Abstract
Smart cities play a vital role to develop a sustainable infrastructure with efficient management of the Internet of things devices. The infrastructure is used to support various applications for smart hospitals, smart factories, and intelligent transportation systems. With the extensive deployment of Internet of things devices, unprecedented growth in data has lead to capacity and transfer issues. In this article, we proposed an efficient data transfer mechanism based on self-sustainable networks over the vehicular environment. Depending on whether the network is connected with vehicles available to support direct connection from the source to destination, we propose end-to-end and hop-by-hop forwarding for vehicular networks that are inherently disconnected. The evaluation results demonstrate that the lifetime of the discovered paths depends on the coverage area, vehicle mobility, and vehicle speed. Therefore, at times redundant disjoint paths are selected for communication. In the proposed work, selected vehicles are used to reach the destination.
Keywords
Introduction
With the advancement of technology, sustainable networks play an important role to support various applications. These networks can be used to transfer information in near real-time. Generally, a typical smart city with a population of one million easily generates 180 PB of data per day, whereas this number can further grow to 49 EB per month by 2021. 1 Undoubtedly, with this exponential growth of generated data, traditional wired networks are impractical and unsustainable to carry such enormous amounts of data. The reason behind is this it is never intended for large-scale data transfer but when used it generates a significant amount of carbon emissions while disrupting other Internet services. 2 Even though satellites and roadside units (RSUs) can alleviate the wired network while executing such large-scale data transfers but with considerably high communication maintenance costs. Especially, satellite communication with its higher data transmission delay and weather-related disruptions.
Recently, vehicular ad hoc networks (VANETs) are explored as an alternative to establish a sustainable virtual network for servicing IoT-based applications involving data sharing and transfer. 3 Notably, the opportunistic network allows vehicles to exploit their low power communication capability to store and forward information across other connected vehicles. For instance, VANETs are often useful for information sharing with all nearby devices using broadcast. However, transmitting information from a source to destination presents several challenges like vehicle unknown mobility-limited storage, broadcast storm, and network congestion.
Principally, the vehicles that will be used in the process are basically volunteers and are not controlled by the sources and destinations of the data, which means that they move arbitrarily, so the main challenge will be on how to use the available information like the vehicles within the range of each vehicle, the location, and/or the speed of the vehicles in order to choose the vehicles that will transfer the messages without affecting in anyhow the destination and movement of these vehicles. A second challenge to overcome will be how to adapt our protocols depending on the nature of the environment: for instance, depending on the density of vehicles and the distance between these.
Evidently, the execution model of smart cities is based on data dissemination. 4 The vehicles alongside RSUs share information and communicate with one another. The information is used to improve the quality of life to achieve sustainable development goals (SDG-9) chalked out by the United Nations General Assembly and intended to be achieved by 2030. 5 It is interesting to exploit the efficiency of the vehicular network since they demonstrate good performance compared to the traditional network at a lower cost.
This work is eventually a part from the 9th goal “Industry, Innovation, and Infrastructure.” In fact, these algorithms will improve the circulation and safety inside the cities because it can be used to transfer information about the traffic and eventual accidents. It can be used as a backup in case of natural disasters where the classical communication systems are not working.
Nonetheless, to adopt vehicular networks for data dissemination demands a dynamic communication framework that establishes a robust communication channel between source and destination to provide low latency communication. 6 In this work, we propose a sustainable framework over vehicular networks for data dissemination. Here, the vehicles act as agents to support requesting vehicles to establish a connection with the destination node. The framework design is flexible allowing any vehicle agent to become a source or destination node. For robust and fast long-distance communication, the system establishes multiple connections to relay the data. More precisely, the framework senses the surrounding environment to establish a connection between source and destination. Upon successful connection setup, the data are transferred. Such a preemptive connection setup mechanism before data forwarding is novel where devices are only used to route the data, in contrast to traditional ad hoc mechanisms where store and forward procedures are adopted. Here, we assume that the source is unaware of the destination location. In another scenario, we assume that the destination location is known. Here, we use global position coordinates to find direction, destination, and intermediate agents. The algorithms are evaluated in terms of messages delivered, throughput, hop count, and communication delay.
The rest of this article is organized as follows: Section “Literature review” describes recent contributions in the domain of vehicular networks for data transfer. The system model is discussed in Section “System model and problem description.” Section “Proposed vehicular data transfer network” describes the proposed framework. Finally, performance evaluation and conclusion are presented in Section “Performance evaluation” and Section “Conclusion,” respectively.
Literature review
This section covers the recent contribution define sustainable networks using vehicular networks for data dissemination. In latest trends, software-defined networks are adopted to define the data dissemination flows. However, in this scenario, RSUs and backend cloud data centers play an important role. To provide a better overview of sustainable networks, the contribution based on SDN has explored in this section.
Zhu et al. present a hybrid emergency message dissemination architecture based on SDN on the Internet of vehicles. 7 The objective is to transfer the data reliably with minimum delay. The control and data plane of the SDN are decoupled into a vehicular network. The onboard units (OBUs), RSUs and, SDN-based centralized controller is used for reliable and efficient dissemination of event-driven safety messages. This approach using SDN enhances the message coverage and decreases the latency in a sparsely connected RUS for inter-vehicular communication in a multi-hop scenario. When an accident occurs, the event-driven emergency messages are sent by the source to the controller as well as to the surrounding vehicles both. In this way, emergency messages are disseminated efficiently and delay by the controller can be incorporated to enhance the overall network performance.
To reduce the network congestion and potential collision between V2V, authors in Liu et al. 8 presented a clustering-based probabilistic broadcasting approach (CPB) for data dissemination. The geographical location and driving directions of the vehicles are the two parameters on which the cluster head is elected. The driving direction corresponds to an important parameter as it increases the stability of the cluster for a longer amount of time before disconnections take place. For sending a packet, a probability assignment function is used to first determine based on the vehicular density and network condition. Furthermore, a data forwarding function is determined based on the probabilistic basis using the already determined probability assignment function. The data forwarding takes place based on the calculated probabilities. The capacity of a cluster head broadcast is determined to guarantee packet delivery ratio and transmission range based on a locally generated counter. The cluster head broadcasts the packets if it is a receiver and resides in the transmission range otherwise the vehicle or node in transmission range sends the packet on a probabilistic basis. The packet is dropped by the vehicle in case the cluster head is in the transmission range. This reduces congestion and delay.
In most of the contributions, the cluster-based approach is adopted for data forwarding to handle the broadcast storm problem. In Ren et al., 9 the unified clustering (UFC) framework is proposed that separates the stable clusters that build a connection with cluster head. The stable clusters are formed based on mobility patterns, which is developed based on two parameters. The first parameter is the mobility pattern that is the speed differences less than a threshold and the second is the direction of vehicles. A cluster head is selected and assigned the lowest random backoff timer to reduce the clustering overhead. The selection of cluster head and random backoff timer is based on the multiple parameters. These parameters are link lifetime, average speed, and relative distance. The vehicle usually sends the cluster head broadcast message and that becomes the first cluster head. All vehicles keep the list of all previous cluster heads in their cache. If a connection is broken, a new cluster head is elected from the cache based on their priorities. The cluster head which has a higher link lifetime is given the highest priority. Similarly, in Ismagilova et al., 5 the authors proposed a technique where a cluster is formulated based on mobility. The hamming distance is calculated to find the similarity in mobility pattern and nodes with the smallest hamming distances form a cluster using a lightweight clustering algorithm. 10 Traffic and synchronization data are sent to other vehicles using V2V and V2R routing protocols. If the data received by the vehicles are outside of the cluster, the information is dropped. And in case of congestion, the RSU tells other vehicles about the network congestion. Furthermore, a location parameter is calculated based on the roadID, lane direction, and physical location of the vehicular nodes. The roadID is received from local RSU, whereas direction and location are received from GPS. Farooq et al. 11 proposed an RTVC protocol consisting of two parts. The first part is the vehicle clustering formation (VCF) scheme and the second part is vehicle multicast routing (VMR). The protocol considered the speed parameter to enhance the stability of multicast routing. The scheme is explored both for highway and urban scenarios. The speed adjustment factor (SAF) is used to enhance cluster performance. The vehicle clustering scheme is multiple factors. The first factor is VCF and second is vehicle cluster maintenance (VCM). The stability is reduced through less number of cluster head switching. The cluster head life is made longer to decrease the cluster head selection process. As the vehicle with the same speed can form a cluster, the cluster is formed for a longer time before the new cluster head election is performed.
Similarly, in other works, vehicles are used as a data carrier to move data between source and destination. Malik et al. 3 proposed a framework to adopt vehicles as a data carrier. The vehicles work voluntarily, upload the data from source spot, and offload the data on the designated spot. The vehicles pick the data from other spots until it eventually delivered to the destination. The authors assume that vehicles know the designated spots and final destination of the node, further, to improve the system efficiency, redundant data blocks are transferred to avoid data loss. Similarly, Kanwal et al. 12 used the machined learning approach to predict the vehicle destination before selecting for data transport. Gulati et al. 13 proposed a deep learning–based data dissemination scheme by considering the vehicle mobility and content nature. The authors use an energy estimation scheme to select the potential vehicles. Later, connection probability between the selected vehicles is computed to find a stable connection. In the last stage, a convolutional neural network scheme is used to estimate the social relationship scores among vehicles. Tiennoy and Saivichit 14 proposed a protocol called roadside-assisted named data network. In this work, the authors handle the dynamic vehicular environment having intermittent network connections. Moreover, in most cases, the source location of data is not known; therefore, the name data networking approach is proposed for efficient data delivery. Similarly, Urmonov and Kim 15 proposed a technique to handle flooding that can cause redundancy, congestion, buffer overflow, and delay issues. The authors introduce the concept of lateral crossing lines which select the relay vehicles based on their location.
Furthermore, the vehicular networks in connection with edge devices are used for resource sharing where the compute-intensive tasks are offloaded to nearby edge locations. Zhang et al. 16 proposed a predictive communication scheme to offload tasks directly or through relay transmission. Similarly, Wang et al. 17 cover the real-time traffic management on the Internet of vehicles enabled fog environment.
Discussion
Most of the existing work focus on a cluster-based approach for data dissemination; however, few contributions exist that cover data transportation using vehicles3,12,18 and ferries. In these contributions, vehicles act as a carrier for data transportation. The data in the forms of blocks are uploaded on the vehicle where it downloads the data at specifically designated stations. In our work, we are focused on establishing a virtual network connection between source and destination nodes using the vehicular networks. Therefore, the challenges in our proposed work are different from the above-mentioned contributions. Furthermore, our technique is more focused on establishing a connection with minimum overhead, hop count, and delay as a key factor to achieve a sustainable network.
System model and problem description
Network model
In this article, we are modeling an urban region where vehicles are moving in different directions. These vehicles are connected through vehicle-to-vehicle (V2V) communication using the IEEE 802.11p standard. Each vehicle moves independently and does not maintain a single position. A vehicle can have access to a piece of the given information, for example, we suppose that each vehicle can connect to other vehicles within a given range. Furthermore, we set constraints on the storage and transmission of data at a given vehicle. A vehicle receives a message, performs a given protocol depending on the model, and then forwards an appropriate message to another vehicle or station. Depending on the model used, the forwarding mechanism does not use vehicle onboard storage in the sightless algorithms since it simply drops a received message when there is no agent within range. In other models, vehicles store a message for a while depending on the method used for persistence period determination.
Communication model
The path loss
where
The one-hop successful transmission probability
where
The propagation latency
where
Road model
Often vehicular traffic models are simulated using a standard Manhattan model, which is a straightforward, rectangular grid of streets. Notably, such a road model ensures a homogeneous distribution of vehicles while avoiding blockage of traffic flow in the simulation. As illustrated in Figure 1, we selected Souk Sebt city in Morocco because it exhibited similar attributes. Even though this city map is not perfectly homogeneous, we add some connecting roads to make it a somewhat uniform road network. The resulting model is flexible for simulating different scenarios, meaning it can be extended in scale, vehicle density, vehicle source rates, and vehicle connected range. We can also change the vehicle density in a wide range by increasing the rate by which the vehicles enter the map (Figure 2), traffic lights are added to avoid blockage but there is a limit value that we did not exceed a lot during our simulations.

Map and road network of Souk Sebt Oulad Nemma, Morocco considered for the vehicular traffic simulation.

Data sources and sinks of the vehicle agent.
Data transmission model
We simulate data transmission from a stationery source station to a stationery destination. Nevertheless, the model is applicable even if the stations are moving. In the simulation, we assume that the source station has an infinite-sized input message buffer and tries to send as much as possible during the simulation run. Moreover, the data messages are generated randomly.
Mobility model
No doubt the model is affected by the general flow of vehicles because in steady state, vehicles handle incoming messages for a while. Assume that the general flow is from the source to the destination that is a flow where more vehicles move in the vicinity of the sources than near the destination. In this case, the model will perform better compared to flow in the opposite direction. This is quite similar to the difference between conduction and convection of heat in gases. To resolve this, we experiment with making flows uniform from all sides, eventually finding a balance between vehicles moving in different directions—with all directions being equiprobable. Furthermore, in situations when the network gets choked at some intersection. To cater for this, we locate the choke point by running the simulation at the highest vehicle arrival rate and add traffic lights or tweak the arrival rates so that to make the vehicle network more homogeneous and flexible.
Problem description
This work aims to make and evaluate solutions for the data dissemination problem. Given two main stations that cannot connect directly because they are out of range of each other, we want to send data from source station to destination station by optimizing different evaluation measures, namely delay, hop count, and efficiency. The data transmission is range bounded, that is the source should not be able to contact the destination or a vehicle out of its range. Moreover, the data transmission is uninformative with agents having no access to information from out of its range.
Proposed vehicular data transfer network
The main contribution is the proposed virtualized communication framework for data transfer between any source location or node to a destination location or node. The conceptual framework of the network is shown in Figure 3. The main modules are sensing module, motion predictor, routing manager, and data manager. The sensing module explores the surrounding environment to identify any smart vehicles within its data communication range. The motion prediction module is used to determine the vehicle heading, speed, and current location. This information is used to determine the life of established connections as well as to refresh the neighboring vehicles database. Subsequently, this information is used to establish a network connection for data transfer.

Proposed virtualized communication network framework.
In this study, we explore two scenarios: Scenario A assumes that the destination location is unknown, whereas Scenario B assumes that the destination location is known. The first scenario uses dynamic source routing where the connection request is initiated by performing path discovery from the source to the destination. Once a connection is established using intermediate vehicles, the messages are forwarded. However, in the second scenario, when a vehicle receives a data message, it performs a look-up operation in the neighboring vehicle database for single-hop selection for message forwarding. Furthermore, due to the fragile nature of the connection, multiple non-overlapping connections can be established allowing redundant data transfer.
Scenario A. Location-aware end-to-end forwarding
The first two algorithms are termed as sightless, as the main supposition here is that each agent (vehicle or station) is unaware of the destination location. They can only sense vehicles within its range. In this algorithm, the process of message transmission is divided into multiple steps that include device sensing and establishing a network path. For connection search, every vehicle has a direct connection to its previous and next vehicle. Furthermore, the first vehicle in the established path is connected to the source, while the last vehicle is connected to the destination. This path is used to send data as long as it exists. When the destination node receives a message, it sends out an acknowledgment taking the same route toward the source. A lack of acknowledgment means the message has failed to deliver.
Here, hop count is the length of the path, while delay is proportional to the sum of distances between the vehicles on the established path. Thus, the objective is to reduce these measures while having the connections last for the longest time possible, in turn successfully sending the maximum number of messages. More precisely, the sum of the distances between successive vehicles should be kept to the minimum so that vehicles can stay within ranges for longer intervals.
In general, in this type of algorithms, the process of transmission is divided into two main steps:
Search step involves the source searching for a list of vehicles such us every vehicle in the list has a direct connection to the previous and the next vehicle in the list, and the first one is connected to the source, while the last one is connected to the destination. In fact, the list represents a reliable connection between the source and destination, which can be used to send messages until the connections in the list break.
Send step. Each time the source begins by sending a message to the first vehicle of the list, which thereafter follows a path comprising vehicles, each one transmitting it to the next one until it reaches the destination. Upon message reception, the destination send back an acknowledgment to the source. In case of successful acknowledgment received by the source, it will repeat the sending step until the connection is lost, which warrants return to searching step.
In this work, we implement two algorithms differing in the search step. Here, the first algorithm performs search using a broadcast method, that is, it tries to determine all the possible paths and then selects one of them. The second algorithm is mainly inspired from shortest path algorithm to find a path for message dissemination to the destination.
Algorithm 1. Hop-bound source routing—We propose an algorithm inspired by classical dynamic source routing (DSR) for message dissemination between nodes. As the name suggests, the searching process in this algorithm is long and arduous. Here, the source sends connection request to all the vehicles within its communication range. The connection request message contains an empty path field, the destination node location, connection id, and tentative distance field between source and destination. On receipt, each vehicle appends its vehicle Id to the path field and adds its distance from the receiving vehicle before broadcasting the message to nearby vehicles. However, to avoid the infinite message loop between vehicles, we adopt a scheme where already visited vehicles drop the received message (Figure 4). This is done using the path field in the message header. Similarly, the connection requests that fail to find any non-visited vehicle within the range are also dropped. When a vehicle receives a connection request where the destination node/vehicle is within range, the vehicle sends back an acknowledgment that travels back through the same path reaching the requested source node. This also indicates that a connection is established for further message transfer. However, there is a possibility where the source node receives multiple connection request messages having non-overlapping paths; in that case, the source node may utilize all the paths to provide redundancy or may choose the path with less number of intermediate hops or distance.
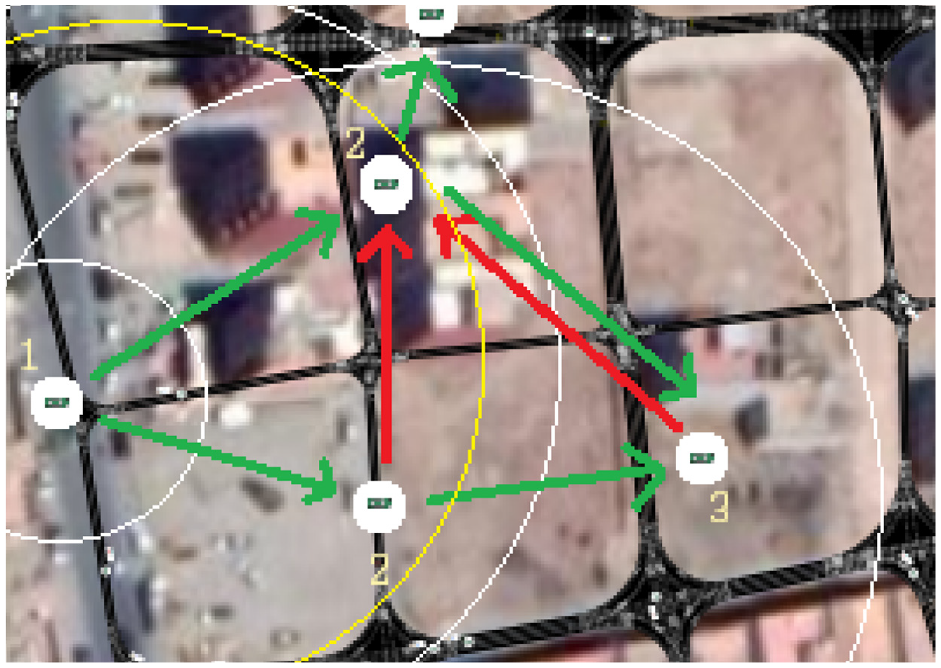
Hop-bound forwarding where nodes are linked once. Here, green connections represent possible newly discovered paths, whereas red connections represent the already discovered paths.
Algorithm 2. Greedy source routing—In this variant, we use shortest path algorithm where the vehicles and their connections are represented as nodes and edges. Initially, the source node with no knowledge of vehicles within its data communication range senses vehicles by sending control messages. During this discovery process, the source node also records the distance to the sensed vehicles. Recall that Dijkstra algorithm uses a visiting process, meaning the initial node visits a vehicle and get all the vehicles within its range alongside their distances. Every time, a vehicle with the shortest distance to the source node is visited, it identifies all vehicles within its range and calculates their distances to the source node in terms of the connection path. Afterward, the source node constructs a shortest path to each vehicle by identifying the best previous vehicle. This is followed by marking these vehicles as visited and moving on to the next nearest vehicle. After a given number of iterations, the destination node is eventually within the data transmission range of the visited vehicle.
Let the source node where we start be the initial node. Let the distance of destination node be the distance from the source node to the destination node.
Mark all in data transmission range of the source node as unvisited vehicles.
Assign to every vehicle a tentative distance value: set it to zero for the source node and to infinity for all other vehicles. From the source node, set the nearest vehicle as current node.
For the current vehicle, scan for all the unvisited vehicles within its range and calculate their tentative distances through the current vehicle. Compare the newly calculated tentative distance to the current assigned value and assign the smaller one. The information about the changes and the newly detected vehicles is sent to the source node as a return message of previous vehicle. Mark the current node as visited.
If the destination node has been marked visited, then stop. Use the previous vehicles from the destination all the way to the source node to get the shortest path.
Otherwise, select the unvisited vehicle that is marked with the smallest tentative distance, set it as the new current node, and go back to the previous three steps.
Here, we assume that there is always a connection between the source node and the destination node through vehicles. Thus, the proposed algorithm is well-suited for urban environments where vehicles are often moving on roads. However, in sparse vehicular environments, the algorithm fails to achieve desired objectives. Generally, in such scenarios, other IoT devices or roadside units are used to support smooth execution of the vehicular framework. However, the proposed data forwarding schemes are designed to work in areas lacking such support. Probably, since such large-scale deployment quickly becomes cost ineffective when providing maximum network coverage. We believe that the proposed hop-by-hop data-forwarding scheme adopts well to sparse vehicular scenarios, as the intermediate vehicles buffer and hold the data for a short while until it is passed on to the next suitable vehicle.
Improvements—The communication delay between vehicles is insignificant; however, the algorithm complexity depends on the number of vehicles in range that are used to establish a path between the source and destination. This becomes an overhead when the lifespan of path is short. Thereby, we introduce few improvements to improve the path finding.
Farthest-first hop selection. Often the destination is located farther from the source compared to the data transmission range of the connection, and it is not useful to send a connection discovery message to the nearest vehicle. Therefore, we adopt a range-based mechanism where the farthest vehicle within a defined minimum distance is selected as the first hop for the connection.
Bounded path length. After performing the search step multiple times, we get an estimation of the distance between the source and destination, as well as, the number of hops in the optimal connection paths. Over time, we use this information to improve the search step. For instance, a vehicle receiving a connection discovery message drops it if the number of visited vehicles (the length of the connection path) is larger than the estimated optimal. Note that this estimate gets dynamically updated with discovery of shorter paths. In case of failure to establish connection path the minimum distance limit is relaxed.
Unvisited route selection. One main reason contributing to the message complexity of the path discovery process is the discovery messages received by already discovered vehicles that are the vehicles in range of the previous vehicle in the connection path. Here, we implement selective route selection where vehicles receiving discovery messages only forwards them onto unexplored paths in range, that is forwards the discovery messages to only unvisited vehicles in range.
In summary, the algorithm is considered more effective if it finds reliable connections lasting for longer time periods, more precisely it is capable of sending the maximum number of data messages without needing to trigger the path searching step. Therefore, while searching we consider a range less than the data transmission range of the vehicle, so that we end up with connections that last at least for a minimum period of time.
Limitations—The primary assumption of the aforementioned algorithms is that the vehicular network is urban, dense, and connected. At every path search step, there is a possible direct connection between the source and destination, and hence, it is possible to determine the minimum of time for message dissemination. Moreover, the resulting long-lived path disseminates a large amount of data in a short period of time using minimal resources. However, when vehicle density decreases or the distance between the source and destination becomes relatively larger compared to the range of vehicles, the possibility of establishing a long-lived connections between the source and destination drops considerably. To tackle this challenge in areas of low vehicle density, necessarily the source is unaware of the locations of vehicles in the network and the location of the destination. Generally, in such scenarios, flooding or broadcasting is used where messages are repeatedly forwarded to all vehicles in range. Even though this results in maximum success rate, but at the expense of huge message complexity in the vehicular network, which in turn leads to large network resource usage and energy consumption. This can be controlled by selective forwarding of the messages to a percentage of vehicles based on the distance to the destination and the vehicular density.
Scenario B. Sink-aware hop-by-hop forwarding
Assuming disconnected vehicular network with vehicles aware of their locations while the destination node is located at a fixed known location. Moreover, we assume that at any time instant each vehicle carries only one message. Note that with vehicles freely moving, using some vehicle selection criterion, the messages move between vehicles to finally reach the destination node. Here, the algorithm starts with a search for a suitable message forwarding candidate, once found the message is forwarded to that vehicle. In this work, we propose two different context-aware algorithms for single-hop selection in the context of disconnected vehicular networks. Note that the difference between these algorithms is the choice of the criterion used when selecting the next single hop. Overall, the concept is similar to any forwarding decision mechanism that starts with searching for a suitable vehicle followed by forwarding the message toward the destination node.
Let the source node where we start be the initial node. Let the distance of destination node be the distance from the source node to the destination node.
From the source node, detect all vehicles within its data transmission range.
Among the vehicles in range, select vehicles based on a criterion. The two context-aware criteria, location-based and speed-based, are detailed in the following sections.
Every time a vehicle gets the forwarded message, it searches for the destination within its range, if found then it forwards the message to the destination node, and the algorithm stops.
Otherwise, scan for vehicles in data transmission range and go back to step 2.
As mentioned earlier, the two context-aware algorithms differ in the criterion used for vehicle selection for message forwarding.
Location-based forwarding assumes that each vehicle gets an update about its location, contacts vehicles in its range, and the destination node is fixed. Here, the criterion for vehicle selection is based on the projection of vehicle location relative to the vehicle-destination axis as illustrated in Figure 5. We know that a suitable vehicle for message forwarding has less distance to the destination node. To do this, we simply project a vector related to vehicle within range to the vehicle-destination axis. Assuming strictly positive limit on these vectors, we select one that maximizes this projection, meaning it is near to the destination node. For example, in Figure 5, vehicles 1 and 4 are ignored because their projection is less than the limit (shown in red), vehicle 4 has a negative projection, and vehicle 5 is out of range. Comparing among the remaining vehicles 2 and 3, we select vehicle 3 because it has the maximum projection.

The vehicle 3 is chosen in location-based algorithm.
Speed-based forwarding assumes that each vehicle has access to its speed, either using some tool or calculating it overtime using its position at different times. In our case, we use the latter solution to get the vehicle speed. For vehicle selection, the criterion is based on the projection of vehicle speed relative to the vehicle-destination axis as illustrated in Figure 5. A suitable vehicle for message forwarding is one that has speed aligned to the destination axis as well as have an earlier arrival time at the destination node. In Figure 6 selects vehicle 3 because it has the maximum speed projection.

Speed-based algorithm, the vehicle 3 is chosen.
Case Study: Information sharing for disaster management
Information sharing in a disaster situation is critical for the effective management of resources and saving lives. The first responders require timely accurate data for decision. In 2008, a hurricane hit ashore near Galveston, Texas. 20 A large number of people are displaced due to high winds, torrential rain, and floods. The survivors are trapped with no electricity and water, all communication systems are wiped out. In the aftermath, the central command center is placed outside the disaster area, where the first responders are deployed to save people. Without any communication mechanism, traditional search mechanisms are adopted to find the survivors, locate casualties. Moreover, sensors are deployed to establish communication between the first responders. Thus, there is no mechanism where the survivors can share their information with the control center.
In the simulated road network, we consider the entry points akin to centers where rescue vehicles, police patrol cars, supply vehicles, and ambulances, and fire trucks originate to participate in the recovery effort. Moreover, volunteers are moving in vehicles, making random trips across the disaster-hit neighborhood. Inarguably, these movements are crucial to carry supplies, provide services, and transport aid workers during post-disaster efforts. We consider that the vehicles are equipped with communication devices capable of transferring data within its data-transmission range. Thus, the vehicles move around and establish connections with other in-range vehicles. This forms a disconnected but functional communication network that can implement a store-carry-forward information dissemination protocol. Often in the aftermath of a disaster, the communication infrastructure goes offline that needs time to revive to a limited or full capacity. In the absence of the communication infrastructure, the opportunistic protocol can relay information between two points, possibly to a static relief center and/or another moving vehicle. In consequence, this gives a viable mode of communication to rescue workers and survivors. Moreover, an opportunity to coordinate and monitor on-ground post-disaster activities from management centers. Therefore, in this article, we proposed a mechanism where the smart vehicles are used to establish a real-time communication path between source and control unit. Communication among vehicles is based on the dedicated short-range communication technique (DSRC).
Performance evaluation
The proposed framework is implemented in AnyLogic (https://www.anylogic.com/) with simulation parameters listed in Table 1. The road network used for traffic simulation is that of an actual region of Souk Sebt city in Morocco. The network exhibits grid road topology that guarantees homogeneous distribution of vehicles avoiding traffic blockages in the region. For evaluation, we benchmark the proposed vehicular data transfer network between static source and destination nodes. The vehicle movement is random with entry and exit points at all four sides of the topology. The vehicle arrival rate is used to control the number of vehicles available for data transfer.
Simulation configuration and specification.

MB: Megabyte; CPU: central processing unit; RAM: random access memory; GB: gigabyte; OS: operating system.
Evaluation measures
The model performance is evaluated by using the three measures listed as follows: (a) throughput is the number of delivered messages per vehicle density, (b) hop count is the number of vehicles that received the message and transmitted it until it reached the destination, (c) delay is the time needed for a sent message to be received at the destination, and (d) success rate is the percentage of sent messages arriving at the destination.
Scenario A. Location-aware end-to-end forwarding
Throughput
The number of delivered messages is an important variable that shows how many messages an algorithm could deliver in the period of the experiment, high throughput corresponds to more data sent. Therefore, we considered this measure an important factor for the evaluation of the vehicular data transfer network. The two proposed source routing algorithms send messages as long as there is an available connection. Note that only the last message before the connection is lost remains undelivered since its confirmation is never received. Later, when the connection is reestablished, the source resends the message, the reason for the two algorithms to achieve has a 100% success rate. Figure 7 shows throughput with increasing vehicle density. The greedy source routing performs well as it selects reliable paths resulting from the shortest path. However, the hop-bound source routing chooses sub-optimal paths that are short lived. In dense vehicular environments, the greedy source routing starts getting computationally expensive during the search step because it visits more nodes. Nonetheless, this can be resolved by selective searching, for example, choosing a given number of vehicles randomly and uniformly distributed, in turn optimizing the process.

Total delivered messages at varying vehicle density.
Hop count
It is another interesting factor to determine the sustainability of the vehicular data transfer network. A high hop count signifies a fragile network with nodes leaving the network frequently. More precisely, it determines the average number of participating vehicles to establish a connection between the source and the destination. Figure 8 shows that the average hop count in greedy source routing is higher compared to hop-bound source routing; however, with increasing vehicle density, both algorithms tend to have similar hop count. More precisely, greedy source routing results in higher hop count because the optimal shortest paths (obtained by comparing the distance) tend to be straight lines and hence containing more vehicles along the way. However, hop-bound source routing involves fewer vehicles along the way extended distances between them; consequently, this leads to the formation of less reliable connections.

Hop count at varying vehicle density.
Delay
It is defined as the amount of time required to transmit a data block from the source to the destination. The measure is directly related to hop count, which is adding more hops resulting in increased delay. Figure 9 shows the communication delay after establishing a connection. In greedy source routing, initially, there are more hops involved contributing to the higher delay. However, with increasing vehicle density, both hop-bound and greedy source routing converge in terms of delay as is in the case for hop count.

Network delay at varying vehicle density.
We observe that initially greedy source routing performs better due to its lower complexity, using less number of steps to find a connection to the destination. But the number of delivered messages decreases with increasing vehicle density. This decrease is a consequence of the adjacent node discovery process used to find the shortest path, which requires visiting all vehicles along the way to the destination. That is, when there are many vehicles, the process takes much longer, resulting in vehicles getting out of range more frequently, and leading up to short-lived connections. This issue can be resolved by selecting a given percentage of vehicles so that the vehicle density is bound to when the maximum number of messages get delivered. Nevertheless, this solution is limited when the distance between the source and destination increases. Again this can be resolved by designating a set of relay agents for path continuity or even to store information for efficient path discovery and its maintenance. In conclusion, the source routing algorithms fail to work in low vehicle densities (20 vehicles per km2) because it becomes harder to get a robust connection using vehicles between the source and destination. Taking this into account, in Scenario B, we propose context-aware hop-by-hop forwarding, more adapted for vehicular data transfer network delivering a good number of messages even when the network is sparse.
Scenario B. Sink-aware hop-by-hop forwarding
Throughput
Throughput of location-based forwarding is evident with higher message sending capacity in comparison to speed-based forwarding with increasing vehicle density. Even though the difference between the two forwarding schemes is small at low vehicle densities but becomes significantly larger at high vehicle densities as shown in Figure 10. The reason being that speed-based forwarding is selective when finding a vehicle with speed suitable for forwarding. This corresponds to blockage of flow channel as messages occupy vehicles for longer periods of time. Moreover, in high vehicle densities, the average speed of vehicle decreases so the speed-based forwarding performance further degrades.

Messages sent at varying vehicle density.
Hop count
It confirms that a speed-based scheme is selective when it comes to forwarding messages. In contrast, the location-based scheme demonstrates frequent hopping of the sent messages. Fortunately, this issue is alleviated around vehicle density 100 as shown in Figure 11. The reason for this frequent hopping of messages is that location-based scheme forwards the message to an incoming vehicle irrespective of its direction. However, in speed-based forwarding, the message may even get forwarded to a trailing vehicle. Since relative vehicle speed in the direction of the destination is used, the selected vehicle may end up nearer to the vehicle forwarding the message.
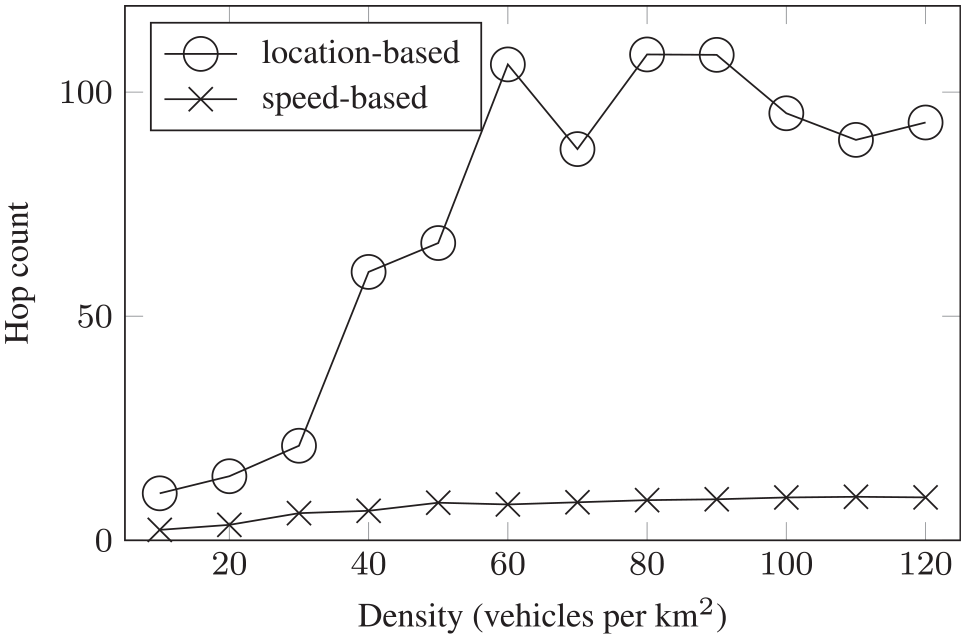
Hop count at varying vehicle density.
Delay
In low vehicle density, speed-based forwarding takes less time because vehicles moving at speed toward the destination are selected. Whereas in the case of location-based forwarding, it becomes harder to find better vehicles. This is demonstrated in Figure 12 where delay in location-based forwarding decreases to about 80 s with increasing vehicle density. This is because there are more neighboring vehicles to deliver the message to the destination. However, the delay in speed-based forwarding increases in the beginning but stabilizes with increasing vehicle density.
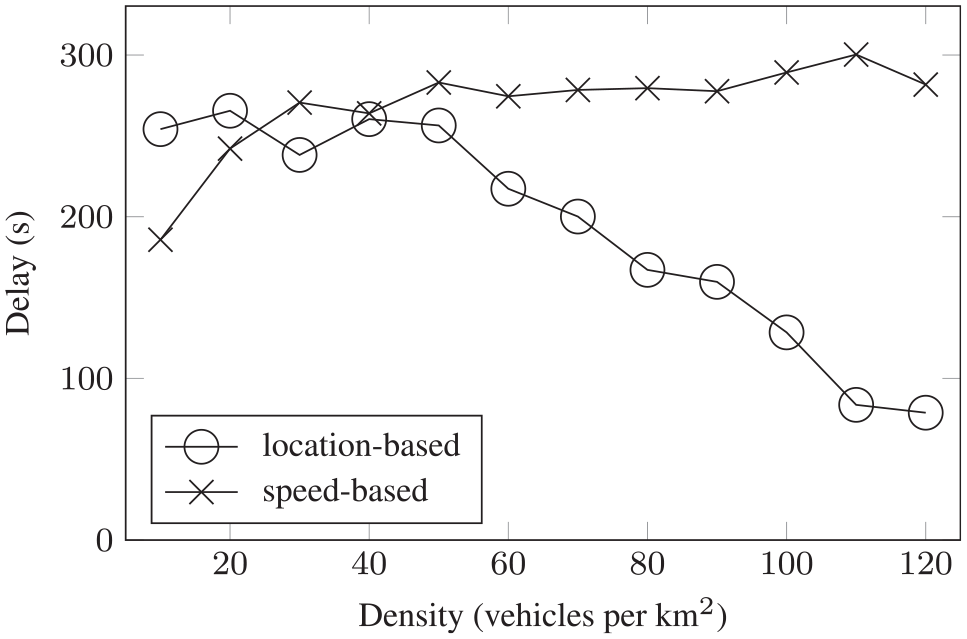
Total network delay at varying vehicle density.
Success rate
Figure 13 indicates the success rate for both forwarding schemes, the increase is proportional to vehicle density. Initially, at low vehicle densities, speed-based forwarding outperforms location-based forwarding but afterward, the difference between the two is insignificant.
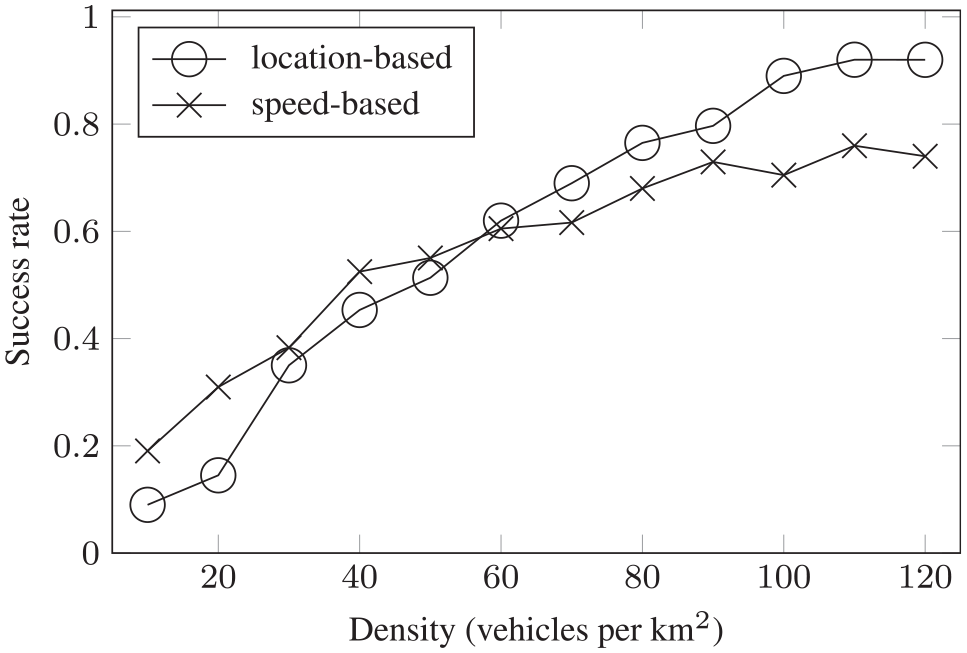
Success rate at varying vehicle density.
In summary, both forwarding schemes are capable of sending messages even at low vehicle densities, in some cases speed-based forwarding performing better. However, with increasing vehicle density, the location-based algorithm outperforms its counterpart and sends a large number of messages with a success rate approaching 100%. As observed in the results, the factors affecting both forwarding schemes are delay and number of agents. Nevertheless, this can be improved by varying the search region limits or maybe the presented forwarding criteria can be combined to improve the performance of vehicular data transfer network.
Conclusion
Sustainable networks play a critical role in information dissemination. The use of vehicular networks to establish achieve sustainable data transfer is a challenging task. In this work, we propose a framework using vehicles to establish a communication channel between source and destination. We take into consideration two scenarios in vehicular networks that are inherently disconnected: sink-oblivious scenario using source routing and sink-aware scenario using hop-by-hop forwarding. The results for the first scenario show that greedy source routing is more effective than hop-bound source routing. Here, the difference in the number of messages delivered is much better even though hop-bound source routing uses fewer vehicles and incurs less delay. Source-initiating path discovery before forwarding becomes challenging in low vehicle density. Furthermore, sink-aware hop-by-hop forwarding using context can send messages even at low densities around 10 vehicles per km2. Here, location-based forwarding results in a high number of messages sent with a small delay with increasing vehicle density. However, location-based forwarding uses considerably more resources than speed-based forwarding and also results in lower success rates at lower vehicle density. To conclude, virtual networks over IoT devices are the future of short-way communication. In the future, we are interested to introduce more intelligent algorithms that can predict the vehicle path to establish a communication network.
Footnotes
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.



