Abstract
Many remote user authentication schemes have been designed and developed to establish secure and authorized communication between a user and server over an insecure channel. By employing a secure remote user authentication scheme, a user and server can authenticate each other and utilize advanced services. In 2015, Cao and Ge demonstrated that An’s scheme is also vulnerable to several attacks and does not provide user anonymity. They also proposed an improved multi-factor biometric authentication scheme. However, we review and cryptanalyze Cao and Ge’s scheme and demonstrate that their scheme fails in correctness and providing user anonymity and is vulnerable to ID guessing attack and server masquerading attack. To overcome these drawbacks, we propose a security-improved authentication scheme that provides a dynamic ID mechanism and better security functionalities. Then, we show that our proposed scheme is secure against various attacks and prove the security of the proposed scheme using BAN Logic.
Introduction
With the rapid development of Internet technology and the smart device industry, users can access any service from anywhere. 1 In addition, the growth in network technology has made these services user-friendly and adoptable and mobile devices have become a vital part of our lives. Nowadays, people are able to easily utilize advanced services such as e-commerce, e-healthcare, and e-learning. 2
Despite advantages of ubiquitous mobile computing technologies, several new threats have emerged. The transmission of data through insecure channels leads to the security challenges such as authentication, privacy, and integrity. And adversaries are considered to be sufficiently powerful to control communication over a public channel. To ensure authorized and secure communication, a user and server should verify their mutual legitimacy and exchange a session key, which can be used to transmit data securely.3,4 Moreover, an anonymous authentication is required to provide secure communications between numerous network users while preserving privacy.
To address security and authorized access in mobile environments, various remote user authentication schemes have been designed and developed. Remote user authentication is a common approach to verify the legitimacy of users who seek service and has become an indispensable component of service access. By employing a remote user authentication scheme, a server first authenticates remote users and grants service access only to those who are legitimate and authorized while rejecting unauthorized entities whose aim is to damage network security.
Smart card–based authentication schemes were introduced initially to resolve such security issues.5–7 Recently, a large amount of research on password-based authentication schemes using smart cards has been presented.3,8,9 However, password-based authentication schemes are vulnerable to identity/password guessing attacks and subject to inefficient password change policies. To resolve single-password authentication problems, several biometric-based remote user authentication schemes have been proposed.2,10–12 In contrast to passwords, biometric information, such as irises, fingerprints, and palmprints, is considered to be a unique identifier of a user and is difficult to spoof. Therefore, biometric-based remote user authentication is inherently more secure and reliable than conventional authentication schemes. 13
Li and Hwang 14 proposed an efficient biometric-based remote user authentication scheme in 2010. In 2011, Das 15 cryptanalyzed and improved Li and Hwang’s 14 scheme. However, An 16 found out that Das’ 15 scheme failed to provide mutual authentication and enhanced it to support secure authentication in 2012. In 2015, Cao and Ge 17 demonstrated that An’s 16 scheme is vulnerable to replay attacks, in which an adversary can masquerade as the legal server. In addition, they mentioned that An’s scheme does not provide user anonymity just as most recently presented biometric-based authentication schemes are not properly addressed, so An’s scheme is insecure against user masquerading attack. Cao and Ge also proposed an improved multi-factor biometric authentication scheme to overcome the security weaknesses of An’s scheme and support user anonymity. However, we point out their scheme fails to provide re-registration and does not withstand several attacks.
This article discusses the security vulnerability of Cao and Ge’s scheme and proposes an enhanced multi-factor biometric authentication scheme with better security functionality than Cao and Ge’s scheme. We provide an analysis of the security and efficiency of our proposed scheme. The major contributions of this study are summarized as follows:
Cryptanalysis of Cao and Ge’s scheme
We cryptanalyze Cao and Ge’s scheme and demonstrate the incorrectness of their scheme in re-registration phase and the vulnerability to the off-line ID guessing attack and server masquerading attack. We illustrate that an adversary can obtain the identity of any legal user of the system once he or she obtains the smart card of the user. Hence, the scheme does not provide user anonymity.
Enhancements of Cao and Ge’s scheme
We propose an enhanced multi-factor biometric authentication scheme to overcome the security weaknesses of Cao and Ge’s scheme. Our scheme supports the dynamic identity mechanism using timestamps and resists off-line ID guessing attack and server masquerading attack. We also provide password change phase to enhance the security of the system.
Security analysis against various attacks
We analyze the proposed scheme in security. Our scheme supports better security functionality than that of Cao and Ge’s scheme. Our scheme is secure against off-line ID guessing attack, user masquerading attack, and server masquerading attack. In addition, it provides user anonymity, mutual authentication, session key agreement, efficient password change, and forward secrecy. We also prove that our scheme provides mutual authentication using Burrows–Abadi–Needham (BAN) Logic. 18
Preliminaries
In this section, we present notations and then define Bio-Hashing.
Notations
The notations used throughout this article are described in Table 1.
Notations.

Bio-hashing
Biometric technology often attracts attention in the area of unique user authentication in general authentication systems. Especially, the use of biometric information is extending steadily in cryptosystem for authentication purpose. However, imprint biometric characteristics (such as fingerprint, palmprint, retina, and iris) may not appear exactly the same in each scan. With high probability, imprinted biometric information rejects registered, legitimate users. To resolve the high false rejection rate, Jin et al. 19 proposed a two-factor authenticator on iterated inner products comprising a tokenized pseudo-random number and user-specific fingerprint features, which produces a set of user-specific compact codes; this is called Bio-Hashing. Later, Lumini and Nanni 20 proposed an improvement of Bio-Hashing. As noted by Chang et al., 21 Bio-Hashing is used to map a user’s/patient’s biometric feature onto user-specific random vectors to generate a code called a bio-code and then discretize the projection coefficients into zeroes and ones. Bio-Hashing is verified to be the most suitable and compatible technique that can be utilized in tiny smart devices such as smart cards and smart phones. 22
Review of Cao and Ge’s authentication scheme
In this section, we review Cao and Ge’s authentication scheme. It comprises four phases: registration phase, re-registration phase, login phase, and authentication phase.
Registration phase
A user
(R1) A user
(R2)
(R3)
(R4)
(R5)
Re-registration phase
(RR1)
(RR2)
(RR3) If
(RR4)
Login phase
In order to login to the remote server
(L1)
(L2)
(L3)
(L4)
Authentication phase
The user
(A1)
(A2) If it is valid,
(A3) If
(A4) Then,
(A5)
(A6)
(A7)
(A8)
Cryptanalysis of Cao and Ge’s authentication scheme
In this section, we analyze the security problems of Cao and Ge’s scheme. Cao and Ge 17 cryptanalyzed Younghwa An’s 16 scheme and improved it to support better security functionality. However, we found out that Cao and Ge’s remote user authentication scheme has security vulnerabilities. We assume that the capabilities of adversaries are as follows:2,23
An adversary
An adversary may either steal a user’s smart card or obtain a user’s password, but not both.
An adversary can extract the information stored in a smart card by means of analyzing the power consumption of the smart card.
Incorrectness in registration phase
Younghwa An
16
claimed that if the password
The user
From the received message
We showed that Cao and Ge’s scheme has fails in correctness and ultimately cannot proceed with re-registration phase because
Off-line identity guessing attack
The identity of a user is registered at the registration center. Users normally choose their social security ID, e-mail, phone number, and so on as their identity and are requested to input their identity, password, and biometric information in login phase. Although users attempt to keep their identities secret, identities are selected from a limited set that can be enumerated, and adversaries have sufficient power to guess from a limited set of identities in the off-line condition. 24 The complexity of this attack depends on the length of the identity. We show that Cao and Ge’s scheme is vulnerable to off-line identity guessing attack.
An adversary
When
Once the identity of the user is revealed, an adversary can recognize and trace the user before the user performs re-registration phase. However, as we mentioned in “Incorrectness in registration phase,” Cao and Ge’s scheme fails in correctness to proceed re-registration phase. Therefore, the adversary can identify and trace the user continuously.
Server masquerading attack
Cao and Ge analyzed the security of their authentication scheme against server masquerading attack by sending
An adversary
When a new session is opened,
An adversary can masquerade as the server before the user performs re-registration phase. However, as we mentioned in “Incorrectness in registration phase,” Cao and Ge’s scheme fails in correctness to proceed with re-registration phase. Therefore, the adversary can continue pretending to be the legal server.
The proposed remote user authentication scheme
We propose a dynamic ID-based multi-factor biometric authentication scheme to overcome the security problems of Cao and Ge’s remote user authentication scheme. In the proposed scheme, we use timestamps to support the dynamic identity mechanism and resist off-line ID guessing attack. We assume that the registration center and the remote server are trustworthy and share a server’s secret key
Registration phase
In this phase, a user
(R1) A user
(R2)
(R3)
(R4)
(R5) Upon receiving
Figure 1 illustrates the registration phase of the proposed remote user authentication scheme.

Registration phase.
Login phase
In order to login to the remote server
(L1)
(L2)
(L3)
Authentication phase
The user
(A1) Upon receiving
(A2) If the verification is failed,
(A3) If the verification is failed,
(A4)
(A5) If the verification is failed,
(A6)
(A7)
Figure 2 illustrates our proposed remote user authentication scheme.

Proposed remote user authentication scheme.
Password change phase
The smart card establishes an authorized session with the user
(P1)
(P2)
(P3) If the verification is failed, the session is terminated. Otherwise,
Figure 3 illustrates password change of the proposed remote user authentication scheme.

Password update phase.
Analysis
In this section, we describe an analysis of our proposed authentication scheme with respect to security and performance. We assume that the capabilities of adversaries are the same as those from our cryptanalysis of Cao and Ge’s authentication scheme. We first prove the security of our proposed scheme using BAN Logic. 18 Then, we show the security analysis of proposed scheme against various attacks.
Authentication proof based on BAN logic
In this section, we analyze the security of our proposed authentication scheme with BAN Logic 18 which is a formal analysis method for authentication protocols. Table 2 illustrates notations used in BAN Logic.
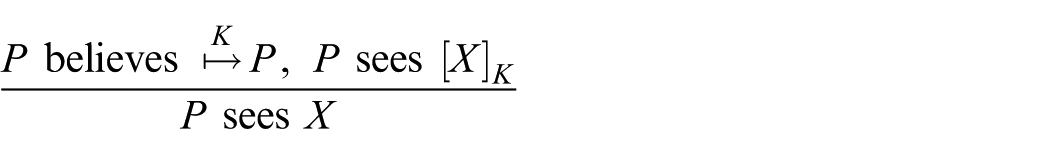
The BAN Logic postulates
Message meaning rule concerns the interpretation of messages. They all derive beliefs about the origin of messages. For shared keys, we postulate
That is, if Nonce-verification rule expresses the check that a message is recent, and hence, that the sender still believes in it
That is, if Jurisdiction rule states that if
If a principal sees a formula, then he also sees its components, provided he knows the necessary keys
Note that if Freshness-conjuncatenation rule states that if one part of the formula is fresh, then the entire formula must be fresh







Security goals. The proposed scheme will satisfy the following goals




Idealized scheme. We transform our scheme into the idealized form as follows




Initiative premises. We make the assumptions about the initial state of the scheme to analyze the proposed scheme as follows




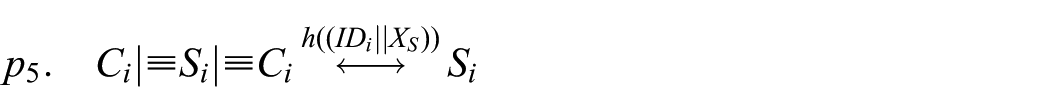






Security analysis of the idealized form of the proposed scheme


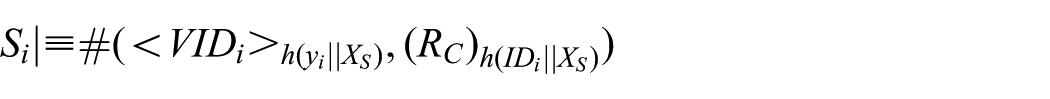
Then, we apply the nonce-verification rule to obtain




Then, we apply the nonce-verification rule to obtain





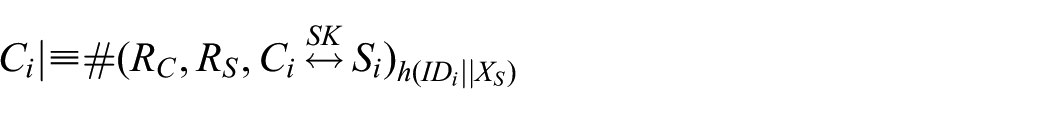
Then, we apply the nonce-verification rule to obtain



BAN logic notations.

According to (Goal 1), (Goal 2), (Goal 3), and (Goal 4), we know that
Security analysis against various attacks
Off-line ID guessing attack
The smart card and login message contain pseudo identities,
User masquerading attack
Server masquerading attack
To masquerade as a legal server,
User anonymity
We use pseudo identities to hide an actual identity. To derive
Mutual authentication
The server verifies the legitimate user by checking the equivalence
Forward secrecy
Suppose that the server’s secret key
We compare the functionality features and the computational cost of the proposed scheme with those of other existing schemes. Table 3 compares the functionality features provided by our scheme with those of other existing schemes. ○ denotes the scheme provides the property; × denotes the scheme does not provide the property; NA denotes the scheme does not consider the property.
Comparisons of the functionality features.

Performance
In Table 4, we compare the computational cost.
Comparisons of the computation costs.

Conclusion
Users are able to access and utilize advanced services owing to the growth of Internet technology and smart devices. However, given the unsolved security problems and adversaries that are sufficiently powerful to control communication, users are exposed to malicious attacks, and extension of Internet service is limited. To ensure authorized and secure communication, a user and server should verify each other’s legitimacy.
In this article, we demonstrated the security vulnerability of Cao and Ge’s scheme and its incorrectness in re-registration phase. We noted that their scheme is vulnerable to off-line ID guessing attack and server masquerading attack and fails in correctness. In addition, we proposed an enhanced multi-factor biometric authentication scheme with better security functionality than that of Cao and Ge. Our scheme supports a dynamic identity mechanism using timestamps and resists off-line ID guessing attack and server masquerading attack. Our scheme satisfies all desirable security attributes, as demonstrated in the security analysis.
Footnotes
Academic Editor: Feng Hong
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Science, ICT and Future Planning (2017R1A2B1002147).
