Abstract
Device-to-device communication is considered as one of the hopeful technologies for proximal communication, which plays a vital role in the wireless systems and 5G cellular networks. The outsourced attribute-based encryption scheme is convinced to be very suitable for secure device-to-device communication since it allows not only fine-grained sharing of encrypted data but also achieves high efficiency in the decryption of general attribute-based encryption schemes. However, almost all existing outsourced attribute-based encryption schemes can hardly be applied directly in the device-to-device communication because many heavy computation operations, such as pairing and modular exponentiations, cannot be taken on the mobile devices in the device-to-device network. In this article, we propose a concept of outsourcing threshold decryption for attribute-based encryption and design a new efficient outsourcing threshold decryption scheme for ciphertext-policy attribute-based encryption. In our definition of outsourcing threshold decryption, the decryption, which is a computationally expensive operation, is outsourced to multiple semi-trusted and lightweight computing devices determined by an access structure and can be jointly taken by these devices. Our scheme supports proxy re-encryption which enables the decryption delegation. Finally, security and efficiency analyses of our proposed method indicate that our proposal guarantees strong security against chosen plaintext attacks and requires less outsourced computation and communication cost than the existing outsourced attribute-based encryption schemes.
Keywords
Introduction
As one of the next-generation wireless communication systems, Long Term Evolution-Advanced (LTE-A) supports mobile content forwarding, 1 and the device-to-device (D2D) technology is proposed as an indispensable component of 5G cellular networks to meet the growing demand for downloading required contents from the local area network.2–4 D2D communication is the underlay of the cellular network to enhance spectrum efficiency and enable a lot of devices to link directly, which helps discover geographically dense devices and allows direct communication among these neighboring devices at low power through reuse of spectrum resources. In general, the D2D technology enables two adjacent users to connect directly in the physical layer. Devices gain energy from reproducible energy sources in the energy layer, and users build social networks representing solid relationships and social structures in the social layer. Thus, it is highly essential for LTE-A to exploit the D2D technology, since it can reduce power consumption, effectually offload traffic and increase spectral efficiency,3,5 on account of the potential reuse gain and physical proximity. In recent years, the D2D technologies have been studied by more and more scholars, and the scope of application is becoming more and more extensive, such as the healthcare system6,7 and fog computing. 8 Many performance problems in the healthcare systems have been studied in the study by.9,10
However, for mobile applications in the D2D communication where users employ devices with11,12 limited computing power, and short battery lifetime, 11 almost all existing public key encryption schemes cannot be applied directly due to the heavy computations required by the attribute-based encryption (ABE) schemes, such as pairing computations and modular exponentiations. An ABE scheme ensures confidentiality of sharing data for cloud services,13,14 which is not necessary for the data owner to store the public key(s) of data receiver(s). For example, data is encrypted with given attributes and access policies, so that it can only be decrypted and shown by the receiver whose decryption key satisfies the specific attributes and access policies. Almost all existing ABE schemes involve pairing computations or modular exponentiations, and their computational complexity increases linearly with the amount of attributes, respectively, access policy size. It means that the ABE scheme is representatively computationally intensive, which is acceptable for common desktop computers but not for restricted computational resources portable devices. To solve this problem, Green et al. 15 proposed the outsourcing ABE scheme first, which introduced a semi-trusted server to reduce the ciphertext decryption computational complexity on portable devices. After that, more and more outsourcing decryption of ABE schemes were introduced.16–18 However, the outsourcing decryption of ABE schemes still cannot be directly applied to the D2D network, since these ABE schemes are based on the assumption that a server has enough computation power to deal with the heavy computations, such as pairing and modular exponentiations, and thus it is usually designed for outsourcing to a cloud server. For the D2D mobile network, as shown in Figure 1, in relay-coverage or out-of-coverage situation, the devices may not be able to build connections to cloud server. 19 The users may prefer to outsource their computation tasks to other D2D mobile devices with which the connections are built by some social ties, as they do not want to upload or download much data to or from the Internet. Therefore, we have to consider how to make the ABE scheme adapted to this situation in the D2D mobile network. In the case of the lower right corner of Figure 1, the user can complete the decryption through other D2D devices to reduce the data communication of the mobile phone.

D2D communication application scenarios.
Our contributions
In this article, we give the concept of outsourcing threshold decryption (OTD) for ABE and its security model and propose a new efficient OTD scheme for ciphertext-policy ABE. In our definition, an access structure in a linear secret-sharing scheme (LSSS) is used as a threshold for outsourcing decryption. It allows the devices to outsource the computationally expensive decryption to multiple devices, the decryption keys of which satisfy the access structure, and the numerous devices jointly take the computational task of decryption, which relieves the problem of devices’ restriction and satisfies the outsourcing requirements in the D2D mobile network where devices are semi-trusted, and their computational capability is limited. Our proposed scheme supports proxy re-encryption, which enables the decryption rights delegation, and it is useful for a mobile user to relieve encryption computation pressure. The formal security and efficiency analyses for our ABE scheme in the D2D mobile network are also present, indicating that our proposal achieves the strong security against chosen plaintext attacks (CPAs) and requires less outsourced computation and communication cost than the existing outsourced attribute-based encryption (OABE) schemes.
Organization of the article
The rest of the article is organized as follows. Section “Related work” briefly describes some related works. Some preliminaries are introduced in section “Preliminaries.” The definition and security model are given in section “Definition and security model for OTD of CP-ABE.” Our scheme construction is described in section “OTD of CP-ABE scheme.” The formal security and efficiency analyses of our scheme are present in section “Security and efficiency analysis.” Finally, the conclusion is drawn in section “Conclusion.”
Related work
In 2005, Sahai and Waters 13 proposed the concept of fuzzy identity-based encryption (IBE). In their scheme, they use attribute sets to replace identities for IBE schemes. It is the first ABE scheme. ABE can provide fine-grained access control in the cloud environment. 20 Then, more and more efficient and flexible ABE constructions have been proposed. Goyal et al. 20 classified ABE schemes into two variants, ciphertext-policy attribute-based encyption (CP-ABE) and key-policy attribute-based encryption (KP-ABE). In CP-ABE, the ciphertext will specify an access policy and each user’s private key is related to a set of attributes. On the contrary, in a KP-ABE scheme, each user’s key is related to an access structure, and ciphertext is related to attribute sets. The difference between KP-ABE and CP-ABE is that which component decides the access policy for the ABE scheme. Goyal et al. 20 proposed the first KP-ABE scheme, which supports the monotonic access structures. Furthermore, Ostrovsky et al. 21 proposed an improved KP-ABE construction, which realizes non-monotone structures’ expression. In other words, their scheme supports more flexible access policies. In general, for the KP-ABE scheme, the access policy is determined when the system generates the user’s decryption key, which makes the encryption algorithm more difficult for a data owner. The encrypter needs to compare receivers’ access policies to those of all other users to select an appropriate attribute set for the ciphertext. Then, the first CP-ABE scheme is proposed by Bethencourt et al., 22 which is more flexible than KP-ABE. But their scheme has an obvious drawback that it is proved to be secure only under the generic group model. This drawback is overcome by another CP-ABE scheme proposed by Cheung and Newport, 23 whose security is proved under the standard model. Furthermore, based on the number theoretic assumption, Goyal et al. 24 also proposed another CP-ABE scheme for more advanced access structures.
To outsource a large proportion of decryption computation, a new paradigm of outsourcing decryption was proposed by Green et al.
15
Similar to the idea of proxy re-encryption,25,26 it allows a proxy to convert an encryption message
Threshold decryption is particularly useful when the centralization of the power to decrypt is a concern, as pointed by Baek and Zheng.
33
An identity-based threshold decryption scheme, which allowed a set of users with valid decryption shares to decrypt the corresponding ciphertext, was constructed by Baek and Zheng.
33
For the ABE, the threshold decryption scheme was proposed by Herranz et al.,
34
where users are authorized to decrypt their data as they hold at least
Preliminaries
Bilinear groups
Let
Bilinearity: for all
Non-degeneracy:
Computable: for all
The Decisional Bilinear Diffie–Hellman (DBDH) assumption based on the studies by Sahai and Waters 13 and Boneh and Boyen 35 is defined as follows.
DBDH assumption
The decisional BDH assumption is that no probabilistic polynomial time algorithm
LSSS
A secret-sharing scheme
The shares of the parties form a vector over
There exists a matrix
It is shown in the study by Beimel 36 that every LSSS according to the aforementioned definition enjoys the linear reconstruction property, defined as follows.
Suppose that
Access structures can also be described in terms of monotonic boolean formulas. Using standard techniques, one can convert any monotonic Boolean formula into an LSSS representation. We can represent the Boolean formula as an access tree. An access tree of
Definition and security model for OTD of CP-ABE
The symbols used in the following definitions are listed in Table 1. An OTD of the CP-ABE scheme generally consists of the following eight algorithms:
We now define the security model for OTD of ciphertext-policy ABE on the basis of the studies by Green et al.
15
and Goyal et al.,
20
which can achieve the security against CPA. It allows an adversary to query for any private keys
Symbols and description.
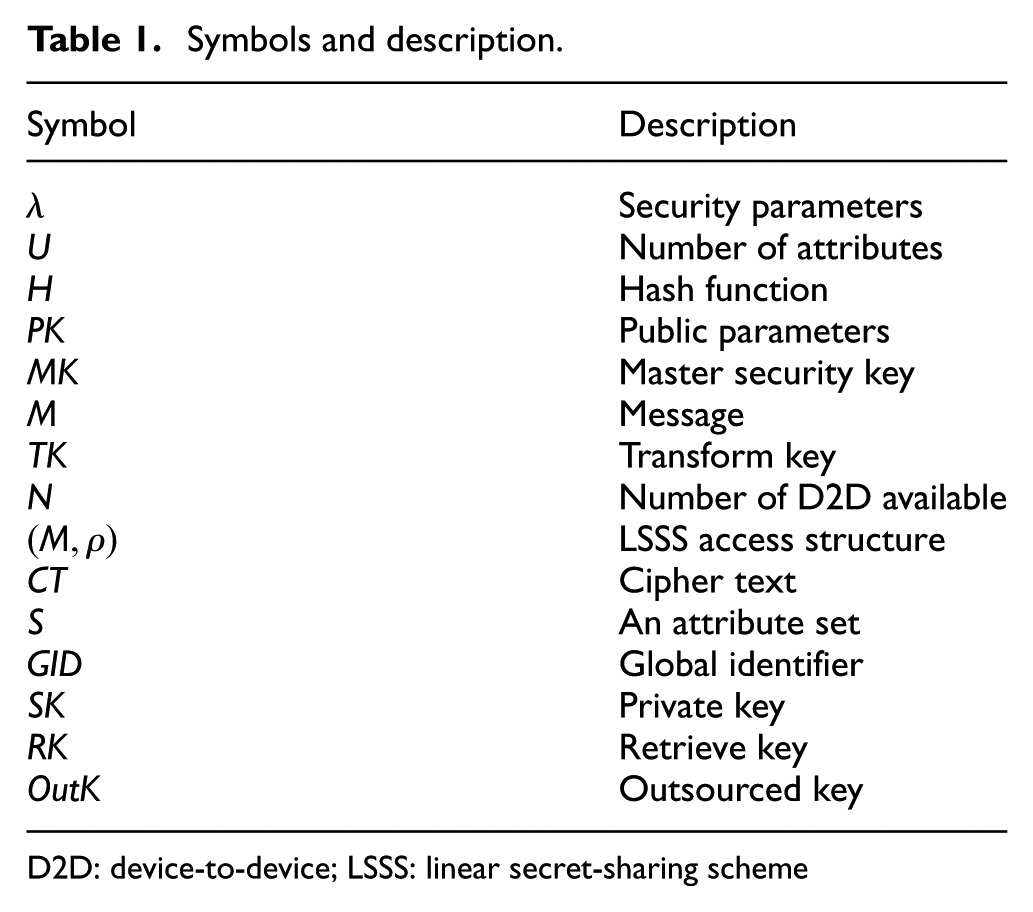
D2D: device-to-device; LSSS: linear secret-sharing scheme
Define adversary

Definition
An ABE scheme is indistinguishability under chosen plaintext attack (IND-CPA) secure if for any polynomial time adversary
OTD of the CP-ABE scheme
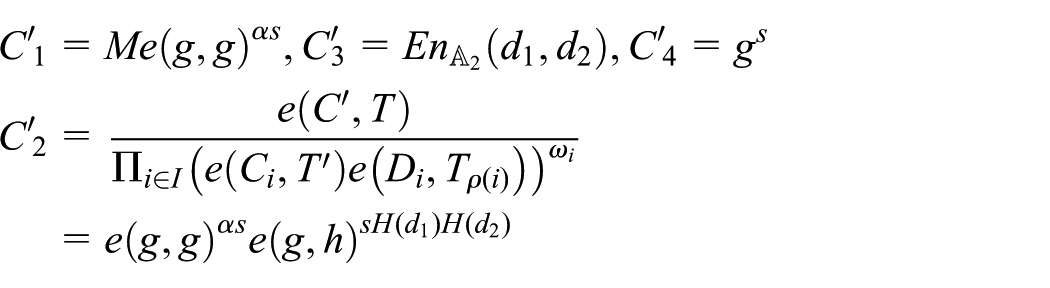
In this section, we first describe our proposed CP-ABE scheme, and the framework is shown in Figure 2. Then the correctness analysis is given.

Framework of outsourcing threshold decryption of the CP-ABE scheme.
The construction


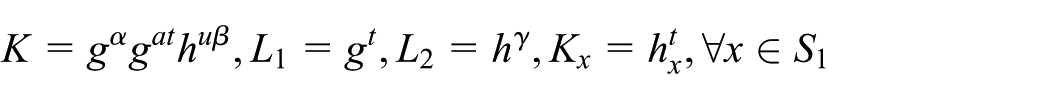
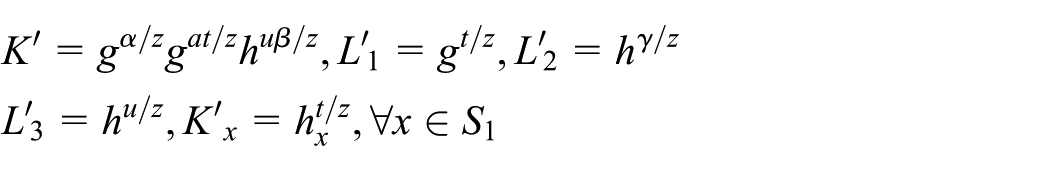
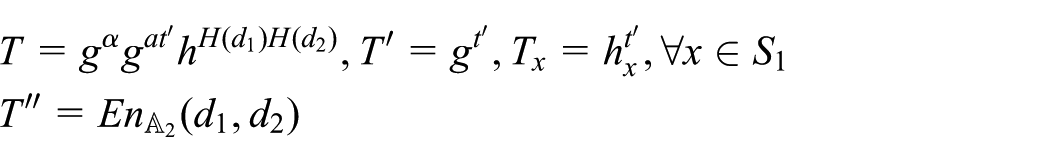

Then, the message
To decrypt the


Then, each device computes

Then, the recipient can get message
The pseudocode of the algorithm is shown in Algorithms 1–3.


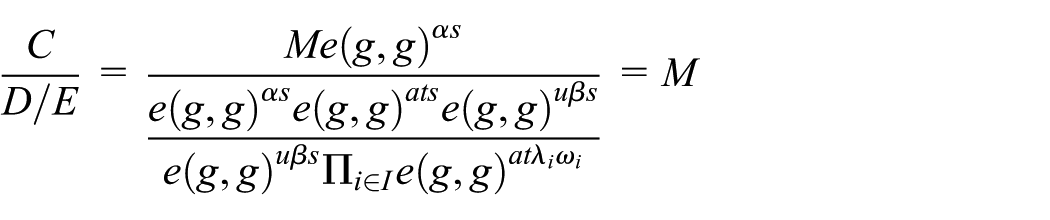
Correctness
We present the correctness analysis for the aforementioned scheme. Since

we have
Security and efficiency analysis
In this section, we prove that our proposed CP-ABE method has strong security against the CPA. It allows an adversary to query for any private keys
Theorem
If there is an adversary
Proof
Suppose there exists a probabilistic polynomial time adversary
For The simulator For The simulator
When
If the adversary
The security comparison is shown in Table 2. Our proposed scheme can guarantee the selective CPA security. Compared with other schemes, the security of our scheme is enough to satisfy the requirements in the D2D mobile network.
The security comparison of outsourced CP-ABE schemes.

CP-ABE: ciphertext-policy attribute-based encyption; RCCA: replayable chosen ciphertext attack; CPA: chosen plaintext attacks.
Now, we make an efficiency analysis for our outsourcing to multiple devices decryption of the CP-ABE scheme in terms of the performance with other three outsourced ABE schemes.15,17,18
We implement our scheme using the libfenc library. 37 All dominant group operations use the PBC library, 38 which is written natively in C. A 201-bit MNT elliptic curve(Miyaji, Nakabayashi and Takano introduced the first method to construct families of prime-order elliptic curves with small embedding degrees, namely (k = 3, 4), and 6. These curves is so-called MNT curves.) and the corresponding asymmetric elliptic curve (EC) group are chosen from the Stanford Pairing-Based Crypto library.38,39 Our code implementations are executed on two dedicated hardware platforms: an Intel i5-4590 CPU (3.30 GHz quad-core processor) with 3380 MB of RAM, running 64-bit Ubuntu Server 16.04, and a Huawei Nexus 6P with Qualcomm Octa-core (4 × 1.55 GHz Cortex-A53 and 4 × 2.0 GHz Cortex-A57) and 3 GB of RAM running Android 6.0.
The functionality comparison of outsourced CP-ABE schemes.

CP-ABE: ciphertext-policy attribute-based encyption.
The efficiency comparison of outsourced CP-ABE schemes.

CP-ABE: ciphertext-policy attribute-based encyption.

The comparison of Out.Comp.Cost.

The comparison of recipient computation cost. The vertical coordinate represents time cost of bilinear pairing operations and modular exponentiation operations for recipients.
The ciphertext size comparison of outsourced CP-ABE schemes.

CP-ABE: ciphertext-policy attribute-based encyption.
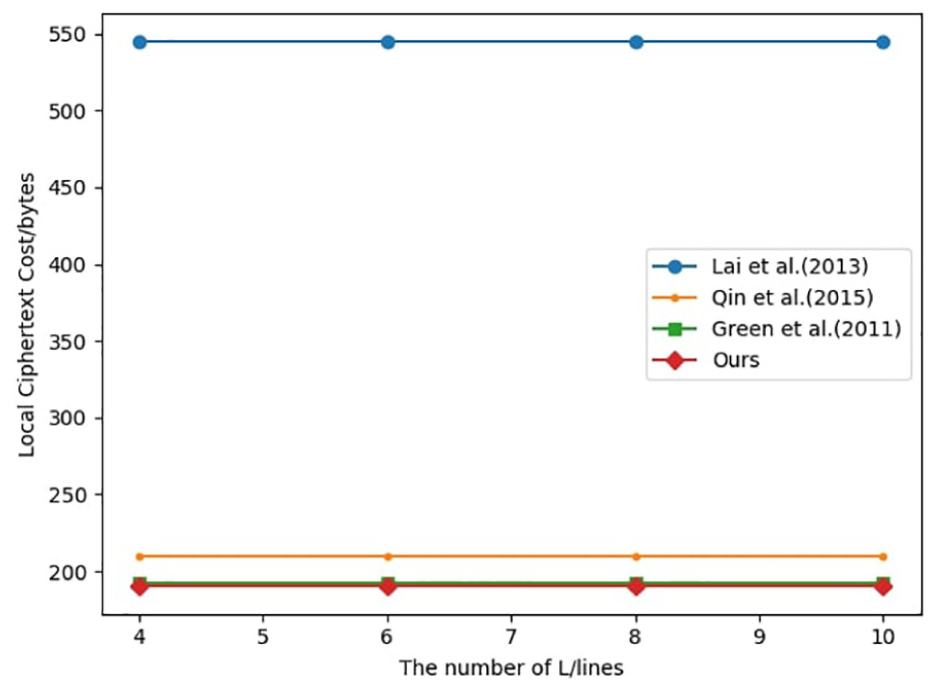
The comparison of Local.Ciphertext.Cost.
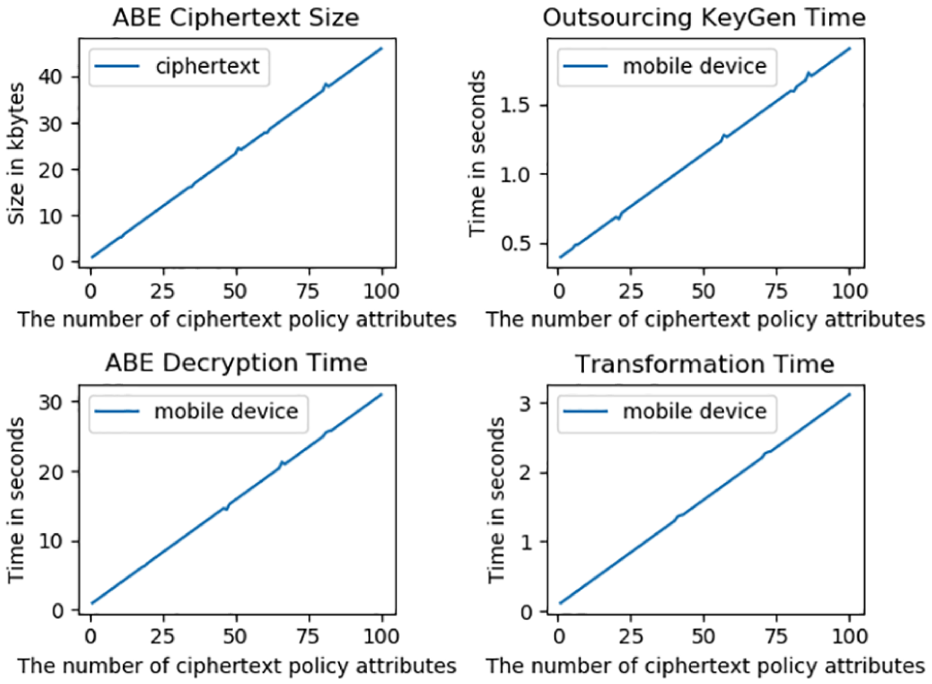
Performance of our scheme in the D2D network.
Conclusion
In this article, we propose an OTD for a ciphertext policy ABE scheme to relieve the problem of device restriction and particular outsourcing requirements in the D2D settings. This scheme can outsource the expensive decryption computation to multiple devices in the D2D mobile network. The security and efficiency analyses show that our proposal is more secure and efficient compared with other existing research works. Following are the limitations of our proposed scheme. First, some additional information for decryption occupies some storage space, which will burden mobile devices with a low storage ability. Second, the total power consumption of all involved mobile devices is increased. Our future research will focus on computation efficiency improvement and power consumption reduction.
Footnotes
Handling Editor: Pascal Lorenz
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
