Abstract
In wireless sensor networks, sensing information must be transmitted from sensor nodes to the base station by multiple hopping. Every sensor node is a sender and a relay node that forwards the sensing information that is sent by other nodes. Under an attack, the sensing information may be intercepted, modified, interrupted, or fabricated during transmission. Accordingly, the development of mutual trust to enable a secure path to be established for forwarding information is an important issue. Random key pre-distribution has been proposed to establish mutual trust among sensor nodes. This article modifies the random key pre-distribution to a random secret pre-distribution and incorporates identity-based cryptography to establish an effective method of establishing mutual trust for a wireless sensor network. In the proposed method, base station assigns an identity and embeds n secrets into the private secret keys for every sensor node. Based on the identity and private secret keys, the mutual trust method is utilized to explore the types of trust among neighboring sensor nodes. The novel method can resist malicious attacks and satisfy the requirements of wireless sensor network, which are resistance to compromising attacks, masquerading attacks, forger attacks, replying attacks, authentication of forwarding messages, and security of sensing information.
Keywords
Introduction
Wireless sensor networks (WSNs) were originally developed as part of a military research project at UC Berkeley. 1 Sensor nodes therein are randomly deployed to the target area. After the random deployment, these nodes start to collect data, communicate with their neighboring nodes, and transfer and relay collected data to a base station (BS). With the increasing use of WSN in recent years, the security requirements of WSNs have become increasingly important.2–4 One of the security concerns of WSNs is the key agreement scheme for secure communication. 5 To resolve the heavy loading of public key infrastructure (PKI), the random key pre-distribution scheme (RKP) for WSNs was proposed. 6 However, the hardware of sensor nodes is not tamper-resistant, and once a sensor node is captured, the key information that is stored in the sensor node will be exposed to an adversary. Attackers could randomly capture nodes to retrieve the secret keys in them, and then use these keys to establish malicious nodes to eavesdrop on communication links. 7 To eliminate the weakness of storing plain keys, a combination of identity-based cryptography 8 and the random secret pre-distribution (RSP) scheme was proposed. 9 Based on the hard elliptic curve discrete logarithm problem (ECDLP), the RSP scheme can prevent exposure of the secret keys. This article presents a method of establishing mutual trust that is based on embedded random secrets, which is utilized to explore the relationship among sensor nodes. According to the relationship, a sensor node can set the pairing value to authenticate a forwarded message, as a session key, or to negotiate a session key for secure communication. The proposed method includes BS initialization, neighbor set building, the pairing process, the establishment of mutual trust, message authentication, and sensor information forwarding. The proposed method can resist malicious attacks and satisfy the security requirements of WSN. The computations that are involved in the proposed method can be implemented in a sensor node. Section “Related works and preliminary techniques” of this article will present related works and preliminary techniques. Section “Proposed method” presents in detail the processes that are involved in the implementation of the proposed method. Section “Security analysis and performance evaluation” presents a security analysis and evaluates the performance of the method. The last section draws conclusions.
Related works and preliminary techniques
This section describes works on secure WSNs and the preliminary techniques that will be used in this article.
Random key pre-distribution
Chan et al. 6 proposed the RKP scheme to perform key agreement for WSNs. In RKP, the BS holds a very large pool of keys, and sensor nodes are embedded in a random sub-set of these keys before deployment. In the WSN’s field, the sensor nodes will implement a challenge-and-response process to explore the common key among the sensor nodes, and use this common key to negotiate a session key for secure communication. However, the hardware of sensor nodes is not tamper-resistant, so once a sensor node is captured, the key information that is stored in it will be exposed. Attacks could randomly capture nodes to retrieve their keys, and use these keys to make malicious nodes to eavesdrop on some communication links. 7
Identity-based cryptosystem
In 1985, Shamir 8 proposed the identity-based cryptosystem (IBC) to facilitate key management in a PKI. In IBC, the public key generator (PKG) assigns a private key to every node, as determined the identity of the node and the well-known parameter. The node’s public key can be derived from the node’s identity. Hence, every node can make secure communication with another node, and the only required information about the other node is its identity.
Pairing function
In 2004, Boneh et al.
10
proposed bilinear pairing to perform key agreement. As specified in Table 1,
Bilinear
Non-degenerate
Computable
Notation associated with public information and function.
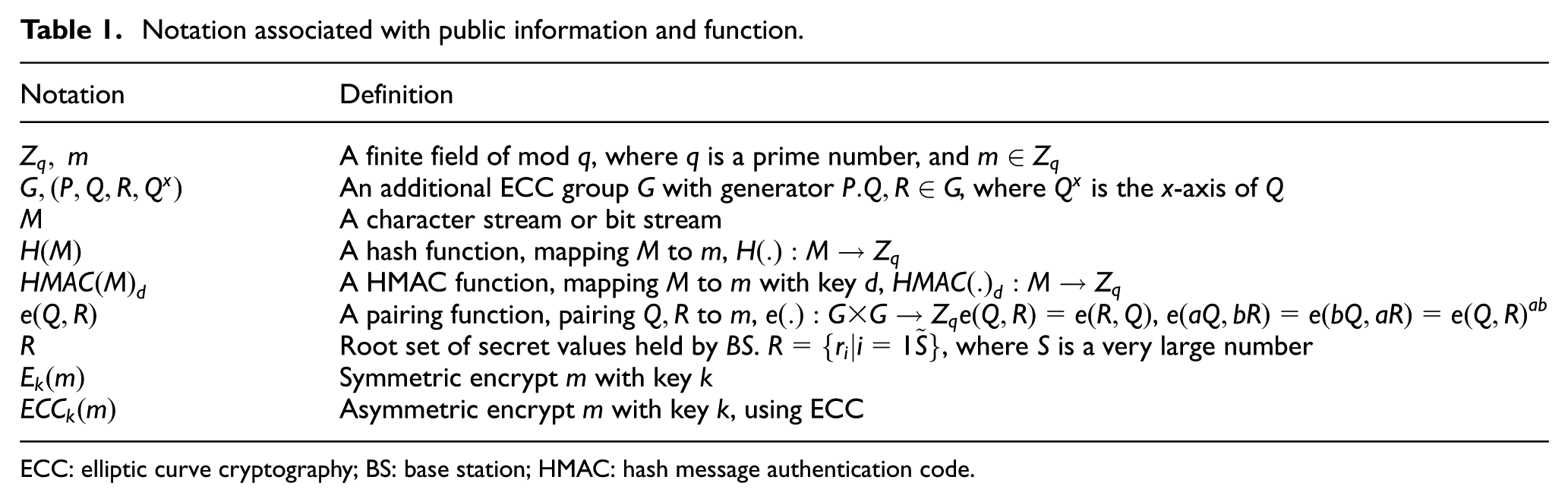
ECC: elliptic curve cryptography; BS: base station; HMAC: hash message authentication code.
Random secret pre-distribution
In 2013, Hsieh et al. 9 proposed RSP, which is based on the concept of IBC and the pairing function. In RSP, the BS maintains a very large pool of secret keys; it randomly chooses a sub-set of these keys, embedding each one in the sub-set in the public key of a node to generate that node’s private key. The public key is derived from the node’s identity. One node can pair the set of private keys with the public keys of another node to find the common secret that is embedded in the private keys of both nodes. Section “Proposed method” describes this scheme in detail description.
Mutual trust
For secure sending the sensed information, the sender node must explore the relationship of neighboring nodes to find a secure path for relaying sensed information. The PKI 5 may be a possible solution. But it suffered from the heavy loading for certificating verification. In 2009, Huang 11 proposed a mutual trust method that is based on elliptic curve and hash chain. In the following years, Kim and Lee, 12 Zeng et al., 13 and Lee et al. 14 pointed out the Huang’s weakness and fixed it under the attacking included replay, masquerade, and deny of service. But they all need time synchronizing and heavy storage loading. In 2014, Chen et al. 15 proposed a chameleon hash function-based trust method that did not need time synchronizing and table loading, but it still suffered from malicious nodes revoking.
Proposed method
Table 1 presents the notation associated with the public information and function that are used in this article.
The proposed method may involve sensor node i, j, or k. Table 2 presents information concerning these nodes.
Notation associated with sensor nodes.

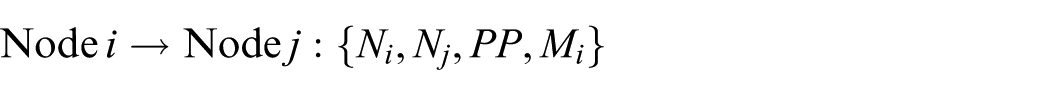
In the proposed method, communication will be performed between two sensor nodes. Table 3 presents the form of communication.
Form of communication.

The following sections will introduce the initialization of the BS and the deployment of nodes, building of a set of neighbors, the pairing process, indirect pairing, and proof of pairing.
BS initialization and deployment of sensor nodes
BS sets generate a very large secret pool R,
For every node (e.g. node i), BS randomly chooses a sub-set of

BS records
Establishing a set of neighbors
In WSN, node i holds
All hello:
Every node (e.g. node i) periodically says hello to its neighbors.
Collect all:
Every node (such as node i) collects all hello messages to build its neighbor set.

The default trust type is U, and the default PB is null.
Pairing process
After every node (such as node i) has built its neighbor set, it performs pairing with its neighbors
1. For all
Node i pairs all of its private secret keys
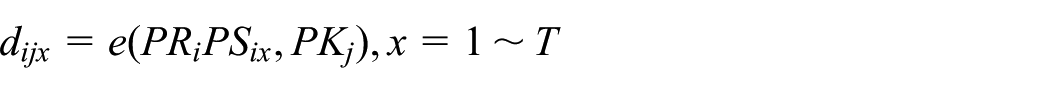
Then, node i sends a pairing message to node j
where
2. Node j receives

makes
Else, it returns NP to node i

3. Node i receives NP and does nothing;
next j goes to step 1.
Direct pairing
4. Node j sets

where
4.1. Node i receives
if so, the node goes to step 4.2; else next j goes to step 1.
4.2. Node i sets
next j goes to step 1.
4.3. Node j receives DR and checks whether
If so, it sets
else, the process ends.
Indirect pairing
Now, every node (such as node i) has established its set of neighbors with possible direct pairing. They will be a set of direct neighbors and a set of non-direct neighbors to ask its direct neighbors for possible indirect pairing.
Node i has
Node i sets the direct and non-direct sets as


Node k is in
1. For all nodes k in
Node i processes indirect pairing to node k

2. Node k receives message
Node k returns

3. Node i receives
For node x in
Mutual trust among the sensor nodes
Node i establishes its neighbor set

When
When

When
Communicating confidentially and sensing information forwarding
Every node has
Negotiation of session key between indirectly trustingneighbors
1. Node i sets SK as a session key; encrypts SK with
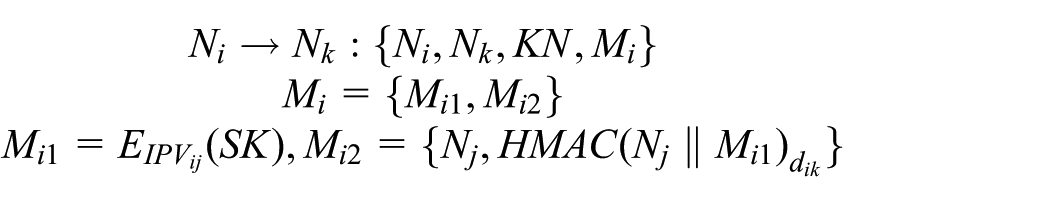
2. When node k receives the message, it verifies
If the verification fails, reject it.
Else,

3. When node j receives the message,
it verifies
If the verification fails, reject it;
else, gets
A message is returned to node i

4. When node i authenticates the return message, the SK becomes the session key for confidential communication between nodes i and j.
Forwarding sensed information
When node i wants to send sensing information (M) to the BS.
It randomly chooses one of
The forwarding process is as follows:
When BS receives the message, it verifies the message with
Proof of pairing with common random secret
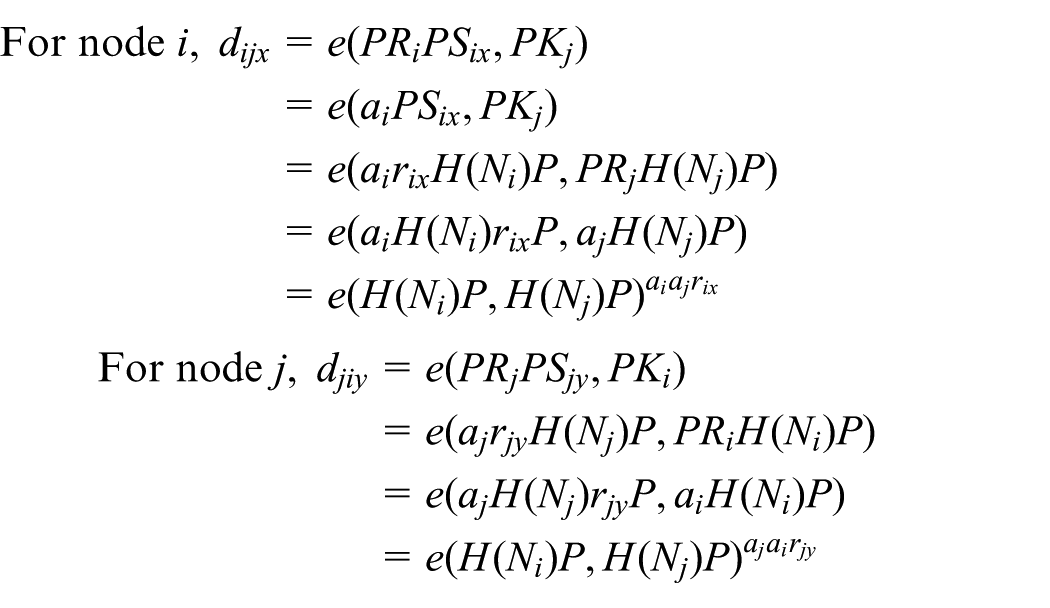
If any
Security analysis and performance evaluation
This section analyzes the security and evaluates the performance of the proposed scheme.
Security analysis
A WSN may be subject to many attacks, including compromising attacks, masquerading attacks, forgery attacks, and replaying attacks. To provide the required security of a WSN, the forwarded message must be authenticated and the sensor nodes must communicate confidentially with their neighbor nodes.
Compromising attack
An attacker who compromises a node can obtain information about its identity and its private secret key, but cannot retrieve any secrets from private secret key because the ECDLP is a hard problem. Therefore, such an attacker cannot issue the valid secret key to any malicious node.
Masquerading attack
In the proposed scheme, the mutual trust of two nodes may be based on common secrets, but these secrets are hidden using private secret keys. Therefore, no node can masquerade as having another identity without information from the secret pool. In establishment of the neighbor set, the exposed information includes only identity and public key, so an attacker cannot retrieve any private information. Therefore, masquerading attacks are impossible.
Forgery attack
In the forwarding of sensing information, this information is encrypted by the sensor’s private secret key, and the encrypted message is decrypted using the secret value that is only found in the private secret key. The hash message authentication code (HMAC) of the forwarded message is keyed with pairing value of the sender and the receiver. Without the secret value and the pairing value, an attacker cannot forge the sensing information and forwarding message.
Replay attack
The “hello” message is used to announce that the node is present, and neighbor nodes use the hello message to build the neighbor set. If the hello message is replayed, it affects one more neighbor, but this neighbor cannot establish mutual trust to perform any attack. The time stamp in the sensing information can resist the replay attack.
Authentication of forwarded message and security of sensing information
In the construction of a neighboring set, the pairing value, trust type, and pass-by node between two nodes are negotiated. The pairing value will be used for message authentication, session key negotiation, or confidential communication. If two nodes do not have a common secret, but do have a commonly trusted neighbor node, then they can negotiate the session key through the commonly trusted node. In the forwarding of sensing information, this information is encrypted using the sensor’s private secret key, and the encrypted message is decrypted using only the secret value in the private secret key. The HMAC of the forwarded message is keyed with pairing value of the sender and the receiver. Therefore, the sensing information can be retrieved only by the BS, and the forwarded message can be authenticated node by node.
Performance evaluation
This section discusses the probability that a node establishes direct or indirect trust with a neighbor to forward sensing information. The performance of the computations in initializing BS, construction a neighbor set, negotiating session keys, and forwarding sensing information are evaluated.
Probability that a node has no directly or indirectly trusted neighbor
As described in section “Proposed method,”S denotes the size of root secret pool in BS; T is the number of secrets in the node assigned by BS. Let the number of neighbor nodes be N.
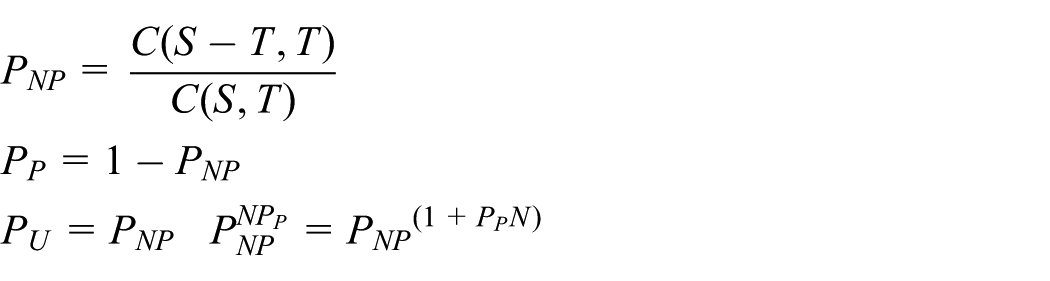
The
Performance evaluation
The proposed methods involve many computations, including bilinear pairing
BS initialization:
Establishment of neighbor set 2.1. All hello: 2.2Collect all: 2.3. Pairing process:
Negotiation of session key
For directly trusted neighbors:
For indirectly trusted neighbors:
4. Forwarding information
For sender (sensing node) and receiver (BS):
For forwarding nodes (relay nodes):
The computations in the proposed method are bilinear pairing, ECC multiplication, symmetric encryption, the hash function, and the HMAC function, which all can be implemented in the sensor node.
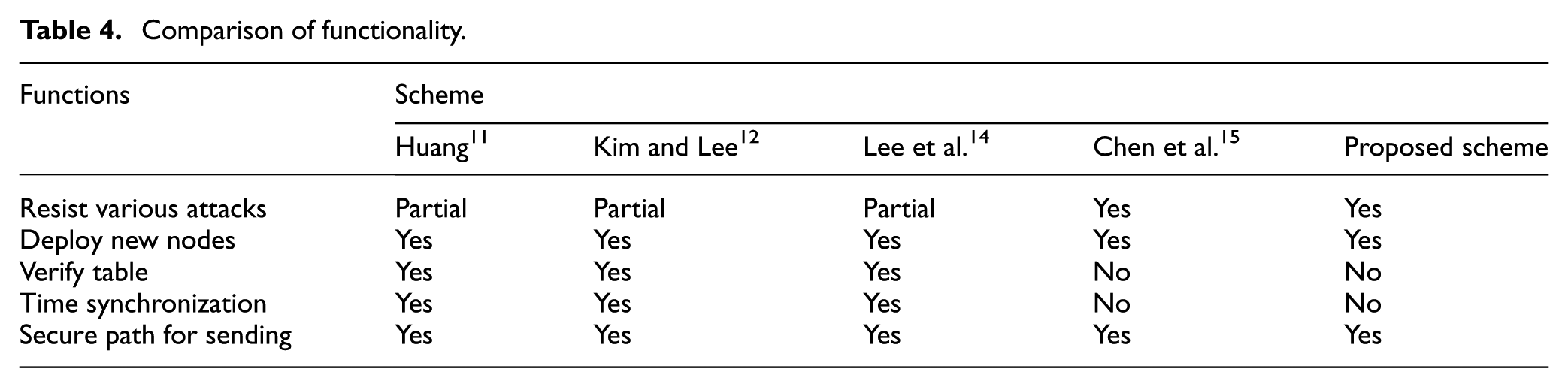
Comparison with the related works
The proposed method will be compared to Huang, 11 Kim and Lee, 12 Lee et al., 14 and Chen et al. 15 with respect to functions and performance in mutual trusting. Table 4 compares schemes in terms of functionality and shows that the proposed scheme fits all functional requirement without time synchronizing and verify table.
Comparison of functionality.
The BS initialization and establishing of neighbor set are performed offline, so the associated loading can be ignored. For secure forwarding the sensed information, the session key will be set to do message authentication so that we compare the computation cost of message forwarding and session key negotiation. The computation times for Tm, Te, Tn, and TH, measured on a 3 GHz Pentium 4 PC 16 are 0.6, 0.54, 0.002, and 0.002 ms, respectively. Table 5 shows the computation cost of message forwarding, computation cost of session key negotiation and the respective required times. In the proposed scheme, Te is the cost of session key negotiation, and the Tm + TH is the cost of encrypting and HMAC message forwarding.
Comparison of computation cost of message forwarding and session key negotiation.

Conclusion
In this article, the concept of RSP is utilized in a method for establishing mutual trust information forwarding path in a WSN.
In the proposed method, T private secret keys with an identity must be embedded in all nodes before they are deployed. At any time, the nodes set their private key to a random number and compute the respective public key, before announcing the identity and the key. Based on the identity and the public key, the neighboring nodes can implement the establishment of a neighbor set such that information about the announcing node includes the type of trust, the pairing value, and the pass-by node. Based on the information of the neighbor set, nodes can communicate confidentially, authenticate messages, and forward sensing information to the BS.
The sensing information will be encrypted by the private secret key of sensing node, and the encrypted sensing information can be decrypted only by the BS, because the secret value is in the private secret key. The encrypted sensing information will be forwarded to a directly trusted or indirectly trusted neighbor, and the pairing value of the sending node and receiving nodes is used as the HMAC key of the forwarded message. The forwarded message can be verified by HMAC. According to a probability analysis, the probability that the sensing information can be forwarded node-by-node to the BS is very high.
The proposed method resists malicious attacks and satisfies the security requirements of a WSN: it resists compromising attacks, masquerading attacks, forger attacks and replying attacks, enables authentication of forwarded messages, and secures sensing information. The computations in the proposed method are bilinear pairing, ECC multiplication, and HMAC, which can be implemented in a sensor node. The comparison shows that the proposed scheme is superior to the related works in terms of functionality and computation cost.
Footnotes
Academic Editor: Stephen D Prior
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This paper is based on some of the results of projects NSC101-2221-E-366-003, MOST103-2632-E366-001, and MOST104-2632-E366-001, which were supported by the Ministry of Science and Technology, ROC.


