Abstract
As a potential technology, the identity-based online/offline encryption scheme is split into two phases (the offline phase and the online phase) which is especially suitable for sensor nodes with limited computation resources in that most of the works can be executed offline. However, a challenging issue is the well-known identity-based online/offline encryption schemes unable to resist continual key leakage attacks of the secret keys. To address the above security challenge, we put forth the first continual leakage-resilient identity-based online/offline encryption scheme which is suitable for ensuring secure communications in wireless sensor networks. More specifically, our formal security proofs analysis indicates that the proposed scheme can guarantee security even if partial information of the secret key is continually leaked due to side-channel attacks or fault injection attacks. Above all, compared to the existing identity-based online/offline encryption schemes, an identity-based online/offline encryption scheme with continual leakage resilient meets wireless sensor networks with strong security.
Keywords
Introduction
Wireless sensor networks (WSNs) as a major technique is an academic hotspot that possesses the advantages of building the Internet of things (IoT). Due to the demand for sensing, gathering, and monitoring data, individual users and enterprises make better management control and decision-making. For example, individual users equipped with tiny sensor nodes continuously monitor their sensitive data such as health records and so on which is necessary to be encrypted before transmitting to the base stations (BSs). However, the security and efficiency challenges need to design access control systems in WSNs. For one thing, the sensor nodes have the limited capabilities. For another, most of the existing access control schemes were proposed in a weak security model. In order to solve the above problems, researchers directly utilized typical identity-based encryption (IBE) schemes to design access control systems. IBE1–4 is one of the powerful cryptographic mechanisms to realize the above functionality. The encryption procedure of IBE simply employs the user’s identity which was composed of an arbitrary string. However, the IBE system always requires the user to execute expensive computations, such as pairings over points on the elliptic curve and exponentiations in groups which is not desirable for weak users with limited computation resources. Especially in WSNs, the nodes have very limited computation resources, memory, and storage capabilities. These make many cryptographic primitives impractical. A good solution to reduce the computational overhead of encryption procedure is the model of identity-based online/offline encryption (IBOOE) which splits the encryption process into two phases: the offline phase and the online phase. In the offline phase, the vast majority of the work is to be done and it requires neither the information of the message to be encrypted nor the receiver’s identity. This division of computational tasks makes most of the works executed offline. However, the security and efficiency challenges have appeared when traditional IBOOE schemes are directly utilized in the WSN environment. In such applications, it is usually assumed that the adversary cannot get any information about the internal secret states. In contrast, this assumption no longer holds in WSNs in that a malicious adversary can obtain partial information from side-channel attacks 5 which will lead to the leakage of important sensitive information. Then, a natural question arises: Can we design a provable secure IBOOE scheme resilient to the continual leakage of secret keys? A plausible solution to the above problem might be dual system encryption which has the potential to address the problem of continual key leakage for traditional IBOOE schemes.
Related work
In this subsection, we summarize leakage-resilient IBE (lr-IBE) cryptography and the online/offline encryption cryptography.
Leakage resilience was first studied in public key setting by Akavia et al. 6 It is a powerful tool to ensure security-protecting data confidential against side-channel attacks. Naor and Segev 5 extended leakage resilience to the public key encryption. More broadly, Alwen et al. 7 first introduced leakage-resilient security to identity-based setting and constructed lr-IBE scheme using the identity-based hash proof system (IB-HPS). Unfortunately, only the third scheme was proved in the standard model based on Gentry’s IBE system. 3 So far, two main models have been proposed: bound leakage model (BLM) and the continual leakage model (CLM). The first line of work constructs lr-IBE schemes that are proven secure in the BLM. In CCS, Chow et al. 8 proposed three lr-IBE schemes assuming that each secret-key holder had two randomness that applied to secret keys and master secret keys. The first two lr-IBE schemes based on BB-IBE 1 and Waters-IBE 2 , respectively, which had selective security and the third scheme was fully secure and short public parameters using Lewko and Waters’s dual system encryption. 4 Namely, they showed how to go from IB-HPS to lr-IBE scheme. Li et al. 9 investigated how to accomplish chosen ciphertext attack (CCA) security of the lr-IBE scheme by applying a hash proof technique into Gentry’s IBE scheme. 3 However, the lr-IBE schemes presented in Alwen et al., 7 Chow et al., 8 and Li et al. 9 cannot resistant to continual key leakage attack. Another line of work is so-called the CLM. It divides the lifetime of the cryptosystem into some periods, and updates the secret keys at the end of each period. Lewko et al. 10 first proposed the IBE scheme under continual leakage resilient which allows continual leakage of user’s key and master key. Subsequently, Li et al. 11 developed the first identity-based broadcast encryption scheme under continual leakage of secret keys of any identity. To improve the security level, Zhou et al.12–14 gave exciting new continual leakage-resilient constructions for IBE from decisional bilinear Diffie–Hellman (DBDH), truncated augmented bilinear Diffie–Hellman exponent (q-TABDHE) assumptions, and a new primitive called updatable identity-based hash proof system (U-IB-HPS). Recently, many BLMs and CLMs were surveyed in Zhang et al. 15 and Yael et al. 16
Online/offline encryption technology has been widely accepted as an effective method to protect data security and privacy in online/offline scenarios and becomes a useful tool to achieve effective encryption such that only the authorized users can access the data. Online/offline encryption technology mainly focuses on efficient encryption which is different from efficient decryption.
17
Guo et al.
18
first introduced encryption schemes which split the encryption procedure into two phases: the offline phase and the online phase. In the offline phase without input of plaintext and user’s identity, it outputs the offline ciphertext. Then, in the online phase, it efficiently generates the online ciphertext concerning plaintext and the identity of the user. Subsequently, Liu et al.
19
presented a more efficient IBOOE scheme in the random oracles which is especially suitable for embedded devices of limited computation power such as smart cards or wireless sensors. Later, Chu et al.
20
proposed a practical IBOOE scheme in the selective-ID model, which is suitable for WSN which removed the elements in the group
Motivation and our contribution
The primary challenge for the IBOOE schemes is to achieve leakage resilience. In this article, we consider the continual leakage resilience in IBOOE schemes. Specifically, the contributions of this work are elaborated as follows:
Motivated by the aforementioned application to leakage tolerance in WSNs, we study IBOOE resilient to a stronger form of leakage. We first introduce the notion of the continual leakage-resilient IBOOE (clr-IBOOE) and formalize its framework. In clr-IBOOE, the encryption procedure is split into two phases, that is, an offline phase and an online phase. To support continual leakage functionality, we expand the space of secret key and ciphertext to
We utilize the semi-functional structures and a hybrid argument which was used in the security proof by a sequence of games. The main difficulty in constructing our scheme is to implement nominally semi-functional secret keys that can decrypt semi-functional ciphertext without the adversary awareness of. Nominality permits the simulator to produce nominal semi-functional keys which is decrypt successfully the interrelated challenge ciphertext while the adversary was unaware of the above process.
We provide provable security of clr-IBOOE, including indistinguishability of normal secret keys and semi-function secret keys, indistinguishability of normal ciphertext and semi-function ciphertext, and continual leakage of secret keys. In addition, we conduct a comprehensive performance evaluation compared with the existing IBOOE schemes, our scheme not only enjoys continual leakage resilience but also avoids the additional online computation. Specifically, clr-IBOOE dramatically realizes the strongest features of continual leakage. This is because that in update process, the secret key is updated over time.
The rest of the article is organized as follows: in section “Preliminaries,” we describe the notation used in this article, composite order bilinear and complexity assumptions. In section “System architecture and security model,” we first present a continual leakage-resilient security model and a formal definition for IBOOE, respectively. Then, we propose a clr-IBOOE scheme based on three assumptions in which encryption can be afforded by mobile devices with limited computation power. We elaborate on formal security proof in the standard model based on the new security model in section “System architecture and security model.” And in section “Provable secure IBOOE with continual leakage resilience in WSNs,” we give efficiency results and security of the new scheme compared to the existing IBOOE schemes. At last, we conclude this article in section “Security proof and efficiency comparisons.”
Preliminaries
In this section, we introduce the preliminary knowledge on some cryptographic background used throughout this article.
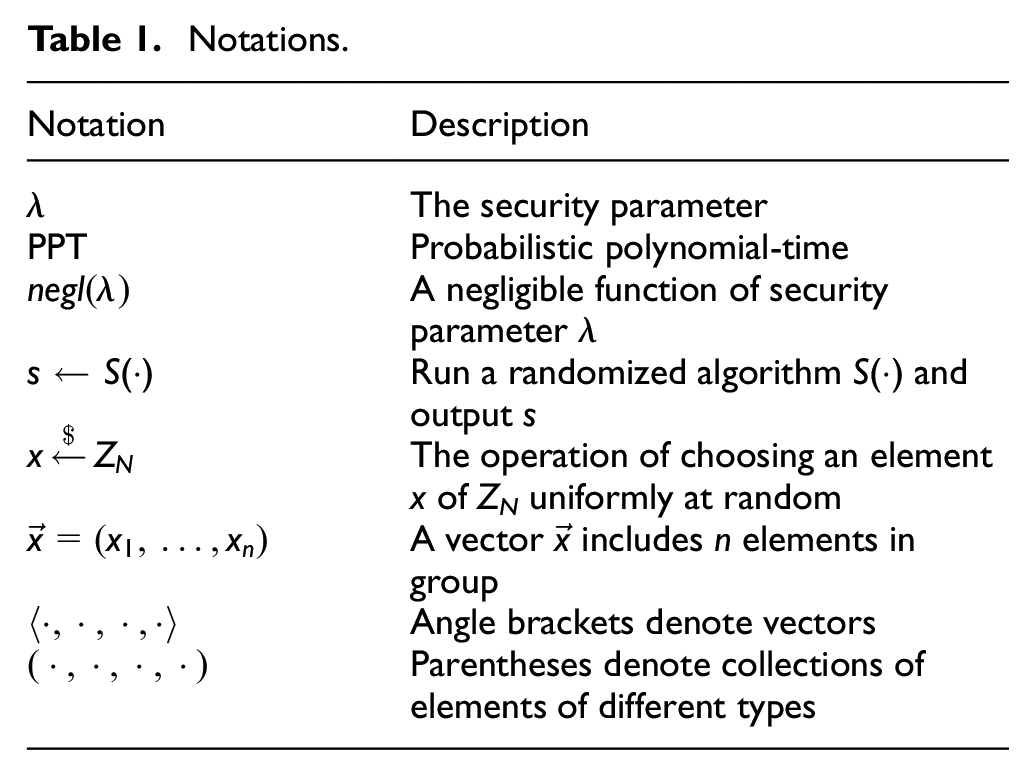
Notations
Assuming that all the algorithms take as input the security parameter represented in unary, that is, 1λ. Let
Notations.
Composite order bilinear groups
Three assumptions based on the pairing over composite order groups4,10 are as follows. Let the parameters be N = p1p2p3, where p1, p2, p3 are three numbers. The group generator algorithm I takes as input a security parameter 1λ and outputs the description of a bilinear group (N = p1p2p3, G, GT, e). In the group description, p1, p2, p3 are three distinct numbers; G and GT are cyclic groups of order N; and e:G × G → GT is a bilinear map. We assume that the generator algorithm outputs the values of p1, p2, p3 and gi is generator of subgroup Gi of order pi. Moreover, let Gij denote the subgroup of order pipj which implicitly have
Complexity assumptions
Assumption 1
Given D1 = (N, G, GT, e, g1, g3), it is hard for an adversary to distinguish
Assumption 2
Given D2 = (N, G, GT, e, g1, g3,
Assumption 3
Given D3 = (N, G, GT, e, g1, g2, g3,
The advantage of an algorithm A in Assumption i where i ∈ {1, 2, 3} is defined as

Security theorem
In the context of Lewko and Waters,
10
it expands the semi-functional space to n + 2 dimensional vectors, where
Lemma 1
Under Assumptions 1, 2, 3 and for
System architecture and security model
Before giving the formalized security model, we first lay out the system architecture and specification of an IBOOE scheme with the key update algorithm which is the underlying technique of the proposed secure identity-based online/offline scheme with continual leakage resilience for WSNs.
Network model
In WSNs, we focus on single-SP (service provider) multi-user sensor network. The overview of the network model is shown in the following Figure 1. There are four different entities in the system, that is, the SP, the sensor node, the gateway, and the network user.
SP is an authority who deploys a sensor network composed of multiple sensors, such as the registration of sensor nodes and users. The SP is a trusted third party.
Sensor nodes are battery powered which is a big challenge for network designers. Note that sensor nodes can offline.
Gateway: compared with sensor nodes, it has much higher storage and processing capability.
Users: a user can join the system by registering with the SP to join the WSN.

Network model.
It is assumed that all the entities except SP are “honest-but-curious.” Sensor nodes generate offline ciphertexts, encrypt a file, and outsource the final ciphertext to SP. When users use the encrypted data, he downloads a ciphertext from SP. Then, he decrypts it based on the secret keys if the ciphertext is legitimate.
Specification of clr-IBOOE
An IBOOE scheme typically consists of six algorithms: Setup, Ext, UpdateSK, Enc off , Encon, and Dec. In the continual leakage setting, we require an additional algorithm UpdateSK which updates the secret key of users. We define a continual leakage resilience IBOOE scheme, clr-IBOOE in short. Note that the public key remains unchanged. The definition below summarizes the above.
Definition 1 (clr-IBOOE)
IBOOE schemes are defined by a tuple of algorithms and protocols
Security model
In our surroundings, there exist two adversaries either an external intruder or a registered network user who intended to obtain other users’ data without the authorization of access according to work.
24
Based on the adversary’s ability and the specification of IBOOE scheme, we formalize the security model by specifying the ability of adversaries. To define continual leakage security, we extend the CLM of Li and Zhang
11
to online/offline identity-based setting. The security model is defined through a game played by a probabilistic polynomial-time (PPT) adversary A and a challenger (also called simulator). Assuming A cannot win the following security game
Ext(h, I): h is a handle that has to refer to a secret key. Given an identity I, the challenger B looks up the item with the identity I in the list L. If it exists, B terminates. Otherwise, it creates a key for this identity I by calling the key extraction algorithm Ext(I, MSK) → SKI, updates h ← h + 1 and adds the item (h, I, SKI, 0) into the list L.
Leak(h, f): Given a handle h, the challenger looks up the item with the handle h in L. A selects a polynomial-time computable function f of constant output size acting on the set of keys. If the handle h exists, B checks if Cntr + |f(SKI)| ≤ lSK where lSK is the leakage bound for the secret key. If this is true, it responds with f(SKI) and updates the Cntr with Cntr + |f(SKI)|.
Reveal (h): The attacker A requests the entire secret key for handle h. The simulator looks up in the list L. If it finds the item, it denotes the tuple by (h, I, SKI, Cntr). B returns this item and adds the identity I to the set K.
UpdateSK (I): The simulator queries a new secret key of I with a polynomial-time computable function f. B looks up the item with the handle h in L. Then, it runs algorithm UpdataSK(SKI) to get the updated secret key
Decrypt (I, c): The adversary queries a message for (I, c), the simulator looks up the list L to get the secret key SKI. The simulator calls the algorithm Dec(skI, c) to recover the corresponding plaintext m and sends it to the adversary.
Definition 2
If for all PPT adversaries A, the advantage
Provable secure IBOOE with continual leakage resilience in WSNs
In this section, we first present the proposed IBOOE with continual leakage resilience in WSNs and then show its correctness. Our clr-IBOOE scheme Π comprises six algorithms detailed as follows.
Details of the proposed IBOOE scheme
Our construction of clr-IBOOE scheme employs a composite order bilinear groups I = (N = p1p2p3, G, GT, e) where p1, p2, p3 are three λ-bits length primes; G, GT are cyclic groups with order N = p1p2p3; and e is such a bilinear map e:G × G → GT. Assume that each identity is an element in ZN and every message is an element in group GT. In our scheme, the secret key is randomized by subgroup G3. The elements of subgroup G2 will not be used in the real scheme, but it supplies semi-functional property.
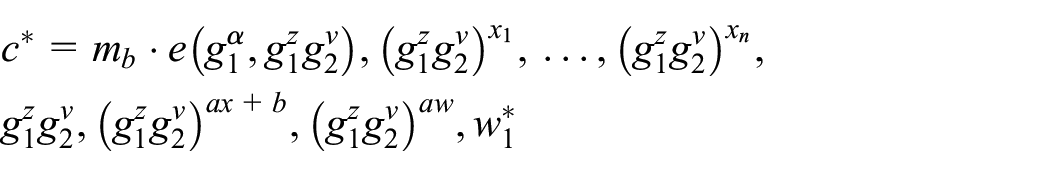
The offline storage is
Finally, the message is computed as
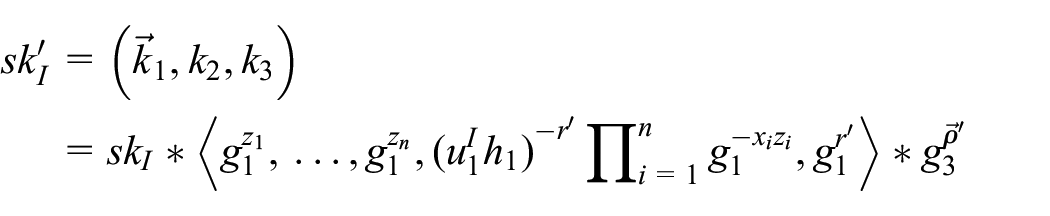
Continual leakage
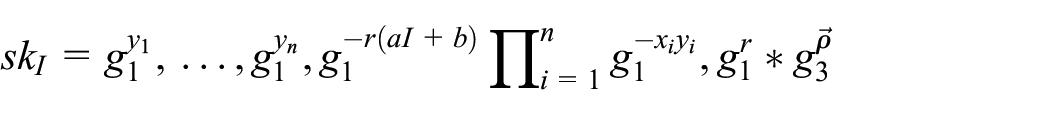
To implement re-randomization, we give here the update algorithm for the secret keys.
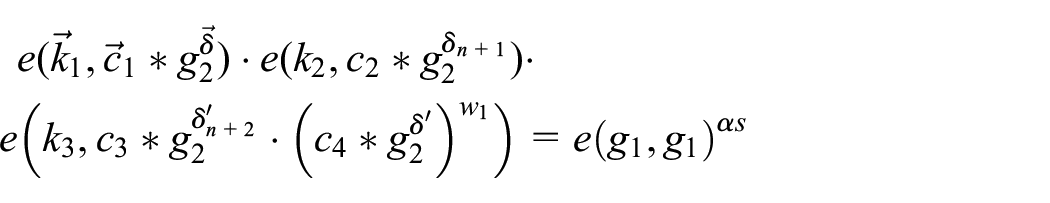
Semi-functionality
All the secret keys and ciphertext generated by the above algorithms are normal which has no group G2 parts. To get semi-functional key and ciphertext, we add a factor of G2 into the normal key and normal ciphertext as follows:
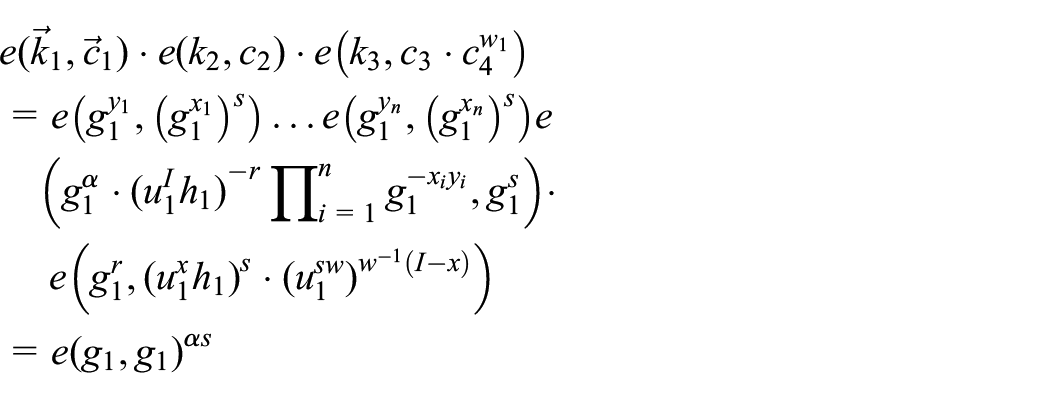
Procedure of decryption
First, we contract the two terms
1. The normal secret key decrypts the semi-functional ciphertext as follows
2. The semi-functional secret key decrypts the normal ciphertext as follows

3. The semi-functional secret key decrypts the semi-functional ciphertext as follows
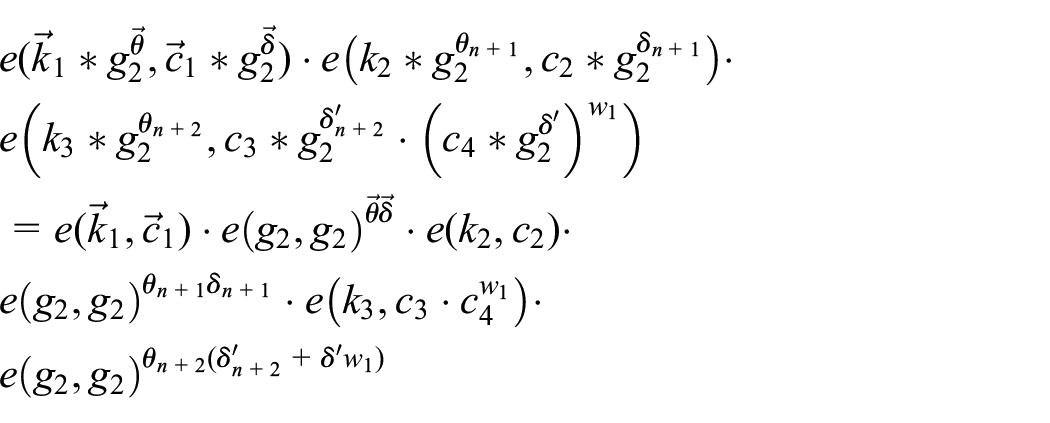
Here, we write
Through the above analysis, we obtain an additional entry
Security proof and efficiency comparisons
Security proof
Theorem 1
If Assumptions 1, 2, and 3 hold in G, GT, then the above proposal Π is lSK-fully secure against key leakage attacks.
Proof
Each secret key skI is a
By the following lemmas, we prove these games are indistinguishable.
Lemma 2
Suppose there exists a PPT algorithm A such that
Proof
The algorithm B simulates fully the encryption scheme Π as follows. B receives D
1
= (N, G, GT, e, g1, g3) and T where
Both games, B always calculates normal secret keys for all identities as follows. B randomly chooses
In the challenge phase, B gets two messages m0, m1 and the challenge identity I* from A. Then, it randomly chooses b ∈ {0, 1},
If
If

This implicitly has s = z. We get the semi-functional parameter
Lemma 3
Suppose there exists a PPT algorithm A such that
Proof
If the challenge instance B simulates fully, the encryption scheme Π as follows. B receives D2 = (N, G, GT, e, g1, g3,
If k < i, B generates the semi-functional secret key for identity I as follows

If k = i, B simulates the challenge secret key for identity I as follows

If k > i, B creates the secret key of identity skI like lemma 1.
In challenge phase, B selects two distinct and random messages m0, m1 with equal length and the challenge identity I*. It sends the messages to A. Then, it randomly chooses b ∈ {0, 1}, x, w ∈ ZN and returns the challenge ciphertext as follows
Here, it has
This implicitly has s = z and
Lemma 4
Suppose there exists a PPT algorithm A such that
Proof
B simulates fully the encryption scheme Π as follows. B receives D3 = (N, G, GT, e, g1, g2, g3,

In the challenge phase, the challenge ciphertext generates as follows

Here, it has coefficient
If
Finally, in game LeakF value of b is information theoretically hidden from the adversary A. Consequently, A has no advantage in winning LeakF. Hence, cLeak is indistinguishable from LeakF if Assumption 1, 2, and 3 hold. As a result, the adversary has negligible advantage in winning game cLeak. Lemma 2, Lemma 3, and Lemma 4 conclude the proof of Theorem 1. Thus, we finish the proof of Theorem 1.
Theorem 2
If Assumptions 1, 2, and 3 hold in G, GT, our proposed scheme
Proof
According to the algorithm UpdateSK given in section “Continual leakage,” we get continual leakage resilience. The algorithm UpdateSK inputs the secret key skI, identity I, and master public key mpk and then outputs a new secret key
Leakage resilience and performance analysis
In this section, we draw a comparison between the proposed scheme and the existing IBOOE schemes in Table 2. The computation efficiency and offline-storage cost are determined by the computation costs of the encryption algorithm which constitutes two subroutines Enc off (mpk) and Encon(m, mpk, I, c off ). When evaluate the computation efficiency, we omit minor factors such as hash functions. We calculate only the dominant operations which are the exponentiations in Gi or GT denoted as E and the multi-exponentiations in Gi or GT denoted as ME. For modular computation in Zp and ZN, we denote by mc(Zp) and mc(ZN). Without loss of generality, we assume that one multi-exponentiation is equal to two exponentiations in group Gi or GT. Moreover, the size of element in the group Gi and GT is denoted by |Gi| and |GT|, the size of element in ZN is denoted by n. Furthermore, to avoid a large number of calculations at the online encryption phase, we place it in the offline encryption phase. According to Table 2, we can obtain that our proposal have the minimum computation of Encon(·,·,·,·) algorithm and achieve leakage resilience. This is suitable for WSNs which were interconnected sensor nodes that communicate wirelessly to collect data about the surrounding circumstance. Moreover, LR and CLR denote the security of leakage resilience and continual leakage resilience, respectively. Even though the offline storage has a larger size than other two traditional IBOOE schemes. From Table 2, it is clear that our scheme resolves the problem of continual leakage resilience which can be obtained naturally using the techniques of dual system encryption.
Comparisons of the existing IBOOE and clr-IBOOE scheme.
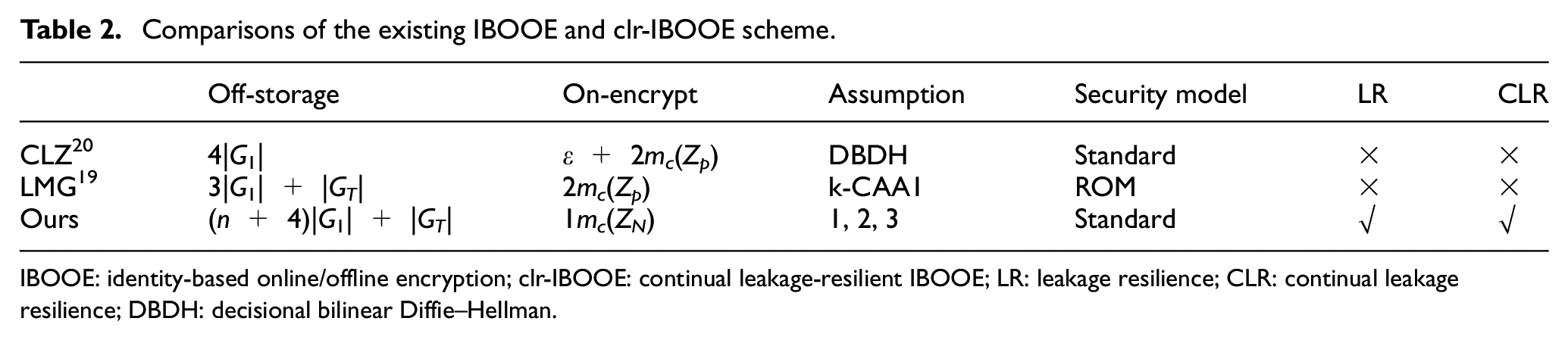
IBOOE: identity-based online/offline encryption; clr-IBOOE: continual leakage-resilient IBOOE; LR: leakage resilience; CLR: continual leakage resilience; DBDH: decisional bilinear Diffie–Hellman.
Conclusion
In this article, we propose the first clr-IBOOE scheme which is suitable for WSNs. Especially, sensor nodes in WSN with limited computation ability, but it also brings some security challenges. To avoid the problems of continual key leakage attacks in the existing IBOOE schemes, we formalize the notion and the security model for clr-IBOOE. Furthermore, we propose the first clr-secure IBOOE scheme based on three static assumptions in composite order groups. To the best of our knowledge, this is the first IBOOE resilient to continual key leakage. It achieves fully secure and continual leakage resilience against chosen plaintext attacks in the standard model. Compared with the schemes,20,19 performance analysis shows the proposed scheme has low computation overhead in the online encryption phase which is suitable for WSN with limited sensor nodes. As a direction of future work, designing secure IBOOE resilient to master secret key leakage would be another interesting work.
Footnotes
Acknowledgements
The authors would like to thank the reviewers for their detailed reviews and constructive comments, which have helped improve the quality of this article.
Handling Editor: Zheng Chang
Author note
The author Xingbing Fu is now affiliated to Guangxi Key Laboratory of Cryptography and Information Security.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by the National Natural Science Foundation of China (No. 61802249, No. U1936213, No. 61902283), the Key Technology Research and Development Program of Sichuan Province and Chengdu Municipality (NO. szjj2015-054), the Project of Shandong Province Higher Educational Science and Technology Program under grant J16LN56, the Weifang Science and Technology Development Plan Project (2017GX002), the Doctoral Research Fund of Weifang University (No. 2015BS11), Zhejiang Provincial Natural Science Foundation of China under Grant No. LY19F020045; Guangxi Key Laboratory of Cryptography and Information Security (No. GCIS201718); the Opening Project of Guangdong Provincial Key Laboratory of Information Security Technology (No. 2017B030314131-05); and the Key Research Project of Zhejiang Province (No. 2017C01062).
