Abstract
Information theft and cyberbullying pose significant threats to users’ privacy on social media. This study applies Protection Motivation Theory (PMT) to explore how online information disclosure awareness and privacy concerns influence protective actions, such as regulated social media usage and detoxification, in response to negative experiences like data heist and cyberbullying. Analyzing survey responses from 1,000 social media users in Pakistan, ranging in age from 18 years to over 50, and using the snowball sampling technique, our findings reveal that awareness of online information disclosure mediates the relationship between data theft and regulated social media use. Privacy concerns similarly mediate the relationship between cyberbullying experiences and social media detoxification, aligning with PMT. In addition, negative online experiences directly correlate with privacy safety behaviors, indicating that motivations may not always drive protective actions. This research sheds light on the intricate dynamics between privacy concerns, negative online experiences, and protective behaviors, offering insights for interventions and policies to enhance users’ digital privacy and safety. Understanding these relationships is crucial for addressing the challenges of information theft and cyberbullying in the digital landscape.
Keywords
Introduction
The increasing use of technology has raised significant concerns about online privacy. Data collection and sharing are now common on the internet, causing many users to worry about their personal information being accessed or monitored without permission (Ogonji et al., 2020). Websites can gather extensive personal data even without user registration, often using cookies that track sensitive details such as location and employment history (Kaur & Randhawa, 2020). Major internet companies like Google, Yahoo, and Facebook not only tailor advertisements using these data but also share it with affiliated companies, raising privacy concerns (PC) (Mondal et al., 2022). The controversy surrounding Facebook’s unauthorized sharing of user data highlights the risks in social network services. The Cambridge Analytica scandal, one of the most widely reported data breaches of 2018, exposed the unauthorized harvesting of data from about 87 million individuals. These data were later used to create targeted ads, allegedly influencing voter preferences in the 2016 US presidential election. This situation emphasizes the need for users to protect their personal information (Mousavi et al., 2020).
The rise in online information theft has heightened users’ concerns about internet privacy. Unauthorized access to personal data can lead to misuse, resulting in severe consequences, including cyberbullying from stolen social media information, causing distress and insecurity (Wall, 2022). Cyberbullying encompasses online threats, posting damaging content, negative comments, and false allegations on social media, all of which significantly impact mental health (Rihhadatul Aisya, 2024). Furthermore, compromised personal contact details can lead to targeted harassment or identity theft. Therefore, it is essential to examine how individuals, especially those not well-versed in security, interact with online social networks to prevent such violations (van Schaik et al., 2018).
In addressing online PCs, recent studies have increasingly applied the Protection Motivation Theory (PMT) to understand user behaviors (Boerman et al., 2018). PMT suggests that individuals first cognitively assess a threat before developing a motivation to protect themselves and ultimately adopting protective behaviors (Sadri et al., 2022). Supporting this model, empirical evidence shows that the motivation to protect oneself, such as PCs and awareness of identity disclosure, can indeed predict protective behaviors among social media users ( H.Chen et al., 2016). In addition, these protective motivations and actions are often triggered by negative online experiences (Cho, 2022).
This study examines the privacy-protection behaviors of social media users in Pakistan. It focuses on how users respond to negative experiences, such as data heist (DH) and cyberbullying (CYBRBULY). Using PMT, it explores how these experiences trigger privacy-protection motivations, leading to behaviors like regulated use of social media (RUSM) and social media detoxification (SMD) (Boerman et al., 2018). The study analyzes how online information disclosure awareness (OIDA) and PCs mediate the relationship between negative experiences and privacy-protection behaviors. It further examines whether these motivations prompt users to adopt practical strategies, escape strategies, or both.
In addition, this study investigates the direct relationship between negative online experiences and privacy-protection behaviors to understand whether motivational factors are essential for adopting these behaviors. It will evaluate the role of protection motivation factors, such as OIDA and PCs, in driving social media users to engage in privacy protection. By examining both the direct effects of negative experiences and the mediating role of motivational factors, this research aims to provide a clear understanding of the dynamics influencing users’ protective actions.
Literature Review and Hypothesis Building
PMT and Adopting Privacy-Protection Behaviors on Social Networking Sites
PMT, introduced by Rogers (1975), explains how individuals are motivated to protect themselves from perceived threats. According to PMT, the motivation to adopt protective actions depends on the perceived severity and likelihood of the threat, as well as the effectiveness of available protective measures. Later, Maddux and Rogers (1983) expanded PMT to include self-efficacy, defined as the belief in one’s ability to perform necessary protective behaviors effectively (Mousavi et al., 2020).
PMT centers around two cognitive processes: threat appraisals and coping appraisals (Chang et al., 2022). Threat appraisals assess the severity and vulnerability to potential threats, especially in information security (Masrek et al., 2022). Coping appraisals evaluate the effectiveness of protective measures and one’s ability to execute them, covering response-efficacy and self-efficacy (Herath & Rao, 2009). In this study, PCs and online information disclosure awareness (OIDA) serve as threat and coping appraisals, respectively. These cognitive evaluations enable individuals to understand the risks involved and determine the appropriate actions to protect their privacy. This dual appraisal process aids individuals in deciding how to best safeguard themselves against online security threats. This research underscores the diverse influences that can shape protective behaviors in digital environments.
Previous research indicates that negative online experiences can activate protection motivation, leading to protective behaviors (Mousavi et al., 2020). However, these studies often overlook specific drivers of protection motivation, like PCs or OIDA. Protection motivation is a broad concept, covering various factors that prompt users, particularly on social media, to adopt certain privacy-protective actions. For instance, Ioannou et al. (2021) highlighted dispositional mindfulness as a motivator, suggesting that increased mindfulness can help enhance protection motivation, encouraging users to take protective measures. So there are different motivating factors suggested by previous researchers which lead to adoption of privacy-protection behaviors.
Previous studies have utilized diverse sets of factors, including negative online experiences, to apply PMT in examining social media privacy behaviors. Salleh et al. (2013) explored how sets of perceived threats on social networking sites (SNS) can enhance users’ trust in these platforms, subsequently motivating them to conceal personal information. Mehraj et al. (2021) identified sets of PCs as key motivators driving users to adopt strategies to mitigate risks associated with negative online experiences. Furthermore, H.Chen et al. (2016) investigated how sets of negative experiences, such as information theft and relational conflicts, lead to an increase in PCs and awareness. This heightened awareness prompts users to engage in protective behaviors, including identity masking and adjusting privacy settings. Collectively, these studies underscore the intricate relationship between sets of perceived online threats and users’ protective actions on social media.
The Role of DHs in Regulating the Use of Social Media
DH refers to the unauthorized acquisition of personal information, images, and identity details from users’ social media accounts, typically by criminals. These stolen data are often used for fraudulent or criminal purposes (Patel et al., 2017). Soussan and Trovati (2021) emphasize the ethical issues arising from the misuse of social media data, arguing that regulation is essential to prevent misuse and promote responsible data management. They note that incidents of data theft on social media highlight the need for regulated data usage. Furthermore, when users face compromised data, they are motivated to adopt control and surveillance mechanisms to safeguard their information (Soussan & Trovati, 2021, pp. 183–189).
Regulated use of social media (RUSM) involves various types of control mechanisms, as noted by Alvarado et al. (2018). These mechanisms can include applying privacy settings to social media posts ( L.Chen et al., 2018), regulating one’s social media friends list (Reza et al., 2017), applying privacy settings to personal information on social media accounts (Meng et al., 2018), and controlling who can view and download pictures on social media (Usharani & Anitha, 2022, pp. 372–384).
When users experience the theft of personal information or content on social media, they may feel a heightened need to protect their privacy. This type of data breach is a common negative privacy experience associated with increased regulation of social media use, as users seek to feel safer and more secure (Zhu & Song, 2022). Therefore, based on the above discussion, we propose the following hypothesis:
Hypothesis 1 (H1). Data heists on social media lead to the regulated use of social media platforms.
The Impact of DHs on SMD
Data theft on social media has become a significant issue, leading to increased concerns about privacy and security. As a result, many users turn to strategies like SMD, which involves reducing or temporarily ceasing social media use to mitigate risks (Syvertsen & Syvertsen, 2017). The lack of digital competence among users often leads to avoidance behaviors, where they feel more comfortable withdrawing from platforms than addressing the underlying security issues ( H.Chen et al., 2016). Research by Sharma and Kumar Sharma (2020) highlights that data theft can cause users to suspend their social media activities as a precautionary measure against future cybercrimes.
In more extreme cases, individuals may deactivate their accounts entirely, choosing to remove themselves from these platforms to prevent further exposure to risk (Joe & Ramakrishan, 2014). In addition, some users, in response to security breaches, seek more face-to-face interactions and deliberately distance themselves from social media (Sapuppo & Seet, 2015). Such experiences often result in feelings of regret, with individuals reconsidering their involvement with social media and the level of personal information they have shared online (Geetha et al., 2020).
There is a clear connection between data theft on social media and the practice of SMD. The experience of DH pushes users to disengage from platforms to protect their privacy and well-being. El-Khoury et al. (2020) found that individuals often reduce or eliminate their social media use as a way to safeguard their personal information. DH increases feelings of vulnerability, prompting users to take protective actions, such as detoxifying from social media, to regain control over their digital presence (Joe & Ramakrishan, 2014).
This process of detoxification allows users to distance themselves from potential risks while also addressing the psychological impacts, such as anxiety and mistrust of digital platforms (Geetha et al., 2020). According to Sharma and Kumar Sharma (2020), SMD serves as a proactive coping mechanism to avoid future DH incidents, helping users feel more secure. Given these observations, the following hypothesis is proposed:
Hypothesis 2 (H2). Data heists on social media lead to social media detoxification.
The Influence of Cyberbullying on Regulated Social Media Use
Cyberbullying is a major issue in social media environments, characterized by intentional and repeated harm inflicted through digital platforms, including computers and smartphones (Doane et al., 2016). Research by Chang et al. (2022) suggests that such negative experiences significantly influence user behavior on social media. The prevalence and severity of cyberbullying are evident in studies, such as one by Doane et al. (2015), which found that a large majority of college students have experienced cyberbullying in various forms: 78% encountered deceptive acts, 88% were targets of malicious attacks, 73% faced public humiliation, and 66% dealt with unwanted contact. These statistics highlight the pervasive nature of cyberbullying and its impact on individuals.
Cyberbullying experiences often prompt users to adjust their content and account settings to protect themselves (Jain et al., 2021). This regulatory behavior stems from the potential damage to a user’s reputation caused by aggressive or harmful content posted online (Wang & Potika, 2021). In addition, cyberbullying may include the dissemination of rude, insulting, or offensive comments designed to tarnish a user’s image among peers and family (Tommasel et al., 2018). Consequently, these negative experiences of cyberbullying prompt users to actively manage their social media presence by implementing various privacy settings and controls on their accounts (Khairy et al., 2021).
Cyberbullying represents a serious challenge to privacy on social media, prompting users to adopt various coping strategies based on their computer proficiency. These strategies typically involve adjusting privacy settings and utilizing mechanisms designed to mitigate the risk of cyberbullying. Based on this, we assume that:
Hypothesis 3 (H3). The experience of cyberbullying on social media is positively correlated with regulated use of social media.
The Role of Cyberbullying in SMD
Cyberbullying victims often experience negative emotions such as embarrassment, depression, and social isolation, which can lead to severe consequences, including suicide attempts (Chatzakou et al., 2019). To cope with these effects, some individuals choose to suspend or detox from social media. This step is often taken to safeguard their mental health, serving as a protective response to the challenges posed by cyberbullying (Giumetti & Kowalski, 2022).
Stress and public humiliation are key factors that urge a user to decide to keep distance from social media as it is not a safe space (Gu et al., 2022). Furthermore, cyberbullying may lead users to suspend social media use due to the significant negative impact on victims’ lives, causing fear, intimidation, and difficulty in detecting bullying content (Suhas Bharadwaj et al., 2023). Therefore, we can propose that:
Hypothesis 4 (H4). Experiences of cyberbullying on social media are positively correlated with social media detoxification.
Impact of OIDA on Data Theft and Regulated Social Media Use
However, not all studies fully document the sequential process from these initial assessments to the adoption of protective behaviors. For instance, a study by H.Chen et al. (2015) revealed that the cost-benefit appraisal directly influenced privacy-protection behaviors without being fully mediated by privacy safety motivations, suggesting the possible existence of other mediating factors in the pathway from risk appraisal to protective actions.
Online information disclosure awareness involves understanding that certain types of private information are accessible online. This awareness is a part of the broader concept of privacy awareness, which focuses on an individual’s knowledge of privacy issues on the internet (H.Chen et al., 2016). Negative experiences related to privacy can increase a person’s concern about the safety of their information online. These experiences often encourage individuals to seek out more information on how to protect their privacy, thereby increasing their awareness (Smith et al., 1996). Furthermore, this heightened awareness enables users to adjust their privacy settings on platforms such as Facebook. They can set their posts to be visible to just themselves, specific people, friends, friends of friends, or everyone. This customization helps reduce the risk of data theft (Padyab et al., 2019).
The recognition of the importance of personal information motivates users to protect their data from theft on social media platforms (Parker & Flowerday, 2021). This awareness also helps users manage their social media use by implementing adaptive privacy interventions. These interventions are guided by privacy heuristics, which provide users with more control over the disclosure of their online information (Ferreyra & Emilio, 2019). In addition, research by H.Chen et al. (2016) indicates that a social media user’s awareness of their own disclosure behaviors is a key motivating factor in reducing the risk of data theft. Users mitigate these risks by adjusting their privacy settings, managing their contacts, and controlling access settings.
Therefore, the OIDA encompasses considerations of severity, vulnerability, and cost/reward, which are related to the cognitive judgments involved in adopting risk-reducing behaviors in response to perceived threats (Maddux & Rogers, 1983; Rogers, 1975). This understanding leads us to propose the following hypothesis:
Hypothesis 5a (H5a). Awareness of online information disclosure positively mediates the relationship between data heist on social media and regulated use of social media.
Impact of PCs on Cyberbullying and Social Media Detoxification
Empirical studies show that online PCs can motivate social media users to adopt protective behaviors when they have negative online experiences (Vrhovec & Damjan Fujs, 2023). These PCs mainly involve fears about losing control of personal information shared on social media platforms (Saura et al., 2023). As a result, PCs are considered an important mediating factor between negative online experiences and protective behaviors (Baruh et al., 2017). However, some researchers argue differently, suggesting that PCs do not significantly influence how perceived risks lead to information-protection behaviors on social media ( H.Liu, 2022; H.Liu & Wang, 2023; Meier & Krämer, 2024).
Cyberbullying on platforms like Facebook underscores the necessity for robust online privacy measures, as it exposes users to various types of harassment and abuse (Khairy et al., 2021). This pervasive issue can lead adults to temporarily disengage from social media as a way to prevent future incidents (Triantafyllopoulou et al., 2021). In addition, PCs stemming from cyberbullying incidents encourage users to adopt behaviors aimed at preserving their privacy (Ramezanian & Niemi, 2019). Such experiences can also lead individuals to take breaks from social media to recover from these negative interactions, ultimately affecting their mental health and well-being (Yang, 2023).
Online PCs have been shown to mediate the impact of cognitive appraisals on the adoption of privacy-protection behaviors (Lwin et al., 2007). These behaviors include strategies such as SMD, which serves as an escape mechanism from negative online experiences (H. Chen et al., 2016). Based on these findings, we propose the following hypothesis:
Hypothesis 5b (H5b). Privacy concern positively mediates the relationship between cyberbully experience on social media and social media detoxification.
The conceptual framework for this study, based on the proposed hypotheses, is presented in Figure 1.

Hypothesized conceptual model.
Method
Information of Study Participants
The study gathered data from a diverse sample of 1,078 social media users across Pakistan, ensuring good geographic representation. To remove invalid responses, a cross-checking method was used. Responses were excluded if a participant gave the same answer to all questions. This process resulted in a final sample size of 1,000 social media users. According to the Population Welfare Department of Punjab, Punjab is the largest province in Pakistan by population, home to more than half of the country’s population. As such, 400 participants were selected from Punjab province and the Islamabad Capital Territory. The remaining 600 participants were distributed as follows: 150 participants from Khyber Pakhtunkhwa, 150 from Sindh, 150 from Balochistan, and 150 from the combined regions of Gilgit-Baltistan and Kashmir. This diverse sample ensures a more reliable generalization of the results to the target population. Table 1 presents the basic demographic information of the study samples.
Basic Information of Samples.

Data Collection and Study Samples
We selected an online survey conducted via Google Forms to study social media users in Pakistan. This method is cost-effective, allows access to a broad audience, and efficiently manages data. In addition, it enables us to reach diverse groups, although it poses some challenges in sampling and generalizing the results (Goodfellow, 2023). Online surveys are particularly suitable for researching social media behaviors (Li et al., 2018). The questionnaire was constructed in English, as it is the official language of Pakistan and the medium of instruction in educational institutions. Participants were reached through various social media platforms, including WhatsApp and Facebook groups, where we posted the Google Forms link. We also requested users who completed the questionnaire to share it with their friends and family members who use social media. No rewards or compensation were provided to the respondents. The data-collection process started on 7th December 2023 and ended on 10th January 2024.
The survey made it clear that participation was voluntary, and respondents were informed of the study’s purpose and their rights, including anonymity and the right to withdraw at any time. This ethical framework aligns with established research practices, safeguarding participants’ rights while ensuring the integrity of the data collected. In addition, ethical approval was obtained from the Academic Review Committee of the School of Journalism & Information Communication at Huazhong University of Science and Technology, Wuhan, China, before data collection commenced.
Development of Measurement Scale
The survey employs a five-point Likert-type scale ranging from “strongly disagree” (1) to “strongly agree” (5) for all questions except for demographics. The survey is structured into four sections: demographic questions, exploration of negative online experiences, privacy motivations, and privacy-protection behaviors. Established scales from prior research are used to ensure accuracy and relevance. The detailed measurement scale for each variable is provided in the Appendix.
Data Heist
The measurement of DH was adapted from the insights provided by H.Chen et al. (2016) and Fire et al. (2014). This construct captures the extent to which participants have experienced unauthorized access to or misuse of their personal information on social media. The items used to measure DH include: “My personal information has been stolen from social media, either once or multiple times,” “My social media account has experienced unauthorized access, either once or multiple times,” “My friends and family have received fake friend requests using my name and profile picture,” and “I have received fake friend requests impersonating my friends, family, or people I know, using their names and pictures.” Responses were scored on a 5-point Likert-type scale, ranging from 1 (completely disagree) to 5 (completely agree).
Cyberbullying (CYBRBULY)
The measurement of cyberbullying was adapted from the scales developed by Ho et al. (2017) and Abaido (2019). This construct assesses the extent to which participants have experienced various forms of online harassment or threats. Items used to measure cyberbullying include: “I have received one or multiple online threats from someone, in which they’ve threatened to post something that could harm my reputation,” “Someone has posted harmful and vulgar content about me on social media, potentially damaging my image,” “A friend or family member who was angry with me harassed me on social media with shameful comments,” and “Someone raised false allegations against me on social media to damage my image.” Responses were scored on a 5-point Likert-type scale, ranging from 1 (Never) to 5 (Always).
Privacy Concerns
PCs were measured using items adapted from Bright et al. (2015) and Fogel and Nehmad (2009). This construct assesses the level of concern participants have regarding the security of their personal information on social media. Items used to measure PCs include: “I am much concerned about the possibility of my pictures and other information being stolen from social media,” “I am greatly concerned about the possibility of my social media account being attacked by hackers,” “I am deeply concerned about someone using my picture, name, and personal information to create a fake social media account,” and “I am much concerned about the potential for someone to harass or blackmail me on social media.” Responses were scored on a 5-point Likert-type scale, ranging from 1 (Strongly disagree) to 5 (Strongly agree).
Online Information Disclosure Awareness
OIDA was measured using items adapted from the study by H.Chen et al. (2016). This construct assesses participants’ awareness regarding safe practices in disclosing personal information on social media. The items used to measure OIDA include: “I am aware of how to avoid disclosing my online identity,” “I am aware of how much personal information I should disclose on my social media account,” “I am aware of the preferred photo posting practice on my social media account, which may involve sharing photos in groups rather than individually,” and “I am aware of what and how much of my routine activities to post on social media, such as dining out with friends, attending academic seminars, or going to the cinema.” Responses were scored on a 5-point Likert-type scale, ranging from 1 (Strongly disagree) to 5 (Strongly agree).
Regulated Use of Social Media
The RUSM was measured using items adapted from the study by Hajli and Lin (2014). This construct examines participants’ preferences for controlling access to their social media content and personal information. The items used to measure RUSM include “I prefer to control who can view my social media posts,” “I prefer to control who can view my friends list on social media,” “I prefer to control who can view my personal information on social media,” and “I prefer to control who can download the pictures I post on social media.” Responses were scored on a 5-point Likert-type scale, ranging from 1 (Strongly disagree) to 5 (Strongly agree).
Social Media Detoxification
The SMD construct was assessed using items adapted from the study by Fan et al. (2021), Fu and Li (2022), Fu et al. (2021), and Gan et al. (2024). This construct explores participants’ tendencies to reduce or stop social media use due to PCs. The items used to measure SMD include: “I have deactivated my social media account at least once or multiple times,” “Due to PCs on social media, it is preferable to engage in physical socialization rather than relying on social media,” “Sometimes, suspending or stopping the use of social media is the best way to cope with privacy issues,” and “Sometimes, I believe that not being a social media user would be a better choice.” Responses were scored on a 5-point Likert-type scale, ranging from 1 (Strongly disagree) to 5 (Strongly agree).
Composite Reliability and Validity of Measurement Scale
We assessed the measurement model’s fit using criteria from the study by Hsu and Lin (2008) and Lim (2015). Composite reliability, which gauges construct reliability, followed Fornell and Larcker’s (1981) method. S.Liu and Wang (2016) suggested a .70 threshold for acceptable reliability; in our study, all constructs surpassed this, ranging from .829 to .864 (see Table 2). Cronbach’s alpha coefficients for each construct exceeded .70, meeting the standards set by Hair et al. (2014).
Factor Loadings, CR, AVE, and VIF.

To assess convergent validity, we considered both average variance extracted (AVE) and factor loadings, following Fornell and Larcker’s (1981) recommendation. Hair et al. (2011) suggest AVE values above 0.50 and factor loadings over 0.60 for adequate convergent validity. Our findings revealed AVEs ranging from 0.662 to 0.710, all above 0.50, and factor loadings from 0.787 to 0.852, surpassing the 0.60 threshold. Hence, our instrument showed no concerns regarding convergent validity.
In addition, we evaluated construct reliability using rho_c, with values surpassing the .70 threshold, ranging from .887 to .907. These results collectively affirm strong reliability and convergent validity of our measurement instrument, validating the robustness of our measurement model (Hair et al., 2014; S.Liu & Wang, 2016).
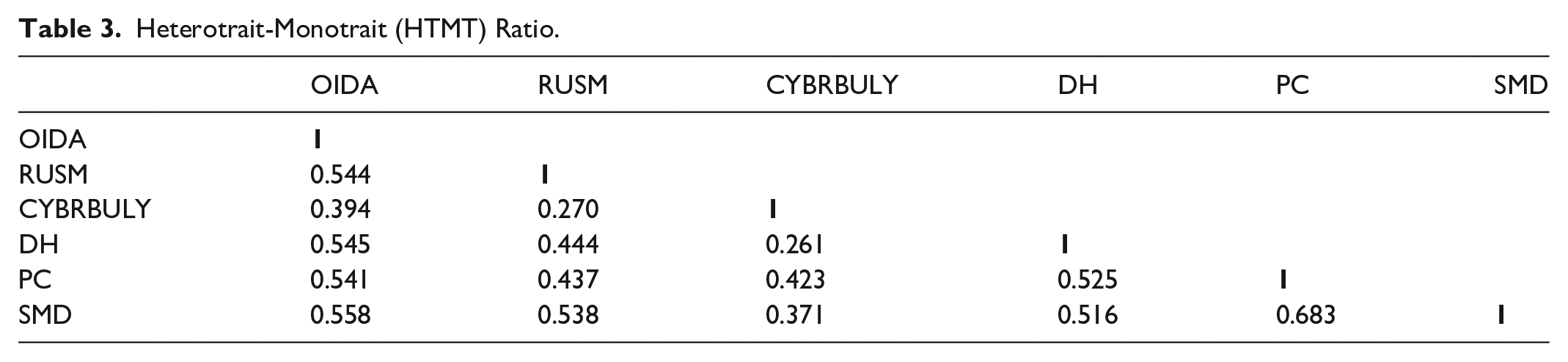
Henseler et al. (2015) recommended that Heterotrait-Monotrait (HTMT) ratio should be used to assess the construct discriminant validity. The HTMT ratio should be less than 0.85 (Benitez et al., 2019). The HTMT ratios of this study constructs were between 0.261 and 0.683 (<0.85, see Table 3). That also confirmed the no issue of discriminant validity.
Heterotrait-Monotrait (HTMT) Ratio.
Testing Model Fit
In SmartPLS, which performs variance-based structural equation modeling (SEM), two key indicators are used to assess the model’s fit: the standardized root mean square residual (SRMR) and the normed fit index (NFI). For a model to be considered a good fit, the SRMR value should be below 0.08, and the NFI value should be above 0.90 (Henseler et al., 2015). Since we have a saturated model with no free paths, the saturated model (measurement) fit values and the estimated model (structural model) fit values are almost same and meeting the criteria. The results indicated that SRMR values for saturated model and estimated models are 0.037 and 0.051 (<0.08) respectively and the NFI value was 0.960 (>0.90; is in acceptable region). Moreover, the discrepancy measure based on unweighted least squares (dULS) < bootstrapped high-confidence interval (HCI) 95% of dULS and discrepancy measure based on generalized least squares (dG) < bootstrapped HI 95% of dG, indicating the data fit the model well.
Results
Descriptive Analysis
Table 4 shows participants exhibited moderate concerns regarding data breaches (DH: M = 3.06, SD = 1.102), privacy breaches (PC: M = 3.11, SD = 1.060), and online identity awareness (OIDA: M = 2.99, SD = 1.055). Cyberbullying experiences were slightly lower (CYBRBULY: M = 2.92, SD = 1.102). Participants showed higher engagement in regulating social media use (RUSM: M = 3.62, SD = 1.001) and moderate detox behavior (SMD: M = 3.42, SD = 0.941). All skewness and kurtosis values suggested a normal distribution of responses.
Descriptive and Correlation Analysis Results.

Correlation Analysis
Table 4 shows the correlation analysis of study variables. OIDA demonstrated moderate positive correlations with RUSM (r = 0.469, p < .01). Similarly, RUSM exhibited moderate positive correlations with CYBRBULY (r = .228, p < .01), DH (r = .38, p < .01), and PC (r = .377, p < .01). Furthermore, SMD demonstrated moderate positive correlations with OIDA (r = .472, p < .01) and PC (r = .579, p < .01). Demographic variables such as age, gender, education level, and time spent on social media showed no significant correlation with the main study variables and were therefore excluded from the correlation table. This lack of association indicates that these demographics may not have a significant impact on the constructs in this study, which supports the generalization of the results to all social media users, regardless of age, gender, education level, or time spent on social media. As a result, these variables were excluded as control variables in the SEM analysis, as they are unlikely to influence the primary relationships being examined.
Measurement of Structural Model
The structural model was assessed using Confirmatory Factor Analysis and Structural Equation Modeling (CFA-SEM) through SmartPLS4, focusing on its overall ability to explain relationships, the estimated path coefficients, and the t-values for each path in the model. To evaluate the model’s robustness, we applied a bootstrap resampling method with 95% confidence intervals and 5,000 samples. The results of these analyses are presented in Table 5 and Figure 2, confirming all of our hypotheses.
Results of Structural Model (Direct Relationships).

p < .05; **p < .01; ***p < .001.

Path analysis of structural model.
Table 5 presents the direct associations between the constructs, supporting the first four hypotheses. DHs on social media demonstrated a positive, significant, and direct relationship with the RUSM (β = .200, p < .001), confirming H1, and with SMD (β = .209, p < .001), confirming H2. In addition, the experience of cyberbullying (CYBRBULY) was positively, significantly, and directly associated with the RUSM (β = .065, p < .05), supporting H3, and with SMD (β = .103, p < .001), supporting H4. Furthermore, DHs on social media demonstrated a positive, significant, and direct relationship with OIDA (β = .466, p < .001), which, in turn, was positively, significantly, and directly associated with the RUSM (β = .355, p < .001). This indicates a positive mediating role of OIDA between DHs and the RUSM. Similarly, cyberbullying (CYBRBULY) was positively, significantly, and directly associated with PCs (β = .36, p < .001), and PCs also showed a positive, significant, and direct relationship with SMD (β = .448, p < .001), suggesting a positive mediating role of PCs between cyberbullying (CYBRBULY) and SMD.
The results from the SEM also indicate an indirect effect of DH on the RUSM mediated by OIDA (β = .114, p < .001), which supports our H5a. Furthermore, the significant indirect effect of cyberbullying (CYBRBULY) on SMD, mediated by PC (β = .080, p < .001), confirms our H5b as shown in Table 6.
Specific Indirect Effects.
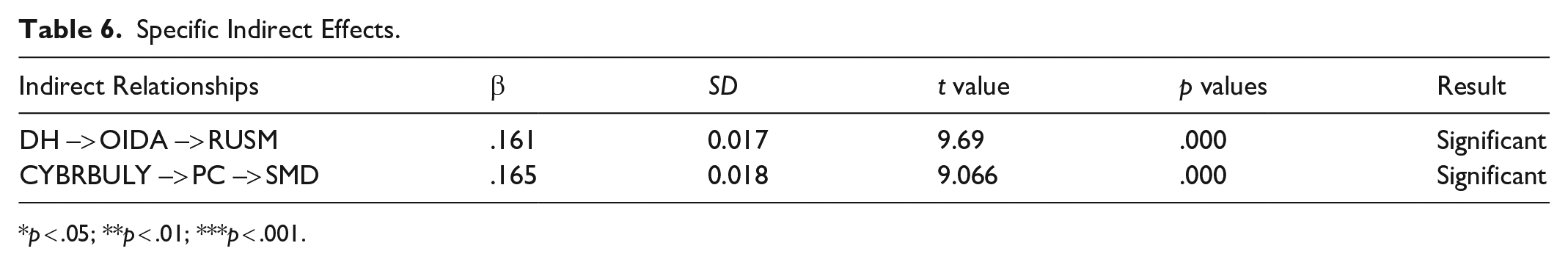
p < .05; **p < .01; ***p < .001.
Discussion and Implications
This study presents several key findings. First, it confirms all six hypotheses. The research model effectively captures the main reasons why social media users in Pakistan adopt privacy safety behaviors, such as regulated social media use and temporary detoxification, in response to negative experiences like data theft and cyberbullying. In addition, we examined the mediating role of privacy-protection motivations, such as OIDA and PCs, to determine if these motivations sufficiently encourage protective behaviors. Our findings indicate that PMT effectively explains the privacy motivations and behaviors of social media users confronted with negative online experiences.
Initially, we examined the direct impact of DH on the adoption of regulated social media use and engagement in SMD. Our findings align with those of H.Chen et al. (2016), who found that experiences of data theft on social media are linked with users adjusting privacy settings, managing access, and employing identity-masking techniques. In addition, research by Wiederhold (2017) indicates that theft and misuse of data on platforms like Facebook can prompt users to consider discontinuing their social media use, although this decision is often challenging. Consequently, our H1 and H2 are confirmed and are consistent with the findings of previous studies.
Second, we examined the direct impact of cyberbullying on the adoption of privacy safety behaviors, specifically RUSM and SMD. Our analysis shows that both relationships are significant, thus supporting H3 and H4. These findings align with previous research, which indicates that RUSM enables users to better understand, control, and update privacy settings on social networks, thereby reducing privacy risks such as cyberbullying (Alqarni & Sampalli, 2016). In addition, experiences of cyberbullying have been found to prompt users to take breaks or detox from social media platforms, such as Twitter, to avoid the negative emotions of embarrassment and depression associated with such abusive behavior (Chatzakou et al., 2019).
H. Chen et al. (2016) emphasized the importance of computer efficacy as a key factor in adopting privacy-protection behaviors on social media. Users with higher levels of computer and social media proficiency are more likely to employ an approach strategy, such as adjusting privacy settings, while those with lower efficacy may opt for an escape strategy, such as SMD, to manage negative online experiences. This relationship suggests that proficiency in computer and social media use significantly impacts how individuals protect their privacy online. Sheldon et al. (2019, pp. 137–149) corroborate this, noting that a deep understanding of digital tools enhances privacy practices. In our research, computer efficacy can be an indirect factor, influencing users to adopt both the approach strategy of regulated social media use and the escape strategy of SMD in response to DHs and cyberbullying incidents.
Employing PMT, we assessed the impact of OIDA and PCs as motivators for users to adopt protective measures. Our analysis supports H5a, demonstrating that awareness of online information disclosure serves as a mediator in the relationship between data breaches and the RUSM. This awareness compels users to implement various privacy measures such as applying privacy and access settings, managing contacts, and masking identities in response to data theft. Such measures are spurred by an increase in perceived severity and vulnerability, which are essential components of PMT (H.Chen et al., 2016). These perceptions are crucial for predicting the application of privacy settings on social media (Bibi et al., 2017). In addition, Alim (2016) found that increased awareness about personal information disclosure on social media leads to more regulated use of these platforms, further affirming the role of information disclosure awareness in motivating privacy-protection behaviors.
In our study, PCs also serve as a mediating factor, motivating users to detox from social media following experiences of cyberbullying, thus confirming H5b. This finding aligns with previous research suggesting that PCs, when viewed through the lens of PMT, significantly influence users’ decisions to adopt self-protective behaviors. Specifically, PCs mediate the relationship between perceived threats on social networks and the likelihood of users engaging in protective actions (Fujs et al., 2018; Mousavi et al., 2020). This highlights the crucial role of PCs in driving the adoption of privacy safety behaviors among social media users.
Our research underscores a significant direct relationship between adverse online experiences, such as DH and cyberbullying, and the adoption of privacy safety behaviors, suggesting a need to revisit the motivational factors outlined by PMT. Notably, the concept of motivation encompasses a broader spectrum of influences, as evidenced by H.Liu and Wang (2023), who found that PCs do not adequately mediate the impact of perceived risks on information-protection behavior. This finding implies that other motivating factors may be at play. Further complicating the landscape, Gerber et al. (2017) highlighted that protection motivation on social media is not only influenced by immediate concerns but also by broader factors such as usage motivation and personality traits. These insights suggest that a more comprehensive exploration of the various motivations that drive privacy-protection behaviors on social media is necessary to fully understand how individuals respond to online risks.
Theoretical Implications
First, our research identifies OIDA as a significant mediator between data theft experiences on social media and regulated social media use. This is the first study to explore this relationship, building on the work of H.Chen et al. (2016), who associated this awareness with privacy behaviors like identity masking and contact management after data theft. Our findings extend these insights by linking awareness directly to regulated social media use, thus enriching the PMT.
This study explores PCs as a motivator for SMD in response to cyberbullying, introducing a novel perspective within the framework of PMT. In contrast, H.Chen et al. (2016) demonstrated that PCs lead social media users to adopt protective behaviors such as adjusting privacy settings and managing contacts to address relational conflicts and data theft. Similarly, Youn (2009) identified PCs as a mediator influencing users to disguise their information and seek advice when facing online threats. In addition, H.-T.Chen and Chen (2015) found that PCs encourage users to limit their profile visibility. This research builds on these findings by examining how PCs drive the behavior of SMD.
In this study, we examined two privacy-protection behaviors influenced by social media users’ computer efficacy. Users with high computer and internet efficacy tend to regulate their social media use, whereas those with low efficacy are more likely to suspend or detox from social media. This approach provides a fresh perspective on social media research through the lens of PMT, highlighting how digital skills impact user responses to negative online experiences.
Practical Implications
The findings of this research offer valuable insights for various stakeholders, with several practical implications. Educators and organizations can develop targeted campaigns and programs to increase awareness of online privacy risks, empowering users to make informed decisions about their digital activities. Social media platforms can use these insights to enhance privacy settings and interface designs, making privacy management more user-friendly. Policymakers can apply the findings to shape regulations that protect user privacy and online safety. In addition, support services and community organizations can tailor interventions to address issues like cyberbullying and DH, considering the psychological drivers behind protective behaviors. By implementing these measures, stakeholders can collaboratively foster a safer and more privacy-conscious digital environment.
Study Limitations and Suggestions
Despite this study’s efforts to enrich the understanding of privacy safety behaviors and motivation of social media users in response to negative online experiences, some limitations need to be noted. First, this study conducted on checking general privacy safety behaviors and motivation of social media users in response to negative online experiences, rather than focusing on specific social media platforms like Facebook, Instagram, or Twitter. However, it is recommended for future researchers to examine individual platforms, as privacy settings, data-sharing policies, and user interactions differ significantly between platforms. For instance, while Instagram prioritizes image-sharing privacy, Facebook may involve more personal data sharing, and Twitter emphasizes public discourse, each presenting unique privacy challenges. Therefore, focusing on specific platforms can provide deeper insights into privacy safety behaviors and motivations.
Second, this study reveals that the direct relationships between data theft, cyberbullying, and privacy safety behaviors—such as RUSM and detoxification—are significant, even without considering the motivating factors of PCs and awareness of online information disclosure. However, when examining these relationships with the mediating effect of privacy safety motivations, they remain significant. This suggests that there may be additional motivating factors influencing these behaviors that future research could explore. Furthermore, researchers could investigate the potential chain mediating effects of PCs and other motivators, along with OIDA. This approach would help identify a broader set of motivations that predict the privacy safety behaviors of social media users.
This study does not specify which age groups or genders are more vulnerable to online privacy threats. Therefore, future research should investigate whether certain demographics, such as males or females, adults or older individuals, are more susceptible to these risks. This direction would help in tailoring interventions and educational programs to the needs of those most at risk.
Conclusion
With the rise in social media users worldwide, including in Pakistan, privacy-related threats have become increasingly common. This research investigates how serious privacy threats, such as DH and cyberbullying, lead users to either regulate their social media use or suspend it altogether. In addition, the study explores the motivational roles of OIDA and PCs in the context of these privacy threats. Specifically, it examines how these factors contribute to the adoption of privacy safety behaviors, such as RUSM and SMD, guided by the principles of PMT.
We empirically validated our proposed research model and hypotheses by analyzing data collected through an online survey of social media users in Pakistan. Our findings show that data theft as a negative online experience encourages users to regulate their social media use or detox from social media. In addition, awareness of online information disclosure acts as a mediator between data theft and the RUSM. Furthermore, cyberbullying is also found to influence the adoption of privacy safety behaviors, such as RUSM and SMD, with PCs mediating the relationship between cyberbullying and these behaviors. A user’s level of computer skills influences their choice of privacy-protection strategies. Users with higher computer skills, including abilities like managing privacy settings, understanding privacy policies, identifying fake profiles, and reporting issues, are more likely to adopt a proactive approach to managing their social media use. On the other hand, users with lower computer skills tend to prefer strategies like temporarily leaving social media, known as SMD, to protect their privacy.
Footnotes
Appendix
Measurement Scale.

| Construct | Items | Source | |
|---|---|---|---|
| Data heist | My personal information has been stolen from social media, either once or multiple times |
|
(Chen et al., 2016; Fire et al., 2014) |
| My social media account has experienced unauthorized access, either once or multiple times |
|
||
| My friends and family have received fake friend requests using my name and profile picture |
|
||
| I have received fake friend requests impersonating my friends, family, or people I know, using their names and pictures |
|
||
| Cyberbullying | I have received one or multiple online threats from someone, in which they’ve threatened to post something that could harm my reputation |
|
(Abaido, 2019; Carter, 2013) |
| Someone has posted harmful and vulgar content about me on social media, potentially damaging my image |
|
||
| A friend or family member who was angry with me harassed me on social media with shameful comments |
|
||
| Someone raised false allegations against me on social media to damage my image |
|
||
| Privacy concern | I am much concerned about the possibility of my pictures and other information being stolen from social media |
|
(Bright et al., 2015; Fogel & Nehmad, 2009) |
| I am greatly concerned about the possibility of my social media account being attacked by hackers |
|
||
| I am deeply concerned about someone using my picture, name, and personal information to create a fake social media account |
|
||
| I am much concerned about the potential for someone to harass or blackmail me on social media |
|
||
| Online information disclosure awareness | I am aware of how to avoid disclosing my online identity |
|
(Chen et al., 2016) |
| I am aware of how much personal information I should disclose on my social media account |
|
||
| I am aware of the preferred photo-posting practice on my social media account, which may involve sharing photos in groups rather than individually |
|
||
| I am aware of what and how much of my routine activities to post on social media, such as dining out with friends, attending academic seminars, or going to the cinema |
|
||
| Regulated use of social media | I prefer to control who can view my social media posts |
|
(Hajli & Lin, 2014) |
| I prefer to control who can view my friends list on social media |
|
||
| I prefer to control who can view my personal information on social media |
|
||
| I prefer to control who can download the pictures I post on social media |
|
||
| Social media detoxification | I have deactivated my social media account at least once or multiple times |
|
(Fan et al., 2021; Fu et al., 2021; Fu & Li, 2020; Gan et al., 2024). |
| Due to privacy concerns on social media, it is preferable to engage in physical socialization rather than relying on social media |
|
||
| Sometimes, suspending or stopping the use of social media is the best way to cope with privacy issues |
|
||
| Sometimes, I believe that not being a social media user would be a better choice |
|
||
Data Availability Statement
The datasets generated and/or analyzed during the current study are available from the corresponding author on reasonable request.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Fundamental Research Funds for the Central Universities in China under Grant No. 2024WKCG008.
