Abstract
Ensuring the confidentiality of communication is of paramount significance. Traditionally, cryptographic practices for Wireless Sensor Networks (WSN) have been primarily based on classical cryptography like RSA and Elliptic Curve, which are potentially susceptible to cyber attacks from future quantum computers with enough computing power. To ensure the protection and safety of inter-node communication in WSNs, it becomes imperative to employ a Post-Quantum Cryptography (PQC) algorithm. This paper presents post-quantum low-energy adaptive clustering hierarchy (PQ-LEACH), an advanced secure wireless communication protocol based on the LEACH protocol. By integrating post-quantum cryptography, specifically Kyber’s key encapsulation method, and a key update system, PQ-LEACH effectively enhances the security of communication and mitigates various WSN attacks. Additionally, a comprehensive performance analysis of PQ-LEACH, including its impact on network energy efficiency and longevity, is conducted. The results demonstrate the trade-offs between enhanced security measures and operational performance, providing critical insights for the deployment of secure and efficient WSNs in a quantum-threatened landscape.
Introduction
Wireless sensor networks (WSNs) are a collection of sensor nodes that communicate wirelessly to gather environmental information, which can be related to temperature, humidity, pressure, or any other parameter monitored in real time.1,2 Moreover, WSNs are currently experiencing accelerated deployment. Thus, it is reasonable to anticipate that, in the next decade or so, WSNs could become ubiquitous, providing environmental sensing, internet access, and other services in an unprecedented number of physical locations worldwide. 3 The vast potential of this innovative technology has generated enthusiasm, predominantly in environmental, medicinal, military, transportation, entertainment, crisis management, homeland defense, and smart space fields. 4
Security is paramount in WSNs because they are often deployed in unattended, resource-constrained, and hostile environments, making them highly susceptible to attacks. These attacks can manifest through eavesdropping, data tampering, denial of service, node compromise, and wormhole attacks. 5 The inherent characteristics of WSNs exacerbate these vulnerabilities, such as their resource limitations, open communication medium, and decentralized nature. Considering these challenges, researchers and practitioners have invested significant efforts to develop and implement robust security mechanisms to protect WSNs from malicious threats while preserving the critical features of scalability, energy efficiency, and ease of deployment. 6
Node identity emerges as a crucial concern in ensuring the security and trustworthiness of WSNs. Adversaries can potentially introduce counterfeit nodes, replicating legitimate ones, or manipulating identities to compromise the network’s functionality.7,8 Various solutions have been proposed for protecting WSNs against identity based attacks,9,10 including solutions for WSN with limited communication capability.11,12
Many protocols and techniques have emerged from the literature to safeguard WSNs against attacks, 13 which typically employ a combination of cryptographic mechanisms, key management schemes, intrusion-detection and prevention systems, secure routing algorithms, and trust management frameworks. 14 This work focuses on the security of the low-energy adaptive clustering hierarchy (LEACH) protocol. 15 Various protocols, such as lightweight secure LEACH (LS-LEACH), modified security LEACH (MS-LEACH) and security added LEACH (SA-LEACH) , have been proposed to improve the security of LEACH.16–18 These protocols have been proposed to address the security vulnerabilities of the LEACH protocol and provide authentication and confidentiality for data transmission in WSNs. Furthermore, they were developed to make WSNs more resistant to such attacks as data eavesdropping, data tampering, and node impersonation. Despite this progress, an imperative need remains for continued research and development to enhance the security and resistance of WSNs, as the landscape of threats and vulnerabilities continuously evolves with technological advances.
This work proposes post-quantum LEACH (PQ-LEACH), a novel communication protocol for WSNs designed to ensure security in the post-quantum era, where quantum-capable computers are expected to emerge, rendering current cryptographic methods vulnerable to compromise. To our knowledge, no existing LEACH-based protocol uses quantum-safe cryptography for securing communication. The PQ-LEACH protocol uses the Cryptographic Suite for Algebraic Lattices (CRYSTAL)-Kyber algorithm, a selected public-key cryptography mechanism for standardization by the National Institute of Standards and Technology (NIST). 19 The new algorithm employs a key update feature that enhances the security of the WSN and protects against sophisticated attacks, such as replay attacks. The security analysis of PQ-LEACH demonstrates that the newly devised protocol efficiently ensures confidentiality, integrity, and authenticity within the WSN. Furthermore, we analyze the performance implications of integrating the CRYSTALS-Kyber algorithm, including the overhead computation and overall efficiency of the resulting system. This comprehensive examination provides valuable insight into the feasibility and practicality of adopting post-quantum (PQ) cryptography in WSNs as a viable countermeasure against the emerging threats posed by quantum computing.
The PQ-LEACH protocol, incorporating post-quantum cryptography with algorithms like CRYSTALS-Kyber, offers a robust security solution ideal for applications such as environmental monitoring. In scenarios like forest air quality monitoring and fire detection, PQ-LEACH ensures that data transmitted across sensor networks is protected against both classical and quantum threats, safeguarding critical information. This protocol’s capability to maintain high data integrity and confidentiality is crucial for applications where data security directly influences operational outcomes, making it also suitable for sectors like healthcare and smart city infrastructures, where secure, reliable data transmission is essential. Additionally, with the advent of quantum computing, traditional cryptographic methods are becoming increasingly vulnerable, necessitating the shift to quantum-safe alternatives to future-proof sensitive data against emerging threats. By integrating quantum-safe cryptography, PQ-LEACH not only enhances current security measures but also prepares for the inevitable advancements in computational power, ensuring long-term protection of WSNs.
This article is organized as follows. Section 2 summarizes the related studies, and Section 3 details the CRYSTAL-Kyber quantum-safe cryptography, including the encryp-tion/decryption and key exchange aspects. Afterward , Sec-tion 4 describes and presents the newly proposed PQ-LEACH protocol, including its security analysis. Then, Sec-tion 5 outlines the performance evaluation of CRYSTALS-Kyber, including the results and discussion. Finally, Section 6 concludes the paper with the conclusions.
Related work
WSNs could be seen as service systems, as they integrate technology, data flow, and protocols to accomplish user needs. This align with the definition proposed by Wang et. al. 20 Many scholars have addressed the security challenges inherent in WSNs. Despite the myriad services WSNs provide in various fields, they remain susceptible to security risks. A principal concern when employing WSNs is their vulnerability in untrustworthy environments or when transmitting sensitive information. Unauthorized intrusion into the network could create privacy violations or data pilfering. 21 Potential security threats include Sybil attacks, flooding, blackhole attacks, and wormhole attacks.22–25
Furthermore, identifying an optimal cryptographic method for WSNs is a significant challenge, primarily due to processing power, memory, energy efficiency, and data size. Traditional cryptographic protocols, such as the Diffie– Hellman key agreement or Rivest, Shamir, and Adleman (RSA) signatures, are often incompatible with the resource constraints of WSNs, necessitating alternative solutions.26,27
Numerous studies have proposed solutions addressing specific problems. For instance, the secure data aggregation protocol was advised for identifying malicious nodes, emphasizing the need for future research to establish higher trust in node aggregation. 28 Chain-based data aggregation has been proposed to address energy consumption and communication overhead in WSNs, with a call for further exploration to eliminate redundant or useless messages. 29
Xiao er al. Presented s a novel Secure Clustering Routing Method based on Blockchain and Swarm Intelligence (BS-SCRM) for WSNs. 30 The proposed approach addresses the limitations of existing clustering routing methods. The simulation results show an improvement in clustering quality while providing a more secure and energy-efficient routing solution compared to existing clustering methods.
The problem of energy constraints is addressed by studies proposing asymmetric key encryption schemes based on the elliptic curve and query privacy-preserving mechanism for data aggregation.31,32 However, both studies noted the need for more comprehensive solutions, such as end-to-end aggregation for security enhancement and the integration of the cluster topology for network fortification. An energy-efficient privacy-preserving data aggregation protocol was also proposed for more effective communication and data preservation, indicating the potential for data decomposition as a viable alternative to traditional slicing mechanisms in future research. 33
The rapid growth of the Internet of Things has exposed WSNs to security transmission challenges due to the numerous data acquisition requirements. Thus, a new protocol has been proposed, 34 using multiple application security data aggregation (MASDA) to enhance data confidentiality through improved homomorphic message authentication and a multiple application elliptic curve cryptography (ECC) mechanism. They determined that MASDA effectively provides integrity and confidentiality, eliminating false data injection and information leakage. Moreover, one author challenged future researchers to verify the effects of the packet loss rate on aggregation accuracy and robust encryption schemes for advanced WSNs. 34
Shah and Jinwala revealed that linear WSNs are usually critical for security due to using maliciously communicated data. 9 The authors proposed a lightweight data aggregation scheme to solve the problem. Following the research, the authors determined that the scheme enhances data verification and privacy, facilitates malicious node identification, and augments resistance against collision attacks and node capture.
Murugeshwari et al. proposed a data aggregation scheme in which an elliptic curve secures the data transfer between cluster agents and the base station (BS). 35 The proposed solution was assessed and analyzed through a simulation using NS-2. The proposed method was compared with the efficient data aggregation technique design and the efficient and provably secure aggregation (CHTPS). The results indicate that the scheme outperforms the current solutions regarding processing time.
Kumar et al. (2018) focused on the problem of high energy consumption in WSNs, proposing a secure data aggregation framework and general secure data aggregation protocol (GSDAP) as the solution. 36 The three researchers found that the secure data aggregation framework and GSDAP boost message authentication, data encryption, and key management, reducing energy use in WSNs. However, Kumar et al. urged future researchers to conduct further studies on GSDAP through concrete cryptographic primitive applications. In addition, Kawade et al. (2019) proposed applying privacy homomorphism using an end-to-end homomorphic pallier crypto-scheme, 37 demonstrating that this mechanism offers data confidentiality and saves energy.
Besides the limited energy of WSN nodes, they are also weak at detecting intrusions in the system. Thus, Zhang et al. (2020) called for a hierarchical intrusion detection model adoption, which guarantees high detection accuracy, lowering the detection processing time. 38
Salim et al. (2021) noted that compressive-sensing-based data methods are ineffective in boosting the performance of WSNs due to their complex network deployments and exposure to attacks. 39 thus, they recommended incorporating ECC, a method they discovered to augment the efficiency of the compressive-sensing scheme. the authors indicated that future work should focus on developing other algorithms to improve the compressive-sensing scheme.
Dou et al. (2020) addressed the vulnerability of node data information during data aggregation, 40 proposing a secure and efficient privacy-preserving data aggregation algorithm that reduces data traffic, improving data node privacy . However, they proposed basing future work on investigating how to realize data integrity during transmissions.
An intrusion detection algorithm was presented by Ling and Hao to solve detection speed, adaptability and accuracy. 41 The proposed method is based on adaptive parallel quantum genetic algorithm. The experimental results indicate that the newly proposed method has higher adaptability and detection accuracy with a lower false negative rate than existing detection methods. Furthermore, the authors proposed another detection method based on normalized mutual antibodies information feature selection and adaptive quantum artificial immune with cooperative evolution of multiple operators. 42 This new method has better detection performance than existing algorithms.
Sanal et al. (2021) presented a version of CRYSTALS-Kyber that is optimized for 64-bit ARM Cortex processors. 43 They introduced multiple optimizations for Number Theo-retic Transform (NTT) to enhance Kyber’s implementation in all cryptographic levels. These optimizations improved the performance by more than 1.72x, 1.88x, and 2.29x for key generation, encapsulation and decapsulation.
The concept of a service system has been defined in various ways in the literature, with some definitions emphasizing the involvement of humans as central to the system, where the customer plays a significant role in the service process. 20 The authors of this paper address these gaps by proposing a new definition that clearly differentiates service systems through the interaction of infrastructure, substance, and management, offering a more precise and functional understanding of what constitutes a service system. A WSN can be viewed as a service system.
Preliminaries
The nodes in WSNs communicate through communication protocols which is a set of rules and procedures that govern how data is transmitted and received among sensor nodes. These protocols ensure efficient communication, data integrity, security, and energy conservation within the network. Quantum computing has emerged as a revolutionary technology with the potential to vastly outperform classical computers.44,45 The ingenious concept of quantum bits, or qubits, lies at the core of quantum computing. Unlike classical bits that can exist in either a 0 or 1 state, qubits leverage a quantum phenomenon known as superposition, enabling them to exist in multiple states concurrently. This unique property can be described as a qubit being 0, 1, or both 0 and 1 simultaneously, providing a dramatically augmented information capacity. It allows quantum computers to perform multiple computations simultaneously, considerably accelerating their problem-solving capabilities. However, this development also has significant implications for classical encryption methods. 46
Equivalent encryption strength level.

The CRYSTALS-Kyber algorithm is a key exchange protocol designed to be secure against quantum attacks. 49 Its security relies on the difficulty of lattice problems, which are challenging even for quantum computers. The specific problem that the CRYSTALS-Kyber algorithm is based on is the learning with errors (LWE) problem and its ring-based variant, the ring-LWE problem.
The LWE problem involves determining a secret vector s, given several linear equations with added random noise. The difficulty increases as the noise increases, making it computationally infeasible for classical and quantum computers to solve. The ring-LWE problem extends this to polynomial rings, leading to more efficient implementations while maintaining the same security level. The CRYSTALS-Kyber algorithm takes advantage of the difficulty of these problems to provide a PQ secure key exchange mechanism.
CRYSTALS-kyber algorithm
The CRYSTALS-Kyber algorithm is an public-key cryp-tographic protocol from the NIST PQ cryptography stan-dardization process. It provides an essential pillar for PQ security in a world where quantum computing’s fast-paced evolution threatens traditional cryptographic algorithms. The CRYSTALS-Kyber algorithm is a lattice-based cryp-tographic system, with security resting on the difficulty of the module LWE (MLWE) problem, a variant of the LWE problem in the ring/module setting. Lattices are geometric structures that can be intuitively visualized as grids of points stretching infinitely in multiple dimensions. The complexity of lattice problems increases exponentially with the number of dimensions, making them suitable for enhanced crypto-graphic security.
The specific problem regarding the security of the CRYSTALS-Kyber algorithm is the shortest vector problem (SVP) in lattice theory. In its decisional version, this problem asks whether a given vector is the shortest nonzero vector in a lattice, whereas its search version requires locating the shortest nonzero vector. Both versions of SVP are challenging to solve for random lattices in high dimensions, both classically and quantumly. In the CRYSTALS-Kyber algorithm, the encryption key is a lattice, whereas the message is embedded in a short vector in this lattice. The difficulty of the SVP ensures that, without the decryption key, it is computationally infeasible to extract the embedded message—offering a high degree of security against an attacker.
The CRYSTALS-Kyber algorithm, as outlined, leverages the difficulty of the LWE and ring-LWE problems to provide a secure key exchange mechanism resistant to attacks from classical and quantum computers. Its lattice-based structure enables efficient implementation, making it a viable candidate for PQ cryptography. As the threat of quantum computing advances, the CRYSTALS-Kyber algorithm presents a promising alternative to classical key exchange protocols, ensuring the continued security of digital communications in the quantum era.
The selection of CRYSTALS-Kyber over other post-quantum candidates was influenced by a combination of factors, including security strength and power consump-tion. CRYSTALS-Kyber offers strong security guaran-tees, making it resistant to known quantum and classical attacks. 50 Furthermore, the lower computational requirement of CRYSTALS-Kyber is suitable for battery-operated sensor nodes, which must optimize energy consumption to extend operational lifespan. 51
In addressing threats from quantum algorithms like Shor’s and Grover’s, CRYSTALS-Kyber benefits from the inherent complexity of the lattice problems on which it is based. Shor’s algorithm poses a significant threat to traditional cryptosystems, such as RSA and ECC, as it can efficiently factorize large integers and compute discrete logarithms. However, lattice-based problems, such as those used by CRYSTALS-Kyber, do not involve the number-theoretic structures vulnerable to Shor’s algorithm, rendering this quantum algorithm ineffective against it.
Grover’s algorithm provides a quadratic speedup in searching databases, potentially halving the time needed to crack cryptographic systems. However, the security of lattice-based systems like CRYSTALS-Kyber remains strong. These systems are based on solving difficult problems such as the shortest vector problem in high-dimensional lattices, which remains computationally intensive even considering Grover’s speedup. By using these complex lattice structures, CRYSTALS-Kyber upholds a high level of security against both current and future quantum algorithms, ensuring the protection of digital communications as quantum computing progresses.
Choosing the CRYSTALS-Kyber algorithm for WSNs was influenced by several key factors. The choice was driven by Kyber’s efficiency in computational requirements, which is critical for the limited resources typically available in WSNs. Kyber’s design allows for reduced memory use and quicker key generation and encapsulation, vital for devices with low processing power. Additionally, the robust security from Kyber’s use of the well-understood MLWE problem provides strong protection against quantum threats, important for securing communications in vulnerable network settings. Kyber also balances security with performance factors like energy use and speed better than other post-quantum options, making it well-suited for WSNs. This match of technical needs and practical demands justifies choosing Kyber’s KEM, underscoring its effectiveness and security benefits in these environments.
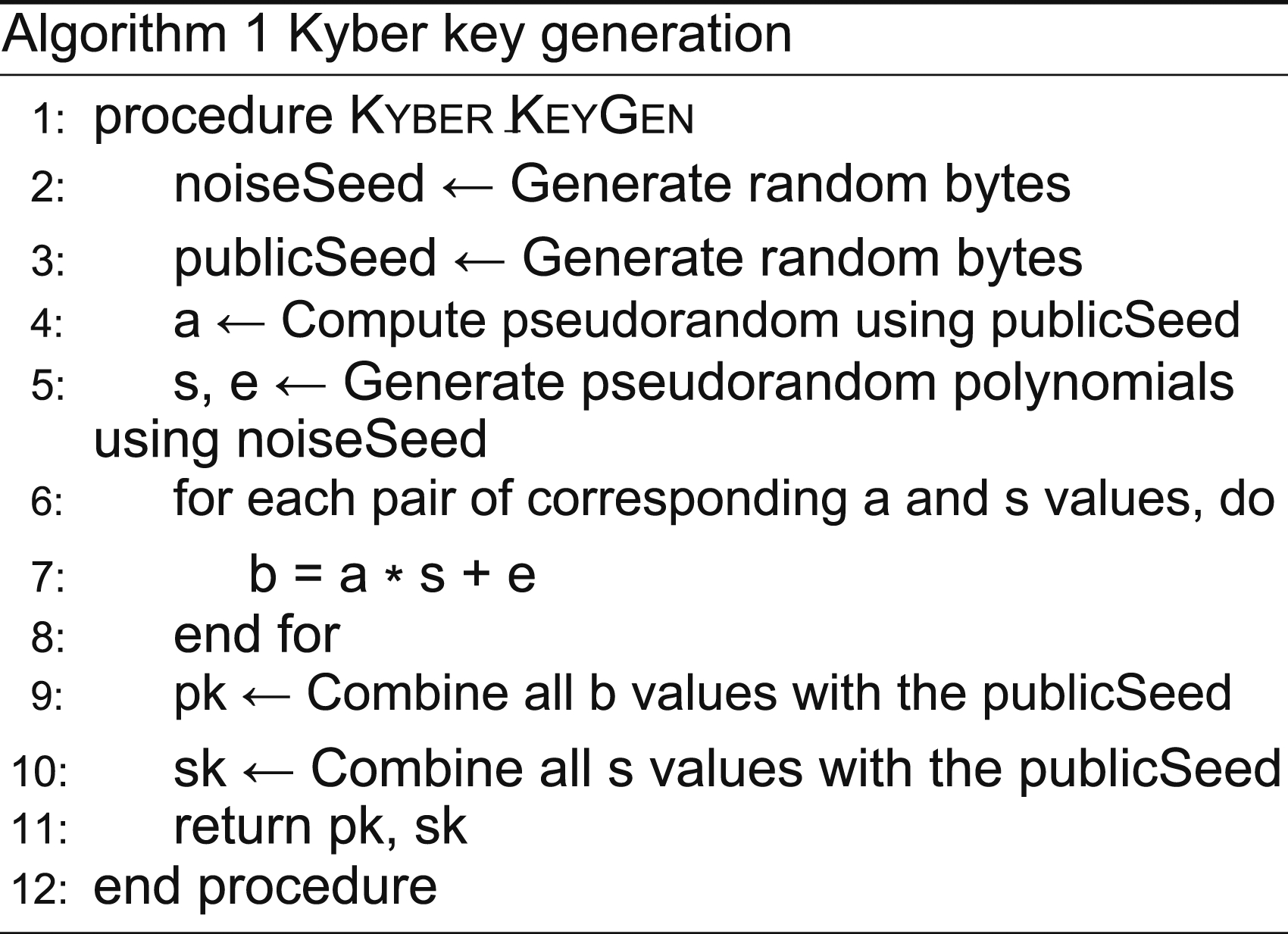
Key generation
Key generation in the CRYSTALS-Kyber algorithm, a critical stage in its encapsulation process, relies on advanced mathematics to ensure top-level security. The pseudocode is presented in Algorithm 1. This process begins with randomly producing public and noise seeds. These seeds form the backbone of the secret key and are instrumental in creating the public key. Using the public seed, a series of polynomials, denoted as a values, are created in the ring of integers of the number field using a pseudorandom number generator. These values represent the public lattice used to construct the public key. Concurrently, the noise seed aids in formulating a set of secret s values and noise e values (polynomials in the same ring). The public key, often represented as b, is created using the equation b = a ∗ s + e. This equation signifies the MLWE problem, and it is computationally challenging to uncover the secret s given a and b without knowledge of noise e. As such, public key
b can be safely disclosed without jeopardizing the security of private key s. In the final stage, the public key merges with the public seed to form the ultimate public key. The private key comprises secret s values and the public seed. In the CRYSTALS-Kyber algorithm, the keys are polynomial vectors , adding an extra layer of complexity and security. This process establishes corresponding pairs of public and private keys, and messages encrypted with the public key are only decryptable using the corresponding private key. By leveraging the MLWE problem, the CRYSTALS-Kyber algorithm ensures that cracking the cryptographic system is as challenging as solving the underlying mathematical problem, providing substantial security against potential quantum computer threats.
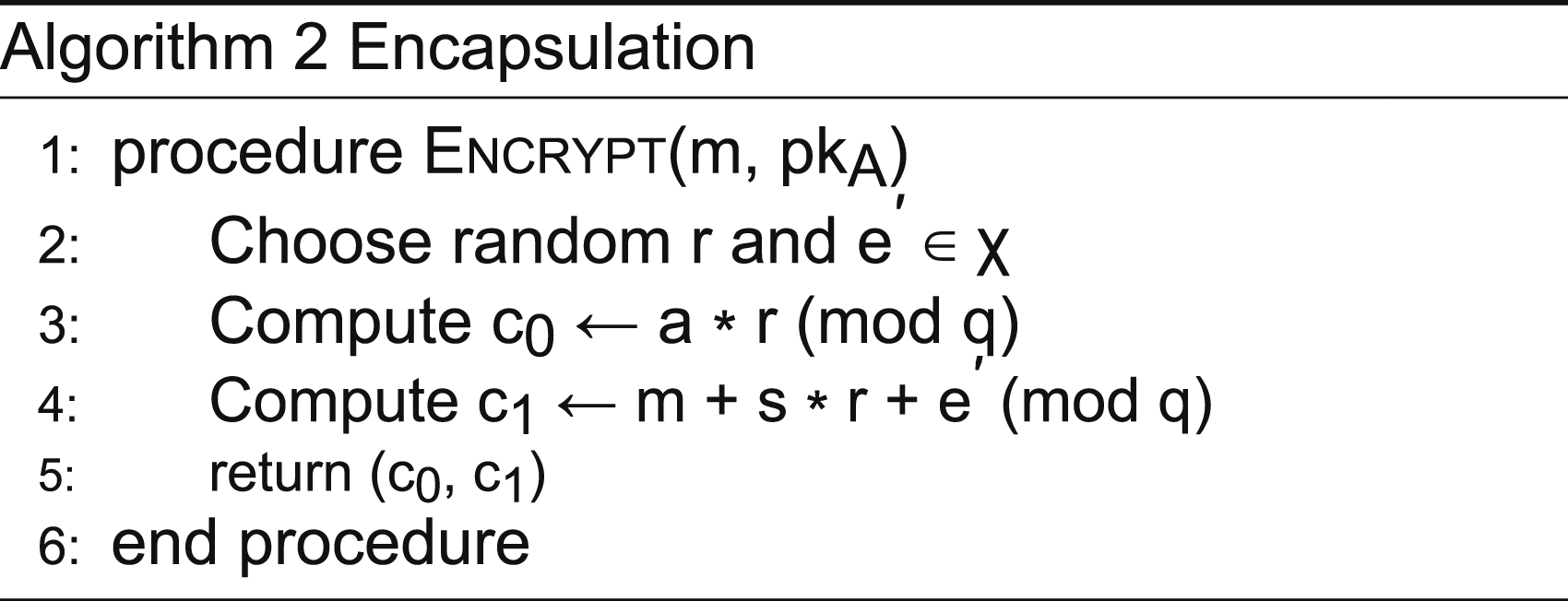
Encapsulation
Focusing on the encapsulation aspect of the CRYSTALS-Kyber algorithm (Algorithm 2), the Kyber encoding process take message m and public key pkA as inputs. The sender selects two random polynomials, r and e′, from error distribution χ for randomness and security. Subsequently, the ciphertext components c and ck are computed in the following manner. First, c is obtained by multiplying the random element a with the random polynomial r, modulo q. In comparison, ck is derived by adding message m to the product of secret key s and random polynomial r, modulo q, followed by adding random polynomial e′. The cipher text is returned as a tuple, (c, ck), where c is the challenge and ck is the shared key.
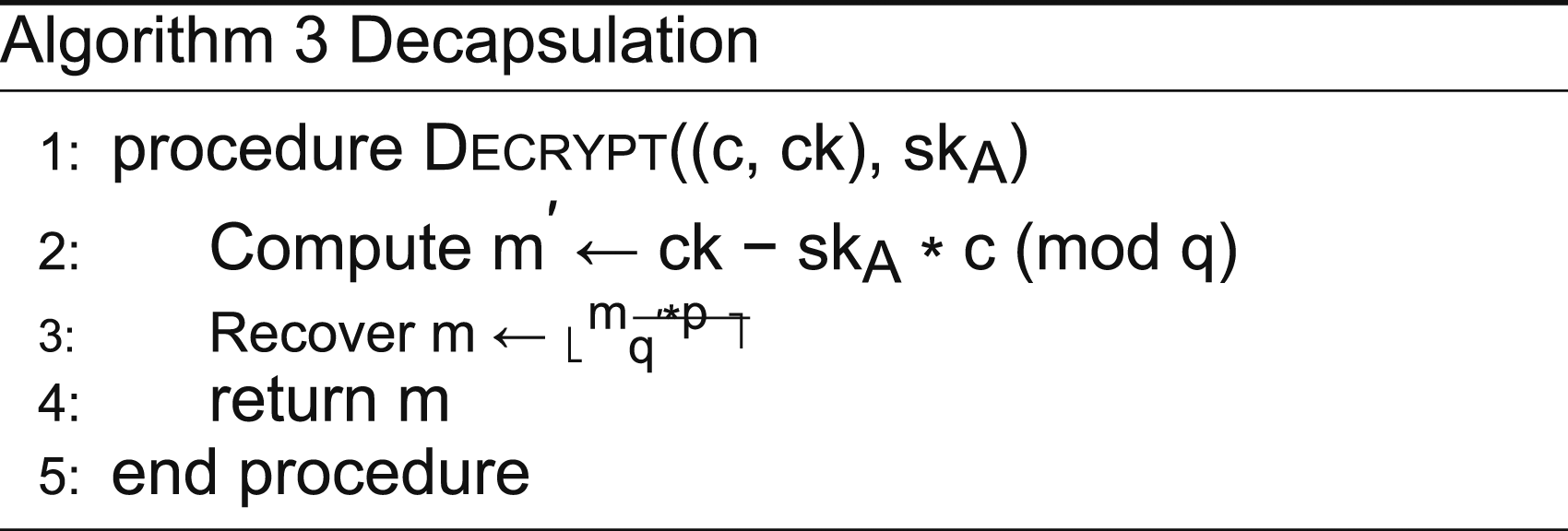
Decapsulation
Transitioning from encapsulation to decryption, we examine the decryption procedure (Algorithm 3). This process inputs the ciphertext (c0, c1) and secret key skA. The receiver’s first task is to compute m′ by subtracting the product of secret key skA and c0 from c1, modulo q. The receiver applies a rounding technique, approximating m′ to the nearest multiple of q/p, where p is a small prime number, to recover the original message m. Finally, the recovered message m is returned as the output.
Key exchange
The authors suggest three primary key exchange protocols for the CRYSTALS-Kyber algorithm. 49 In the first protocol, the anonymous key exchange protocol, neither party has prior knowledge of the other’s public keys, which is typically how initial communications commence in a public key infrastructure. In this case, both parties independently generate public-private key pairs and share their public keys over the network. This exchange is the foundational step in establishing secure communication. Despite the public and potentially insecure nature of the network, exchanging public keys enables secure communication due to the properties of the public-key cryptographic scheme.
Second, in the authenticated key exchange protocol, one party has preexisting knowledge of the other’s public key, which can arise if the public key is stored in a certificate or is available in a public key directory. When one party knows the public key of the other, they can initiate authenticated communication. This authenticated approach substantially reduces the risk of man-in-the-middle attacks because the public key of the communicating party is already verified.
Finally, the third protocol covers when both communi-cating parties know each other’s public keys. This scenario primarily occurs in systems where parties have previously communicated or within networks where the public keys are shared through a trustworthy third party or a secure public key infrastructure. When both parties have prior knowledge of each other’s public keys, they can mutually authenticate each other, creating a secure communication channel and significantly reducing the probability of impersonation or man-in-the-middle attacks.
Proposed protocol
We introduce PQ-LEACH, a wireless communication secure protocol for WSNs based on the LEACH protocol. The QS -LEACH is designed to address the specific constraints and security needs of WSNs. It leverages PQ secure cryptography to protect against PQ attacks. In addition, the protocol introduces a key update feature to isolate and address risks from malicious or compromised nodes efficiently, allowing the protocol to update the keys at regular intervals for all nodes. This approach helps mitigate several attacks, such as reply and man-in-the-middle attacks, improving the security of the WSN.
In the design of PQ-LEACH, it is assumed that the number of nodes n is known by the sink node (SN) and that all nodes are continuously listening during the initialization phase. In addition, the number of nodes is assumed to be fixed such that no additional nodes could join the network. Further, the nodes have a pre generated CRYSTALS-Kyber public and private key pair. This key must be made available to the nodes, such that the nodes know the private key while the SN knows the public key.
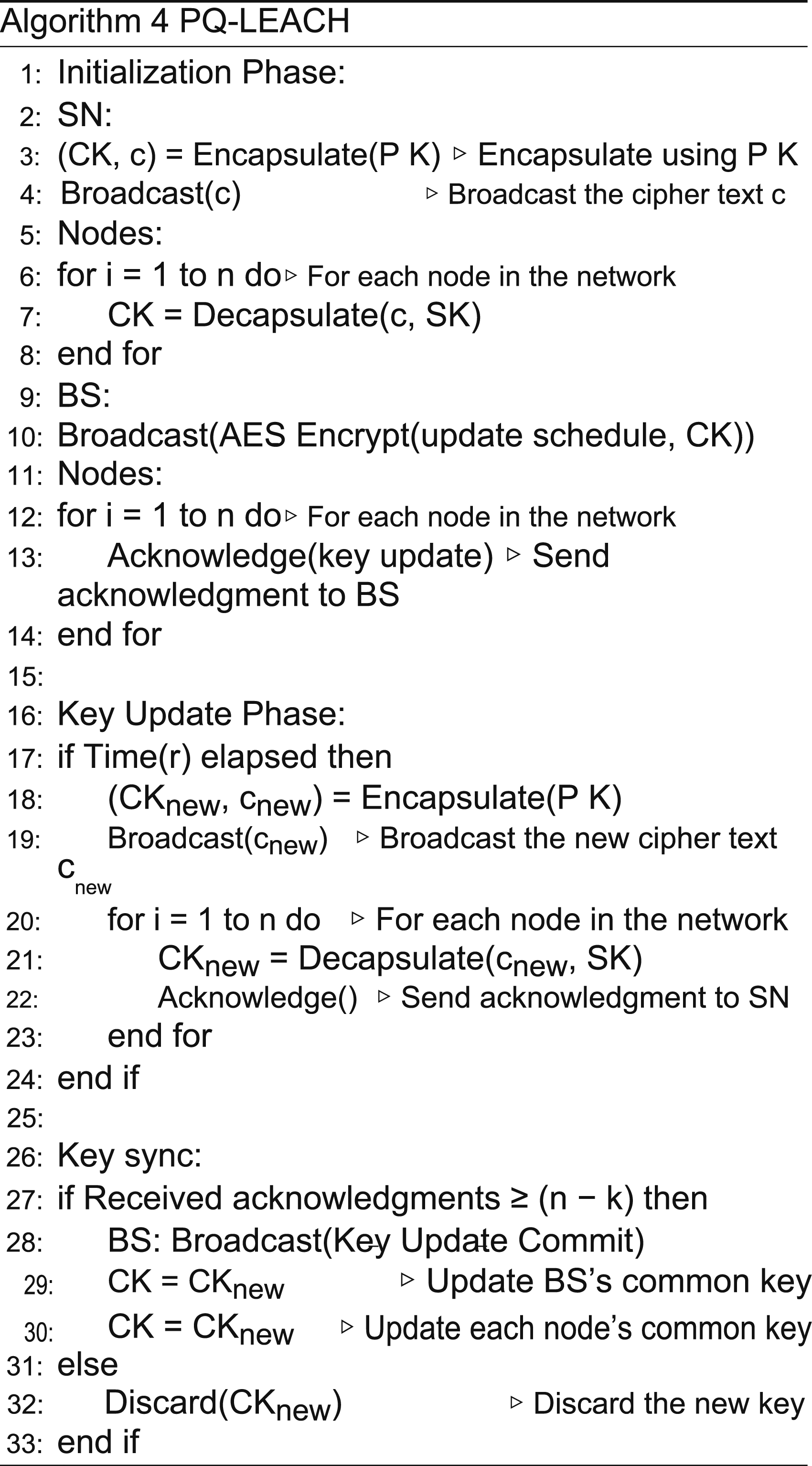
The protocol consists of two phases: initialization and key update (see Algorithm 4). The protocol begins with the initialization phase, which is mandatory for establishing a secure communication link between the SN and nodes. The protocol uses the authenticated key exchange protocol, where one of the parties has existing knowledge of the other’s public key. In this phase, a secure communication link is established between the SN and each node. The communication is secured using CRYSTALS-Kyber’s key exchange mechanism, in which a common key is generated for all nodes. The communication between all nodes is secured using Advanced Encryption Standard (AES) and the common key. Additionally, any key exchange message that is transmitted is preappended with a hash signature using SHA256. 52 This approach allows the receiver to verify the integrity and authenticity of the received message.
Initialization Phase We explain the initialization phase process, where the main objective is to create a secure link using CRYSTALS-Kyber’s key exchange mechanism.
The authenticated key exchange protocol is applied in PQ-LEACH; thus, a CRYSTALS-Kyber key pair is pregenerated (P K, SK). The secret key SK is included with every node, whereas the SN must know the public key P K. This method allows the SN to securely transmit messages to the nodes. In the beginning, the SN generates a shared secret key using the CRYSTALS-Kyber key encapsulation method. The encapsulation method generates a common secret key CK and a cipher text c:
The SN broadcasts the cipher text c to all nodes. Each node that receives the message uses Kyber’s decapsulate method to decrypt the cipher text c using its private key P K and obtain the common secret key CK. This results in all nodes sharing a common key, which is used for securely encrypting subsequent communication.
In the next step, the SN must securely transmit the key update schedule to all nodes. Therefore, the SN broadcasts the node update schedule encrypted using AES and the shared secret key CK. Afterward , the nodes must confirm their receipt of the key update schedule from the SN. Thus, the nodes transmit an acknowledgment message to the SN encrypted using AES and the shared secret key CK. The acknowledgment message is sent during the node’s defined schedule and includes its identity. Consequently, the SN processes each received message after decrypting it using AES.
The initialization phase is complete when all nodes have successfully acknowledged the receipt of the key update schedule. At the end of this phase, the SN transmits a notification message to all nodes, informing them of the termination of the initialization phase. Consequently, all nodes begin the normal operation of the LEACH protocol with the addition of securing communication using AES and the shared key CK.
Key Update Phase In the key update phase, the common secure key of the nodes is updated at regular intervals r. When time r has elapsed, the BS generates a new common key CT and its cipher text cnew using the following CRYSTALS-Kyber key encapsulate function:
Afterward, the SN distributes the new cipher text cnew through a broadcast message to all nodes, which can only be decrypted by existing nodes using the CRYSTALS-Kyber decapsulation method. Accordingly, the nodes obtain the new updated shared common key CKnew, replacing the existing shared common key CK.
The SN maintains knowledge of the number of off-line nodes k, which is initialized to zero. Updating the keys for the SN and all nodes requires receiving at least n − k acknowledgments from active nodes. This step is required to verify that all keys are synchronously updated. Upon confirming the acknowledgment from all nodes, the BS sends a key commit notification message to all n − k nodes and updates its shared common key CK as follows:
Accordingly, all nodes update their keys upon receipt of the key update notification message as follows:
Otherwise, when less than n − k acknowledgments are received, the current key update interval is marked as failed. When y consecutive key update interval fails, the SN increments k by one. For any failed key update interval, the keys are discarded for both the SN and the nodes.
The key update feature of PQ-LEACH ensures that all nodes are updated including those with limited resources that might enter sleep state. All nodes are provided with the key update schedule before the initialization stage. The key update schedule describes the time interval for the key update phase. Regardless of whether the nodes are active or in a sleep state, the nodes must update their keys to keep them in sync with other nodes. Nodes that became sleep will be active for the duration of the key update interval and conduct the key update phase. Therefore, it is guaranteed that all nodes’ keys are updated.
Informal security analysis of the quantum-secure LEACH
The WSN presents unique challenges due to its open commu-nication environment, making data transmission more prone to eavesdropping and tampering. Attackers may alter the message content , resulting in the BS receiving and process-ing incorrect information, subsequently wasting significant electrical power in handling these compromised messages. This section rigorously assesses the cryptographic robustness of PQ-LEACH in a WSN environment. Specifically, we focus on ensuring confidentiality, authenticity, and integrity of data transmission within the network.
Confidentiality
Protecting data confidentiality is highly crucial in the current digital age, especially for WSNs, where the communication medium is inherently susceptible to eavesdropping. The proposed PQ-LEACH protocol employs the CRYSTALS-Kyber key encapsulation mechanism for cryptographic operations. In this scheme, the BS generates a public-private key pair for communication between the nodes and BS. The protocol uses the authenticated key exchange protocol; thus, the BS has preexisting knowledge of the nodes’ public key P KNS. Therefore, the BS can use the key P KNS to generate an encrypted version of the common secret c using the encapsulation method. The cipher text c can be decrypted using only the private key of the nodes P KNS, ensuring the confidentiality of the shared common key CK. Likewise, any further communication is secured using AES and the shared common key CK. Therefore, both the BS and the nodes established two-way secure communication, ensuring the confidentiality of communicated messages.
The key update phase employed by PQ-LEACH further fortifies this aspect, which periodically updates keys for all nodes. The key update feature adds another layer of security, making it computationally infeasible for an attacker, even with quantum capabilities, to decrypt intercepted messages within a practical period. This phase uses the existing private-public key pair to generate a new shared common key. It starts with the BS generating a new common shared key. The cipher text of the common shared secret is broadcast to all nodes, and the broadcast cipher text can only be decrypted using the private key of the nodes, ensuring the confidentiality of updated keys and further communication.
Furthermore, the key update feature of PQ-LEACH protects the network against replay attacks, where a malicious node may attempt to tamper with the obtained data by repeating the existing transmitted messages. Thus, it is challenging for attackers to determine which messages are encrypted with updated keys. Thus, messages that cannot be decrypted correctly are simply discarded.
Authentication
The PQ-LEACH protocol uses the authenticated key exchange protocol where the node is already preauthenti-cated by providing the BS with the node’s public key P KNS. Thus, when nodes receive a message, they attempt to decap-sulate it using their existing private key SKNS. The nodes can determine whether the decapsulation was successful. If it was successful, it implies that the message was transmitted from an authentic source. Thus, they process the received information and obtain the shared secret key accordingly. Otherwise, they discard any other message transmitted by an unauthenticated source.
For any normal communication with the BS or nodes, any received message is decrypted using AES and the key CK. A successful decryption is checked using the appended hash value. If successful, it implies that the message originated from an authentic source. Any other message that is not decrypted successfully is discarded.
Integrity
Both the BS and nodes must receive messages without any alterations. A SHA256 hash is appended to the messages to protect against message tampering, preventing potential attackers from maliciously tampering with messages. The BS and nodes can identify any tampered messages, and the tampered messages are thrown away.
Another potential attack is the replay attack, in which an attacker stores intercepted messages and then later retransmits them. This attack can tamper with the collected data from the nodes. However, this attack is mitigated through the key update feature of the PQ-LEACH protocol. Therefore, the BS only receives messages encrypted with the recently updated keys, making it difficult for attackers to anticipate which messages use the updated keys.
Performance analysis
Simulation parameters for WSN energy consumption.

The simulation runs a simulated WSN over a predefined number of rounds, typically sufficient to observe the energy depletion in nodes. The number of rounds is set to 2500 rounds which is enough for the purpose of simulating energy consumption. In each round, nodes either act as cluster heads or member nodes, and energy consumption for data transmission, receiving, aggregation, and encryption is calculated. The PQ-LEACH protocol introduces additional energy consumption due to the AES encryption and the cryptographic operations involved in the key exchange and key update phase. Since modern IoT hardware implement AES in hardware, the energy requirement for cryptographic operation is negligible.53,54 Thus, the performance overhead is set to 10%.
The simulation implements both the standard LEACH protocol and the PQ-LEACH protocol. The standard LEACH protocol serves as the baseline, where no additional security measures are implemented. The PQ-LEACH protocol implements security measures to protect communication that include encryption and updating of keys. The primary metric for evaluation is the number of dead nodes over time. The secondary metric is the total number of packets on the network.
The purpose of the simulation is to quantify the impact of the security measures implemented in PQ-LEACH on the energy consumption of the WSN. By comparing the energy consumption profiles of the standard LEACH protocol and PQ-LEACH, we aim to provide insights into the trade-off between enhanced security and energy efficiency in WSNs. This analysis is crucial for understanding the feasibility and practicality of deploying PQ-LEACH in real-world WSN applications.
Results and discussion
In our comprehensive simulation study, we analyzed and compared the performance of both the LEACH and PQ-LEACH protocols. This analysis was based on two critical metrics: the number of dead nodes and the total number of packets transmitted. We derived these metrics from an average of 100 simulation runs to ensure statistical reliability.
Figure 1 presents the results concerning the number of dead nodes. The horizontal axis in this figure delineates the progression of simulation rounds, while the vertical axis quantifies the cumulative count of dead nodes over time. A notable observation is the parallel growth in the number of dead nodes for both protocols up to approximately round 1250. Post this threshold, a marked divergence is observed; the PQ-LEACH protocol exhibits a more rapid increase in dead nodes. This accelerated rate of node depletion in PQ-LEACH can be attributed to its higher energy demands. Remarkably, by round 2200, the PQ-LEACH network experiences a complete shutdown, indicated by the count of dead nodes reaching 200. In contrast, the LEACH protocol maintains operational nodes beyond round 2500, highlighting its relatively enhanced endurance. Number of dead nodes over time.
Further insights are garnered from Figure 2, which illustrates the total number of packets sent across the network. Here, the horizontal axis represents the number of nodes, while the vertical axis tracks the count of transmitted packets. Intriguingly, the packet transmission trends for both protocols align closely until around round 2000. Beyond this point, the PQ-LEACH protocol shows a decline in packet transmission, directly correlating with its higher incidence of node mortality compared to the LEACH protocol. Total number of packets sent over time.
The network topology post-simulation is depicted in Figure 3. In this representation, active nodes are symbolized by blue dots, whereas red dots signify dead nodes. The left and right sections of the figure correspond to the LEACH and PQ-LEACH protocols, respectively. It is evident that, following the conclusion of the simulation, the PQ-LEACH network does not retain any active nodes, unlike its LEACH counterpart. Network map showing the random placement of nodes over a 300 × 300 m area.
By conducting a key generation process for each methodology, we examined the performance of the CRYSTALS-Kyber algorithm and ECC, capturing the results in Figure 4. Each graph segment illustrates a combination of an encryption method and the selected key size. The results indicate that ECC requires more cycles than the CRYSTALS-Kyber algorithm across all tested strength levels. For example, at the lowest strength level, the computing needs for the CRYSTALS-Kyber algorithm were drastically lower—24 times less compared to ECC. Moreover, this performance gap widened with increasing strength levels, reaching 35 and 45 times less computing at the following two levels. Comparing the number of cycles required for key generation for ECC and CRYSTALS-Kyber.
These findings collectively underscore the impact of integrating an additional security layer in the PQ-LEACH protocol. While it enhances security, there is a noticeable compromise on network longevity. The simulation demonstrates that the inclusion of enhanced security measures in PQ-LEACH shortens the network lifespan by less than 10% compared to the standard LEACH protocol. The trade-off between security and longevity is a critical consideration in the deployment of WSNs. In many WSNs applications, security typically takes precedence over energy efficiency due to the significant consequences of network compromise.55,56 Moreover, the implementation of these networks is relatively straightforward, as it is based on the LEACH protocol, which is currently utilized in various real-world applications.
Conclusions
In summary, this research emphasizes the essential shift toward encryption methods that are safe against quantum computing, with the CRYSTALS-Kyber encryption approach as a key example. We introduced PQ-LEACH, a new, more secure communication method for WSN that is designed to withstand a variety of attacks, including those from quantum computers. This method not only secures communication within WSNs but also regularly updates security keys, adding an extra layer of protection, particularly against repeated and sophisticated attacks.
Our simulation results reveal that while PQ-LEACH significantly improves security, it also increases energy usage slightly. These results show that the PQ-LEACH protocol greatly increases security at the cost of a slight decrease in the lifetime of the network. This balance between enhanced security and network lifespan is a crucial factor to consider in future WSN deployments.
In future versions of PQ-LEACH, we aim to adapt the protocol to dynamically accommodate a changing number of nodes. This flexibility is crucial for the protocol to be applicable across a wider range of WSN applications, such as smart cities, disaster recovery scenarios, and industrial environments. Dynamic node management allow networks to scale as needed, enhancing their utility and deployment efficiency. Allowing for a dynamic number of nodes introduces additional security vulnerabilities. For instance, the risk of imposter nodes infiltrating the network could lead to severe security breaches of the WSN system, including eavesdropping and denial of service attacks. To address these challenges, the next iteration of PQ-LEACH should incorporate an authentication mechanism to rigorously verify new nodes before they join the network.
Overall, this study not only highlights the growing need for advanced encryption techniques to prepare for quantum computing threats but also paves the way for further research in this area. It encourages a shift in thinking about encryption strategies to ensure the security and effectiveness of WSNs in the rapidly changing world of technology. A future direction of the work is to enhance the key update mechanism to allow for dynamic number of nodes. Also, comparing Kyber with other post-quantum algorithm is another direction.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Princess Nourah bint Abdulrahman University Researchers Supporting Project number (PNURSP2024R412), Princess Nourah bint Abdulrahman University, Riyadh, Saudi Arabia.
