Abstract
The use of location-based real-time dating applications (LBRTDAs) has become commonplace among college-aged persons. With an increase in their use, these applications may serve as vectors for experiencing cybervictimization. Limited research has examined the implications that application usage has on individual experiences with cybervictimization, particularly cyberstalking, cyberharassment, image-based abuse, and identity deception. Using a sample of college students (N = 324; 73% female), and concentrating primarily on Tinder users, this study examines the correlates of experiencing these forms of cybervictimization, concentrating on the influence that application infrastructure and profile features (e.g., Global Positioning System [GPS] functionality) have on the likelihood of cybervictimization. Results indicate inconsistent and largely insignificant effects, suggesting that opting into the use of safety features and protective measures cannot guarantee protection from application-based forms of cybervictimization. As such, policy implications and directions for future research are discussed.
Keywords
Introduction
Ninety-three percent of Americans regularly use the internet for activities such as communicating with family and friends, commerce and banking, and reading the news (Pew Research Center, 2021). Many of these online activities are facilitated by social networking platforms or applications. These types of social communication are some of the most common forms of online engagement, with many individuals accessing these and other mobile applications on smartphones or other smart devices (Anderson, 2019). These mobile applications help facilitate an array of connections, including dating. Roughly 30% of U.S. adults have used a location-based real-time dating application (LBRTDA); the use of these platforms is especially common among young adults, individuals ages 18 to 29 years (Anderson et al., 2020). This is particularly true of college students, who comprise a considerable amount of application users (Beauchamp et al., 2017; Fansher & Eckinger, 2020; Griffin et al., 2018).
While the majority of users have reported positive experiences on these platforms, more than one third of users have noted unwanted or negative interactions with someone they connected with on an LBRTDA (Vogels, 2020). Many of these negative interactions can be considered forms of cybervictimization. These incidents can occur within an LBRTDA or be facilitated by the application itself (Phan et al., 2021). LBRTDAs include several “infrastructural features” that increase exposure to potential offenders, including Global Positioning System (GPS) functionality/distance visibility, the ability to list employment and education affiliations, and share other social media usernames/other forms of communication (Boillot-Fansher, 2017). Applications also provide a platform to showcase or “promote” profile features that depict engagement in risky behaviors, such as drinking or drug use, providing increased opportunities for offenders to access potential victims.
While studies have examined the relationship between profile exposure and experiences of cybervictimization on other platforms (e.g., Facebook; see Henson et al., 2011), less is known about this relationship in the context of LBRTDAs. Specifically, little is known about the potential role that LBRTDAs play in facilitating common forms of cybervictimization, including cyberstalking, cyberharassment, image-based abuse, and identity deception (Choi et al., 2018; Lauckner et al., 2019). Furthermore, research has not explored how infrastructural and profile features of these applications are related to the risk of experiencing cybervictimization.
Better understanding the link between LBRTDA usage and cybervictimization is important, as young adults are increasingly using these applications to facilitate social communications, connections, and interactions; users can use application or profile infrastructures in ways that may increase their risk of victimization. To that end, the purpose of this study is twofold. First, it assesses the prevalence of four forms of cybervictimization (i.e., cyberstalking, cyberharassment, image-based abuse, and identity deception) in relation to the use of LBRTDAs, primarily Tinder, among a predominantly female sample of 324 American college students. Second, it examines the correlates of these experiences, focusing on whether application infrastructures and profile features are associated with the likelihood of experiencing LBRTDA-facilitated cybervictimization.
Literature Review
The Development and Usage of LBRTDAs
Although traditional dating websites (e.g., Match.com) have existed since the mid-1990s, LBRTDAs employ geosocial networking technology that allows users to engage with individuals in various locations at one time and at various hours. Specifically, LBRTDAs contribute to the portability, availability, locatability, and multimediality of connecting with individuals (Ranzini & Lutz, 2017). In addition, while traditional dating websites may have smart device[s] applications available for their services, LBRTDAs are uniquely structured to be more relaxed, having shorter sign-up processes and requiring less effort when creating one’s profile compared with traditional dating websites. LBRTDA users have the option of linking their other social networking sites (SNS), such as Facebook, with their dating profiles, providing additional personal information to potential connections (Duguay, 2016). LBRTDAs, such as Tinder, also use “swipe-match” technology, increasing the fluidity and ease of connectivity between users. Relatedly, features of LBRTDAs may influence the type(s) of relationships they encourage (Yeo & Fung, 2018).
While traditional dating websites often catered to heterosexual persons seeking monogamous relationships, LBRTDAs have long accommodated individuals pursuing relationships outside of these traditions. Indeed, LBRTDAs provided a platform to establish connections individuals may not have the opportunity to do otherwise (Goldenberg, 2019). For example, one of the first LBRTDAs to gain popularity was Grindr. This application launched in 2009 and caters specifically to men who have sex with men (Miles, 2019). The accessibility to others that is offered by LBRTDAs applies to both sexual minorities and heterosexual users. This accessibility has corresponded with a growth in use, particularly among college students (Lundquist & Curington, 2019).
With the current generation of college students accustomed to social interactions facilitated by technology, LBRTDAs are commonly associated with the spontaneity of college “hookup” culture (Allison, 2019; Goluboff, 2016). As Murphy (2018) noted, LBRTDAs also align with the autonomous lifestyles of college students, as they are not required to leave their homes to meet new people, providing ease and comfort for communicating with strangers. This includes the freedom offered by these applications in terms of one’s online self-presentation (e.g., images and location; Sumter et al., 2017; see also Lauckner et al., 2019; Miles, 2019). Relatedly, Fansher and Randa (2019) found that it is also common that users share their personal information with strangers in a short time through these applications. While such disclosure of personal information on social media in general has been found to increase the risk of cybervictimization (e.g., Reyns et al., 2011; Welsh & Lavoie, 2012), limited research has examined how LBRTDAs specifically may facilitate cybervictimization or how application infrastructure and profile features influence that risk (Phan et al., 2021).
Forms of Cybervictimization and Dating Application–Facilitated Victimization
Given the integral role technology plays for college students, it is unsurprising that this population is at an increased risk for many forms of cybervictimization (Reyns et al., 2011; Wright, 2016). Four forms of cybervictimization that are particularly relevant in the context of LBRTDAs are cyberstalking, cyberharassment, image-based abuse, and identity deception. Cyberstalking encompasses a range of unwanted behaviors in which an individual is repeatedly harassed through online and/or in-person communications (Clevenger et al., 2018). Social networking sites and other applications have contributed to the intrusive nature of these communications, providing convenient opportunities and accessibility to personal information, therefore facilitating cyberstalking (Marcum et al., 2017). With regard to LBRTDAs, cyberstalking could occur if an individual was messaged on a dating application and subsequently contacted on another platform after failing to respond. Relatedly, the disclosure of additional personal information by users (such as linked social media accounts or email addresses) has been found to exacerbate this risk (Reyns et al., 2011). For example, platforms such as Instagram and Twitter encourage users to “geo-tag” (i.e., publishing the locations of their content) in their posts, providing their physical location to would-be offenders (Chugh & Guggisberg, 2020). Cyberharassment is frequently discussed in tandem with cyberstalking, as it is a form of cybervictimization where an individual engages “in an act or behavior that torments, annoys, terrorizes, offends, or threatens an individual” (Hazelwood & Koon-Magnin, 2013, p. 157), although instances of harassment do not necessarily have to occur more than once, resulting in isolated incidents. As such, cyberstalking and cyberharassment are considered as related but distinct forms of cybervictimization.
Moreover, the risk for experiencing these forms of cybervictimization may be heightened for LBRTDA users as their physical location is often shared with the applications’ built-in geosocial networking features. A person’s location is updated as they move closer or farther from other respective users. Many users intend to meet offline with individuals in close proximity to them, often with strong expectations of sexual encounters (Murphy, 2018). The display of a user’s information, including proximity and locations, can facilitate victimization by providing offenders with more information to target victims. Furthermore, some LBRTDAs (e.g., Tinder) require users to pay to hide their proximity from other users. This can present a barrier to users, particularly college students, who may lack the financial resources to safeguard their physical location in this manner. Even when users opt to conceal their geo-locations on their account, there may still be security concerns (e.g., hacking) for users (Shetty et al., 2017).
In addition to their present location, users may list their student status (including institution) and workplace on their dating profiles, providing potential offenders with information on places where users frequent. Some of these applications automatically populate this information from a user’s Facebook page if a user registers with their Facebook account. Users can also link their other social media accounts to their dating profile or include this information (e.g., usernames) in their biographical description section. LBRTDA users may do this to legitimize their profile identity to other users. In doing so, however, this behavior provides opportunities for potential offenders to cyberstalk potential victims across multiple platforms.
The use of LBRTDAs also provides opportunities for users to experience image-based abuse, a form of cybervictimization involving the nonconsensual creation or distribution of private sexual images (e.g., “dick pics,” or photos of male genitalia) through online communications (Henry & Powell, 2018; Paasonen et al., 2019). Although some LBRTDAs have protective features (e.g., artificial intelligence [AI] photo-recognition technology) in place to prevent receiving unsolicited sexual images, not all applications use this technology in the same manner (Matney, 2019). Users may also come across these explicit photos while swiping through potential matches. While some LBRTDAs do not allow for the exchange of personal images through their network/private chats, users may be contacted “off-app” on a linked SNS. Offenders may also text these images to users’ cellphones if a user shares that information. Image-based abuse may be particularly pervasive among college students who use LBRTDAs, as the concept of sexually explicit messaging (“sexting”) is prevalent and more acceptable among younger generations (Hertlein & Twist, 2017). The prevalence of sexting might blur the lines between wanted and unwanted sexually explicit communication (Reyns et al., 2013). In addition, while consensual, sexting has been associated with dating victimization (Bianchi et al., 2021).
Powell and colleagues (2020) noted that particular types of image-based abuse may be associated with increased levels of stalking and related forms of victimization. As such, it can be postulated that image-based abuse can co-occur with or be a precursor to other forms of cybervictimization, including identity deception (colloquially known as “catfishing”). Often, users report coming across profiles known as “catfish” (made popular by the Catfish: the TV Show), defined as individuals who take on false identities, using other individuals’ pictures to create a fictional profile (Lauckner et al., 2019; Mosley et al., 2020). Users frequently alter their self-presentation in an effort to look more desirable and be a better dating candidate (Chan, 2018). Self-presentation encompasses an array of features. These include—but are not limited to—gender, height, age, education, employment, income, personal characteristics, and overall appearance. For example, as Guadagno and colleagues (2012) addressed, men tend to be deceitful over characteristics such as income and height, while women are more likely to misrepresent their weight or overall appearance.
Some users reported that “being catfished” was part of the dating application experience (Lauckner et al., 2019). However, experiencing identity deception can cause emotional distress and other psychological harm (Beauchamp et al., 2017; Mosley et al., 2020). Vandeweerd and colleagues (2016) identified deception may lead to other forms of victimization, such as being financially scammed. Cases of identity deception have become so commonplace that a number of jurisdictions have enacted legislation criminalizing the online impersonation of others (Derzakarian, 2017). Identity deception is particularly concerning for college-aged persons, as perpetrators often impersonate young adults (Simmons & Lee, 2020). In addition, the odds of being victimized by identity deception also increase when one considers that an individual can not only be deceived (that is, be “catfished”), but have their photos and identity stolen as well (Paat & Markham, 2021).
Powell and Henry (2017) argued that LBRTDAs should take a more rigorous approach in confirming identities, including requiring background checks. However, those measures are unlikely to be implemented. Indeed, they would be financially burdensome for the LBRTDA companies and likely dissuade potential users from joining applications due to privacy concerns. Furthermore, as the success of modern LBRTDAs relies on the flexibility and relaxed approach to membership, longer, more laborious sign-up processes may deter potential users from registering.
Current Study
Young adults, particularly college students, are increasingly turning to LBRTDAs to facilitate social connections, interactions, and intimate relations. While beneficial for many users, LBRTDAs may also be associated with experiences of cybervictimization. This study seeks to address several gaps in LBRTDA use relating to cybervictimization by asking the following questions:
LBRTDA share inherent risks associated with their usage. While these platforms seem to provide protective features to reduce the risk of exposure and victimization, it is unclear whether or not they influence the risk level of users. As such, it is important to assess risk reduction efforts and interventions that may be useful for lowering the likelihood of individual victimization.
Method
Procedure and Sample
Data used in this study consisted of a sample of undergraduate students (N = 324) enrolled in a number of different social science courses at a large urban university in the Southeastern United States who reported using LBRTDAs. Alternative assignments were provided to individuals who were enrolled in two or more of the participating courses, ensuring that respondents did not take the survey more than once. The sample was part of a larger data set regarding college dating experiences and attitudes (N = 545). Data have been collected through a self-administered web-based survey via Qualtrics for 3 weeks in the spring of 2019. This study was approved by the university’s institutional review board (IRB).
Measures
Dependent Variables
Indicators of cybervictimization (i.e., cyberstalking, cyberharassment, image-based abuse, and identity deception) were composed of modified items from Reyns and colleagues (2012), as adapted by Boillot-Fansher’s (2017) cyberstalking victimization scale, and Pew Research Center’s (2013) “Internet & American Life” Project Survey. Victimization experiences were considered in the 12 months prior to the survey and restricted to those where respondents indicated that the victimization experience specifically occurred on or as a direct result of using an LBRTDA.
Cyberstalking was measured with three indicators. Participants were asked to indicate whether they had (1) “been repeatedly messaged by an individual after not responding,” (2) “been repeatedly messaged after asking someone to stop,” and (3) “been contacted by someone on other social media without giving them my username.” Respondents were coded as affirmative for cyberstalking if they experienced any of the three indicators as a result of using LBRTDAs. Cyberharassment was measured with two indicators, including whether participants had (1) “been spoken to in an insulting or degrading manner” and/or (2) “been threatened physically.”
To measure exposure to image-based abuse, participants were asked to indicate whether they had “been sent an unsolicited, sexually explicit photo(s) through other social media or other forms of messaging” by someone they met on an LBRTDA. Finally, identity deception was measured with two indicators. Participants were asked to indicate whether they had (1) “encountered a profile using my pictures, pretending to be me” and/or (2) “felt like someone had misrepresented themselves in their profile by using another person’s pictures.” Like the aforementioned victimization experiences, participants were coded as affirmative for identity deception if they experienced any form of cyberstalking stemming from the use of dating applications.
Independent Variables
Participants were also asked a series of questions regarding profile exposure, including items regarding application use, system settings, and information sharing. Most items were adapted from Boillot-Fansher (2017). First, respondents were asked the number of people they would “like/swipe right on” on “any given day” with responses including a range of [number of] matches: five or less (34.36%, n = 111), six to 10 (21.60%, n = 70), 11 to 15 (16.67%, n = 54), 16 to 20 (11.42%, n = 37), 21 or more (16.05%, n = 52). Next, GPS functionality was measured by asking, “Is the GPS function active on your profile?” prompting respondents to answer “no” (19.75%), “yes” (80.25%), or “I don’t know.” “I don’t know” responses were recoded as yes, as users have their GPS function on by default (i.e., a user has to manually turn it off to hide their distance). Relatedly, users were asked to indicate their average distance setting in miles for connecting with other users. Based on the distribution, this was dichotomized reflecting those who indicated 1 to 20 miles (58.95%; n = 191) or 21 miles or more (41.05%; n = 133). The number of pictures on one’s profile (“How many pictures do you typically have of yourself on your profile?”) was also reported with users indicating whether they had one to two photos (15.43%, n = 50) or three or more (83.64%, n = 271). Users who reported uploading no photos were omitted from the analyses (0.93%; n = 3), as most applications require users to upload at least one photo.
Participants were also asked about their motivation for using LBRTDAs with the following categories: “hooking up,” “to bring another person into an already existing relationship,” “casual dating,” “in search of friendship,” “a serious relationship,” and/or “other,” in which respondents were required to write in a response, if selected. For this study, respondent intentions were measured dichotomously, with “hooking up” and “casual dating” considered together (79.32%, n = 257), and all additional responses collapsed as “other” (20.68%, n = 67). Regarding information sharing, users were asked whether they had engaged in any of the following: “shared my place of employment on my profile” (20.68%, n = 67), “shared other social media information on my profile” (48.77%, n = 158), “messaged my phone number to someone”(63.58%; n = 206), “described an interest in drug use (e.g., “4/20 friendly”)” (10.22%, n = 33), “uploaded a picture of myself drinking or using drugs” (12.38%, n = 40), and “intentionally uploaded a sexually suggestive photo” (8.95%, n = 29). Table 1 also notes these frequencies.
Descriptive Statistics of LBRTDA Application College Student Users (N = 324).

Note. LBRTDA = location-based real-time dating application; LGBTQ+ = lesbian, gay, bisexual, trans, queer/questioning.
Control Variables and Participant Demographics
While all respondents reported using some type of LBRTDA, the majority of the sample (88.27%, n = 286) reported using Tinder. The sample was also predominantly female (72.53%; n = 235). Four participants identified as gender variant/nonconforming; due to the small sample size and thus limited ability to make valid comparisons between these and the remaining study participants, these individuals were omitted from analyses. In addition, participants indicated their sexual orientation by noting whether they were “straight (heterosexual),” “lesbian,” “gay,” “bisexual,” “pansexual,” “queer,” or “questioning” (LGBTQ). More than three fourths of respondents identified as heterosexual (78.40%); therefore, sexual orientation was dichotomized to reflect heterosexuality, compared with sexual minorities. 1 Participants ranged in age from 18 to 64 years old, with the average respondent being approximately 23 (SD = 5.84) years old. More than two thirds of the sample identified as White, non-Hispanic/non-Latino (73.77%), while approximately 26% identified as Black, Indigenous, or Persons of Color (BIPOC) or Other race. Finally, previous research in the United States has noted an increased risk of victimization among fraternity/sorority students (Lasky et al., 2017; Van Baak & Hayes, 2018), and therefore, respondents were asked to report their fraternity/sorority affiliation, with the majority of respondents (86.73%) indicating that they were not affiliated with these organizations.
Analytic Strategy
Indicators of cybervictimization were regressed on profile features with the demographic characteristics of respondents serving as control variables. Because the dependent variables reflecting victimization were mutually exclusive (i.e., a respondent can indicate more than one form of victimization stemming from LBRTDA usage in the last 12 months), the residuals were correlated. Therefore, a multiequation probit model was used to estimate the likelihood of victimization (Cappellari & Jenkins, 2003). This analytic strategy is an extension of seemingly unrelated regression modeling where the regression models are estimated simultaneously. Missing data were handled via listwise deletion, although made up less than 5%.
Results
Prevalence of Victimization Types
Table 1 provides the summary statistics for the disaggregated counts of types of cybervictimization on or as a direct result of using an LBRTDA. Most users reported using Tinder. More than half of participants reported experiencing cyberstalking (n = 210; 64.81%); this victimization type was the most prevalent among participants. Next, nearly two thirds of the sample reported experiencing cyberharassment (n = 103; 31.79%). Similarly, 34.57% of respondents reported experiencing image-based abuse (n = 112). Finally, approximately 28% of the sample reported experiencing identity deception (n = 91).
Gender Effects
The results of the multiequation probit model are shown in Table 2. To begin, there were consistent significant and negative associations between identifying as male and experiencing three of the four forms of cybervictimization discussed. Specifically, men were less likely to report experiencing cyberstalking (b = −0.73, p < .001), cyberharassment (b = −1.06, p < .001), and image-based abuse (b = −0.85, p < .001) on or as a direct result of using an LBRTDA.
Multiequation Probit Model for Cybervictimization (n = 314).
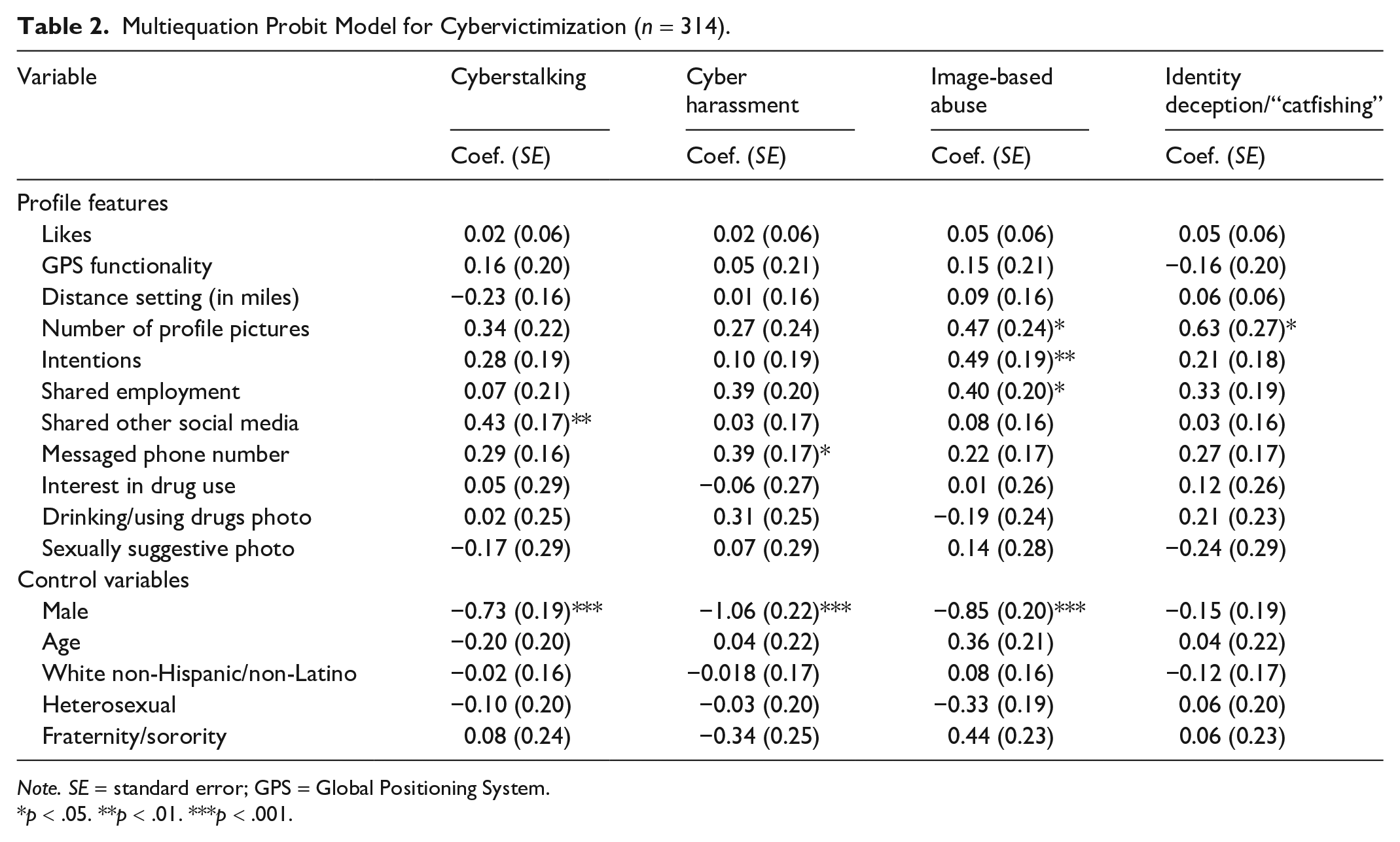
Note. SE = standard error; GPS = Global Positioning System.
p < .05. **p < .01. ***p < .001.
Profile Features
Sharing social media information on one’s dating profile was statistically significant and positively related to cyberstalking (b = 0.43, p < .01). For cyberharassment, sharing one’s phone number with another use was also significant and positively associated with an increase in victimization (b = 0.39, p < .05). For the third victimization type, image-based abuse, the number of profile pictures was statistically significant and positively related to victimization (b = 0.47, p < .05). That is, users who shared more photos were more likely to indicate experiencing image-based abuse. Moreover, shared intentions of hooking up (b = 0.47, p < .01) and shared place of employment (b = 0.40, p < .05) were also positively and significantly associated with experiencing image-based abuse. Finally, the number of photos shared was also statistically significant and positively associated with identity deception. Specifically, users were more likely to experience identity deception if they had more photos on their profile (b = 0.63, p < .05).
Discussion
Better understanding the linkages between LBRTDA usage and cybervictimization experiences is important, given that young adults are increasingly using these applications to facilitate social communications, connections, and interactions. In answering the first research question, this study examined experiences with cybervictimization (i.e., cyberstalking, cyberharassment, image-based abuse, and identity deception) on LBRTDAs using a sample of college students. This study specifically focused on the roles that application infrastructure and profile features have on the likelihood of victimization. With regard to the second research question, application features—including number of profile photos, GPS distance, and sharing of personal information—had inconsistent effects on the likelihood of experiencing various forms of cybervictimization. The factor which most consistently influenced individual risk of cybervictimization was identifying as female. We thus situated our discussion at the nexus of technological infrastructure and culture.
Our findings linking respondent gender with victimization comport with the broader cybervictimization literature (Powell & Henry, 2019). They also align with the gendered nature of LBRTDA offending described in the existing application literature (e.g., Douglass et al., 2018; Pooley & Boxall, 2020; Shaw, 2016). The pervasiveness of cybervictimization experienced by women may be attributable to many factors, but might be best understood through a victim-blaming narrative. That is, women are often considered the responsible parties for their victimization by perpetrators, particularly men, because they “agree to enter these [cyber]spaces in the first place,” presumably aware of the inherent risks of participating in them (Vitis & Gilmour, 2017). Even with the risks associated with the use of technology, women should not need to police their application presence and usage any more than other users; doing so further perpetuates the idea that victims are responsible for their abuse.
Hayes and Dragiewicz (2018) similarly identified the role that sexual entitlement may play in cybervictimization. As women enter cyberspaces, men feel entitled to take advantage of this proximity and create an unequal balance of power more than they would in offline settings. This sexual entitlement may also be misunderstood as acceptable modern-day flirtation, resulting in increased experiences of cybervictimization (Henry & Powell, 2018). Indeed, the association between displayed intentions of hooking up and image-based abuse suggests LBRTDAs may place users at an increased risk of victimization even when users are clear about their intentions on the application.
Our results suggest that LBRTDAs may be especially dangerous environments for women, as users do not have much control over their safety, even when seemingly minimizing exposure on their profiles or engaging in harm reduction strategies online. Theories of target hardening suggest individuals engage in certain self-protective behaviors to avoid victimization (see Tewksbury & Mustaine, 2003), but these behaviors may not necessarily translate well for online communications. As evidenced by the findings of this study, this is particularly true with regard to online sexual violence. Moreover, many of the “self-protective” measures posited by traditional victimization frameworks often place responsibility on the users (Ireland, 2020). They may also not be applicable or suited for addressing online forms of sexual victimization on LBRTDAs, such as making one’s profile private or not communicating with strangers (Reyns et al., 2016). While such suggestions may limit the opportunity for cybervictimization on certain types of social media, they can also increase censorship and impede on an individual’s technological freedoms on dating platforms (Henry & Powell, 2014).
Many LBRTDAs appear to be structured in a way to collectively fail in protecting users from victimization when using their platforms. This consideration is magnified when considering the prevalence of victimization experiences for women and sexual minorities on these platforms. In addition, while these platforms may be policed through standard guidelines and terms of use agreements, and encouraging the reporting of negative experiences, the culture of dating applications discourages reports of victimization, perpetuating the societal narrative of responsibility for one’s own victimization experiences (e.g., Lauckner et al., 2019).
Policy Implications
This study highlights that cybervictimization experiences are prevalent on LBRTDAs, regardless of users enabling protective features on their profile or reducing profile exposure to others. As noted by Pooley and Boxall (2020), very few applications enable safety features that extend beyond standard terms and conditions regarding user communications. For example, Bumble, a women-centric application founded by Whitney Wolfe Herd, provides women more control over interactions than most platforms, including requiring them to message their matches first. The platform also asks users to verify their profiles by uploading a photo in real time, as opposed to one saved on a user’s phone. These features somewhat provide more security for users to avoid cybervictimization experiences like identity deception. Standardizing this and similar safety features across platforms may help lessen instances of cybervictimization. Indeed, much of Bumble’s success is predicated on its empowerment and consideration of users, particularly women (Bennett, 2017). To that end, it is worth noting that the absence of integration of such features may stem from the lack of women and diversity in technology, particularly software/application development (McGee & Bentley, 2017). Given the similarities in dating website/application usage by gender (see Anderson et al., 2020), it is imperative that more women are included in the development and design of LBRTDAs in efforts to lessen the risk of abuse.
Developers could also integrate economics’ nudging theory to encourage positive behaviors and choices when using LBRTDAs, potentially mitigating opportunities of victimization (Bauer & Capron, 2020; Thaler & Sunstein, 2008). Specifically, this places the responsibility on application developers to facilitate safer spaces and potentially lessen instances of cybervictimization while still allowing users to have control of their decisions. For example, LBRTDAs could “nudge” users to disable certain features, such as their GPS visibility, or make this the default setting when an individual begins using an application. Likewise, when users share information across platforms or link to other social media accounts, a verification message asking whether they want to share this information could be provided. Doing so would provide users with a cognitive pause to consider the possible implications of increased exposure or encourage them to engage in other behaviors to moderate risk.
Application developers should also provide streamlined ways of reporting instances of cybervictimization, as these incidents are likely to happen regardless of protective measures taken by the users. Likewise, more effective measures to limit repeat offenders should be employed. While LBRTDAs may delete or freeze the accounts of users who are reported, there are no effective measures in place to prevent new profiles from being created by the same offenders. As a related consideration, LBRTDAs should require user screening questions before allowing individuals to use the application. Currently, applications have no regulations on individuals who can and cannot use the application (Picciani, 2020). Consequently, there is no need to disclose whether or not a user has previously engaged in any form of technology-facilitated sexual violence, which is concerning due to the increased reliance on LBRTDAs for establishing relationships among young adults. Most importantly, these platforms should provide users with resources on how to handle these experiences. While LBRTDAs cannot legally be held accountable for the communications that occur on their platform, users should be assisted in dealing with victimization experiences whether or not they decide to report on the application (Henry & Powell, 2016).
Limitations and Directions for Future Research
These findings and implications notwithstanding, it is important to consider the limitations of this study. First, this study does not control for the type of dating application used. That is, the correlates of using one dating application may differ significantly from using another (e.g., Tinder vs. Plenty of Fish). While the vast majority of the current sample used Tinder, future studies should aim to specify the type of LBRTDA used and the relationship between use and victimization. Relatedly, while we focus on victims’ experiences using LBRTDAs, we cannot assume that these experiences occurred solely on LBRTDAs. As such, victimization experiences such as image-based abuse may have taken place on other platforms and therefore may be related to other variables that this study does not consider, including privacy settings on other social media accounts held by users. Future research should explore the relationship between security and privacy settings across applications and the role of these settings in shaping the likelihood of experiencing cybervictimization.
In addition, although this study contributed to knowledge about the pervasiveness of cybervictimization experiences by exploring less common forms of victimization (i.e., image-based abuse and identity deception), future victimization scholarship should examine the severity and pervasiveness of these forms of victimization through more nuanced measures or qualitative data. Indeed, given the inherent relationship between the aforementioned types of cybervictimization, data should provide more extensive measures of cybervictimization, particularly those that have become more common due to the increased use of technology.
While a college-aged sample is suitable for answering the current research questions, the results may not be generalizable to all LBRTDA users. While the features of the application appear to matter little in the risk of victimization for college students, perhaps they are effective in risk reduction among older adults matching with potential offenders who are not as “tech-savvy.” For example, with regard to some forms of identity deception, younger adults may engage in more “internet sleuthing” before agreeing to directly communicate with someone. This may involve checking a user’s presence on other social media platforms and searching for other online records that verify their profile. Nonetheless, while users may be willing to share other social media account information on their profile to appear more genuine, this may inadvertently increase exposure—and therefore their risk—of cybervictimization. Taken together, future research should consider general risk(s) and risk perceptions of LBRTDA usage across a wide range of demographics, as they may vary across groups.
Finally, this study had too few gender-nonconforming and transgender respondents to include them in analyses. Prior research has found that these individuals are at an increased risk of sexual victimization and that this risk extends to the use of LBRTDAs (e.g., Albury et al., 2020). Future scholarship, including qualitative work, should more thoroughly explore the experiences of sexual minorities with respect to LBRTDA use and specific forms of cybervictimization. Indeed, victimization experiences may have larger implications for these individuals when compared with their cisgender, heterosexual counterparts (Albury et al., 2020; Steinfeld, 2020). Approaching future LBRTDA victimization research through an intersectional lens allows for the critical and necessary examination of the nuances and linkages across different groups of users and their individual experiences.
Conclusion
The increased popularity of LBRTDAs has influenced the landscape of dating and communications, consequently influencing experiences with victimization. This study contributes to existing scholarship by highlighting the importance of developers reconfiguring the infrastructure of LBRTDAs to increase the security and safety of their users. We find inconsistent and largely insignificant effects of infrastructure features on cybervictimization. This suggests that existing features of these applications, that users may modify as preventive measures, may be ineffectual for addressing cybervictimization. LBRTDAs can incorporate more security and safety measures without compromising the appeal of the applications.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
