Abstract
Businesses are expected by the society to operate sustainably nowadays. However, companies are having a hard time to make business decisions to achieve both business sustainability and environmental sustainability, especially when such decisions involve numerous uncertainties. Making the wrong decision can result in damaging reputation in the least and going out of business in the worst. In this case study, we consider companies providing service parts maintenance, which have a great potential to bring positive impacts to the environment by refurbishing and reusing the replaced items. However, these companies also need to weight against cost effectiveness of doing so to maintain business sustainability. Informed decision making, meanwhile, is achievable with the use of the latest technologies. Here, we present the integration of Internet-of-Things to collect and provide real-time data for business analysis, such that companies can decide effectively which item(s) can be refurbished economically. We show that by doing so, uncertainties concerning the cost of refurbishment can be reduced, such that service parts operators can achieve both business sustainability and environmental sustainability.
Introduction
Sustainability has become an important issue to business operation in recent years,1,2 no matter the sustainability towards the environment or to the business itself. A particular sector that faces such an issue is the systems maintenance companies and its associated reverse supply chain.3,4 In such a business, parts replaced from the customers could have a great potential to be refurbished and reused for environmental sustainability. The public is also expecting such companies to take up their social responsibility.
However, it is non-trivial for systems maintenance companies to decide if a replaced part should be refurbished and reused for business sustainability due to various costs incurred during the refurbishment process and the uncertainties therein. The services of part replacement and collection are delivered through a highly integrated process. Making the wrong decision in the process could harm either the business sustainability, the environmental sustainability, or both. Business intelligence systems could assist the decision-making process and help the companies make sustainable decisions, given that up-to-date information, if not the real-time one, such as inventory, failure rate, repair rate, and demand, is made available and accessible by these business intelligence systems.
To provide more up-to-date information to business intelligence systems, items need to be easily identified and verified. Fortunately, modern information technologies have enabled such capabilities. For instance, RFID5,6 is one of the promising technologies to provide such real-time information collection and sharing by enabling the RFID-tagged object to be connected and identified in the cloud, and hence, becoming part of the Internet-of-Things (IoT),7,8 which would be beneficial to supply chain management,9,10,11 sustainable supply chains,12,13 and reverse supply chain management.14,15 As such, RFID is one essential building block for both business sustainability and environmental sustainability.
Although there are cases in the literature which demonstrate the use of RFID or IoT in forward supply chain management,16,17 the application of IoT in the reverse supply chain process is under study. In this case study, we use an online mobile application development platform by MIT 18 to develop mobile applications with IoT functions. The case study is motivated by the service parts operational challenges, such as decentralized information in scattered systems, non-standardized process flow of part replacement and collection, fake parts, etc. Based on the data provided by a leading electronic product company in Hong Kong, a mobile app is developed to assist the work of an operator who is tasked with completing the part replacement orders in the company and is involved in both forward and reverse supply chain management. More details of the mobile application are described in later section.
The organization of this paper is as follows. We briefly describe the key concepts of reverse supply chain and RFID and its security issues in Section II. We describe the key lessons on the mobile application development which makes use of RFID technology to facilitate the reverse supply chain in Section III. We then present the implications for the practical use of the mobile application in Section IV. We conclude in Section V.
Key Concepts
In this section, we describe the key concepts of supply chain management, reverse supply chain, and RFID and its security issues.
Supply Chain Management and Reverse Supply Chain
Supply chain management, and in particular, inventory management, is an important issue faced by many businesses and is well studied in the literature.19–22 Deciding when to order from the supplier has a great impact to the running of the business—ordering too early or too many and resulting in excess inventory would increase storage costs and cash-flow shortfall due to having too much money tied up in the inventory, ordering too late or too few and resulting in low inventory would increase the lost in business due to missed sales, unsatisfied customers, or disrupted production process. Luckily, advances in technology, such as barcode and RFID, have enabled the collection of up-to-date information to facilitate such decision making.23,24
When a company decides to restock, ordering from which source—new or refurbished one, has both economic and environmental concerns. Using refurbished items improves environmental sustainability, but the company also needs to consider its cost to maintain business sustainability. This is especially the case for service parts maintenance companies, as they collect a large amount of replaced items which could have a great potential for refurbishment, redeployment and reducing the demand of new items.
As we compare the costs of new items and the refurbished ones, the cost of the new ones can be more readily estimated—the item itself specified by the provider and that for its delivery. The cost of refurbished items, however, is trickier to estimate, especially when the refurbishment is done in-house instead of a third-party who may provide the refurbished items with a price. For instance, the cost of refurbishing items includes the cost of setting up and running a repair center, logistics of the items, success repair rate of failed items, and the failure rate of refurbished items; other factors that also affect the decision include the demand of the items in the future and the current inventory. These factors are not readily available unless individual item is identified and tracked throughout the forward and reverse supply chains, which is enabled by recent advances in wireless technology. For instance, the Internet-of-Things paradigm has been found to be useful to facilitate the reverse supply chain. 14
As a result, we develop a mobile application which implements part of the forward and reverse supply chains to demonstrate the potential of RFID in improving business and environmental sustainability.
RFID and related Security Issues
RFID5,6 is a wireless Automatic Identification and Data Capture (AIDC) technology which allows the collection and connection of objects (or their associated information) to the cloud without contact or line-of-sight access. Of course, simply attaching an RFID tag to an object does not make it part of the Internet-of-Things (IoT)7,8—we also need to have the cyber counterpart of the object in a backend server, and a network-connected RFID reader as the bridge connecting the object and the server (cyber world). Such a set up forms part of the cloud computing infrastructure, which is vital to enterprises nowadays. 25 Indeed, IoT has become an important enabling technology for better monitoring and resource utilization in many sectors, including healthcare26,27 and agriculture.28,29
Despite its usefulness, RFID technology faces numerous security and privacy issues.30,31 For instance, low-cost re-writable RFID tags without any computational abilities cannot prevent tag cloning, 32 which can result in having genuine parts being substituted by counterfeit ones. To counter such cloning attacks, the RFID tags need to have the capability to generate random numbers and perform (keyed) hash function or Cyclic Redundancy Code (CRC) for the authentication purpose, as suggested in various RFID tag authentication schemes.33–36 However, due to budget and limitations of NFC functions provided in MIT App Inventor 2, we do not implement such authentication schemes in our mobile app. Instead, we use asymmetric key encryption (RSA with random padding 37 ) to encrypt the serial number of the RFID tag as a preliminary protection mechanism.
Key Lessons
In this section, we present the details of the implementation of the mobile application that facilitates the collection of information in both the forward and the reverse supply chains. This IT solution is used in a case study on a leading electronic product company in Hong Kong. According to the company’s operations team, over 200 stocking units could be reused to avoid material waste and the process flow of return parts for service parts management could be enhanced if the forward logistics of parts replacement and reverse logistics of parts collection could be managed effectively.
The case study has been illustrated in the class of students for understanding the management of forward and reverse supply chain processes by adopting the latest mobile application of IoT without the requirement of computer programming background knowledge. The mobile application development environment, the design of database schema, and the communication between information stored on NFC RFID Tags and the mobile applications are discussed as follows.
Development Environment
The mobile application is developed using MIT App Inventor 2. 18 MIT App Inventor 2 is a web-based mobile application development environment, originally provided by Google, and now maintained by the Massachusetts Institute of Technology (MIT). The environment provides an easy-to-use interface and numerous tutorials are available online, allowing students without much programming background to develop mobile applications. The developed mobile applications can be downloaded, installed, and run on smart phones with Android or iOS.
Various extensions have also been developed and provided by the community to enhance the functions of the mobile applications developed under MIT App Inventor 2. In particular, two of them are used in our development, 1) TaifunTools (com.puravidaapps.TaifunTools.aix)
The function of SHA256 computation is used. 2) AsymmetricCryptography (com.sunny.AsymmetricCryptography.aix)
The function of asymmetric key encryption/decryption is used.
More details of these two extensions are provided in Section III.E.
Database for Mobile Application
To implement the functions of the app, we need to have a database to store the information of parts, parts inventory, and service orders. App Inventor supports different ways to store data, such as file, CloudDB and TinyDB. However, these approaches either do not support sharing of data between instances on different smart phones or require setting up the database from scratch. Meanwhile, Google Sheets is a cloud-based spreadsheet application, and its stored data can be accessed or manipulated through API calls directly or Apps Script codes indirectly, very much similar to a database without much setup involvement from the users. As a result, we choose to use Google Sheets as the database to store the data to be accessed in our mobile app for demonstration purpose.
There are three ways for the mobile app to access data on Google Sheets. They are listed as follows.
1) Export the Spreadsheet as csv
We can export the data from Google Sheets as a csv file and retrieve the csv file directly in the mobile app. Range (and only range) may be specified to retrieve part of the sheet only.
In this way, no program or scripting language need to be written to retrieve the data. However, processing of the data needs to be done in the app. Also, the amount of data transferred between the database (Google Sheets) and the app could be huge, resulting in high data usage on the smart phone (when it needs to retrieve the data through cellular data network).
2) Export the Spreadsheet as csv with sql-like query
We can also export the data from Google Sheets as a csv file using an SQL-like query. We can retrieve data that satisfy certain criteria from Google Sheets without performing such processing in the mobile app. This allows part of the processing be done by Google Sheets and can reduce the amount of data that needs to be transferred from Google Sheets to the mobile app.
The following link shows the query language that can be used to retrieve data from Google Sheets: https://developers.google.com/chart/interactive/docs/querylanguage
However, notice that not all functions listed on the webpage are available—for instance, max is found to be not working with Google Sheets.
Hint: One may test if the desired function works with Google Sheets by running a formatted query string in a web browser.
3) Apps Script
We can use Apps Script to access and manipulate (update and/or retrieve) the data. We can write scripts (similar to program codes) to manipulate the data stored on Google Sheets and execute them through calling the corresponding scripts from the mobile app.
Operations that update the data on Google Sheets, such as data addition, replacement, and removal, need to be done in this way.
Hint: One may test the Apps Script codes with a web browser using a formatted URL string calling the Apps Script.
Database Schema Design
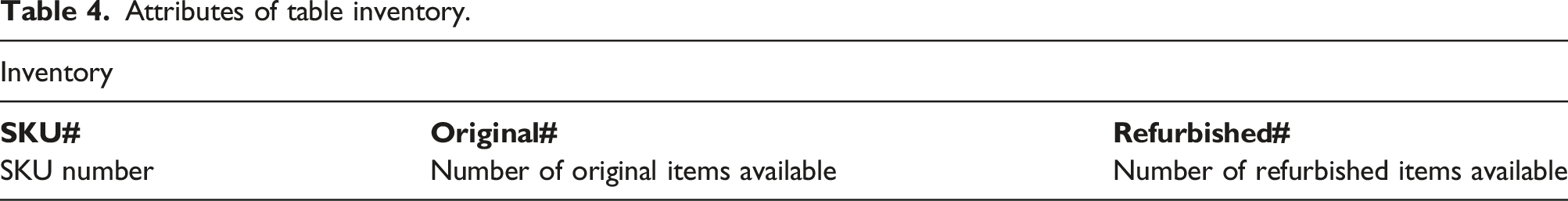
The Google Sheets contain the following sheets, each corresponds to a table in a relational database.
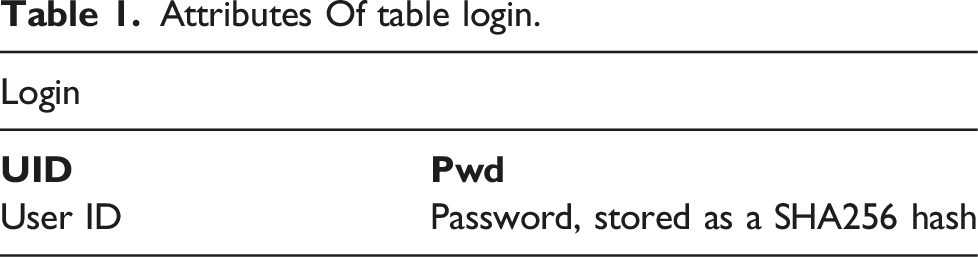
The password is stored as a hash value only for security purposes.
Notice that the “reusable” field, specifying if a replaced item should be refurbished, will be updated by a business intelligence system from time to time depending on the profitability of doing so.
Public key and private key are the key pair for tag ID encryption and decryption. In theory, we assume that an RFID tag is encrypted by the manufacturer, and hence, the private key should be kept by the manufacturer without disclosure, i.e., uploading to the database. However, since we also act as the manufacturer in this case study to prepare the NFC tags (using another app), we also keep the private key in the Google Sheets.
Attributes of table orders-pending.

Attributes of table orders-completed.

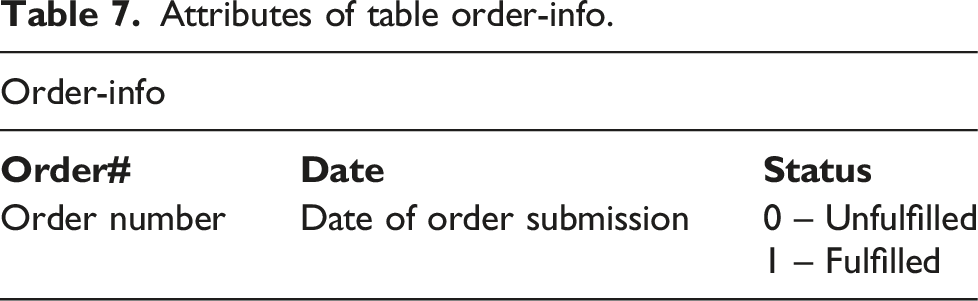
Attributes of table order-info.
Information stored on NFC RFID Tag
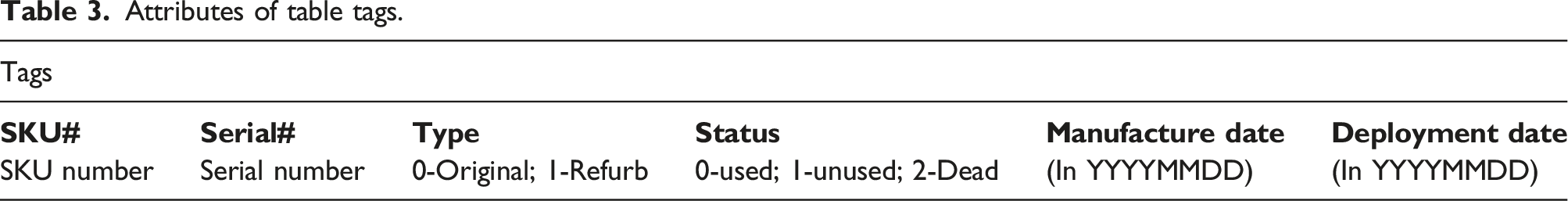
In this case study, we assume that each service part item is coupled with an NFC RFID tag, and hence, each item can be represented by the corresponding RFID tag, which stores various information about the item as follows,
SKU number; encrypted serial number; item type -original or refurb; manufacture date (in YYYYMMDD); deployment date (in YYYYMMDD)
An example is as follows, SKU1;XXX;0;20211231;20220504 which indicates that the item (tag) is an original item of SKU 1 with encrypted serial number XXX, manufactured on 31st Dec, 2021, and deployed on fourth May, 2022. We assume that the manufacturer prepares the tags with the SKU number, the encrypted serial number, and the manufacture date, while the service provider may update the type of the item from original to refurb and the deployment date.
Main Features of the Order Service App
The mobile application assists the work of the operator who is tasked with completing the service parts replacement orders. To streamline the work of the operator for parts replacement, the mobile app solution facilitates the work on both the forward and reverse logistics. In particular, the operator uses the app to select the replacement order to be fulfilled, collect the corresponding service parts, authenticate the replaced service parts, and decide if the replaced service parts are to be refurbished or not.
Functions of the Order Service App
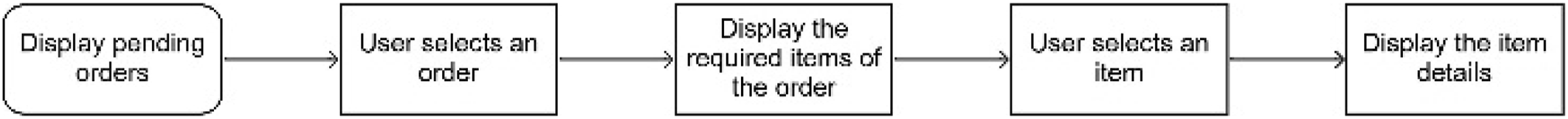
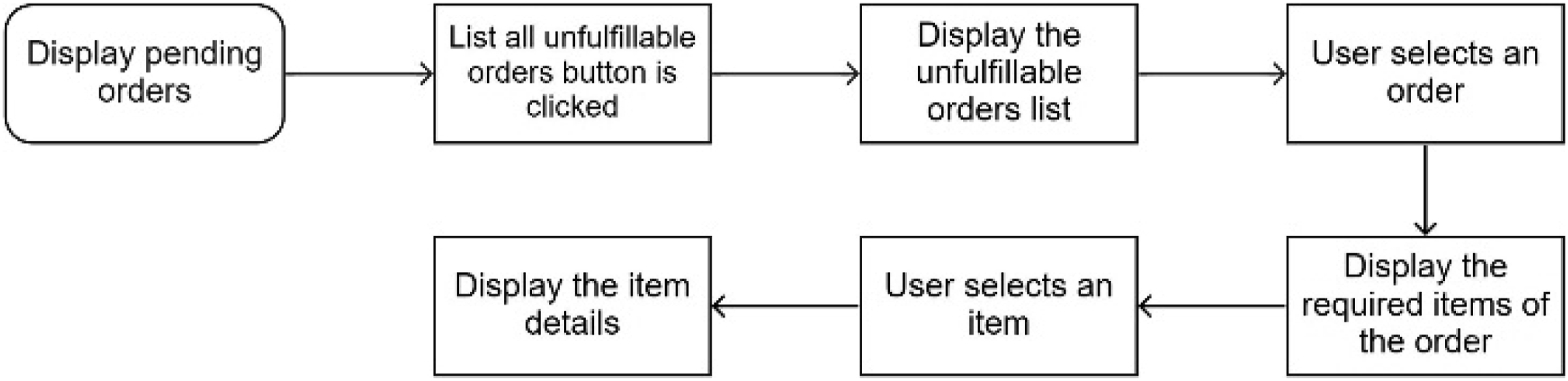
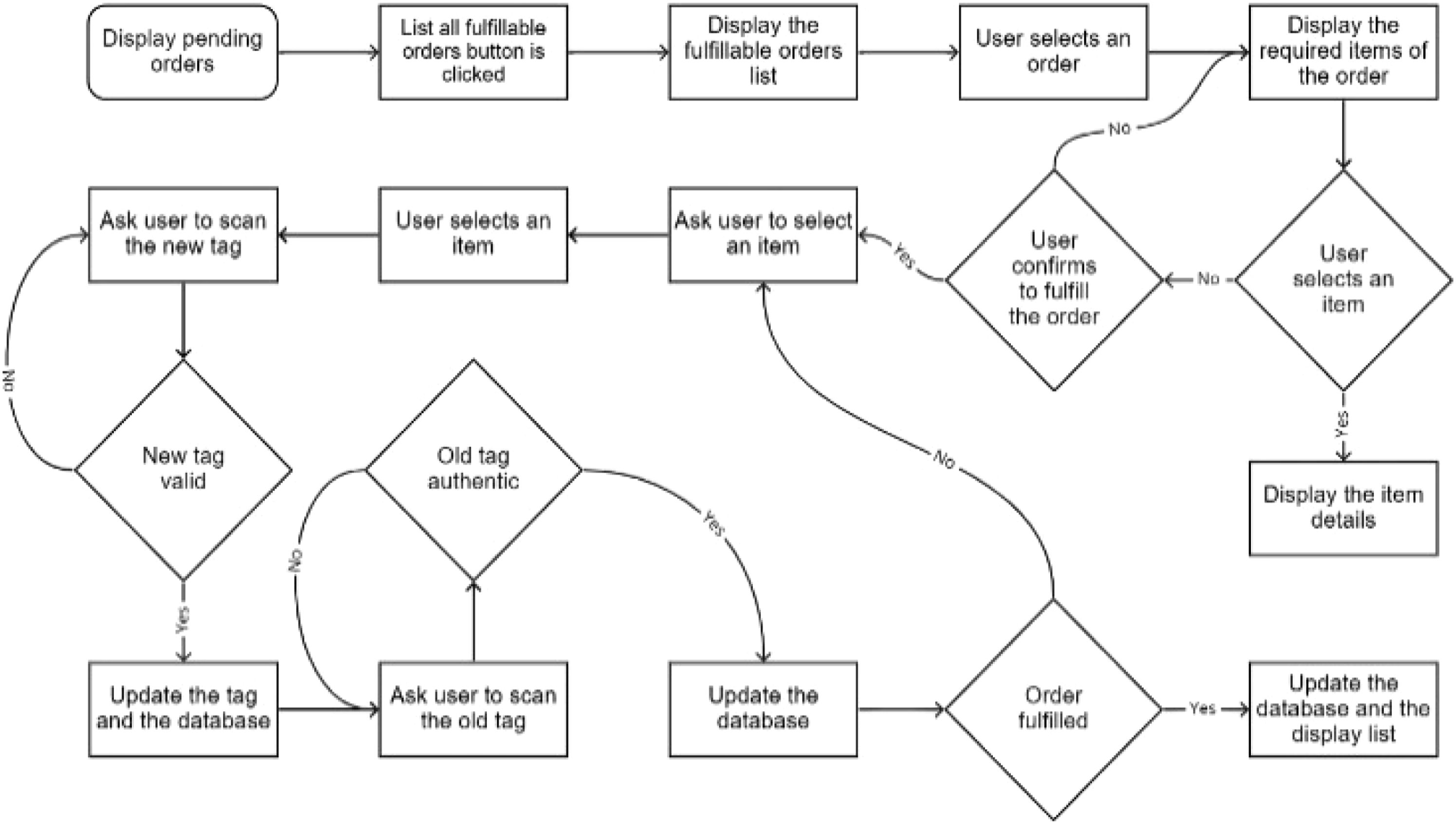
To complete an order, the operator must follow the steps showed on the mobile app. Step 1) The operator first logins to the mobile app. After login, a parts replacement order list will be displayed, which shows the replacement orders that can be fulfilled with the current inventory. (Figures 1 and 2) Step 2) The operator then selects an order from the list, and the app will show the order details at the bottom of the screen, such as the number of items for each part in the order. (Figure 3) Step 3) The operator follows the order and collects the required service parts from the warehouse (Figure 4). Step 4) When the operator arrives on site and begins the replacement work, he/she uses the app to complete the order – the operator scans the RFID tag of the replacing item and that of the corresponding replaced item one-by-one using the app to ensure that the replacing item and the replaced item are of the same type as the one in the replacement order. As the replaced item is scanned, the app also checks its authenticity and shows to the operator if the replaced item should be returned for refurbishment or not. (Figure 5) Step 5) Once all the items of the replacement order have been replaced and scanned successfully, the order is completed, and the app prompts the operator of its completion together with the corresponding updates in the database. The app then returns to the main interface again with the completed order removed from the parts replacement order list. Flow chart for user login. Flow chart for displaying all pending orders. Flow chart for displaying details of a pending orders. Flow chart for displaying details of an unfulfillable pending order. Flow chart to fulfill a fulfillable pending orders.


Extensions used in the Order Service App
Two extensions are used in the order service app,
1) TaifunTools (com.puravidaapps.TaifunTools.aix)
To improve security, one-way hash value of passwords instead of their raw values are stored in the database as a standard practice. Hence, this extension is used to compute the SHA256 hash of the login password, and only the hashed values are stored in the database and compared with user input. 2) AsymmetricCryptography (com.sunny.AsymmetricCryptography.aix)
The extension is used to encrypt/decrypt the serial number stored on the RFID tag to verify its authenticity.
Due to the limitation of the extension, we assume the “private key” in the extension is used as the “public key” for decryption in our implementation, and hence, it is published and made available. Meanwhile, the “public key” in the extension is used as the “private key” for encryption in our implementation, and is not disclosed to our order service app. However, the two keys are both stored on Google Sheets so that the other app (RFID tag manipulation app) can make use of the keys to prepare the encrypted version of the serial number for new tags.
App for RFID tag manipulation
To facilitate the demonstration, another mobile app is developed using MIT App Inventor 2 to manipulate the RFID tags. The app performs three functions, 1) Register a new tag (Figure 6) Flow chart to register a new tag.

This function is used to add a new tag into the inventory.
User inputs the SKU number and the corresponding information is retrieved from the Google Sheets (sql-like).
Upon confirmation of the SKU, the new serial number is retrieved from the Google Sheets (sql-like).
The tag information is then written to the Google Sheets (Apps Script) and on the tag (NFC write). 2) Register a refurbished tag (Figure 7) Flow chart to register a refurbished tag.

This function is used to add a refurbished tag into the inventory.
To register a refurbished tag, user first reads the tag (NFC read) to retrieve the SKU and the serial number.
The app then retrieves the public key of the SKU from the Google Sheets to decrypt the serial number.
Upon confirmation from the user, a label in the tag, which indicates if it is an original one or a refurbished one, will be updated and written to the tag (NFC write). The corresponding entry in the Google Sheets will also be updated (Apps Script) with the record identified using the decrypted serial number. 3) Deploy a new tag (Figure 8) Flow chart to deploy a (new) tag.

This function is used to prepare a tag that is assumed to be installed on an existing system and is to be replaced.
To deploy a new tag, user first reads the new tag (NFC read) to retrieve the SKU and the serial number.
The app then retrieves the secret key of the SKU from the Google Sheets to decrypt the serial number.
Upon confirmation from the user, the deployment date will be written to the tag (NFC write). The corresponding entry in the Google Sheets will also be updated (Apps Script) with the record identified using the decrypted serial number. The corresponding inventory will also be updated.
Implications for Practice
Despite the limitations of mobile application development using MIT App Inventor 2, especially the NFC related functions, the two mobile applications we develope have successfully demonstrated the effectiveness of using RFID technology to facilitate the reverse logistics, integrated with the forward logistics. For instance, the integration of work in the last mile of the forward logistics (collecting items from the warehouse to service site) and the first step of the reverse supply chain (collection of replaced items from the service site) means more streamlined workflow to the service parts operator, making his job more efficient.
Moreover, service parts authentication can be done when the item is being replaced by the operator, ensuring that only genuine items, when they are deemed profitable to be refurbished by the business intelligence system, are forwarded to the repairing center for refurbishment. Meanwhile, the use of RFID tags also enables easier inventory checking, so that the business intelligence systems can access more up-to-date information to make better decisions for business sustainability.
Regarding the impacts of this case study to the supply chain sustainability, the proposed IoT solution not only facilitates the visualization of service parts operations, but also streamlines the integrated process of forward and reverse logistics of failure parts collection for component reimbursement. With the integration of business intelligence and IoT into service parts operations, companies can achieve the cost saving of component reuse as well as the environmental benefits of waste reduction. Our proposed IT solution featured by the low-cost development can be used for both small and medium enterprises as well as international enterprises.
Conclusion
In this case study, we studied the use of RFID to facilitate the information collection for the reverse supply chain in the service parts maintenance industry. In particular, we presented the implementation of a mobile application for such an application using MIT App Inventor 2. We showed that by equipping service parts with NFC RFID tags, the developed mobile application can act as an RFID reader to verify and authenticate the service parts wirelessly without line-of-sight or physical contact, enabling the service parts to become a part of Internet-of-Things. The collected information can then be updated or stored in the backend server. Such real-time information collection helps provide more up-to-date data for business intelligence analysis and contributes towards business sustainability and environmental sustainability, for instance, by removing the uncertainties in refurbishing replaced items.
Supplemental Material
Supplemental Material - Integrating internet of things in service parts operations for sustainability
Supplementary Material for Integrating internet of things in service parts operations for sustainability by Chris Y Tak and Daniel Y Wing in International Journal of Engineering Business Management.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the Strategic Development Grant from The Hang Seng University of Hong Kong (Project Title: HSUHK Decision Analytics Impact Awards) and the Research Grants Council of Hong Kong under the Research Matching Grant Scheme (RMGS) (700004).
Supplemental Material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.