Abstract
Internet of Things devices are responsible for collecting and transmitting data in smart cities, assisting smart cities to release greater potential. As Internet of Things devices are increasingly connected to smart cities, security and privacy have gradually become important issues. Recently, research works on mitigating security challenges of Internet of Things devices in smart cities mainly focused on authentication. However, in most of the existing authentication protocols, the trustworthiness evaluation of Internet of Things devices in smart cities is ignored. Considering the trustworthiness evaluation of Internet of Things devices is an important constituent of data source authentication, in this article, a cloud-aided trustworthiness evaluation mechanism is first designed to improve the credibility of the Internet of Things devices in smart cities. Furthermore, aiming at the problem that the user’s privacy is easy to leak in the process of authentication, an anonymous authentication and key agreement scheme based on non-interactive zero knowledge argument is proposed. The proposed scheme can ensure the privacy preservation and data security of Internet of Things devices in smart cities. The security analysis demonstrates that the proposed scheme is secure under q-SDH problem. The experimental simulation indicates that the performance of the proposal is greatly improved compared with other similar schemes.
Keywords
Introduction
With the continuous increase of population in cities and the formation of new urban agglomerations, the problems caused by urbanization, such as traffic jams, environmental degradation, lack of resources, and the decline of residents’ quality of life, have become increasingly prominent. The concept of smart cities was proposed to realize the sustainable development of the cities. 1 Information and communication technologies are showing an increasingly accelerating development trend in the world. 2 A series of key technologies, such as 5G network, Internet of Things (IoT), cloud computing, big data analysis, new generation geographic information systems, are gradually carried out from the proposal of the concept to the actual application landing. These technologies give birth to many emerging urban application scenarios and innovative management modes, bringing more opportunities for the construction of smart cities. 3
In the architecture of smart cities, the terminal perception layer provides the ability of intelligent perception of the physical environment and realizes the identification, data collection, monitoring, and control of the infrastructure within the scope of the city through sensing devices and sensor networks. 4 With the rapid development of IoT and mobile communication technologies, smart meters, smart cameras, wearable embedded devices, smart home appliances, and other terminal devices come into family life. Although a large number of IoT terminal devices provide people with convenient life, they also provide a broader attack platform and environment for attackers. 5 As shown in Figure 1, in smart cities, most of the data collected by these IoT devices is sensitive, attackers may eavesdrop or tamper with these data to obtain benefits, which may bring serious consequences. For example, smart meters collect electricity consumption data, which will expose the user’s life behavior track once leaked; wearable embedded devices collect people’s physiological data, which will endanger people’s lives once leaked or tampered in the transmission process. To ensure the security of terminal communication services in smart cities, prevent the data collected by IoT devices from being eavesdropped on or tampered in the process of transmission, and avoid the damage or major security accidents to the business applications of the smart city caused by the leakage and tampering of data content, it is necessary to authenticate the devices and encrypt the transmitted data end-to-end.6,7
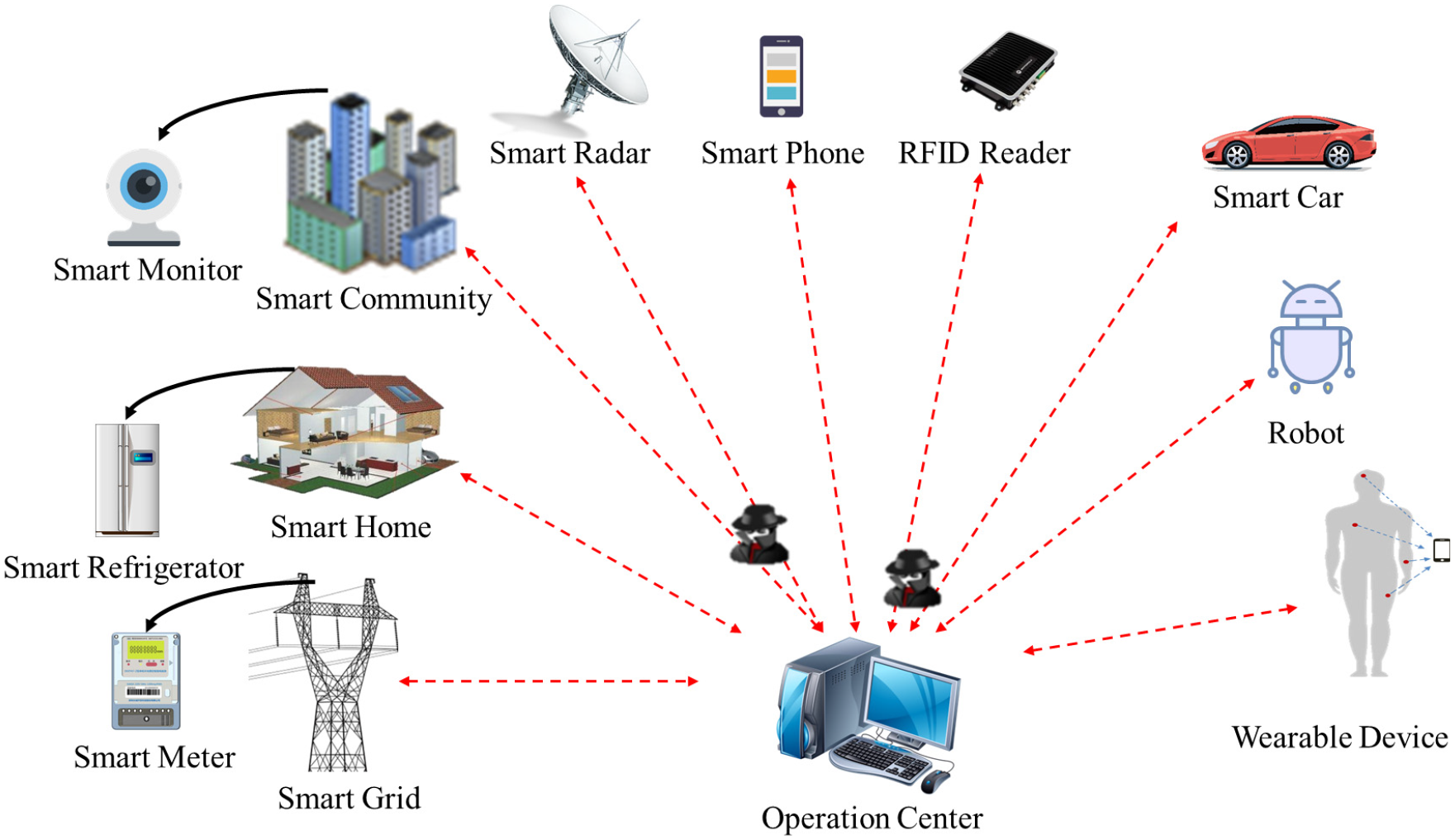
IoT devices in smart cities transmitting data to the operation center in the presence of adversaries.
Motivations
In smart cities, IoT devices are facing a variety of serious security threats, such as replay attack, data tampering attack, device simulation attack, man-in-the-middle attack, and privacy leakage. 8 These security threats hinder the development of smart cities. Therefore, security is gradually becoming a key demand in the development of smart cities. 9 Device authentication is regarded as one of the basic security services to protect the IoT system in smart cities. It verifies the identity of the IoT devices involved in the communication, so as to provide appropriate access control for these IoT devices.10,11 The key agreement provides end-to-end secure communication for smart cities and ensures the confidentiality and integrity of data in the process of data transmission. 12 To mitigate the security challenges in smart cities, we will start with authentication and key agreement to design a protocol suitable for IoT devices with limited computing power.
Main contributions
The main contributions of this study can be summarized as follows:
A cloud-aided trustworthiness evaluation mechanism is designed. Trustworthiness evaluation provides reliable authorization basis for identity authentication. However, due to the limited computing and storage resources of IoT device, the trustworthiness evaluation cannot be completed by itself. Considering the powerful computing resources and storage capacity, cloud server is introduced to evaluate the reliability of IoT devices. The operation center will decide whether to authorize the IoT device according to the trustworthiness level value calculated by the cloud server, so as to achieve mutual trust between the IoT device and the operation center.
An anonymous authentication and key agreement protocol with privacy preservation is proposed. A non-interactive zero knowledge (NIZK) scheme is constructed to realize anonymous authentication and key agreement between operatiion center and IoT devices. As the properties of NIZK, the proposed scheme can protect the data security and privacy of IoT devices in smart cities.
Formal security analysis and experimental simulation are presented. Security analysis demonstrates that the proposed protocol can meet many security requirements such as anonymity, privacy preservation, mutual authentication, forward security, and unlinkability. Performance analysis shows that the proposed protocol requires much less time overhead than similar protocols, so the proposed protocol is more suitable for deployment in smart cities.
The remainder of this article is organized as follows: A detailed description of the related work is given in section “Related works.” The system model, security model, and security requirements of the proposed scheme are presented in section “System model, security model and security requirements.” The preliminaries required for the proposed scheme are described in section “Preliminaries.”“The proposed scheme” section elaborates the cloud-aided trustworthiness evaluation mechanism and anonymous authentication process. The section “Security analysis” provides provable security analysis and analysis of the security requirements for the proposed scheme. And the performance analysis of the proposed scheme is presented in the section “Performance analysis.” Finally, we give a conclusion and future work of this article in the section “Conclusion.”
Related works
In recent years, IoT devices are widely used in various fields of smart cities. Its security has also received great attention.13–17 For the secure authentication of IoT devices, scholars have done a lot of research. Now, the related work is sorted out as follows.
In 2014, aiming at security issues of implantable medical devices in wireless body area network environment, Liu et al. 18 proposed an authentication scheme based on certificateless signature. The scheme is proved to be secure against the existence forgery of adaptive chosen message attack in random oracle model. However, Xiong 19 pointed out that Liu et al.’s scheme could not resist the public key replacement attack and proposed an extensible certificateless remote authentication protocol with anonymity and forwarding security to solve this problem, but this scheme has the problem of member revocation. To solve this problem, in 2015, Xiong and Qin 20 proposed a remote authentication scheme which was constructed by incorporating an efficient revocation certificateless encryption scheme for short-term key disclosure and a certificateless signature scheme. The security analysis shows that the scheme satisfies anonymity, key escrow resistance, and revocability. However, Shim 21 pointed that the scheme was insecure against the adversary who knows a secret value. According to the secret value, the adversary can forge signatures. That is the scheme cannot resist signature forgery attack. In 2021, Wei et al. 22 proposed an efficient, secure, and privacy-preserving message authentication scheme. The scheme supports IoT devices in smart cities with different encryption systems (whether RSA or ElGamal), and allows offline/online computing, making it more versatile and efficient than previous solutions.
However, the process of identity authentication may reveal users’ privacy. To protect the privacy of users, more and more scholars focus on anonymous authentication. In 2017, Dimitriou and Karame 23 proposed an anonymous authentication scheme based on the blind signature and the hash chain. Blind signature technology has the characteristic that the signer is invisible to the message signed by him, so as to protect the privacy of the sender. But this scheme cannot trace malicious senders. To solve this problem, Kong et al. 24 proposed an anonymous authentication scheme based on blind group signature. In this scheme, the group manager can trace the group signatures generated by the group members by using the group private key. But the scheme needs multiple interactions to ensure the security of authentication, resulting in huge computation and communication costs. Aiming at the low efficiency of authentication and resisting load modification attacks on the smart meter, Boyapally et al. 25 proposed an authentication scheme based on physically unclonable functions(PUF). The scheme uses lightweight cryptographic primitives, which makes the scheme feasible in resource-constrained IoT devices. Vasco et al. 26 proposed an authentication scheme based on oblivious pseudo random functions (OPRF), and further proposed a blind anonymous identity-based encryption scheme. The scheme will not disclose to the eavesdropper whether the execution is successful, so as to hide whether the sender’s password is in the receiver’s password set. In addition, the scheme provides a provable security model to capture the security and anonymity of sender and receiver. In most authentication schemes, the evaluation of the credibility of the devices in smart cities is not considered, which makes the authentication schemes lack reliability. Besides, designing a privacy-preserving authentication protocol with low computational and communication overhead is also an urgent problem in smart cities.
System model, security model, and security requirements
In this section, the system model, security model, and the security requirements in the proposed scheme are presented. Table 1 lists some of the symbols used in the proposed scheme.
Notations in the proposed scheme.

System model
The system model is shown in Figure 2. First of all, before the IoTD sends registration request to the OC, it needs to collect its own trustworthiness attribute(TA) information and send it to the CS. The CS calculates its trustworthiness level(TL) and returns it to the IoTD. Second, the IoTD signs the TL and sends the report to the OC. To prevent cheating, the OC requests the TL of the device from the CS for comparison. And the authorized tag is granted to the IoTD whose TL falls within its acceptable range. Among them, the CS is semi-trusted, it may deliberately reduce the TL value of the IoTD to prevent the authentication and key agreement between legitimate IoTD and OC; the IoTD is semi-trusted, it may deliberately improve its TL value to cheat the OC; the OC is also semi-trusted, it may be curious about the privacy of data in the IoTD.

System model.
Security model
We define the security model of the proposed anonymous authentication scheme for smart cities by a game. The game is played by an adversary
Extract
Send
Reveal
Corrupt
Test
When the adversary
Definition 1
q-SDH assumption. With the public parameter
where
Definition 2
AKA secure. It is defined that the proposed solution is AKA secure if the
Security requirements
In this scheme, the following security goals should be realized:
Mutual authentication: A malicious adversary will fake a legitimate IoTD to obtain the corresponding services. At the same time, due to the privacy of the data collected and transmitted by the IoTD, the malicious attacker will fake the legitimate OC to request private data. To ensure the security for smart cities, the proposed scheme should achieve mutual authentication.
Session key aggrement: To ensure the data security in smart cities, the proposed scheme should achieve session key agreement. Session key can provide guarantee for subsequent data security communication between IoTD and other communicating parties.
Privacy preservation: The data in the IoTD have high privacy. Once the data are leaked, it will cause serious consequences. To protect the privacy of data in IoTD, the proposed scheme should achieve privacy preservation, that is, any unauthorized entities cannot get the data in plaintext, and the authorized third parties cannot disclose the user’s privacy according to the accepted data.
Perfect forward security: To protect the data security, the designed scheme need satisfy perfect forward security, that is, although the attacker obtains the current session key, he cannot recover the previous session keys.
Resistance of other attacks: What is more, the proposed protocol should be able to resist multiple attacks. Such as replay attack, man in the middle attack, forgery attack, and so on.
Preliminaries
In this section, a basic definition of the cryptographic primitives required for the proposed protocol is given.
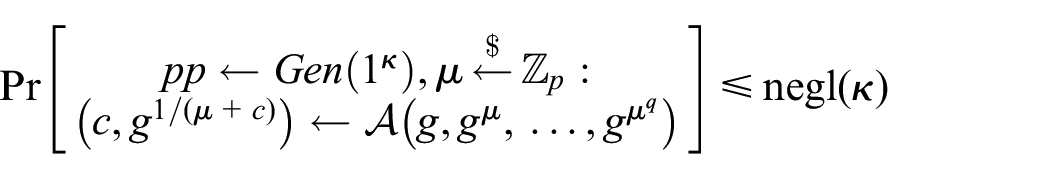
-Protocol
Let
Completeness: If
Special soundness: Given two accepting transcripts
Special honest verifier zero knowledge: On input
where
NIZK arguments
None-interactive zero-knowledge proofs (NIZKs) make a prover
1. Completeness: For any statement

2. Soundness: If

3. Zero-knowledge: There is a PPT simulator

A NIZK argument can be constructed by transforming a
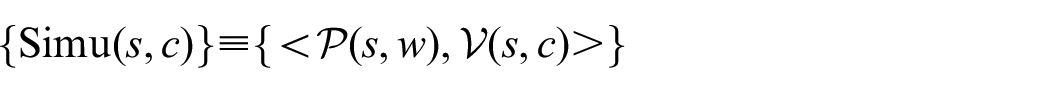
The proposed scheme
In this section, we will demonstrate the proposed scheme in detail from the following phases. The detailed process of anonymous authentication and key agreement is shown in Figure 3.

Authentication and key agreement phase.
Setup
In this scheme, each IoTD maps its information to a specific and unique identity
First, on input security parameter
Second, the OC randomly picks
Finally, the OC chooses cryptographic hash functions
Trustworthiness level computation
Pouryazdan et al. 30 proposed a vote-based trustworthiness management system. The detailed process of trustworthiness level computation is presented in their scheme. This method is also used in the proposed scheme. Before IoTD sends registration to OC, it needs to ask the CS to calculate its TL value, the detailed process is given below:
First, the IoTD collects a set of attribute values which can reflect its reliability, and sends the set to the CS. The set is
Second, when receiving the set

Because the importance of each attribute is different, we use weight

where
Third, the CS encrypts the TL value
Authorized tags generation
Data storage and processing on the CS is secure, but there is a situation that the CS deliberately reduces the TL value
When receiving the TL value


Encrypted the value
Upon receiving the data package, the OC decrypts using its private key and acquires
First, the OC picks a random number
Second, when the IoTD receives

Checks whether
Session key agreement
This phase can be divided into the following steps:
Step 1: The OC randomly selects a number
Step 2: When the IoTD receives

The IoTD generates proof
Step 3: When the OC receives

If
Security analysis
Provable security
Through the above security model, a formal security analysis is given in this subsection as follows:
Theorem 1
If the
Proof
If there exists an adversary
Given a

Using the tuple and technique of Boneh-Boyen,
27

Finally,
Extract
Send
-when
-when
Reveal
Corrupt
Test
Finally,
Analysis of the security requirements
In this subsection, we will show that proposed protocol meets all the security requirementsmentioned above. The security analysis is shown as follows.
Mutual authentication
When the IoTD sends a registration request to the OC, the OC will assign authorized tag for it who has high trustworthiness level value. And the OC generates a proof
Session key agreement
As
Privacy-preserving
Only entities with session keys
Perfect forward security
If the adversary intercepts the report
Resistance of other attacks
As this protocol injects a timestamp
Performance analysis
In this section, first, a comparison about features of the proposed scheme with those of other schemes is given. Second, the communication overhead of the proposed scheme is analyzed. Finally, the computational cost is discussed and the time cost of authorized tag generration and session key exchange is described.
Features comparison
In this subsection, the comparison between the proposed scheme, revocable and scalable certificateless remote authentication (RSCR
20
), threshold-based anonymous identification (TAI
32
), and conditionally anonymous ring signature (CRS
33
) is given. As displayed in Table 2, only the proposed scheme can satisfy all of these features. By generating NIZK proofs, the proposed scheme satisfies the mutual authentication and privacy-preserving. As the hash function is collision resistant, the data integrity is guaranteed in the proposed scheme. As the
Features comparison.

Communication overhead
To show the superiority of the proposed scheme, other similar schemes are compared with the scheme. It is assumed that the number of IoTDs is
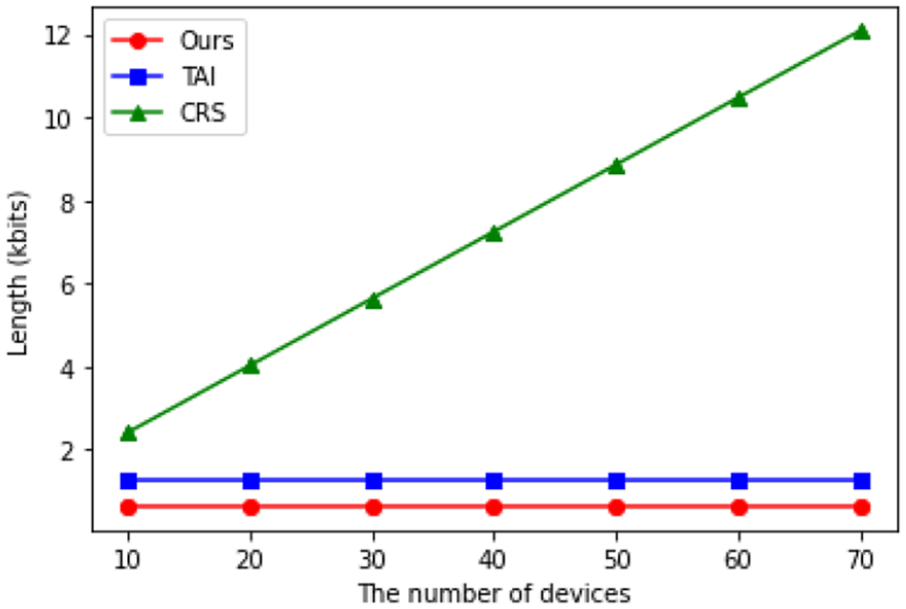
IoTD to OC communication cost.
Computational complexity
In this subsection, we denote
Execution time demonstrates the complexity of the proposal, which can be evaluated by time cost of the tag authentication and zero knowledge proof generation at the IoTD side, authorized tag generation and proof authenticaition at the OC side. First, we compare the time cost of the authorized tag generation and proof authentication at the OC side with other similiar schemes. The computational complexity of authorized tag generation phase in TAI is
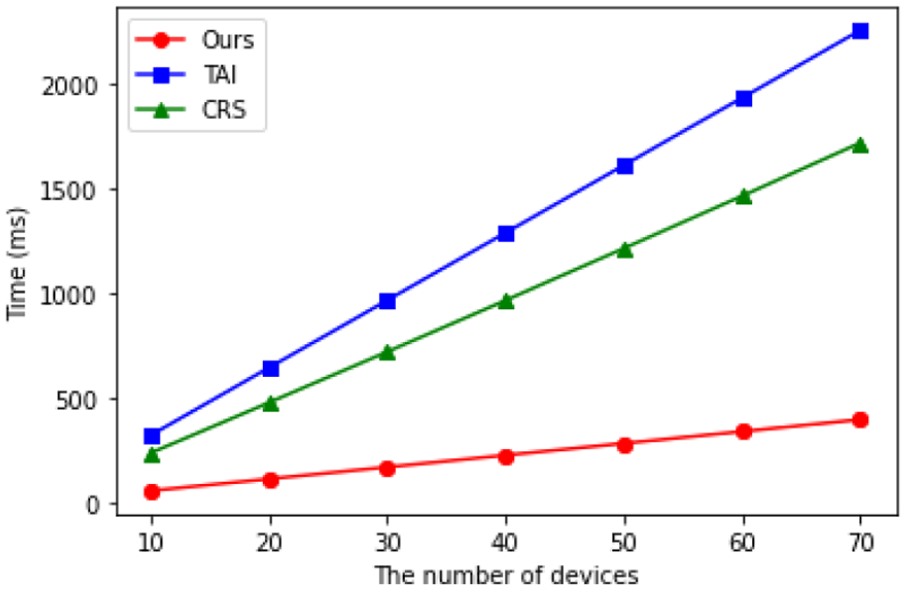
Time cost of OC for tag generation.
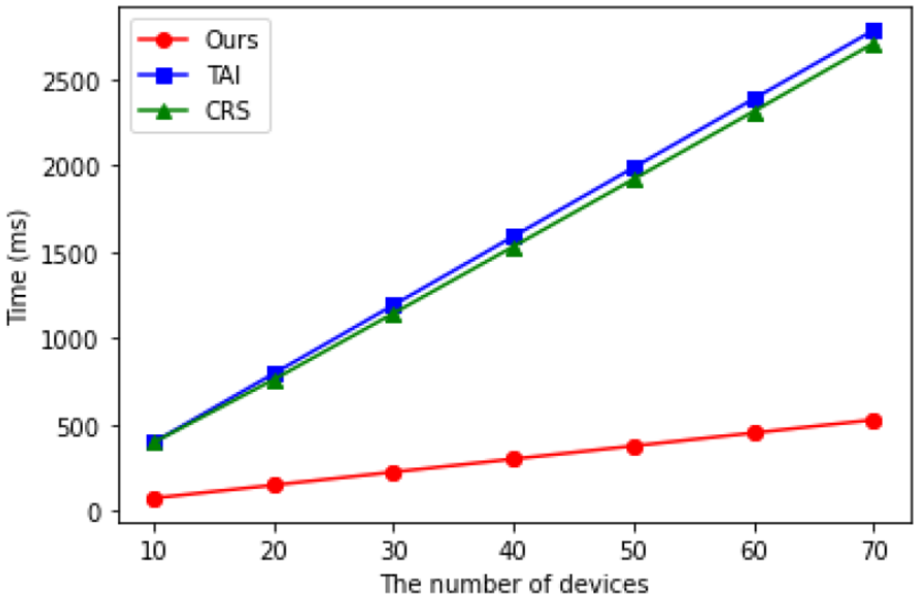
Time cost of OC for proof authentication.
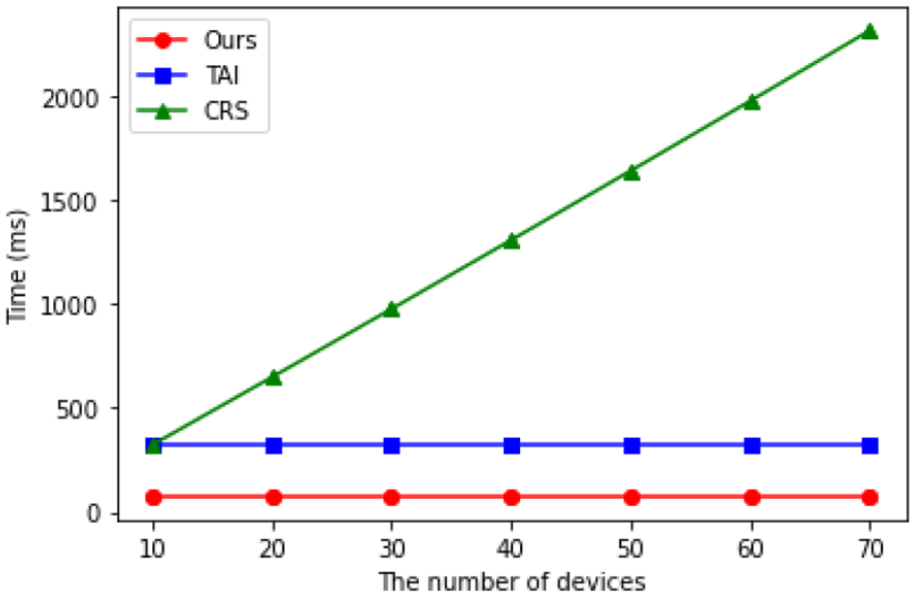
Time cost of IoTD for tag authentication.

Time cost of IoTD for proof generation.
Therefore, from the perspective of practicability, the proposed scheme is more applicable to smart cities.
Conclusion
In this article, we first propose a cloud-aided trustworthiness evaluation mechanism. According to the trustworthiness evaluation calculated by CS, the OC decide whether to authorize tag to IoTD, hence mutual trust between IoTD and OC is guaranteed in the proposed scheme. In addition, an efficient anonymous authentication and key agreement scheme based on non-interactive zero knowledge is proposed. Based on this scheme, the OC can authenticate the validity of IoTD without revealing its identity, hence privacy preservation of IoTD is guaranteed in the proposed scheme. And the session key prevents attackers acquiring data in plaintext, hence data security of IoTD is guaranteed in the proposed scheme. Security analysis indicates that the proposal can satisfy many security properties, such as anonymity, privacy preservation, mutual authenticaition, forward security, and unlinkability. The result of performance evaluation demonstrates that the proposal is more suitable for deployment in smart cities.
However, how to seek a balance between privacy protection and regulation is a problem worthy of discussion in the data security protection of the smart city. In the future, we will study how to design a revocation mechanism which can revoke malicious entities while keeping the anonymity of legitimate entities in smart cities.
Footnotes
Handling Editor: Dr Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by the National Natural Science Foundation of China under Grant Nos U1836115, 61672295, 61922045, 61672290, and 61877034; the Natural Science Foundation of Jiangsu Province under Grant No. BK20181408; the Jiangsu Key Laboratory of Big Data Security and Intelligent Processing, Nanjing University of Posts and Telecommunications under Grant No. DSIP1901; the Peng Cheng Laboratory Project of Guangdong Province PCL2018KP004; the CICAEET fund; and the PAPD fund. Besides, this work is also supported by FCT/MCTES through national funds and when applicable co-funded EU funds under the Project UIDB/50008/2020; and by the Brazilian National Council for Scientific and Technological Development—CNPq, via Grant No. 313036/2020-9.
