Abstract
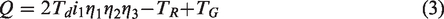
A novel data encryption method is presented for howitzer shell transfer arm using chaos and compressive sensing. Data are stored in the embedded fault diagnosis machine using chaos and compressive sensing, so the encrypted data are more secure in the embedded system and in the process of transmission with host computer. When the host computer extracts the operation data of the howitzer shell transfer arm monitored by the fault diagnosis machine, firstly, the encrypted data in the embedded diagnostic machine are read, then decrypted, and then the original signal is reconstructed by the orthogonal matching pursuit algorithm for further analysis and processing. The similarity degree between the reconstructed data and the original data is 0.947, the key space of the algorithm is
Introduction
Shell transfer arm is an important component of the ammunition automatic loader system of a large caliber self-propelled howitzer. It is mainly used to transport the shell pulled out from the magazine to a required position. 1 The location accuracy of the shell transfer arm is often out of tolerance during its service time. Therefore, the reliability of the ammunition automatic loader system is severely reduced. Monitoring the movement of the shell transfer arm is of great significance for deducing how the system characteristics of the shell transfer arm changing during its running processes, and for achieving the fault diagnosis and fault prediction of the shell transfer arm. Condition-based maintenance (CBM) is the use of machinery run-time data to determine the machinery condition and hence its current fault/failure condition, which can be used to schedule required repair and maintenance prior to breakdown. The area of intelligent maintenance and diagnostic and prognostic-enabled CBM of machinery is a vital one for today’s complex systems in industry, aerospace vehicles, military and merchant ships, the automotive industry, and elsewhere. The industrial and military communities are concerned about critical system and component reliability and availability. 2 Embedded fault diagnosis machine real-time monitors the ammunition automatic loader system, collects the data by using sensors, analyzes the data, detects and isolates faults, and predicts the health of the system in the future. Zhang et al. 3 analyzed a large amount of electric current data from the oil source supply battery to obtain the fault reasons of the automatic reloading system of artillery; Du and Pan 4 achieved the fault diagnosis of an autoloader by transferring the fault tree of a shell-lifting machine into a Petri net; Wang et al. 5 proposed a type of search algorithm of an expert system based on the fault tree of a rotary gun loading machine and designed a reasoning machine for the rotary gun loading machine; Huang et al. 6 proposed a method, which is used to diagnose the faults of small caliber artillery automation by applying the information entropy and the genetic algorithm support vector machine; and Yan et al. 7 analyzed the fault causes of an autoloader on an armored vehicle, and achieved the fault diagnosis by fault tree, expert system, and neural network. In summary, at present, the mainstream fault diagnosis methods of ammunition automatic loader system are mainly checked and diagnosed periodically by technicians. Technicians regularly collect data and make diagnostic results, and the normal working state of the automatic loading system cannot be monitored and diagnosed in real time. The literature and examples of real-time monitoring and diagnostic method for howitzer shell transfer arm are rare, and the application of data compression collection and encryption is also rare. So, it is a new attempt of application for howitzer shell transfer arm using chaos and compressive sensing (CS). Real-time diagnosis and monitoring system collects and stores a large number of data, and the upper computer periodically extracts the stored data, analyzes faults, or predicts the future health status. This is a great challenge to the storage capability of the storage elements and the security of the stored data for the embedded fault diagnosis machine. Therefore, only a small amount of data is collected and stored using CS during data sampling. 8 The lower computer only judges the basic characteristic parameters such as peak value, rise and fall rate, single action time, and so on, and data reconstruction, filtering, faults analysis, location, and prediction are given to the superior computer, which is better at calculation. It is more conducive to the optimization of the overall performance of the system. The operation data are related to the confidential information of the ammunition automatic loader system, if leaked, it is likely to infer the ammunition loading time, swing amplitude, hydraulic pressure, and other confidential information. Therefore, the data are stored in the embedded fault diagnosis machine using chaos and CS, so the encrypted data are more secure in the embedded system and in the process of transmission with the host computer. When the host computer extracts the operation data of the ammunition automatic loader system monitored by the fault diagnosis machine, firstly, the encrypted data in the embedded diagnostic machine are read, then decrypted, and then the original signal is reconstructed by the orthogonal matching pursuit (OMP) algorithm for further analysis and processing. It is a new attempt in the application of the ammunition automatic loader system operation data monitoring and storage fields.
Operational principle of the shell transfer arm
Structure and operational principle
The structure of the shell transfer arm is shown in Figure 1(a), and it is driven by two parallel series motors. The reduction gearbox consists of two-stage spur gear transmission and one-stage worm and worm gear transmission. The worm gear is installed on the trunnion of the howitzer. The arm is fixed with the worm gear, and it can rotate around the trunnion. The balance machine consists of a cylinder and an accumulator, and it is used to balance the gravitational torque of the arm to reduce the load of the motors. An angle sensor and an angular velocity sensor (tachometer generator) are installed on the arm to provide the angle signal to make the shell transfer arm to rotate to a required position. 1

The structure and working principle of the shell transfer arm. (a) The structure of the shell transfer arm and (b) Working principle of the shell transfer arm.
The working principle of the shell transfer arm is shown in Figure 1(b). It is a typical single-degree-of-freedom system, and according to its force analysis, the dynamic equations of the arm can be achieved
Then, the torque of the balance machine acting on the arm can be written as
Control system
The shell transfer arm is driven by two parallel series motors, the dynamic equation are as follows
9
The motion process of the shell transfer arm is shown in Figure 2. AB is the motion range of the arm, when the arm rotates from point C to point D as required, and the whole motion process can be divided into two stages: in stage CE, it only needs to control the rotation direction of the motors, which means it just need to apply a rated voltage on the motors to cause the motors to rotate at the rated speed to drive the arm rotate to point D at full speed. When the arm rotates to point E, the control system becomes a closed-loop position system, and the arm is located in point D accurately. The motion speed curve of the arm is shown in Figure 3.

The sketch diagram of the motion process of the arm.

The angular velocity of the shell transfer arm.
The driving circuit controls the speed of the motors by changing the average voltage applied to the motors. The voltage is a quasi-pulse, which is like pulse width modulation. The motors have two opposite direction field windings for controlling the rotation direction. The power device is an insulated gate bipolar transistor (IGBT) for simplifying the driving circuit. The control signal is generated by a closed-loop proportional–derivative controller. There is a threshold circuit in the trigger circuit to prevent the two field windings from being activated at the same time.
Chaos and compressive sensing theory
Definition and characteristics of Li–Yorke chaos
The continuous self-mapping function For any For any For any Extreme sensitivity to initial values; Long-term unpredictability; Internal randomness.
And the chaotic system mainly has the following characteristics:12,13
These features are especially suitable for military data encryption, its sensitivity to the initial value ensures that decryption data needs a unique password, and a small change in the password can result in a failure to decrypt the original data correctly. This is very important for data storage and transmission in military projects.
Logistic mapping
Logistic mapping is one-dimensional mapping, and it is a classical model for studying complex system behaviors such as dynamical system, chaos, and fractal. Its mathematical expression is as follows
Compressive sensing and sparse signal
Assuming there is a set of basis vectors
Equation (9) can be expressed as a vector form
Compressed sensing sampling signal

Signal compression sampling schematic.
Because
Signal reconstruction condition
In order to reconstruct the signal accurately, Candes and Tao 15 have given restricted isometry property (RIP) of the measurement matrix, which should be satisfied, and have proofed it. RIP conditions are stated as follows.
If there is a constant
For all
Where
The essence of RIP is that all subsets in
The principle of the CS method is to use the sparse information in the scene, reconstruct the scene g accurately in the case of a small amount of data sampled or remained. Scene is sparse, which means only a small number of nonzero elements. For sparse features, the norm is the most direct measure. It represents a number of nonzero elements in the scene. If g is sparse, then they must be able to accurately solve the problem through the following optimization
16
In equation (14), Donoho
17
pointed out that the least
The theoretical analysis shows that equations (14) and (15) have the same solution in the scene and the sparse measurement matrix
Data encryption method for a howitzer shell transfer arm using chaos and compressive sensing
The angular velocity of the shell transfer arm is collected during the system operation. The angular velocity is collected by a single-axis gyro CS-ARS-02 manufactured by Xi’an Chinastar M & C Limited in China, as shown in Figure 5. The measuring range of CS-ARS-02 is ±200°/s, the output voltage is 0 –5 V, the resolution ratio is less than 0.15°/s, and the sampling frequency is 1000 Hz, and USB-6211 data acquisition card from National Instruments is used to collect the angular velocity data.

Test photo.
In a complete automatic loading action, a single-axis swing lasts 2 s, and 2048 data are collected using normal sampling method, as shown in Figure 6.

2048 data of angular velocity normal sampled.
Compressive sensing method is used in the experiment, and there is a large probability to satisfy RIP when the observation matrix is a random matrix. Therefore, the 2048*200 random matrix is used as the measurement matrix to multiply the collected data.
Because of the regulations of army, the monitoring data of artillery cannot be transmitted online. Technical personnel read the data stored in the lower computer regularly and copied it to the upper computer through SD card. When compiling the data acquisition program of the automatic loading system of artillery, a 2048*200 matrix is randomly generated as the measurement matrix. The matrix is stored separately in the lower computer for monitoring and the upper computer for analysis. Data compression is done by the same measuring matrix about loading action of mechanical arm, and technicians use the same measurement matrix to restore data after periodically reading the stored data to the host computer. The measurement matrix is also replaced by a new 2048*200 random matrix when the data acquisition program of the automatic loading system is updated. The angular velocity of the shell transfer arm is compressed to 200 data, as shown in Figure 7.

200 data of angular velocity compressed sampled.
The collected data are the original signal through the measurement matrix
Then the second level encryption is carried out by using chaos and the process is as follows:
Select the initial value and the size of the surrogate matrix of the logistic map according to the encrypted data. Generate key by N iterations of the input password. The storage data are generated through the key XOR, the data of angular velocity compressed sampled.
When the input password is 3.1415926, the encryption result is as shown in Figure 8.

Chaotic encrypted data.
The chaotic encrypted data are randomly distributed between
When the host computer needs to read the stored data for analysis and processing, detecting, isolating the fault or predicting the future health condition of the shell transfer arm, first, the stored data are decrypted through the input password. The XOR inverse operation is XOR itself and, therefore, it only needs to be executed the encryption process again when knowing the input password. After the password 3.1415926 is entered, the decryption result is shown in Figure 9.

Decrypted data.
After decryption, the original signal is reconstructed by the OMP algorithm,
18
where the OMP algorithm is the Initialization residuals Calculate the projection coefficients of all column vectors and residual recovery matrix. Find out the location of the maximum projection coefficient, and expand the matrix. Least squares, minimize the residuals, and update the residuals. Record the maximum projection coefficient corresponding to the position.
Cyclic iterating K times (K is sparse), the 2048 data recovered are as shown in Figure 10.

Reconstructed 2048 data.
The result shows that the OMP algorithm could reconstruct the original data accurately, guarantee the correctness about diagnosis and prognosis of the fault diagnosis machine. There appears a small deviation in the reconstructed angular velocity data and the actual data, and only fundamental and low frequency are used in extracting characteristic value, while the deviation has no effect on final fault location results.
The similarity degree of the time-varying curves
Similarity degree
The quantitative relationship among identical, similar, and alien.
For two time-varying data
The numerical similarity
The shape similarity is calculated by landmark dividing method, where the main process of landmark dividing method is as follows
22
Normalize the original data
where 2. Subtract the adjacent elements of data 3. Multiply the adjacent elements of data 4. Determine the index value of the negative 5. Assume that data
For
When
Analysis of algorithm security
Real-time monitoring and diagnosis system collects and stores a large number of working data of automatic loading system, and due to the regulations of the army, the monitoring data of artillery cannot be transmitted online. The upper computer periodically extracts the stored data, analyzes faults or predicts the future health status by technical personnel through SD card. So, it is a great challenge to the storage capability of the storage elements and the security of the stored data for the embedded fault diagnosis machine. Only 9.77% of the working data are collected and stored using CS during data sampling, where it effectively reduces the storage burden of the lower computer.
Similarity comparison between encrypted data and original data
The encrypted data must be able to hide the shape of the original data, and not reveal any information of the original data or the relationship between the encrypted data and the original data, so the encryption algorithm is considered to be safe. Dynamic time warping (DTW) is used to measure the similarity between two signals because the encrypted signal and the original signal have different time lengths. DTW can calculate the similarity between two time series by extending or shortening the time series. First, two 200*2048 matrix D and d are applied, which are cumulative distance and frame matching distance, respectively. The frame matching distance matrix d of the two signals is calculated by loop. Then the dynamic programming is carried out to calculate the cumulative distances D1, D2, and D3 for each lattice
Differential analysis
When some data of the original signal change, the encrypted data will change greatly, which shows that the algorithm can resist the differential attack well. First, the 600th data of the original signal is changed from 52.93 to 0, and then the changed data are encrypted with the same measurement matrix and key. The encrypted data are shown in Figure 12.

Chaotic encrypted changed data.
The number of changing pixel rate (NPCR) and the unified averaged changed intensity (UACI) are important indexes to measure the resistance of encryption algorithm to differential attack. NPCR and UACI denote the percentage and degree of change in the number of pixel values of the encrypted signal after randomly changing a certain pixel value of the original signal. If two encrypted images are
Because the encrypted data are a one-dimensional signal,
Key space analysis
A good encryption algorithm’s key space should be large enough to resist exhaustive attack.
23
The data encryption method for a howitzer shell transfer arm using chaos and CS is encrypted two times, the measurement matrix
Key sensitivity analysis
In security analysis, a small change in the password can result in significant changes in the encrypted data. 24 The password is 3.1415927 when decrypting the storage data in the experiment. The decryption result is shown in Figure 13 when the password changes by 3.2e-6%, and the data reconstructed by OMP are shown in Figure 14.

Decrypted data by wrong password.

Reconstructed data by wrong password.
The results show that the final reconstructed data changes greatly when there is a minimal change in the decryption password and, therefore, it is considered that the chaotic encryption algorithm is sensitive to the key.
Conclusions
In this paper, a novel data encryption method is presented for a howitzer shell transfer arm using chaos and CS. Data are stored in the embedded fault diagnosis machine using chaos and CS, so the encrypted data are more secure in the embedded system and in the process of transmission with the host computer. When the host computer extracts the operation data of the ammunition automatic loader system monitored by the fault diagnosis machine, firstly, the encrypted data in the embedded diagnostic machine are read, then decrypted, and then the original signal is reconstructed by the OMP algorithm for further analysis and processing. The similarity degree between the reconstructed data and the original data is 0.947, which is more than 0.92 of the design requirements. The key space of the algorithm is