Abstract
In the smart grid and big data environment, accurate and large amount of power load data for users can be obtained with the wide application of non-intrusive load monitoring technology. In the research process of customers’ information, information security protection of users’ electricity data has become a research hotspot urgently. This article proposes a new type of load decomposition method for electric vehicle load information and compares it with hidden Markov model algorithm to verify its accuracy. On this basis, the elliptic curve encryption algorithm is used to encrypt the users’ electricity data, and the function and effectiveness of the encryption algorithm are verified by comparing the load decomposition of the electric vehicle with the unencrypted data.
Keywords
Introduction
With the dramatic development of smart grid and electric vehicle, machine learning methods have been widely used for information security of smart grid in various fields1,2 such as non-intrusive load monitoring technology, 3 information inference attack and preserving,4,5 and Internet of Things technology. 6 On the aspect of researches on users’ electricity load identifications, it is mainly focused on the identifications of users’ load equipment.7–9 Yet, it is precisely in the smart grid and big data environment that users’ electricity data face serious information security threat. In the process of big data information being researched, the privacy protection of information is also a major problem to be solved.10–12 Previous studies13–15 proposed k-anonymity and its improved algorithm to generalize and compress the sensitive data to achieve the purpose with hidden data. Wu et al. 16 proposed blind signature, anonymous processing, and Paillier homomorphic encryption to realize the anonymous data transmission and to protect users’ electricity data from being leaked.
In this article, a new type of load decomposition is applied for the process of load decomposition, including electric vehicles’ load signals, and compared with hidden Markov model (HMM) algorithm to prove its superiority. At the same time, the security of the users’ electricity data is considered during the transmission. The elliptic curve encryption (ECC) algorithm is used to encrypt the users’ electricity data, and the new load decomposition method mentioned above is used to decompose the loads of electric vehicles. The feasibility of the ECC algorithm is verified by the decomposition results of encrypted and unencrypted data.
New load decomposition algorithm
The new load decomposition algorithm is a method of separating the electric vehicles’ charging signals from the gathered house electrical power signals. This method can effectively alleviate the interference from household appliances except electric vehicles (especially from air-conditioning (AC) system). In this way, electric vehicles’ charging signal detection and electric power estimation can be accurately realized under the interference from the power signals of AC system.
New load decomposition algorithm implementation steps
Threshold processing of aggregated signals
For a given aggregated signal, the threshold signal is first applied to the aggregated signal for threshold processing, the portions of which having an amplitude less than the specified threshold are deleted, and the waveforms greater than the threshold portions are retained. The following is the threshold processing formula
here,
Filter AC pulse sequence
After the aggregated signal is processed by threshold, the AC pulse sequence still needs to be removed. Assuming that the duration of AC pulse sequence does not exceed minutes, the sequences that pulse sequences are not exceeding minutes are marked as “segments to be deleted.” One of the “segments to be deleted” is taken as initial data, and the adjacent “to-be-deleted segments” are analyzed and checked whether it meets the following two conditions
where
The adjacent “to-be-deleted segment” that satisfies the above two conditions will be marked as a new initial “to-be-deleted segment.” The above filter operation is repeated again. If the search criteria do not meet the above requirements of the filter, then the next pulse sequence segment will be initially checked. All periods of time marked as “segments to be deleted” are deleted from
Removal of residual interference
There are many residual interference in the aggregated signal, which refer to the fluctuations in the power signals of electrical appliances, the loss of the power line, and the hybrid error of low-amplitude electrical appliances’ power signals. After the threshold processing, the position information of each divided waveform segment can be obtained, and the residual interference amplitude around each segment can be estimated. The amplitude of the interference of each segment is estimated by taking the average value between the minimum value before segmentation of point A and the minimum value after segmentation of point B.
For each waveform segment, we can set two reference points to distinguish them. The minimum value of A is set as a reference before each segment, and the minimum value of B is set as a reference point after each segment. We can estimate the interference amplitude of each segment by averaging the minimum values of these two reference points. The residual interference amplitude can be removed by subtracting the segment from other related local interference.
Classification of segmented signals
After the above processing, the resulting aggregated signal leaves only a few signals which can be divided into the following three categories.
First, the cumulative counting function is defined
where
Second, the gradient function
Third, a normalized gradient function is defined if the gradient function has two segmented signals above two prominent peaks
Then, calculate the areas,
And the segmented waveform is classified as the first type of waveform; otherwise, it is classified as the third type of waveform.
Reconstruction of various types of electric vehicle charging load waveform
After classifying the segmented waveform in the first four steps, it is necessary to take one more step to extract the electric vehicle charging load waveform in the sub-class of Figure 1. The effective width

Three types of segmentation signals.
Neutron class identification of three types and the processing of electric vehicle charging load waveform reconstruction are shown in Figure 2.

Three types of electric vehicle charging load reconstruction process.
When the electric vehicle charging load overlaps with other equipment loads, the electric vehicle charging load waveform needs to be restructured. Considering that the electric vehicle waveform has a characteristic of constancy and amplitude stability, the height of the electric vehicle waveform can be estimated on the same day or some other time in a single day. Therefore, this article uses the actual height of the electric vehicle charging load and calculates the effective width of the segmented signal to reconstruct the square waveform of the electric vehicle.
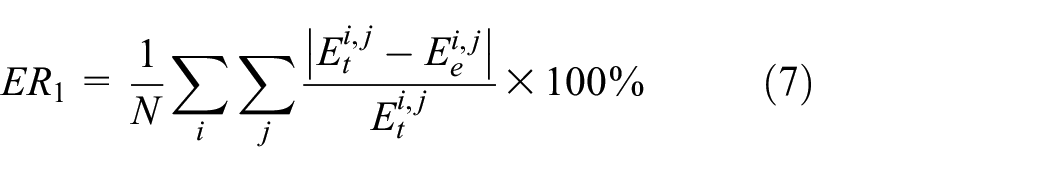
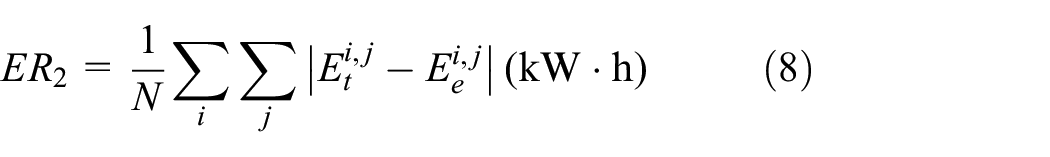
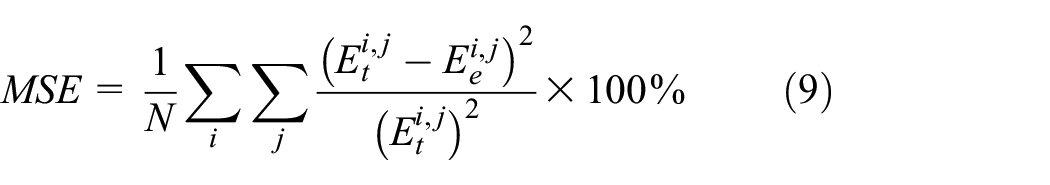
Evaluation index for new load decomposition algorithm effect
In order to evaluate the efficacy of the decomposition algorithm, three evaluation indicators are defined, as follows:
1. Average estimated error percentage
2. Average estimated error
3. Mean square error (MSE) of electric vehicle charging load signals
where
ECC algorithm
ECC algorithm is an asymmetric cryptosystem based on the elliptic curve discrete logarithm problem. It has strong unit data security and it is widely used due to the advantage of its short key. Based on the finite field arithmetic operation, ECC algorithm is easy to complete using computer operation.17,18
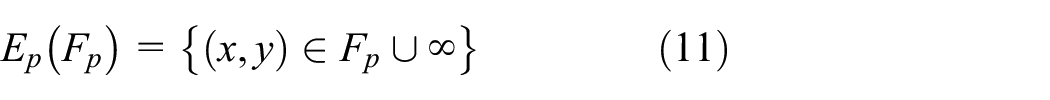
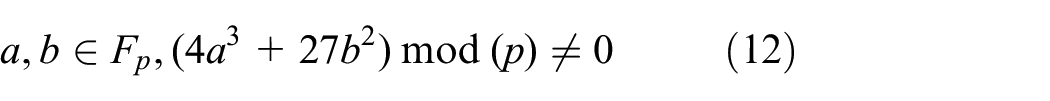
Prime field elliptic curve
Set p as a prime number, and the entire remainder set
where
The pair
If there is a point P on the elliptic curve and there exists a minimum positive integer
ECC encryption and decryption principle
An elliptic curve on

Encrypted communication flow.
Case analysis
This section is based on the aggregated power signal data from Hickory Street Database of the Americas someday. Through the new load decomposition algorithm mentioned above, the process of decomposing the charging load waveform of the electric vehicle for 1 day is described in detail and compared with the HMM method proposed in Zheng et al. 21 The accuracy is verified.
Implementation of new load decomposition algorithm
Threshold processing of aggregated signals
The threshold

Aggregated signals before and after threshold processing.
By comparing the aggregated signals after the threshold processing with the signals before the threshold processing, the bottom burr waveform is sharpened and appears flat.
Filter AC pulse sequence
It can be seen from the aggregated signal after the threshold processing that there are still many AC pulse sequences in the signal which need to be filtered out.
Set the parameters T = 10, η = 1,
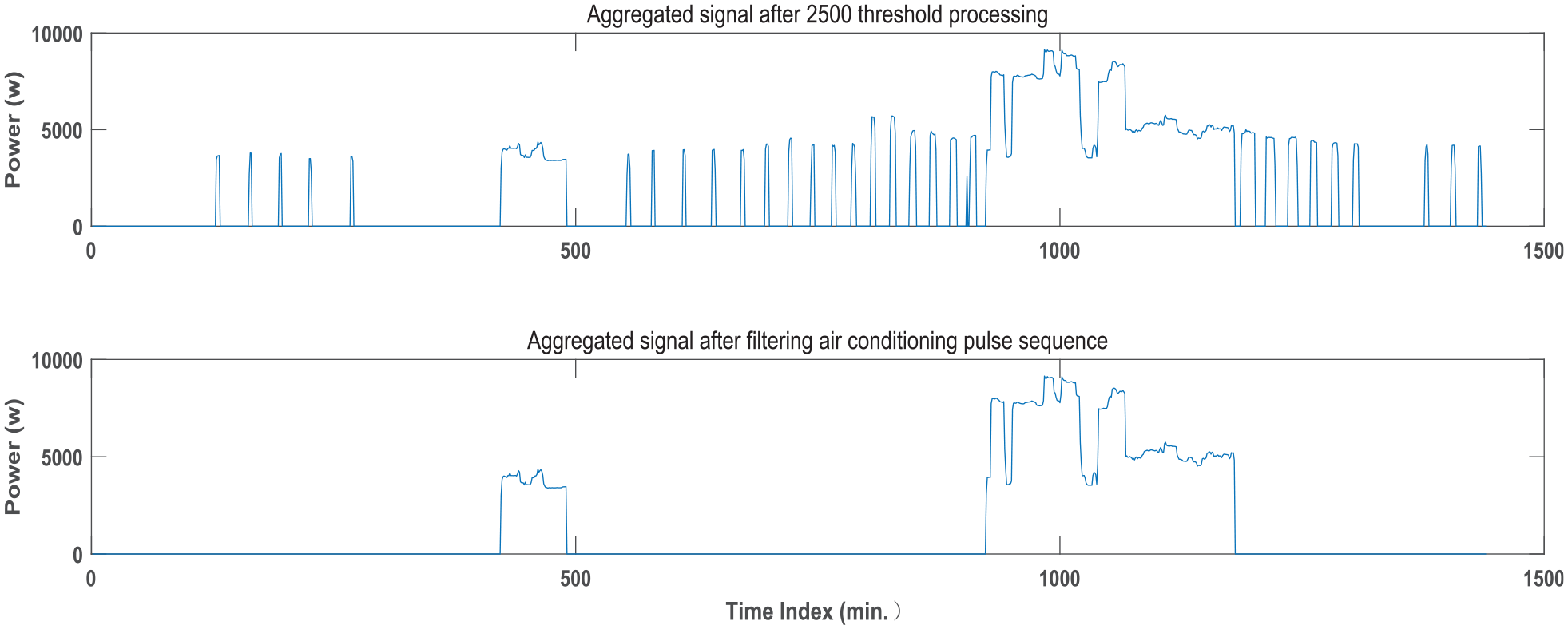
Aggregate signal before and after filtering.
After filtering the AC pulse sequence, the aggregated signal has retained several segmented waveforms (there are two segmented waveforms in Figure 4). The filtering effect is significant.
Removal of residual interference
Set the position of A = 5 and B = 5 as reference points and remove the interference amplitude using the above methods of removing residual interference. The effect after removing the residual interference is shown in Figure 6.

The effect map of removing residual interference.
After that, the signal for removing the residual interference can redo the threshold process and filter the AC pulse sequence process. Now move to the next step.
Classification of segmented signals
As it can be seen from Figure 5, the remaining two segmented waveforms need to be classified after the threshold process and filtering process.
According to equation (4), the cumulative counting functions,

First segment

Second segment
It can be seen from waveform
Reconstruction of various types of electric vehicle charging load waveform
The segmented waveform of Figure 7 is the second type of waveform. Hence, the effective height

First segment
The segmented waveform of Figure 9 is the third type of waveform. First, determine whether the electric vehicle charging load waveform is on the top or bottom of the segmented waveform.
Set the threshold

Segmented sub-section waveform.

Filling of the processed sub-segment waveform.
The filtering does not delete the sub-segment waveform. Therefore, the top of the sub-segment waveform is the electric vehicle charging load. Then, the effective height and effective width of the top of the sub-segment waveform in Figure 11 are also obtained using the way shown in Figure 9. Eventually, the electric vehicle charging load waveform in the aggregated signal is reconstructed, as shown in Figure 12.
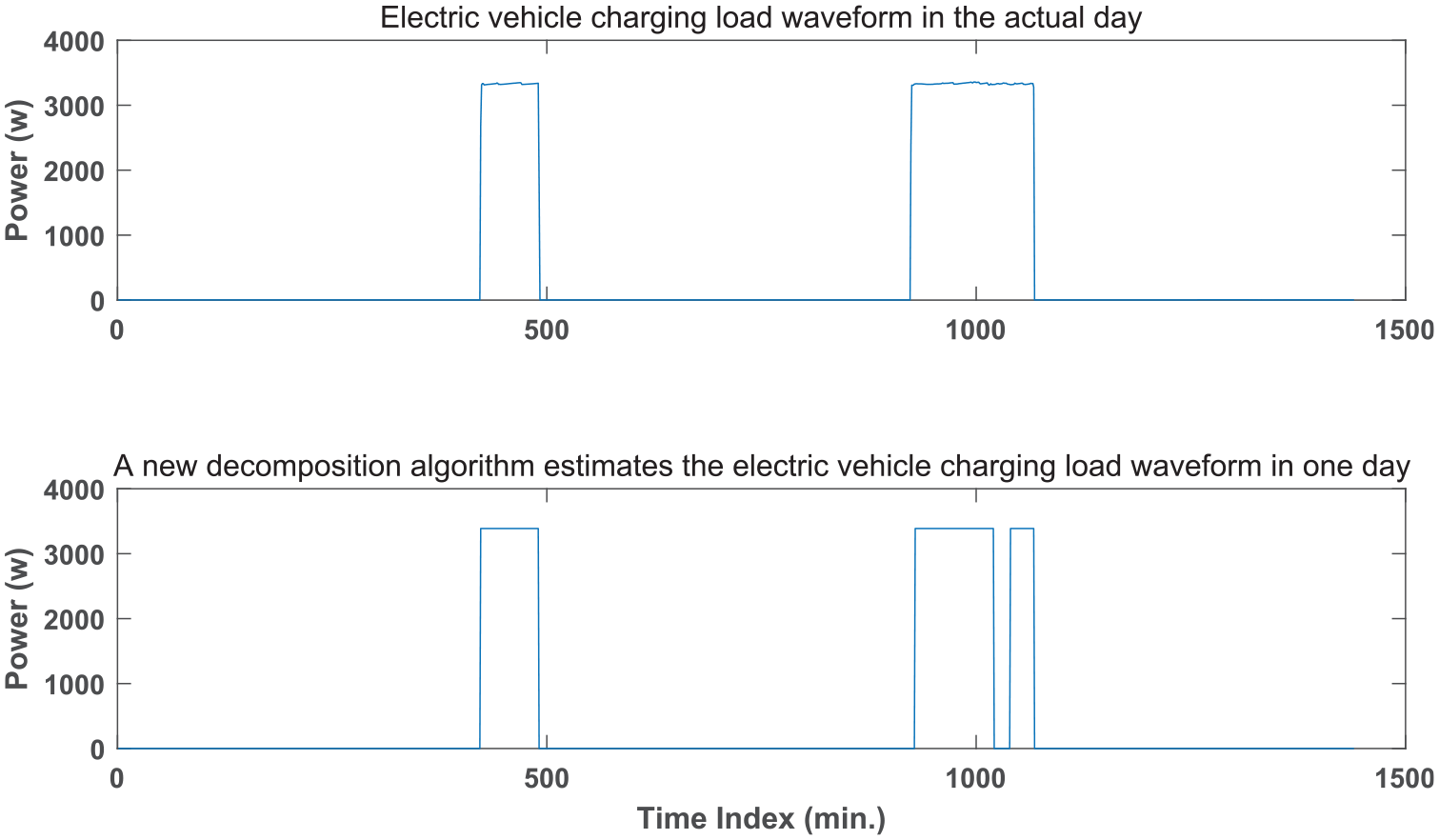
The actual and estimated comparison of the electric vehicle charging load waveform in 1 day.
Based on the aggregated signal, three decomposition effect evaluation indexes are calculated respectively based on equations (7)–(9):
Comparisons between new load decomposition algorithm and HMM algorithm
The new load decomposition algorithm proposed in this article and the HMM algorithm proposed in Zeadally et al. 22 are used under the same conditions. Users’ electric vehicle load waveforms of Hickory Street Database of the Americas are decomposed. The data in Table 1 can be obtained.
Comparison between new algorithm and HMM algorithm data under the same conditions (partial data).

HMM: hidden Markov model; MSE: mean square error.
As shown in Table 1, the average estimated errors of monthly electricity consumption are compared. The errors of the new algorithm are smaller than the errors of the HMM algorithm. As for the average estimation error of electric energy consumption of 8.44% of the new algorithm, the estimation error of HMM algorithm which is up to 64.4% is undoubtedly not suitable for energy decomposition with electric vehicle charging signals. Therefore, the new algorithm is better than the HMM algorithm.
ECC-based encrypted signal decomposition
The ECC algorithm is used to encrypt the aggregated signal of a certain day.21–24 Parameter setting of ECC algorithm is calculated as follows:
1.
2. With regard to the determination of parameter p, the larger the p-value, the safer it will be. But it will also affect the calculation speed. In order to meet the security requirements, a prime number of about 200 bits is generally selected;
3. With regard to the determination of parameters a and b, a can be a positive integer randomly generated which is less than
A positive integer b less than
4. About the determination of the base point, the determination of curve
5. For the determination of the private key k, randomly select a prime number from 0 to
6. With regard to the determination of the public key K, multiply k by the base point G to get the public key K, which is
The process of decomposing the charging load waveform of the electric vehicle is described as shown above. After that, stealers can only obtain the encrypted signal as shown in Figure 13 at most.

Unencrypted signal (top) and encrypted signal (bottom).
Compared with the encrypted signals and unencrypted signals, the encrypted one expands to an order of magnitude with violent vibration frequency. Afterwards, the new decomposition algorithm is used to decompose the encrypted signal to verify whether it can also decompose the electric vehicle load waveform or not and prove its encryption security. The decomposition results are shown in Figure 14.

Waveform diagram after decomposition of the new decomposition method.
As it can be seen from Figure 14, the load waveform of the electric vehicle with the signals encrypted cannot be decomposed by the new decomposition method, which ensures the security of signals during the transmission.
Conclusion
This article proposes a new type of load decomposition algorithm especially for electric vehicle users. By comparing with the HMM algorithm, the superiority of the new load decomposition algorithm is verified from three evaluation indicators,
Footnotes
Handling Editor: Peio Lopez Iturri
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported by the Natural Science Foundation of Fujian Province of China (Grant Nos 2018H0003, 2017J01731, and 2017J01732) and Educational Commission of Fujian Province of China (Grant Nos JT180339 and JAT171096).