Abstract

Why We Need Cybersecurity Standards
The word “standard,” as defined by the Merriam-Webster online dictionary, is “something set up and established by authority as a rule for the measure of quantity, weight, extent, value, or quality”. 1 Standards have been created by different organizations for a wide spectrum of purposes, from food safety to energy management. 2 Establishing this type of norm for a certain level of quality is important for both consumers and manufacturers. For technology standards in particular, the National Institute of Standards and Technology (NIST) from the U.S. Department of Commerce states that standards are necessary for the purposes of: (1) interoperability between devices from different manufacturers, (2) ease-of-communication by developing a language for how to evaluate and measure device quality, (3) consumer protection by ensuring that people are able to use any device with the same minimum level of “safety, durability, and market equity,” and ultimately (4) a smoothly operating market. 3
Creating standards for cybersecurity is particularly important as the world becomes increasingly digitally connected. We may take for granted that our personal data is safe from being seen or manipulated by others. However, the level of safety guaranteed in our digital devices is in the hands of the manufacturers. Manufacturers of medical devices are responsible for ensuring that personal health data stored on or transmitted by their devices is not compromised. A person’s health information is data that is not replaceable. If hackers are able to access this information, then there can be concerns with privacy and safety especially if the data’s integrity is breached and altered to where this manipulation could alter a patient’s medical treatment. Most manufacturers of medical devices, however, claim to meet generally required levels of performance or FDA-mandated levels of performance for cybersecurity without necessarily conforming to specific standards.
The Role of Self Attestation
Consumers generally assume that companies will follow existing industrywide standards developed to ensure that their product meets the level of quality that is needed or expected. However, how can there be assurance that a device actually meets the set standards? One level of assurance that can be established at a minimum is self-attestation. The term, self-attestation, means companies are self-reporting their results regarding the quality of their product in accordance with a standard.
A self-attested level of assurance by a manufacturer (known as first party testing) might be considered a “fox in the henhouse” situation and might be questioned. It is possible that a conflict of interest or a lack of independence may exist in some internal assessment. Therefore, it is critical that any internal assessment teams are as independent as possible from the team whose product is under review. However, while self-attestation is the lowest level of assurance, it can be useful to consumers to know that the manufacturer is claiming that the device has met standards, even if the product has been tested by the manufacturer themselves rather than by an outside test lab. This is because when a manufacturer states that their product meets set standards through self-attestation, then they are providing a commitment to consumers that their product can be trusted. A manufacturer who fails to deliver on a claim has greater liability than if the claim had not even been made. If a problem were to arise that contradicted the manufacturer’s claim of meeting set standards, then this could potentially lead to financial liability and negative publicity. Therefore, claiming that the product has met standards, even if only through self-attestation, does carry some weight. While higher levels of assurance are more trustworthy than self-attestation, this level of assurance may be better than no assurance claims at all. Testing by a purchaser of a product (known as second party testing) is rarely practical, unless the purchaser is planning to turn around and resell the products. When a product is tested against a standard by a qualified external lab, then this process is known as third party testing, which compared to first party and second party testing, is generally considered to provide the greatest assurance of performance.
Conformity Assessment
A conformity assessment scheme may be established to outline procedures for ensuring that a product or service meets an established standard. 4 According to NIST, a conformity assessment scheme demonstrates that specified requirements relating to sampling and testing, inspection, certification, and management for a product, process, system, person or body are fulfilled,” 5 Self-attestation may be included in some programs as the lowest level of conformity assessment. The highest level of conformity assessment is a conformity assessment standard that includes an accreditation process for labs that test to that standard. Standardizing the conformity assessment process with a lab accreditation process ensures all labs that conduct testing based on a standard are preforming their testing equally.
Common Criteria for Cybersecurity
An important standard that was created for general cybersecurity is the Common Criteria for Information Technology Security Evaluation (ISO 15408), generally referred to as Common Criteria. This internationally recognized standard provides a common set of requirements for the security functionality of information technology products and for assurance measures applied to these products during a security evaluation. This third-party evaluation process establishes a level of confidence that the security functionality of these products meets the requirements and informs consumers whether these products should meet their security needs. 6
Beyond the need for third-party evaluation, Common Criteria has also established standards for conformity assessment. A test lab must employ staff with adequate knowledge, and experience to be trusted to assess cybersecurity of a device. In order to ensure that test labs meet a high standard for assessing devices, test labs can be accredited by an accrediting body. One of the most important reasons for ensuring that a lab is accredited is to promote consistency between how different test labs are applying the standard. Accreditation might even require that the people testing the product have the same minimum level of training and experience. With the same level of training and experience, testers will be able to apply testing protocols properly and use the appropriate tools for each test.
Common Criteria establishes three concepts for describing the security of a product, including a protection profile (PP), which is a broad set of potential security features that a product could deliver, a security target (ST), which is a set of potential features derived from the PP that a specific product claims to provide, and a target of evaluation (TOE), which is the product being tested. 7 Both STs and PPs must be evaluated in order for a device manufacturer to claim conformity to Common Criteria. 7
Common Criteria presents not only performance requirements, but also assurance requirements (through a conformity assessment protocol by a test lab) that ensure the test lab’s evaluation is thorough and can be trusted. This standard specifically outlines for testing labs: (1) a process to demonstrate their capability and experience, so that the measured performance of the product or service can be trusted, as well as (2) specific steps to conduct the security assurance assessment. 8 Common Criteria also outlines Evaluation of Assurance Levels (EALs), which reflect the trustworthiness that specific security features are actually present, based on the amount and rigor of testing. Three factors determining the level of rigor include the necessary level of experience of the cybersecurity lab staff, the sophistication of testing tools, and the amount of time required to break into a system. 8
The Common Criteria standard is an example of a successful security standard that is internationally accepted because both its mandated performance requirements and formal accreditation process ensure that laboratories and their testers will adequately carry out the testing procedures. Thus, Common Criteria provides multiple layers of assurance that the cybersecurity of devices that meet its specifications can actually be trusted.
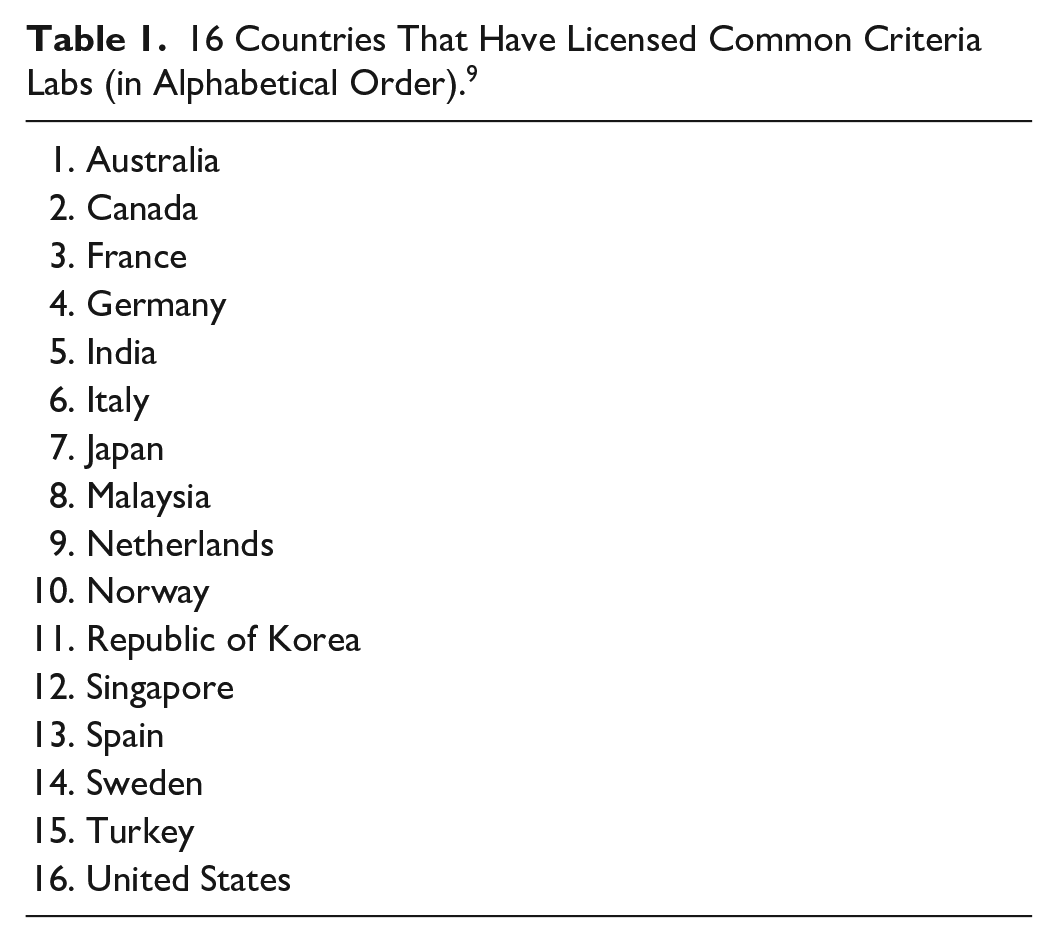
Licensed test labs accredited for the ISO 15408 standard are located in 16 countries (see Table 1). 9 To become an accredited lab for Common Criteria in the United States, a lab must go through an evaluation process by NIST. In the Unites States, the National Information Assurance Program (NIAP) is used for validating NIST-accredited test labs’ evaluations of products undergoing Common Criteria certification, specifically for military software. 10 Common Criteria certified products also include smart card systems and network equipment. 11
16 Countries That Have Licensed Common Criteria Labs (in Alphabetical Order). 9
Standards for Diabetes Devices
We believe that there would be great benefit to increasing the confidence by medical device stakeholders in the security of these devices because a breach of any medical device could possibly cause safety damage as well as a lack of confidence in the entire class of products. Patients, healthcare professionals, payers, and regulators could all have greater confidence in the security of medical devices, including diabetes devices, if manufacturers of these devices were to follow cybersecurity standards through testing and certification by qualified test labs assessing cybersecurity. The lack of cybersecurity conformity assessment in the medical device field is a missed opportunity to improve confidence by these stakeholders in the security and safety of their products. We believe that greater assurance of cybersecurity would be useful for promoting and demonstrating security for various types of wireless connected wearable/carryable/implanted diabetes devices. These connected devices include: (1) blood glucose monitors, (2) continuous glucose monitors, (3) insulin pumps, (4) automated insulin delivery (AID) systems, (5) smart insulin pens, and (6) other sensors for remote monitoring of complications, such as problems with feet, eyes, blood pressure, or weight. We also believe that greater assurance of cybersecurity is needed by hospitals for large devices (such as point-of-care blood glucose monitors that connect with the hospital’s electronic health record, infusion pumps or imaging equipment), which are sometimes used for diabetes patients. In Germany on September 18, 2020 the first case of a patient death due to a hospital cyber-attack was reported. 12 This death followed a ransomware extortion incident that shut down a hospital. A critically ill patient being transported in an ambulance had to be diverted to another hospital, but died en route. This case illustrates the need for strengthened cybersecurity in hospital-based medical devices and hospital networks.
Potential scenarios that highlight the need for cybersecurity for wireless connected wearable/carryable/implanted diabetes devices could consist of a security breach of a connected glucose monitor or insulin delivery device, that could interfere with the confidentiality, integrity, or availability of blood glucose data or insulin dosing data. If a hacker were to alter a report of the glucose concentration or alter an intended dose of insulin, then the patient might not realize that they were headed for a dangerous level of glycemia. Fortunately, there have not been any reports of such incidents occurring, and following prior coordinated disclosures of insulin pump vulnerabilities, manufacturers have proposed remedies to permit continued safe function of these devices,13,14 underscoring the necessity of sound medical device cybersecurity. The United States Food and Drug Administration (FDA) acknowledges this concern by stating, “Cybersecurity is safety.” 15
Benefits of Diabetes Device Cybersecurity Standards That Include Conformity Assessment
We believe that it would be useful to apply the same principles of conformity assessment to medical device and diabetes device cybersecurity standards that are applied to some other types of mission critical standards. Although following a specific cybersecurity standard is not the only way to build cybersecurity into a product to meet regulatory premarket security requirements, it is an efficient method and one which lends itself to being easily documented and understood by patients, healthcare professionals, and regulators. Demonstration of conformity to a standard provides additional reassurance to diabetes device stakeholders, and might also mitigate liability in the case of a breach. 16 In the future, liability insurance companies might choose to preferentially cover medical devices that document meeting a cybersecurity standard over those that do not. Finally, adherence to a standard—especially one embodying conformity assessment—can serve as a product differentiator, to provide a marketing advantage. One study has demonstrated that consumers are willing to pay a premium price for a secure product compared to a similar non-secure product. 17
Currently Available Medical Device and Diabetes Device Cybersecurity Standards
Aside from general software cybersecurity standards (such as Common Criteria), the currently available cybersecurity standards for medical devices includes four standards for medical devices in general and two standards specifically for diabetes devices. It is important for standards to be specific, in order to adequately address unique problems to the field. This outlines the necessity to have cybersecurity standards for medical devices, rather than having manufacturers use more general software cybersecurity standards. The four standards for medical devices in general are: (1) IMDRF/CYBER WG/N60, “Principles and Practices for Medical Device Cybersecurity,” developed by the International Medical Device Regulators Forum (IMDRF) in 2020, 18 (2) the Technical Information Report 57 (TIR57), “Principles for Medical Device Security—Risk Management,” developed by the Association for the Advancement of Medical Instrumentation (AAMI) in 2016, 19 (3) TIR97, “Principles for Medical Device Security—Postmarket risk management for device manufacturers,” developed by the AAMI in 2019, 20 and (4) UL 2900-2-1, “Software Cybersecurity for Network-Connectable Products, Part 2-1: Particular Requirements for Network Connectable Components of Healthcare and Wellness Systems” developed by Underwriters Laboratories (UL) in 2017. 21 The FDA has recognized the TIR57, 22 TIR97, 23 and UL-2900-2-1 24 standards. While these standards capture different important aspects in ensuring cybersecurity of medical devices, they do not outline an accreditation process that would maintain consistent testing to their standards across multiple independent labs. The two standards for diabetes devices were created by Diabetes Technology Society (DTS) do outline an accreditation process that would maintain consistent testing to their standards across multiple independent labs. These cybersecurity standards for connected diabetes devices are: (1) Diabetes Technology Society Cybersecurity Standard for Connected Diabetes Devices (DTSec) 25 developed in 2016 26 and (2) Diabetes Technology Society Mobile Platform Controlling a Diabetes Device Security and Safety Standard (DTMoSt) 27 developed in 2018. 27
IEEE 2621 Standard and Conformity Assessment
DTSec and DTMoSt have not been formally recognized by the FDA, which only recognizes standards from official standards development organizations, and Diabetes Technology Society is not such an organization. These two standards are currently being further developed under a joint effort between two official standards development organizations, the Institute of Electrical and Electronics Engineers (IEEE) Standards Association and UL. 28 This standard will be called IEEE 2621. 29
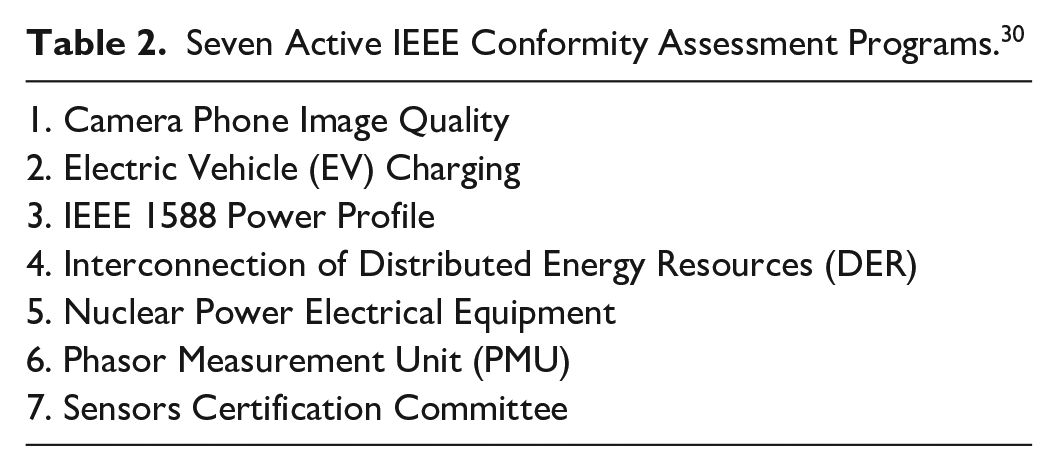
The IEEE Conformity Assessment Program (ICAP) works to develop and implement conformity assessment programs for IEEE standards, and has active programs for seven different standards (see Table 2). 30 DTS is working with IEEE to develop an IEEE-branded conformity assessment scheme for the IEEE 2621 standard, that will ensure appropriate standardized testing by high quality labs. Once IEEE 2621 is officially complete, the conformity assessment program will be launched to help ensure that the diabetes device manufacturers, who choose to seek documentation for cybersecurity in their products, are adhering to and are recognized for adhering to IEEE 2621.
Seven Active IEEE Conformity Assessment Programs. 30
Conformity Assessment for Non-Diabetes Wireless Medical Devices
After a conformity assessment program is developed for IEEE 2621, this approach to medical device cybersecurity might serve as a model for stakeholder development of conformity assessment standards for other non-diabetes wireless medical devices. Cybersecurity is also important for non-diabetes wireless medical devices. For example, the FDA has cleared electrocardiogram apps on watches, which include irregular rhythm notification feature that can detect atrial fibrillation, sinus rhythm, and/or a rapid heart rate.31-34 If the cybersecurity of these applications was compromised, then mission critical notifications for abnormal heart rhythm might not be displayed. Digital health devices that provide physiologic data or deliver electrical cardiovascular, neurologic, or gastrointestinal stimulation must be built to perform securely, and standards are a widely used engineering tool to enhance performance. We expect that cybersecurity standards with conformity assessment for non-diabetes connected devices will also be developed in the near future.
FDA and Conformity Assessment
In 2020, the FDA announced support for medical device conformity assessment to selected standards, (although not specifically for medical device cybersecurity), by launching their Pilot Accreditation Scheme for Conformity Assessment (ASCA) Program. 35 The FDA has released a draft guidance for this project, which currently only applies to (1) basic safety and essential performance standards and (2) biocompatibility testing of medical devices. This pilot program involves several layers of accreditation for medical device conformity assessment. The FDA will use the ASCA program to recognize certain accreditation programs. These accreditation programs can accredit certifying test labs, allowing the test labs to then apply to FDA for ASCA accreditation. 36 The accreditation bodies in turn must be accredited by the American National Standards Institute (ANSI) 37 to perform accreditation of certifying labs and to create standards. 36 Once a test lab that is certified by an ASCA member accreditation body applies to FDA and becomes ASCA-recognized, they can begin testing medical devices using FDA-recognized consensus standards. 36 Perhaps a medical device cybersecurity standard, which incorporates conformity assessment could one day be added to this program or to a spinoff program.
The Future of Diabetes Device Cybersecurity
Conformity assessment to standards exists in many other industries outside of medical device cybersecurity. 38 As the IEEE 2621 standard and its associated conformity assessment program for cybersecurity move forward in development, we expect that many manufacturers of diabetes devices will partake of this standard and demonstration conformity. We also expect that greater use of conformity assessment cybersecurity standards for diabetes devices will stimulate interest in the use of such standards by manufacturers of medical devices for other diseases, which will improve the safety of the increasingly connected healthcare ecosystem.
Footnotes
Acknowledgements
We thank Annamarie Sucher-Jones for her expert editorial assistance.
Abbreviations
AAMI, Association for the Advancement of Medical Instrumentation; ANSI, American National Standards Institute; ASCA, Accreditation Scheme for Conformity Assessment; DTMoSt, Diabetes Technology Society Mobile Platform Controlling a Diabetes Device Security and Safety Standard; DTS, Diabetes Technology Society; DTSec, Diabetes Technology Society Cybersecurity Standard for Connected Diabetes Devices; EAL, evaluation of assurance levels; FDA, Food and Drug Administration; IEEE, Institute of Electrical and Electronics Engineers; ILAC, International Laboratory Accreditation Cooperation; IMDRF, International Medical Device Regulators Forum; NIAP, National Information Assurance Program; NIST, National Institute of Standards and Technology; PP, protection profile; ST, security target; TIR, technical information report; TOE, target of evaluation; UL, Underwriters Laboratories.
Declaration of Conflicting Interests
The author(s) declared the following potential conflicts of interest with respect to the research, authorship, and/or publication of this article: TS and JYZ have nothing to disclose. JD works for Intertek, a company involved with security certifications and testing, and also participates in committees that are involved in the development of both UL 2900 and IEC 62443. DCK is a consultant for EOFlow, Fractyl, Lifecare, Novo, Roche Diagnostics, Samsung, and Thirdwayv.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
