Abstract
When nodes and/or links are down in a network, the network may not function normally. Most of the existing work focuses on the reachability between two nodes along a path, that is, path reliability, and that through arbitrary paths, that is, network reliability. However, in case of wireless multi-hop networks and road networks, it may be inefficient or difficult to recalculate a path from the source to the destination when a failure occurs at an intermediate link in the path. In such cases, we can expect that the reachability between two nodes will improve by taking a detour from the entry of the failure link (i.e. failure point) to the destination without traversing the failure link. Since the detour may also increase the communication/travel delay, in this paper, we propose a new path metric (i.e. path reachability including distance-constrained detours), which consists of the conventional path reachability and the reachability along distance-constrained detours under arbitrary link failures in the original path. We first prove the two important characteristics: (1) the proposed metric is exactly the same as the network reliability in case of no distance constraint and (2) it is upper bounded by the diameter constrained network reliability. Through numerical results using a grid network and more realistic networks (i.e. wireless networks and a road network), we show the fundamental characteristics of the proposed metric and analyze the goodness of several representative paths in terms of the proposed metric as well as the conventional metrics (i.e. path length and path reachability).
Keywords
Introduction
Nowadays, our human society relies on various types of networks such as communication networks and road networks. When some of nodes (e.g. network devices and intersections) and/or links (e.g. communication links and road segments) are down, due to failures, natural disasters, or malicious attacks, the network may not be able to work normally. There are many studies on quantitatively evaluating the reliability of the network when the failure probability (or availability) of each node/link is given.1–4 In this paper, we mainly focus on the link failure.
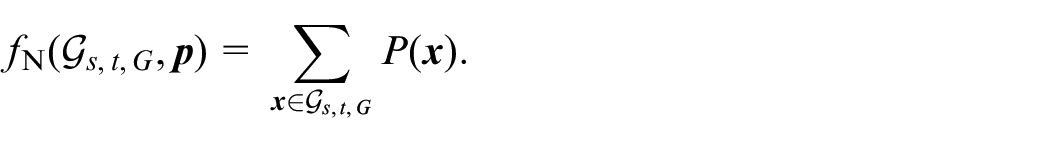
One possible path reliability metric is the path reliability (reachability), which is defined as the probability that a path
In case of several situations, for example, multi-hop communications in wireless networks and evacuation over road networks,5,7,8 when a failure occurs at an intermediate link in the
In this paper, we introduce a new concept of distance-constrained detour possibility, which is the probability that the source
The main purposes of the manuscript are following: (1) proposing the new metric (i.e. path reachability including distance-constrained detours) and (2) revealing the potential of the proposed metric in terms of path selection through several numerical experiments. In this context, we mainly focus on the application of the proposed metric in a proactive approach. More specifically, given a certain
Through numerical experiments using a grid network, we show the fundamental characteristics of the proposed metric and the relation with the existing metrics, that is, path length, path reliability, and network reliability. We further evaluate the goodness of some representative paths in terms of the proposed metric and existing ones through numerical experiments using realistic networks, that is, wireless networks and a road network.
The rest of the paper is organized as follows. The following section gives related work, and the subsequent section gives the proposed path metric of the path reachability including distance-constrained detours. A further section demonstrates numerical results using three kinds of networks. The final section provides conclusions and future work.
Related work
Network reliability metrics
The
Since the computational complexity of the network reliability and its variants are NP-hard,11–13 many researchers have studied on efficient algorithms for exact solutions (e.g. sum of disjoint products,
14
state enumeration,
15
direct decomposition,
16
factoring,
17
and binary decision diagram (BDD) based approaches9,18) or those for approximate solutions (e.g. Monte Carlo simulation method,
19
its extension with binary-addition-tree algorithm,
20
approximate zero-variance importance sampling,
21
counting based method,
22
convolutional neural network based method,
23
and graph neural network based method
24
). As we will see in “Proposed metric” section, the proposed metric (i.e. path reachability including distance-constrained detours) requires the calculation of the diameter constrained network reliability. Since our main focus is revealing the potential of the proposed metric as mentioned in “Introduction” section, we adopt one of the efficient algorithms for exact solutions. (The details will be given in “Numerical experiments” section.) As for other network reliability metrics, several studies focused on the fraction of important nodes to maintain the network connectivity. Li et al.
25
proposed a new network reliability metric using percolation theory.26,27 Percolation theory focuses on the network connectivity when part of the nodes and/or links are removed from a network. If a link has capacity (e.g. radio frequency of a wireless link and road width), the link availability depends not only on the failures but also on the capacity. Inoue
3
evaluated the network reliability when using two disjoint
In this paper, we focus on the path reachability including distance constrained detours, which is the reachability of the
Path reliability metrics
One possible path reliability metric is the path reliability, which is reachability of an
In mobile ad-hoc networks (MANETs), dynamic change of link reliability between nodes due to the node mobility may fail in guaranteeing the quality of service (QoS) of the routing. Chatterjee and Das and Das 34 proposed a dynamic source routing scheme based on the number of hops, congestion degree of a path, and the received signal strength (RSS) of nodes. Kumar and Padmavathy 35 proposed a link reliability model that determines whether a link between two nodes is connected or not based on the Euclidean distance, transmission distance, and the radio propagation characteristics between them. Thanks to this reliability model, they further evaluated the reliability of the shortest path between two nodes.
These existing schemes focus on the reliability of a certain path between two arbitrary nodes but it may be inefficient and/or difficult to reconstruct an alternative
Routing with detours
In wireless sensor networks, each sensor node may not be able to accurately grasp its own location as well as other nodes’ locations, which will make data packets encounter a routing hole where there is no node closer to the destination. 36 To address this problem, several studies proposed geographical routing algorithms to transfer data to the destination node by bypassing routing holes.37,38 Lima et al. 38 proposed a geographic routing algorithm for transferring data to the destination node by bypassing routing holes under the assumption that RSS from the sink node has a positive correlation with the distance to the sink node. Huang et al. 37 proposed an energy-aware geographic routing protocol with bypasses of routing holes for wireless sensor networks with resource constraints.
These schemes can be regarded as reactive ones because they determine a detour after a link failure occurs in the
Proposed metric
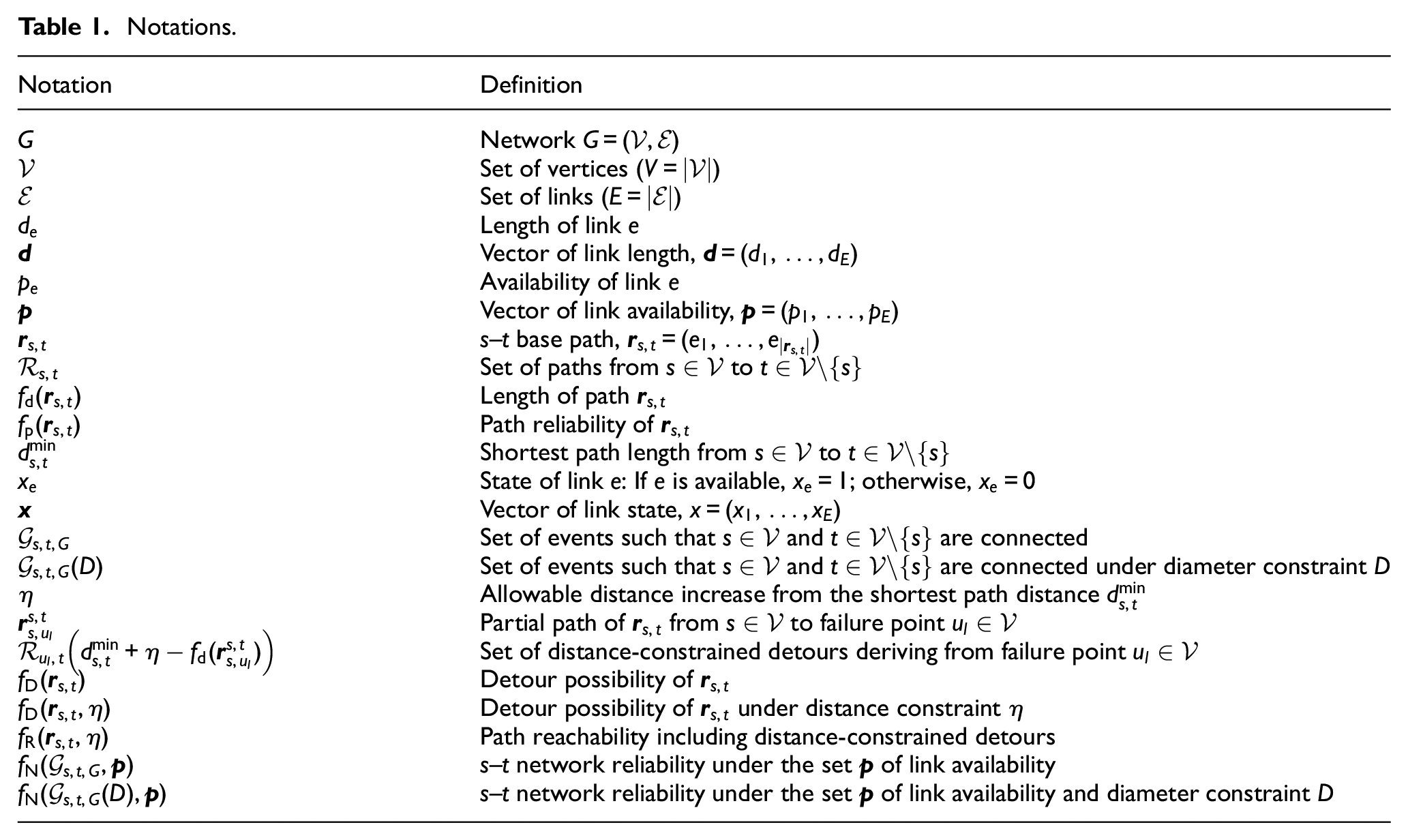
In this section, we will define the proposed metric, that is, path reachability including distance-constrained detours. Table 1 summarizes the notations used in this paper. Figure 1 illustrates the flow to derive the proposed metric, where the left side gives the steps in general cases and the right side gives an illustrative example using a
Notations.
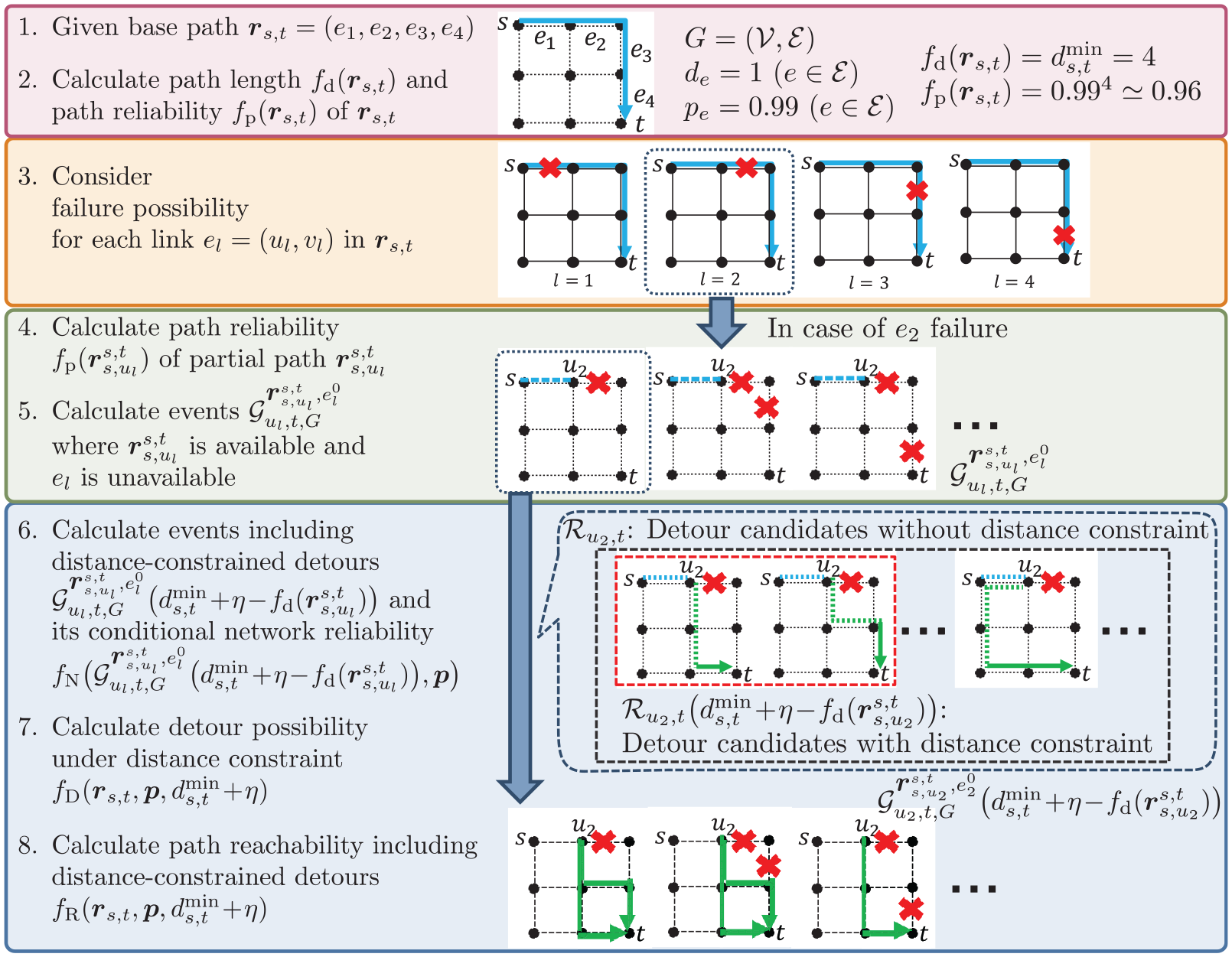
Flow to derive proposed metric.
Preliminaries
For simplicity of explanation, in what follows, we assume communication networks.
The length

where the path
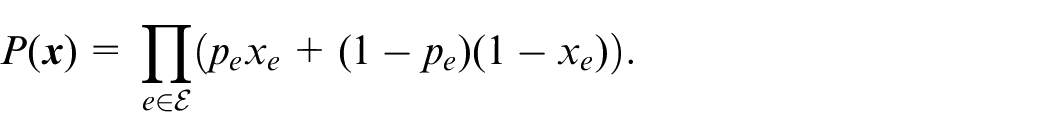
If the link availability

Let
The
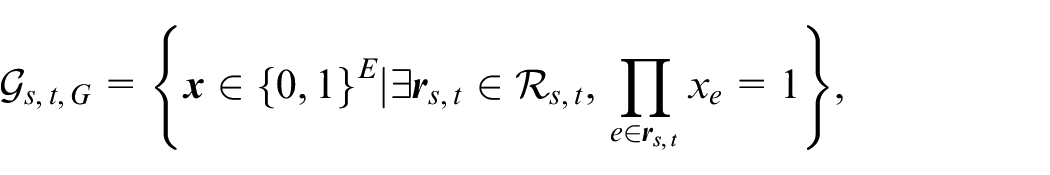
As a result,
Similarly, the diameter constrained network reliability for an
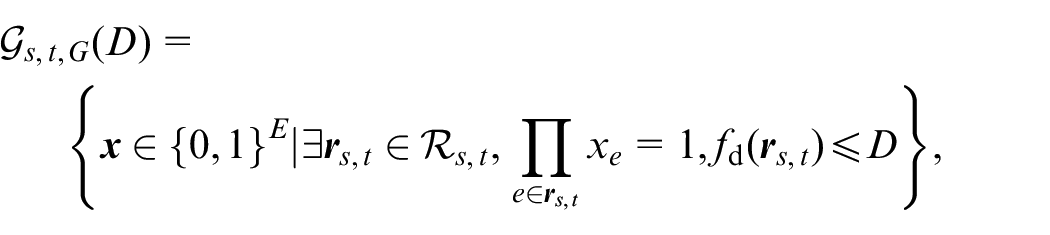
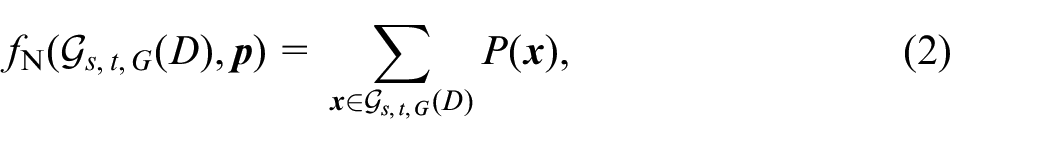
respectively. Therefore,
In what follows, we will see the calculation of the diameter constrained network reliability is required to derive the proposed metric (i.e. path reachability including distance-constrained detours) in equation (8). Note that the computational complexity of the network reliability and its variants are NP-hard as mentioned in “Network reliability metrics” section. In this paper, to reveal the potential of the proposed metric itself, we will strictly calculate the (diameter constrained) network reliability. (The details will be explained in “Evaluation model” section.) As for a more lightweight algorithm for the calculation, which will be more important in reactive approaches, we plan to develop it with the help of existing studies given in “Network reliability metrics” section.
Detour possibility
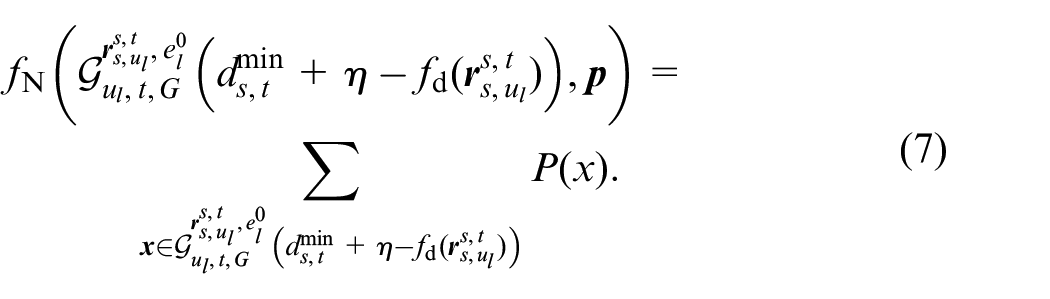
Suppose that the

where
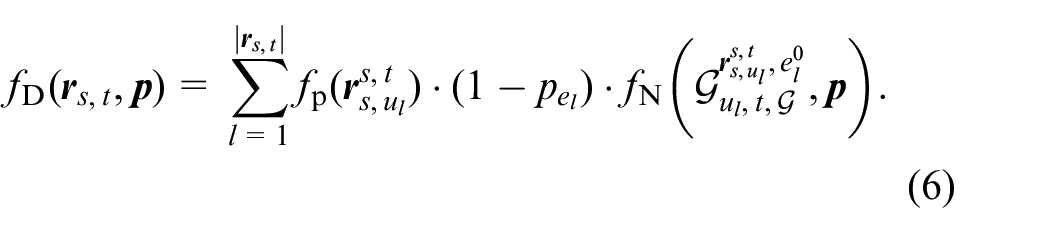
Under the events where the partial path
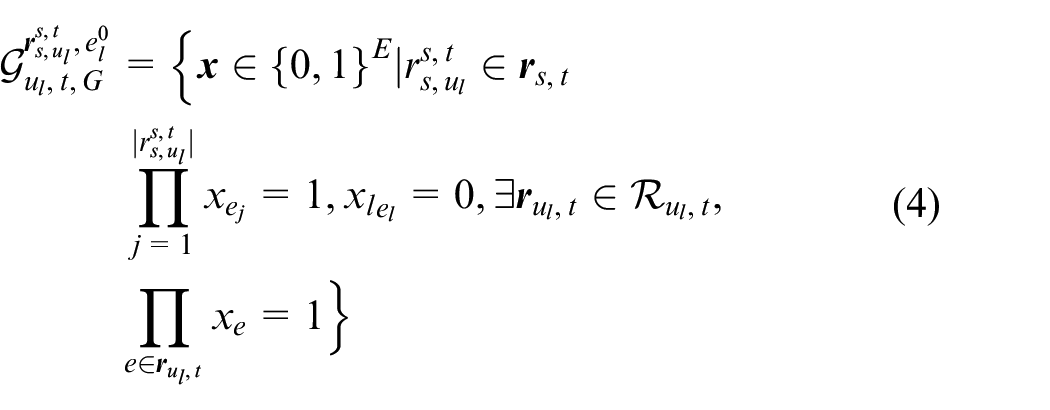
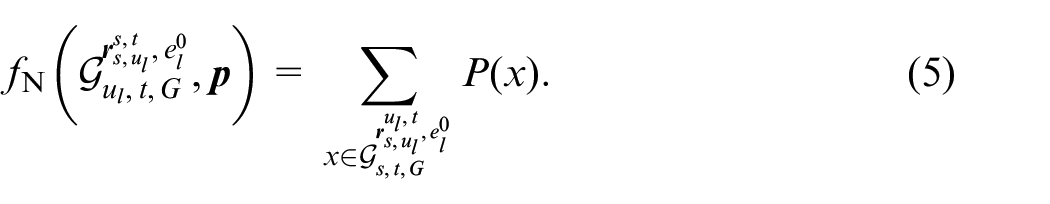
This event occurs with the probability, which is the product of the path reliability of
In the right side of Figure 1, part of
Path reachability including distance-constrained detours
As for the detour possibility, taking a detour may increase the total length of the
Suppose that the
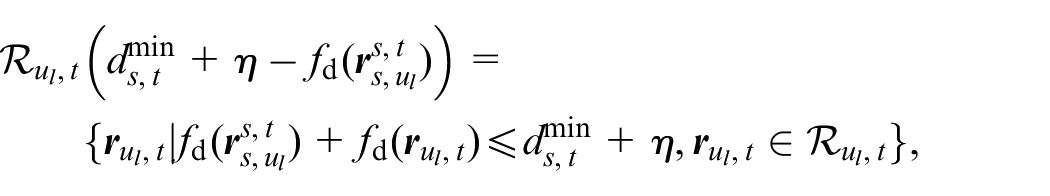
where
In the right side of Figure 1,
Under the event where the path
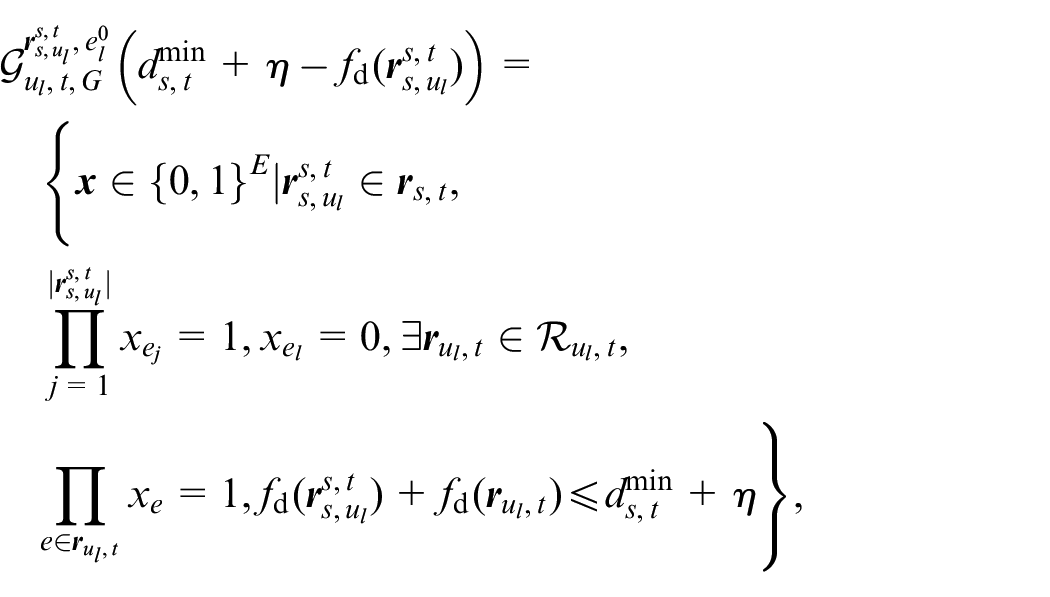
In the right side of Figure 1, part of
From equations (3) and (7), we can define the detour possibility under the distance constraint
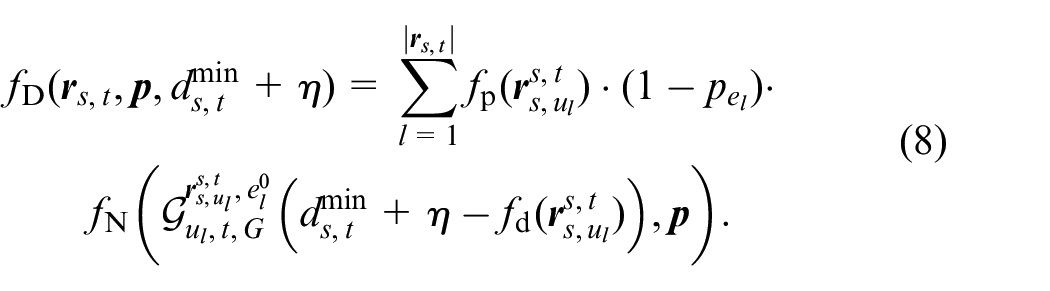
The path reachability including the distance-constrained detours of
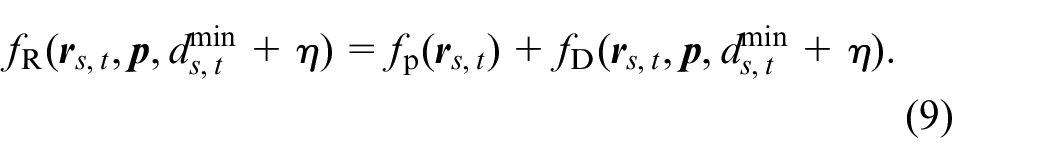
Here, we provide the following important theorems related to the path reachability including the distance-unconstrained detours.

The proof will be given in “Proof to Theorem 1” section.
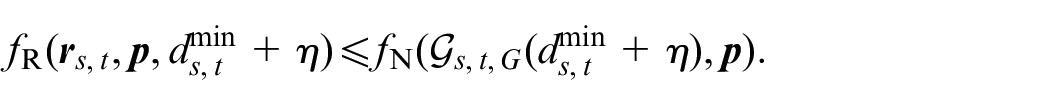
The proof will be given in “Proof to Theorem 2” section.
Base path selection strategy
As mentioned above, given a base path, the proposed metric can be calculated. At the last of this section, we briefly explain how to select the base path. It is difficult to evaluate the distance-constrained detour possibility of all possible
Considering these points, in this paper, we will focus on the following five representative paths, that is, the shortest path
There may be more suitable base path selection strategies but it is one of the future directions.
Numerical experiments
In this section, we first show the fundamental characteristics of the the proposed metric (i.e. path reachability including distance-constrained detours) through evaluations under a grid network. Then, we further evaluate the goodness of some representative paths in terms of the path length, path reliability, and proposed metric, under wireless networks and a road network.
Evaluation model
Since the computation of the network reliability is NP-hard, multiple algorithms have been proposed to tackle the computational complexity.18,39 In this paper, we use Graphillion, 40 which is a Python library for efficiently computing the network reliability utilizing a zero-suppressed binary decision diagram (ZDD). 41 ZDD is one of the compressed data structures for a family of sets. As for the evaluation networks, we use three kinds of networks, that is a grid network, wireless networks, and a road network.
Fundamental characteristics of proposed metric
We first reveal the fundamental characteristics of the path reachability including distance-constrained detours through numerical experiments using a grid network. Figure 2 illustrates the
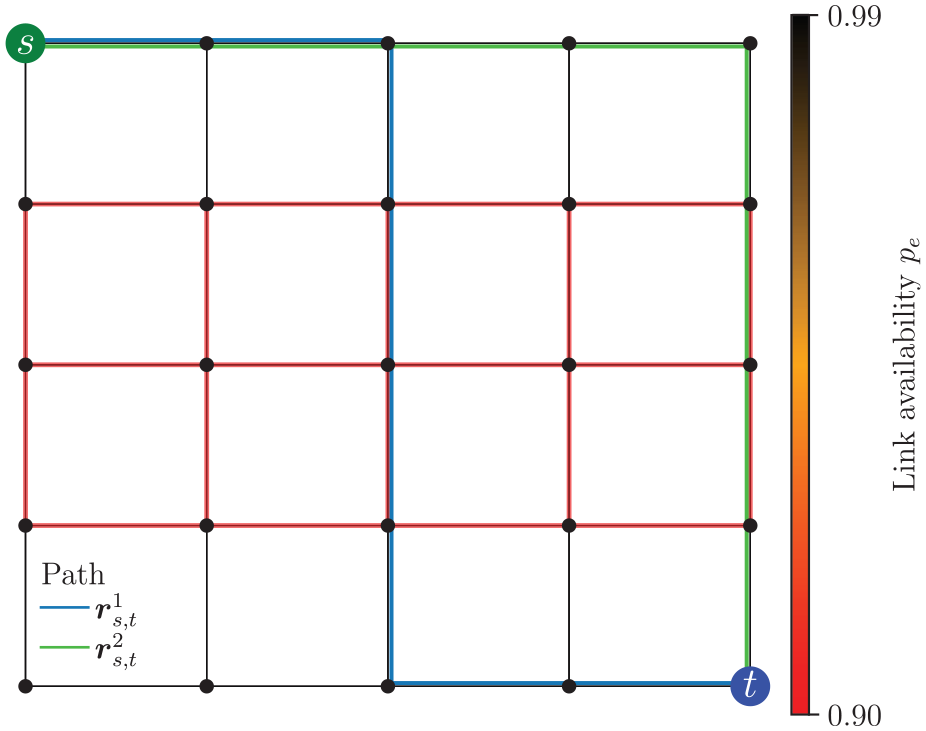
Grid network (
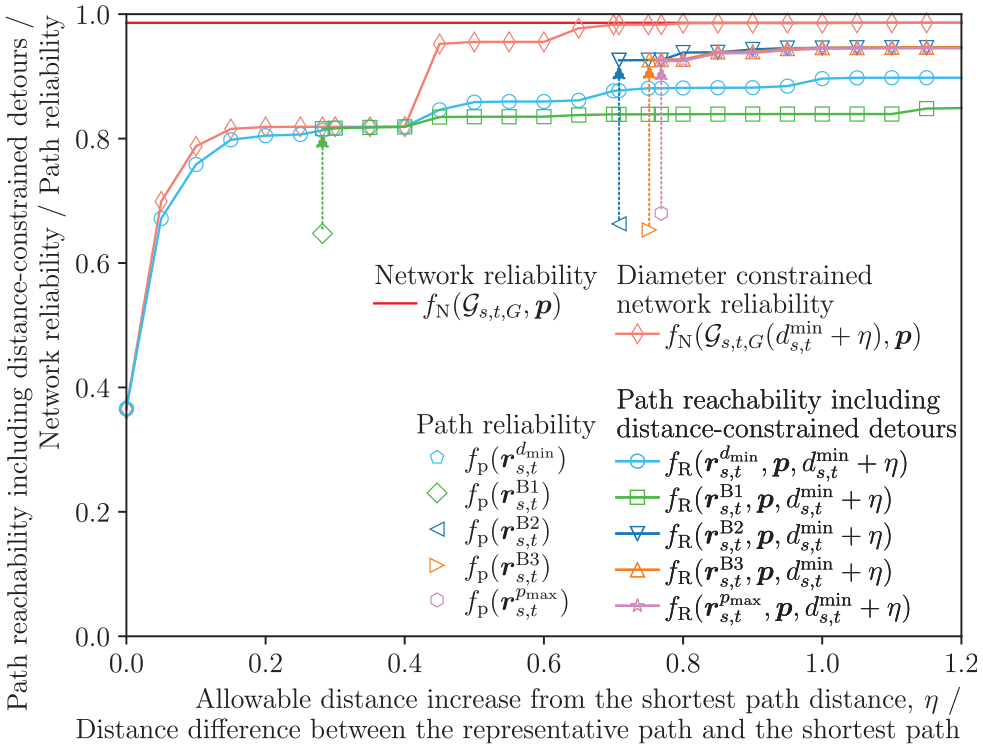
Figure 3 depicts the transition of the path reachability including distance-constrained detours of
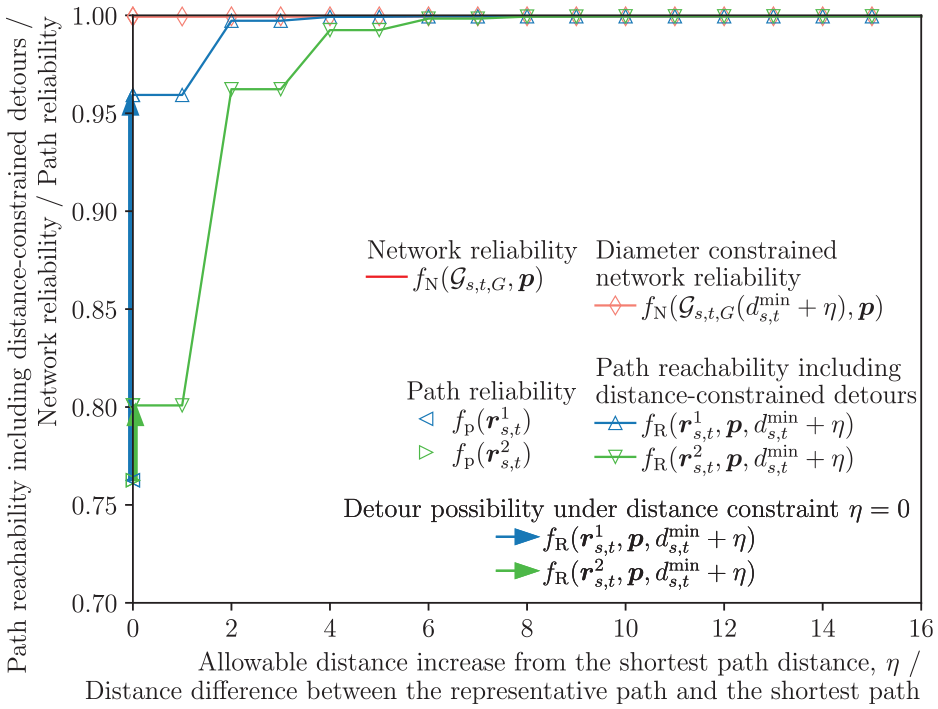
Impact of
We also confirm that the path reachability including distance-constrained detours of
Numerical examples of proposed metric for representative paths under realistic networks
In this section, we evaluate the goodness of some representative paths under realistic networks, that is, wireless networks and a road network, in terms of the path length, path reliability, and path reachability including distance-constrained detours. In what follows, we use the five representative paths (i.e. the shortest path
Evaluation under wireless networks
As for wireless networks, we use a unit disk graph model,
42
which has widely been used for modeling MANETs and sensor networks.43,44 In the unit disk graph, nodes with transmission range
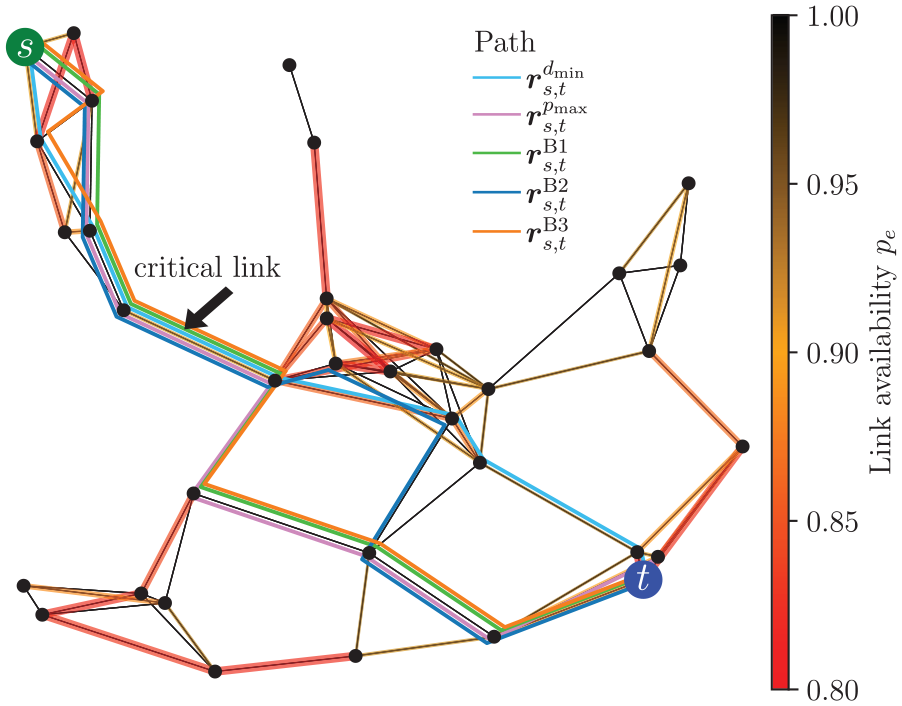
Wireless network 1 (
We randomly select 60% links as “less reliable” and the remaining as “more reliable.” In particular, each less (resp. more) reliable link
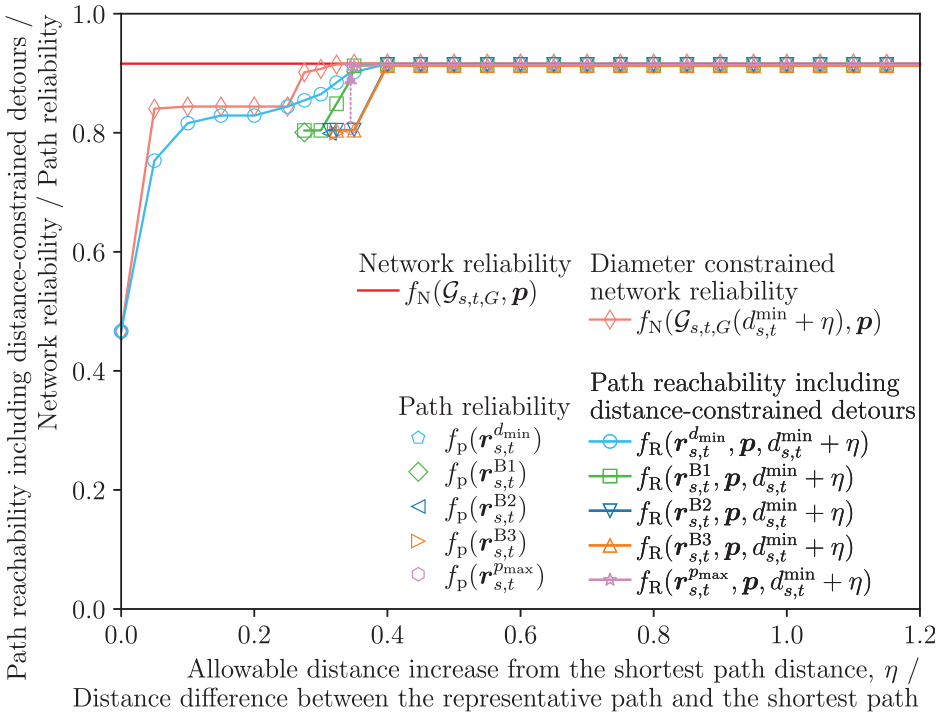
Figure 5 illustrates the impact of
Impact of
We also observe that the path reachability including distance-constrained detours monotonically increases with
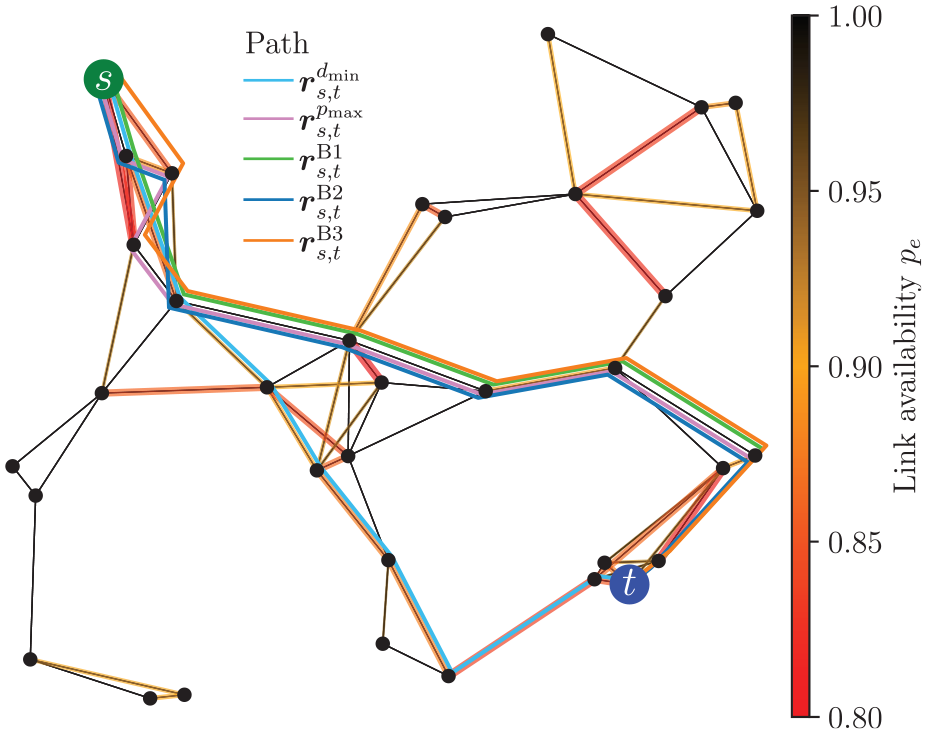
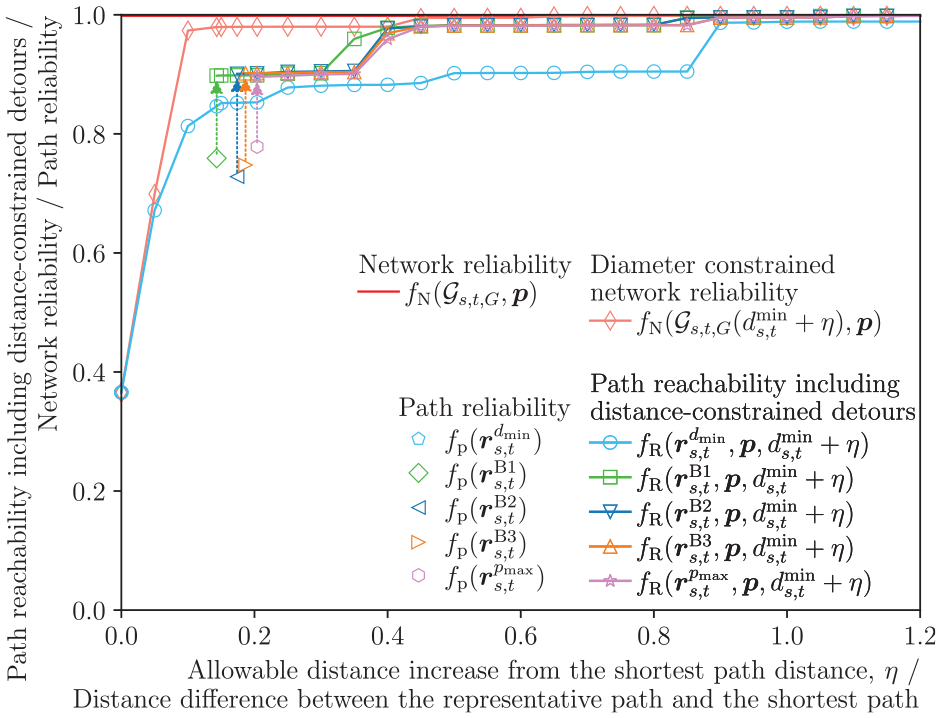
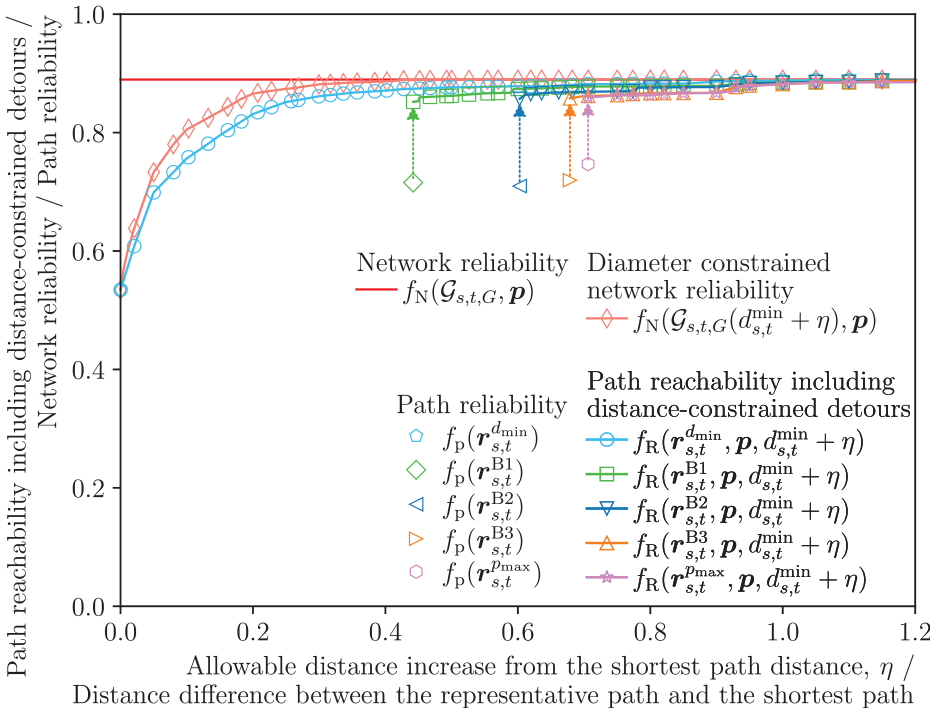
Next, we focus on another network example (wireless network 2) with five representative paths, as shown in Figure 6. Figure 7 illustrates the impact of
Wireless network 2 (
Impact of
As for the impact of
So far we have focused on wireless networks 1 and 2 as illustrative examples. Finally, we demonstrate more general results by showing the average results of 25 wireless networks, as shown in Figure 8. We confirm that the trends observed in the two examples hold.
Impact of
Finally, we focus on the routing hole problem. Although the routing hole itself is a problem in the reactive approach (i.e. the hop-by-hop based routing like the greedy forwarding), where nodes in the routing hole cannot find any nodes closer to the destination, we can use the above-mentioned proactive approach to assess the upper bound of the reactive routing performance under a potential risk of routing holes. In what follows, we give a simple example.
Suppose that a node
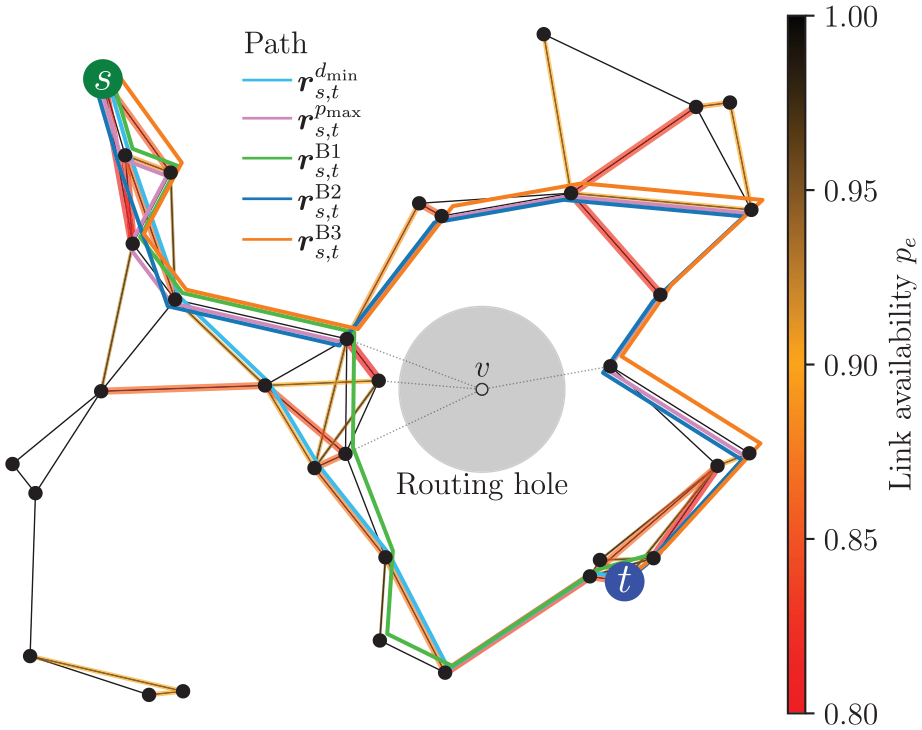
Wireless network 1 with routing hole (
Figure 10 depicts the impact of
Impact of
Evaluation under a road network
We consider an evacuation situation under a large-scale disaster. In Japan, a municipality, for example, Nagoya city, has been assessing the potential blockage risk of each road segment in its administrative area under large-scale disasters, for example, earthquake. More specifically, using a mathematical model, it gives the road blockage probability
Figure 11 shows the road network of
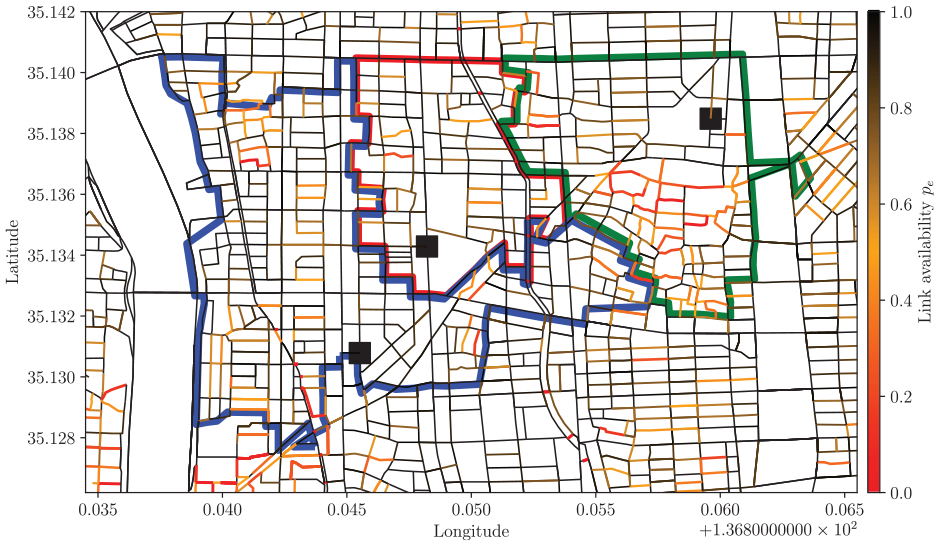
Road network (
In each area
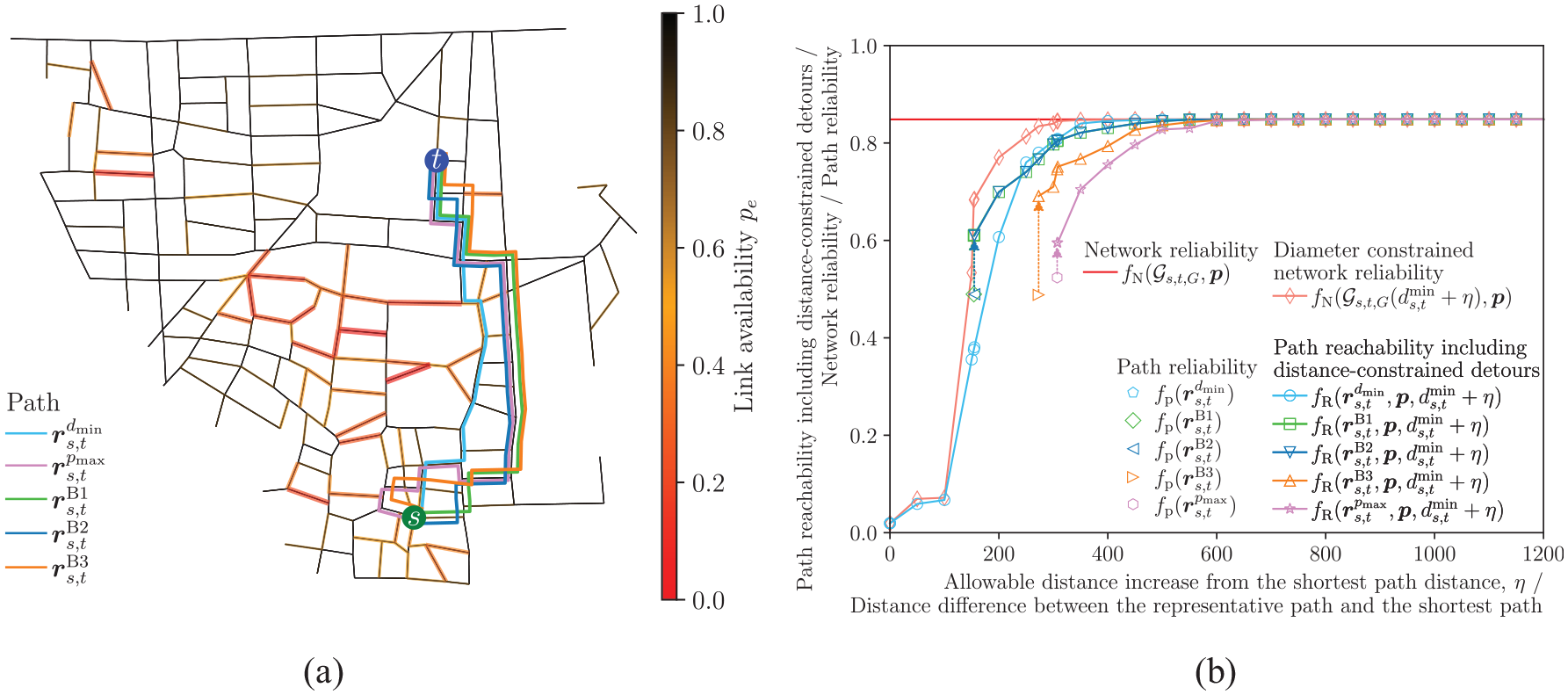
Results of road network (Area 1,
Figure 12(b) illustrates the impact of
We can confirm the similar tendency in other cases as shown in Figures 13 through 20 in the supplemental materials.
Conclusion
In this paper, we have proposed a new concept of distance-constrained detour possibility, which is the probability that the source
Through numerical experiments using a grid network, we have shown the fundamental characteristics of the path reachability including distance-constrained detours and the relation with the network reliability and diameter constrained network reliability. We have further evaluated the goodness of five representative paths, that is, the shortest path, the most reliable path, and three paths taking account of the balance between path reliability and path length, through numerical experiments using realistic networks, that is, wireless networks and a road network. We have shown that some of the representative paths can be well-balanced paths for these networks in terms of the path length, path reliability, and path reachability including distance-constrained detours.
In future work, we plan to tackle the computation complexity problem of calculating path reachability including distance-constrained detours, with the help of approximation methods for network reliability, for example, Monte Carlo based approaches.
Supplemental Material
sj-pdf-1-pio-10.1177_1748006X221133600 – Supplemental material for Path reachability including distance-constrained detours
Supplemental material, sj-pdf-1-pio-10.1177_1748006X221133600 for Path reachability including distance-constrained detours by Masahiro Sasabe, Miyu Otani, Takanori Hara and Shoji Kasahara in Proceedings of the Institution of Mechanical Engineers, Part O: Journal of Risk and Reliability
Footnotes
Appendix
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Supplemental material
Supplemental material for this article is available online.
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
