Abstract
We introduce a motion control which is a stealth strategy of a team of autonomous ships to approach a target without being detected. The target is equipped with a radar to detect a nearby ship. In the team, one ship, the leader, has a stealth ability not to be detected by a radar as it approaches the target. We steer the leader so that it moves to the target while appearing to be at the same bearing line from the target to the leader. Assuming that the target can readily observe optical flow, but only poorly sense looming, this type of motion by the leader is difficult to be detected by the target. We steer every ship, except for the leader, so that a pulse signal emitted from the radar on the target cannot reach any ship, since the signal is blocked by the leader. In this way, even in the case where multiple ships approach the target, the target cannot detect any ship. In our control law, a ship, except for the leader, does not have to access the position of the target in real time. However, a ship must access the bearing line from the target to the leader in real time. Our motion control is inspired by line-of-sight guidance control laws and is developed in discrete-time systems. We present MATLAB simulations to verify the performance of our motion control law.
Keywords
Introduction
Nowadays, stealth ships are built, employing stealth technology in an effort to ensure that it is harder to be detected by a radar. The main idea of stealth technology is to absorb a pulse signal emitted from a radar or to reflect the pulse in such a way that the signal cannot return to the radar which emitted it.
Let us consider a scenario of deploying multiple autonomous ships to approach and attack a target without being detected. Since weapon range of a ship is bounded, they approach a target until they are sufficiently close to the target. As they are sufficiently close to the target, they attack the target simultaneously to maximize the attack efficiency. Usually, a stealth ship is expensive due to its stealth technology. Thus, deploying multiple stealth ships may not be feasible.
This article introduces a motion control which is a stealth strategy of a team of autonomous ships to approach a target without being detected. The target is equipped with a radar to detect a nearby ship. In the team, one ship, the leader, has a stealth ability not to be detected by a radar as it approaches the target.
We steer the leader so that it moves to the target while appearing to be at the same bearing line from the target to the leader. This type of motion by the leader is called the motion camouflage with respect to a fixed point at infinity. 1 This motion camouflage is employed by various visual insects and animals to achieve prey capture, mating, or territorial combat. 1 –4 This motion is a time-optimal solution to capture a prey moving along a straight line. 2 Also, Ghose et al. 2 argued that this motion minimizes time-to-capture of an unpredictably moving prey. Assuming that the prey can readily observe optical flow, but only poorly sense looming, this type of motion by the predator is difficult to be detected by the prey. 1
Justh and Krishnaprasad 1 developed a feedback control law to achieve this kind of motion camouflage. As far as we know, Justh and Krishnaprasad 1 are unique in proving that under their controller, the predator converges to the motion camouflage state in finite time. We use the controller of Justh and Krishnaprasad 1 to achieve the motion camouflage of the leader.
We steer every ship, except for the leader, so that a pulse signal emitted from the radar on the target cannot reach any ship, since the signal is blocked by the leader. In this way, even in the case where multiple ships approach the target, the target cannot detect any ship. There are many papers on control of multiple autonomous vehicles. 5 –16 Ji and Egerstedt 9 introduced distributed coordination control of multi-agent systems while preserving connectedness. Zhang and Leonard 12 presented formation control approach to improve source seeking using distributed sensors. Cao et al. 14 discussed the overview of literature on multi-agent systems. As far as we know, stealth motion control for multiple robots has not been considered in the literature on formation control.
In our article, we design the control law for a ship except for the leader. We develop the control law in discrete-time systems. In our control law, a ship, except for the leader, does not have to access the position of the target in real time. However, a ship must access the bearing line from the target to the leader in real time.
The marine community has been using various guidance algorithms to make a marine vehicle follow a predefined path. 17 –19 Line-of-sight (LOS) guidance control has been widely used to make the vehicle follow the path robustly. 17,19 LOS guidance control demonstrated a high level of robustness to even a discontinuous path. 20 LOS guidance control is designed to steer the vehicle in such a way that it stays on the path, or to lead it toward the path if the cross-track error (the shortest distance to the path) is not zero. LOS guidance control makes the cross-track error converge to zero as time goes on. 17
Our motion control is inspired by the LOS guidance control law in the study by Lekkas and Fossen. 17 In our article, each ship is controlled so that it moves toward the bearing line from the target to the leader while getting closer to the target. The cross-track error for a ship is the shortest distance between the ship and the bearing line. We use a conventional LOS guidance control, which is based on a constant look-ahead distance. We present MATLAB simulations to verify the performance of our motion control law.
The article is organized as follows: The section “Assumptions and definitions” introduces assumptions and definitions in our article. The section “The motion control” presents the motion control law. The section “MATLAB simulations” introduces MATLAB simulations to verify the effectiveness of our control law. The last section provides conclusions.
Assumptions and definitions
We introduce several assumptions and definitions before presenting our main results.
We consider the team of pursuers consist of one leader and N followers. There are N + 1 pursuers in total. vl denotes the speed of the leader and vf denotes the speed of each follower. Note that every follower moves with the same speed.
We say that a target is captured in the case where it is within the weapon range of every pursuer. Note that we can capture the target only if it is within the weapon range of all pursuers. The problem tackled in our article is as follows: develop a controller for every follower to capture the target as fast as possible without being detected.
To capture the target in finite time, we assume that the speed of a target, vt , is strictly less than vl or vf . We simplify all pursuers and the target as circles in two dimensions. Moreover, collision avoidance among circular pursuers is not within the scope of this article. To avoid collision among pursuers, we can use a decentralized reactive collision avoidance algorithm in the study by Lalish and Morgansen. 21 The algorithm in the study by Lalish and Morgansen 21 can work in conjunction with our motion control law to guarantee that all pursuers remain free of collisions.
We assume that every follower localizes itself and accesses L in real time. Here, L denotes the infinite line crossing both the target and the leader. We argue that this assumption is feasible in practice. The leader and followers can use Inertial Measurement Units or Global Positioning Systems to localize themselves, respectively. The leader can use sensors, such as onboard radars, to access the target position in real time. Ristic et al. 22 presented various methods to estimate the target position using sensor measurements. Since the leader can localize itself as well as the target in global coordinate systems, the leader can access L in real time. Then, a follower can communicate with the leader to access L in real time.
In this article, we consider discrete-time systems. The subscript k is used to represent the time step k. In other words, for an arbitrary notation A, Ak
represents A at time step k. Let Fi
denote the i th follower, where i ≤ N.
Let
An illustration of concepts.
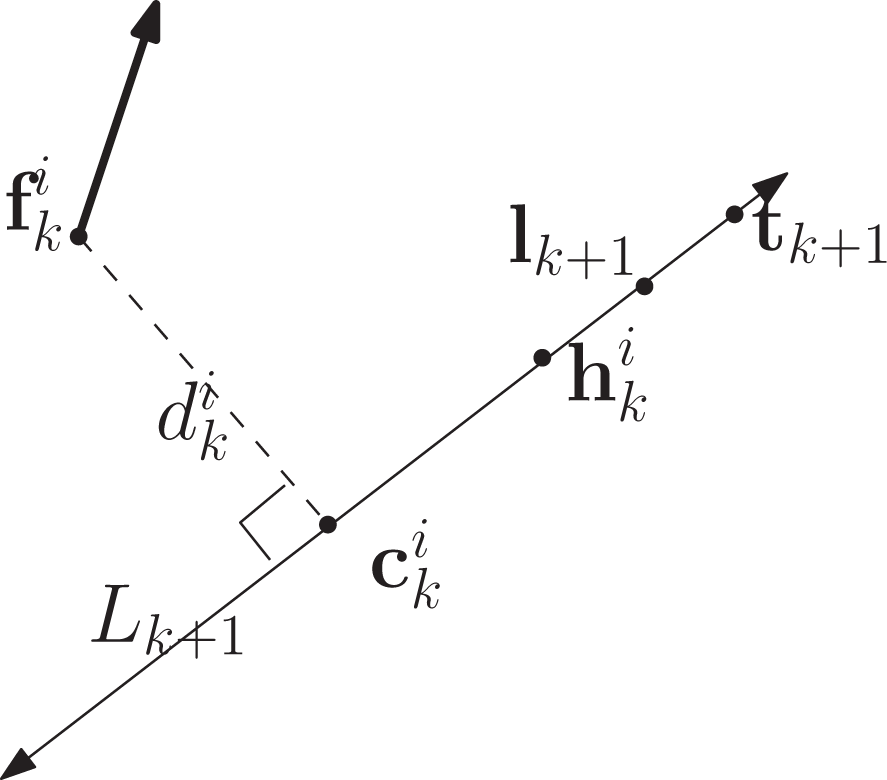
Let us consider Fi
at time step k. A follower’s reachable area within one time step forms the circle, called the reachable circle, whose radii has length vfT.

The reachable circle of Fi within one time step.
Conditions for stealth state
In the team, one ship, the leader, has a stealth ability not to be detected by a radar as it approaches the target. We steer every ship, except for the leader, so that a pulse signal emitted from the radar on the target cannot reach any ship, since the signal is blocked by the leader. In this way, even in the case where multiple ships approach the target, the target cannot detect any ship.
We assume that a radar emitting a pulse signal is located at the center of the target. Considering the size of each pursuer, a pulse signal cannot reach Fi in the case where
The stealth task of Fi is to achieve equation (1). In the case where Fi achieves the stealth task at time step k, we say that Fi is in the stealth state Ss at time step k. This implies that the target cannot detect Fi even in the case where Fi approaches the target.
See Figure 3 for an illustration of the case where the stealth task of Fi
is achieved. A pulse signal emitted from the target cannot reach Fi
, blocked by the leader. Thus, Fi
cannot be detected by the target’s radar. To make the definition of this stealth task feasible, both

Fi is in the stealth state. However, Fj is not.
Figure 3 also shows the case where Fj is not in the stealth state. A pulse signal emitted from the target can reach Fj . Thus, Fj is detected by the target.
In the case where
To make Fi
stay in the stealth state, it is desirable to make Fi
converge to L. Suppose that
The motion control
In this section, we introduce our motion control law. At each time step k, our control law is given as follows: Fi
moves to
Stability analysis
We analyze the stability of our control law. Let us consider the special case where Lk does not change with respect to k. In this special case, Fi converges to Lk as k increases, while heading toward the target. The proof for this convergence is provided in the study by Lekkas and Fossen. 17
To make our problem more interesting, we consider the general case where Lk changes with respect to k. We have the following theorem.
Theorem 1
Under our control law, we achieve the stealth task of Fi
at time step k + 1 in the case where
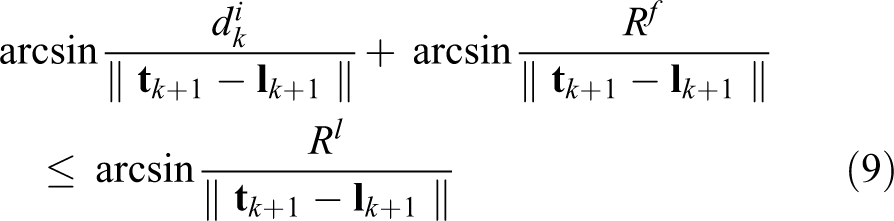
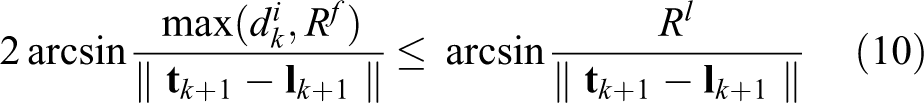
Proof
The stealth task of Fi
is to achieve equation (1). Suppose that
We prove that under our control law,
since

An illustration.
We have
Using equation (3), we derive
Consider the triangle formed by the following three vertices:
where θe
denotes
where
Using equation (6), we get
Since
□
Let us assume that the relative distance between a follower and the target is bigger than or equal to that between the leader and the target. In other words,
Corollary 1
Let us consider two constants a and b within the interval
Lemma 1
Assume that
Proof
Under our control law, a sufficient condition to achieve the stealth task of Fi at time step k + 1 is
Using Corollary 1 and the assumption that
Moreover, since
Using the fact that
Here,
Since
Under our control law, a sufficient condition to achieve the stealth task of Fi
at time step k + 1 is
□
Theorem 2 proves convergence of our control law under the following three assumptions. The first assumption is that
Theorem 2
Fi
moves under our control law. Assume that
Proof
We assume that
Moreover,
□
Assume that
We provide the conditions to satisfy that
We need to introduce new notations before presenting the conditions. Let

L k+1 and L k+2 are parallel to each other. l 2 is negative.
Lemma 2
Consider the case where L
k+1 and L
k+2 are parallel to each other.
Proof
Figure 5 shows the case where L k+1 and L k+2 are parallel to each other.
We draw both x-axis and y-axis on the plane satisfying the following conditions:
x-axis and y-axis are normal to each other.
The xy coordinate of
Using the geometry in Figure 5, the y-coordinate of
This lemma is proved.
Corollary 2 proves convergence of our control law under the following three assumptions. The first assumption is that
Corollary 2
Fi
moves under our control law. Assume that
Proof
Since
MATLAB simulations
In this section, we verify the effectiveness of our motion control law using MATLAB simulations. In all scenarios, T = 1 s. Also, the leader and five followers move with unit speed, and the target moves with the speed 0.7. The initial position of the target is (100, 100), and that of the leader is (0, 0). The initial positions of all followers are as follows
Rl
= 2 and Rf
= 1, and we check whether the stealth task of Fi
is achieved by measuring
We control the motion of the leader using the motion camouflage control in the study by Justh and Krishnaprasad. 1 The motion camouflage control is designed so that the bearing of the leader with respect to the target does not change as time goes on. However, as we use the motion camouflage control in the study by Justh and Krishnaprasad, 1 the bearing of the leader with respect to the target changes slowly as time goes on. We will show that the stealth task of each follower is achieved despite this slow bearing change.
Justh and Krishnaprasad 1 introduced Frenet–Serret frames 23 to model the movement of a target
where ut
is the steering (i.e. curvature) control of the target and vt
is the speed of the target, which is 0.7.
Recall we assumed that every follower localizes itself and accesses L in real time. Here, L denotes the infinite line crossing both the target and the leader. In practice, there is an error as a follower measures L in real time. Thus, in simulations, we generate a noisy target position
Each MATLAB simulation runs for finite time, at the end of which the distance between the leader and the target is equal to or less than 5 distance units.
Figure 6 shows the behavior of the system in the case where ut
in equation (14) is

The target and pursuer positions (
Figure 7 shows the behavior of the system in the case where ut in equation (14) is 0.1. We simulate noisy environments using std = 0.5. Figure 7 further shows both Ss and the bearing of each pursuer from the point of view of the target. The bearing of each follower almost converges to that of the leader. See that the stealth task of each follower is achieved as time goes on.

The target and pursuer positions (ut = 0.1).
Figure 8 shows the behavior of the system in the case where ut in equation (14) is 0.45 during the time interval from 50 to 60 s. ut is 0 outside this interval. In this way, we simulate abrupt maneuvers of the target. We also simulate noisy environments using std = 0.5. Figure 8 shows that as the target maneuvers abruptly, every pursuer maneuvers significantly under our control law. Figure 8 further shows both Ss and the bearing of each pursuer from the point of view of the target. The bearing of each follower almost converges to that of the leader. See that the stealth task of each follower is achieved as time goes on.

The target and pursuer positions (ut changes abruptly).
Conclusions
We introduce a motion control which is a strategy of a team of pursuers to approach the target without being detected. Our control law is to steer followers so that they remain stealthy under the cover of the leader with stealth abilities. We present MATLAB simulations to verify the performance of our motion control law.
Our motion control can be applied in various military scenarios. For instance, assume that the target is equipped with LOS weapons, such as cannons. The leader is equipped with defense systems to protect itself against the LOS weapons. On the other hand, followers are vulnerable to the LOS weapons. In this case, our motion control can be applied to attack the target while protecting all pursuers.
Footnotes
Authors’ note
This paper is novel and has not been published before. All figures/tables are created by Jonghoek Kim.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was financially supported by the Agency for Defense Development, South Korea and grants from Kyung Hee University in 2017 (KHU-20170717).