Abstract
Internet of Things (IoT) enabled wireless body area network (WBAN) is a novel technology that combines medical, wireless, and non-medical devices for healthcare management applications. Indoor healthcare institutions, such as hospitals, may employ IoT devices to manage medical equipment, maintain inventory, and monitor patients. In addition to monitoring temperature, humidity, and air quality, IoT sensors may help prevent the spread of sickness. The data generated by small sensor devices need strong security methods for secure transmission over a public network. Security of the data sent from source to destination is handled by transport layer security (TLS) protocol and prevent message loss or reordering. The most difficult component of TLS is determining how to handle reliability. Low-power wireless networks employ the Datagram Transport Layer Security (DTLS) protocol to solve this problem. But if the Server is exposed to a malicious attack (i.e., flooded with ClientHello messages, the DTLS protocol may no longer serve the purpose) as it may lead to Denial-of-Service (DoS). The paper proposes an intelligent gateway-based verification and approval system to protect health data from IoT wearable devices, a key worldwide data security risk. Paper used Contiki Network Simulator for designing an advanced smart gateway-based constrained application Improved DTLS (CoAP I-DTLS) security protocol. To assess the effectiveness of the proposed work, the packet loss ratio is computed for the CoAP, CoAP-DTLS, and CoAP I-DTLS protocols. To assess the effectiveness of the improved CoAP I-DTLS, calculations are also made for data transfer and handshake time. Paper will also look at ways to increase security by integrating the CoAP I-DTLS protocol with the Secure Hash Algorithm (SHA-256) and utilizing Certificate Authority (CA) improvements. Evaluation parameters such as Packet loss ratio, Data transmission time, and Energy consumption average are considered and detailed simulation results have been presented.
Keywords
Introduction
A vital aspect of living is access to healthcare. Regretfully, the increasing age of the population and the corresponding increase in chronic illnesses are putting a great deal of stress on contemporary healthcare systems, since hospital beds, physicians, and nurses are in high demand. It appears that a solution is needed to lessen the burden on healthcare systems while still offering at-risk individuals high-quality care. The potential of Internet of Things (IoT) technology to relieve the burden on healthcare systems brought on by an aging population and an increase in chronic sickness has garnered significant attention in recent years. Since standardization is a major barrier to advancement in this field, this article suggests a standard model that will be used in IoT healthcare systems in the future. A big transition is necessary in healthcare to more scalable and cost-effective alternatives. The solutions to these issues involve redesigning healthcare systems to actively manage wellness rather than illness and putting an emphasis on early disease identification and prevention. 1 In order to deal with the rising costs of healthcare, the Internet of Things in healthcare applications has drawn the attention of numerous researchers in recent years.
Collecting physiological parameters like the heartbeat and body temperature is a crucial duty for such a system. One of the best technologies for creating discrete, scalable, and reliable IoT healthcare systems is WBAN. Sensor nodes that are structured make up a WBAN. 2 These sensors can be inserted beneath the skin, on the body, or in clothing. There is a wireless interface on the sensors. Body sensors gather data about the environment (the human body), which is then correlated for monitoring and/or actuation purposes, similarly to conventional wireless sensor networks. IoT advances are expanding quickly, having turned into an achievement progression in the computerized medical services area. 3 As indicated by, 4 today 50 million clinical gadgets are being used, and it is expected that by 2025 there will be more than 161 million of them associated around the world. This enormous extension of the IoT clinical gadgets market is because of the development of high-velocity organizing advances, and the expanding reception of wearable gadgets, cell phones, and other versatile stages in medical services. Notwithstanding, these gadgets are regularly portrayed by a serious level of heterogeneity, creating tremendous measures of wellbeing and wellness information in heterogeneous configurations. 5
These days, scalability is a topic that must be covered while talking about IoT healthcare systems. Vernon Turner, senior vice president of enterprise systems at IDC, claims to know. By 2025, there will be 152,000 smart gadgets online per minute. 6 IoT solutions must expand significantly in order to accommodate this enormous number of linked devices. To put it another way, scalability is a crucial factor to consider when selecting an IoT solution supplier. Scalability guarantees that, as your company expands, your deployment will continue to be viable and secure. When growing IoT systems, there are a few basic obstacles to overcome. In addition to ensuring that your IoT solution can expand without problems, you also need to think about connection, device management, security, necessary certifications, and the availability of IoT devices. Data security and privacy are the primary concerns when deploying IoT in logistics and supply chains since many IoT device makers disregard even the most basic security standards for IoT systems. 7
Many medical care associations bargain regularly with challenges in removing information from various types of clinical gadgets, influencing both patient consideration and clinical exploration.
8
By and by, this load of medical services associations is confronting numerous troubles in dealing with this load of colossal measures of information, mostly inadequate with regards to an incorporated information trade framework.
9
To trade in-formation with however many associations as would be prudent, interoperability is the main way for allowing frameworks to connect,
10
being considered as a need in the electronic medical care frameworks for settling in-formation heterogeneity issues. Major applications of IoT in healthcare are shown in Figure 1. Applications areas of internet of things in healthcare domain.
A key is a series of pieces that are utilized by the encoding calculation or calculations during the method involved with encoding and unscrambling the information. 11 A cryptographic key resembles a key for a lock; just with the right key would you be able to open the lock. 2 When sending scrambled information, TLS regularly utilizes a cryptographic hash capacity to guarantee information honesty. 12 The hash work keeps Charlie from altering information that Alice ships off Bob. A cryptographic hash is like a checksum. The smallest change to the message normally rolls out an enormous improvement in the subsequent hash. A cryptographic key doesn’t require cryptographic hash work. 13
Interoperability in the healthcare industry refers to an electronic health system’s capacity to interact with other computers or software systems from different hospitals or healthcare providers in an easy and smooth manner. It permits the sharing and openness of health information across pharmacies, laboratories, clinics, hospitals, and hospices, going beyond simple interconnection. A strategic strategy with detailed steps is needed to ensure that healthcare information systems can cooperate effectively, improve data interchange, and ultimately improve patient care. WBANs use wireless sensor nodes attached to a human body to track various physiological parameters like BP, temperature and sugar levels. This is being done to make it easier for patients to have remote health monitoring. Both implanted and wearable versions of these WBANs are available. WBANs aim to provide medical personnel with insights into a patient’s health status by strategically positioning sensors on the body to transfer bodily information to data servers, ultimately aiming to protect human well-being. 14
These technologies greatly benefit both medical boards and individuals during emergencies by providing functions such as monitoring, dispensing health information, enhancing data administration, managing home appliances, and transferring information. In the context of WBANs, this study paper attempts to examine different options that might extend the network’s lifespan, reduce node energy consumption, and increase security and safety at the same time. 15 To put it another way, the paragraph underlines the significance of addressing both security and energy consumption concerns. 16 WBAN is a confined network that operates within, on, or around the human body. Sensor advancements, Micro-Electro-Mechanical Systems (MEMS), and wireless communication have all contributed significantly to WBAN advances. WBANs have proven invaluable in healthcare monitoring, medical, sports, and multimedia communication. However, the small size of the sensors and actuators necessitates significant energy consumption levels. WBANs provide the secure storage and delivery of patient information to healthcare providers while reducing the risk of data loss.17,18
Objectives, motivation, and contributions
The primary objective of paper is to strengthen the DTLS protocol’s defense against Denial-of-service attacks. Put the suggested technique into reality using the Cooja simulator for Contiki OS to demonstrate its practicality. The recommended DTLS’s performance was assessed and contrasted with that of the conventional DTLS protocol in terms of DTLS Handshake Run-Time and energy consumption. To assess the success of the proposed task, the packet loss ratio is computed for CoAP, CoAP-DTLS, and CoAP I-DTLS. Data transit and handshake timings are also monitored to gauge how well the upgraded DTLS performs. The success of IoT devices in providing low power consumption, secure information, and cost-effective solutions to IoT networks for smart healthcare systems in emergency scenarios provided the inspiration for this contribution. Important contributions made by this article are: a. It discusses the latest papers investigating the intermingling of smart healthcare with various IoT applications. b. CoAP, CoAP-DTLS, and CoAP I-DTLS have been used for performance comparison and analysis. c. To increase security, it suggests using a CoAP I-DTLS smart gateway system. d. Evaluation parameters such as Packet loss ratio, Data transmission time, and Energy consumption average are considered and detailed simulation results have been presented. e. To integrate the CoAP I-DTLS protocol with SHA-256 using optimizations from the CA to improve security.
The rest of the paper is organized as follows: Section 1 discusses how IoT works in the healthcare sector. In Section 2, a review of the literature is presented, and in Section 3, IoT healthcare architecture is covered. The suggested strategy or solution is presented in Section 4, and the findings and analysis are expanded upon in Section 5. Section 6 concludes the paper.
Literature review
Many researchers have developed IoT-enabled healthcare solutions. The main problem with IoT-based healthcare research is that it has been applied in a very limited context to connect a particular group of medical devices, like sensors and wearables, while ignoring many non-medical items, like those found in the transportation and security sectors, which are undoubtedly used in healthcare organizations. 19 Even if some crucial healthcare devices might not be able to connect to the Internet, communication between healthcare system nodes is exclusively relied on the Internet. It’s possible that internet signals are unavailable in many isolated areas. The monitoring, security, and hardware design industries account for the majority of related work. 20
Since an IoT-based wellness system gathers all of the weak person’s information and transmits it to the network, which is accessible both locally and worldwide, a framework was created to address the main problems with the structured engineering of the system. 21 It attempted to use the Contiki continuing working framework in this paradigm. The model included three levels, each of which had a certain capacity; in any case, the system came up short on the security foundation to consolidate the current managerial undertakings. The framework upholds a proficient person to examine the wellbeing data, even in the absence of the patient. 22 A few arrangements offer key situations for e-wellbeing applications. All things considered, this examination has given a vigorous strategy to consolidate undisclosed sharing plans and associating personalities to shape gatherings of people of patients experiencing a comparable infection. 23
The gatherings are isolated into independent blocks, and the block division helps the square chief gather point-by-point data from patients’ cell phones. Albeit the framework does not answer noxious trespassers, these intruders are not malignantly influencing the patients; all things considered, it helps the patients in antagonistic circumstances by sharing some delicate data about their security. 24 WBAN frameworks currently have advancements defeating limitations like force, handling, versatility, overseeing, and figuring by taking on distributed computing innovation. The fusion of WBANs with distributed systems upholds the medical services climate through continuous patient following and early infection recognition. 25
Notwithstanding, this needs standard design, strategy consistency, regular information assortment, patient conduct on the board, medicinally coded passwords, information sharing, information exposure, information for the executives, and different information associations. 26 Reliable information correspondence assumes a fundamental part in IoT for solid information combination, information mining, setting mindful-based administrations, and client protection. 27 A method of talking about these worries is to hypothetically virtualize the IoT climate across the cloud and afterward interface every gadget with at least one cloud specialist. 28 To do this, an algorithm known as CoTAG (Cloud of Things Agent Grouping algorithm) was developed to group agents based on information about their dependability and reputation gathered by them. To test the efficiency and usefulness of this method, certain experiments were conducted in a simulated environment. 29
In Ref. 30, two important characteristics are examined for the optimum next hop selection while routing medical data packets to the BS. Each on-body sensor has its own link quality and energy usage rate determined. The next hop is a sensor with good connection quality and residual energy. The limitations of this technique include restricted criteria for determining the next hop and a lack of suitability for transmitting sensitive data. An improved health monitoring mechanism was implemented in Ref. 31. This work includes cluster members, cluster chiefs, and core networks. In this study, the cluster head is selected by introducing three optimization algorithms: ant colony optimization, multi-objective particle swarm optimization, and the complete learning particle algorithm. The chosen cluster head serves as a link between the core network and the clusters. This work uses a cluster head as a gateway between the core network and members in clusters, which influences the QoS limitations in terms of latency and throughput.
A secure healthcare monitoring strategy 32 is used to monitor and operate the smart healthcare system. To create a safe technique, the authors combined two AI algorithms: a fuzzy system and neural network classifiers. It determines the data’s priority level depending on the information obtained from the sensor. The GSM module sends sensor data obtained from the patient’s body to the Azure IoT hub. Ref. 33 presents a safe certificateless biometric authentication method for WBAN that includes group key management. However, the coordinator node is critical in gathering medical data since it serves as the personal controller for each WBAN. The biometric component utilized for authentication is electrocardiogram (ECG) recordings. Then, group key management is carried out for all verified sensor nodes in the WBAN. The lack of security and privacy caused by ECC and the one-way hash function make it unsuitable for resource-constrained IoT devices.
Ref. 34 presents a two-level lightweight technique for identifying anomaly data from huge sensor readings. First, the game theory technique is used to identify the spatial correlation of sensor data and the dynamic changes in the WBAN. Second, the Mahalanobis distance is shown in the local processing unit (LPU), which provides a global perspective on the multivariate analysis. Overall confidence in sensors is quite low, and defect detection consumes more energy.
The authors of 35 proposed a secure architecture for WBAN-IoT in healthcare systems. This work employs five layers, namely, the collection of the data layer from the WBAN sensors to the gateway agent, the second layer is responsible for data routing to the local gateway server from the gateway agent, the third layer is responsible for data routing to the distant server, and the fourth layer is responsible for data routing to the fog layer, where controllers are deployed to provide data security and classify the data as critical and noncritical. Finally, all data is kept in a private cloud. This work secures the data in the fog layer; nevertheless, the authenticity of the users was not addressed, resulting in security issues and numerous assaults in the networks. The authors of 36 demonstrated a WBAN design with dual sink nodes. Clusters were established based on LoS and NLoS, followed by the placement of two sinks. The primary goal of this article was to reduce the energy usage of the network. After the data is sensed, essential data is transmitted immediately to the sink, while periodic data is routed to the subsequent forwarders. All sensors put on a patient are given equal time periods, which must be slotted based on the node priority. The intermediary cooperates with the client from one viewpoint and with the administrations on the other. 37
Data security, pricing, memory, scalability, trust, and openness amongst platforms are all concerns that the smart health architecture must address. 38 Since user identification is uncertain in the open internet environment, it is essential to manage data integrity and privacy. An assembly of electronic medical devices and software that can enhance patient care is known as the Internet of Medical Things (IoMT). 39 The project’s objective is to make remote patient data collection utilizing the CoAP more secure. Different techniques may be used to protect these sensor networks. For communication between multiple IoMT devices and a remote server, the secure CoAP is compatible with the DTLS protocol for establishing a secure session utilizing current techniques like lightweight establishment of secure session. However, there are concerns with key control, session establishment, and multicast message exchange with the DTLS layer of CoAP. These networking protocols are very vulnerable to intrusion. The authors argue that the distributed approach, in which IoT devices employ powerful gateways attached to them, may not be sufficient, and that the controller’s access control decisions make the security of CoAP messages more efficient and can help prevent DDoS attacks. Subsequently, auhos implemented a software-defined networking scheme to authorize the messages over the CoAP protocol. 40
Many studies have been done to find solutions to these security problems in various IoT sectors. Using two popular IoT protocols, CoAP and MQTTT, his paper offers a security architecture for real-time health monitoring systems that ensures the privacy, accuracy, and reliability of data. As sensor data is continuously communicated through the layers, this security framework uses HTTPs to shield it from security issues. As a result, it offers an extremely low-risk defense against the breach. 41 Numerous studies evaluate the CoAP protocol’s performance and security on the commonly used Raspberry Pi 4 as an Internet of Things endpoint. The research used strict performance criteria, such as CPU, memory, and latency, in conjunction with a comprehensive security analysis that concentrated on vulnerabilities at the network level. Theoretical and practical methods are employed to arrive at conclusions.
The study’s conclusions shed light on whether CoAP is appropriate for Internet of Things installations on Raspberry Pi 4s and make suggestions for improving security and functionality. 42 The careful examination of putting CoAP into practice revealed that, while employing several threads to move data via sockets can even boost the total throughput of some known systems, it also limits the potential of others, as demonstrated by the Micro benchmarks. The server may select the right number of thread-lines for a fixed platform by wrapping the receiving and sending operations into their own distinct stage, all without significantly influencing the other stages. Moreover, it operates on top of the UDP or DTLS protocols when security mode is enabled, and it employs a brand-new, ultra-sleek binary number format. It even permits multicasting connectivity and communication.
Replica flow identification and dependable digital message delivery are provided by the sub-layer of the digital messaging level. 43 The Datagram Transport Layer Security (DTLS) protocol is used to secure CoAP communication. The DTLS implements a handshake procedure to create a secure connection and negotiate the same cipher suites before initiating a secure transmission. On the other hand, DTLS is susceptible to DoS assaults. The DTLS cookie exchange procedure was unable to manage the DoS assaults during the handshake mechanism. This study proposed an improved DTLS Handshake authentication technique that lessens the vulnerability to denial-of-service attacks. The outcomes were assessed in relation to elapsed time, energy efficiency, and handshake time. In order to simulate the proposed mechanism, simulation is performed using the Cooja simulator and Contiki-NG operating system.
The literature review covers relevant work based on factors such as efficiency, environmental surveillance, secure transmission, speed, and service quality (QoS). All of the solutions discussed above are designed with certain features in mind. As a result, this article focuses on the CoAP I-DTLS protocol for smart healthcare, which will provide the greatest security, less packet loss ratio and less energy consumption.
Proposed architecture
The upgraded smart gateway-based CoAP I-DTLS is shown in Figure 2. The suggested approach is expanded with the use of typical Datagram TLS. Authentication and authorization are often initiated between the client and server. However, it is possible that an attacker or malicious user will send a number client greeting message in order to compromise the server and get access to important health data. To address this issue, a variety of smart gateways are employed in improved CoAP I-DTLS to establish a connection between the client and server. Traditional CoAP I-DTLS is done between the client and gateway rather than the client and server. After successful login and authorization, a session update is utilized to connect to Gateway. This suggested work focuses on preserving ongoing monitoring of an individual’s physiological circumstances, such as healthcare data on heart rate, perspiration, ECG, breathing rate, skin temperature, blood pressure, and heart sound. The IoT wearable devices in this architecture continuously provide clinical data to doctors. When physiological indicators such as heart rate, ECG, respiration rate, perspiration, skin temperature, blood pressure, and heart sound exceed normal levels, IoT devices transmit a clinically relevant alarm message to other caregivers and doctors. Architecture for health care using the internet of things.
WBAN innovation has been progressively utilized in medical care. Various clinical gadgets are utilized or embedded and coordinated into the WBAN to screen patient wellbeing and treat patients with robotized treatments, and that’s just the beginning. These frameworks should ensure information during assortment, transmission, preparing, and putting away]. A WBAN gadget is comprised of keen, low-controlled sensor hubs. WBAN is a remote organization made out of associated sensors equipped for ascertaining and assembling information on a client’s wellbeing circumstance. The sensors can be worn on various parts of the body and held beneath the skin by the patients. 44 Sensors placed in distant body region organizations can monitor a patient’s mental state, and the data gathered by these sensors is subsequently communicated to doctors and medical clinics. 45 The interchange of health-related data between human body sensors and the medical services monitoring system must be encoded for the patient’s vital data to remain safe and private while being transmitted over the network.
Sensors collect data from the environment and then transmit it to a company or the cloud, where it is analyzed and important decisions are made. In the field of medical services, even the smallest advancement in a patient’s data might result in passing or real outcomes. Actual security and virtual security are two more comprehensive divisions of security. Real IoT security controls cutting-edge technology like equipment and sensor devices. It is interesting how virtual security controls a person’s virtual adversary across a wired or remote connection. It is challenging to adjust to the second type of safety because attackers or sniffers seek to modify the information while they are sitting on the communication channel. Due to the identical functionality of all Internet-connected devices, it is crucial to boost system security and offer end-to-end protection, whether this is accomplished by installing sensors at entryways, opening doors to the cloud, or tying the cloud to healthcare providers. Electrocardiogram (ECG) of a wild-type (WT) man derived from DII, displaying measurements of wave amplitudes and durations transferred to WBAN cloud.
IsoDAM8 amplifiers from WPI, Aston, UK, were used to amplify DII derivation recordings with a bandwidth of 1–500 Hz, and a Gould oscilloscope (20 MHz, model 1421) was used to continually examine the results. 46 Both patients and medical professionals greatly benefit from WBAN. This network may be used to monitor the patient’s condition remotely. Each node in a WBAN is independent and equipped to find an appropriate path for data transmission at a distant site. The WBAN node may link to the internet for data transfer. The healthcare sector is becoming more effective and technologically sophisticated thanks to the usage of information technology. WBAN was developed with consideration for medical systems and emergency situations. The network’s small sensor nodes in these situations gather crucial data from the body and transmit it to the hospital’s medical server. A doctor or medical professional at the hospital then examines this material to determine the diagnosis. Communication in the WBAN is secure because this network employs physiological values (PVs), which are private pieces of human data.47–52
Methodology
Contiki is a low-power operating system for the Internet of Things. Cooja is a knockoff of a Contiki firm. Contiki is a memory-required, well-structured operating platform for low-power distant Internet of Things clients. Road lighting systems, delicate structural sound control, radiation monitoring, and warnings all make use of Contiki. Additionally, a simulation environment may be used to construct the remainder of the framework in the future. CoAP I-DTLS is a protocol designed for usage by IoT nodes in resource-constrained internet networks. CoAP is designed to automatically transition to HTTP for ease network integration while maintaining particular characteristics such as multicasting, minimal overhead, and usability CoAP I-DTLS communicates in two ways: requests and answers, using a basic binary base header format. Options in an appropriate Type-Length-Value format can be sent to the base header. CoAP I-DTLS is designed to be coupled to UDP and, optionally, DTLS, ensuring a high level of communication security. Now the simulation begins, and ping may be conducted in a fresh terminal for each node address in the network.
Simulation Contiki settings.


Proposed simulation scenario in Contiki Cooja.
Power tracing of Tx and Rx anteena.

The basic CoAP I-DTLS features include a Real-Time Publishing Subscription (RTPS) service. The CoAP I-DTLS architecture is decentralized to offer a high degree of stability and low-latency data access for essential IoT applications. The RTPS protocol employs discovery module data readers, data authors, and themes to reveal preconfigured QoS and security protocols, as well as current domain participant information. A domain member is newly created. Definitions can also be omitted when network or system services are restricted from exploration announcements (see Figure 4). CoAP I-DTLS handshaking real-time publishing subscription.
Length of bit size in SHA-1 is 160 bit and in SHA-256-bit size is 256. Because of its smaller bit size, SHA1 is more vulnerable to attacks and SHA1 has been deprecated due to security flaws. SHA256, which is more secure and reliable, uses a Public Key Infrastructure (PKI) where X.509 v3 certificates, signed by a trustworthy shared Certificate Authority (CA), are authenticated by communicating parties. DTLS uses approvals and governance manuals defining the right of access within the entire Domain to specific themes and general security policies. Thus, the IoT technology’s SHA-256 Cryptographic Hash Algorithm generates hashes for secure access, which are primarily used for verifying data and message integrity during transactions, session time, data identification, and password verification.
A Sleeping End Point (SEP) is a special form of the system allowed by CoAP I-DTLS that spends a significant portion of its lifespan disconnected from the network, largely to conserve energy, or simply because it does not store the energy needed for its service. Nonetheless, in the same restricted RESTfull environment, it owns and hosts a collection of services and wants to make them accessible to the other participants. In this respect, the processes that allow it to operate within its limitations must be built and enforced, and its services must be accessible as if it were an ordinary, always linked, CoAP I-DTLS server. The Central Smart Gateway (SG) is the second related CoAP I-DTLS mechanism. Mirror servers can often be used on behalf of mobile devices for mirror services, which, due to their flexibility, often alter their Internet endpoint. Figure 5 demonstrates the configuration of a mirror server. SEP will start by registering it’s to be mirrored resources with the mirror server via a POST request. From then on, sleeping endpoints will serve as clients of the CoAP I-DTLS. They upgrade their services to the mirror server via CoAP I-DTLS PUT requests and can request updates to the mirror server via CoAP I-DTLS POST requests. CoAP I-DTLS mirror server: clients and G.
Data aggregation methods at border routers have a significant optimization goal of reducing energy consumption, which may be accomplished by reducing the mandatory communication burden of routing. Applying data aggregation is an effective technique to boost the energy efficiency of smart healthcare networks as both the number of IoT sensor devices and the volume of transmitted data grow.
53
Using a mathematical model, consider how information is obtained in the system here in line with the guiding convention. Reinforcement Signal (RS) is the total number of data packets received at border router (node j) throughout time t.


For the processing of data from many network sources, data aggregation is a crucial component of wireless routing. It gathers data from the sensor, reducing the amount of delivered data and removing data redundancy. As a result, it preserves the IoT sensor nodes’ strength.
Contiki cooja tool activates the shrewdness of the energy utilization with data transmission for packet loss calculation throughout the reception, the transmission, the CPU cycles, and in the low power mode, based on time spent in the modes 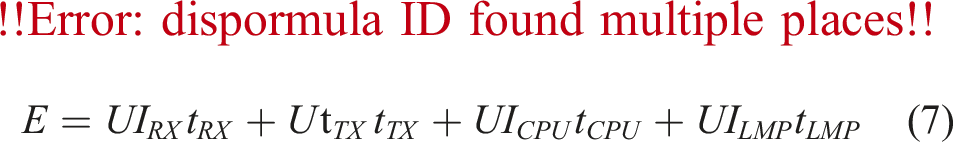
The 
The handshake procedure for CoAP I-DTLS is shown in the illustration in Figure 6. Multiple CoAP I-DTLS messages can be combined into a single set of messages to simplify network packet utilisation. In the diagram, the horizontal arrows represent these groups of messages. The process is started by the CoAP I-DTLS client by sending the ClientHello message, to which the server replies with a HelloVerifyRequest message. A stateless cookie created for DoS risk mitigation is contained in the HelloVerifyRequest message, and the client is required to repeat this cookie in its following ClientHello message. The ServerHello message is sent after the server successfully validates the cookie. These messages help the client and server communicate while developing security enhancing features. All the following are established: cypher suite, compression mechanism, protocol version, and session ID (used for session restart). Additionally, two random values—one for the client and one for the server are generated and exchanged. The full CoAP I-DTLS handshake.
The agreed-upon improvements in security capabilities determine the order of handshake communications. The diagram’s messages marked with an asterisk (*) are either optional or reliant on the context. The graphic depiction shows the message exchange for a certificate-based encryption scheme. Messages like Certificate, ServerKeyExchange, CertificateRequest, and ServerHelloDone are included in the server’s reply. When the cypher suite requires server authentication, the server transmits its X.509 certificate via the Certificate message. A ServerKeyExchange message could be sent if the key exchange skips using a server certificate. The server could alter-natively send a CertificateRequest message to the client to start the certificate acquisition process. The server then sends a ServerHelloDone message to end the hello-message portion of the handshake.
Smart e-health gateways include a local database that enables them to temporarily store medical sensor data, do local processing, and obtain clearance as an embedded server, in contrast to standard gateways and delegation servers. The verification and approval tasks of a centralized server can be made decentralized and controlled by intelligent e-health gateways by utilizing the properties of these gateways. 54 With this strategy, individual smart e-health gateways can manage remote endpoint authentication and authorization across various smart medical environments’ sub-domains or rooms. The potential impact of a DoS attack or compromised smart e-health gateway is restricted to the medical sub-domain. 55 In this paper, initially intend to reuse existing security protocols in order to offer authentication and authorization across many network domains in the proposed architecture. Second, paper strive to give medical devices with limited hardware resources the security context they require to properly connect with a distant healthcare institution.56–59
One more attack, A sophisticated, ongoing cyberattack known as an advanced persistent threat (APT) occurs when an attacker sneaks into a network and remains there for an extended amount of time with the goal of stealing confidential information. APT attacks are meticulously prepared and intended to sneak inside a particular company, circumvent security protocols, and go unnoticed. Unfortunately, a company cannot be adequately protected against an APT assault by typical security measures like firewalls, defense-in-depth, and antivirus software. To thwart any assaults, sophisticated persistent threat detection systems must be employed, utilizing the most recent threat signatures and threat methods on the manipulating threat actors.
As seen in Figure 7, a full handshake starts with a ClientHello message that contains the connection’s credentials. During the handshake, this message is used to calculate the pre-master secret key. On Flight 3, a ClientHelloVerify cookie is present. The ServerHello message, the first message in Flight 4, contains the agreed-upon cypher suite. It also includes the random value generated by the smart gateway during the handshake, which is utilized to create the master secret key. The supported cypher suites of the end user provide the foundation for the mutually agreed-upon cypher suite. For Flight 4, the message ServerHelloDone signifies the end of communication. The end certificate is the first message of flight 5 if mutual authentication is utilized. The master secret key is calculated in ClientKeyExchange using the user-provided additional parameters. Throughout flight 6, gateway transmits its own ChangeCipherSpec and Finished signals. The final communications are used by both peers to send and receive data from apps that are correctly encrypted. Contrarily, the smart e-health gateway uses certificates or an application-level password to authenticate with the remote endpoint following the DTLS handshake. Full handshake between CoAP I-DTLS server and client.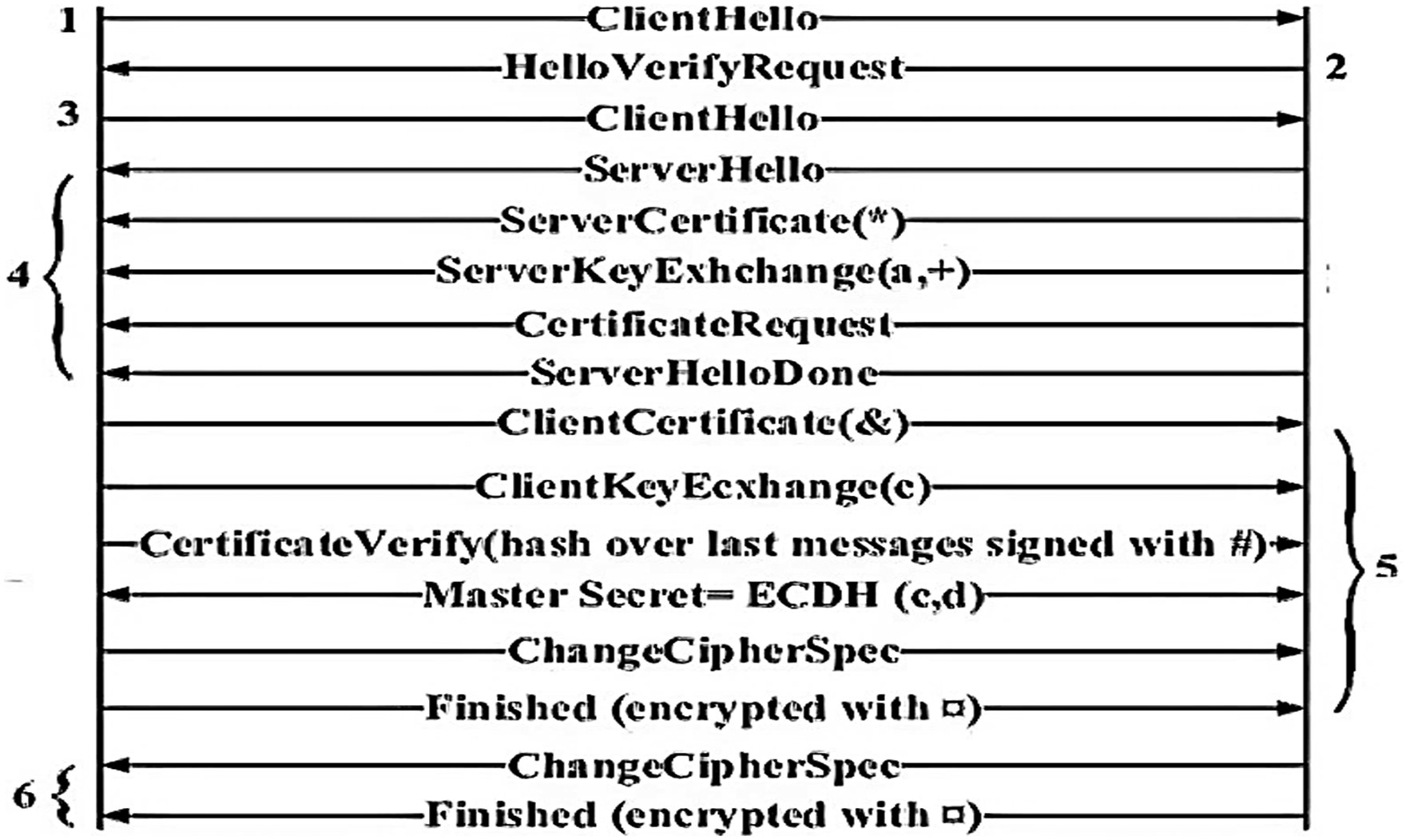
Results and discussion
IoT has a favorable effect on healthcare, enhancing millions of people’s lives. It finds illness and conducts a thorough analysis of the healthcare system. It offers personalized attention to each person for their benefit. IoT de-vices may remind patients about appointments, activity checks, calorie counts, blood pressure, disease states, and much more when employed in medical crises. The Internet of Things (IoT), which is supported by cutting-edge technology, has a surprising capacity to produce better results. Innovative concepts that improve patient care and allow for precise surgical interventions are put into practice when they lead to significant improvements in the field of medicine. Even in the face of the ongoing pandemic’s difficulties, complex situations can be smoothly managed and digitally supervised. IoT helps to build first-rate support services for medical professionals, such as doctors, surgeons, and patients, by solving new issues in the medical field.
The traditional I-DTLS is performed between the customer and entryway rather than customer and server. Small DTLS 0.8.1 was picked for library capacities, and Contiki 2.7 is picked to demonstrate the complete work. By and large, MSPSim is additionally named as Cooja test system. The bundle misfortune proportion is determined for the CoAP, CoAP-DTLS, and CoAP I-DTLS. Similar outcomes are shown in Figures 8–10 with Packet loss ratio at a time out of 20 s, 40 s, and 60 s respectively. Packet loss ratio at a time out 20 s. Packet loss ratio at a time out 40 s. Packet loss ratio at a time out 60 s.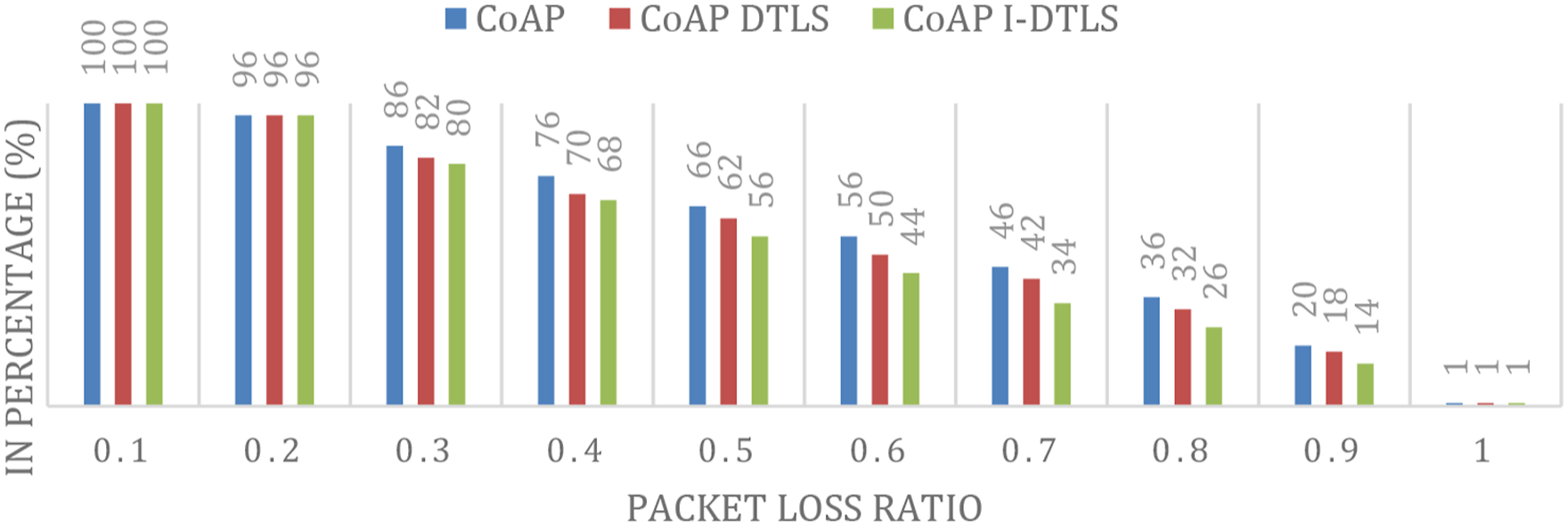


Data is routed along the shortest path, which increases network capacity and promotes a longer network lifetime. Equation (9) gives the estimated PDR as 
Furthermore, data transmission is computed to assess I-DTLS efficiency. When compared to other security protocols such as CoAP and CoAP-DTLS, the CoAP I-DTLS protocol performed better, as demonstrated in Figure 11. Data transmission.
Figure 12 shows the energy consumption rates of the three protocols such as CoAP and CoAP-DTLS and CoAP-DTLS. The energy spent by sensing, communication, and processing activities is utilized to estimate the average node energy consumption. The simulation duration and average energy consumption rates are shown by the x- and y-axes, respectively. The suggested IoT-enabled healthcare architecture’s energy usage is lower than that of traditional healthcare architecture. Energy consumption average.
Healthcare has been greatly impacted by IoT, which improved the infrastructure and information system during the COVID-19 Pandemic. It enhances hospital administration and medical procedure digitization. New medical applications are made available as more gadgets and instruments are connected to the internet. Several inter-net-connected patient devices are being introduced in an effort to monitor patient health more effectively. It alerts the public to problems with public health by monitoring climate change. The hospital can function efficiently during the COVID-19 Pandemic because to this technology. It offers verifiable information, which greatly aids in drug monitoring. This result can be explained by the availability of alternative coverage technologies that enable interactivity amongst all medical equipment in an IoT-enabled healthcare architecture. As a result, compared to traditional design, the transmitted data is dispersed among a larger number of devices. As a result, the amount of each device’s sent data is reduced, resulting in lower energy consumption rates. Furthermore, the prioritized component’s ability to reduce the quantity of processed data is an essential aspect that has a beneficial impact on energy consumption rates. Because of the growing data processing requirements, the energy consumption rates for both healthcare systems have grown over time.
An IoT healthcare system prototype was detailed in this study. The CoAP I-DTLS routing protocol was proposed in the paper. The neighbor discovery procedure gathers and stores the movement and energy data of the neighbor Coordinators. To choose the most appropriate neighbor to forward the data to, CoAP I-DTLS forwarding is used. According to the simulation results, in comparison to the other three routing protocols, the suggested protocol performs better. With the aid of the data gathered and monitored by the sensors, the CoAP I-DTLS protocol, which offers a high level of communication security in our proposed work, will be employed to help achieve energy efficiency. In contrast to other studies, the proposed protocol has developed a system that uses IoT sensors to monitor physiological metrics like respiration rate, sweat, skin temperature etc. The user of the system we are developing will have direct access to sensor data and will also need to follow the device guidelines in order to take any actions.
Conclusion
This paper describes how IoT technology can be utilized to build smart healthcare systems and smart systems that will boost as well as maximize the accuracy of expected results. As a result, the Internet of Things and sensor networks have enormous potential to free up doctors and improve disease detection. In recent years, security and privacy in healthcare have emerged as major concerns. Several academics have created a variety of authentication and authorization techniques to avoid and secure sensitive data obtained using wearable IoT devices. However, end-to-end security solutions are required to prevent and regulate access to health data. TLS is a well-known protocol for reliably transferring data from source to destination. The primary function of this protocol is to ensure that no messages are lost or reordered. The challenge with this protocol is to accept unreliability. To address this issue, the DTLS protocol is commonly used in current wireless networks. The technical issue with the DTLS protocol is that an attacker might send multiple ClientHello messages to a server. As a result, there is a chance of causing a DOS attack on the server. To address this issue, we suggested a smart gateway-based authentication and authorization solution that prevents and protects health data acquired from IoT wearable devices. In this study, smart gateway-based improved DTLS is shown using a Contiki-based network simulator. The performance of the upgraded DTLS protocol is compared to other security protocols as CoAP, HIP, and CoAP-DTLS. Based on extensive simulation testing, the proposed CoAP I-DTLS protocol beats earlier work by attaining the highest security and the best throughput with respect to consumption of energy. As future work perspective, work can be done to develop a more effective routing protocol that increases network efficiency rather than continuously moving the smart gateway location to add more nodes covering a larger area.
Footnotes
Author contributions
All authors contributed equally to the conceptualization, formal analysis, investigation, methodology, and writing and editing of the original draft. All authors have read and agreed to the published version of the manuscript.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
