Abstract
In the Internet of Medical Things (IoMT), medical devices are connected to the Internet of Things (IoT), allowing better tailored healthcare, faster hospital treatments, more affordable medical solutions, and more patient comfort. The most serious threat to the safety and confidentiality of patient’s medical records is the possibility of attacks on the IoMT environment. In order to address these problems, researchers have proposed several approaches and methodologies. None of these protocols presents a low-computing-overhead method that combines authentication with privacy preservation. This research proposes a protocol for secure authentication of IoMT devices while protecting user privacy. The proposed approach ensures the confidentiality of the IoMT devices connected to the patient’s body while communicating. In addition, the proposed protocol is validated using the widely recognized formal validation tool Automated Validation of Internet Security Protocols and Applications (AVISPA). The suggested protocol resolves existing protocols’ vulnerabilities and is resistant to many well-known security issues. Compared with existing protocols that use public cryptosystems, such ElGamal and RSA, the suggested protocol stands out due to its smaller key size and reduced computational overhead. A comparison with the well-known protocols revealed that the combined method for “lightweight authentication and privacy preservation” is computationally 5 to 6 times more efficient. However, this research has significant real-world implications from various social, economic, and business viewpoints, both locally and globally.
Introduction
The development of the Internet of Things (IoT) led to the creation of the IoMT, an initiative to improve healthcare quality. 1 IoMT entails gathering and transferring private medical information from patients to a central authority (CA) that stakeholders, including doctors, can access. The IoMT is made up of a variety of medical devices and applications, including wearables, sensors, remote monitoring systems, and health-tracking apps. These devices can collect a wide range of health data, including vital signs, blood glucose levels, adherence to medications, and more. This data is then transmitted to healthcare providers, who can use it to monitor patients remotely and make better decisions about their healthcare.2–4 The IoMT could completely transform healthcare delivery by enhancing patient outcomes, decreasing costs, and increasing efficiency. With IoMT help, healthcare professionals can better manage chronic diseases and avoid hospital readmissions, allowing patients to receive proactive and individualized treatment. 5 However, the IoMT has its shared problems. Some of these include concerns about the security and privacy of user data, the need to comply with regulations, and the necessity of systems and devices to communicate.6,7,4,8 However, due to its potential benefits, the IoMT is a promising new frontier in healthcare research and development. A crucial part of controlling the COVID-19 epidemic has been the use of IoMT devices. 9 In relation to COVID-19, IoMT devices have the following advantages: they are accessible from anywhere and are quick to identify, locate contacts, and analyze data. IoMT devices help control the COVID-19 pandemic by facilitating remote monitoring, early detection, contact tracking, and data analysis. However, it is essential to address privacy and data security concerns to ensure that patients can benefit from this technology safely and ethically. Using elliptic curve cryptography (ECC) and resolving security vulnerabilities, this paper introduces a lightweight privacy-preserving authentication protocol for IoMT. Rigorous security analysis and validation using AVISPA have confirmed its robustness, and comparisons have shown that it is well-suited for IoMT applications.
The remainder of the paper is structured as follows: first, review existing research related to privacy and security. Next, outline the motivation for the study and its contributions. Following that, present the foundational concepts, including the Elliptic Curve Discrete Logarithm Problem (ECDLP) and blind signatures based on ECDLP. The subsequent section details the proposed scheme, which includes the system model and describes a secure, privacy-preserving initialization phase, registration phase, and authentication protocol for IoMT devices, gateways, and the CA. Then, the paper addresses the removal of malicious IoMT devices and gateways. A security analysis is provided, including formal validation using the AVISPA tool and informal protocol validation. Finally, results and discussions are covered, and the paper concludes with a summary of key findings.
Related work
Many methods have been offered to verify the legitimacy of nodes in IoMT systems and to guarantee authentication between gateway nodes and IoT devices. Such methods use various cryptographic techniques, including lightweight cryptography, elliptic curves, and hash functions.10,11,6 In this section, give a summary of some of these research initiatives.
In the year 2009, a two-factor authentication technique was designed for wireless sensor networks (WSN). 12 Later in 2010, He et al. found the weaknesses in Das et al.’s protocol, found some vulnerabilities such as insider and impersonation attacks, inability to change passwords, information leakage, lack of anonymity, no mutual authentication, and no session key establishment. 13 Later, they suggested an enhanced two-factor authentication scheme to overcome these vulnerabilities. In 2011, Kumar 14 identified deficiencies in the He et al.’s 13 protocol. These deficiencies include the absence of user anonymity, mutual authentication, the establishment of session keys, and the susceptibility to information leakage attacks. 14 In the same year, Kumar found that Khan’s 15 scheme has some vulnerabilities, such as mutual authentication, session key establishment, and message confidentiality.
In 2010, a system developed known as GDP (Group Key Distribution System) specifically to ensure secure communication in Body Area Networks (BANs). 16 The protocol’s objective is to establish a collective key that can be utilized to disseminate messages inside the network. However, the author discusses the deployment of the protocol on a sensor network platform but does not provide comprehensive evaluation data or performance analysis. After that, in 2013, 17 introduced a protocol for a Certificate less Signature Scheme, and the protocol guarantees protection, confidentiality, and resilience against many threats. After that, in 2017, He et al. 18 reviewed Liu’s protocol and found that it is susceptible to impersonation attacks. Later on, Anonymous authentication scheme for WBANs was proposed by.18–20
In 2019, Zhou et al. 21 developed an authentication technique that relies on an IoT-enabled cloud architecture, and both protocols relied on the use of logical OR operations and hash functions. Nevertheless, these protocols are vulnerable to privileged insider attacks, replay attacks, MITM attacks, and impersonation attacks. Whereas Jaiswal et al. 22 proposed a edge computing based ,Srivastava and Debnath 23 propose a multivariate-based certificate less signature system to improve security in IOMT networks. In the same year, Chatterjee 24 suggested an authentication protocol for wireless body sensor networks that relies on the Paillier public key encryption cryptosystem. Nevertheless, the proposed system may encounter algorithmic complexity concerns, rendering it inappropriate for Body Sensor Networks (BSN). Also, Fotouhi et al. 25 introduced a safe authentication system that is lightweight and based on hash chains. Later Sureshkumar et al. 26 introduced a streamlined authentication protocol for smart healthcare systems that relies on ECC. Unfortunately, the protocol is susceptible to traceability, integrity conflict, and de-synchronization attacks, which can be easily exploited and result in substantial security problems.
In 2021, Lee and Chen 27 presented a secure IoT protocol for medical networks that uses Physical Unclonable Functions (PUFs) for authentication and defense against attacks such as side-channel assaults and data tampering. In the same year, Mohammed et al. 28 presented a bio-inspired robotics system that uses blockchain technology to enable task planning in an IoMT environment. However, these protocols are not resistant to physical tampering and have more computation than other schemes.
In 2021 Wang et al. 29 proposed a lightweight and reliable authentication protocol for WMSN. To overcome these problems physical layer security and over-centralized server problem in WMSN. This protocol is susceptible to different types of attacks, including man-in-the-middle attacks and session key leakage, lacks mutual authentication. Whereas in the same year, Li et al. 19 introduced the PSL- MAAKA authentication protocol, which offers lightweight authentication by utilizing hash and XOR operations for authentication and key agreement.
In 2022 yu and Park 30 provide a more advanced authentication mechanism that utilizes Blockchain and PUFs to tackle these problems. They verify the security of their protocol by conducting both informal and formal assessments, such as the AVISPA simulation and the ROR Oracle model. However, this protocol suffers from certain safety flaws. The research conducted in 2023 Praveen and Pabitha 31 introduces a secure and efficient user authentication method that is specifically used for IoMT applications which uses bioacoustics and a fuzzy embedder and Singh et al. 32 proposed a group based protocol i.e GBEKA. These two authentication methods have more computational costs than other authentication schemes in terms of constraint devices. Later, Das and Namasudra 33 proposed a privacy- preserving mutual authentication scheme using lightweight components like XOR, concatenation, and hash functions to secure sessions between IoT devices and gateways. However, their approach is vulnerable to several attacks, including insider, impersonation, man-in-the-middle (MITM), and replay attacks, and lacks mechanisms for detecting malicious devices and Gateways.
In summary, devices with limited resources are not the focus in most of the existing works. In addition, most of the works do not consider patient data privacy since they rely on offline registration. An improved solution for IoMT environments is proposed in this work, which fills this gap by offering a lightweight authentication method that protects privacy and uses lightweight components like XOR, hash functions, and the proposed protocol to detect malicious devices and Gateways, thus providing a more robust solution for IoMT environments.
The networked medical devices and systems that makeup IoMT can enhance healthcare delivery, patient monitoring, and treatment outcomes. Nevertheless, the interconnected nature of IoMT brings about a plethora of security concerns. These include vulnerability exposure to impersonation, stolen-verifier attacks, data non-repudiation, data confidentiality breaches, anonymity compromises, known- key security risks, replay attacks, message authentication, privileged-insider threats, parallel session exploits, and man-in-the-middle attacks, etc.. 34 The confidentiality of patient information, adherence to regulations, and the efficacy of healthcare procedures depend on the security and privacy of IoMT systems.3,35,36
Ensuring the security and privacy of IoMT systems is essential for maintaining patient trust, regulatory compliance, and the integrity of healthcare operations. To protect healthcare data and reduce risks,it is necessary to deploy comprehensive security measures such as authentication, privacy, encryption, access control, anomaly detection, and threat intelligence. These security challenges must be resolved for the IoMT to realize its promise of transforming healthcare delivery while protecting patients’ privacy and safety.
The following are the most important takeaways from this paper: • The healthcare system utilizes IoMT devices with limited resources. The suggested protocol has been explicitly designed to tackle the difficulties presented by this system. • Protocol has been proposed for registering an IoMT device and the gateway with the CA. • Lightweight components such as XOR, Hash function, and concatenation were used to minimize computational power usage. • The methodology ensures patient privacy by employing blind signatures upon registration with the CA. • Certain security aspects, including confidentiality, anonymity, integrity, lightweight, mutual authentication, and privacy preservation, are guaranteed by the proposed protocol. Furthermore, this protocol is resistant to a number of attacks, such as CCA, replay attacks, Man in the Middle, impersonation, and modification attacks. The suggested protocol also detects malicious IoMT devices and gateways. • The protocol enables identifying and eliminating any malicious Gateway and IoMT devices from IoMT healthcare environments. • The AVISPA tool is utilized to validate and verify the suggested protocol. • Our comparison analysis highlights the superior ability of our protocol to preserve privacy compared to other protocols operating in the same situation.
Preliminaries
This section provides preliminaries for a proposed protocol for an IoMT based healthcare system network.
Elliptic curve cryptography (ECC)
ECC is a well-known public key cryptosystem 10 with features of smaller key sizes compared to other cryptosystems like Integer Factorization Problem-based RSA 37 and DLP-based ElGamal 38 for achieving the same level of security. Since only exponential-time attacks are known so far, the Elliptic Curve Discrete Logarithm Problem (ECDLP) might still be intractable even if factoring and multiplicative group discrete logarithms are broken.
As per NIST.

The equation of the elliptic curve over Finite Field 
The domain parameters for the Elliptic curve over
A blind signature issued to provide anonymity and privacy for entities. It consists of four phases, as below (Figure 1). • Initialization Phase • Blinding Phase • Signing Phase • Extraction phase


Registration of gateway with CA.
Proposed scheme
In this section we describe the suggested system model and then explain the proposed protocol.
System model
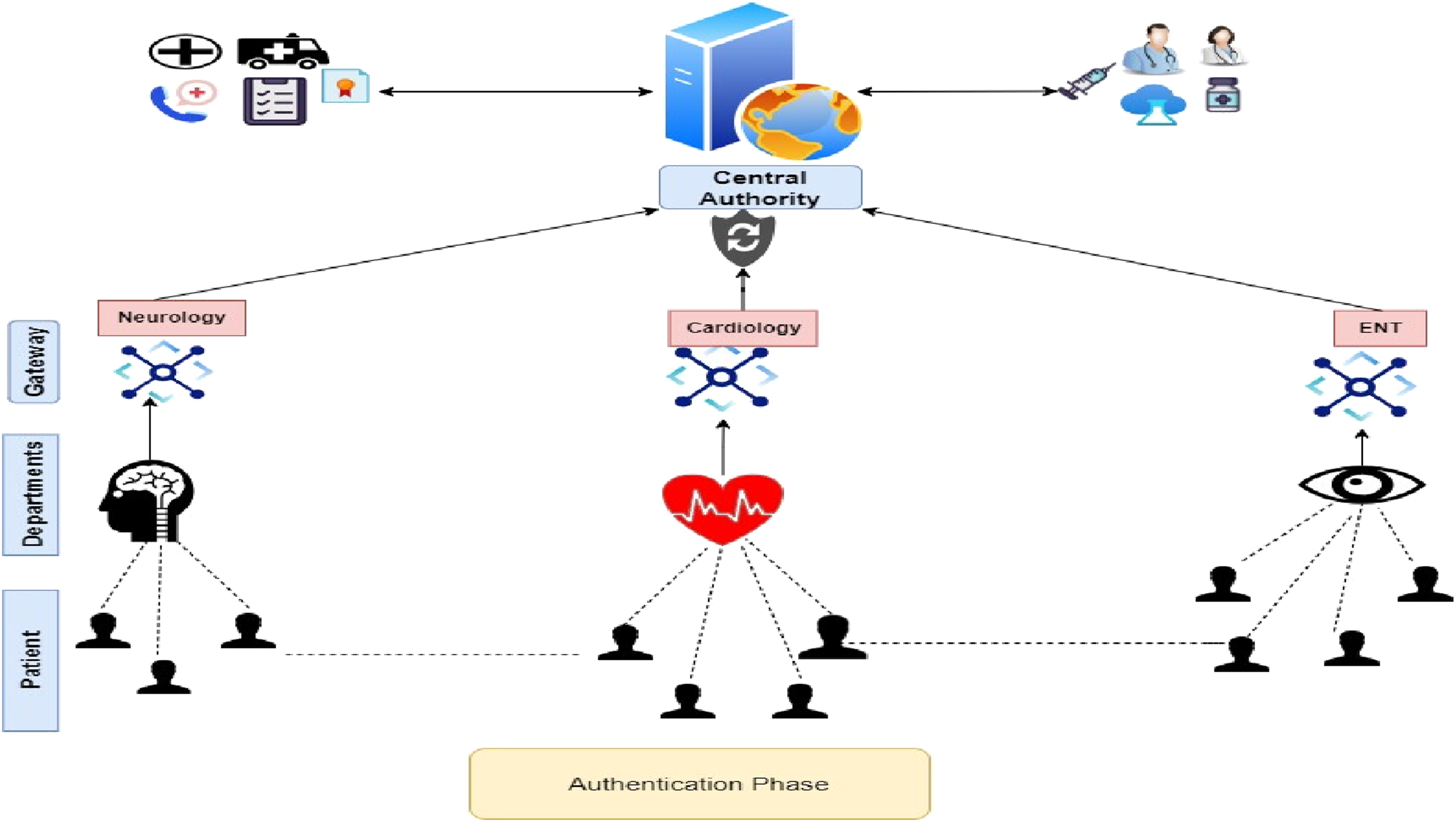
The architecture of the IoMT-based healthcare system network model is shown in Figures 2 and 3. This section outlines the process of setting up the network in preparation for implementing the proposed protocol. In this model, each IoMT device has a unique identifier that is affixed to the patient’s body. Patients move from one place to another in a dynamic route (e.g.: from the Pathology department to the Cardiology department), while each Gateway is fixed at some critical locations in the proposed model. When patient comes into the coverage area of a Gateway, all the IoMT devices affixed to the patient are first authenticated after that communication starts. Patients travel from one location to another; as previously noted, they enter the coverage area of one Gateway and then later enter another again; authentication of IoMT devices is done with the Gateway in that range. We suggest implementing a CA, which will be accountable for managing the identities of all devices registered within its network. System model for the registration phase. System model for the authentication phase.
Notation used in the manuscript.

IoMT device: IoMT devices collect medical data using sensors, analyze it locally, and securely communicate it to CA. By being integrated with healthcare systems, they provide patients with more control and importance while also making data security a top priority, thereby guaranteeing privacy. This technology transforms healthcare by facilitating un-interrupted monitoring and tailored treatment, improving patient outcomes.
Gateway: Gateways are essential in IoMT environments since they authenticate IoMT devices in consultation with CA. These gateways function as intermediates, guaranteeing the establishment of secure communication routes. The gateways share all transferred data with the CA and, in turn, forward it to medical experts, ensuring smooth and secure data transmission while upholding privacy and confidentiality.
CA: The CA establishes and enforces regulations, standards, and guidelines to ensure compliance with healthcare regulations. It certifies IoMT devices, evaluating their functionality, safety, and adherence to regulatory requirements before granting authorization for deployment. It also authenticates the Gateway installed in the IoMT healthcare system. CA maintains registered IMT devices and Gateways. CA plays an important role in removing malicious IoMT devices and Gateways. Additionally, the CA manages digital identities and authentication mechanisms to facilitate secure communication and data encryption within the IoMT network. More-over, it aggregates anonymized data collected from IoMT devices. The CA also plays a critical role in incident response and security monitoring, detecting and responding to security breaches or unauthorized access attempts. Furthermore, it promotes interoperability and standardization, ensuring seamless integration and communication between different IoMT devices and healthcare systems. In the IoMT health-care system, the CA is essential for assuring the security, stability, and compliance of IoMT systems, promoting innovation and better healthcare results.
Protocol
In this section, we have explored online registration procedures for IoMT devices and Gateways using CAs and discussed an authentication protocol for IoMT devices with Gateways. We have suggested an authentication protocol for the IoMT devices with a CA that uses blind signatures based on ECC. This section also provides a detailed explanation of the scheme’s mathematical formulation.
In the proposed protocol, all entities involved in the IoMT Health care system agreed upon the domain parameter of ECC. Randomly select a secret key dc for the CA,
The shared secret key between the IoMT devices and the Gateway is denoted as

Algorithm for registration of IoMT device with CA
The IOMT device used its MAC address for its unique identification, known as

Algorithm for authentication of IoMT by gateway
The protocol involves the IoMT device retrieving its anonymity Identification from its memory

Removal of malicious IoMT device and gateway
Initially, the Gateway and IoMT device was registered with the CA in online mode. CA maintains a registered list for Gateway and IoMT devices. The authentication process starts when an IOMT device comes in the range of one of the gateways. Gateway, after receiving a request from the IoMT device, in turn, sends CA for verification of whether the said IoMTdevice is registered or not, along with its own identity. CA searches both identities in the registered list; if it does not find anyone or both, then marks it as a malicious device or gateway and removes them from the IoMT environment. This process has been explained in Algorithm 4 in step-2 to 13. After this, any impersonate attack has been done by the malicious entity in step-32. If it does not match the authentication code, the CA removes the IoMT device from the network.
Security analysis
This section introduces formal and informal analysis. The formal analysis simulates the authentication protocols with the AVISPA tool, ensuring the system meets specified security standards. Whereas informal analysis involves a theoretical consideration of security features and attacks. Here are the specifics:
Formal security verification with AVISPA tool
AVISPA is a robust tool designed for Automated Validation of Applications and Internet Security Protocols. Created in 2004 by Basin et al.
40
as a component of a European project, it functions as an automated analysis tool specifically designed to assist in the verification of security protocols. AVISPA addresses two prominent challenges: it strives to achieve operational efficiency while also ensuring accessibility to people who may not possess expertise in the field of security. This tool is adaptable and can be used for both small and medium-sized protocols, such as those present in the Clark/Jacob library, as well as larger-scale Internet security protocols. AVISPA analyses protocols that are written in the High-Level Protocol Specification Language (HLPSL). This language is formal and based on roles. It is used to specify data structures, cryptographic operations, control flow patterns, and algebraic features. Subsequently, the protocol requirements are converted into an intermediary format referred to as IF. AVISPA utilizes four distinct backend tools, each with the capability to analyze protocols encoded in the IF format. The back ends provide four different approaches to analyzing the protocol, which improves the tool’s versatility and adaptability.
41
AVISPA has the capability to verify any language that can be transformed into IF, without any limitations on specific languages. In summary, AVISPA is a highly beneficial tool for automatically validating security procedures. It provides efficiency and accessibility to a diverse range of users, regardless of their level of competence in the field of security. Our analysis includes three distinct roles: “IoT Device,” “Gateway,” and “CA.” Each position has particular session and environment parameters that outline the security aims. We employed the CL-AtSe and OFMC back ends to verify the security of our system. The intruder possesses complete network authority, enabling them to intercept, analyze, or change messages using the appropriate encryption keys. Nevertheless, our simulation results validate the robustness of our method, even in scenarios where the attacker can impersonate entities and transmit messages. The results demonstrate that the system is secure, highly effective, and capable of preventing attacks such as Man-in-the-Middle (MITM), replay, and impersonation. The validation conducted by AVISPA is illustrated in Figures 4–6 displays the results of the registration and authentication protocol of the system. Registration of gateway with CA. Registration of IoMT device with CA. Authentication phase.


Informal security analysis
Result and discussion
This section describes the system configuration, evaluates the communication and computation costs associated with the log-in and authentication stages, and compares the security features and resilience to different attacks. Additionally, we will contrast our suggested protocol’s computation and communication costs with those of the current protocol.
System configuration
A well-known validation tool AVISPA was used to validate the suggested authentication protocol. Here is the system configuration: • Operating System: SPAN-Ubuntu 10.10-light (32-bit) • Virtualization Platform: Oracle VM Virtual Box Manager • Host Machine: iMac • Processor: Intel(R) Core (TM) i5 CPU, 2.3 GHz (Dual-Core) • Memory (RAM): 8 GB
Security features and attacks
Comparative summary: security features and attacks.

Computation and communication cost
Comparative summary: computation and communication cost.

Computational cost efficiency
One of the key factors in our protocol’s superior performance is its use of lightweight cryptographic components. In the proposed scheme, hash functions, XOR operations, and simple concatenation are extensively used in place of more complex and computationally heavy operations, which are commonly found in traditional security protocols. This choice makes our protocol particularly suited for devices with limited computational resources, such as the device nodes. Device nodes, which have far lower computational capacity than gateway nodes, benefit the most from this lightweight design. In real-world deployments, device nodes often handle authentication and session initiation, making computational efficiency a critical factor in protocol performance. By reducing the computational complexity, our protocol minimizes the time spent on processing, which in turn conserves energy for battery-powered IoT devices. Based on the study
25
we can see that a single hash function operation takes approximately
Communication cost
Another important consideration in the design of security protocols is communication cost, which refers to the amount of data exchanged during authentication processes. High communication costs can lead to increased bandwidth usage, higher power consumption, and longer delays, all of which can degrade the performance of resource- constrained devices. The proposed scheme minimizes the communication overhead by keeping the size of exchanged messages small. The security parameters used in the protocol, such as hash values, identities, and nonce values, are carefully chosen to strike a balance between security and efficiency. For example, the hash values and identities in the proposed protocol are assumed to have a security level of 160 bits, while the nonce values have a security length of 128 bits. These sizes are adequate to provide a strong level of security while ensuring that the message sizes remain small, thus minimizing the communication cost. The proposed protocol, focusing on symmetric key operations and hash-based authentication, avoids such costly exchanges. Despite its lightweight nature, proposed protocol does not compromise on security. The use of hash functions and nonce values effectively prevents replay attacks, where an adversary reuses old authentication messages. Additionally, the security levels of 160-bit hashes and 128-bit nonce are strong enough to resist common cryptographic attacks such as brute-force or collision attacks, thereby ensuring the integrity and confidentiality of the communication. When compared to other protocols that may rely on heavier cryptographic operations, such as RSA, ECC, or even multi-round message exchanges, the proposed protocol clearly demonstrates lower computational and communication costs. For example, public key-based protocols typically require larger key sizes and involve computationally expensive operations like exponentiation, which are unsuitable for resource-constrained devices. In contrast, the proposed protocol depends on simple hash and XOR operations, making it ideal for environments where both power and processing resources are limited. Figure 7 compares the computational cost, and Table 4 illustrates the protocol is more efficient than the other existing protocols in terms of reduced computational and communications overhead when compared to other protocols, further emphasizing its practicality for real-world deployments in constrained environments. Comparison of computational cost with other existing scheme.
Conclusion
The suggested protocol meets the pressing requirement for a solution that balances security, resource efficiency, and practicality, which is particularly important in light of the growing demand for interconnected healthcare devices. The proposed light weight protocol significantly assists in integrating IoMT by enhancing patient safety and preserving sensitive medical data. The proposed protocol was specifically designed to address the challenges with in the IoMT environment. Online methods of registering an IoMT device and Gateway with the CA have been suggested. Lightweight components, such as the XOR operator, the hash function, and concatenation, were utilized to minimize computing power consumption. This approach ensures patient privacy by using blind signatures while registering with the CA. Certain security features, including anonymity, confidentiality, integrity, lightweight operation, mutual authentication, and privacy protection, are guaranteed by this protocol. In addition, this protocol is resistant to several attacks, such as CCA, replay attack, impersonation, and Man in the Middle attack. The protocol allows for the detection and removal of any malicious Gateway and IoMT devices that threaten IoMT healthcare environments. The proposed protocol is validated and verified using the AVISPA tool. According to the comparison analysis, this protocol preserves privacy better than other protocols in the same scenario. According to the comparison, it is computationally five to six times more efficient than the existing methods. From a local and global perspective, the study presented in this paper has substantial practical consequences that can be understood through social, economic, and commercial lenses. This work represents a major advancement towards secure communication in healthcare and opens up possibilities for more research and development in this important area.
Footnotes
Author contributions
Kalpana Samal Design of Authentication protocol and informal security analysis for IOMT device and written the manuscript. Shanta Kumari Sunanda Verified the security protocol by using BAN Logic. Debasish Jena has done the verification of the proposed protocol using AVIPSA and written the manuscript. Srikant Pattnaik has verified the logic for the proposed scheme.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
