Abstract
In an IEEE 802.11 Distributed Coordination Function–based wireless network with multiple hops, a node operates on its own with several predefined data rates (i.e. following modulation and coding schemes). Moreover, the IEEE 802.11 Distributed Coordination Function node’s communication is characterized by transmission and carrier-sensing distances. The transmission one is, in general, reverse proportional to the data rate. Meanwhile, the carrier distance keeps constant regardless of the modulation and coding scheme. Therefore, when a node has a high transmission rate, within its carrier-sensing range, the number of nodes may increase. The previous works have not yet extensively investigated the impact of data rates on such a scenario. This article addresses that issue aiming to quantify the network performance of the multi-hop IEEE 802.11 networks. As a solution, we propose the mathematical expressions, which consider data rates, for end-to-end throughputs, as well as delays in the network with string topology. We confirm the expressions’ correctness by presenting the quantitative agreements between the analytical and simulation results.
Introduction
Recently, there has been renewed interest in adopting wireless multi-hop networks, which will be useful in various applications ranging from the traditional wireless sensor networks1–3 to the Internet of Things4–6 and vehicular ad hoc networks.7–9 Such a system can relax the complexity of underlay infrastructure, hence improving the easiness and flexibility in network construction. More importantly, the wireless multi-hop networks enable the autonomous operations of network nodes, each of which is predetermined, for example, in a standard. This article focuses on the multi-hop networks in which each node’s operation relies on the IEEE 802.11 Distributed Coordination Function (DCF). The IEEE 802.11 DCF defines the behaviors of medium access control (MAC) and physical (PHY) layers of a wireless node. Moreover, the physical data rates depend on predefined modulation and coding schemes.
The operation of an IEEE 802.11 DCF node is following Carrier Sense Multiple Access/Collision Avoidance (CSMA/CA); hence, the transmission and carrier-sensing ranges are essential. In general, the one-hop transmission distance is inversely proportional to the data rate in the IEEE 802.11 standards. As a result, in a complete transmission within an identical end-to-end distance (ED), the number of nodes increases when the data rate increases, and vice versa. That results in the inherent trade-off between transmission speed and transmission distance when selecting the data rate. However, the node’s carrier-sensing range is identical under the same transmission power. Therefore, the higher the data rate is, the more nodes exist in the carrier-sensing range, wherein the impact of frame collisions is not negligible. Motivated by that, this work aims to establish mathematical models considering the data rates accounting the issue.
In theory, several articles theoretically analyze the network performance of multi-hop wireless, mostly the string topology, using the airtime concept.10–20 First introduced in Chung and Liew 10 for saturation throughput in IEEE 802.11 networks, the concept combines a contention graph to derive the saturated throughput model for a given source–destination pair in Gao et al. 11 In Sugimoto et al., 13 the authors have extended the model to account for the throughput of two-way flows (of a VoIP traffic). Other IEEE 802.11 features such as Request To Send/Clear To Send (RTS/CTS), hidden node collision, long-frame communications, and back-off-stage synchronization have been investigated in previous studies,14–16 respectively. In Qinjuan et al., 17 the integration of airtime Markov chain analysis has well handled the IEEE 802.11 multi-hop network’s unsaturated condition. The proposed model in Shimoyamada et al. 18 can formulate multi-hop networks’ performance using the IEEE 802.11e Enhanced Distributed Channel Access (EDCA). In Sanada et al., 19 the authors successfully derive the models that can manipulate varying hop number, frame length, and offered load. Besides the throughput, the airtime concept is also applicable for the delay analysis in multi-hop networks as in Sanada et al. 20 The previous works, however, often assume the carrier-sensing range is as twice as the transmission one. Hence, they have considered the varying number of nodes within a carrier-sensing range. As a result, the previous models cannot formulate the aforementioned trade-off caused by the data rates.
This article introduces the new theoretical analysis, which derives expressions for end-to-end throughputs and delays for IEEE 802.11 multi-hop networks. The expressions, which are formed from the airtime concept, efficiently assess the data rate parameter. The proposed model newly introduces the parameter
The remainder of this article is organized as follows. Section “Background and related works” describes the related works about conventional models for multi-hop networks. Our analytical approach, which considers data rates, is presented in section “Proposed analytical models.” In section “Evaluation results,” we validate the proposed model by comparing its results to the simulation ones and discuss the network performance. Finally, we draw the conclusion for this work in section “Conclusion.”
Background and related works
IEEE 802.11 data rates
There are multiple data rates (i.e. transmission speeds) in the physical layer of the IEEE 802.11 standards. Each defined data rate follows a modulation and coding scheme (MCS) index that includes a modulation type, a coding rate, several spatial streams, and an operation band. When the data rate increases, the signal of associated MCS becomes more sensitive to noise. Hence, the higher the data rate, the shorter the transmission distance in general. In a multi-hop IEEE 802.11 network, considering one-hop transmission, there is a similar trade-off between the transmission speed and the transmission distance. However, in such a scenario, the carrier-sensing range of a node is independent of the transmission speed. When a node operates at a high data rate, the number of nodes within its carrier-sensing range is more significant than that in a lower data rate operation. Therefore, to comprehend the trade-off within the carrier-sensing range of a node, it is necessary to consider the impact of hidden node and concurrent frame transmissions among the nodes.
Airtime concept
The airtime concept is a useful theory to understand the behaviors of the IEEE 802.11 wireless networks. During a duration, the theory can be used to characterize each IEEE 802.11 node’s state corresponding to the IEEE 802.11 operation. More specifically, the IEEE 802.11 node is always in a transmission state, a carrier-sensing state, or an idle state. The first one indicates that the nodes’ frames are being transmitted. The second one represents the condition in which the node detects frame transmissions of other nearby nodes. The last state means there is no transmission in the network. All the three states could be formulated in consideration of the neighboring nodes’ states. Hence, the airtime analysis is possible to express each network node’s operation and the mutual effects between the nodes, and that is effective in the context of the multi-hop IEEE 802.11 network. The fundamental of airtime concept can be represented via the transmission airtime as follows. At Node
where
Airtime-based analysis
The theoretical analysis using airtime concept has shown the applicability in IEEE 802.11 wireless networks under various conditions.10–20 The airtime concept was initially proposed in Chung and Liew 10 to construct a model for the maximum saturation throughput. However, the model assumed that simultaneous frame transmissions are negligible. Moreover, it considers only collisions with hidden nodes for the sake of simplicity. The authors in Gao et al. 11 proposed the analytical model that combines airtime and contention graph to derive the throughput of a given source and destination pair. In Inaba et al. 12 and Sugimoto et al., 13 the authors additionally considered two-way flows and RTS/CTS handshake, respectively. Both works have got the maximum throughput in multi-hop wireless networks. The proposed model in Zhao et al. 14 can analyze the intra-flow contention problem by expressing hidden node operation using airtime. In Sekiya et al., 15 the applicable range of the airtime model has been extended from short-frame communication to long-frame communication. In Sanada et al., 16 the mechanism of back-off-stage synchronization, which is efficient in multi-hop networks, was revealed. In Qinjuan et al., 17 the authors proposed the bandwidth mapping model in unsaturated conditions by combining the airtime concept and the Markov chain model. The work in Shimoyamada et al. 18 established the mathematical model for multi-hop networks considering IEEE 802.11e EDCA. The generalized analytical model for string-topology multi-hop networks, which is applicable under any conditions of hop number, frame length, and offered load, has been proposed in Sanada et al. 19 The same authors have proposed the analytical models for the end-to-end delay in multi-hop IEEE 801.11 networks in Sanada et al. 20 However, all these previous works assume a small number of network nodes in the carrier-sensing range, and that is because the carrier-sensing distance is assumingly the same or twice as the transmission distance. Therefore, all of them have not considered the condition where many nodes coexist in the same range. One of the recent works, which uses airtime concept, addresses the dense nodes but within a transmission range (i.e. single-hop), focusing on the capture effect. 21 In Liu et al., 22 the airtime-based analysis has been also applied in dense wireless networks aiming to quantify the inter-network interference. The earlier results of this work have been presented at IEEE VTC Spring 2019. 23 In this article, we newly include the delay analysis, besides the throughput one. Moreover, the evaluation results are more extensive.
Proposed analytical models
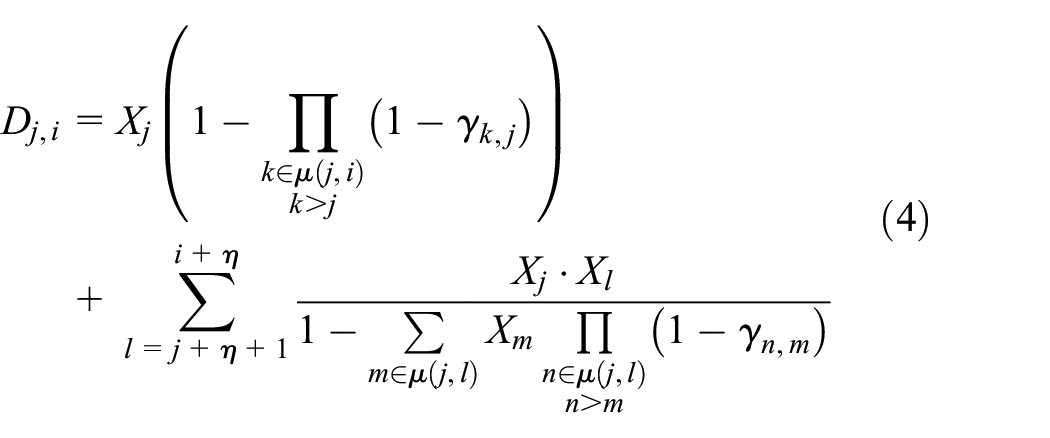
This analysis expresses the difference in transmission distances that depends on the data rate using the ratio of the carrier-sensing distance to the transmission distance. We aim to derive the end-to-end throughput and delay as functions that take the ratio into account when modeling each network node’s operation. Moreover, the airtime concept is used to quantify relationships among network nodes. Figure 1 shows the investigated network, which is an H-hop string-topology IEEE 802.11 one. In such a network, the wireless nodes are located at an identical distance, while the total distance from the source to the destination node is denoted as ED. The following analysis is based on several assumptions:
Node 0 is the only data source, which generates traffic to Node H (i.e. the destination). The traffic including fixed sized data frames follows the Poisson distribution.
The intermediate node (e.g. Node i) only relays the frame from Node
All links have ideal channel conditions. In other words, the transmission failures occur only due to the MAC layer.
Node i can sense frame transmissions from Node
Investigated wireless network topology with H hops and the end-to-end distance ED.
Transmission airtime
The transmission airtime, which is defined as the timeshare of frame transmissions, includes both the successful and failure transmission durations. 10 Using the general expression of the transmission airtime in equation (1), the throughput of Node i can be expressed as
where
Carrier-sensing airtime
The carrier-sensing airtime is known as the timeshare of the frame transmissions of the nodes in the carrier-sensing range. Considering the duplication time of frame transmissions, the carrier-sensing airtime of Node i is
where
where
Channel-idle airtime
The channel-idle airtime is the timeshare that no neighbor node transmits a frame, and that means the node associated with the channel is not in either the transmission state or the carrier-sensing state. Therefore, the idle airtime is
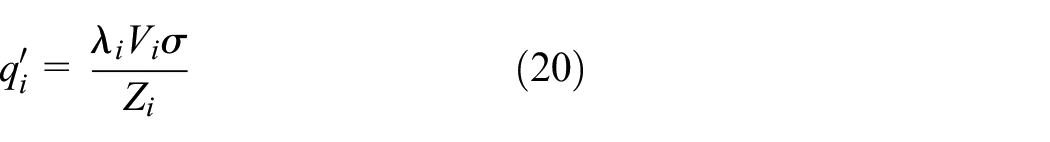
Collision probability
In the investigated topology, the frame collisions occur due to either the concurrent frame transmissions or the hidden node frame ones. Those collision events are, however, independent. Therefore, at Node i, the probability of frame collision is
where
The concurrent transmissions occur at Node i when at least one node within its carrier-sensing range transmits a frame at the same moment as Node i begins a fame transmission. Hence, the concurrent-transmission collision probability of Node i is
From the assumption 4, we know that the hidden node of Node i is Node
where
The collision probabilities can be formed from a Markov chain model as in Figure 2.
19
In the model, d is the number of slots required for a DATA frame transmission;
where

Node i’s Markov chain model with the back-off timer decrement and transmission states in case of
From the Markov chain model in Figure 2,
where
where
and
Frame transmission probability
At Node i, the probability of frame transmission is the probability that the node starts frame transmission when being in the idle state. More specific, the node attempts to transmit a frame when its BT is zero. From the Markov chain model in Figure 2, the frame transmission probability of Node i in the saturated condition is
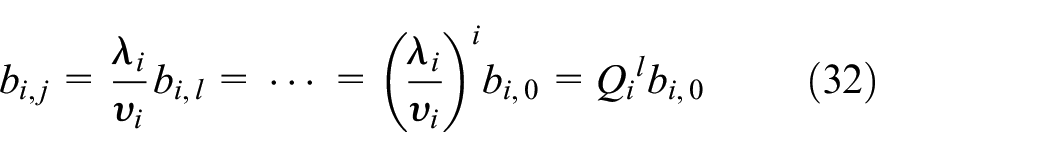
In the case of expressing the non-saturated condition, we need to define the frame-existence probability,
where
Therefore, the airtime for the BT decrement is
where
In equation (19),
We know that the frame-existence probability in the saturated condition is one. Therefore, the frame-existence probability in the whole time can be expressed as
Using the probability in equation (21), the frame transmission probability is
which is also valid for both the non-saturated and saturated states. Considering the number of frame transmissions per unit time and the time for one frame transmission success, the transmission airtime of Node i is expressed by
In addition, the probability that Node i and Node j simultaneously start transmitting a frame is expressed as
where
End-to-end throughput
In the string-topology network with H hop, the end-to-end throughput can be derived as
End-to-end delay
The definition of end-to-end delay in this work is similar to the one in Sanada et al. 20 The delay is the duration from the moment that the DATA frame is generated at the source node to the instant when the destination node receives the DATA frame. In other words, the end-to-end delay is the sum of multiple delays of single-hop transmission from the source node to the destination node. However, the single-hop transmission delay includes two types of delays, which are the MAC access delay and the queueing one.
The frame-existence probability,
From equation (27), we have
Figure 3 shows the

Node i’s buffer queueing model.
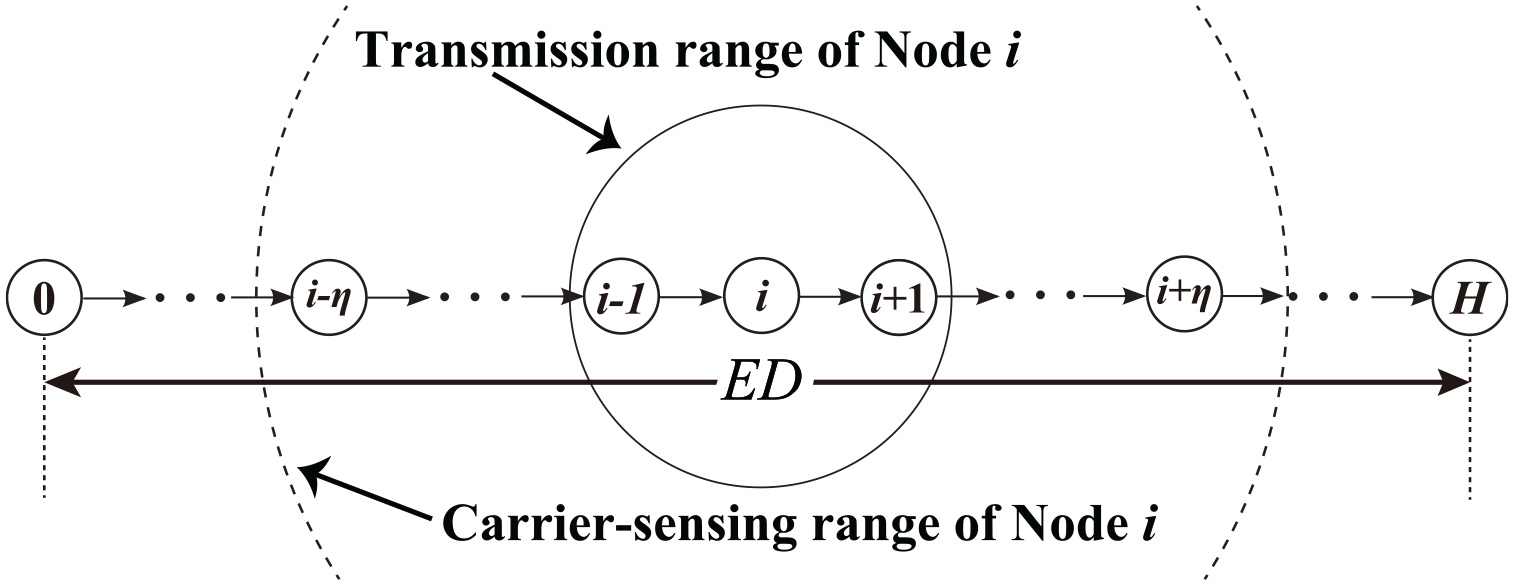
The queueing delay is the time duration from the instant that Node i receives a frame to the instant that the frame reaches to the top of Node i’s buffer. Using the service time in equation (29), the service rate of the model in Figure 3 can be as follows
Since we know the frame reception rate from equation (19) and the service rate from equation (30), the buffer utilization rate of Node i can be derived in equation (31)
From the model in Figure 3, we can derive the steady-state probability that the Node i has
Because
Besides, since the sum of the steady-state probability that Node i has
By combining equations (32)–(34), we have
Using the steady-state probability that the Node i has
From equations (33) and (36), the total transmission delay at Node i is calculated as
From equation (37), we can obtain the end-to-end delay in the H-hop string network
From the above analysis, when the offered load is given, we can obtain the end-to-end throughput and delay by fixing 4H unknown parameters including
Evaluation results
This section presents the validation of the proposed analytical models. We compare the analytical results to simulation ones, as well as evaluate the network performance. We use the simulator, which has been developed in our laboratory. The simulator efficiently describes the operations of IEEE 802.11 wireless nodes. Moreover, the validity of our simulator is carefully discussed in Ikuma et al.
24
In our evaluation, the system parameters have been associated with the IEEE 802.11a standard. Table 1 gives the values of typical investigated parameters. We investigate the throughput and delay performance with the variations of
System parameters.

ACK: ACKnowledgement; SIFS: short inter-frame space; DIFS: distributed inter-frame space.
Throughput performance evaluation
Figure 4 shows comparison between the analytical and simulation results of the end-to-end throughput with different values of
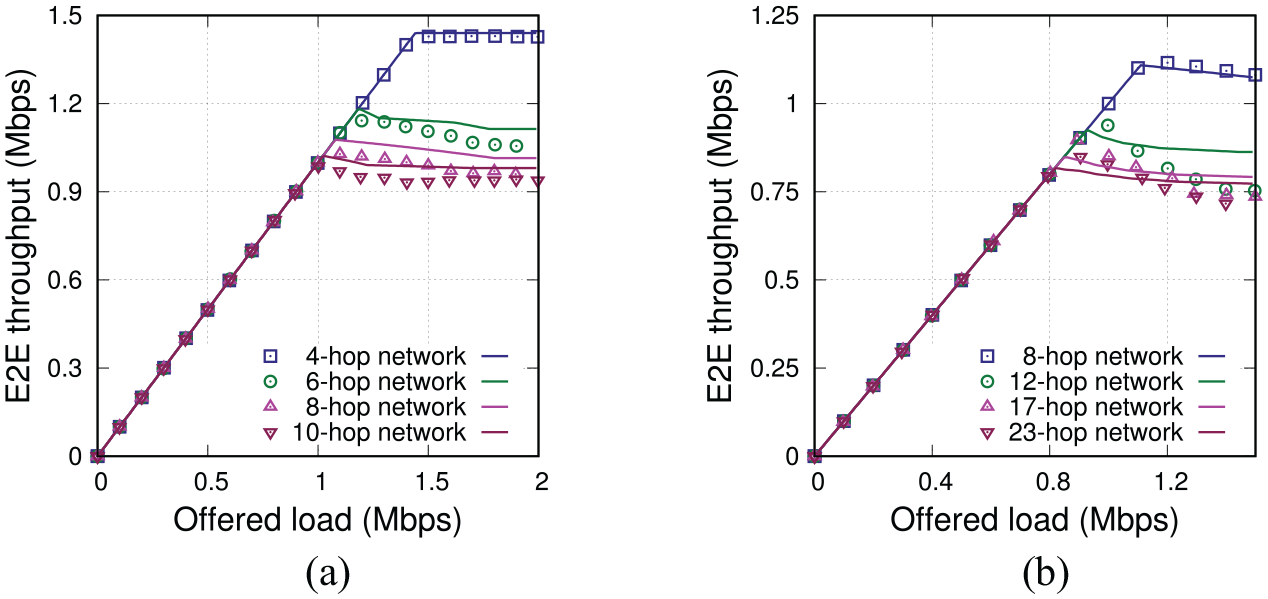
Comparing end-to-end (E2E) throughput between analytical model (lines) and simulation (plots) with different
Figure 5 shows the comparison of end-to-end throughput when the ED is fixed while the value of

Comparing E2E throughput between analytical model (lines) and simulation (plots) in different ED scenarios: (a) end-to-end distance
Delay performance evaluation
Similar to the previous evaluation, this section investigates the network performance when the offered load varies, but focusing on the end-to-end delay. Figure 6 shows the comparison of end-to-end delay values, which are collected from the simulation and analytical results. Wherein, Figure 6(a) and (b) shows the results for fixed-hop networks with
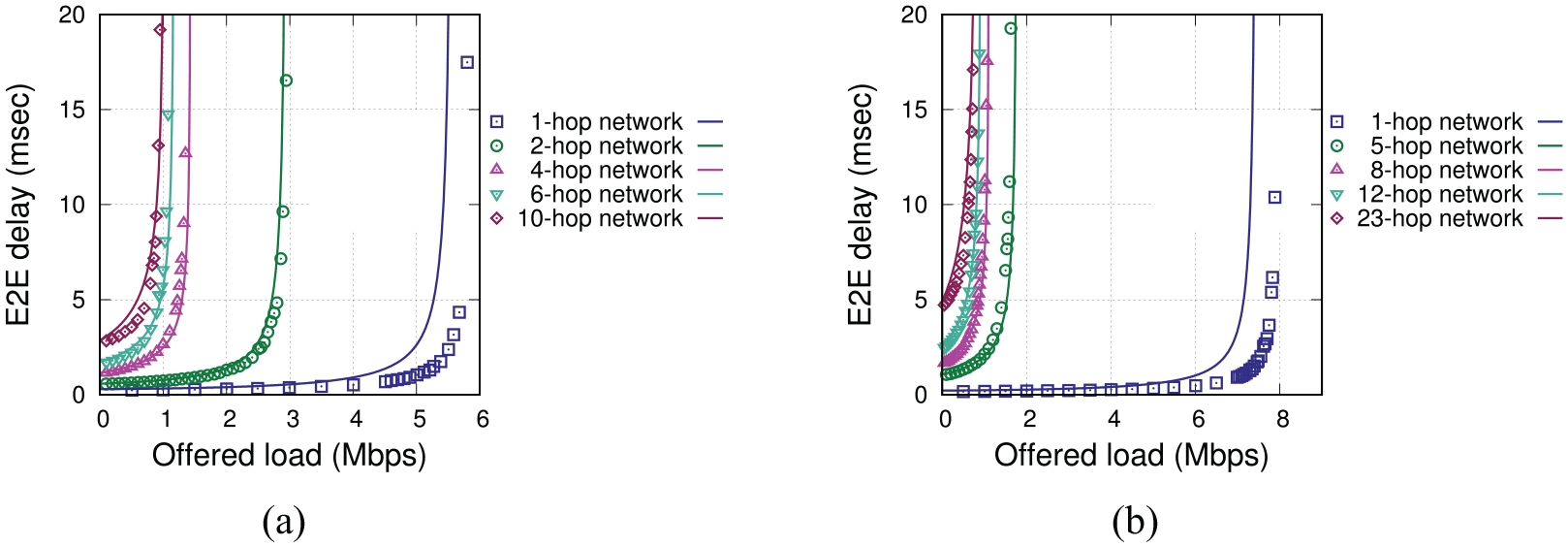
Comparing E2E delay between analytical model (lines) and simulation (plots) with different
Figure 7 shows the end-to-end delay with different EDs, at each of which five fixed values of
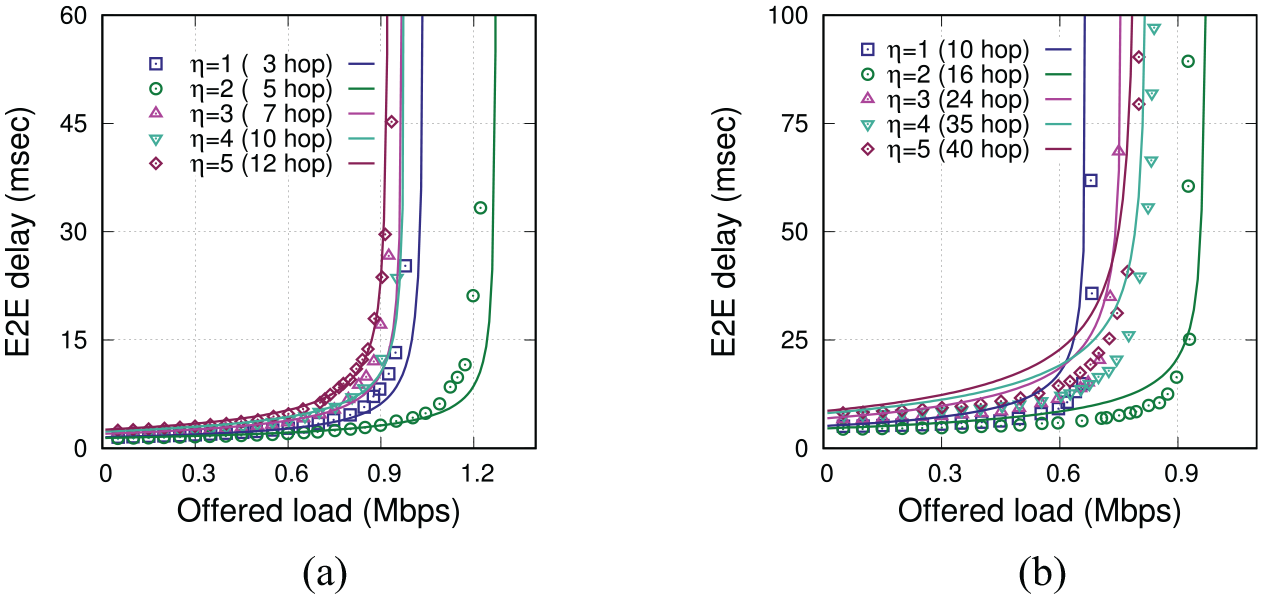
Comparing E2E delay between analytical model (lines) and simulation (plots) in different ED scenarios: (a) end-to-end distance
Conclusion
In this work, we have proposed the new theoretical models for the IEEE 802.11 string-topology multi-hop networks’ performance, including the end-to-end throughputs and delays. The models newly take into account the data rate by introducing the parameter
Footnotes
Handling Editor: Donatella Darsena
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the JSPS KAKENHI (grant no. 19K20251). In addition, K.N. is supported by the Leading Initiative for Excellent Young Researchers (LEADER) program from MEXT, Japan.