Abstract
With the development of cloud computing, more and more video services are moving to the cloud. How to realize fine-grained access control of those data on cloud becomes an urgent problem. Attribute-based encryption provides a solution. However, heavy computation is still a bottleneck restricting the wider application of attribute-based encryption in cloud computing. In addition, we find that expression of the access control structure on media cloud can be further improved. To solve these problems, we propose an enhanced media ciphertext-policy attribute-based encryption algorithm and introduce its two key components, the multiple access tree and the key chain. To increase the scalability of the proposed algorithm, we discussed the issues of multi-authorization, user revocation, and 1 −
Keywords
Introduction
Media cloud provides video storage, processing, and distribution services to users. How to realize fine-grained access control of massive amounts of videos is a huge challenge for the media cloud. 1 Ciphertext-policy attribute-based encryption (CP-ABE) is an important technology to tackle this challenge in application scenarios such as personal health records (PHR)2,3 and smart girds.4,5
In CP-ABE, conversion from the access control policy to the access structure is an important step. However, when CP-ABE is applied in media cloud, the traditional conversion methods become inefficient. On media cloud, one video file is often available with different resolutions. The fact is that users with access to high-resolution videos are always allowed to access low-resolution versions. For example, paying users can watch a movie in all three versions: the standard definition (SD) version, the high definition (HD) version, the ultra-high definition (UHD) version; registered users can watch the movie in HD or SD versions, and guests can only watch the movie in the SD version. The corresponding access control policies (Table 1) have the following inclusion relation:
Access control policies in media cloud.

SD: standard definition; HD: high definition; UHD: ultra-high definition.
In this article, we assume that the access tree is the default method to finish conversion from policy to access structure. When using the CP-ABE scheme proposed by Hong et al., 6 the three aforementioned policies have to be converted into three corresponding access trees. Wu et al. 7 presented a multi-message CP-ABE (MCP-ABE) scheme in which a single access tree could be used to describe all policies. Compared with CP-ABE, MCP-ABE needs to maintain fewer and simpler access structures. Ma et al. 8 optimized the access tree in their CP-ABE algorithm called scalable ciphertext-policy attribute-based encryption (SCP-ABE), and expanded the access control rules from one dimension to three dimensions, thereby reducing the time required for encryption and decryption. However, access trees in both MCP-ABE and SCP-ABE are efficient only when representing the access control rules with full inclusion relations. When there exists any common attribute, the efficiency of access trees reduces, because the common attributes have to be described repeatedly on different levels of the tree.
To solve this problem, we propose a new access tree called multiple access tree (MAT) and a new one-way key chain scheme. On the basis of these two components, we introduce a novel enhanced-media Ciphertext-policy attribute-based encryption (eM-CP-ABE) algorithm. Then, eM-CP-ABE is applied to media cloud for fine-grained access control. Two steps are required: first, the video is divided into segments according to resolution or time and encrypted by the advanced encryption standard (AES). Note that different segments correspond to different keys. Second, these symmetric keys are encrypted by eM-CP-ABE to achieve fine-grained access control. The contribution of our proposed algorithm is reflected in the following four aspects:
In the encryption process, eM-CP-ABE consumes less time and space than MCP-ABE; in the decryption process, when an authorized user switch from a high-level resource to a low-level resource, only two hash operations need to be performed without any new decryption operations. Compared with SCP-ABE, eM-CP-ABE has better performance both in encryption and decryption processes.
Using one
eM-CP-ABE has strong scalability. We have proved that both multi-authorization and user revocation are feasible when the eM-CP-ABE algorithm is used.
We have also proved security of the eM-CP-ABE algorithm. It can successfully resist chosen-plaintext attacks (CPAs) under the decisional bilinear Diffie–Hellman (DBDH) assumption.
The rest of the article is organized as follows: section “Related work” provides an overview of the related work. Section “Preliminary” presents necessary preliminary knowledge. Section “Proposed algorithm” introduces eM-CP-ABE and its extensions. Section “Security analysis” analyzes eM-CP-ABE in terms of security. Section “Performance analysis” analyzes the operation overheads of the proposed algorithm. Finally, section “Conclusion” presents the conclusion.
Related work
CP-ABE was first proposed in 2007. 9 In CP-ABE, user keys are associated with sets of attributes, whereas ciphertexts are associated with policies. CP-ABE is widely used in fine-grained access control of data outsourced on the cloud. However, the problem is that CP-ABE entails heavy computation and complex conversion from access policy to access structure.
Heavy computation will degrade real-time performance and increase the workload of computation. To optimize real-time performance, Li et al. 10 introduced online/offline ABE. A similar online/offline scheme was proposed by Cui et al. 11 The online/offline transfer technology allows the computation tasks to be outsourced to public cloud servers. However, the online/offline transfer technology can just transfer the workload of computation, but cannot reduce it. Expanding the single authorization center to multi-authorization centers can improve the efficiency of key generation. Han et al. 12 introduced a decentralized CP-ABE scheme, in which each authority can work on one unique attribute subset independently. The robust and auditable access control (RAAC) scheme was proposed in 2017. In RAAC, any authority can manage the whole attribute set individually and an auditing mechanism is introduced to coordinate all authorities’ work. 13 Multi-authorization greatly improves the performance of key generation, but does not reduce the workload of encryption and decryption in CP-ABE. Xue et al. 14 proposed an attribute-based controlled collaborative access control scheme, in which multiple users having different attribute sets could collaborate to gain access permission. The scheme is efficient in terms of storage and computation overhead, but user collusion is forbidden in most scenarios of the media cloud.
However, addition of many practical factors makes the access structure more expressive. The factor of time was introduced to realize time-release encryption.6,15 In some existing studies,16–19 user revocation was supported in their CP-ABE schemes. In studies by Ning et al.,20,21 illegitimate access could be traced. However, the problem of complex conversion from access policy to access structure remains unsolved. Traditional access trees are inefficient when the corresponding access control policies have the inclusion relationships such as file system. In hierarchical file systems, if a user can decrypt a file corresponding to a level node in the access structure tree, he or she can decrypt all these files corresponding to the lower level nodes. To avoid repetitive description of attributes on different levels, Wang et al. 22 used an integrated access structure to encrypt multiple files on different levels separately. As only one file can be encrypted on each level, the scheme proposed by Yeh et al. 2 is not practical. Li et al. 23 proposed an extended file hierarchy CP-ABE scheme (EFH-CP-ABE), which could encrypt several files on the same access level. To simplify the complex structure of inclusion relation among these privilege levels, Bobba et al. 24 introduced a ciphertext-policy attribute-set-based encryption (CP-ASBE) scheme in which the set of user attributes was extended into a recursive set structure. CP-ASBE was used in the conditional access system to resist collusion attacks. 25 Based on CP-ASBE, Wan et al. 26 proposed a hierarchical attribute-set-based encryption (HASBE) algorithm. HASBE builds a hierarchical system model and realizes the key delegation scheme and user revocation scheme. Teng et al. 27 improved the HASBE algorithm by keeping the length of the ciphertext and the number of bilinearity operation fixed. However, if strict mutual exclusion cannot be satisfied between different privilege levels, the common attributes will still be described repeatedly.
The same problem is faced in media cloud. CP-ABE is widely used to ensure the security of outsourced videos and support flexible video services.7,8,28 Yang et al. 28 used traditional access trees that could not improve the efficiency. Access trees both in MCP-ABE 7 and SCP-ABE 8 can represent the access control rules with full inclusion relation efficiently. However, when there is any common attribute, these trees become less efficient because the common attributes have to be described repeatedly on different levels of the tree.
In this article, we propose a new access tree called MAT and a new one-way key chain scheme. On the basis of these two components, we introduce a novel encryption algorithm called eM-CP-ABE. In the encryption process, one
Preliminary
To ensure the independence of the article, the relevant information is given in this section.
Bilinear maps
Let
Access structure
Let
In CP-ABE, a set of attributes is used as the decryption key, and an access structure is used to encrypt the plaintext. We describe the access structure in terms of an access tree. If and only if a set of attributes satisfies the access tree, the ciphertext can be decrypted correctly.
Access tree
Let
DBDH assumption
Let

where the probability is taken over the random choice of the generator
Proposed algorithm
In this section, eM-CP-ABE is described in detail. First, two important components that construct the proposed algorithm is introduced. Then, the model and implementation of eM-CP-ABE are proposed. Last, multi-authorization, user revocation, and
Components
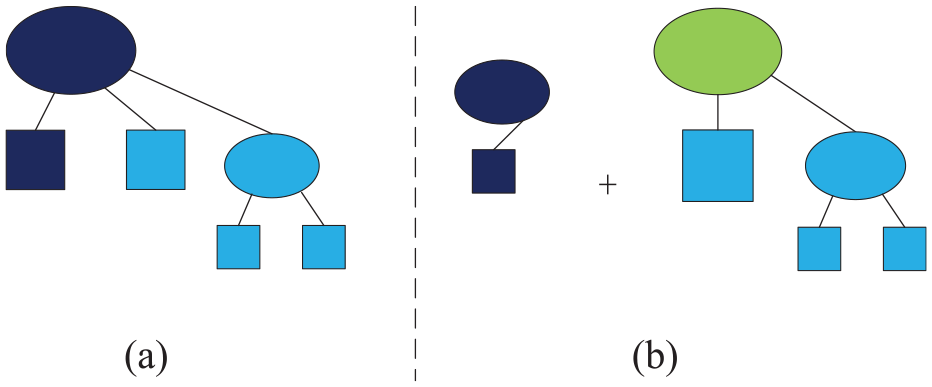
MAT
MAT is introduced to improve the expression efficiency of access control tree in eM-CP-ABE. In our article, MAT’s nodes are divided into three types: virtual nodes, attribute nodes, and ordinary nodes. A virtual node
We also make the following assumptions:
The parent of a virtual node cannot be a virtual node.
The virtual node has one and only one child
We define a MAT with

Satisfying an access tree
To clearly describe the process, MATs
Key chain
Without loss of generality, we assume there is a

The goal we need to achieve is that if the user can access the content of level
Input data of arbitrary lengths and output data of fixed lengths. For a given input, it is easy to calculate the output. For a given output, it is not computationally feasible to find a correct input.
Step 3. The final key chain
When a set of attributes satisfies both the base tree constructed by the common attributes (
Using MAT and key chain
In this part, we show how to use MAT and the key chain to convert complex policies into access trees. According to Table 1, we add the time factor to construct more complex access rules (Table 2). In this scenario, the common attributes (id, category, and duration) of the three rules must be described in each branch of CP-ABE or MCP-ABE, which considerably reduces the expression efficiency of the access control structure.
Three access control rules for the video with ID=10010.

The rules that conform to the ABAC format 29 are described in Table 2.
We assume that two bits are used to describe the user’s type (Paying: uType=11, Registered: uType=10, and Guest: uType=01). In CP-ABE, three rules will be converted into three access trees (Figure 3). We use the integer comparison technology
9
to describe the expiration time “duration <30.”

Access trees corresponding to the three rules in CP-ABE. The access tree of (a)
In MCP-ABE, the three rules will be converted into one complex access tree (Figure 4). In MCP-ABE, a special access tree is consisted of one “trunk” and some “branches.” As shown in Figure 4, the trunk represents the inclusion relationship between the three rules,

Access tree corresponding to the three rules in MCP-ABE.
We use MAT and key chain to simplify the access tree. As shown in Figure 5, subtrees of the common attributes are extracted to form the base tree, which is then merged with the hierarchical tree through an ordinary node. The access tree described in Figure 5 has one virtual node, so we call it

Access tree corresponding to the three rules in eM-CP-ABE.
Compared with CP-ABE and MCP-ABE, the eM-CP-ABE algorithm realizes expression of the three rules with a simpler tree structure and fewer nodes.
eM-CP-ABE
eM-CP-ABE model
Figure 6 shows the model of eM-CP-ABE. The system consists of five participants. They are media cloud, video provider, video consumer, attribute authority center, and trusted encryption center.

eM-CP-ABE system model.
The proposed eM-CP-ABE has five functions: Setup, Encrypt, KeyGen, Decrypt, and Delegate.
eM-CP-ABE algorithm
We take

1–1 MAT decomposition.
We choose
The ciphertext has two parts. In the first part, a symmetric encryption algorithm
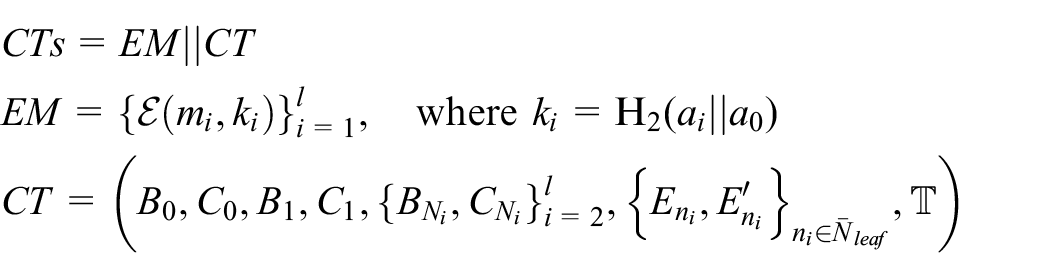
where

where
else
Otherwise, we compute
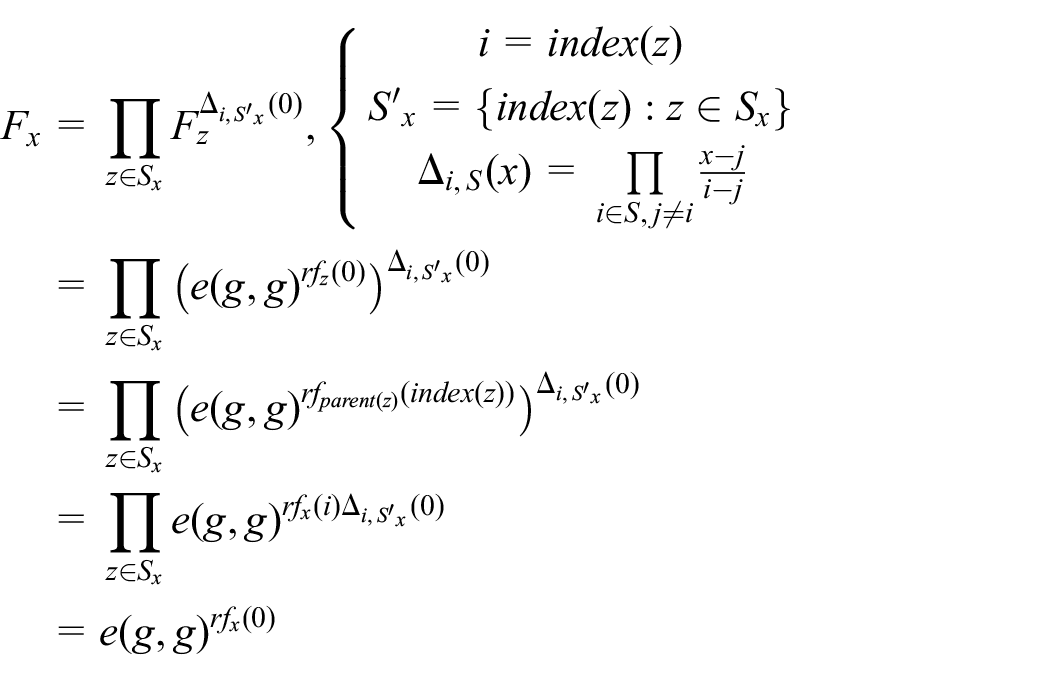
When

Similarly, if
Then

Extension
Multi-authorization
In the cloud environment, when a large number of users access a hot video content in a short time, it poses a big challenge for the attribute authorization center. Extending the single authorization center to multiple centers can alleviate the pressure effectively. Using

Hierarchical authorization group.
We assume that each attribute authorization center can complete the authorization service independently:
Multi-authorization is realized as follows.
where
where
User revocation
To realize user revocation, eM-CP-ABE adds timestamps to the MAT and attribute sets separately. Compared with CP-ABE, eM-CP-ABE is more flexible when the timestamp is added in a branch, then the algorithm implements user revocation on the corresponding privilege level. When the timestamp is a set of common attributes, the algorithm implements user revocation on all privilege levels, that is, the plaintext
1−n MAT
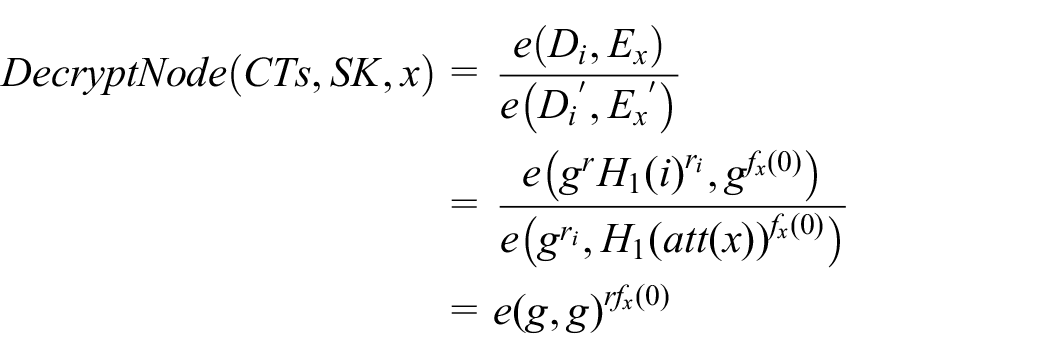
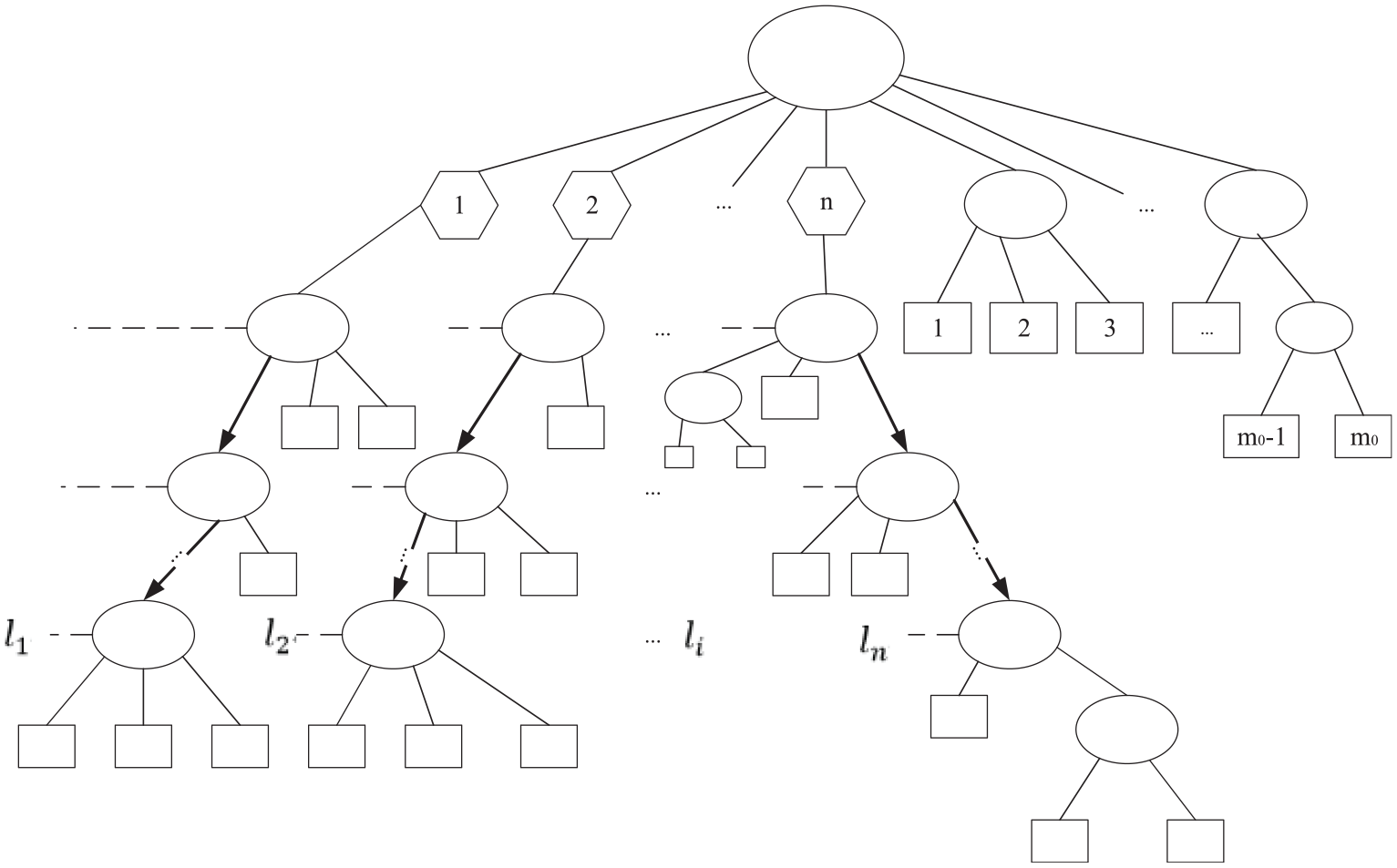
When using ABE, different access control trees need to be established for data with different access requirements. Generation and maintenance of a large number of access trees is a tough task. A
Figure 9 shows a

where

where
Security analysis
Selective-set model
There are four common types of attacks: ciphertext only, known plaintext, chosen plaintext, and chosen ciphertext. The CPA is the most powerful type of attack. If an algorithm can resist this attack, it can also resist other types of attack. To prove that eM-CP-ABE is secure, we first define a selective-set model based on CPAs. The model is described as follows:
The advantage of an adversary in this game is defined as
Proof of security
We prove that the security of eM-CP-ABE in the selective-set model reduces to the hardness of the DBDH assumption.
First, the challenger provides two groups

where
If

Or else, the ciphertext

The overall advantage of the simulator
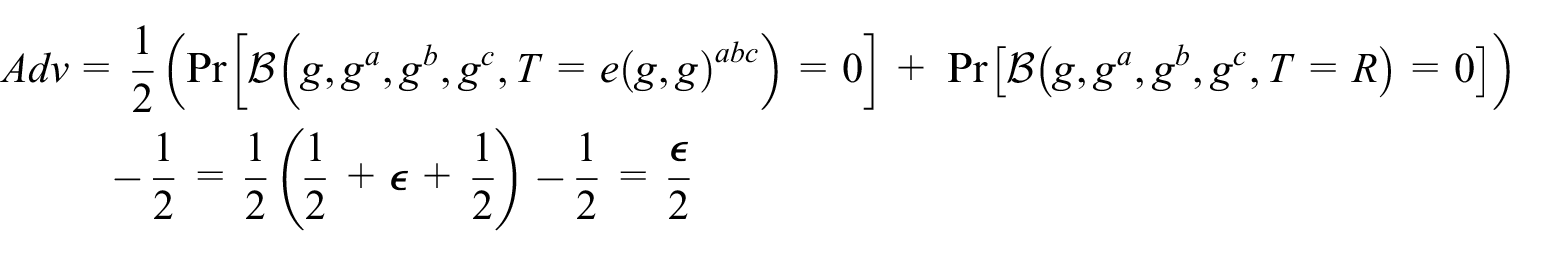
Above all, eM-CP-ABE can successfully resist chosen plaintext attacks under the DBDH assumption.
Performance analysis
Compared with the MCP-ABE 7 and CP-ABE, 9 the time and space complexity of eM-CP-ABE perform better in the following scenario. In addition, eM-CP-ABE consumes much less time than SCP-ABE 8 for each attribute in the encryption and decryption processes.
We assume a

Different access trees under the same access rules: (a) eM-CP-ABE, (b) MCP-ABE, and (c) CP-ABE.
On the basis of Figure 10, we discuss the time and space complexity of
KeyGen
For the three algorithms, there is the same attributes set
Encryption
The time needed by CP-ABE, MCP-ABE, and eM-CP-ABE to satisfy the access control (Figure 10) is shown in Table 3. Compared with MCP-ABE, eM-CP-ABE has one more
Time complexity of three encryption functions.

eM-CP-ABE: enhanced media ciphertext-policy attribute-based encryption; MCP-ABE: multi-message ciphertext-policy attribute-based encryption; CP-ABE: ciphertext-policy attribute-based encryption.
The theoretical analysis above proves that eM-CP-ABE consumes less encryption time than CP-ABE and MCP-ABE with the increase of
Note that eM-CP-ABE is used as a digital envelope to encrypt the secret keys, not the content. Therefore, the size and resolution of videos have no effect on the efficiency of eM-CP-ABE. The three elements that affect eM-CP-ABE are

Encryption time of the three algorithms.
In Figure 11, when
There are different ciphertext lengths in the three algorithms shown in Table 4. When
Space complexity of three encryption functions.

eM-CP-ABE: enhanced media ciphertext-policy attribute-based encryption; MCP-ABE: multi-message ciphertext-policy attribute-based encryption; CP-ABE: ciphertext-policy attribute-based encryption.
Decryption
We assume that the user has the second privilege in Figure 10, the MCP-ABE needs to iterate the
Different access trees in (a) MCP-ABE and (b) eM-CP-ABE.
Deployment
We deployed the streaming media system supporting HTTP live streaming (HLS) under the media framework proposed by Li et al.
30
The system is shown in Figure 13. The video provider in
Send the ABE key request to authorization center;
Get the SK;
Get the index file including the encrypted video segments keys from the video storage and distribution;
Decrypt the video segments keys using eM-CP-ABE;
Get the encrypted video segments from the video storage and distribution;
Decrypt the video segments using AES.

Deployment of eM-CP-ABE in the media cloud.
In this system, we implemented the decryption algorithm in Android version 4.2.2. After the two levels of decryption (ABE and AES), the plain-video segments are obtained. Then, the video segments are combined and played (Figure 14). In the full video playing process, the CPU consumption is stable (between 15% and 25%). It proves that the application based on our proposed algorithm can complete the video on-demand service smoothly.

Encrypted video display.
Conclusion
Media cloud built by cloud providers collects the videos from video providers and provides kinds of video services with guaranteed quality to video consumers. Meanwhile, for video providers, they pay attention to whether the media cloud can provide effective copyright protection; for video consumers, they are concerned about whether the media cloud can respond to their request in real time. Therefore, how to establish a fine-grained and fast video access control scheme is a major challenge for media cloud.
In this article, eM-CP-ABE is proposed to meet the requirement of multi-level access control of massive videos in the mobile environment. Based on the MCP-ABE, the virtual node and key chain are introduced to construct a new hierarchical access control structure. In the new structure, common attributes are extracted to the root node to save the encryption cost. When the user switches from a higher level privilege to a lower level, only a few hash operations are required without re-calling decryption in ABE, which greatly saves the decryption time and computation consumption.
In addition, we discussed the extended application of the proposed algorithm. Multi-authorization can improve the scalability of the algorithm. Using integer comparison, user revocation can be realized. More important, the access tree in eM-CP-ABE can be extended to
Footnotes
Acknowledgements
The authors thank the anonymous reviewers for their very helpful comments which helped to improve the presentation of this article.
Handling Editor: Hongxin Hu
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The research was funded by China Postdoctoral Science Foundation 2019M663358, Fundamental Research Funds for the Central Universities of the Communication University of China (CUC2019A009), the High-quality and Cutting-edge Disciplines Construction Project for Universities in Beijing (Internet Information, Communication University of China; CUC190J054), and National Key Task Team Cultivation Project 2019 (CUC19ZD003).
