Abstract
Creative, community-based methods are recognised for their ability to challenge top-down approaches and uncover alternative policy solutions. Despite their value, such methods often face criticism for lacking rigour. This paper addresses this concern by integrating participatory research with Bayesian Causal Process Tracing (CPT) to enhance methodological robustness, triangulate findings and provide actionable policy insights. Using a case study on female entrepreneurs in North Yorkshire, England, we adopt a multi-stage approach—combining interviews, focus groups, and problem trees—to identify key challenges female entrepreneurs face. Bayesian CPT is applied, a method that systematically traces causal mechanisms through diverse evidence sources. By moving beyond descriptive analysis, CPT weighs evidence, compares hypotheses, and strengthens causal inferences. Rather than simply identifying correlations, CPT reveals how and why a hypothesis affects an outcome by revealing the underlying mechanisms that shape causal relationships. In offering an empirical example, the logarithmic scale in Bayesian CPT (Fairfield & Charman, 2022) estimates the “loudness” of evidence. This provides a structured, interpretable way to assess causal strength. This approach offers a powerful tool for balancing community-driven insights with empirical rigour, strengthening the link between research and practical policy solutions. Beyond policymaking, triangulation and validation of participatory research, future research should look to incorporate and maximise the potential of Bayesian CPT, which is yet empirically underutilised.
Introduction
Established policymaking norms traditionally rely on technical expertise and democratic accountability, adopting a structured, evidence-driven approach that prioritises technical rigour. Critics argue that creative methods lack the systematic rigour of these established processes (Lewis et al., 2020), yet there is growing recognition that creative, community-focused methods, far from undermining policy foundations, enhance rigour by supporting place-based insights and seek alternative policy responses that may otherwise be unknown to policymakers and missed by top-down approaches (Considine, 2012; Ison & Straw, 2020; Rodriguez & Komendantova, 2022). While creative methods incorporate robust analytical steps, this study demonstrates how its methodological rigour can be intensified through systematic triangulation. This research employs Bayesian causal process tracing (CPT) to validate qualitative findings derived from participatory workshops with female entrepreneurs in North Yorkshire, England. This approach exemplifies how creative methods can maintain innovation while strengthening empirical foundations through causal analysis.
CPT systematically examines evidence to trace causal chains in social and political phenomena, addressing limitations of descriptive and statistical analyses by illuminating underlying causal mechanisms and give insight into how something occurred (Crasnow, 2017), often called causal process observations (CPOs) (Podestà, 2023). CPT enables researchers to incorporate diverse evidence sources (Gonzalez-Ocantos & LaPorte, 2021), conduct within-case analysis (Green et al., 2022), examine evidence in a temporal sequence (Collier et al., 2010) and engage in both theory-testing and theory-building (Hall, 2006; Mahoney, 2015; Schimmelfennig, 2014). While CPT is popularly underpinned by Van Evera’s (1997) four tests (see also Collier, 2011; Mahoney, 2012) this paper adopts Bayesian CPT. As outlined by Fairfield and Charman (2022), Bayesian CPT provides an intuitive framework for assessing the strength of hypotheses by expressing their plausibility in decibels, indicating whether a hypothesis is ‘loud’ (strongly supported) or barely audible (weakly supported). This approach is particularly valuable when triangulating data from participatory and creative methods, integrating multiple data sources and evaluating underlying mechanisms of causality. By linking descriptive evidence to relevant policy outcomes, this approach helps bridge the gap between empirical analysis and practical application (Bijak et al., 2021).
This paper proceeds as follows: The participatory research methods and data analysis employed are first described before qualitative validation techniques and rigour are discussed. CPT is offered as a method to strengthen rigour of participatory data, demonstrated through its empirical application of the logarithmic approach of our case study.
Methodology
Qualitative research allows for the development of causal processes and mechanisms that inform hypotheses and relationships, which includes collaborative methods such as participatory action research (Kopec, 2023), offering an effective basis to combine participatory methods with CPT.
Participatory research methods are particularly well-suited for our study on the challenges faced by female entrepreneurs. Creative and participatory approaches emphasise more active, open and inclusive policymaking processes (Broadley & Dixon, 2022; Considine, 2012) and highlight the value of local knowledge in assembling processes that bring together people, ideas, and spaces to co-create policy and generate knowledge (Braye & McDonnell, 2013; Escobar, 2013). By engaging local people in the research process, we gain a deeper understanding of the specific challenges they face.
This research adopts a multi-stage approach that incorporates qualitative data from five focus groups (4 in-person and 1 online, n = 32) and a small number of purposefully sampled interviews (n = 4) to ensure inclusion of intersectional identities and characteristics. This formed the exploratory work ahead of hosting a participatory workshop. Access to participants was made possible due to the collaborative nature of this research between the researcher and the Federation of Small Businesses.
The leading researcher is a woman and sharing the gender identity of participants may have fostered a sense of trust and rapport, potentially encouraging openness and richer data sharing. This might have helped participants feel comfortable discussing challenges unique to female entrepreneurs. However, the researcher’s position as an outsider to the entrepreneurial community could also affect interpretation, and the nuances captured. The presence of other ‘insider’ members from the research collaboration provided valuable contextual understanding and facilitated the emergence of relevant, community-grounded insights.
Thematic analysis of transcripts from the focus groups and IDIs, conducted using NVivo software, identified key themes or challenges for exploration during the workshop. The transcripts underwent open coding through an inductive, iterative process before axial coding to form categories based on interlinkages between the identified codes. Continued familiarisation with the data facilitated further iterative coding. Engagement with collaborative research partners aided a critical reflection on the emerging categories. This external perspective helped to challenge assumptions and enhance the credibility and trustworthiness of the analysis. Subsequently, these categories were organised into thematic groups. Throughout the coding process, reflexive and iterative coding, alongside discussions of key themes with the collaborative research group, helped guard against subjective bias. Additionally, the researcher’s familiarity with the data from collection necessitated careful attention to minimise selective memory from impacting the coding process. To address this, the researcher engaged in ongoing reflexive practices, critically examining assumptions and interpretations.
While the workshop had seven key challenges, each derived from thematic areas generated, this paper focuses on the issue of customer acquisition and retention, as illustrated in Figure 1. Other themes included lack of confidence, balancing work-life and access to finance/funding. Problem Tree on Retaining and Acquiring Customers
Approximately 35 female entrepreneurs from the region participated in a workshop focused on several problem and solution trees (PASTs). Popular in development studies, the problem tree is a useful tool for communities to order their cause-effect relationship (Chevalier & Buckles, 2013; Hinds, 2013), circumnavigating the restrictions of linear problem-solving approaches (Salinas, 2022). Subsequently, to provide corrective actions, evidence on a problem tree can be followed by converting the causes and effects into means and ends through a solution tree (see Sapkota et al., 2024).
Participants began by reflecting on the key challenge identified in their problem tree and used sticky notes to record what they believed to be the root causes of that challenge. Next, they considered the consequences that this challenge has on their daily lives and entrepreneurial aspirations, writing these reflections on the leaves of the tree. In the final step, participants grouped their responses into broad themes, creating colour-coded clusters for both root causes and consequences to visually represent related ideas on the problem tree. These identified causal relationships will be validated to ensure that resulting policy recommendations are well-targeted and evidence-based.
Participants reframed their reflections into actionable solutions using star-shaped sticky notes beside the thematic clusters of sticky notes developed at the workshop. Actionable solutions are interventions that can be implemented through policy or changes to address the root causes and consequences identified in the problem tree. This step aimed to generate feasible policy responses that directly target the underlying issues and their effects. Validation of cause-effect relationships identified through the problem tree can inform subsequent workshopped solutions.
Qualitative Validation and Rigour
Although design-led or human-centred approaches such as design thinking are popular (Lewis et al., 2020), such methods are not without drawbacks as a lack of policy-focused research can lead to unactionable generalised recommendations. 1 Strengthening policy impact requires the use of robust qualitative validation frameworks and subjecting data to rigorous standards, including credibility (such as ethical conduct, credible sources, and appropriate research design), contextualisation, and iterative processes like coding. Rigour is further ensured through transferability, dependability (e.g., audit trails or reflexive journals), and confirmability via triangulation by cross-checking findings across sources, combining methods, or involving multiple researchers or analysts.
Building on these standards, evaluation studies have introduced innovative approaches to strengthen causal inference and impact assessment. Contribution Analysis (CA), for example, is discussed by Mayne (2012, p.270) as an “approach to confirming that an invention is a contributing cause”. He notes that CA is valuable because it constructs a case for an intervention’s contribution within a theory of change. An empirical example is offered by Delahais and Toulemonde (2017) who applied CA to assess whether programmes led by the Centre for International Forestry Research (CIFOR) contributed to sustainable forest management in the Congo Basin. Also enhancing qualitative evaluation, Remnant et al. (2024) highlight the Qualitative Impact Protocol (QuIP), which collects narrative causal statements from those affected by an intervention through ‘double-blindfolded’ interviews, where neither party knows the intervention details. Copestake (2025) discusses QuIP’s value in complex contexts and its push for more systematic, transparent qualitative evaluation. While QuIP is a standalone method, it can complement approaches like process tracing.
Building on this, this paper offers logarithmic Bayesianism as another validation technique that can aid in enhancing qualitative rigour and evaluation methods.
Causal Process Tracing (CPT)
Whilst CPT does not have one singular definition (see Trampusch & Palier, 2016), it is a qualitative research method generally understood as a within-case analysis like detective work where the researcher builds upon suspects (or theories) and clues (evidence) (Bennett, 2023). Maxwell (2004) contends that quantitative methods favour a variable-oriented approach, treating causation as an unobservable process and focusing solely on systematic relationships between inputs (X) and outputs (Y). Maxwell stresses that the link between X and Y is not fixed but context-dependent, shaped by the mechanisms at work. Gerring (2010, p. 1500) builds on this, arguing that a focus on causal mechanisms offers an alternative to positivist notions of causality, which often reduce causation to a mere “probabilistic association between X and Y.” Instead, Gerring underscores the importance of examining generative components, i.e., the actual processes through which X influences Y.
A key strength of CPT is that it uses mechanisms to describe the unobservable physical, social, political and psychological phenomena to illuminate and evaluate causal claims by opening the ‘black box’ of underlying causal mechanisms (Beach, 2016; Collier, 2011; Kay & Baker, 2015; Trampusch & Palier, 2016). Unlike variables, mechanisms are theoretical constructs that explain recurring relationships and clarify why X causes Y (Hall, 2013), such that:
A key advantage of CPT is the ability to collect a range of evidence to incorporate into analysis to determine the strength of hypotheses, and to enable the researcher to establish the weight of causation or the likelihood of one hypothesis over another. The researcher goes through a ‘soak and poke’ open-ended research to immerse themselves in a case (Bennett, 2023; Gonzalez-Ocantos & LaPorte, 2021) and provide thick description (Byrne et al., 2009).
From a policy perspective, it is often more important to know what effect a treatment has an on outcome than why it has that effect (Gerring, 2010). However, adequately addressing complex issues requires dismantling the messy and complex underbelly of social interventions (Byrne et al., 2009) to adequately understand the complex issue in the first place, to then appropriately develop a policy response. For example, solely focusing on the effect of a sugar tax in reducing confectionary consumption, overlooks the underlying mechanisms behind this outcome, which could include tougher family finances, more awareness of healthy eating, etc. CPT is useful for dealing with complex systems that do not have sharp boundaries and should be understood as a series of flows that can transform over time (Byrne, 2024). It is also useful in this context to demonstrate the relative strength of competing hypotheses on an outcome.
Bayesianism
Advances in CPT and its links to Bayesianism has prompted some scholars to go so far as to say that Bayesianism is the only sound approach for causal analysis within qualitative data as it provides a clear framework for scrutinising inferences and pinpointing sources of disagreement (Fairfield & Charman, 2022). While Bayesianism can be used in comparative analysis, generally with typical and deviant cases, small-N comparisons or within-case studies are more useful for assessing causal theories as the researcher can investigate causal processes in detail (Hall, 2003). While there is some disagreement over the use of deductive and/or inductive characteristics of CPT (see Checkel, 2021), it is an iterative process where inductive investigation can alter our hypotheses and the values ascribed to competing hypotheses.
The first step of Bayesianism is in clarifying the research question and hypotheses. The researcher must develop a well-defined theoretical framework and theorise the causal pathways leading to an outcome (Ulriksen & Dadalauri, 2016), requiring careful consideration of factors such as the mutually exhaustive and exclusive nature of chosen hypotheses. Typically, Bayesian scholars advocate for the assessment of rival hypotheses to determine which hypothesis has a greater probable impact on the outcome. However, this research assesses a hypothesis
After clarifying the research question and hypotheses, priors are identified, i.e., theoretical and verifiable expectations (Ulriksen & Dadalauri, 2016). This is the initial view on the plausibility of a hypothesis (Fairfield & Charman, 2022). Generalist knowledge informs arguments about a plausible prior probability, but this informal step can be formalised by relying on a structured evidence synthesis (Behrens & Rohlfing, 2025). How prior probabilities are assigned differs depending on the model of Bayesianism employed. In heuristic Bayesianism, a fraction of 1 is assigned to each hypothesis. For example, in the case of two rival hypotheses, equal priors of 0.5 may be assigned to each hypothesis, or, if prior knowledge favours one hypothesis over the other, priors such as 0.7 and 0.3 can reflect this preference. The researcher must clarify why there is a preference. This is represented through Bayes’ rule where:
P (probability),
Qualitative to Quantitative Correspondence (dB): (Fairfield & Charman, 2022, p. 133)

Typical Sound Levels (dB): (Fairfield & Charman, 2022, p. 134)

After assigning a dB level to the prior probability, the next step is to incorporate the likelihood ratio or the weight of evidence (WoE). Documenting different aspects of the causal story often requires evidence from different sources (Collier, 2011). For example, where national economic statistics may authenticate a key step in a causal chain, it might also be necessary to conduct interviews with policy makers to account for the mechanisms that led to the particular state of affairs (Gonzalez-Ocantos & LaPorte, 2021). Bayesian process tracing prefers unstructured evidence because it has a greater exploratory potential and a higher probability of generating observations for alternative hypotheses (Kreuzer, 2016). In Bayes’ rule, the likelihood ratio is represented as:
The total WoE can be decomposed into separate calculations per each evidence such that:


The researcher evaluates each piece of evidence individually, assigns a dB value, and then calculates a total sum that considers all the evidence. Each piece of evidence can add dBs, take away, or have no effect where the evidence neither strengthens nor weakens the hypothesis. A dB value is assigned after inhabiting the world of the hypothesis and asking how expected (high probability) or surprised (low probability) the evidence would be (Fairfield & Charman, 2022).
Finally, we move to the posterior probability:
Posterior odds = prior odds x likelihood ratio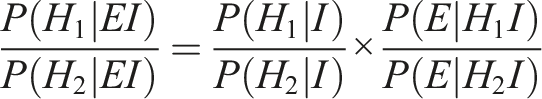
However, this research instead refers to the logical negation of the hypothesis, as the objective is not to test the relative strength of one hypothesis against another but rather to use Bayesianism as a triangulation and validation tool. Testing a hypothesis in isolation increases the risk of researcher bias, where only supporting evidence is sought. By evaluating the logical negation, evidence for and against the hypothesis is collected. In Bayes’ rule, the equation of logical negation is: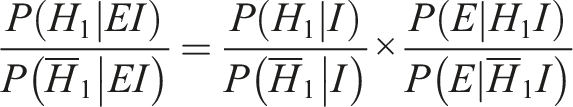
However, given that a logarithmic scale is adopted, the execution of the equation looks slightly different as the odds of 
Step-by-step Guide

Discussion
The research question is: What challenges do female entrepreneurs face in acquiring and attaining customers?
Hypotheses, Mechanisms and Outcomes
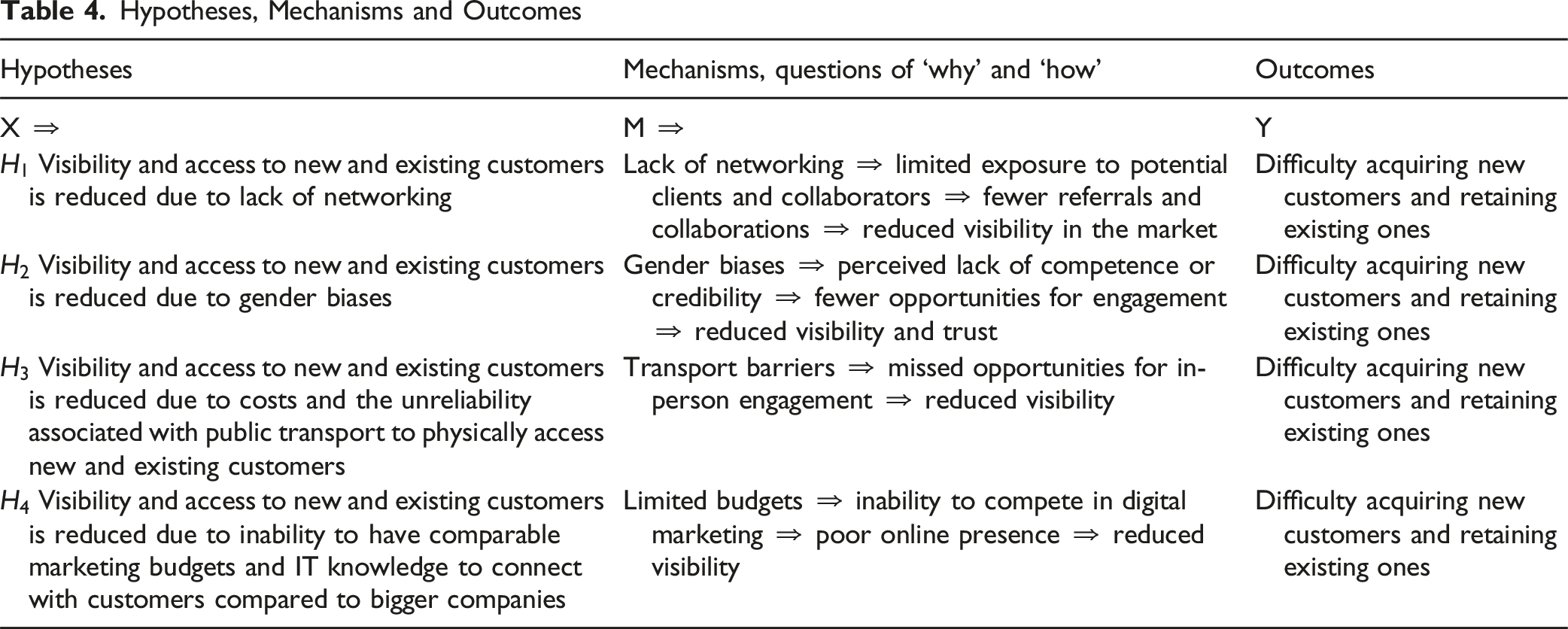
For illustrative purposes and to manage the breadth of available evidence, this paper applies logarithmic Bayesianism CPT to the first hypothesis and its logical negation (
A limitation of this study is that decibel assignments were made by a single researcher. However, the process was iterative, involving individual assessment of each source contributing to a piece of evidence, followed by a review of all sources for that evidence. Later, the relative strength of each evidence was reconsidered in the context of other evidence (e.g., vs. E0, E1, E2, etc.) to ensure balanced scoring. This approach, combined with a range of primary and secondary data, enhanced the robustness and validity of the scoring. Peer-reviewed articles are included among the secondary sources, increasing the credibility of the evidence base and supporting triangulation, as emphasised by Delahais and Toulemonde (2017), who highlight the importance of authoritative sources in strengthening evaluation credibility. Triangulation is further enhanced by drawing on independent sources, to reduce bias and provide a more comprehensive evaluation.
Assigning Priors
Prior Probabilities

The Weight of Evidence (WoE)
Throughout the evidence gathering and analysis, this study seeks to open the ‘black box’ of causality by identifying and explaining the mechanisms that produce observed outcomes by analysing evidence from primary and secondary sources.
Secondary sources consistently highlight the gender-specific challenges female entrepreneurs face, including societal perceptions, self-confidence barriers, and household responsibilities as structural biases. However, there is relatively limited literature focusing explicitly on female entrepreneurs’ access to new customers as limited due to lack of networking. This gap became evident through systematic searches of peer-reviewed literature, where limited relevant results necessitated both methodological refinements and careful inclusion of international studies with directly applicable findings (see Appendix A). The discussion reviews each piece of evidence and its supporting evidence sources in turn. The remainder of the discussion will focus on E0-E3 with inclusion of E4-E7 in Appendix B.
The Weight of Evidence


Primary research reveals that female entrepreneurs in non-urban areas face significant challenges in accessing professional networks, largely due to inadequate public transport and limited knowledge of where to find networking opportunities. This issue is particularly pronounced in rural regions. One interviewee expressed the dilemma succinctly: “It’s a choice, yes, fine, live rurally, but it’s how you access the bigger places … I feel disadvantaged because of that. Particularly for my type of career.” These transportation difficulties directly impact access to valuable networking opportunities, which are often concentrated in urban centres. As one entrepreneur noted, “I really miss out on the networking opportunities because they are fabulous in Leeds. They really are. You could go out every night and network with people that obviously bring about opportunity, and we just haven’t got that here.”
Delahais and Toulemonde (2017) note data credibility and reliability when the same themes emerge within different stages of the primary data collection. Indeed, this is true of the focus groups and IDIs where the same themes around rurality and transport as barriers to accessing networks emerged. These accounts highlight several interconnected challenges faced by non-urban female entrepreneurs, including the time and resource investment required to travel to nearby cities, the limited availability of local networking options, especially for those outside dominant regional sectors, and reduced visibility to potential customers. The evidence strongly suggests that rural and coastal entrepreneurs face distinct disadvantages compared to their urban counterparts, where networking opportunities are more plentiful and accessible.
However, this primary evidence, drawn from the rural and coastal sample, indicates that refining the hypothesis to focus specifically on non-urban participants would likely increase the strength of this assessment. Such refinement underscores the importance of geographic context in understanding the networking challenges faced by female entrepreneurs outside urban centres.
Considering that the sample holds both urban and non-urban participants, if one inhabits the worlds of the two hypotheses, i.e., the hypothesis and its logical negation to determine the strength of the causal relationship between networking and customers as developed through the causal-linear pathways in the PASTs, the evidence is in favour of
By examining these issues in depth, the analysis opens the ‘black box’ of causality, revealing the underlying mechanisms, such as geographic isolation and transport barriers, that explain how networking challenges reduce customer acquisition for non-urban female entrepreneurs.

Research underscores the multifaceted value of networking for female entrepreneurs. Bozkurt et al. (2022) in their study of a female entrepreneur operating a circular business, acknowledge that while some view networking as a ritualistic exercise, it nonetheless provides substantial benefits, particularly in facilitating knowledge-sharing. Similarly, Nevi et al. (2024) emphasise the role of networks in developing human capital, reinforcing the idea that access to diverse connections is instrumental for entrepreneurial growth. This is echoed in primary accounts from female entrepreneurs, who describe the tangible consequences of limited networking: “information-sharing is limited. It means I don’t get to know what’s going on out there. Those are the challenges that I have face, that I keep facing, and I hear a lot of other female entrepreneurs talk about.” Another participant elaborates: That’s where it’s a real challenge if you don’t have that network and you just focus on one thing, and you don't have the flexibility to go out and meet other people, then you’ll never grow, well, it’ll be a challenge to grow. It’ll be really tough. That’s one way of really expanding knowledge.
Beyond simply acquiring knowledge, entrepreneurs also recognise the strategic value of building networks that extend their own expertise. As one participant explained, “I want to create a good network that I can refer to if my expertise doesn’t cover that client.” This perspective highlights that effective networking is not only about personal gain, but also about being able to connect clients or collaborators with the right expertise within a broader network.
The importance of networks is further highlighted in The Alison Rose Report (2019), which advocates for centralised, government-led information initiatives designed to create a first-stop information shop for entrepreneurs. The report notes that improving access to information is critical for both men and women but also observes that “women are more likely than men to identify networks as an important source of business help” and that networks function as “loose umbrellas of connections that allow like-minded individuals to meet, compare notes and seek informal advice” (The Alison Rose Report, 2019, p. 68).
Limited access to networking not only restricts information sharing but also reduces visibility and access to key resources such as funding, training, and mentorship. Exclusion from these circles makes it more difficult to stay abreast of industry developments and to understand evolving customer needs. Primary data shows consistency with findings in secondary sources, raising the likelihood ratio to a level comparable to the difference between a quiet bedroom and a moderate rainstorm as the findings are both supported by triangulation of multiple data sources and authoritative data source types. Evidence shows the substantial impact that restricted networking has on the opportunities and growth potential of female entrepreneurs.

HSBC’s 2019 report, She’s the Business, while primarily focused on investment and securing capital, also highlights the importance of supporting female trailblazers and emphasises the role of banks in facilitating introductions to collaborators with other organisations. Similarly, the Global Entrepreneurship Monitor (GEM) (2024, p. 67) notes that “incubators, accelerators, and co-working spaces specifically for women entrepreneurs in male-dominated contexts can foster collaboration, mentoring, and access to resources”. GEM (2024, p. 69) further argues that “collaboration between startups and established businesses can accelerate innovation”, and stresses the critical role of networks in education, mentorship, and market access. Ozkazanc-Pan and Clark Muntean (2018) also highlight that incubators help female entrepreneurs to access customers and potential partners, underscoring the importance of such environments in facilitating collaboration and business growth.
The impact of network access on business growth leaves a clear “signature” or “fingerprint” in the evidence, as discussed by Delahais and Toulemonde (2017). This is evident in the experiences of entrepreneurs who become well-networked, consistently reporting increased opportunities and visibility. As one participant described, “we just became essentially well-networked. Because of that, a lot of opportunities came our way. So if there was any funding or any events to be put on, our names were always at the top of the list.” This recurring pattern where greater network access consistently leads to enhanced visibility and more opportunities serves as a fingerprint of the causal relationship between networking and the ability to scale a business.
However, networking opportunities and their collaborative benefits are not equally accessible to all entrepreneurs. Treanor and Marlow (2025) highlight that females are underrepresented in sectors such as STEM and in business incubators, where support structures often reflect a gendered landscape. They argue that gender, as a social construct, shapes power dynamics within networks, affecting females’ confidence and ability to engage effectively in networking activities that lead to collaboration and investment readiness. Ozkazanc-Pan and Clark Muntean (2018) further explain that females often lack access to informal social networks, such as the “old boys club,” which limits their ability to build and leverage social capital. Their research also suggests that females tend to approach networking through relationship-building and mutual support rather than transactional exchanges, fostering collaborative environments that encourage learning and shared growth. This indicates that females may be less likely to benefit from the transactional aspects of networking in the same way as male entrepreneurs. This context helps to explain concerns raised by Treanor and Marlow (2025), who note that female mentors often encourage female entrepreneurs to adopt more ‘masculine’ qualities when networking.
Many networking groups remain exclusionary, with one participant describing them as “men-only clubs” and another recounting an experience where a male counterpart dismissed her business expertise during a networking event: One of the things, challenges, there was this networking event I attended a couple of months back, and there was this guy, when everyone’s pitching, and this guy sounded really interesting. So I thought, I’ll have a chat with him, see what we can do together. So I went to speak with him and instantly he decided to teach me about my business.
Despite some negative experiences of networking for collaboration, there is a general consensus of its value in fostering business growth and support when expanding a clientele base. The evidence shows the importance of fostering introductions and collaboration with other entrepreneurs. Not only does this expand the network of the entrepreneur and facilitate knowledge sharing, but it also gives way to collaboration, which in turn can open a new customer base. Collaboration can enable entrepreneurs to scale their businesses and encourage high growth. Evidence also highlights the role of gender bias in networking opportunities and points out that female entrepreneurs are comparatively less likely to experience such benefits in contrast to their male counterparts. There is a moderate confidence reflecting recognition of challenges but consistent evidence of positive collaborative outcomes. The evidence is in favour of

While networking provides female entrepreneurs with valuable support, such as mentoring, confidence-building, and collaborative brainstorming (Ricciardi et al., 2025), its direct impact on business growth remains tenuous. Access to networks is often framed as essential for entrepreneurial success, yet many face a lack of peers and mentors, limiting their growth potential (HSBC, 2019). Evidence suggests that networks often foster solidarity (e.g., female-led “communities” rather than transactional exchanges) and emotional resilience, but their translation into concrete commercial outcomes such as customer acquisition or retention, is weakly correlated.
This aligns with Ozkazanc-Pan and Clark Muntean's (2018) observation that women approach networking in a less transactional and more supportive manner, as reflected in the primary data: “I think there is more networking, but there is less network … It’s very much women helping other women … I think if you changed the word ‘network’ to ‘community’, then I think that's what I find.”
Moreover, while familial support in culturally specific contexts (George & Dhaliwal, 2024) aids entrepreneurs through financial and informational resources, such dynamics operate independently of formal networking structures. This further underscores the limited causality between networking and commercial success. Additionally, George and Dhaliwal (2024) note that networking fails to mitigate structural barriers, such as sexism from male-dominated customer bases, demonstrating that support systems rarely override systemic constraints. Even when women do gain access to networks, these connections, while valuable for personal encouragement and motivation (O’donnell, 2014), often lack the strategic influence or industry leverage needed to drive significant growth.
Some research suggests that networking can indirectly contribute to business growth by expanding support circles and improving SME performance. John (2024), for instance, argues that entrepreneurial networks, social, business, and supportive, enhance learning, product quality, and customer attraction. However, these findings are context-dependent, emerging from studies in informal economies like Tanzania, and may not be generalisable.
Even where social and business networks improve SME performance metrics (e.g., customer retention strategies), the link between networking and tangible business growth remains weak. While support networks may boost confidence and provide mentorship, access to customers is a secondary benefit rather than a direct outcome. As one entrepreneur notes: I think it’s so short-sighted of businesses not to work together if you’re in the same field, or in any field. I’d be happy to help anybody out if I could. I was more than happy, I think, to tell you I don’t see you as competition. Obviously, were in the same field. There’s lots of business to go around.
This sentiment highlights networking’s emphasis on collaboration over competition, reinforcing its role in community-building rather than direct commercial gain.
This analysis unpacks the underlying causal mechanisms shaping networking for female entrepreneurs, emphasising emotional and social support while revealing why these benefits often fall short of driving direct business growth. By opening the ‘black box’ of causality, the study moves beyond surface correlations to illuminate the nuanced roles networks play in fostering entrepreneurial resilience and growth constraints. Indeed, evidence shows that networking’s benefit for female entrepreneurs lies in non-transactional support rather than in measurable business expansion and this is evidenced in both primary and secondary data collected, which triangulate to support the probability of



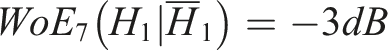
This results in a total of 59 dB in favour of the hypothesis over its logical negation:
Posterior Probabilities
Finally, turning to the posterior probability, i.e., the total probability of a hypothesis taking the prior probability and the WoE into account to determine the probability of 


There is overwhelming evidence in favour of
Conclusion
This paper demonstrates the application of explicit Bayesian analysis using a logarithmic scale to validate qualitative data. The method allows researchers to transparently assess the strength of causal relationships in hypotheses, considering the mechanisms between hypotheses and outcomes. While not providing definitive judgments (Fairfield & Charman, 2022), it offers an approach to grounding and contextualising hypothesis strength. The method incorporates various sources to demonstrate hypothesis volume and can be used to compare hypotheses or validate a single hypothesis against its negation. In this case, overwhelming evidence supports
CPT while useful for articulating the volume of a hypothesis, has some limitations. It can be a time-consuming process and resource constraints may necessitate prioritising hypotheses that are uncertain or warrant further investigation. Researchers must balance data quality and quantity, using discretion to determine an appropriate stopping point. This decision-making process is like those encountered in field research and literature reviews, where researchers must weigh the trade-offs between thoroughness and resource availability. A challenge of solely relying upon CPT is that policy initiatives are often developed on the assumption that strategic action can be understood through analysis of simple cause-and-effect mechanisms (De Smedt & Borch, 2022). Therefore, CPT should be grounded in its environment in a more holistic way.
Inevitably, researcher positionality and potential bias can be called into question when applying decibel scores. Positionality was addressed through researcher reflection and noting that no males participated. While the primary research shouted loudly in favour of a hypothesis, a very loud decibel score above 20 db was not awarded both to reflect the data collected, and to correct for any researcher bias. This method could be furthered strengthened by a larger research team that independently assess pieces of evidence to ensure consistency of dB application. To offer a detailed rationale for dB ratings within the context of the research topic, it is recommended that greater narrative analysis of the evidence be conducted, particularly in relation to policy formation or theory-testing/building, to provide more detail and validate the dB awarded.
Beyond using Bayesian CPT to offer validation to creative and/or participatory methods, the method, yet relatively underutilised, could be incorporated into policy feedback literature where mechanisms remain unknown (Campbell, 2012; SoRelle & Michener, 2022), further aiding with the problem of feedback effect directions. CPT can also be incorporated into evaluation studies (Podestà, 2023; Rothgang & Lageman, 2021) and is also an ideal method to understand institutional change (Skarbek, 2020). Ultimately, this paper presents an empirical application of logarithmic Bayesian CPT, marking only the beginning of its potential applications.
Supplemental Material
Supplemental material - Amplifying Insights: How Logarithmic Bayesianism can Validate Causation in Participatory Policymaking Methods
Supplemental material for Amplifying Insights: How Logarithmic Bayesianism can Validate Causation in Participatory Policymaking Methods by Rebecca Kerr in International Journal of Qualitative Methods.
Footnotes
Acknowledgements
The author would like to thank the participants of this research in giving up their time and contributing so openly to this research. The author would also like to thank the support of those involved and who enabled this research, including those at The Federation for Small Businesses and Enterprise Works and The York Policy Engine (TYPE) at the University of York. The author would also like to thank the anonymous reviewers who provided considered reflections.
Ethical Considerations
Ethical approval was granted by the Social Policy and Social Work Ethics Committee at the University of York.
Funding
This research was supported by a research grant from Research England Development (RED) funding, which has funded the Yorkshire and Humber Policy Engagement Research and Network (Y-PERN) that enabled this research.
Declaration of conflicting interests
The author declares no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Supplemental Material
Supplemental material is available online.
Note
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.


