Abstract
Attribute-based encryption is an efficient and flexible fine-grained access control scheme. However, how to realize the attribute privacy concerns in the access policy and optimize the heavy computing overhead have been not adequately addressed. First, in view of the open-access policies formulated by data owners in the cloud environment and the linear growth of bilinear pairing operations with the number of attributes in the decryption process, a verifiable outsourced attribute-based encryption with partial policy hidden scheme is proposed, in which the attribute name of access policy can be sent while attribute value involving sensitive information can be hidden, so nobody can infer information from the access policy. Second, the bilinear pairing operation and modular power operation are outsourced to the cloud server, then users only need to perform constant exponential operation to decrypt. In addition, the proposed scheme is based on the composite order bilinear group and satisfies full secure under the standard model. Finally, compared with other schemes in term of function and performance, it shows that this scheme is more efficient and suitable for resource-constrained mobile devices in outsourcing environment.
Introduction
With the rapid development of cloud computing, it is increasingly favored by all fields of the Internet because of its powerful computing resources and storage performance, thus lead to a new computing pattern: outsourcing computing. 1 Under cloud computing environment, users with limited computing and storage resources can outsource some time-consuming computing to the cloud server in order to reduce the burden. Based on the pay-as-you-go service, users can enjoy various information services provided by the cloud. When the data owner (DO) uploads the encrypted data to the cloud, he also loses actual control of the data. However, the cloud server is not completely trusted, so how to protect the private information in the uploaded data has become a popular research. Because DO encrypts data under access policy, ciphertexts can be decrypted by anyone with a set of attributes that satisfies the access policy. In attribute-based encryption (ABE) schemes, access policy is embedded in ciphertext implicitly and outsourced to cloud service provider (CSP) together with the ciphertext in a cloud environment. Because access policies are publicly available, everyone can access policies that contain private information. For example, in an electronic medical system, a patient authorizes a cardiologist to access encrypted data through the access policy as {Department: Cardiology; Doctor: Alice}. Without decryption, anyone who gains access to the encrypted data and can conclude that the patient might suffer from “heart disease.” If the content of the attribute value in the policy is not visible, that is, the policy is set as {Department: XXX; Doctor: XXX}, then the patient’s privacy can be guaranteed. Thus, the idea that a policy is not uploaded to the cloud with ciphertext is produced by Nishide et al. 2 and Lai et al. 3 Subsequently, Li et al. 4 proposed an efficient ABE scheme with partial hidden policy. The scheme has less decryption cost, but the public parameters, ciphertext, and attribute information related to the policy are easily obtained by arbitrary malicious users. Therefore, Yin et al. 5 proposed a more efficient scheme to supplement the deficiency of the scheme proposed by Li et al. 4 in the standard model. And it was successfully reduced to the Decisional Bilinear Diffie–Hellman (DBDH) assumption.
However, most of the above schemes are based on the construction of prime order group. Cui et al. 6 proposed a construction based on the composite order group supporting the attribute value hidden, but it only achieves selective security. In the application scenario of the electronic medical system, Zhang et al. 7 not only implement policy concealment but also render less computing cost and storage overhead during the decryption process. In addition, the scheme is full secure under the standard model. However, the bilinear pairing operation and modular power operation involved in the decryption process are still associated with the number of attributes. To decrease the complicate pairing operation, Zhang et al. 8 proposed a semi-hiding ABE scheme with a constant pairing operation; however, modular power operation remains linearly related to the number of attributes. To solve communication delay in remote cloud service centers, Xiong et al. 9 introduced an attribute-based broadcast encryption scheme with partial policy hidden, user revocation, and outsourced decryption in the edge computing environment. The scheme has more practical function, but it was proved to be only selective secure.
In addition to implement partial policy hidden, the proposed scheme transfers the decryption load from user’s local device to the cloud. Therefore, the proposed scheme can easily be executed in resource-constrained devices (like mobile phones or Internet of things (IoT) devices). Because local computing nodes in an IoT environment are limited in computation and energy. For example, the merging of distributed ledger technology and IoT system is also the embodiment of outsourcing application in F Shahid et al.’s 10 scheme. Therefore, to satisfy the typical IoT requirements, the proposed scheme transfers decryption load from local terminal to the cloud.
Our contribution
In order to preserve users’ privacy, the modern ABE schemes offer a “hidden access structure.” These schemes divide the “access structure” into two parts, namely, “attribute name” and “attribute value,” such that, attribute name is publicized and attribute value remains confidential. However, many of the existing ABE schemes are either inefficient or offer just a “selective security.” In almost all of the existing schemes, the decryption cost increases linearly with “number of attributes.” This article proposes a “full secure” ABE scheme with an outsourced decryption. The proposed system model transfers the decryption load from users’ local device to the highly resourceful cloud nodes. The proposed scheme has the characteristics of partial policy hiding and flexible expression. With respect to attribute hiding, the attribute is divided into two parts: attribute name and attribute value. When encrypting the data, the attribute value is only used to compute the ciphertext and not sent to the cloud along with the ciphertext. In addition,
It has a flexible expression in access policy. The proposed scheme employs linear secret sharing scheme (LSSS) to support “AND,”“OR,” and “Threshold” structure.
It offers outsourced decryption, while at the same time, and simultaneously eliminates redundant ciphertext components. In the decryption process, the bilinear pairing operation and modular power operation are outsourced to the CSP which will execute to compute the computation instead of the users. Users only need to verify the calculation results returned by CSP and perform a constant exponential operation to recover the plaintext.
It is proven to be full secure against chosen plaintext attack (CPA). Some of the abovementioned schemes satisfy selective secure by adding the “Init” stage, that is, adversary commits the challenge object in advance; however, selective secure is weaker than full secure. The proposed scheme was proven to be full secure through dual system encryption technology. 11
It has advantages in terms of performance and function. From the comparison and experiment, it shows that our scheme is more effective in terms of function, communication cost, and computing cost than the previously established schemes.3,5,7
Related work
ABE
Sahai and Waters 12 proposed a new public key cryptosystem, ABE, which can be divided into two categories according to the location of the access policy: KP-ABE 13 and CP-ABE, 14 the policy in the KP-ABE scheme is embedded in the key and the policy in the CP-ABE scheme is contained in the ciphertext. Bethencourt et al. 14 gave the CP-ABE scheme first, but only supported the “AND” gate structure. In order to achieve better ability of policy expression, Waters 15 proposed the CP-ABE based on LSSS under the standard model. Since the policy is embedded in the ciphertext for CP-ABE, it means that the DO can set the policy to determine which attributes can access to the ciphertext, namely, making a fine-grained access control of the data. Compared to KP-ABE, CP-ABE is more widely used than KP-ABE, such as personal health care systems and fine-grained sharing in cloud storage.
Policy hidden
In order to resolve the privacy issue of user attributes in the cloud environment, Nishide et al. 2 first proposed a CP-ABE scheme that supports the hiding of the access structure. The access structure is set implicitly in the ciphertext, which is not sent along with the ciphertext. Lewko et al. 16 proposed a full secure CP-ABE scheme using the dual system encryption technology under the standard model. In Lai et al.’s 3 scheme, the attribute is divided into two parts: attribute name and attribute value. The attribute name can be publicized, while the attribute value is hidden. And Jin et al. 17 established a CP-ABE scheme supporting partial policy hiding. The ABE scheme achieves full secure, but the access structure uses the “AND” gate structure. In order to reduce the bilinear pairwise operation and modular exponentiation involved in decryption process, other specific schemes3,18–20 have been established. First, it is judged whether the attribute of users is matched with access policy before decryption first, if matched successfully, then the decryption operation is performed. But some of the proposed schemes18–20 only support “AND” gate structure, and the linear pair operation and modular exponentiation are still linearly related to the number of attributes during decryption process. Moreover, the schemes are proved to be only selective secure. Lai et al. 3 adopted more flexible LSSS structure, and the scheme is full secure under the standard model. But the bilinear pairing operations and modular exponentiations involved in the user testing phase and decryption phase increase linearly with the complexity of the policy. Yan et al. 21 introduced a multi-authority ABE of partial policy hidden with dynamic policy updating. In the above schemes, the policy hiding is only to hide the attribute value, hence it is called semi-hidden policy. Hao et al. 22 used the Bloom filter to achieve complete hidden, that is, neither the attribute name nor attribute value is disclosed. In addition to judging whether the attribute information is in the set, the Bloom filter can also remove the mapping function between the matrix and the attribute, making the attribute completely hidden. However, the formal implementation of attribute privacy protection is not provided in the security proof process. In addition, the function of attribute hidden completely can also be realized using the inner product predicate encryption technology. 23 Nevertheless, most of them only support the “AND” gate structure with weak expression ability, which limits in the actual application process.
Outsourced ABE
For the first time, Green et al. 24 proposed an outsourced ABE scheme that is secure in random oracle model. The scheme commits the decryption operation to the decryption server provider (DSP), thus the ciphertext is converted into the Elgamal type, and then delivered to users to reduce the computing cost of data user (DU). Li et al. 25 presented an offline/online ABE scheme, which reduces the computational overhead during the encryption phase using offline/online technology. Furthermore, “chameleon” hash function is introduced to implement verification before the decryption phase. The scheme is proved to satisfy the adaptive chosen ciphertext attack security, but the bilinear pairing operation involved in decryption process remains a large overhead for the user. Fan et al. 26 introduced a verifiable outsource scheme for multi-authorization in cloud-fog computing, which outsources encryption and decryption to fog nodes close to the end user. Relative to the remote CSP, fog nodes can handle data with low latency, which is ideal choice for real-time calculation of data. Zhang et al. 27 proposed an access control of full outsourcing scheme for the first time, in which the key generation, encryption, and decryption operations are all handled by the cloud, but it lacks a verification mechanism. Zhao et al. 28 proposed a verifiable full outsourcing scheme based on the original scheme. 27 The scheme supports verification and optimizes performance such that the computational cost does not increase significantly with the number of attributes or access policy complexity. For the issue of key leakage, Yan et al. 29 proposed a traceable CP-ABE scheme in a multi-domain environment.
Organization
The rest of the article is organized as follows. Some background knowledges are provided in section “Preliminaries.” The algorithm definition and security model of outsourced CP-ABE are introduced in section “System architecture and security model.” Our outsourced CP-ABE of supporting partial policy hidden is stated in section “Our construction.” The scheme’s security is analyzed in “Security proof.” The performance comparison is provided in “Performance analysis.” The article is concluded in section “Conclusion.”
Preliminaries
Composite order bilinear group
The scheme of this article is based on the design of composite order bilinear group whose order is the product of four distinct primes. Let
Bilinear:
Non-degenerate: if
Assuming that there is an group operation in
LSSS
The secret sharing scheme on the participant set
A vector can be formed by the secret share of each party over
For the secret sharing scheme
The LSSS has the characteristics of linear reconstruction. If
Complexity assumption
The security of this article is based on the following complexity assumptions, and a detailed description of the complexity assumptions is given.
Assumption 1
Given a group generation algorithm
If the advantage of adversary
Definition 1
For any probability polynomial time, if
Assumption 2
Given a group generation algorithm

If the advantage of adversary
Definition 2
For any probability polynomial time, if
Assumption 3
Given a group generation algorithm

If the advantage of adversary
Definition 3
For any probability polynomial time, if
Assumption 4
Given a group generation algorithm

If the advantage of adversary
Definition 4
For any probability polynomial time, if
System architecture and security model
System model
The system model proposed in this article is shown in Figure 1, including DO, storage service provider (SSP), DSP, DU, and attribute authority (AA).

System model of outsourced ABE.
The DO specifies an access policy and performs an encryption algorithm on the data using the public parameter (
The DU can access the ciphertext file in the cloud server and download the ciphertext from the SSP. Due to the terminal device of limited resources, the module exponent and the bilinear pairing operation involved in the decryption process are performed by the DSP that uses the transformed key (
Algorithm definition
This article assumes that collusion does not occur between servers. AA is a key distribution center and is completely trusted. The algorithm contained in the scheme consists of the following six algorithms.
Security model
We define the security model of this article through the security game between simulator
Our construction
The verifiable outsourced ABE scheme proposed that supports policy hiding in the cloud environment is based on the scheme of Zhang et al., 7 which can realize the attribute hiding in the policy and support the outsourced decryption procession. The scheme is composed of the following seven algorithms, and the detailed description of each algorithm is as follows:
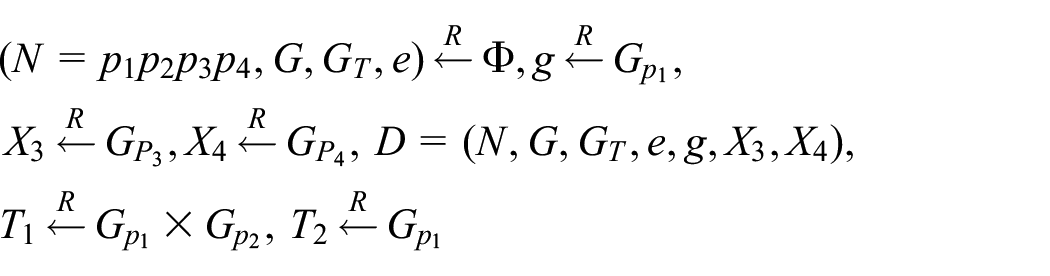
1. Initialization: AA performs group generation algorithm
2. Setup (
The user attribute set is defined as
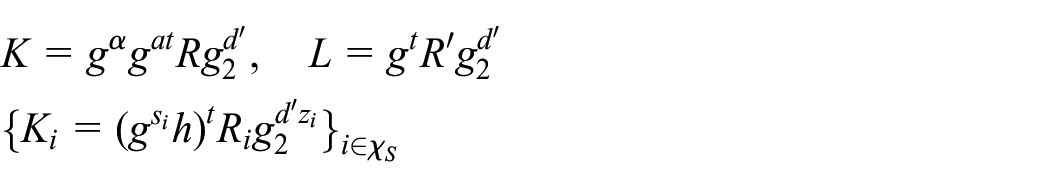
3. KeyGen
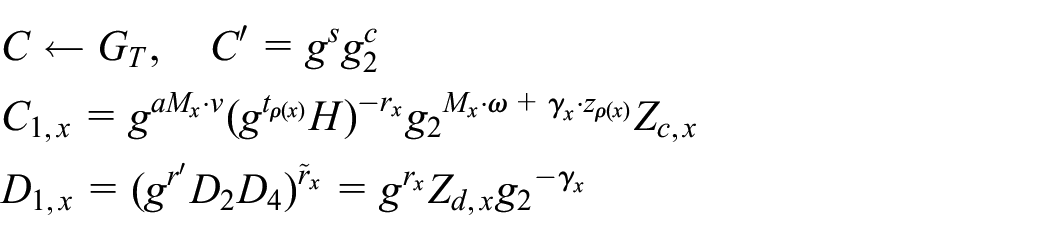
4. Encrypt (
The algorithm selects
5.
generated by running the KeyGen algorithm then selects
6.

Finally, gain partial ciphertext
7.
Security proof
Theorem 1
If the Assumptions 1–4 hold, then the proposed scheme based on the defined security model is proved to be full secure and satisfy CPA security.
The security proof of the scheme is similar to the literature, 3 that is, the dual system encryption technology is used to prove its security. First, define two semi-functional structures: semi-functional ciphertext and semi-functional key. The normal secret key can decrypt normal ciphertext and semi-functional ciphertext, but the semi-functional secret key cannot decrypt semi-functional ciphertext. And semi-functional key and semi-functional ciphertext are only used in security proof and do not appear in actual systems.
Semi-functional ciphertext: We set the

Semi-functional key: we set
Semi-functional key of type 1

Semi-functional key of type 2

Semi-functional key of type 3

The proof of this article’s security is based on the Assumptions 1–4 and is demonstrated through a series of games, now we define the following games:
The number of key query between the simulator and adversary is set to
We can prove that these games are indistinguishable based on Lemmas 1–6. If the Assumptions 1–4 hold, it can be proved that
Lemma 1
Suppose the algorithm
Proof
If there exists an advantage of adversary
1.
2.
3.

4.

where

Hence, this challenge ciphertext is semi-functional and
Lemma 2
Suppose the algorithm
Proof
If there exists an advantage of adversary
1. For

Note that it is semi-functional of type 3, because the value of
2. For
3.
(a) If
where

Note that the value of
(b) If
1.
2.
3.

4.

where

We know this challenge ciphertext is semi-functional and the value of
Lemma 3
Suppose the algorithm
Proof
If there exists an advantage of adversary
Similarly, to answer the
Lemma 4
Suppose the algorithm
Proof
If there exists an advantage of adversary
(a) If

where

Note that the value of
(b) If
Lemma 5
Suppose the algorithm
Proof
If there exists an advantage of adversary

where
1.
2.
3.

4.

where

Note that the value of
Lemma 6
Suppose the algorithm
Proof
If there exists an advantage of adversary

We observed
1.
2.
3.

4.
where

Performance analysis
The scheme of this article is compared with that of Lai et al.,
3
Yin et al.,
5
and Zhang et al.
7
from the perspectives of function and performance. In the scheme comparison process,
Theoretical analysis
Table 1 mainly compares the functionalities of the schemes. It can be seen that the schemes all implement the policy-hiding function, and they are all proven to be full secure apart from the scheme proposed by Yin et al. 5 is selective secure under the standard model and this scheme 5 does not support outsourced decryption operations. However, the schemes of Lai et al. 3 and Zhang et al. 7 are constructed based on the composite order group, which realizes the full security of the scheme, but does not support outsourcing decryption as well. The proposed scheme is based on the composite order group, and it not only realizes policy hidden but also supports outsourced decryption operations, which reduces the user’s computational cost. In addition, it is proved to satisfy full secure under the standard model.
Comparison of performance.

Table 2 mainly shows the comparison of the public key size (
Comparison of communication overhead.

Table 3 shows the computational overhead. In the encryption process, the exponent operation involved in this scheme is
Comparison of computing overhead.

DO: data owner; DU: data user.
The proposed scheme makes a trade-off between ciphertext size and cost of decryption. More precisely, the scheme accepts unnecessary exercises of decryption process in order to reduce the ciphertext size. However, because decryption is performed by sufficiently powerful cloud nodes; therefore, additional decryption exercises are acceptable. From the analysis above, our scheme not only has the characteristic of outsourcing decryption and policy hidden but also has certain performance advantages.
Experiment analysis
Through the above theoretical analysis, our scheme has more advantages in terms of function and efficiency. In order to more accurately evaluate the actual performance of the scheme, we further analysis computing overhead through experiments, including the encryption time and the decryption time.
Experimental environment: Windows 10, Inter® CoreTM i5-8300H (2.30 GHz), memory 8 GB, the experimental code is based on java pairing-based cryptography library (JPBC-2.0.0), and MyEclipse development environment. In the experiment, the paired structure of type A is used to construct an elliptic curve
Experimental setup: In the ciphertext-policy ABE scheme, the number of attributes in the access policy affects the encryption and decryption time. In the experiment process, because the high computational overhead is outsourced to the cloud server for calculation, we only test the computing time of the terminal device. In the experiment, we set the number of attributes as 50 and increase by 10 the number of attributes each time, generating five different access policies. By comparing the computing time of the terminal user under different access policies, we tested 10 times for each policy and took an average value as the experimental result.
Figure 2 has two subgraphs (Figure 2(a) and (b)), which represents the execution time of the DO’s encryption and the execution time of the DU’s decryption. In Figure 2(a), we can see that the execution time of the proposed scheme is lower than the computational time of other schemes of Lai et al. 3 and Yin et al., 5 but slightly higher than the calculation time of the scheme proposed by Yin et al. 5 In Figure 2(b), during the procedure of user’s decryption, the schemes of Lai et al., 3 Yin et al., 5 and Zhang et al. 7 do not support the outsourced decryption operation. And they involve the computational cost of the bilinear pair operation and the computational cost increasing linearly with the number of attributes. This scheme achieves outsourcing decryption operations and verification operations, so the user only needs to perform constant exponential operation, which greatly reduces the user’s computational overhead.
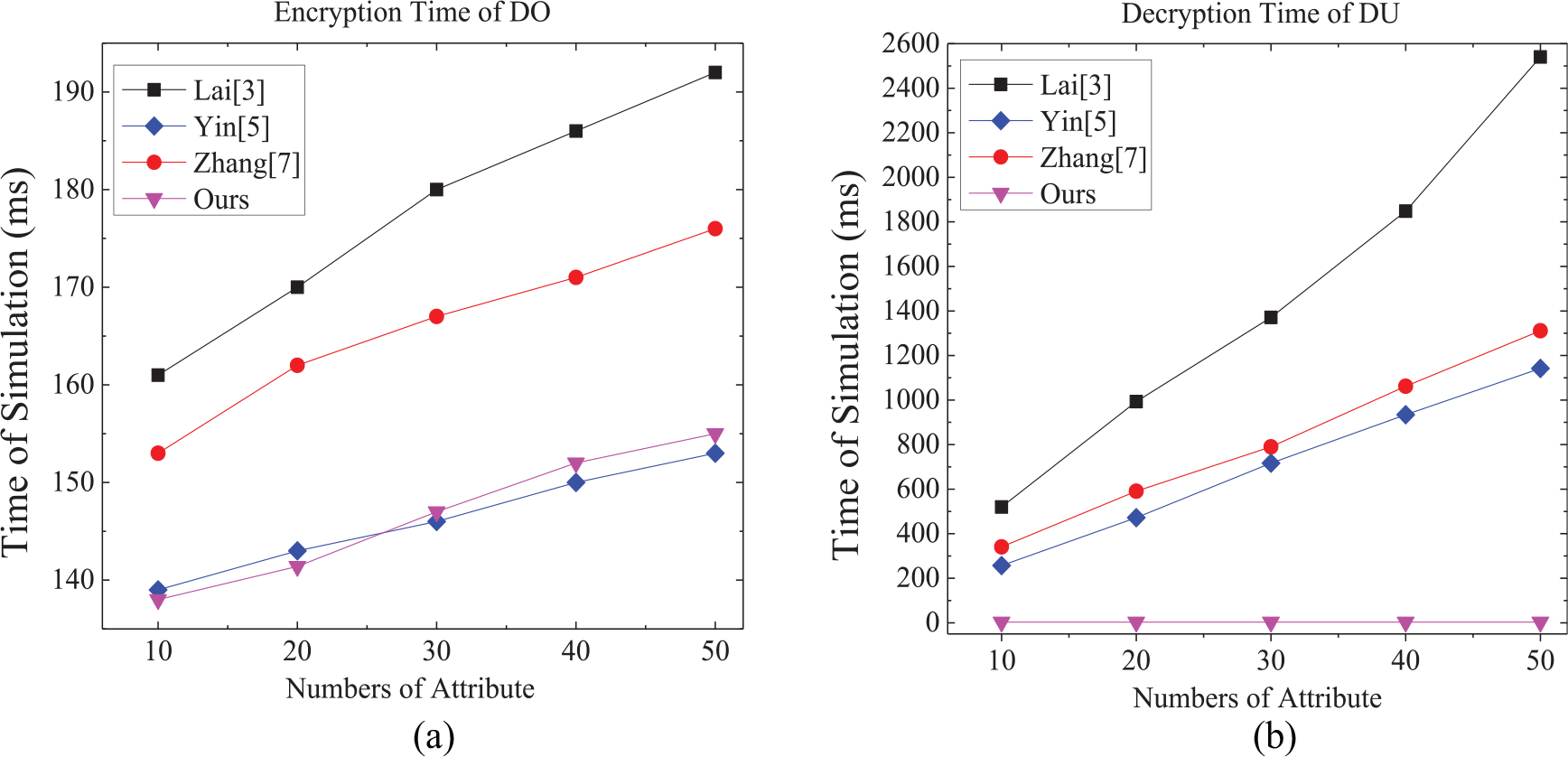
Comparison of computing time: (a) encryption time of DO and (b) decryption time of DU.
By comprehensive analysis, the proposed scheme is superior to other schemes in terms of function, communication, and computational burden, so it is effective and feasible in the application of cloud computing.
Conclusion
In order to solve the problem of privacy protection and heavy computing overhead in the cloud outsourcing environment, this article proposes a partial policy-hiding ABE scheme that can verify the result of outsourcing decryption. The privacy of user attributes is realized by dividing attributes into two parts: attribute name and attribute value, attribute name disclosure and attribute value concealment. For the bilinear pairing operation and module power operation, this article will decrypt the operation by outsourcing to the cloud server and verify the outsourced calculation results to ensure the accuracy of the returned calculation results. It is proved that the scheme based on the static assumption problem can achieve full secure under the standard model. Finally, through theoretical and experiment analysis, it shows that our scheme has more advantages than other schemes.
Footnotes
Handling Editor: Iftikhar Ahmad
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was funded by the National Natural Science Foundation of China (Grant No. 61802117), in part by the Research Foundation of Young Core Instructor in Henan province (Grant No. 2018GGJS058), and in part by the Innovative Scientists and Technicians team of Henan Provincial High Education (Grant No. 20IRTSTHN013).
