), ‘whether an organization is “slow moving” or “quick on its feet” is an empirical question rather than a theoretical premise or assumption’. Structure should be empirically reconstructed rather than assumed (Morselli, 2009: 18).
The instrumental perspective on networks
Rather than a distinct form of organisation, networks can be conceptualised as based on the presence of two distinct sets of entities: actors (nodes) and relationships (ties). Wasserman and Faust (1994) define a network as: a finite set or sets of actors and the relation or relations defined on them. (p. 20)
Similarly, Robins (2015) defines a social network as ‘a set of social actors and a relationship among them in the form of dyadic relational ties’ (p. 18, emphasis in the original). Within the broad domain of networks, ‘social networks are importantly distinctive in one major regard: the actors in the network have intentionality’ (Robins, 2015: 5, emphasis in the original). By and large, this is an instrumental perspective on networks. As pointed out by Borgatti et al. (2013), networks are ‘a way of thinking about social systems that focuses our attention on the relationships among the entities that make up the system, which we call actors and nodes’ (p. 1). This perspective is commonly referred to as Social Network Analysis (SNA).
SNA offers a set of conceptual tools and analytic procedures that allows researchers to first collect and systematise evidence in a relational way and then use the same evidence to test substantive hypotheses. When interpreted in this way, the concept of networks thus ‘provides us with a way of viewing social relations. It is not a theory of society, though the builders of theories will have to take such networks into account’ (Boissevain, 1974: 24–25). By adopting a relational approach to data collection, we are in a position to gather evidence on both actors and ties in a network, including the attributes of both entities (actors and ties). In very simple terms, the most basic unit of analysis is the dyad ‘Actor-Tie-Actor’ (Wasserman and Faust, 1994: 18). Once relational evidence has been collected, one can then run joint analyses of actors and ties (for a comprehensive discussion of SNA, see Wasserman and Faust, 1994; Carrington et al., 2005; Borgatti et al. 2013; Robins 2015).
An instrumental approach to networks has been applied to the study of a number of different social phenomena, from occupational mobility to research on communities, groups, markets and organisations (Wasserman and Faust, 1994: 6). Yet, the broad reach of this approach has come under criticism. For instance, the definition of ‘network’ upon which it is premised has been regarded as a ‘loose definition, designating nothing more than a set of interlinked elements that form a coordinating structure’ (Thompson, 2003: 54). Its ability to encompass a vast variety of organisational forms, including both markets and hierarchies, has been interpreted as a major limitation (Podolny and Page, 1998; Powell, 1990; Thompson, 2003). A second, related, criticism that has been formulated is that SNA is an empirically driven approach that lacks a structural model for the explanation of the phenomena observed (Thompson, 2003: 56). This article takes a different view, and contends that what may be perceived as a weakness is in reality a strength. For example, by not assuming a structure a priori, it is possible to test hypotheses on the mechanisms that have brought about that very same structure. Network analysis can indeed be combined with one or more substantive theories of network processes, such as preferential attachment, structural balance, social selection and social influence (for a review, see Robins, 2015: 28–38). More generally, SNA achieves its full potential when it is matched with substantive, theory-driven, research questions (Varese, 2010: 13; Campana 2015). There is no need to conflate the network approach with any prior assumption about the structure of a network, as the ‘network model’ of organisation would require. For instance, as suggested by Von Lampe (2009: 96), problems that have been formulated within organisational theory can find an answer using a network analysis approach.
In criminology, a network analysis approach to the study of organised criminal activities has been fruitfully adopted by an increasing number of scholars. Among the most recent works, Varese (2012, 2013) has applied SNA to the study of a Russian Mafia group; Campana and Varese (2013) to the comparative study of cooperation within a Russian and an Italian mafia group; Mancuso (2014), Morselli and Savoie-Gargiso (2014); Malm and Bichler (2011) and Campana (2015) to investigate human trafficking; Calderoni (2012) and Bright et al. (2012) to explore drug trafficking. Calderoni and Piccardi (2014) have applied a specific community detection algorithm (indeed, a network analysis technique) to reconstruct the structure of a Mafia organisation based on the attendance of its associates to meetings that were monitored by the police. Morselli (2014) offers an insightful collection of studies that have adopted a network approach to investigate a number of criminal phenomena, including the evolution of a drug co-arrest network (Iwanski and Frank, 2014), homophily effects among co-offenders (Van Mastrigt and Carrington, 2014), the core membership of a youth gang (Bouchard and Konarski, 2014), drug trafficking (Boivin, 2014; Gimenez-Salinas Framis, 2014) and cybercrime (Decary-Hetu, 2014; Dupont, 2014) as well as historical networks such as that established by Al Capone in Chicago during the Prohibition era (Papachristos and Smith, 2014). Earlier pioneering works using formal network models include Natarajan (2000, 2006), Morselli (2005) and Varese (2006).
Ultimately, the instrumental approach to networks (SNA) does not assume the existence of any structure a priori, but derives it from the evidence collected in a relational way (Morselli, 2009: 18–21; Varese 2010: 13; Campana and Varese 2012). This makes such an approach rather appealing, and well-suited to test hypotheses on the mechanisms that may have brought about the structure observed. However, this approach is not without its drawbacks, and I will now turn to discuss some possible perils.
Potential pitfalls in criminal network research
This section briefly touches upon a selection of issues that may arise when adopting an instrumental approach (SNA) to the study of criminal networks.
Dangers related to data collection
Inevitably, an instrumental approach to social networks is highly sensitive to the quality of the data collected. As with any network data, criminal network data is subject to a number of threats to validity and reliability. These include the incorrect attribution of characteristics of nodes and ties, and errors in data mining and in secondary sources (Borgatti et al., 2013: 37–40). Sampling can also be problematic: contrary to non-network approaches, a random sampling may severely distort inferences when a network is clustered around very few focal nodes (Robins, 2015: 11). Boundary-specification problems and issues of missing data can also be particularly acute (Kossinets, 2006; Robins, 2015: ch. 5). These threats are inherent to all network data; however, the specific nature of criminal behaviour may exacerbate the impact of some of them. For instance, missing data, i.e., potential missing nodes or ties, can pose a very serious issue to the validity of criminal network data; external validity procedures should therefore be adopted to double-check the evidence extracted from a given source (Campana and Varese, 2012: 16–17). When dealing with court records and police investigations, Campana and Varese (2012) suggest performing external validity checks based on information extracted from additional court and law enforcement files, interviews with key informants and other open source records. Whenever possible, an internal validity control (i.e. internal to the same source) should also be carried out, for example by contrasting the information extracted from the content of the tapped phone calls with the metadata related to the same set of conversations. Ultimately, the coverage of a specific source of network data should be carefully and critically scrutinised by researchers using all available contextual evidence.
An additional problem relates to the identification of the boundaries of a given network (Kossinets, 2006; Laumann et al., 1989). This is a key issue in network analysis, and it is arguably exacerbated in the case of criminal networks. This is due, for instance, to the lack of an accessible membership list according to which nodes can be included in a network. In addition, the boundary-specification problem may become even more acute when networks are composed of largely independent actors carrying out market-based transactions (Bouchard and Morselli, 2014: 294–295). Both the coverage and the boundary-specification problem have a direct impact on network measures, as the latter tends to be largely dependent on the structure of the network as a whole (Robins, 2015: 117). Morselli (2009: 44–50) and Berlusconi (2013) explore the impact of missing data and boundary-specification on real-world criminal networks.
Campana and Varese (2012) and Bright et al. (2012) critically assess the different sources of data that are available within the justice system, and the potential biases that each may include. The work of Campana (2015) shows that, when only an incomplete or not sufficiently reliable set of ‘1-mode’ network ties is available, researchers could adopt a ‘2-mode’ data collection strategy to minimise biases arising from coverage and boundary-specification problems. A typical ‘2-mode’ coding strategy would generate a network based on a series of events and the actors (nodes) associated with them. In summary, structural measures can be subject to biases due to errors, sampling procedures, boundary-specification problems and missing data. However, even structural measures that are not biased can still pose a challenge for researchers, particularly in relation to their interpretation.
Additional dangers in the interpretation of network data
Structural measures are indeed a very useful tool to investigate criminal network data. However, an over-reliance on structural measures alone without an adequate grasp of the context may lead to ambiguous or, worse still, misleading conclusions. If taken out of context, even simple statistics such as degree centrality, that is, the number of ties that an actor exchanges with the other actors in the network, may be rather ambiguous. Ambiguity can manifest itself in a number of ways that are worth discussing at some length.
Centrality measures are arguably among the most common statistical measures that researchers and practitioners alike calculate on criminal network data (for a formal discussion of centrality measures, see Wasserman and Faust, 1994: ch. 5). While the idea behind most of these measures – particularly degree centrality – is relatively straightforward, their interpretation is not always without challenges. Let us take degree centrality as an example. A high level of degree centrality is usually taken as an indication of prominence of a given actor. Conversely, a low level of degree centrality is commonly associated with peripheral actors. The latter are often interpreted as performing less important roles in a network. This may indeed hold true for many networks; however, this is not necessarily the case for all networks. To illustrate this point, I now turn to some additional analysis of the network included in Campana (2015).
The network under scrutiny includes 58 actors, of which 25 are offenders and 33 are victims. Figure 1 presents the distribution of degree centrality for the 25 offenders. 1 In this network, degree centrality indicates the level of participation in trafficking activities by each individual. Two actors immediately stand out as the most central players (#1 and #2); a third offender (#4) also scores relatively high. Then, the index quickly drops and we observe a rather large number of peripheral actors (a core group of three offenders was also identified by a core-periphery algorithm). Based on this figure, one would be tempted to conclude that the key players are only Actor #1, #2 and #4. The reality, however, is more complex.
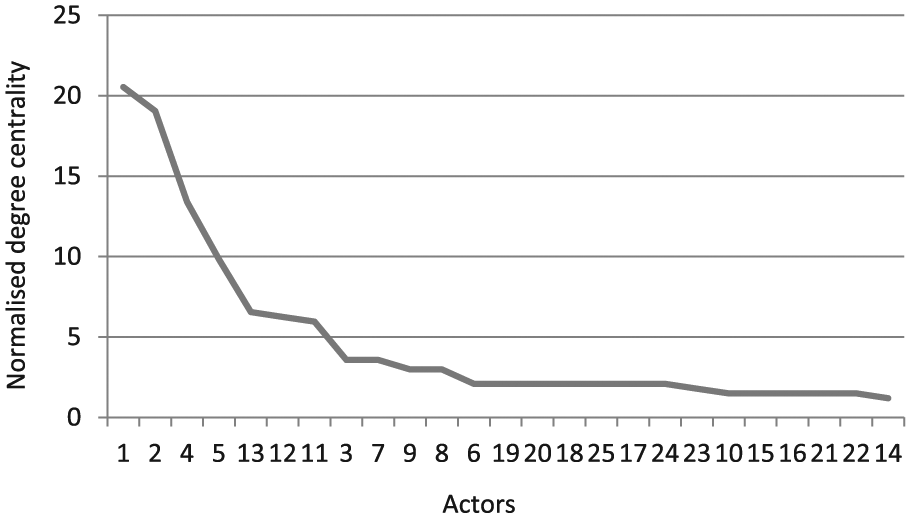
Human trafficking network: degree centrality by actor.
Based on the content of the phone conversations wiretapped and other evidence included in the court files, four distinct roles where identified: management, resource acquisition, escorting of victims (‘trolley’) and the so-called ‘madams’, typically former prostitutes turned into traffickers (for a full description, see Campana, 2015). On average, ‘madams’ present the lowest degree centrality in the network. 2 Should we therefore conclude that they also have a marginal role in the trafficking ring?
If we base our judgement on structural measures only, the answer will be in the affirmative. However, the content of the phone conversations and other evidence extracted from the court files tell us that this is not the case. In fact, it was the ‘madams’ who were generating the demand for the trafficking services that were then supplied by the individuals coded as ‘management’ (Actor #1 and #2 are included in this category). Indeed, the ‘managers’ were in charge of the transportation of victims from Nigeria to Europe, and in this respect they played an important role. Nonetheless, they worked as contractors hired by the ‘madams’. The low degree centrality of ‘madams’ is explained by the fact that they were largely independent of each other and of the other offenders (each tie in this network records the co-participation of two offenders in a given trafficking event). Yet, by no means are they marginal players in the ring; quite the opposite is true: they can be considered as key players (see Campana, 2015 for additional details on the modus operandi of the network).
What is crucial to stress here is that the presence of a tie is not the only important feature of a criminal network; the absence of a tie can be equally telling. Understanding the reasons why an actor has not established a given tie with another actor can be very informative (provided, of course, that this was not due to missing data). For this reason, one needs to complement structural measures with additional (often qualitative) evidence to have a full grasp of the mechanisms at play.
More generally, a joint analysis of the structure and content of criminal connections has been advocated by Campana and Varese (2012) and Varese (2013). Building on Natarajan (2000, 2006), Varese (2013) employs both structural measures and a systematic coding of the orders given by each actor to empirically test to what extent the Russian Mafia group under scrutiny could be considered ‘flat’ or hierarchically structured. Similarly, Calderoni (2012) includes both structural measures and measures of ‘status’ in his analysis of two Mafia organisations involved in drug trafficking. Westlake et al. (2011: 11) have applied a formal model developed by Schwartz and Rouselle (2009) to identify key players in an online child exploitation network; their model combines a measure of the resources available to each actor with measures of cohesion of the network as well as the strength of the relationships between actors. Instead of a task-based approach, Carley et al. (2002) have suggested taking the cognitive abilities of each actor into consideration in order to identify potential ‘leaders’. In their view, leaders may or may not be the central nodes in a network. 3
In addition, based on the idea that ‘centrality comes in many different forms’ (Morselli, 2010: 384), one can analyse the joint distribution of different centrality measures. For instance, Morselli (2010) has looked at a joint distribution of degree and betweenness centrality in order to identify different types of individual positioning within criminal networks. His work has shown that the individual positioning had an impact on the likelihood of arrest in the case of a Hells Angels group based in Canada: actors with high betweenness centrality but low degree centrality were less likely to be arrested (Morselli, 2010: 389).
To summarise, both the presence and the absence of a tie can equally represent an important feature of a given network. Up to this point, the article has focussed on the analysis of a single network. In reality, people, and indeed offenders, may share a multiplicity of ties (see, for example, Boissevain, 1974: 28–32). These ties can be both economic, for instance financial transactions, and non-economic, such as kinship. 4 To gain a full grasp of the mechanisms at play, one can model multiple networks simultaneously in a fashion similar to regression models. I will now discuss a possible strategy of doing so that is particularly well-suited to the analysis of criminal network data.
Explanation in criminal network research: the use of QAP regression models
Carrington (2011) has aptly noted that research on criminal networks ‘tends to be exploratory and descriptive rather than theory-testing’ (p. 244); for the most part, ‘it seeks to give a (literally) graphic account of the structure of the network being studied’ (p. 248). This has been reiterated by Papachristos (2014: 350; Papachristos, 2011: 112). Recently, there have been some interesting developments in teasing out possible factors that may lead to the disruption of criminal networks. Bichler and Malm (2015) include an informed, up-to-date, collection of works spelling out strategies to preventing crime by applying SNA to the study of various forms of organised crime and terrorism (on the structural differences between organised crime and terrorism due to their distinct time-to-task requirement, see Morselli et al., 2007). Yet, by and large, Carrington’s observation still holds true.
There are a host of reasons that may account for the limited number of explanatory studies using criminal networks, including the difficulties in accessing good quality data (on this, see; Campana and Varese, 2012; Bright et al., 2012). A further – yet crucial – complication lies with the very same nature of the data collected within a network framework. Due to their relational nature, network data violate the assumption of independence of observations upon which standard statistical models are built (Robins, 2015: 11; Wasserman and Faust, 1994: 4–5). This is a potentially serious problem as significance tests commonly included in standard statistical packages do assume independence of observations (Borgatti et al., 2013: 126). The implication is that, when seeking to explain how a given structure has been brought about (i.e. tie-formation), one cannot rely on the usual statistical tools. Yet, there are solutions to this problem as I briefly discuss below.
QAP regression models
The use of QAP regression models to test hypotheses on the organisation of criminal activities has been largely overlooked by criminologists. Nevertheless, these models may prove to be a very fruitful tool. QAP procedures offer a solution to the problem of auto-correlation, or non-independence, of observations (Dekker et al. 2007; Krackhardt, 1987, 1988). More specifically, QAP models are based on a family of procedures to perform a permutation-based nonparametric test of statistical significance on network data (Dekker et al., 2007: 565–566). The approach is akin to a linear regression, and the results can be interpreted in a similar way. In the case of a QAP regression, we typically regress a dependent network matrix on two or more independent network matrices. Regression coefficients are estimated through an ordinary least squares method (OLS). The major departure from a standard regression model is constituted by the way the significance test for these coefficients is performed. In a nutshell, a QAP procedure would create a number of randomly permuted matrices – usually between 10,000 and 50,000 – that are a random rearrangement of the original one. To determine whether a regression coefficient is statistically significant, the procedure compares the observed coefficient against the distribution of the same coefficient calculated on the randomly permuted matrices. If the observed coefficient is greater than 95 per cent of the random coefficients, this is considered to be statistically significant at the 0.05 level (see Borgatti et al., 2013:126–133; Whitbred, 2011: 732–734). Earlier approaches to permutation tests were confined to a rather restricted set of conditions (Dekker et al., 2007: 565). However, progress has been made on how permutations are performed and recently, thanks to the work of Dekker et al. (2007), a new permutation method has been proposed: Double-Semi-Partialing (DSP). Dekker et al. (2007) have shown the DSP method to be reasonably robust in models in which the dependent variable is continuous or at least countable integers (Poisson-like; for a formal description of the method, see Dekker et al., 2007). 5 The appeal of QAP regression models to criminologists lies in their ability to handle valued networks as dependent variables. The implication is that one can model the strength of contacts among offenders, for example, based on the number of phone calls exchanged or meetings attended. 6 Some basic conditions, however, need to be met in order for a QAP regression to be performed: all the matrices need to be square and of the same size, and they all have to include exactly the same actors. 7
Campana and Varese (2013) and Campana (2015) have pioneered the use of QAP models to test hypotheses using real-world criminal network data. Campana and Varese (2013) have tested the impact of kinship and violence on fostering cooperation among criminals. They have interpreted both devices as a way to establish credible commitments among offenders, thus situating their work in the broad literature on cooperation in the absence of law and trust. They collected data on contacts exchanged by members of two mafia organisations – a Russian Mafia group and a Neapolitan Camorra clan – and ran a series of QAP multiple regression models to estimate the impact on tie-formation of sharing information about violent acts and of sharing a kin-tie when controlling for other variables such as sharing the same task within the organisation. They have found evidence that both factors, kinship and violence, enhance cooperation. In addition, they have also discovered that violence has a much greater impact than kinship even in groups made up of relatives. They have concluded that there is nothing ontological in the role of kinship in organised crime, and when better and more reliable mechanisms to increase commitment are available, criminals will resort to them, just as organisations in advanced societies tend to rely on merit rather than kinship.
Campana (2015) is a study of the organisation of human trafficking. It relies on a novel, manually built, dataset recording the co-participation of offenders in trafficking activities between Nigeria and Europe (victims are also included in the dataset). It first elaborates a theoretical framework to interpret trafficking activities based on Coase (1937) and the theory of agency, and then derives and tests a number of substantive hypotheses on the organisation of ‘high-capacity’ trafficking networks. The network under scrutiny shows a tendency towards a separation between different stages of the trafficking process as a strategy to decrease monitoring costs and thus increase the overall ‘trafficking capacity’ of the ring. In addition, the study shows that even in networks that are not a unified organisation, there is still some level of centralisation. Nonetheless, coordination supplied by the core group of offenders did not extend to all the stages of the trafficking process, but was mostly confined to the transportation stage. Finally, a QAP regression model has also shown that, contrary to a widely held belief, the trafficking ring was not run along ethnic or family lines. Rather, a more sophisticated model based on division of labour and role specialisation was adopted by traffickers.
The QAP procedure presents some limitations. By performing random permutations on a matrix, it is able to calculate a significance test that is not biased by the non-independence of observations; however, the types of dependence present in a given network are not directly modelled. In other words, it is not possible to estimate the impact of local network configurations on the global structure of a network. Network processes such as reciprocity, local closure or more complex forms of dependence cannot be modelled directly, and therefore a measure of their impact cannot be estimated (for a formal discussion of different dependence assumptions, see Koskinen and Daraganova, 2013). To model structural configurations and actor-level attributes simultaneously, one needs to adopt a different strategy, for example, fitting an Exponential Random Graph Model (ERGM; for an excellent discussion on ERGMs, see Lusher et al., 2013). To date, ERGMs have been mostly limited to binary networks, and therefore used to predict the presence or absence of a tie, and not the strength of a relationship (Lusher et al., 2013; Robins, 2015: 193–194). Attempts to extend these models to valued networks are currently under way (see, for example, Krivitsky, 2012). In criminology, ERGMs have recently been applied to test hypotheses using binary networks in relation to intra-gang violence (Papachristos et al., 2013) and the role of ethnic homophily in gangs (Grund and Densley, 2015). 8
Conclusion
This article has offered some remarks on a few critical issues related to explanation in criminal network research. It has first discussed two perspectives on networks, namely a substantive approach that views networks as a distinct form of organisation, and an instrumental approach that interprets networks as a collection of nodes and attributes. The latter is at the basis of SNA. Ultimately, this article has argued against the conflation between the substantive and the instrumental approach. It has contended that the instrumental perspective (SNA) is the most productive strategy to foster explanation in criminal network research – in line with, among others, Varese (2006, 2013), Morselli (2009) and Campana and Varese (2012). SNA techniques can be fruitfully applied to explain criminal networks while rejecting the notion of networks as a distinct form of organisation. In addition, the instrumental approach allows researchers to derive the structure of a network from the empirical evidence rather than merely assuming it (Morselli, 2009; Varese, 2010). This also opens up the possibility to test hypotheses on tie-formation using real-world data. SNA achieves its full potential when matched with substantive, theory-driven, research questions.
This approach, however, is not without its pitfalls. Besides the issues related to data collection and the quality of the data available, this article has cautioned against an over-reliance on structural measures alone as the latter may lead to ambiguous if not misleading interpretations. In line with Varese (2013) and Campana and Varese (2012), this article has thus invoked a greater emphasis on additional – qualitative – evidence when investigating real-world criminal networks. Finally, this work has sought to foster explanation in criminal network research by discussing an empirical strategy to test hypotheses using (multiple) network datasets. This strategy is based on QAP regression models. Some recent applications reviewed in the article have shown this procedure to be particularly apt for the study of a number of research questions relevant to criminal network researchers.
Footnotes
Acknowledgements
I am very grateful to the Editor and the three anonymous reviewers for their most helpful comments. I owe a large debt of gratitude to Federico Varese for introducing me to SNA and for a countless number of extremely insightful discussions on the topics explored in this article.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
